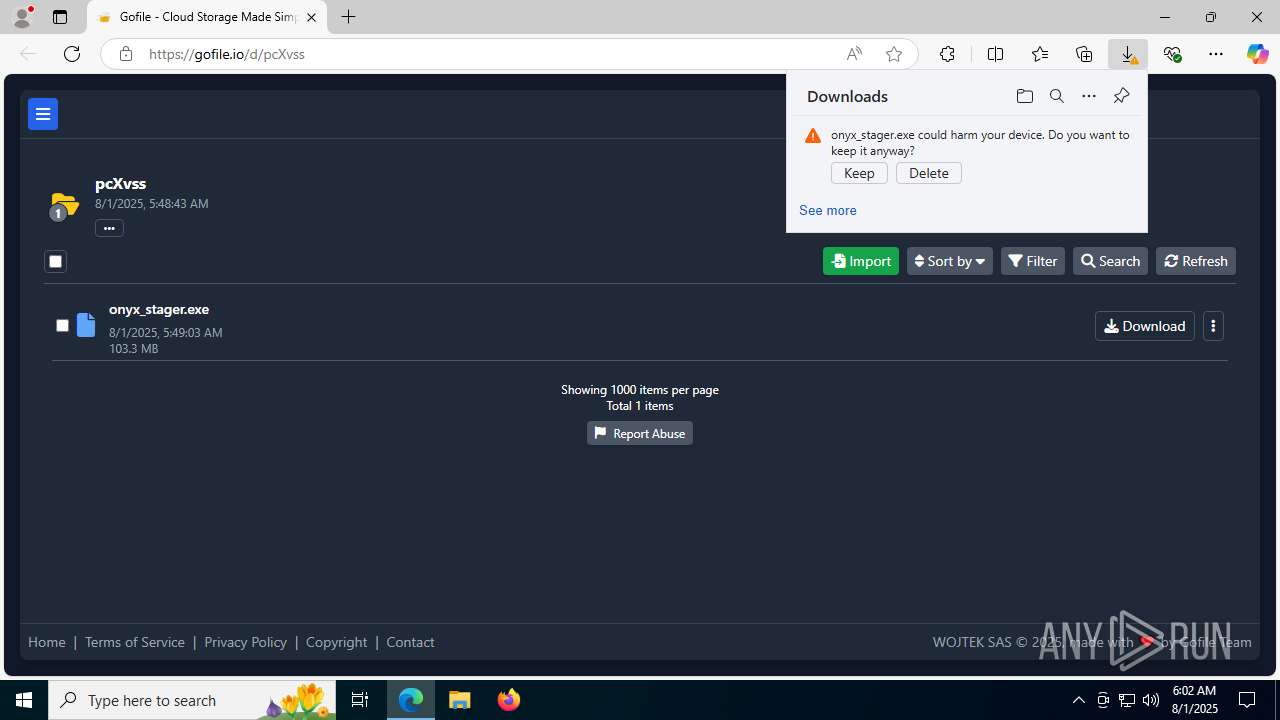
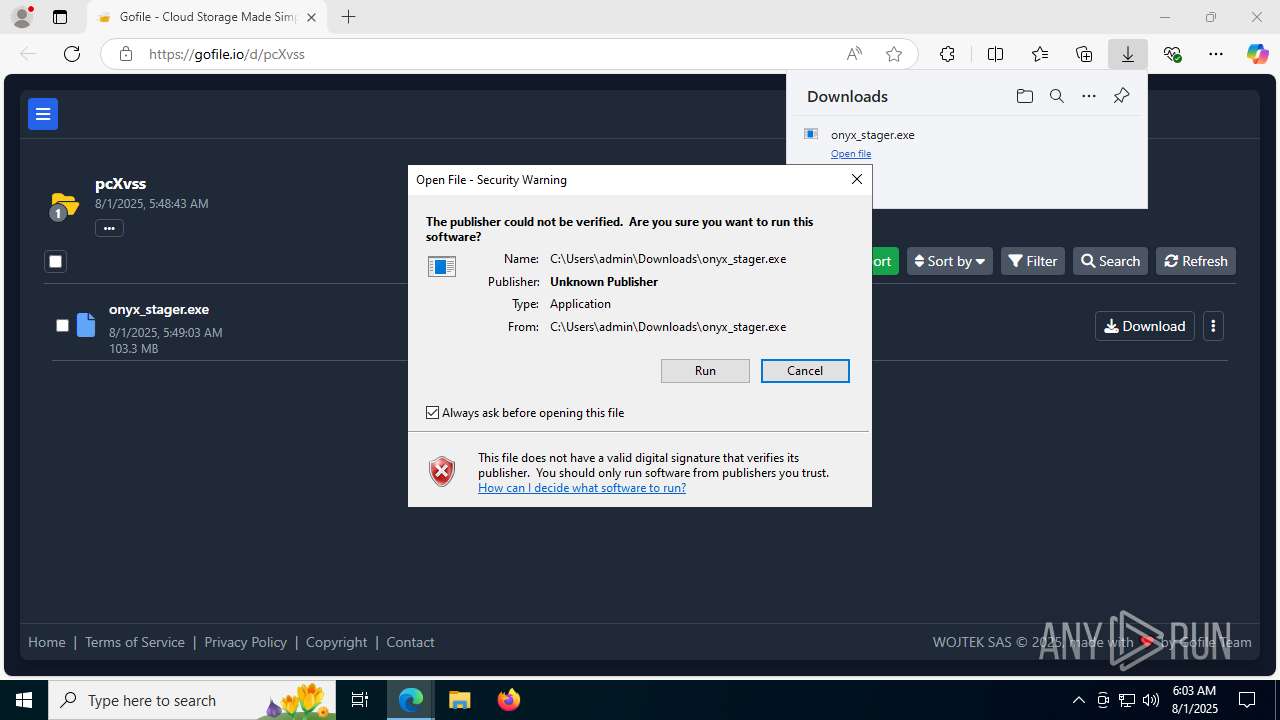
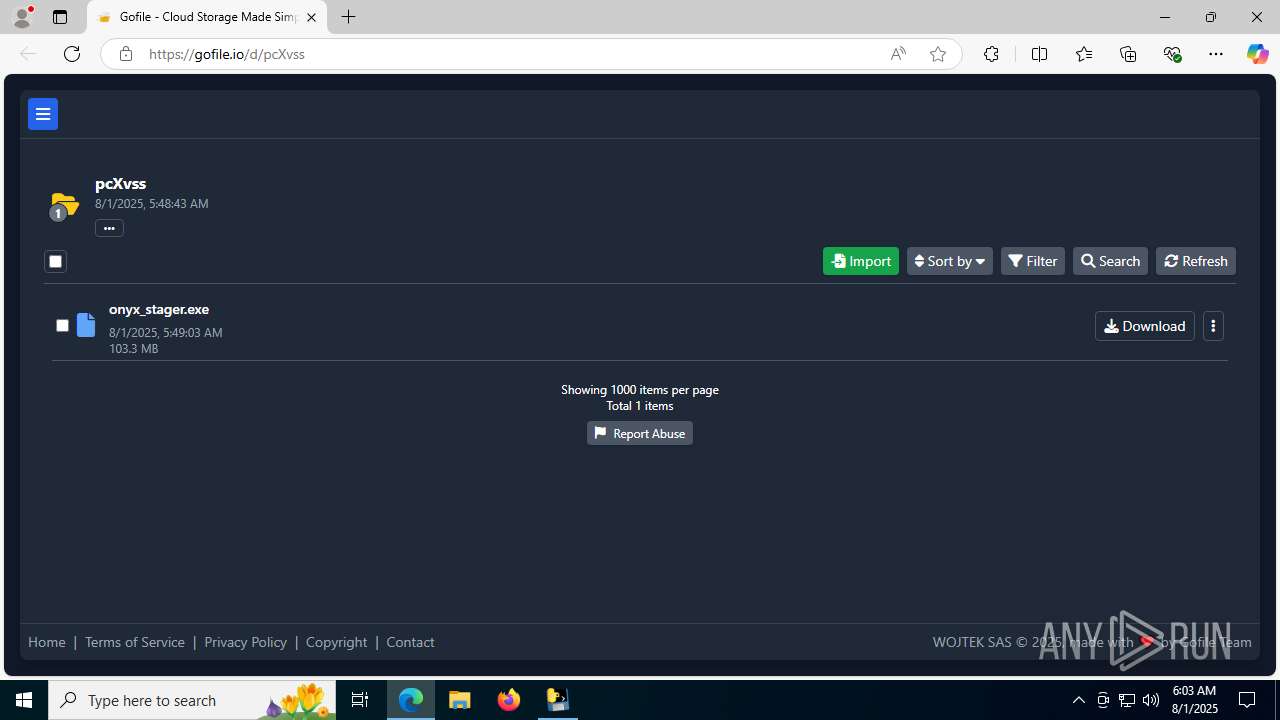
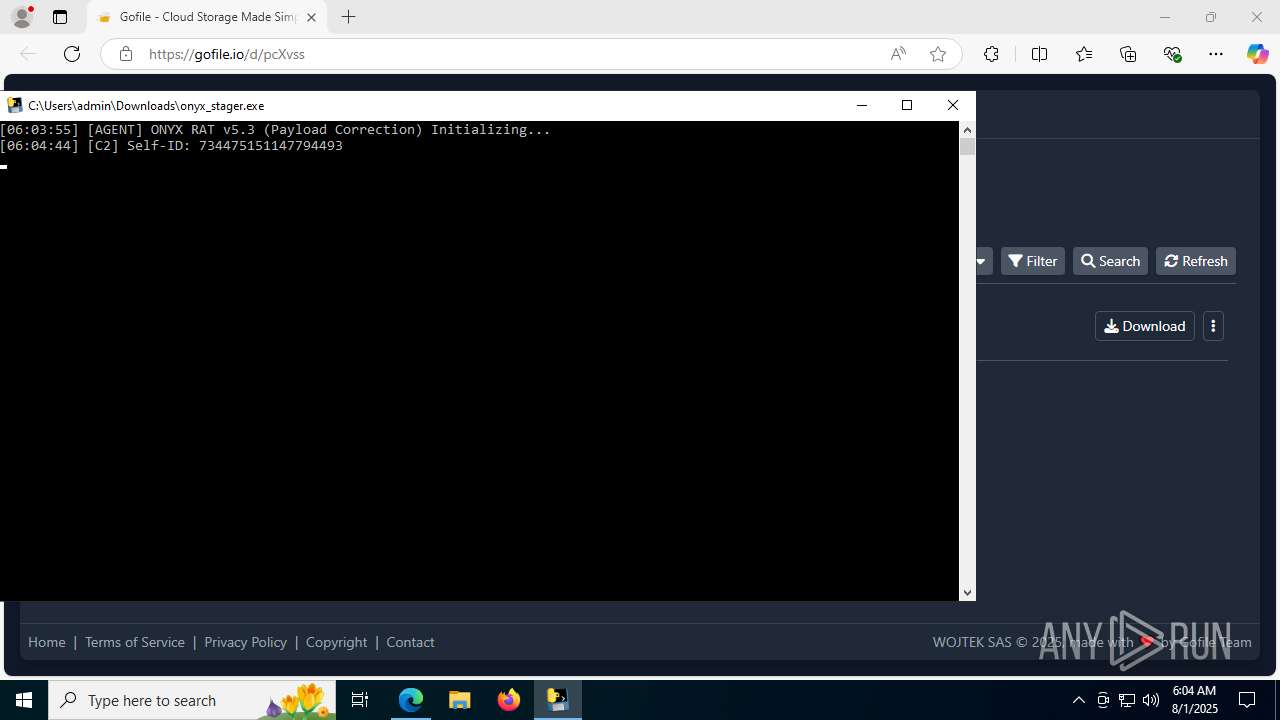
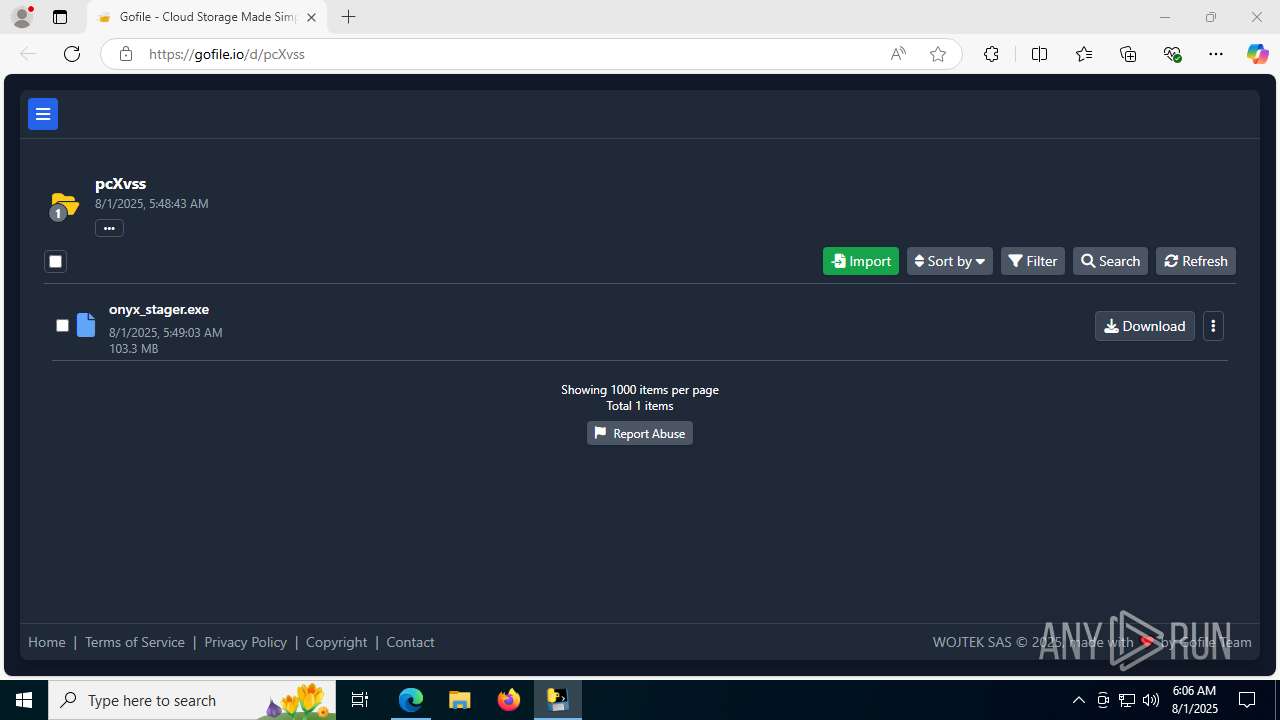
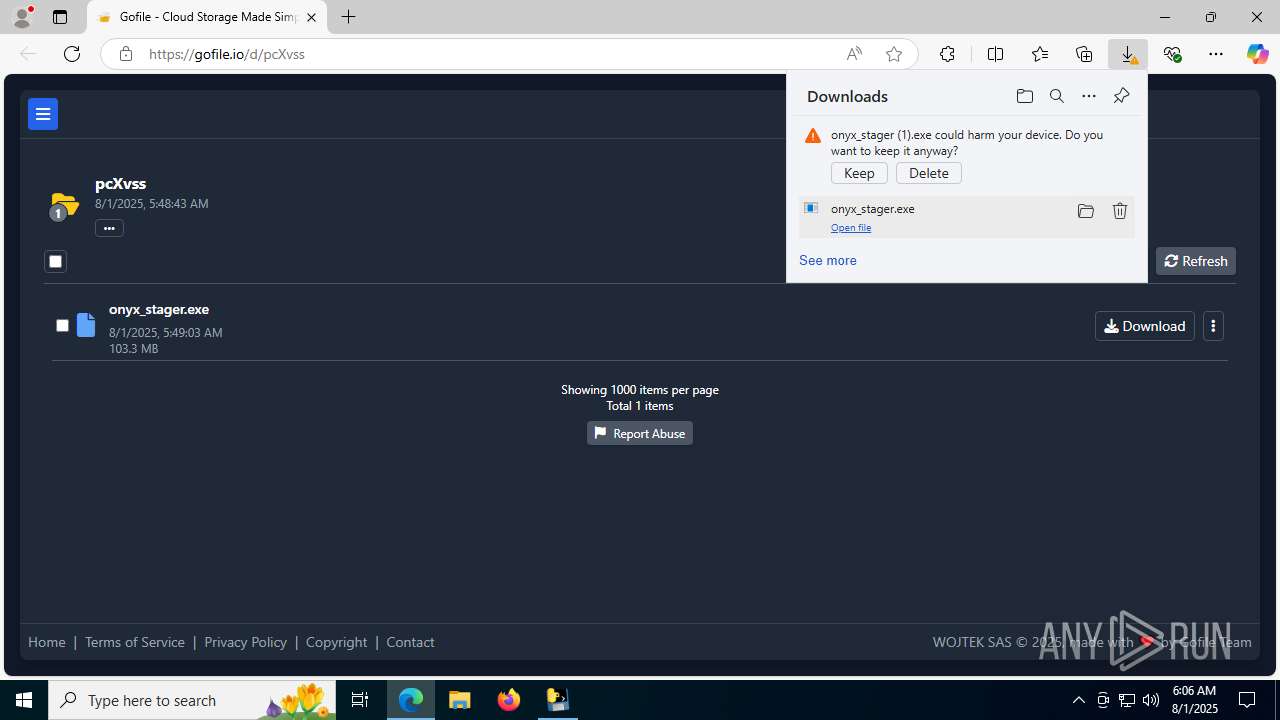
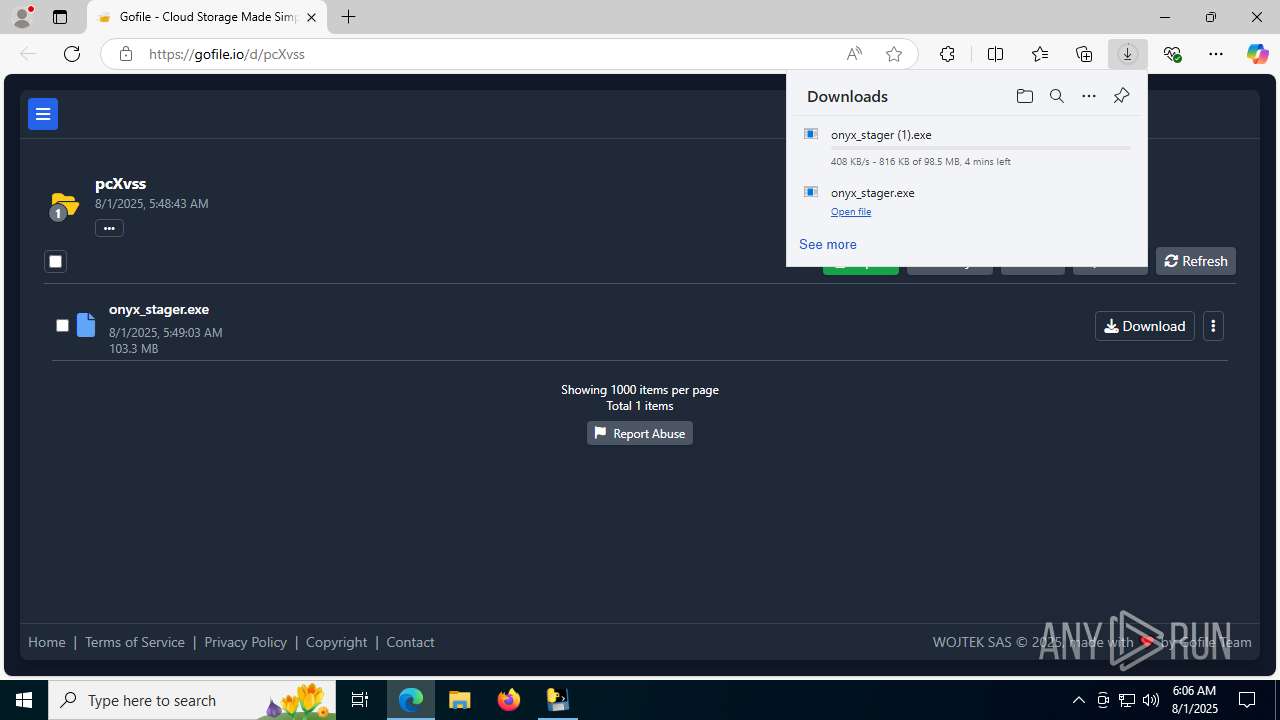
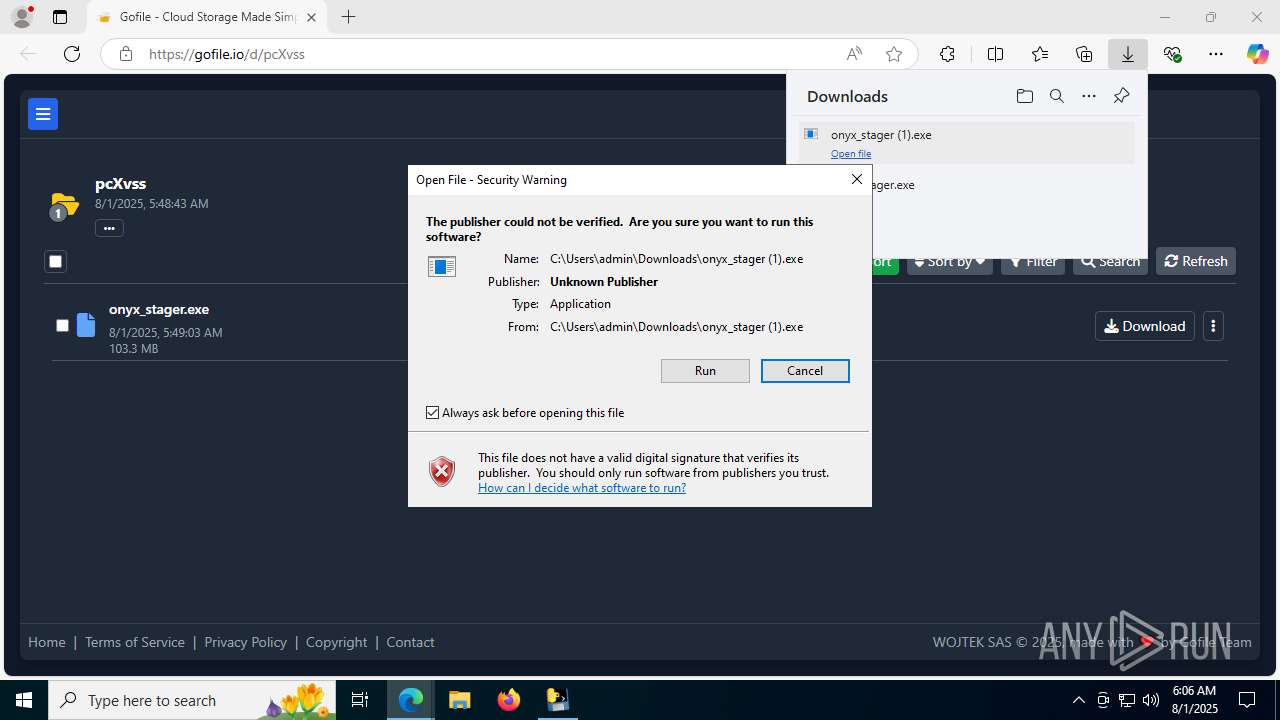
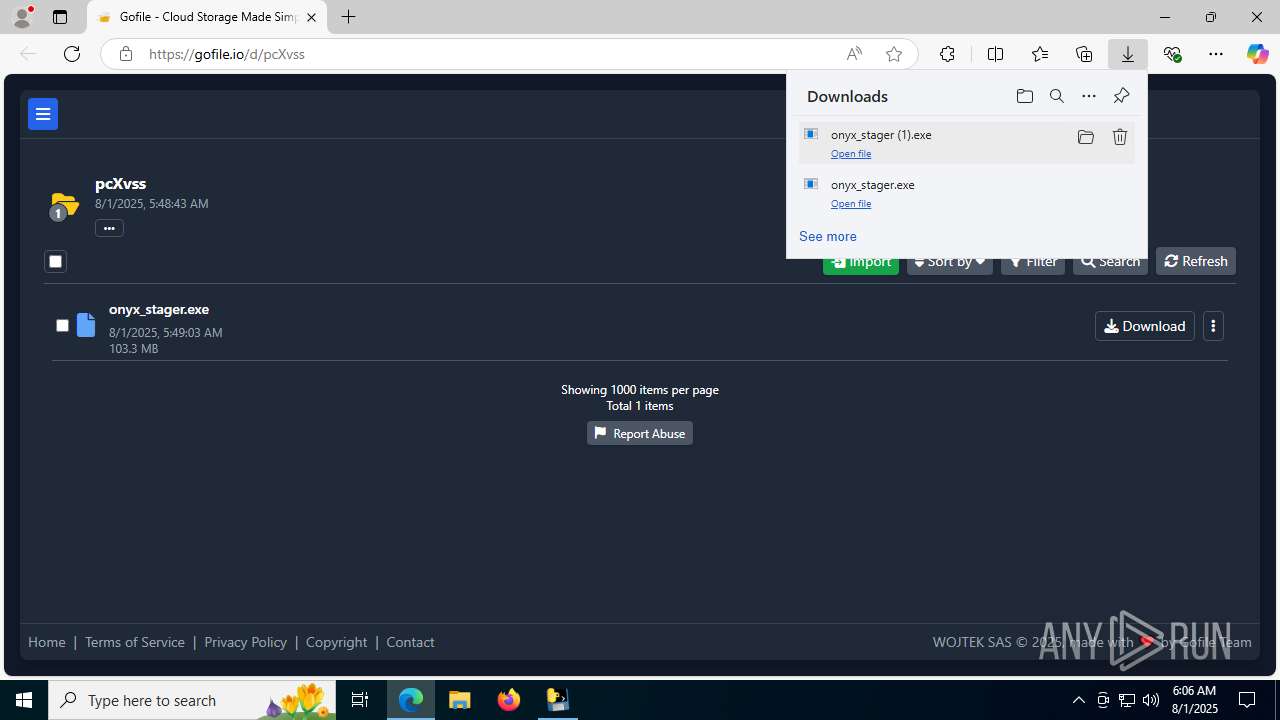
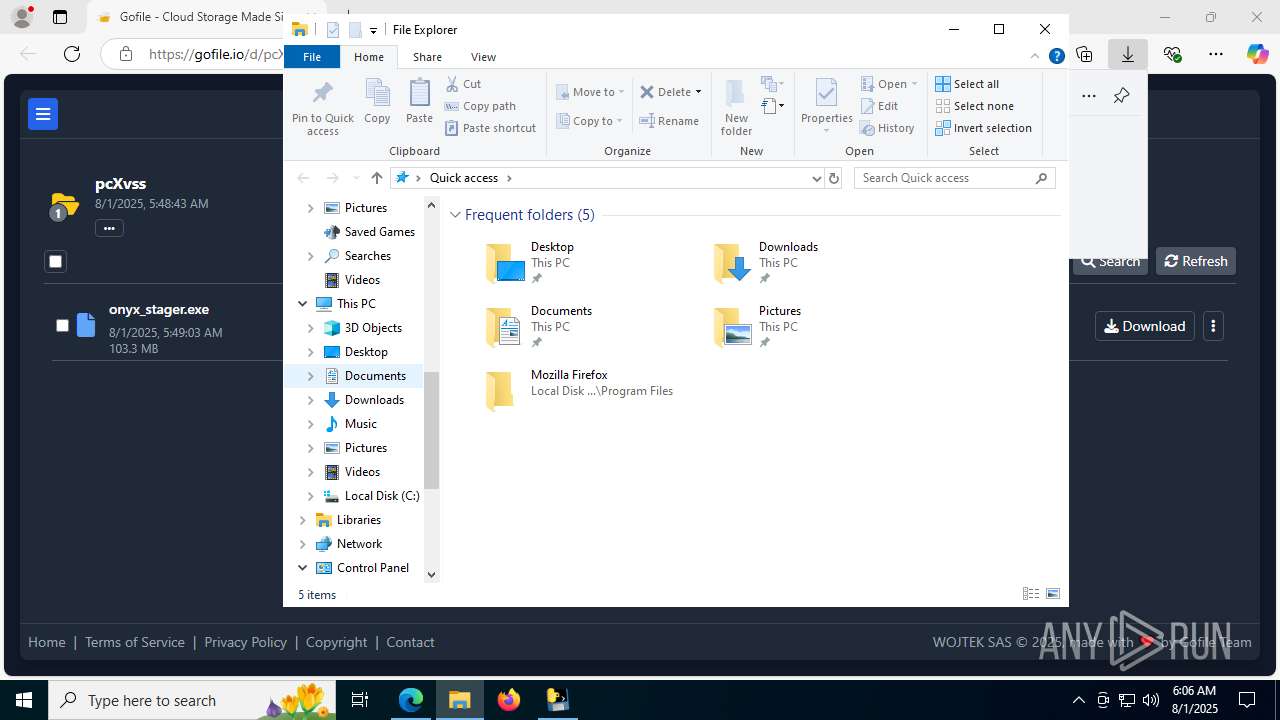
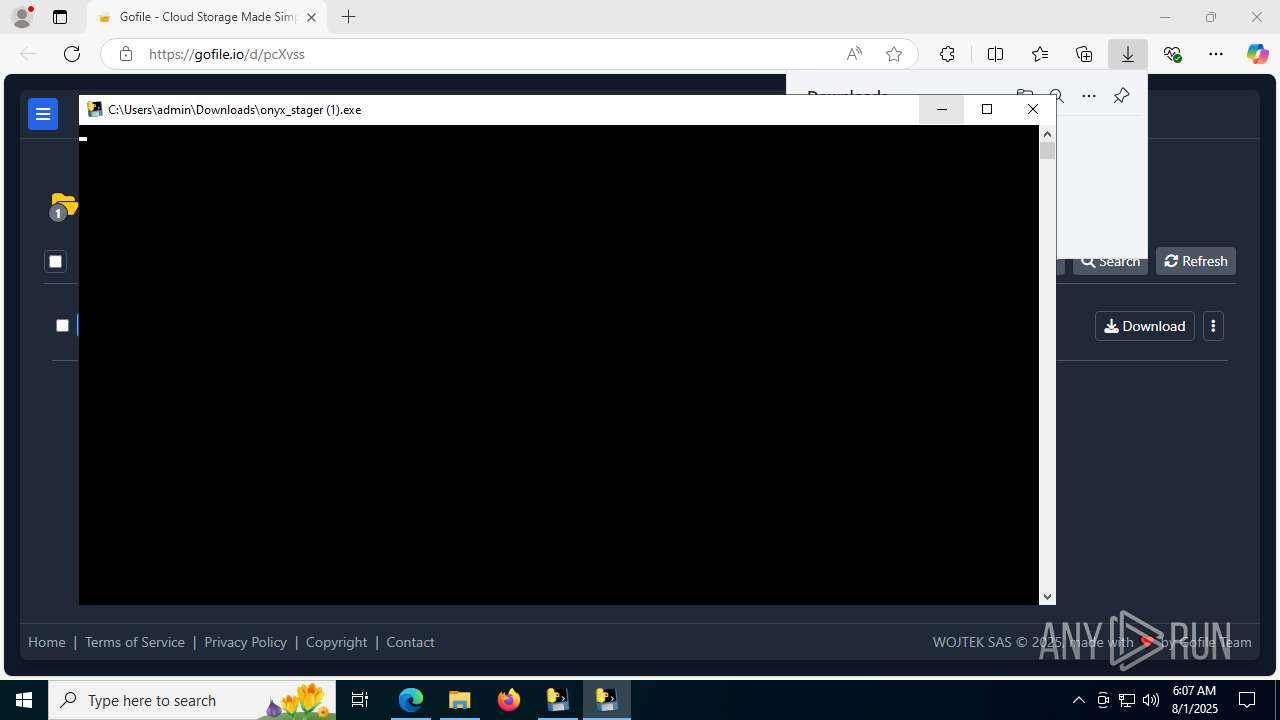
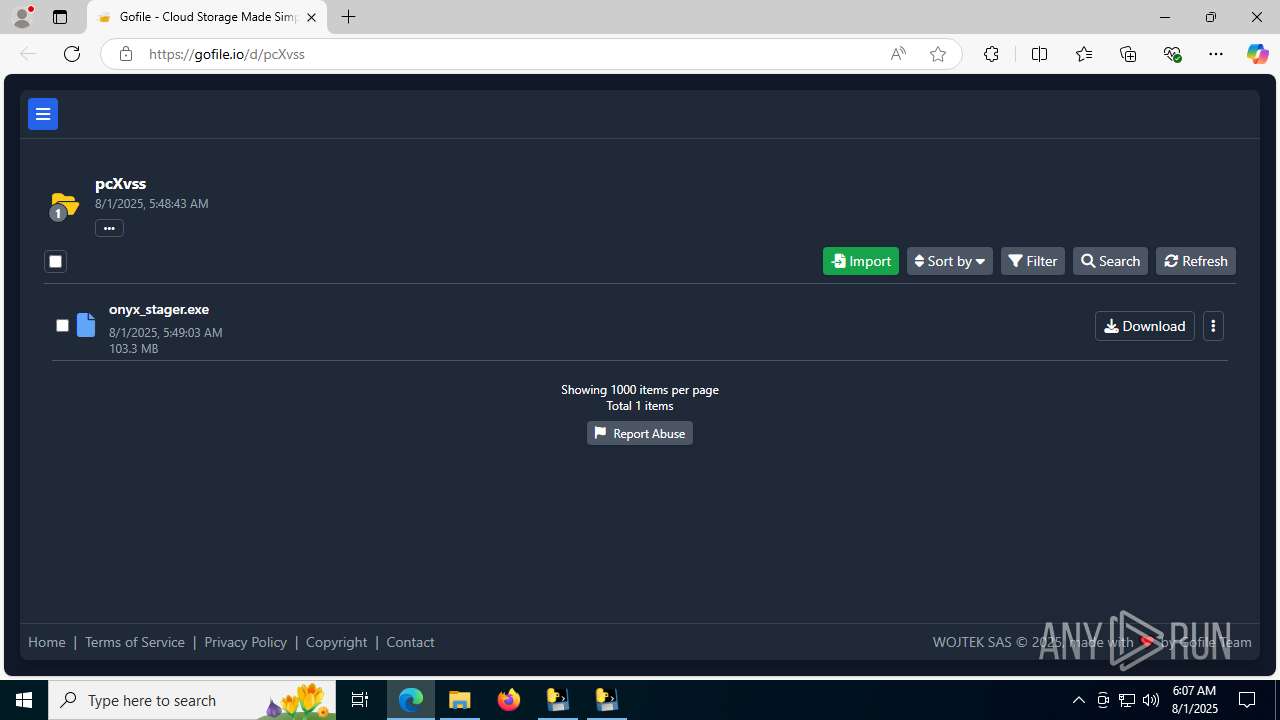
| URL: | https://gofile.io/d/pcXvss |
| Full analysis: | https://app.any.run/tasks/fb682162-ef83-41bc-8e82-bc7a6d3c0950 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 06:02:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 37AD3410DAE0BEFB0F9D6D3DDEA9B339 |
| SHA1: | CD8083AE064FAA46DE07363E10E586C56A7B4423 |
| SHA256: | 090FB405BC900E09AEFE247080A95D4A2466AA0D87610327F8370FE681ADE2E0 |
| SSDEEP: | 3:N8rxL1s9aW:2ZyaW |
MALICIOUS
No malicious indicators.SUSPICIOUS
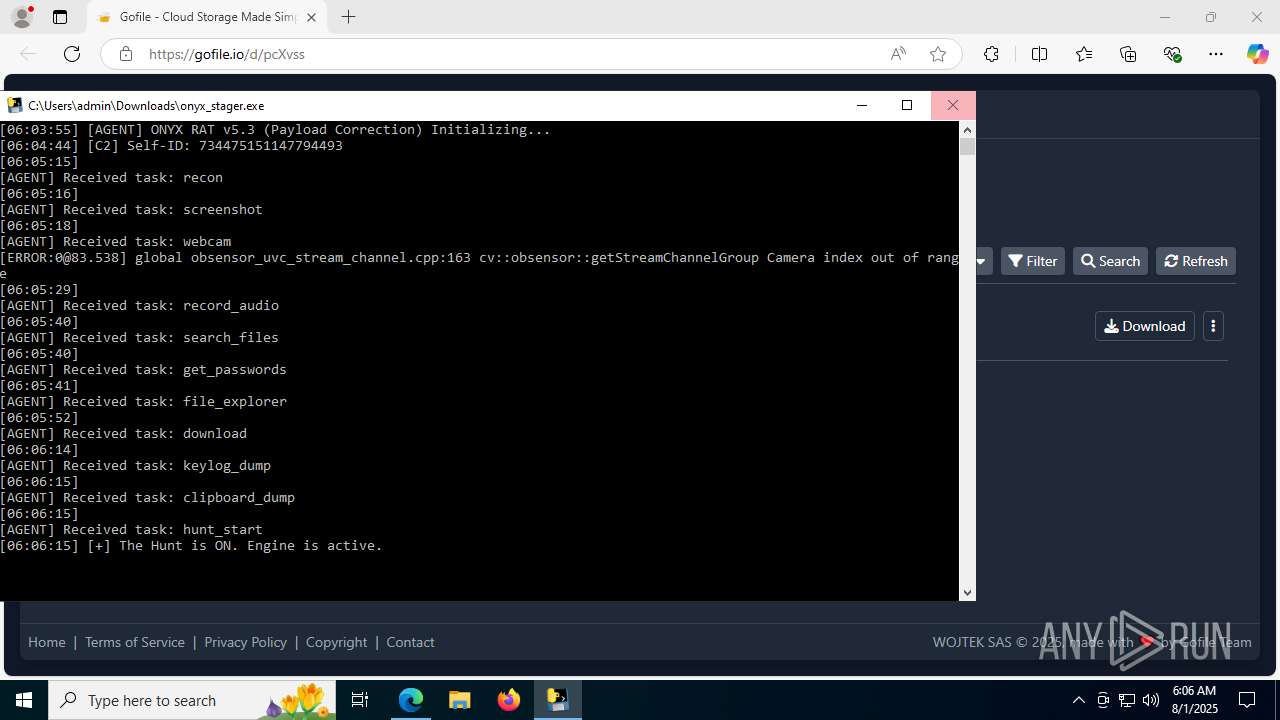
Executable content was dropped or overwritten
- onyx_stager.exe (PID: 1660)
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
Process drops python dynamic module
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
Starts CMD.EXE for commands execution
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 6788)
Process drops legitimate windows executable
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
The process drops C-runtime libraries
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
Application launched itself
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 6788)
Loads Python modules
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 6788)
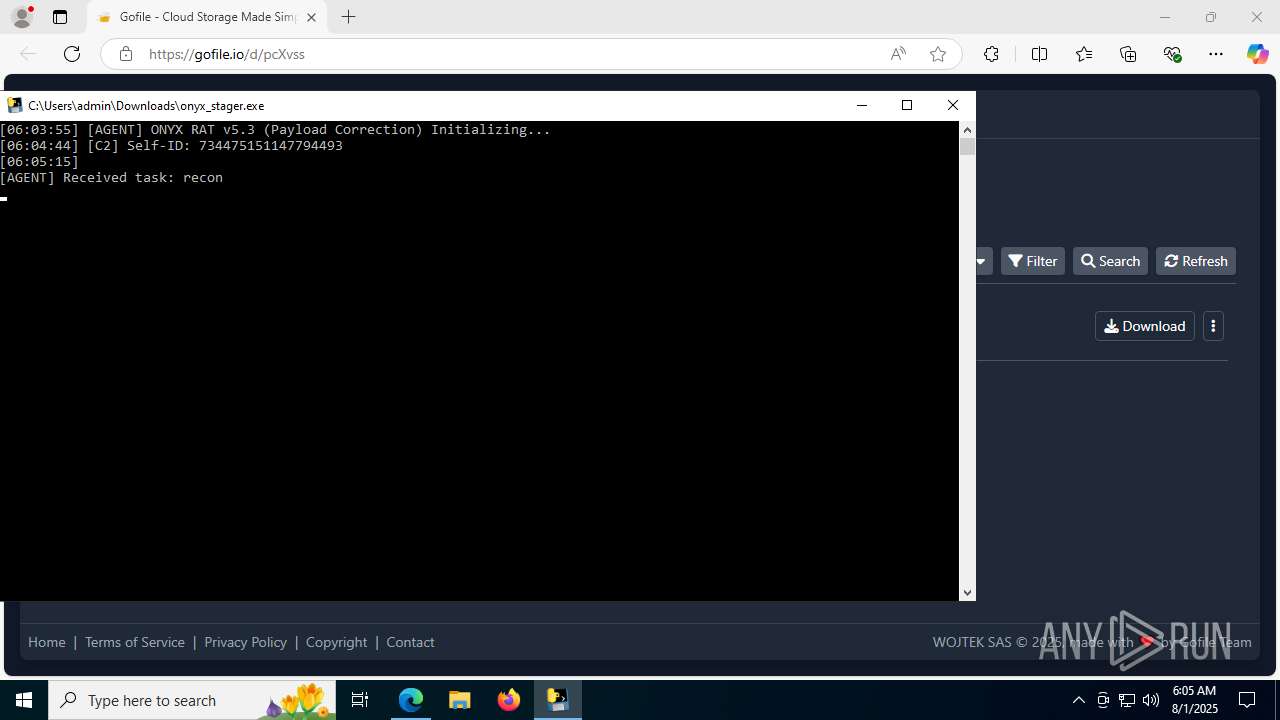
Get information on the list of running processes
- cmd.exe (PID: 620)
- onyx_stager.exe (PID: 5824)
There is functionality for taking screenshot (YARA)
- onyx_stager.exe (PID: 5824)
Reads security settings of Internet Explorer
- onyx_stager (1).exe (PID: 6788)
Reads the date of Windows installation
- onyx_stager (1).exe (PID: 6788)
INFO
Reads the computer name
- identity_helper.exe (PID: 7664)
- onyx_stager.exe (PID: 1660)
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 6788)
- onyx_stager (1).exe (PID: 7712)
Application launched itself
- msedge.exe (PID: 3392)
Checks supported languages
- identity_helper.exe (PID: 7664)
- onyx_stager.exe (PID: 1660)
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
- onyx_stager (1).exe (PID: 6788)
Reads Environment values
- identity_helper.exe (PID: 7664)
Create files in a temporary directory
- onyx_stager.exe (PID: 1660)
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
UPX packer has been detected
- onyx_stager.exe (PID: 5824)
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
Executable content was dropped or overwritten
- msedge.exe (PID: 3392)
The sample compiled with english language support
- onyx_stager.exe (PID: 1660)
- onyx_stager (1).exe (PID: 5988)
- onyx_stager (1).exe (PID: 7712)
PyInstaller has been detected (YARA)
- onyx_stager.exe (PID: 1660)
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 5988)
Reads the machine GUID from the registry
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 6788)
Checks operating system version
- onyx_stager.exe (PID: 5824)
- onyx_stager (1).exe (PID: 6788)
Attempting to use instant messaging service
- onyx_stager.exe (PID: 5824)
Checks proxy server information
- slui.exe (PID: 7064)
- onyx_stager.exe (PID: 5824)
Reads the software policy settings
- slui.exe (PID: 7064)
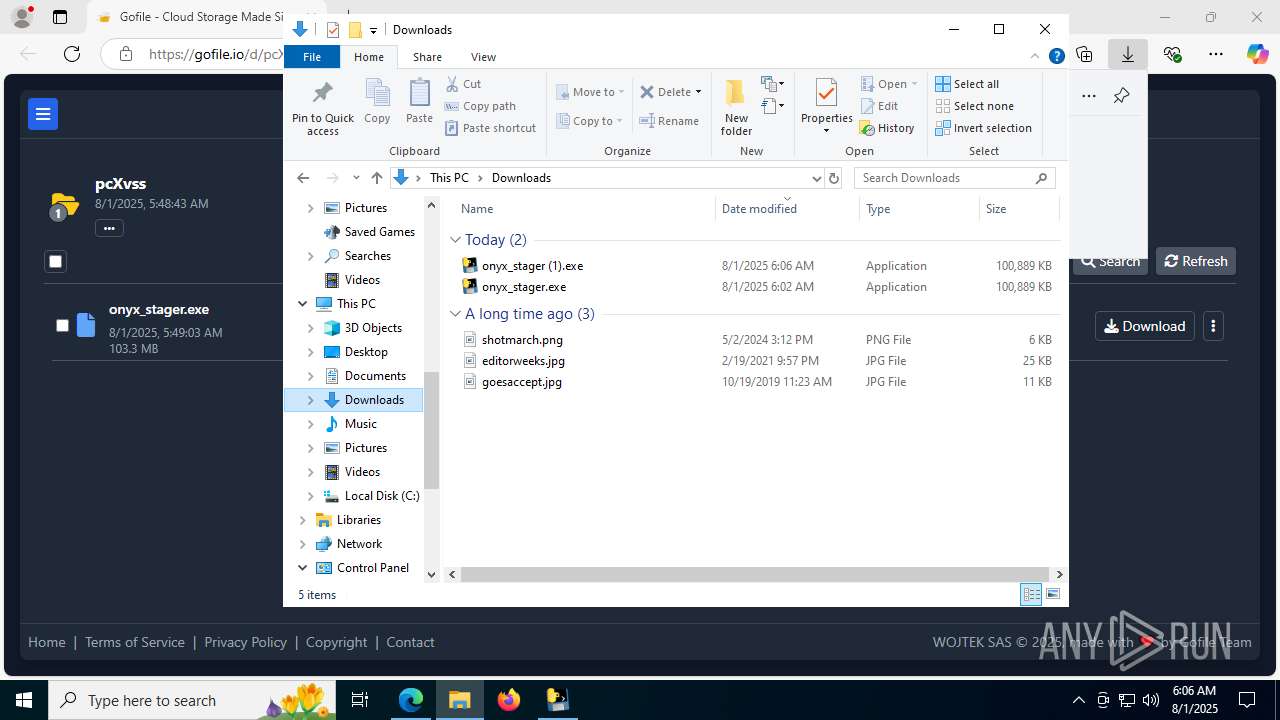
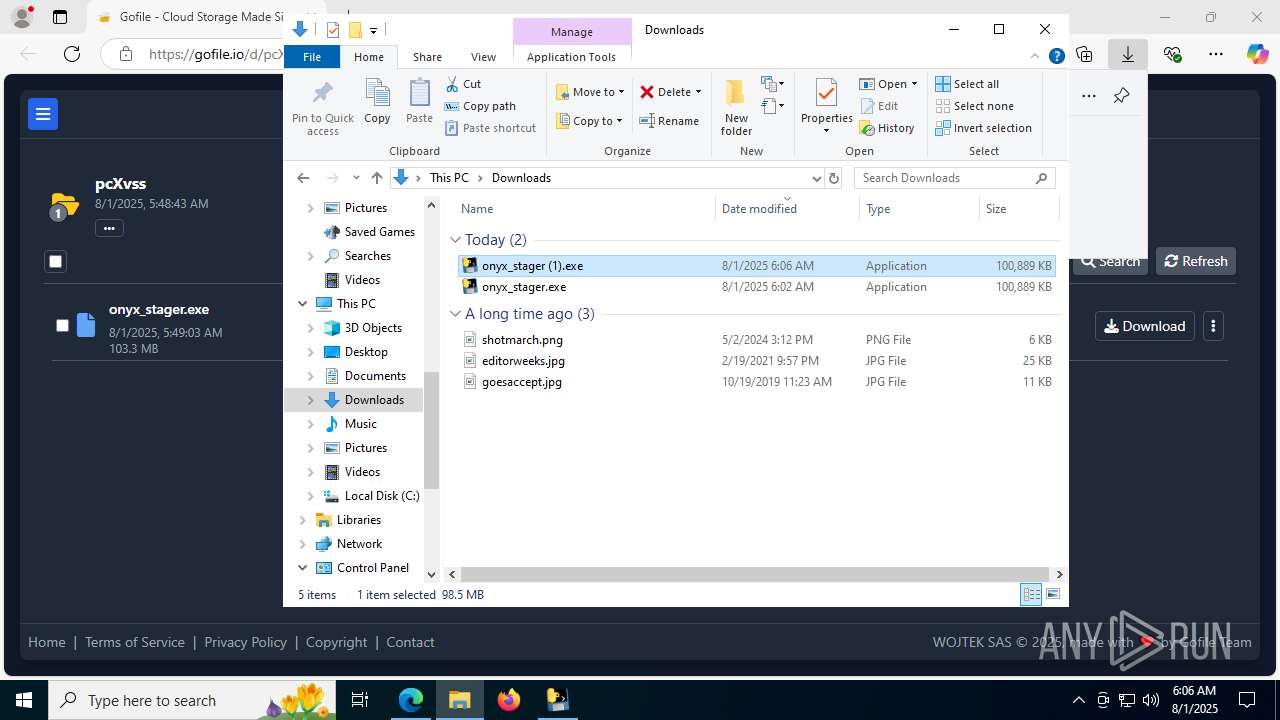
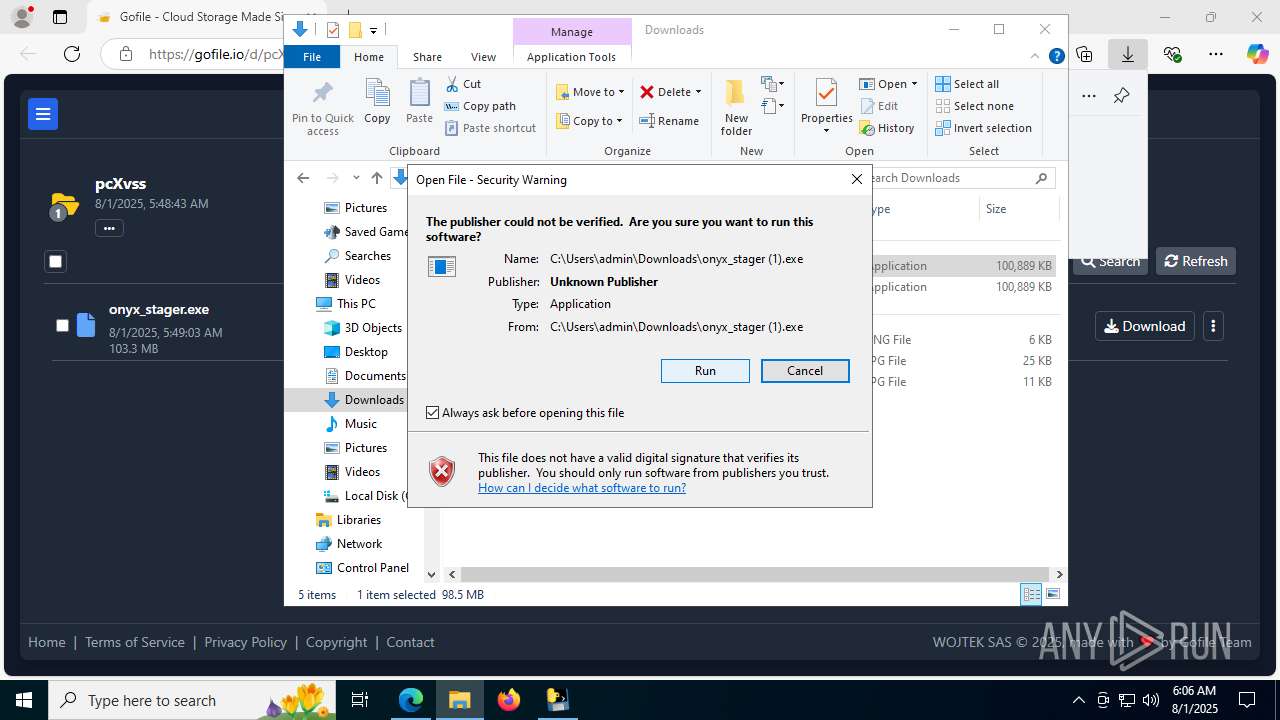
Manual execution by a user
- onyx_stager (1).exe (PID: 5988)
Process checks computer location settings
- onyx_stager (1).exe (PID: 6788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
58
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6008,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=6016 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | C:\WINDOWS\system32\cmd.exe /c "tasklist" | C:\Windows\System32\cmd.exe | — | onyx_stager.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2324,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=5896 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7380,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=6168 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5876,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=7228 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\Downloads\onyx_stager.exe" | C:\Users\admin\Downloads\onyx_stager.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1712 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7368,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=7476 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3612,i,13649438688900960981,15348986052539683665,262144 --variations-seed-version --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 907
Read events
10 860
Write events
43
Delete events
4
Modification events
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31195817 | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5168) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
539
Suspicious files
277
Text files
2 680
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d59a.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d5c9.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d5c9.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d5aa.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d5d9.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
116
DNS requests
88
Threats
114
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4124 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:C-sOtnFHoYT0Q8JAsEcbcMNzhnVj7zXdalHNznXEGFg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3644 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5460 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5460 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8164 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754608597&P2=404&P3=2&P4=NeNNiT%2bTSURouXzid14vDKWdxq95XFSVyb%2fGdSnV%2bSzwN6pUx7i%2bUp8JOb3oJUw7dJP6VyBC7Cvrr3Mb6Ta%2b1A%3d%3d | unknown | — | — | whitelisted |
8164 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754608599&P2=404&P3=2&P4=VM0sEafqf918LI9A%2b246ZOu7Pa1OklPJapCswhAXDO7%2b7YUMZEab5EOvMa6WlN9bZ%2fW16asnLkCnNXvbkHFPRw%3d%3d | unknown | — | — | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754608597&P2=404&P3=2&P4=NeNNiT%2bTSURouXzid14vDKWdxq95XFSVyb%2fGdSnV%2bSzwN6pUx7i%2bUp8JOb3oJUw7dJP6VyBC7Cvrr3Mb6Ta%2b1A%3d%3d | unknown | — | — | whitelisted |
8164 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754608599&P2=404&P3=2&P4=VM0sEafqf918LI9A%2b246ZOu7Pa1OklPJapCswhAXDO7%2b7YUMZEab5EOvMa6WlN9bZ%2fW16asnLkCnNXvbkHFPRw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4124 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4124 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4124 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
4124 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4124 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
s.gofile.io |
| whitelisted |
api.gofile.io |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4124 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4124 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4124 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4124 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4124 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |