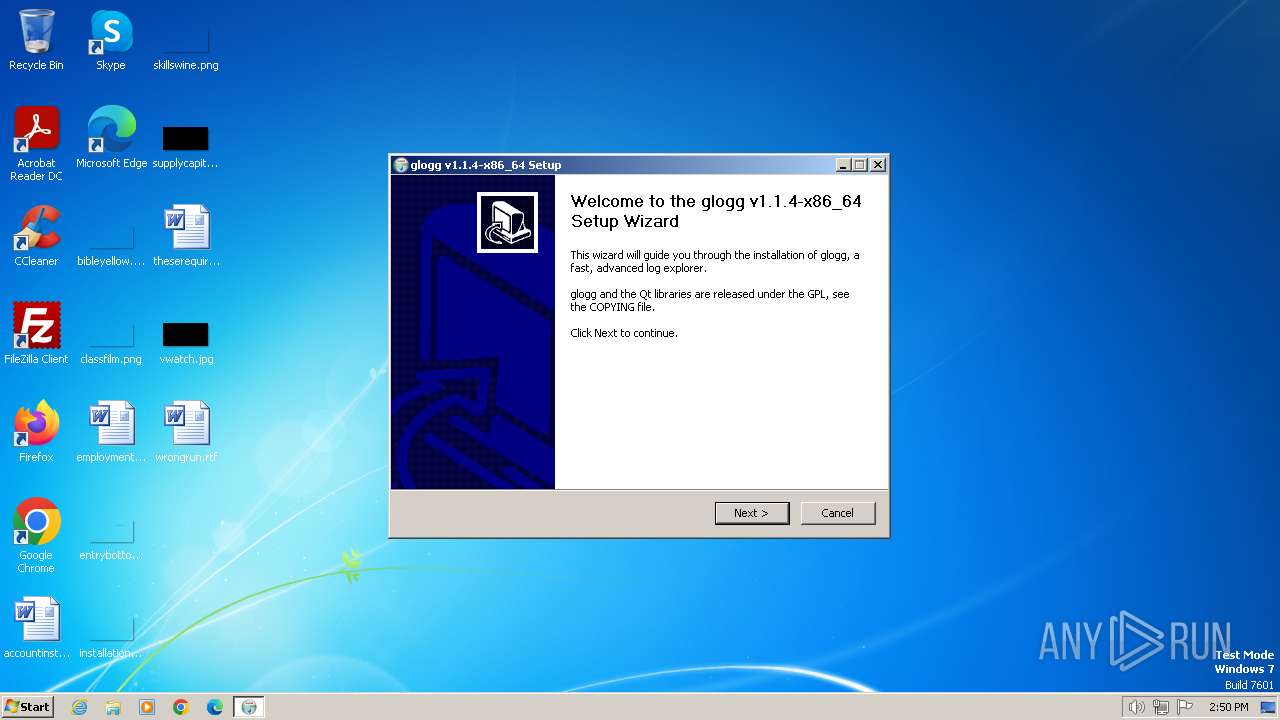
| File name: | glogg-latest-x86_64-setup (1).exe |
| Full analysis: | https://app.any.run/tasks/008b1d64-2df4-470e-9170-7fe5ede80b02 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 14:50:30 |
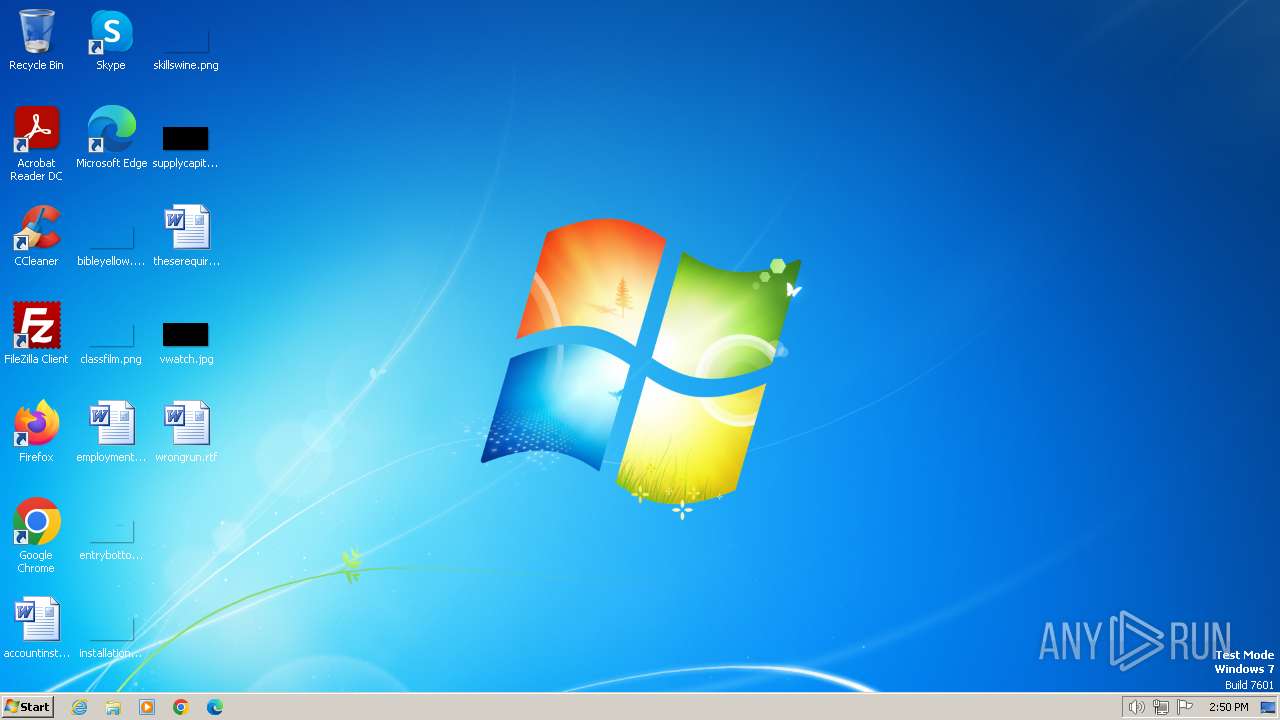
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1F71C2DA992A77ADC264F6173F2005D6 |
| SHA1: | B943E14C5BEA9EC4B7E527FB2FCC0D4D02B82697 |
| SHA256: | 08FE13B713327BEF93298B6D11717A93BBAA9D49165995BE93F4A3282E76B22F |
| SSDEEP: | 98304:YT1Y9speoWZZdofSuCcD2WNu808cMW2WqZ6RJrB0yTLarhUP04lSVSox5mWhVVcB:ZN68t5 |
MALICIOUS
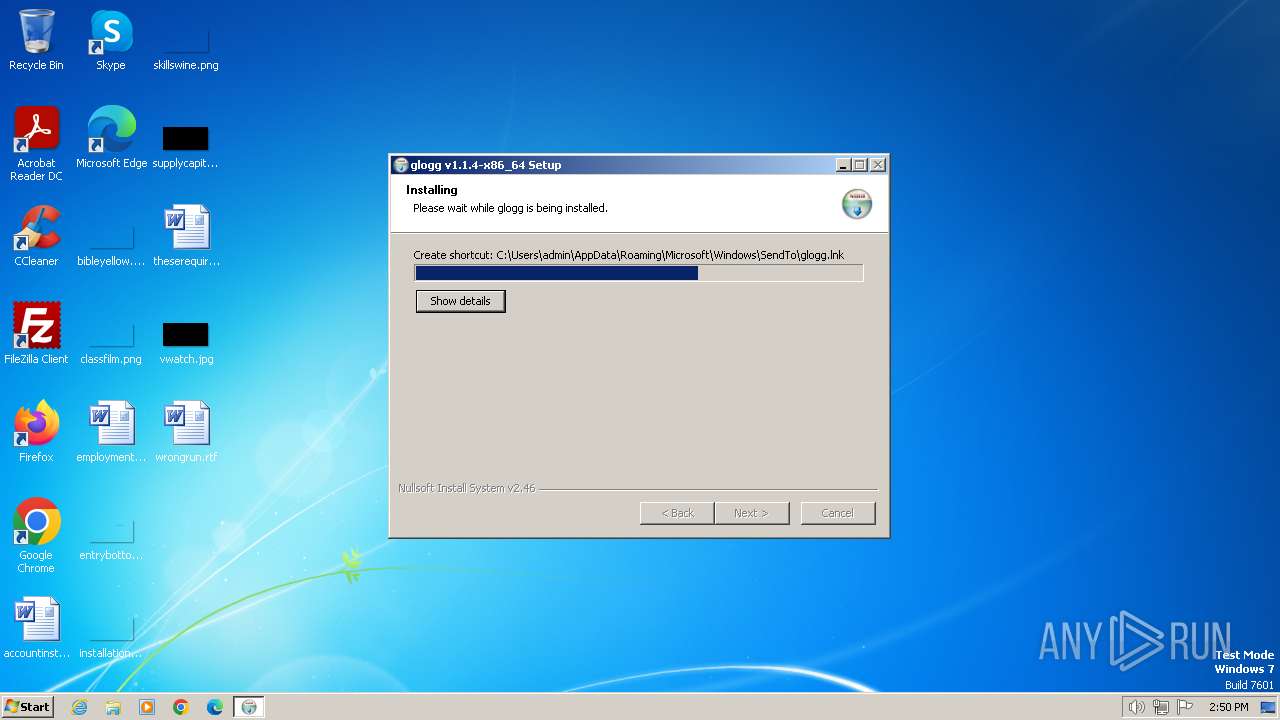
Drops the executable file immediately after the start
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
The process creates files with name similar to system file names
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Executable content was dropped or overwritten
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
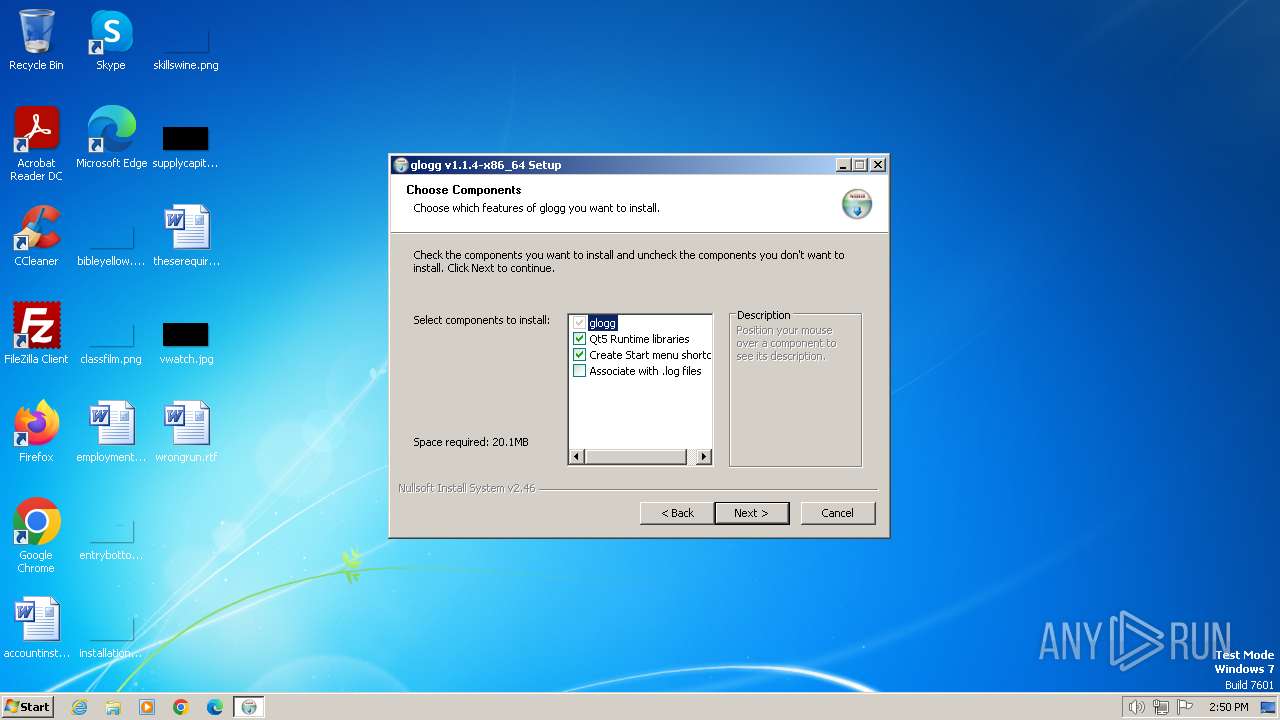
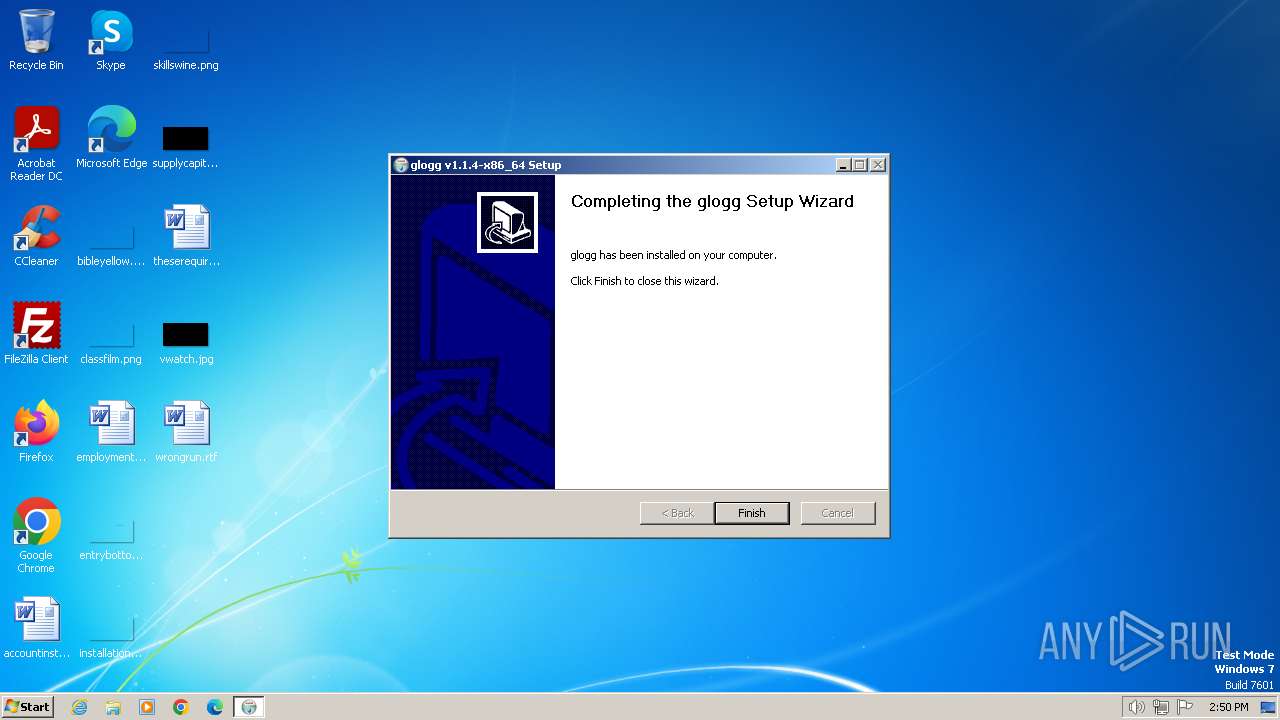
Creates a software uninstall entry
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
INFO
Reads the computer name
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Checks supported languages
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Creates files in the program directory
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Create files in a temporary directory
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Creates files or folders in the user directory
- glogg-latest-x86_64-setup (1).exe (PID: 2036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\Users\admin\AppData\Local\Temp\glogg-latest-x86_64-setup (1).exe" | C:\Users\admin\AppData\Local\Temp\glogg-latest-x86_64-setup (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
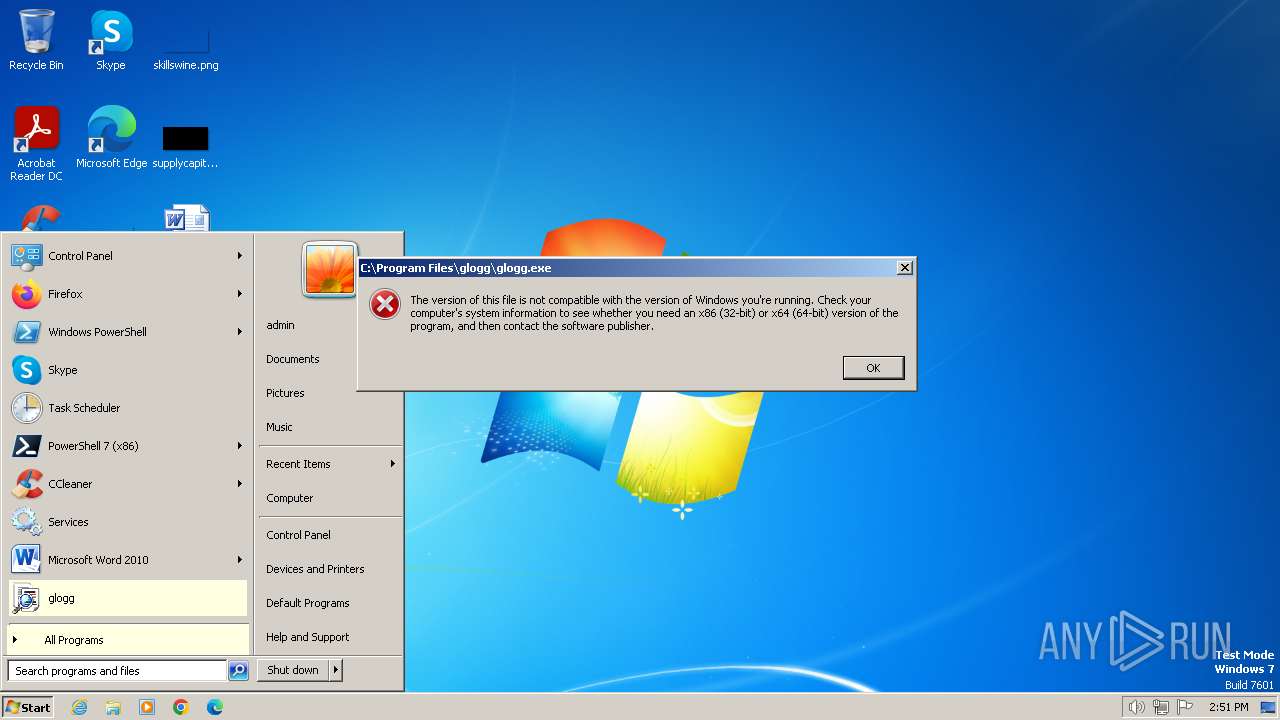
| 3864 | "C:\Users\admin\AppData\Local\Temp\glogg-latest-x86_64-setup (1).exe" | C:\Users\admin\AppData\Local\Temp\glogg-latest-x86_64-setup (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 406
Read events
2 399
Write events
7
Delete events
0
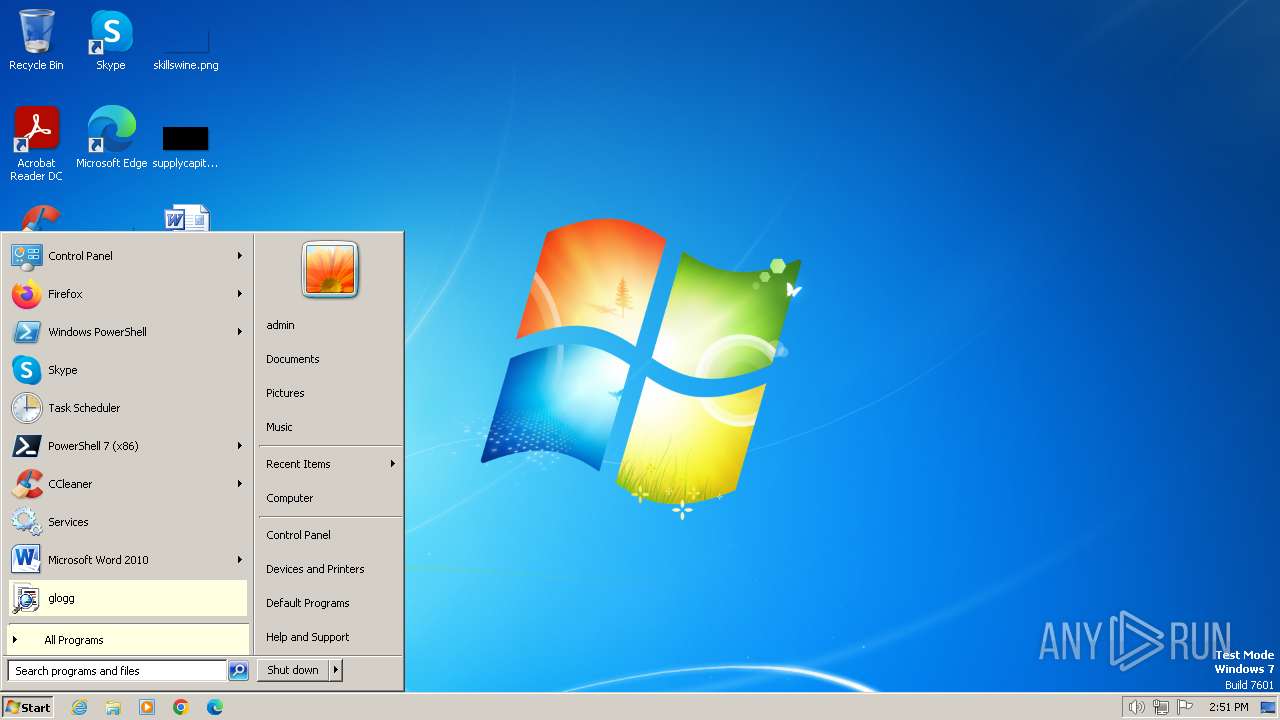
Modification events
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\glogg.exe\shell\open |
| Operation: | write | Name: | FriendlyAppName |
Value: glogg | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\glogg\Uninstall.exe" | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\glogg | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | DisplayName |
Value: glogg | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | DisplayVersion |
Value: v1.1.4-x86_64 | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2036) glogg-latest-x86_64-setup (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\glogg |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
10
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Users\admin\AppData\Local\Temp\nsjF1A4.tmp | — | |
MD5:— | SHA256:— | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\glogg.exe | executable | |
MD5:3CD8305B89A91971CD92409ED548C453 | SHA256:E309EFDD5828B158CE0626C055C7DC7DB7A62CA0D489BF0D63A63D2F0C2C3D25 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\Qt5Network.dll | executable | |
MD5:D309014C0023A9473F633EF0C6F2AC81 | SHA256:63307C6D137EF531CA3A940662479E6F0B26C334A3680EB6E7459C81BDB38E22 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\COPYING | text | |
MD5:D32239BCB673463AB874E80D47FAE504 | SHA256:8CEB4B9EE5ADEDDE47B31E975C1D90C73AD27B6B165A1DCD80C7C545EB65B903 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\README.md | text | |
MD5:82AC88A0450517C1A7626FE6C84E4E08 | SHA256:73294D0ECFE6979F13D8B51E491ADCE8C35E76AFC3C0D9378E6702217CB9C62A | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Users\admin\AppData\Local\Temp\nszF1B5.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\Uninstall.exe | executable | |
MD5:DDA11E8374465B795C6A0C4640FC6A9F | SHA256:C818869E4280D7504A3FDC12699F60DEF60ECA59469A9CC14D172B5F54F176A0 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\Qt5Gui.dll | executable | |
MD5:FE78193C8E70E237228A743644F48CC2 | SHA256:76ED1D350C039B75C4A7960368CD49FBD1400B1CC4CBF30BACC35ABE3EA30F70 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\SendTo\glogg.lnk | binary | |
MD5:75832A3E78658526170DC48A81EEBD08 | SHA256:3BB8DB7751AB4A93C2A6F0BAB9DE31A98E61521B4B6906D527FEFBBB43DFC029 | |||
| 2036 | glogg-latest-x86_64-setup (1).exe | C:\Program Files\glogg\libwinpthread-1.dll | executable | |
MD5:99A9EA05E3C12000701D2F04803C4DE1 | SHA256:285D58A93A64F451B2A622D42ABC876319E14631F288C65B5FA987D3CF62D15A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |