| File name: | NMF64.exe |
| Full analysis: | https://app.any.run/tasks/037593b9-6fe6-4a60-bc0e-85fce6c18709 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 16:20:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | CEB2135168094FF656B49A500AA4ED7B |
| SHA1: | F514801D9D8FEA493E8C71FC74D57D3B7614D0DE |
| SHA256: | 08E30FA97DA7F31BC50E9007581A392CDFFE3C753610786162DC5C01E96B80E4 |
| SSDEEP: | 6144:IdUF5b20qHgpUibm8xXz2Sty4ovQV/iFUlQD2/bw:ITgpRxXz2StyOicbw |
MALICIOUS
Executing a file with an untrusted certificate
- NMF64.exe (PID: 5556)
- NMF64.exe (PID: 1696)
SUSPICIOUS
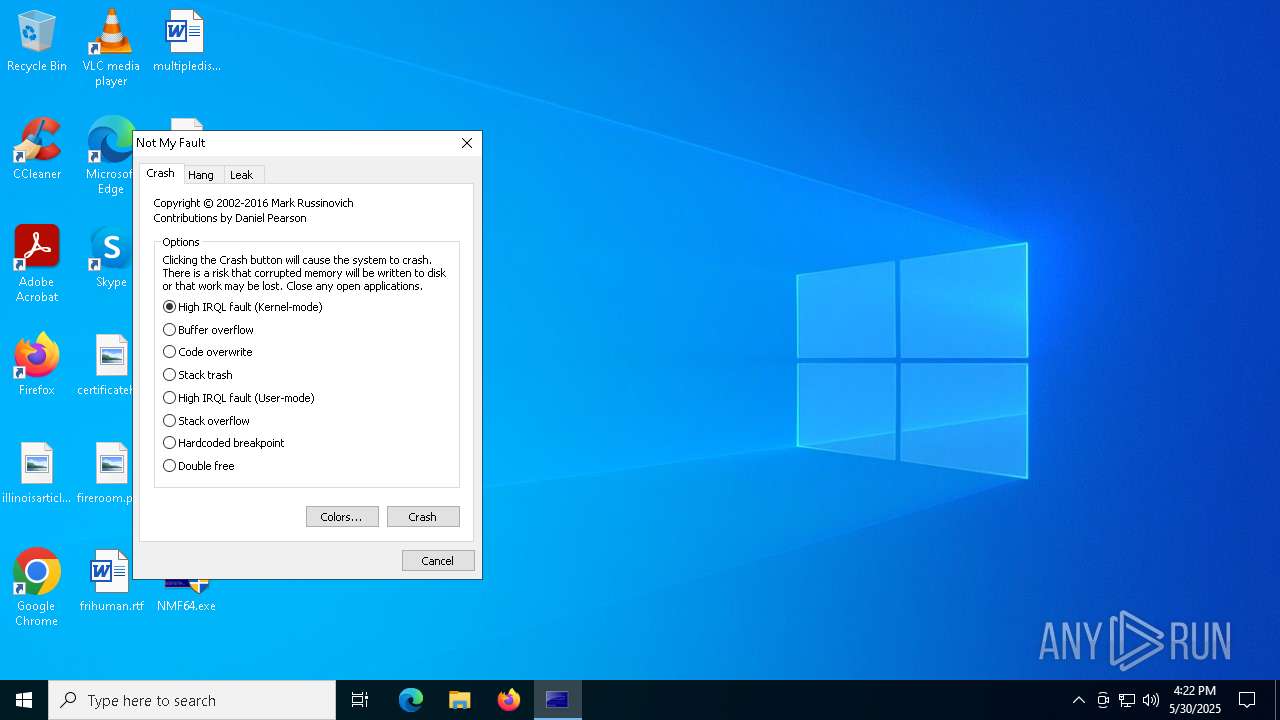
Creates files in the driver directory
- NMF64.exe (PID: 1696)
Drops a system driver (possible attempt to evade defenses)
- NMF64.exe (PID: 1696)
Executable content was dropped or overwritten
- NMF64.exe (PID: 1696)
INFO
The sample compiled with english language support
- NMF64.exe (PID: 1696)
Reads product name
- NMF64.exe (PID: 1696)
Checks supported languages
- NMF64.exe (PID: 1696)
Reads Environment values
- NMF64.exe (PID: 1696)
Reads the computer name
- NMF64.exe (PID: 1696)
Reads the software policy settings
- slui.exe (PID: 1512)
Checks proxy server information
- slui.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2016:09:17 21:31:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 12 |
| CodeSize: | 80896 |
| InitializedDataSize: | 177152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5b0c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.0 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
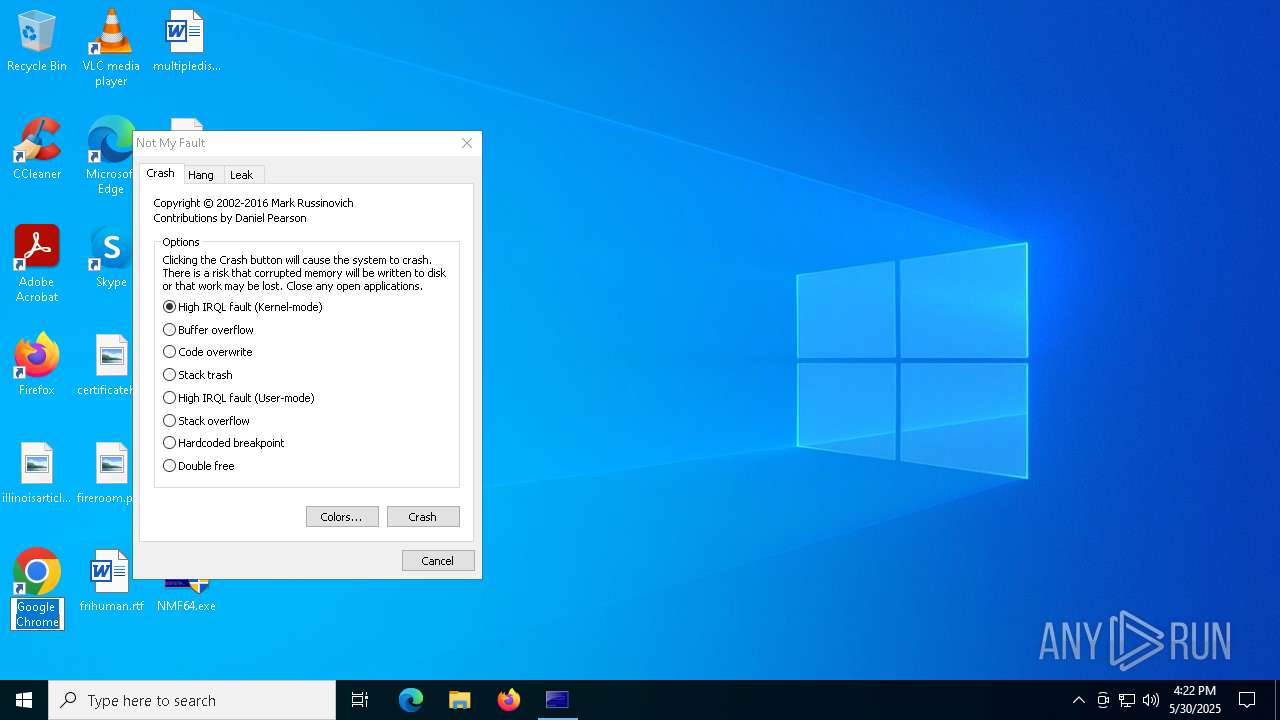
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Driver Bug Test Program |
| FileVersion: | 4.01 |
| InternalName: | Sysinternals NotMyfault |
| LegalCopyright: | Copyright (C) 2002-2016 Mark Russinovich |
| OriginalFileName: | NotMyfault.exe |
| ProductName: | Sysinternals NotMyfault |
| ProductVersion: | 4.01 |
Total processes
125
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1512 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\Desktop\NMF64.exe" | C:\Users\admin\Desktop\NMF64.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Driver Bug Test Program Version: 4.01 Modules
| |||||||||||||||
| 5556 | "C:\Users\admin\Desktop\NMF64.exe" | C:\Users\admin\Desktop\NMF64.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Driver Bug Test Program Exit code: 3221226540 Version: 4.01 Modules
| |||||||||||||||
Total events
3 380
Read events
3 379
Write events
1
Delete events
0
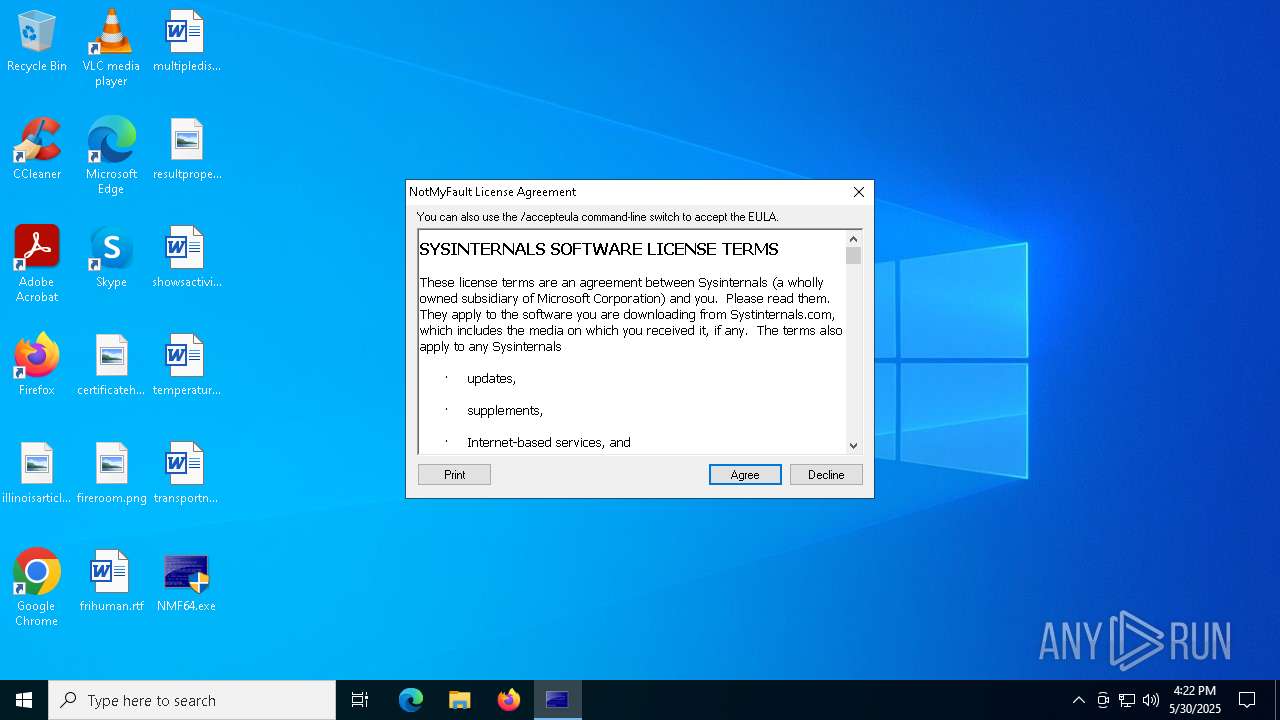
Modification events
| (PID) Process: | (1696) NMF64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\NotMyFault |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | NMF64.exe | C:\Windows\System32\drivers\myfault.sys | executable | |
MD5:2C1756A2D5659E7945BA5294E5136922 | SHA256:7F6ABC1F2086C07264F6F8620526CDC656197A22232E25937E1D2EDCDA739370 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7856 | RUXIMICS.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
7856 | RUXIMICS.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7856 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7856 | RUXIMICS.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
7856 | RUXIMICS.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7844 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1512 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |