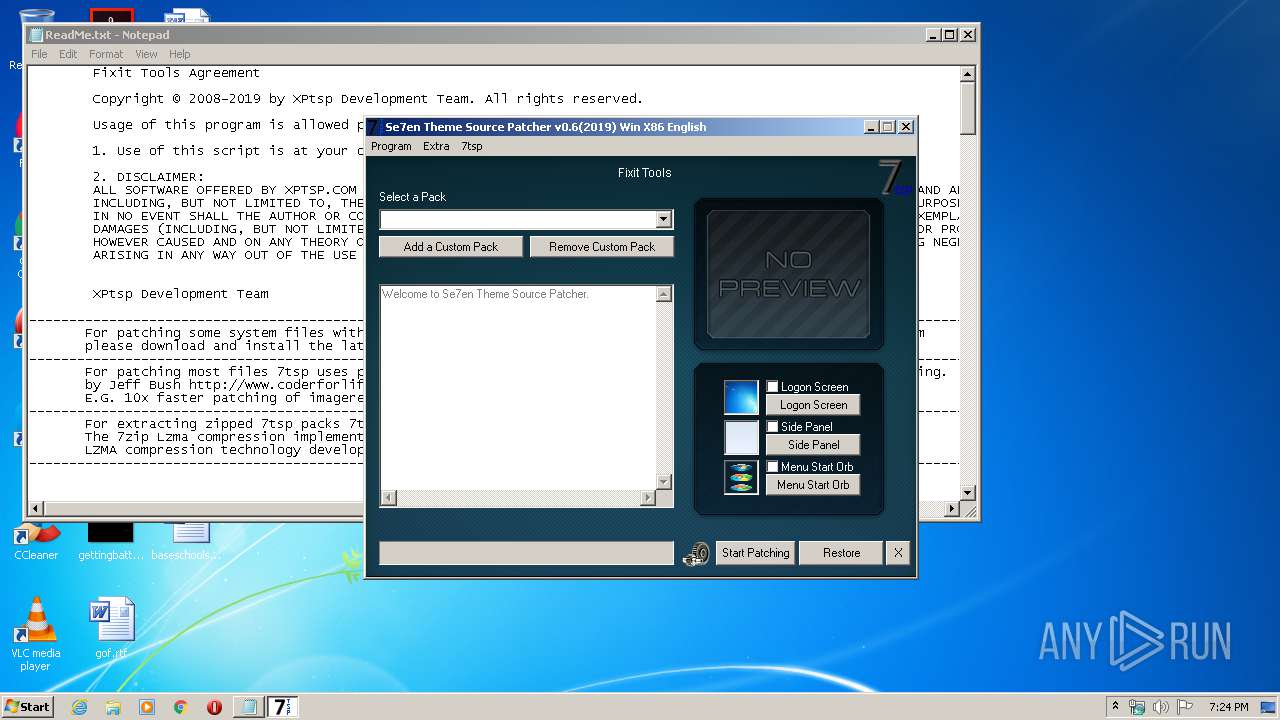
| File name: | 7tsp GUI v0.6(2019).exe |
| Full analysis: | https://app.any.run/tasks/4af7eeb9-4797-4569-b44b-b7429c522ddc |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2020, 19:23:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0FC4B5592E3B58F1FC87D5EF81DE981A |
| SHA1: | F9408F54BE6540CCAF7CE0B9DBB80B81AFD83CA8 |
| SHA256: | 090C9E214599150F6ED241171BB2107E04D13BFA5E74927B094B139EAE280B65 |
| SSDEEP: | 98304:+KeDBgMNTwmVKhf79kBoHKVa8emhb8C3W8T4aBFvP7Y5Iks:+KurwJxncFz3BX7Y5k |
MALICIOUS
Application was dropped or rewritten from another process
- ResHacker.exe (PID: 3992)
- ResHacker.exe (PID: 2988)
- ResHacker.exe (PID: 3272)
- ResHacker.exe (PID: 3044)
SUSPICIOUS
Executable content was dropped or overwritten
- 7tsp GUI v0.6(2019).exe (PID: 2288)
Creates files in the program directory
- 7tsp GUI v0.6(2019).exe (PID: 2288)
- ResHacker.exe (PID: 2988)
- ResHacker.exe (PID: 3992)
- ResHacker.exe (PID: 3044)
Starts CMD.EXE for commands execution
- 7tsp GUI v0.6(2019).exe (PID: 2288)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2668)
INFO
Application launched itself
- chrome.exe (PID: 2668)
Manual execution by user
- chrome.exe (PID: 2668)
Reads the hosts file
- chrome.exe (PID: 2668)
- chrome.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:03:07 17:08:39+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 270336 |
| InitializedDataSize: | 151552 |
| UninitializedDataSize: | 602112 |
| EntryPoint: | 0xd5bc0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.6.2.0 |
| ProductVersionNumber: | 3.3.6.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 0.6.2.0 |
| Comments: | Se7en Theme Source Patcher v0.6.2019 Patches your Windows Se7en System Files with new Icons and Bitmaps |
| FileDescription: | Se7en Theme Source Patcher |
| LegalCopyright: | XPtsp Team -Program Written By Fixit- |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Mar-2010 16:08:39 |
| Detected languages: |
|
| FileVersion: | 0.6.2.0 |
| Comments: | Se7en Theme Source Patcher v0.6.2019 Patches your Windows Se7en System Files with new Icons and Bitmaps |
| FileDescription: | Se7en Theme Source Patcher |
| LegalCopyright: | XPtsp Team -Program Written By Fixit- |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Mar-2010 16:08:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00093000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00094000 | 0x00042000 | 0x00041E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9298 |
.rsrc | 0x000D6000 | 0x00025000 | 0x00024400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36446 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09206 | 789 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.26337 | 5672 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 3.51836 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 3.82848 | 2216 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 7.7836 | 1328 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 7.81318 | 1680 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 7.75969 | 1082 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 7.74685 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
82
Monitored processes
39
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7219156997438002386 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1597722710357339520 --mojo-platform-channel-handle=3492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4286871912679887859 --mojo-platform-channel-handle=3308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
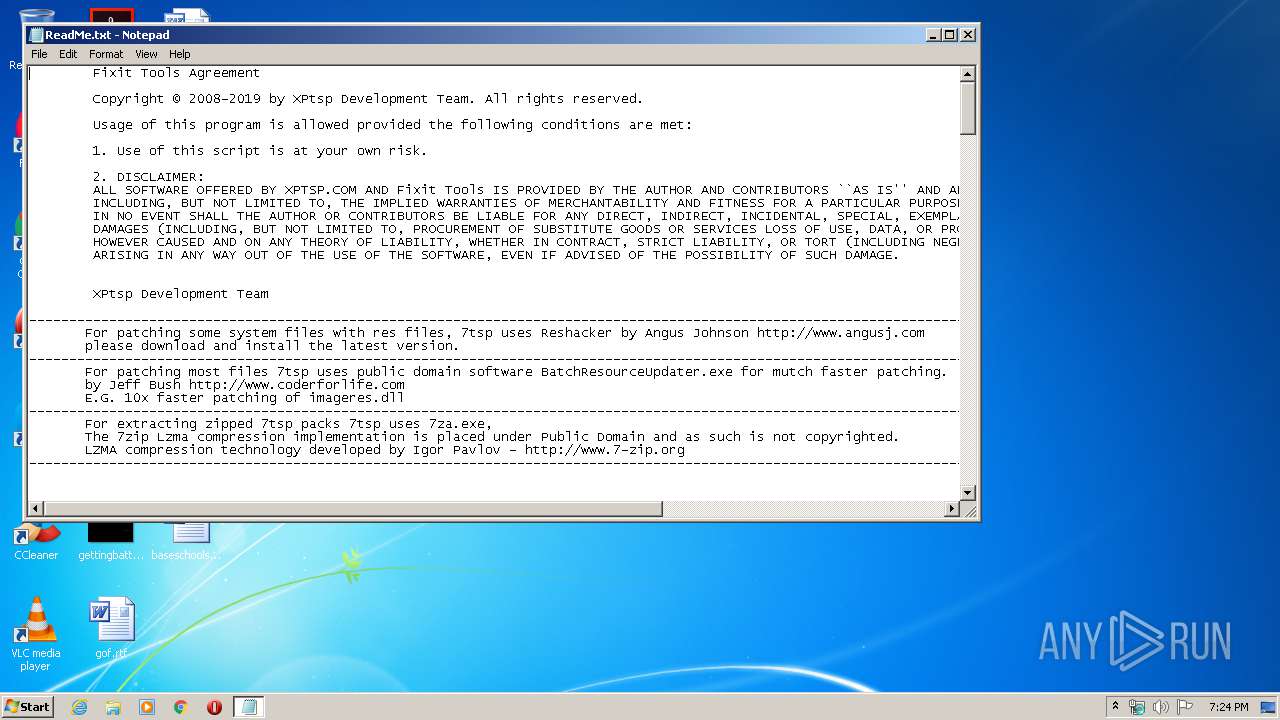
| 1744 | notepad.exe C:\ProgramData\local\temp\ReadMe.txt | C:\Windows\system32\notepad.exe | — | 7tsp GUI v0.6(2019).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12526660102426774855 --mojo-platform-channel-handle=3396 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1866118957630458756 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12933750245470994155 --mojo-platform-channel-handle=4420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\7tsp GUI v0.6(2019).exe" | C:\Users\admin\AppData\Local\Temp\7tsp GUI v0.6(2019).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Se7en Theme Source Patcher Exit code: 0 Version: 0.6.2.0 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14464707320634387484 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5028188841369763850 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
373
Read events
300
Write events
68
Delete events
5
Modification events
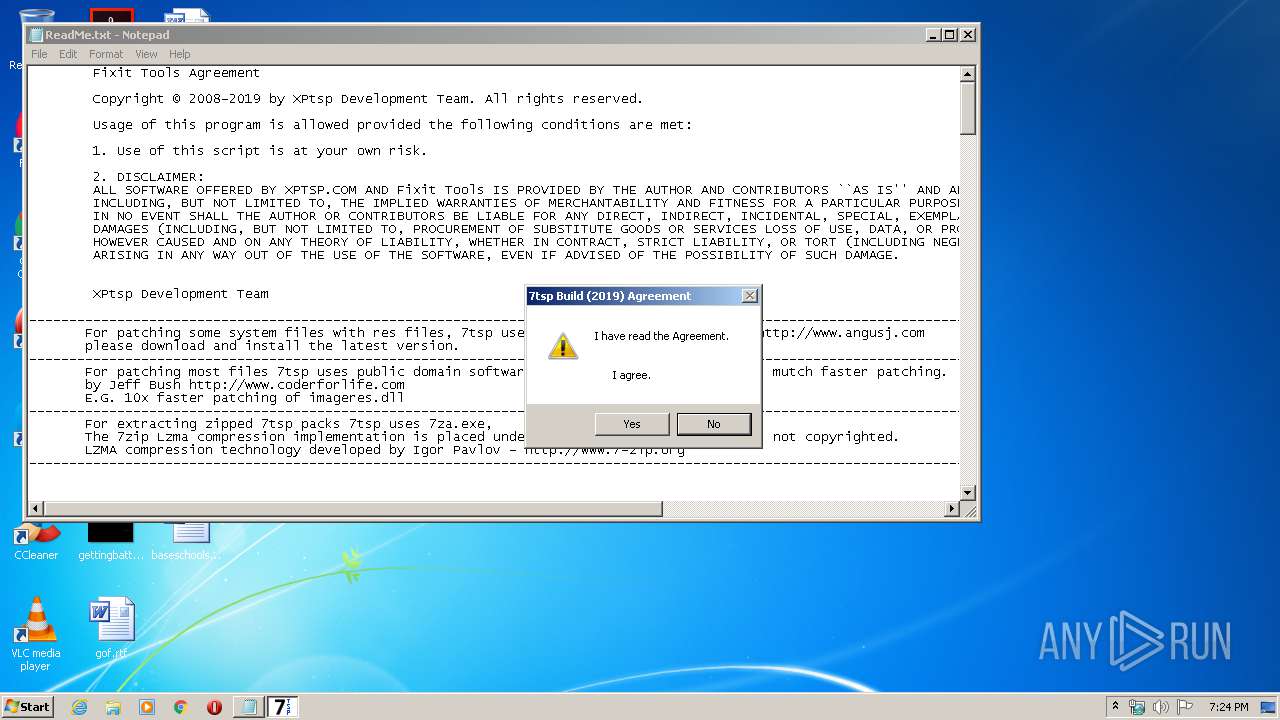
| (PID) Process: | (2288) 7tsp GUI v0.6(2019).exe | Key: | HKEY_CURRENT_USER\Software\Fixit Tools\7tsp |
| Operation: | write | Name: | Agreement |
Value: (2019)Yes | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2668-13229637864589125 |
Value: 259 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
4
Suspicious files
20
Text files
261
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut7160.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut718F.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8324.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8335.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8336.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8337.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8367.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8378.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut8379.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | 7tsp GUI v0.6(2019).exe | C:\Users\admin\AppData\Local\Temp\aut83A8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2532 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2532 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
2532 | chrome.exe | GET | 200 | 173.194.150.249:80 | http://r3---sn-2gb7sn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=45.86.200.17&mm=28&mn=sn-2gb7sn7z&ms=nvh&mt=1585164195&mv=m&mvi=2&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2532 | chrome.exe | GET | 200 | 173.194.150.252:80 | http://r6---sn-2gb7sn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=45.86.200.17&mm=28&mn=sn-2gb7sn7z&ms=nvh&mt=1585163906&mv=u&mvi=5&pl=27&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2532 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2532 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.206:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.23.174:80 | clients2.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 173.194.150.252:80 | r6---sn-2gb7sn7z.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-2gb7sn7z.gvt1.com |
| whitelisted |