| File name: | paradox.exe |
| Full analysis: | https://app.any.run/tasks/975775c7-4b13-4b86-9e76-f8e6155007b5 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2019, 01:20:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 56A38D9FFF1022EA9D93346B99B689DA |
| SHA1: | BCEA4B089DAE9B001F6B919A03AF082942B324E2 |
| SHA256: | 08E605C9B883077FAF1EBFEADCA8ACE4980031DB670AA802F15D7ED056DA01EA |
| SSDEEP: | 196608:9TLtfNqAor54J5qhFYU0/Yyj6BUdi+MI+9OZibq:VpcfuWhFYvVEZ+M59S0 |
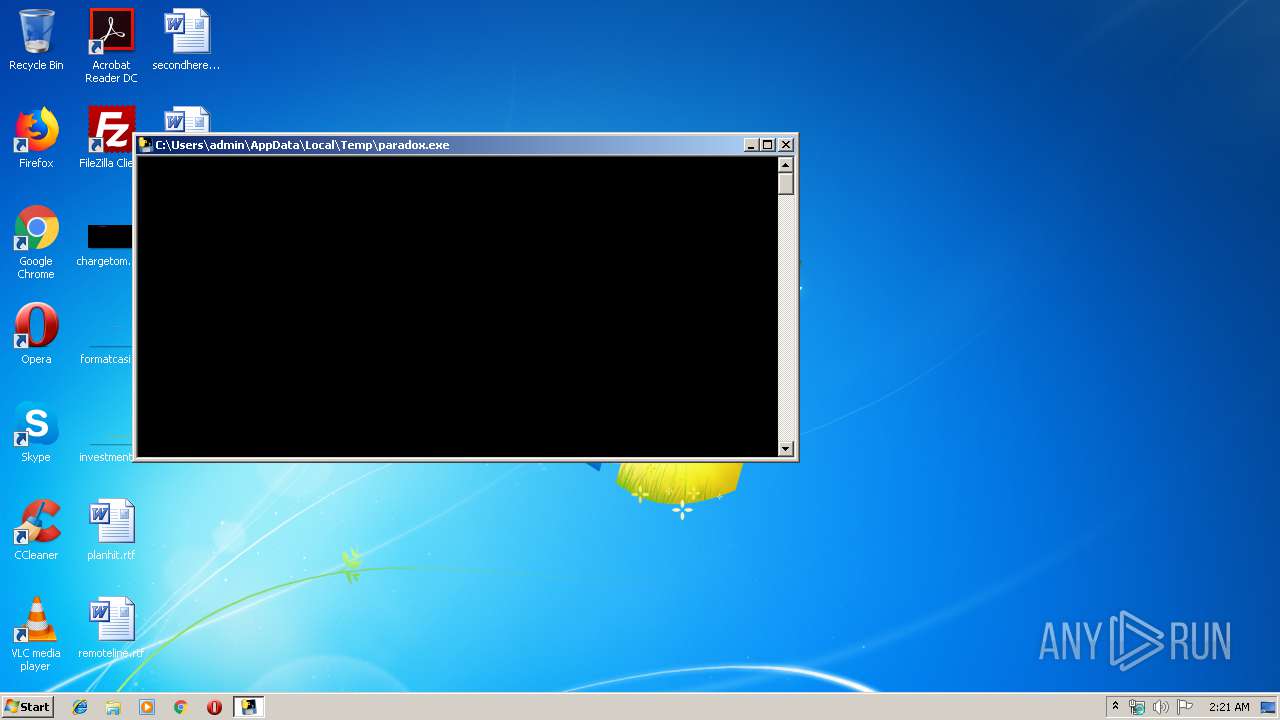
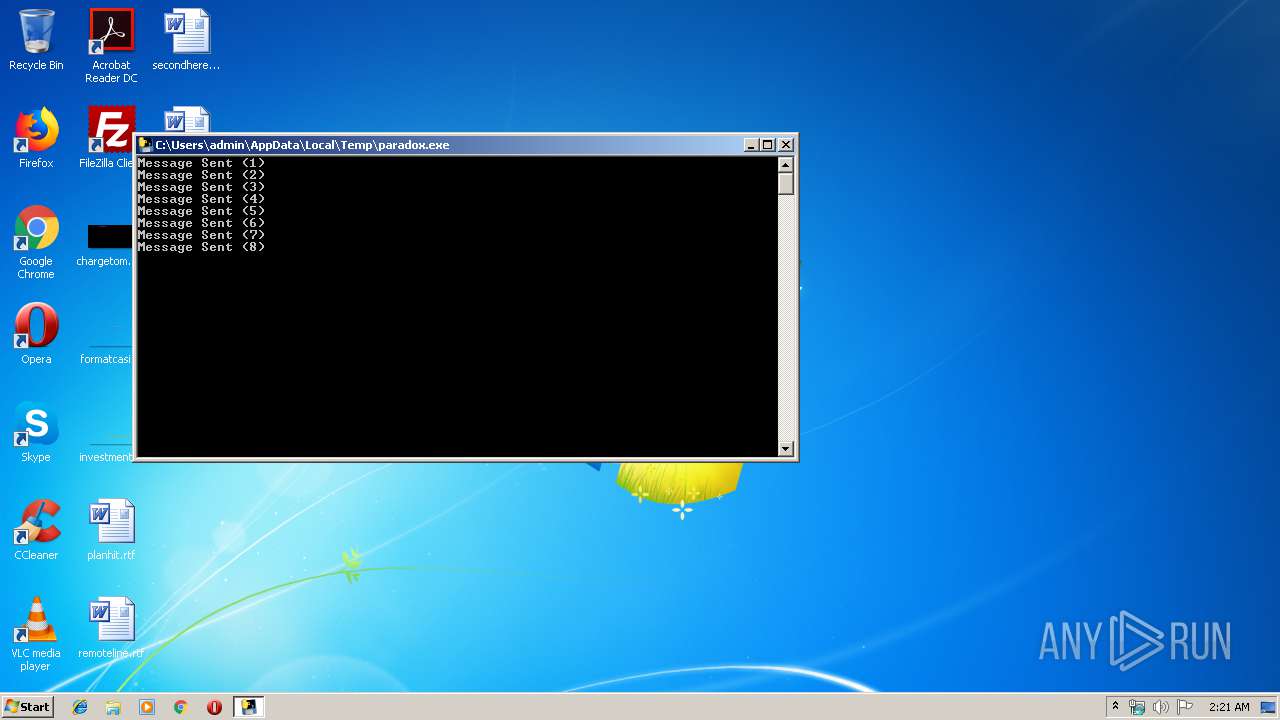
MALICIOUS
Loads dropped or rewritten executable
- paradox.exe (PID: 2296)
SUSPICIOUS
Loads Python modules
- paradox.exe (PID: 2296)
Executable content was dropped or overwritten
- paradox.exe (PID: 3224)
Starts CMD.EXE for commands execution
- paradox.exe (PID: 2296)
INFO
Dropped object may contain Bitcoin addresses
- paradox.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2296 | "C:\Users\admin\AppData\Local\Temp\paradox.exe" | C:\Users\admin\AppData\Local\Temp\paradox.exe | paradox.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3168 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | paradox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\Temp\paradox.exe" | C:\Users\admin\AppData\Local\Temp\paradox.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3652 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | paradox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4088 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | paradox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
65
Read events
65
Write events
0
Delete events
0
Modification events
Executable files
18
Suspicious files
1
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\paradox.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\base_library.zip | compressed | |
MD5:— | SHA256:— | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\_bz2.pyd | executable | |
MD5:2DD25AC2510C5640169D89EE220E748E | SHA256:F5086031019C5E03AFCFEE227C4D30E82B68C24F5A5871640C3E8682852D9A54 | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\pyexpat.pyd | executable | |
MD5:FCB814F2CD464625C3768041C771BC1F | SHA256:312016B81FA555E222B550BECE978E7612B64D079045CBB5597D84F77099660A | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\cryptography\hazmat\bindings\_openssl.cp37-win32.pyd | executable | |
MD5:6060B0D2596BFBEC7C2E3C16D5237686 | SHA256:0B192A88494F19C5D099C2F7937534830DDDDE40745C30A0B1A0F24A96A2AA04 | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\_queue.pyd | executable | |
MD5:4F38EB31E85412B5BB3CC955F7A83CFB | SHA256:326F00F00DABF86B33325B8F6344A141AEFB2A56BA5C173D2EFE175EFA72058B | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\libssl-1_1.dll | executable | |
MD5:A11C90DEFA3969B20B8730450447636C | SHA256:5B24D33EF69546A929B021738018C55EE6CEA62B3DDD8D69A78DCAD4DC5C6255 | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\_ssl.pyd | executable | |
MD5:6E8D415D50D8292DBFB479447AC09C27 | SHA256:5B616AF730AA15A75558AFA50E725C7D4D4E5B22BBFFD348DF2239425CFEADD0 | |||
| 3224 | paradox.exe | C:\Users\admin\AppData\Local\Temp\_MEI32242\_decimal.pyd | executable | |
MD5:2A22A7C58067BED977EE3656D1818F69 | SHA256:6FBECEB84331902154A5F81573228149AE9FCB3E6A814ABEA99589DE09FCC433 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
20
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2296 | paradox.exe | 35.187.79.8:443 | api.eu.mailjet.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.eu.mailjet.com |
| unknown |