| File name: | MultiTool.exe |
| Full analysis: | https://app.any.run/tasks/9079bb6e-d745-4a4d-847e-c87c245321e9 |
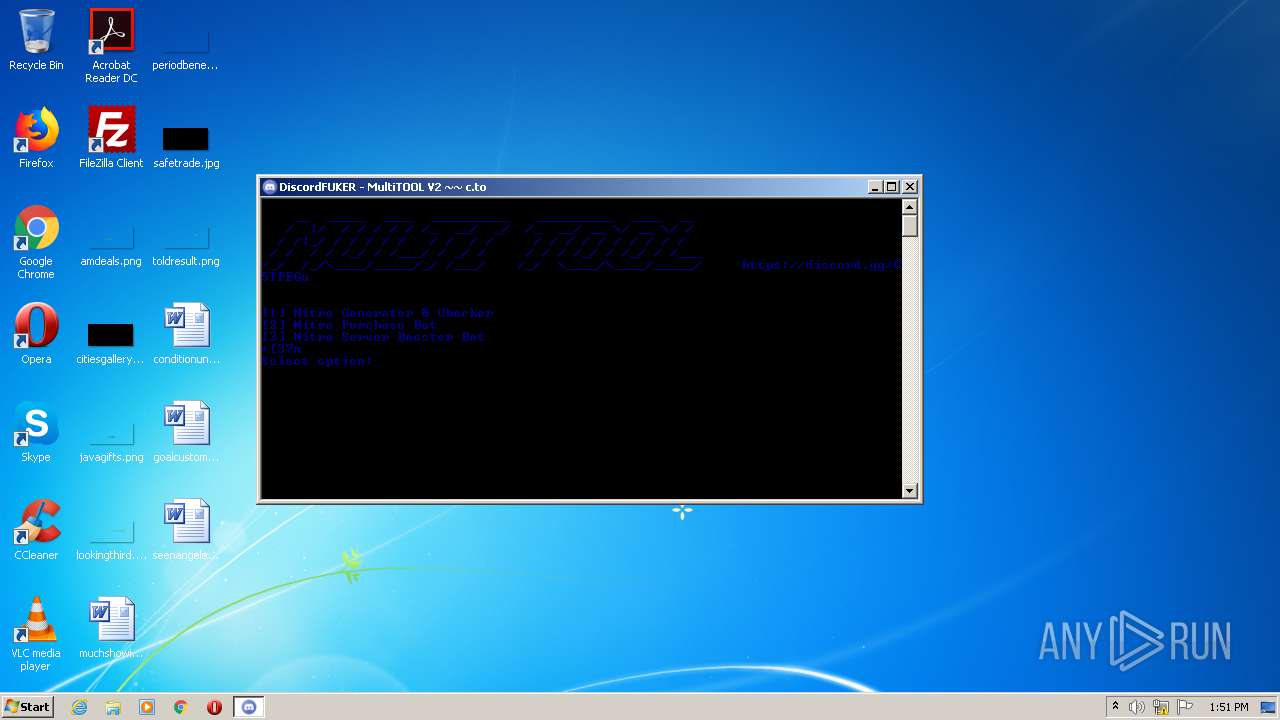
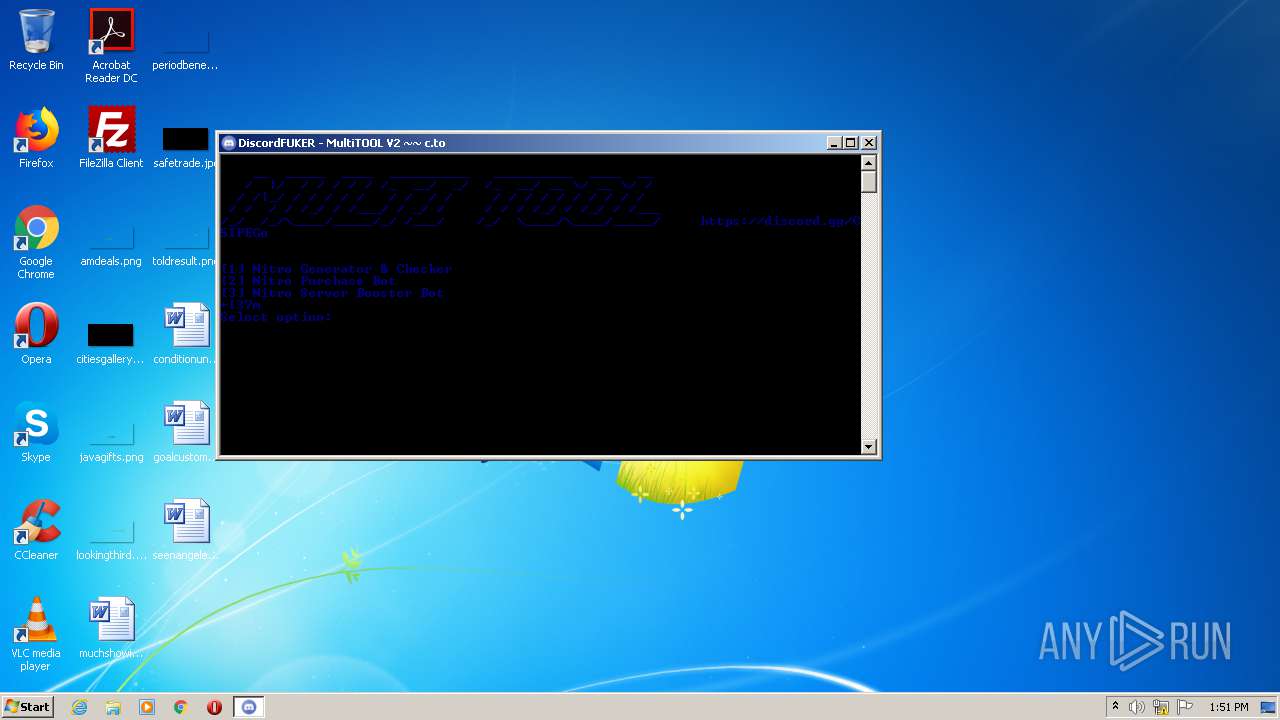
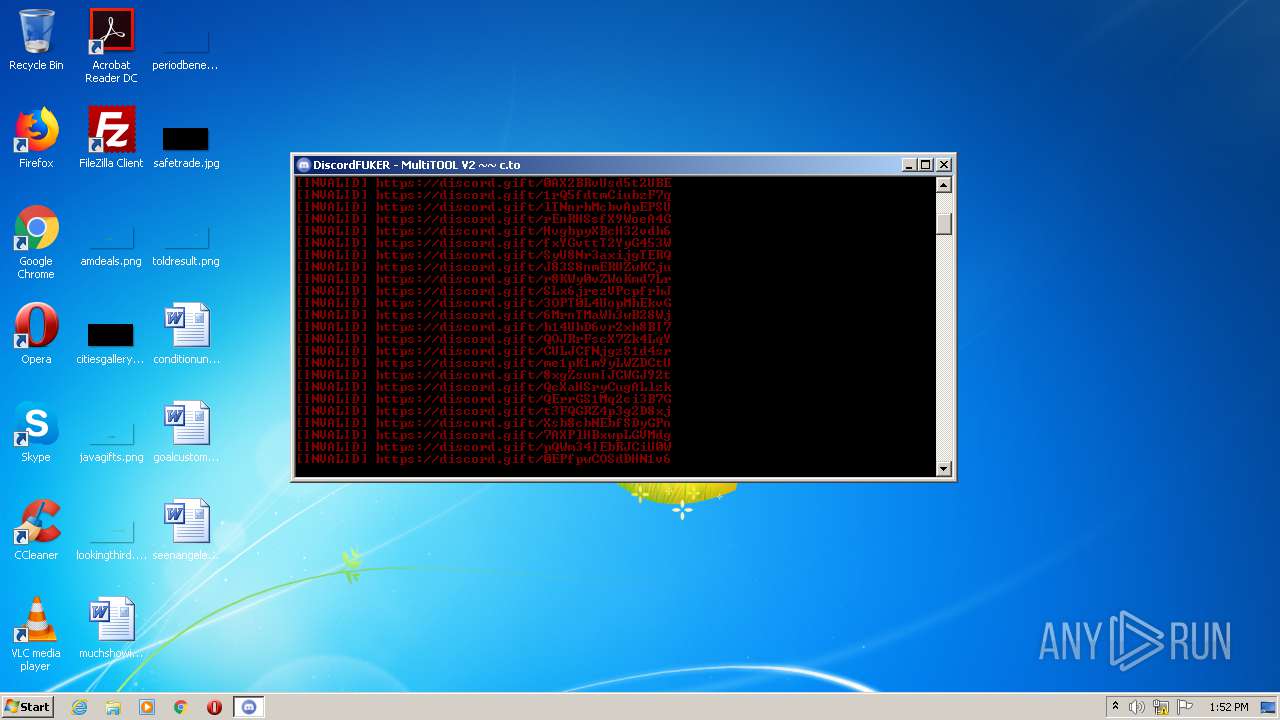
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 12:50:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | B312DDB69E2341D958F0007713A2E803 |
| SHA1: | B118D48B60254B9E9189F0C0E8FC87D3A12686ED |
| SHA256: | 090EE03CA195540324145A69318789C32DBF10097E45B3D534513658F7518538 |
| SSDEEP: | 196608:jcGOfAxEoP1HSsimvlG2Ms0tbYPvbJQlHJCsj58Cr/JZi7bb3:Gf8P1pimt2kJQlpZBKf |
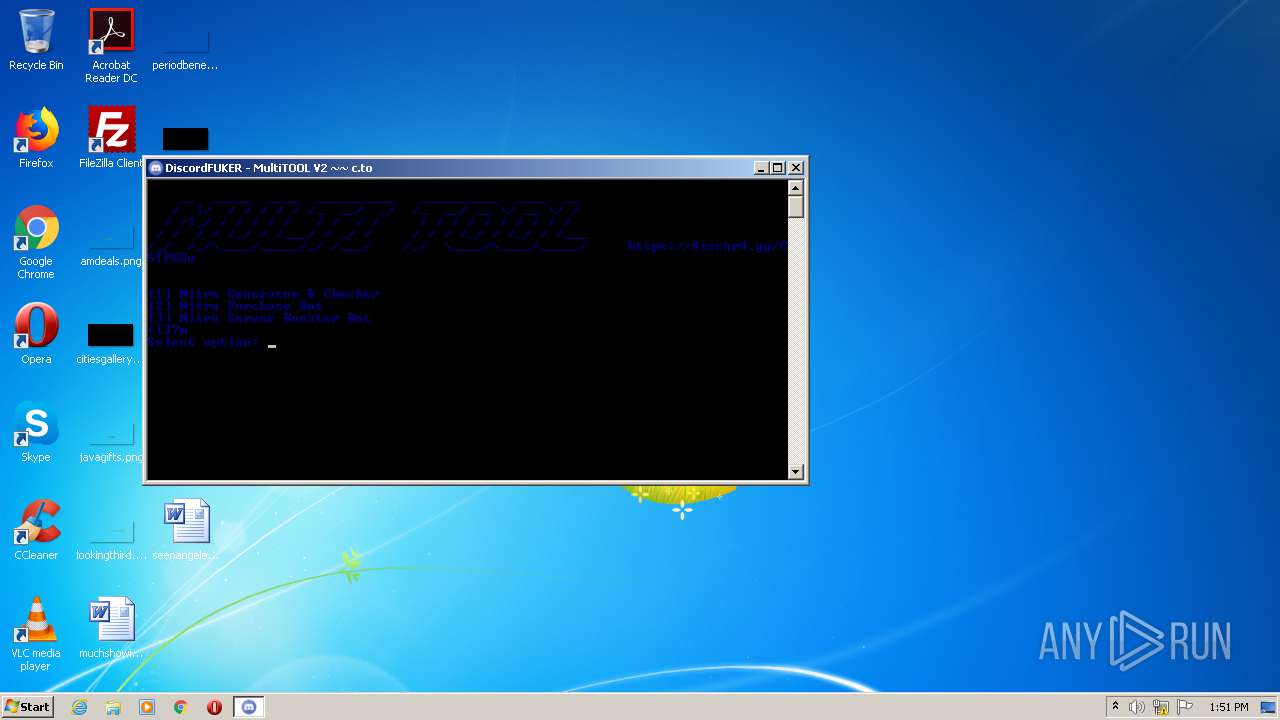
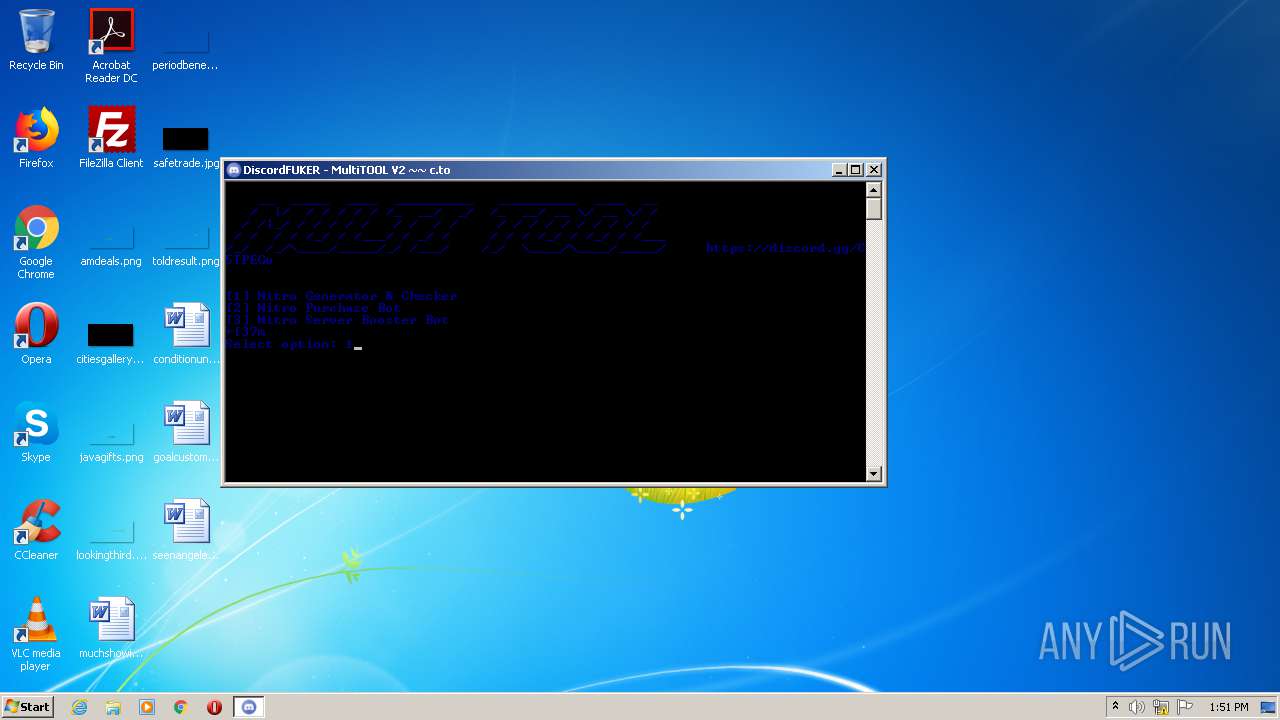
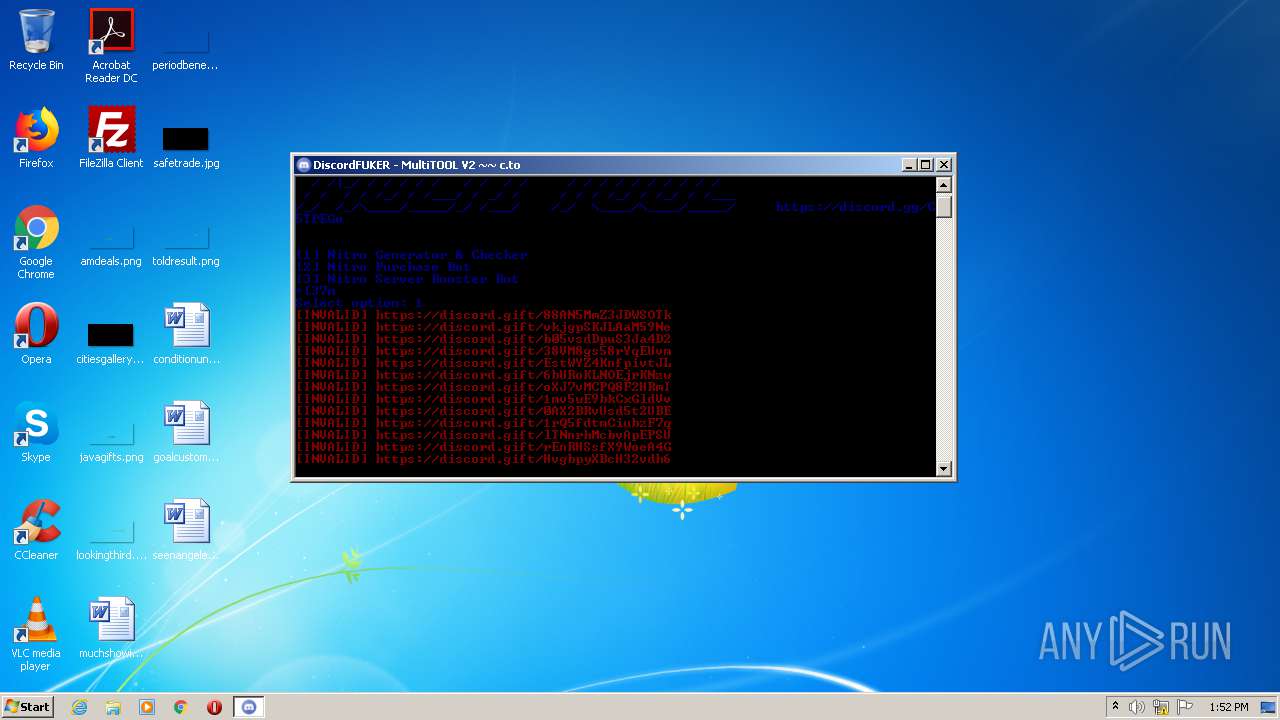
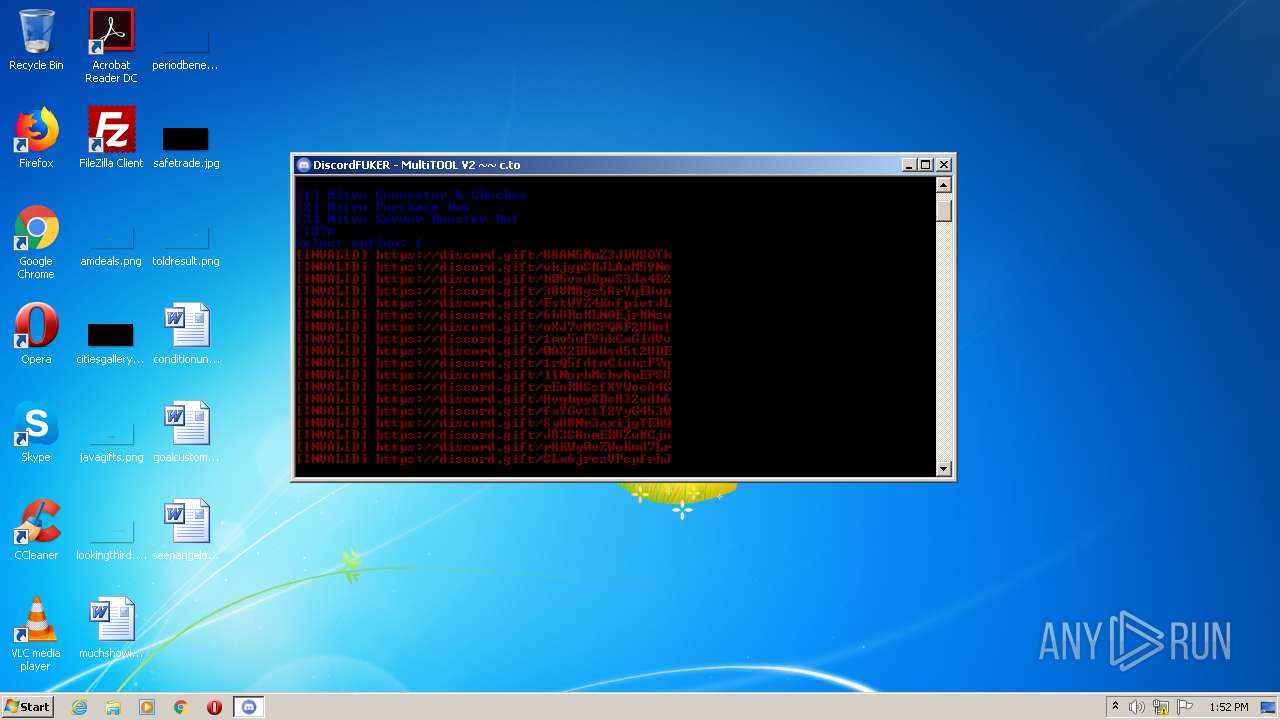
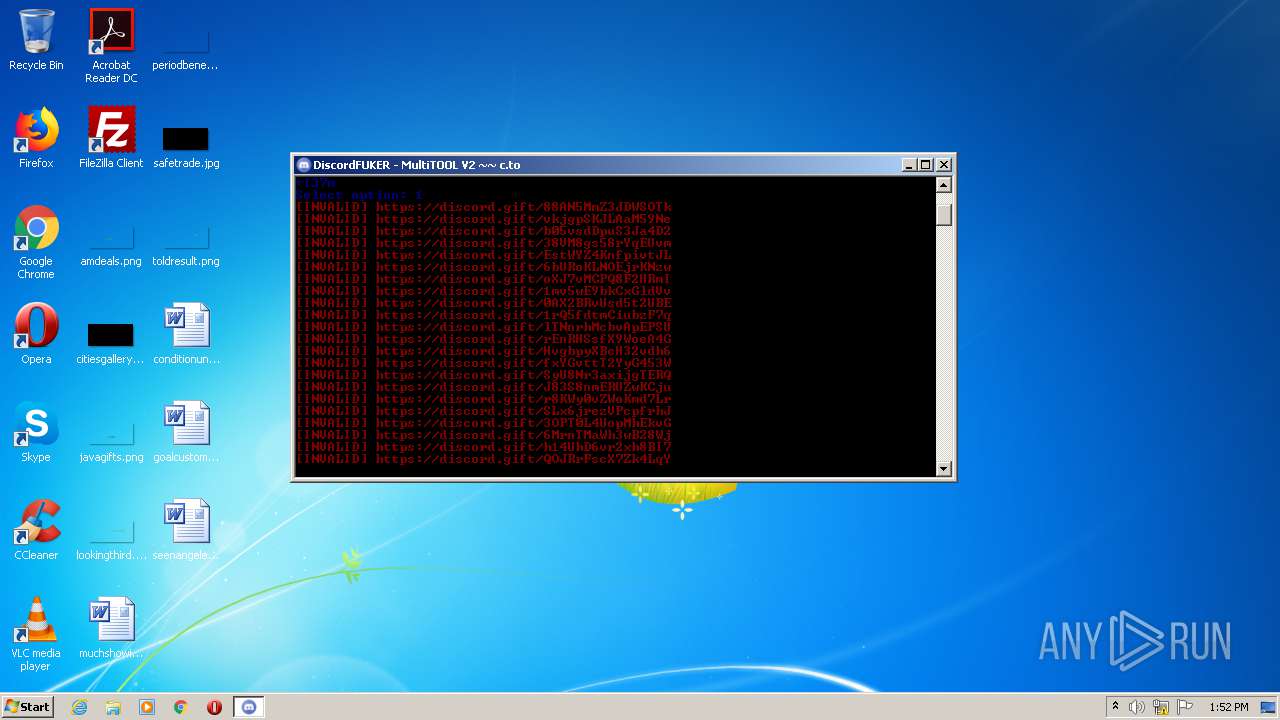
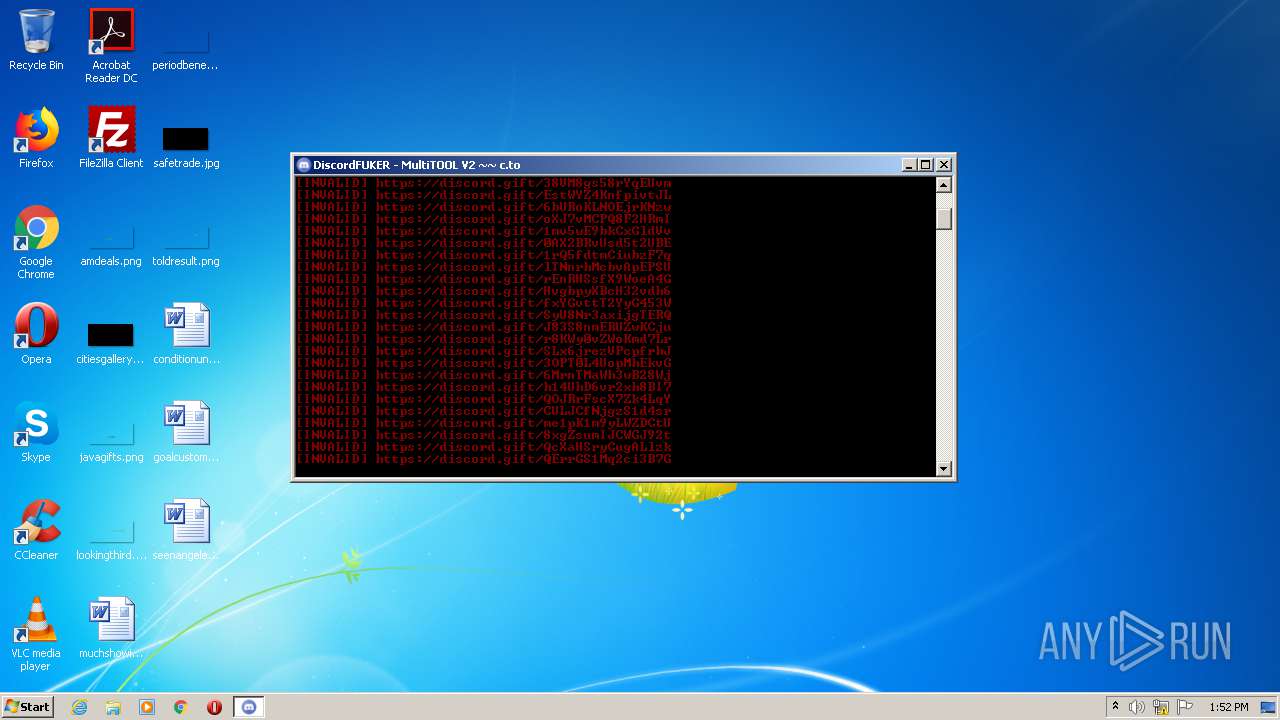
MALICIOUS
Loads dropped or rewritten executable
- MultiTool.exe (PID: 3012)
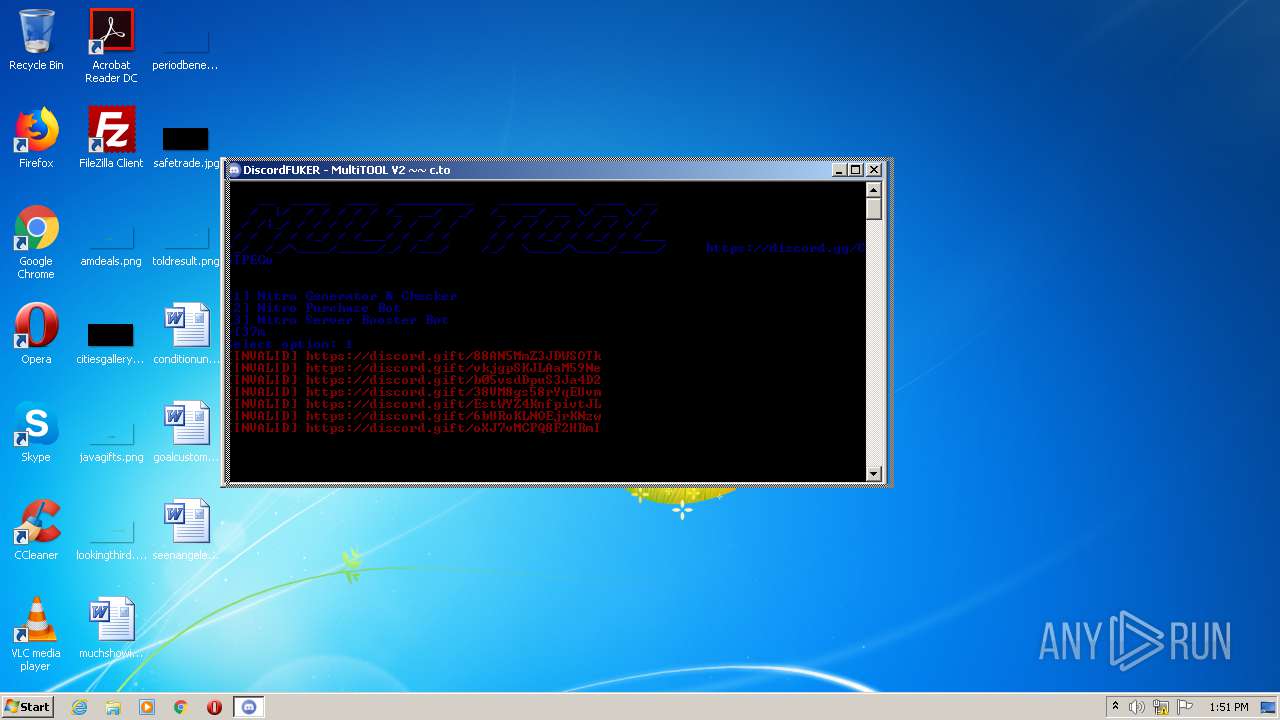
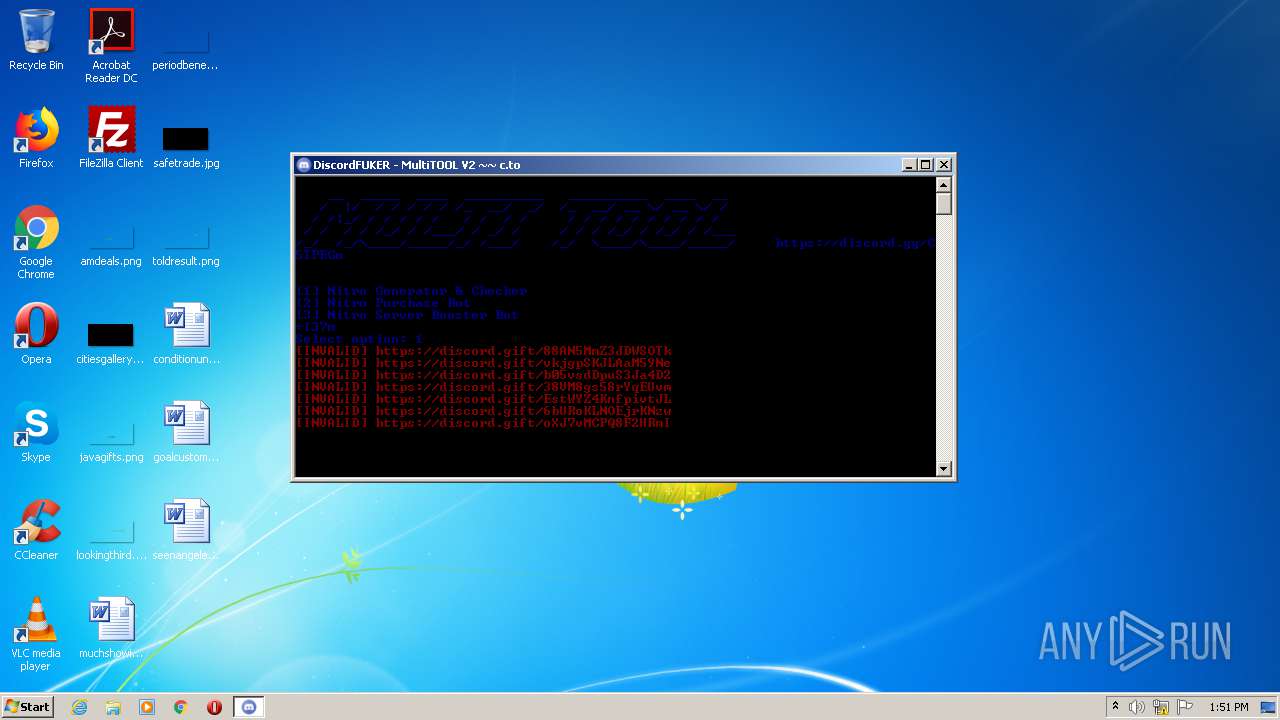
Actions looks like stealing of personal data
- MultiTool.exe (PID: 3012)
SUSPICIOUS
Executable content was dropped or overwritten
- MultiTool.exe (PID: 3020)
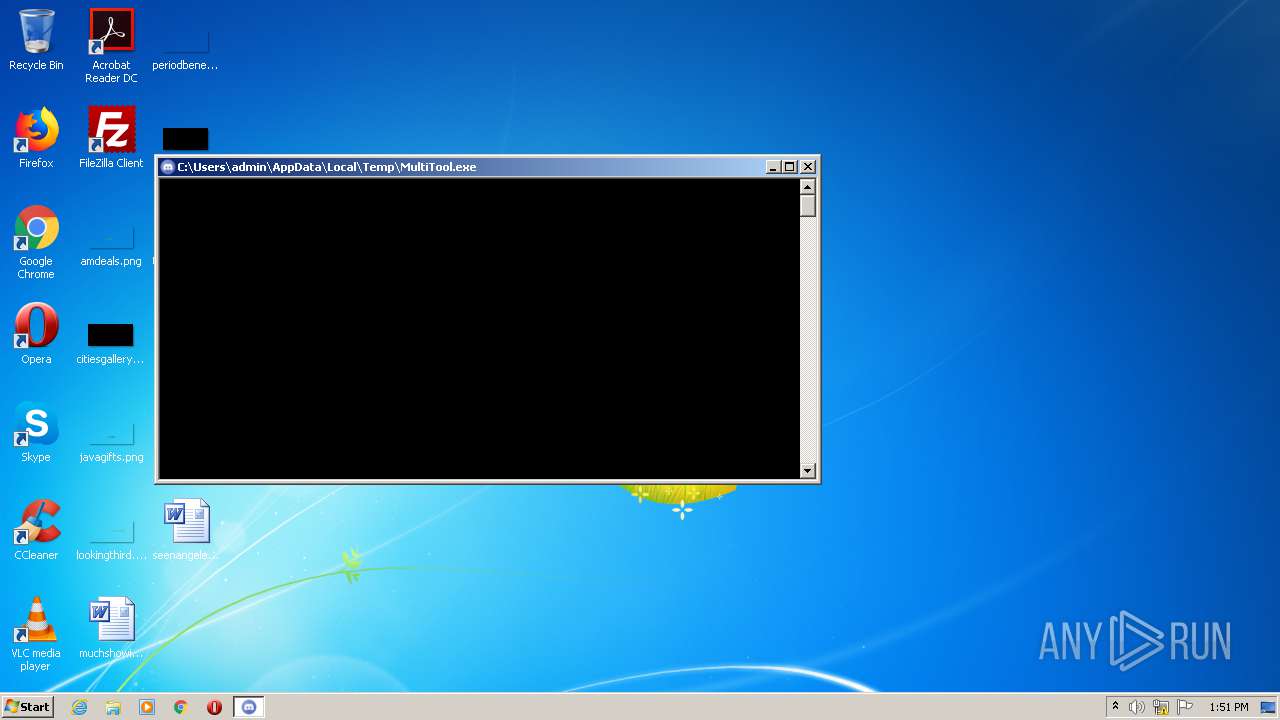
Starts CMD.EXE for commands execution
- MultiTool.exe (PID: 3012)
Loads Python modules
- MultiTool.exe (PID: 3012)
Application launched itself
- MultiTool.exe (PID: 3020)
INFO
Dropped object may contain Bitcoin addresses
- MultiTool.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:05 13:16:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128512 |
| InitializedDataSize: | 172544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a6a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 05-Jan-2020 12:16:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jan-2020 12:16:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F4D4 | 0x0001F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6643 |
.rdata | 0x00021000 | 0x0000B19E | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.11204 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93811 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86299 |
.rsrc | 0x0003D000 | 0x0001CBB8 | 0x0001CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94537 |
.reloc | 0x0005A000 | 0x000017D4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65456 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.82914 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.3006 | 1035 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.09866 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.82294 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.45308 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.59924 | 93040 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
WS2_32.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3012 | "C:\Users\admin\AppData\Local\Temp\MultiTool.exe" | C:\Users\admin\AppData\Local\Temp\MultiTool.exe | MultiTool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\MultiTool.exe" | C:\Users\admin\AppData\Local\Temp\MultiTool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3976 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | MultiTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
108
Read events
108
Write events
0
Delete events
0
Modification events
Executable files
27
Suspicious files
6
Text files
920
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\Main.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_lzma.pyd | executable | |
MD5:38C434AFB2A885A95999903977DC3624 | SHA256:BFE6E288B2D93905F5CBB6D74E9C0FC37145B9225DB6D1F00C0F69EB45AFD051 | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_multiprocessing.pyd | executable | |
MD5:7D3306BA4645463CB0D4C34C77B2BDF2 | SHA256:3A183E0F6A31507C3B0ACBCAE5D6C3D843C590BB370DE5382E2DF9CFC2CB156E | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_sqlite3.pyd | executable | |
MD5:49848CA2C6ED629A5FA24ABAB96E5EC9 | SHA256:C222806D471A71D0FD804162E5DA3DC607973367819453C20119A5742EFF5113 | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_tkinter.pyd | executable | |
MD5:B6D0111BF1ED6122D4D03A332B13C8D6 | SHA256:0D1B0F2180B095CF742F4629026C2BF14E5D788755DDF9E9EBDC5574082318D9 | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_testcapi.pyd | executable | |
MD5:58B6D54036BB03B606A11EA1A4FE376B | SHA256:03F67F5AE47EB4AF1C6DE599AFA9640E6B77BEB0A71CFF79223D07BA63E94D2F | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\VCRUNTIME140.dll | executable | |
MD5:2EBF45DA71BD8EF910A7ECE7E4647173 | SHA256:CF39E1E81F57F42F4D60ABC1D30ECF7D773E576157AA88BBC1D672BF5AD9BB8B | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_overlapped.pyd | executable | |
MD5:09716BCE87ED2BF7E5A1F19952305E5C | SHA256:F4A27F4E242D788FCB1F5DD873608C72CDFC0799358364420ECEA1A7E52CC2B0 | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_hashlib.pyd | executable | |
MD5:F9799B167C3E4FFEE4629B4A4E2606F2 | SHA256:02DD924D4EBFBB8B5B0B66B6E6BB2388FCCDAD64D0493854A5443018AD5D1543 | |||
| 3020 | MultiTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI30202\_socket.pyd | executable | |
MD5:6B59705D8AC80437DD81260443912532 | SHA256:62ED631A6AD09E96B4B6F4566C2AFC710B3493795EDEE4CC14A9C9DE88230648 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
49
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
3012 | MultiTool.exe | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
3012 | MultiTool.exe | 162.159.137.232:443 | discord.com | Cloudflare Inc | — | malicious |
3012 | MultiTool.exe | 174.129.214.20:443 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
discord.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3012 | MultiTool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3012 | MultiTool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report