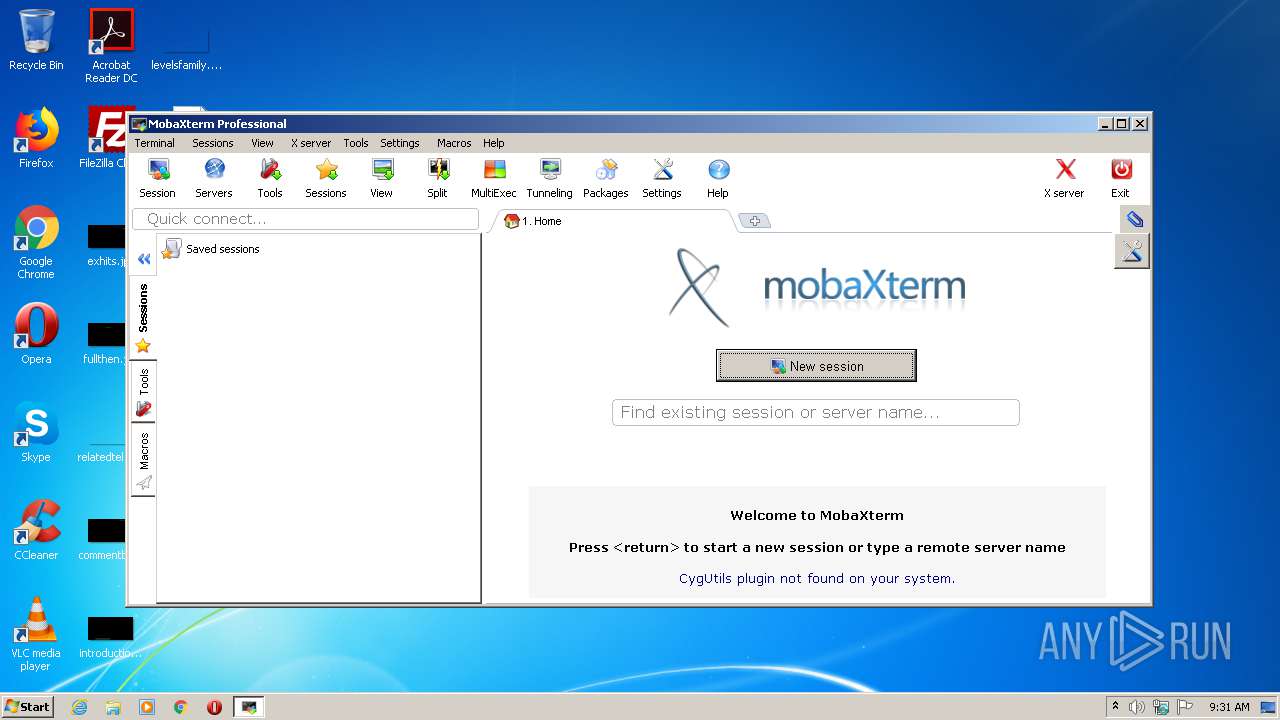
| File name: | MobaXterm.exe |
| Full analysis: | https://app.any.run/tasks/7e30c3eb-96d1-4de5-b107-4ea844ddb843 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2021, 08:30:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2A117DAFB531CD68612D887741E85D30 |
| SHA1: | 7C5EF9C94002AA73455A64C619BA77B3F12A9D5D |
| SHA256: | 08FBF4F5127C08CF556DCE2376FED1B1BA8BC233B5E66F4D4912AB9C4A826B41 |
| SSDEEP: | 196608:Su0938okbztgW4vhFOiTxaDi0Wj4qAXr4N+jA3DnDA5GKQnjMjzjVqbFj4ZXj:Qq5gciFadE4qX+83DnDEnQIjFqbB4Zz |
MALICIOUS
Loads dropped or rewritten executable
- XWin_MobaX.exe (PID: 784)
- xkbcomp_w32.exe (PID: 3160)
Application was dropped or rewritten from another process
- xkbcomp_w32.exe (PID: 3160)
- XWin_MobaX.exe (PID: 784)
SUSPICIOUS
Drops a file with too old compile date
- MobaXterm.exe (PID: 3832)
Executable content was dropped or overwritten
- MobaXterm.exe (PID: 3832)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| Comments: | http://mobaxterm.mobatek.net |
|---|---|
| ProductVersion: | 9.1 |
| ProductName: | MobaXterm |
| OriginalFileName: | MobaXterm |
| LegalTrademarks: | Mobatek - http://mobaxterm.mobatek.net |
| LegalCopyright: | Mobatek - http://mobaxterm.mobatek.net |
| InternalName: | MobaXterm |
| FileVersion: | 9.1.0.0 |
| FileDescription: | MobaXterm |
| CompanyName: | Mobatek |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 9.1.0.0 |
| FileVersionNumber: | 9.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1786a00 |
| UninitializedDataSize: | 12886016 |
| InitializedDataSize: | 6639616 |
| CodeSize: | 5140480 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Mobatek |
| FileDescription: | MobaXterm |
| FileVersion: | 9.1.0.0 |
| InternalName: | MobaXterm |
| LegalCopyright: | Mobatek - http://mobaxterm.mobatek.net |
| LegalTrademarks: | Mobatek - http://mobaxterm.mobatek.net |
| OriginalFilename: | MobaXterm |
| ProductName: | MobaXterm |
| ProductVersion: | 9.1 |
| Comments: | http://mobaxterm.mobatek.net |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00C4A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00C4B000 | 0x004E7000 | 0x004E7000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90062 |
.rsrc | 0x01132000 | 0x00655400 | 0x00654D58 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99707 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02853 | 1782 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.71206 | 9640 | UNKNOWN | French - France | RT_ICON |
3 | 5.82736 | 4264 | UNKNOWN | French - France | RT_ICON |
4 | 5.95255 | 2440 | UNKNOWN | French - France | RT_ICON |
5 | 5.85997 | 1128 | UNKNOWN | French - France | RT_ICON |
6 | 3.16869 | 4264 | UNKNOWN | French - France | RT_ICON |
7 | 4.32468 | 1128 | UNKNOWN | French - France | RT_ICON |
8 | 7.85153 | 4268 | UNKNOWN | French - France | RT_CURSOR |
9 | 7.86972 | 4268 | UNKNOWN | French - France | RT_CURSOR |
10 | 7.85541 | 4268 | UNKNOWN | French - France | RT_CURSOR |
Imports
IPHLPAPI.DLL |
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
crypt32.dll |
gdi32.dll |
gdiplus.dll |
imm32.dll |
netapi32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Users\admin\AppData\Local\Temp\Mxt91\bin\XWin_MobaX.exe" -silent-dup-error -notrayicon -nolisten inet6 -hostintitle +bs -clipboard -nowgl -multiwindow -noreset :0 | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\XWin_MobaX.exe | MobaXterm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\Mxt91\bin\xkbcomp_w32.exe" -w 1 "-RC:\Users\admin\AppData\Local\Temp\Mxt91\usr\share\X11\xkb" -xkm "C:\Users\admin\AppData\Local\Temp\Mxt91\var\log\xwin\xkb_a01568" -em1 "The XKEYBOARD keymap compiler (xkbcomp) reports:" -emp "> " -eml "Errors from xkbcomp are not fatal to the X server" "C:\Users\admin\AppData\Local\Temp\Mxt91\var\log\xwin\server-0.xkm" | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\xkbcomp_w32.exe | — | XWin_MobaX.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\AppData\Local\Temp\MobaXterm.exe" | C:\Users\admin\AppData\Local\Temp\MobaXterm.exe | explorer.exe | ||||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm Exit code: 0 Version: 9.1.0.0 Modules
| |||||||||||||||
Total events
366
Read events
362
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3832) MobaXterm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3832) MobaXterm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
28
Suspicious files
43
Text files
477
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\registry | binary | |
MD5:12DCC755A41FFE9983DFC47E545B132D | SHA256:8D7D8B8FDEC94104B0EE6A90665106B02A8ECC705EAF33DAA91FC83AEDD7CF18 | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\cygdrive | binary | |
MD5:2064A8DFFC77A2130D9F64018604769E | SHA256:D7F3656E9078257BD9B7558EE2D01E94D3C30B81F035FA3417B745139C9ECCB8 | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\media | binary | |
MD5:2064A8DFFC77A2130D9F64018604769E | SHA256:D7F3656E9078257BD9B7558EE2D01E94D3C30B81F035FA3417B745139C9ECCB8 | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\mnt | binary | |
MD5:2064A8DFFC77A2130D9F64018604769E | SHA256:D7F3656E9078257BD9B7558EE2D01E94D3C30B81F035FA3417B745139C9ECCB8 | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\etc\baseprofile | text | |
MD5:89842E66D91DCE9527302A5E39CB9224 | SHA256:910E11CFBB1E38B8962935426E41F9B25E935866E1FD1FA8B52B062EF93D0335 | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\nimesweeper.exe | text | |
MD5:EDF814BD8DE2A14A46F4C979E3A1902C | SHA256:50F017656B19D5A1928DCA01002D6D606021D392D84F2285BDD59CFD3100688D | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\sudoku.exe | text | |
MD5:EDF814BD8DE2A14A46F4C979E3A1902C | SHA256:50F017656B19D5A1928DCA01002D6D606021D392D84F2285BDD59CFD3100688D | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\ninvaders | text | |
MD5:EDF814BD8DE2A14A46F4C979E3A1902C | SHA256:50F017656B19D5A1928DCA01002D6D606021D392D84F2285BDD59CFD3100688D | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\greed | text | |
MD5:EDF814BD8DE2A14A46F4C979E3A1902C | SHA256:50F017656B19D5A1928DCA01002D6D606021D392D84F2285BDD59CFD3100688D | |||
| 3832 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt91\bin\ninvaders.exe | text | |
MD5:EDF814BD8DE2A14A46F4C979E3A1902C | SHA256:50F017656B19D5A1928DCA01002D6D606021D392D84F2285BDD59CFD3100688D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report