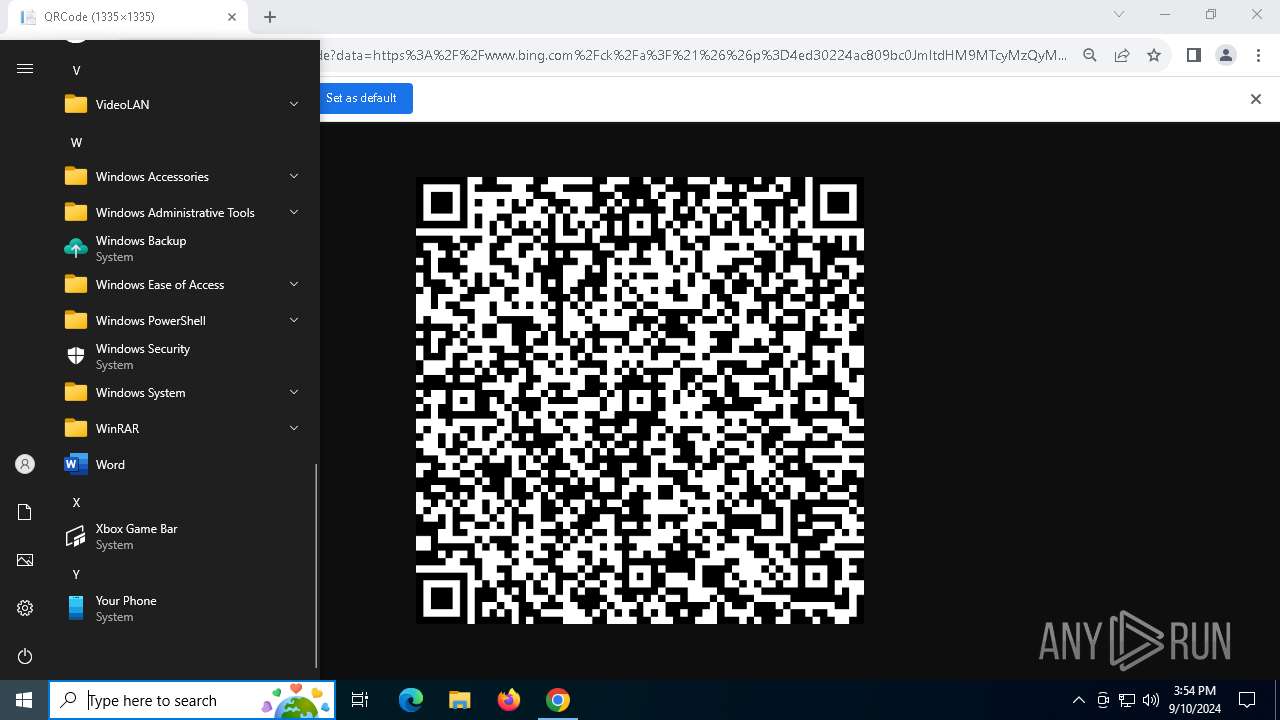
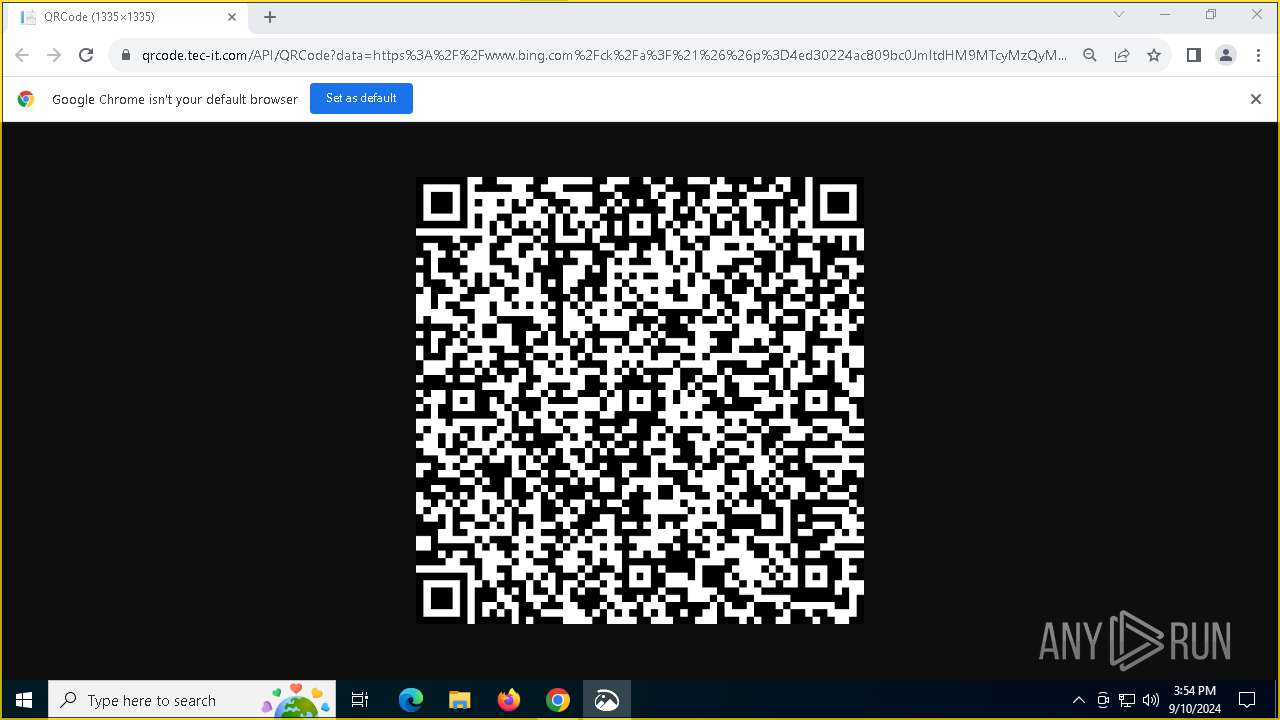
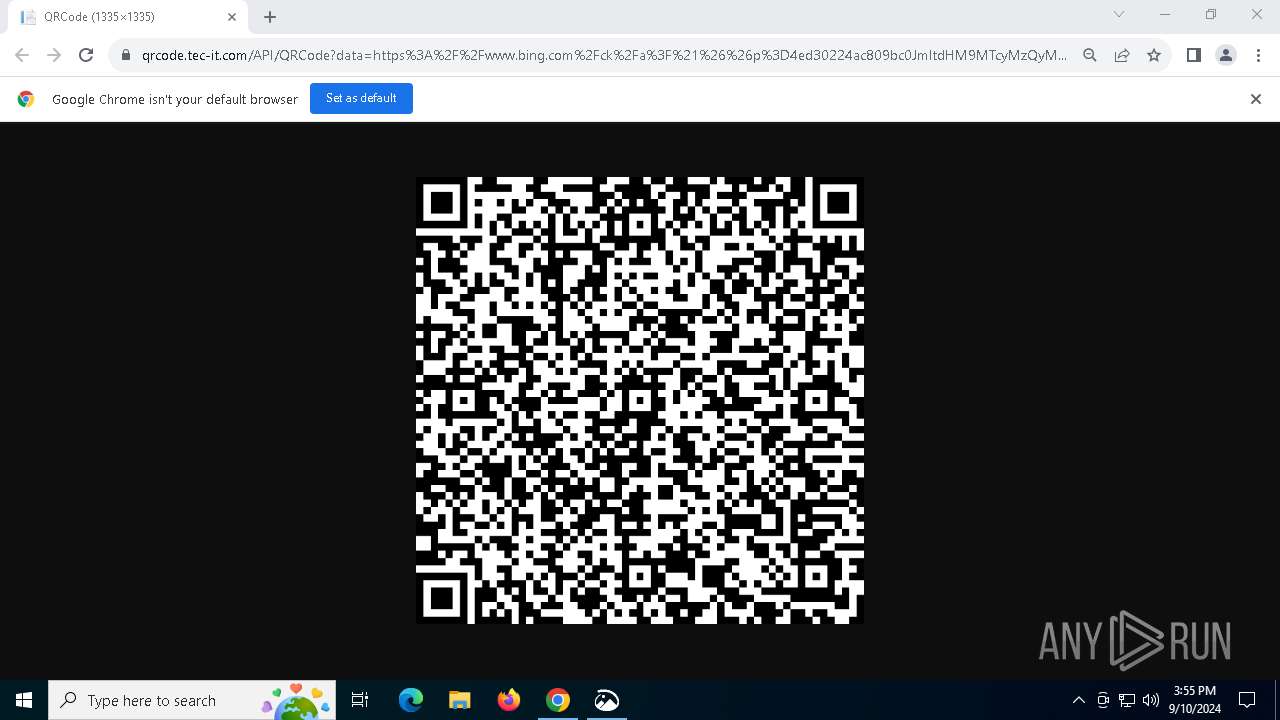
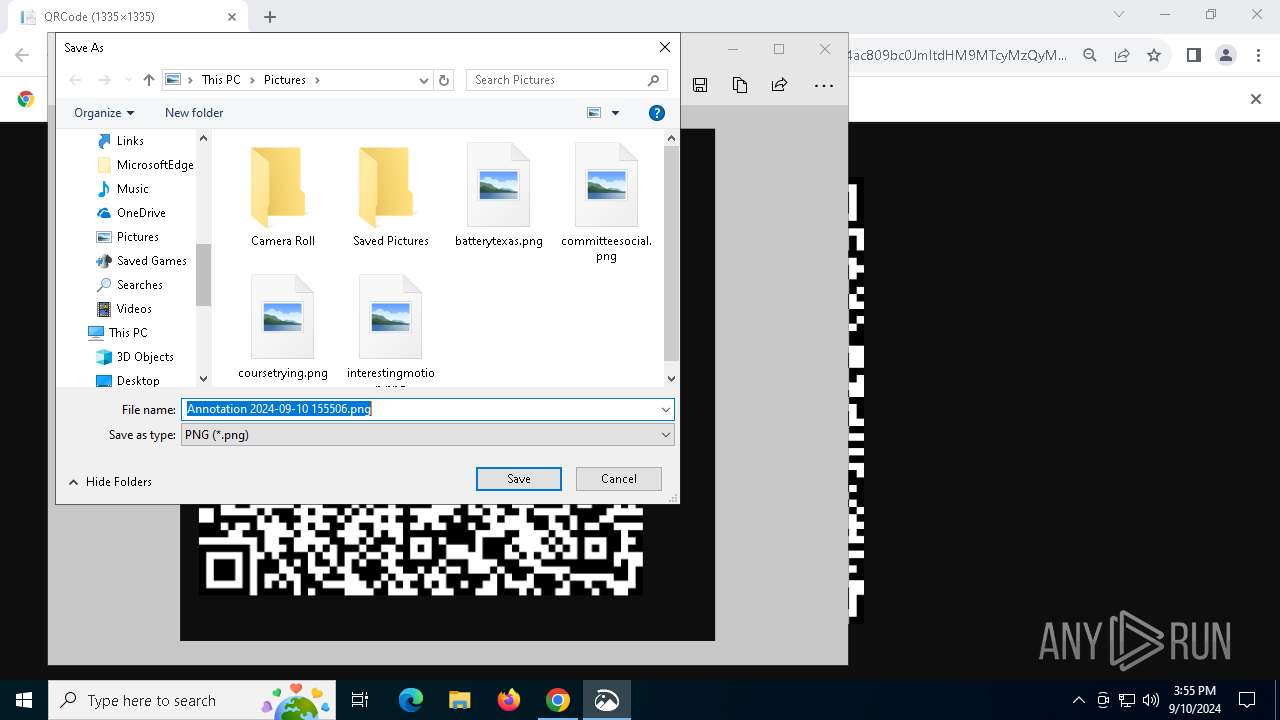
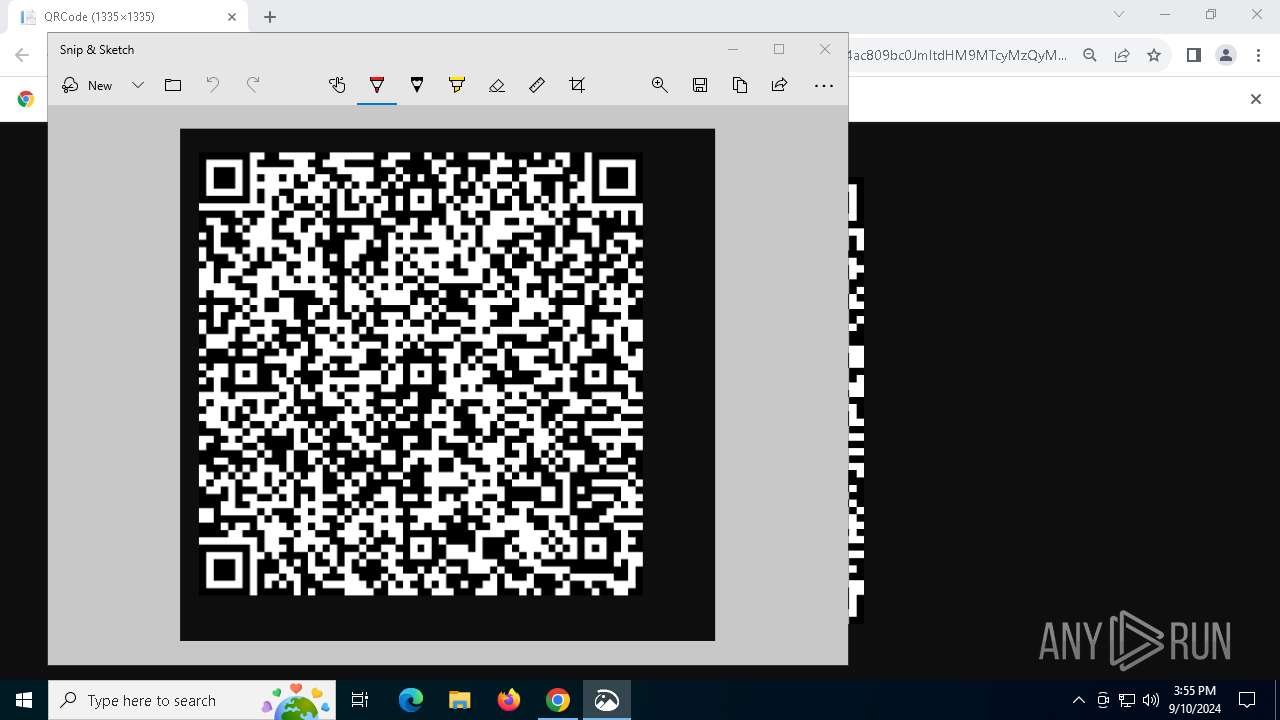
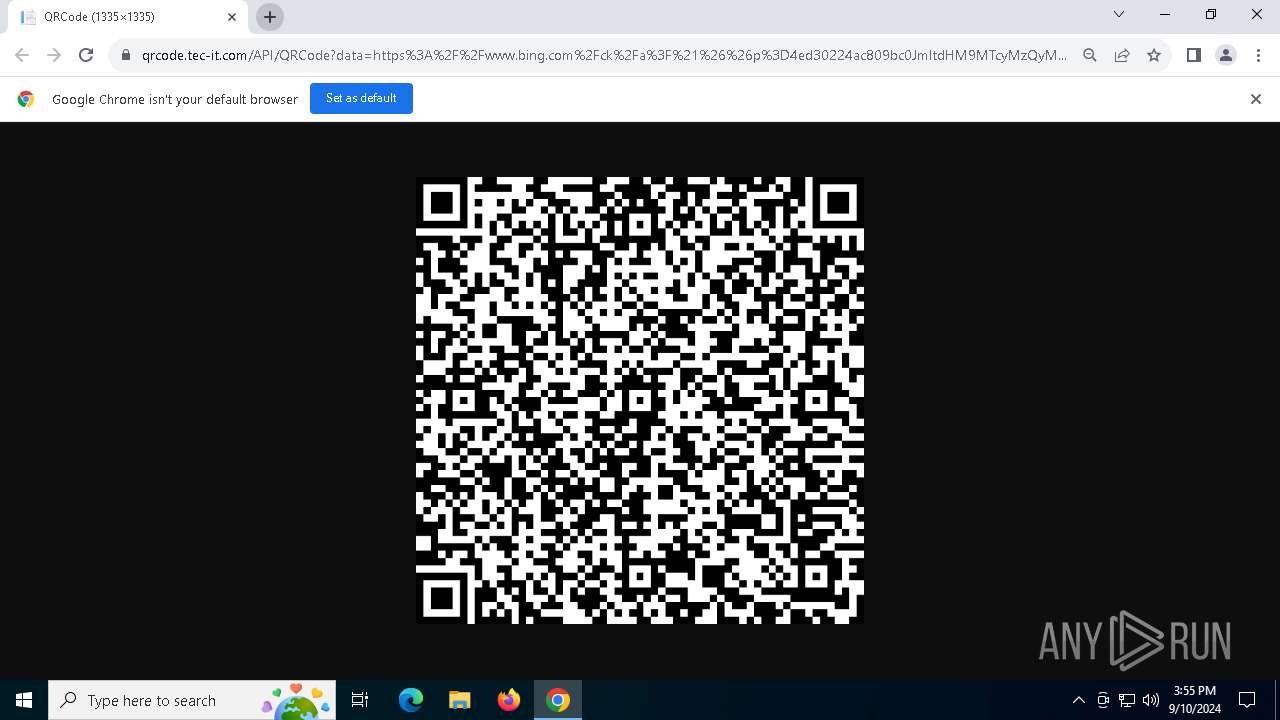
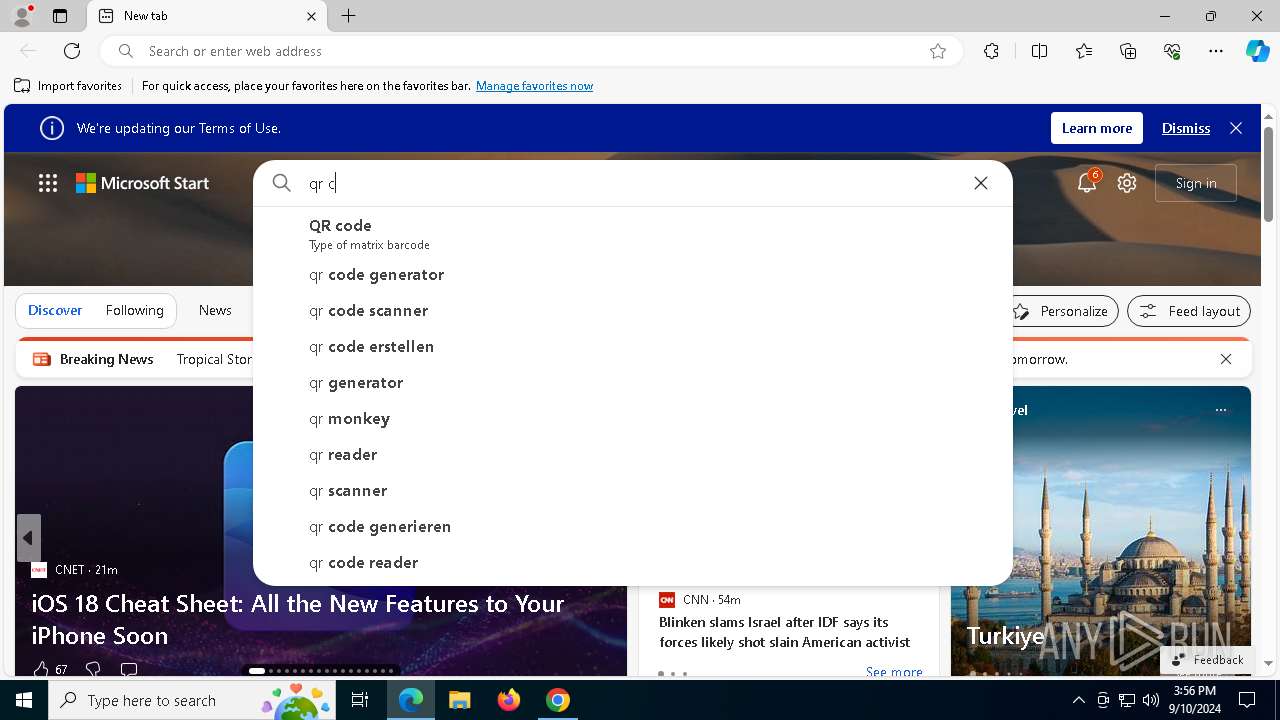
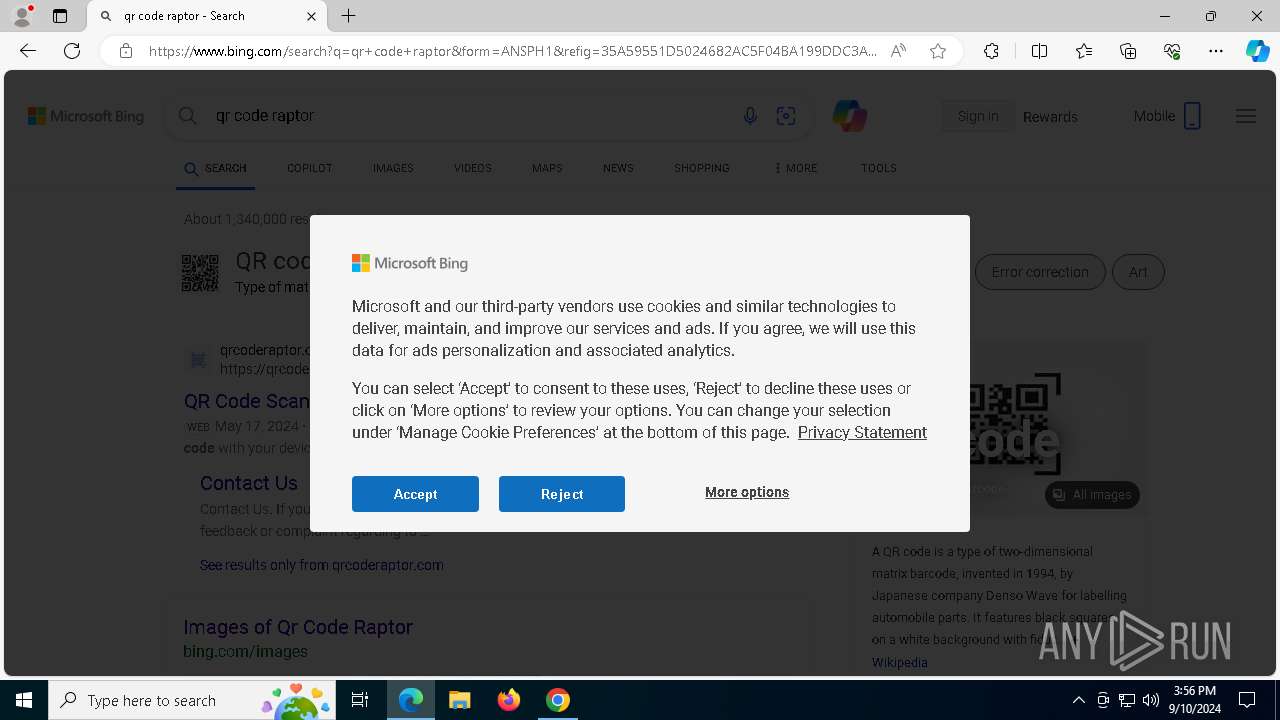
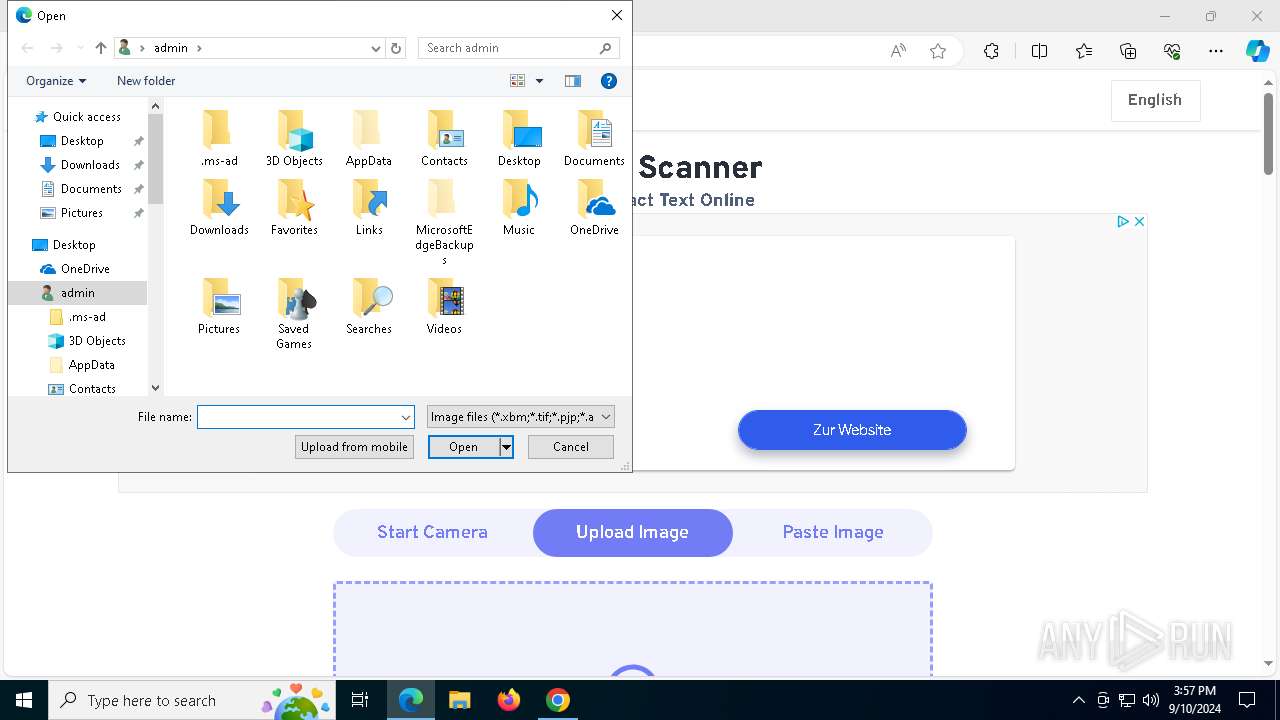
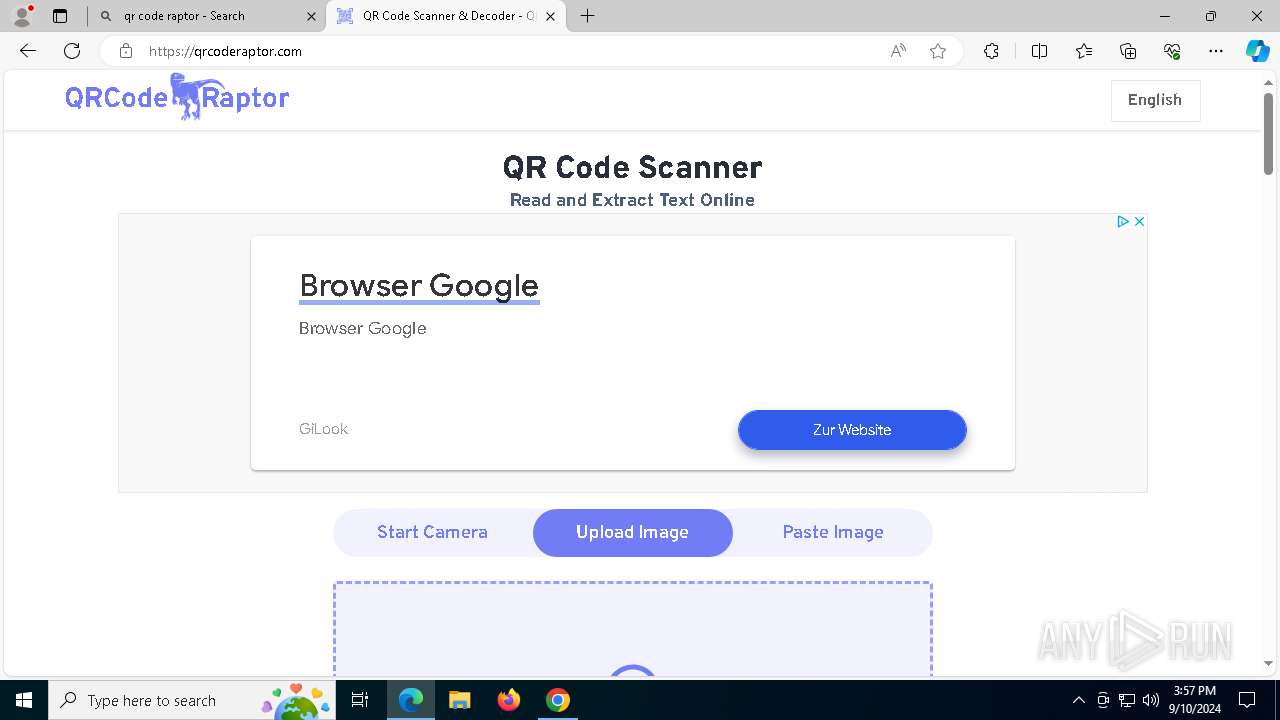
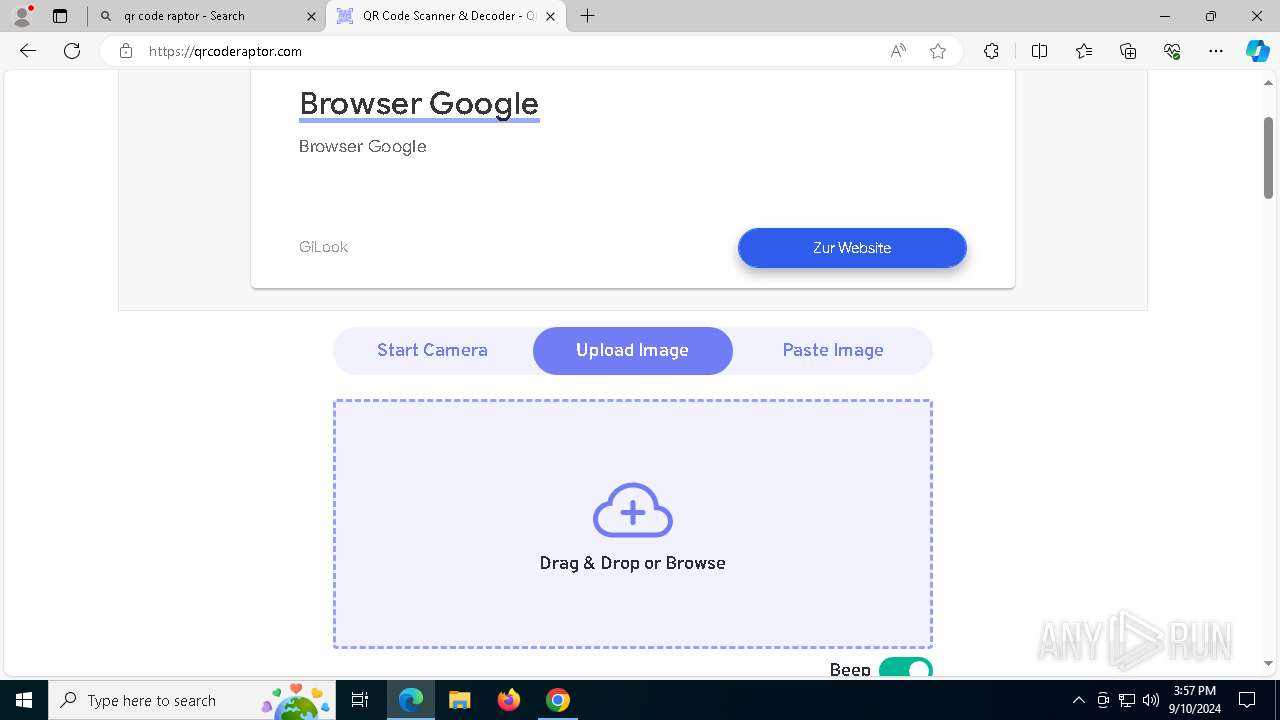
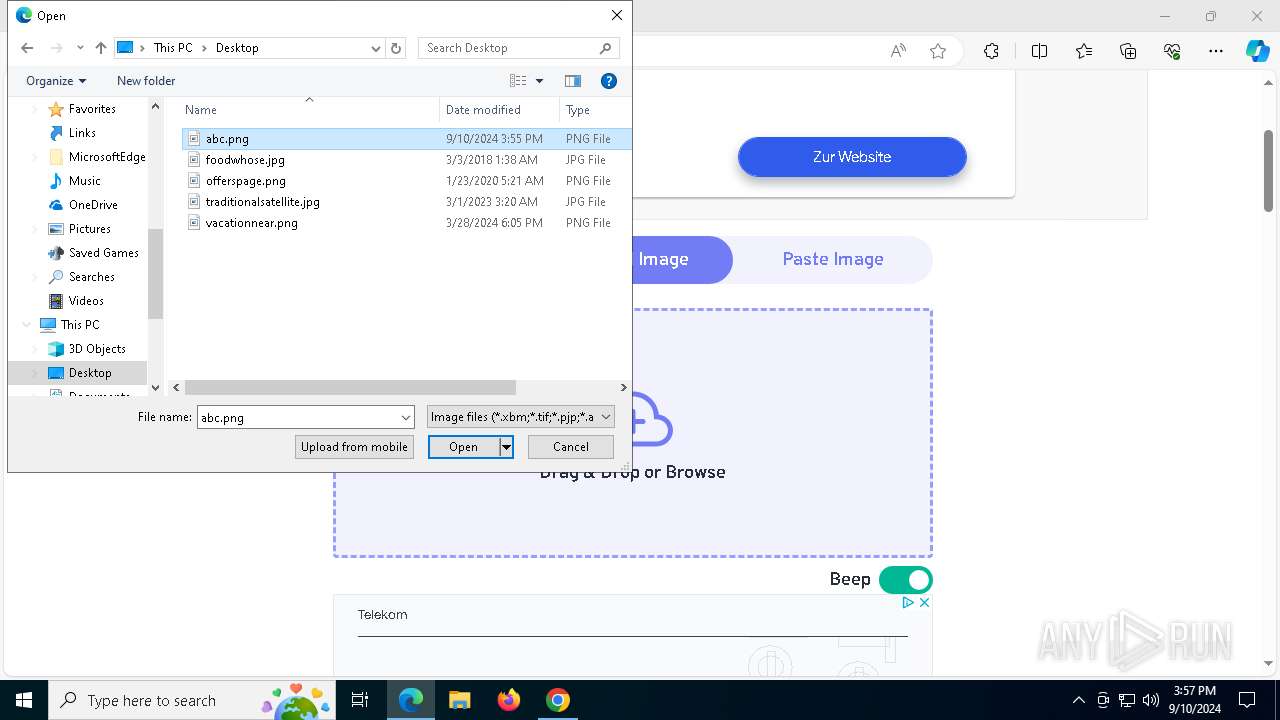
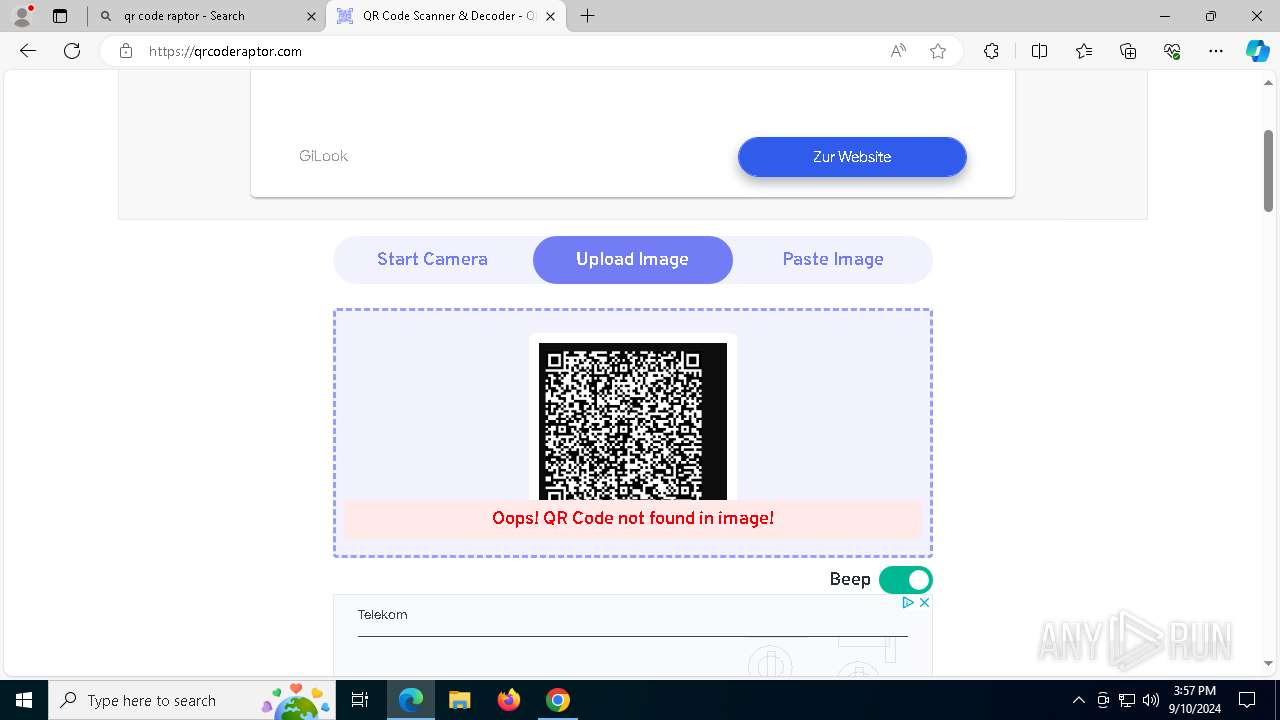
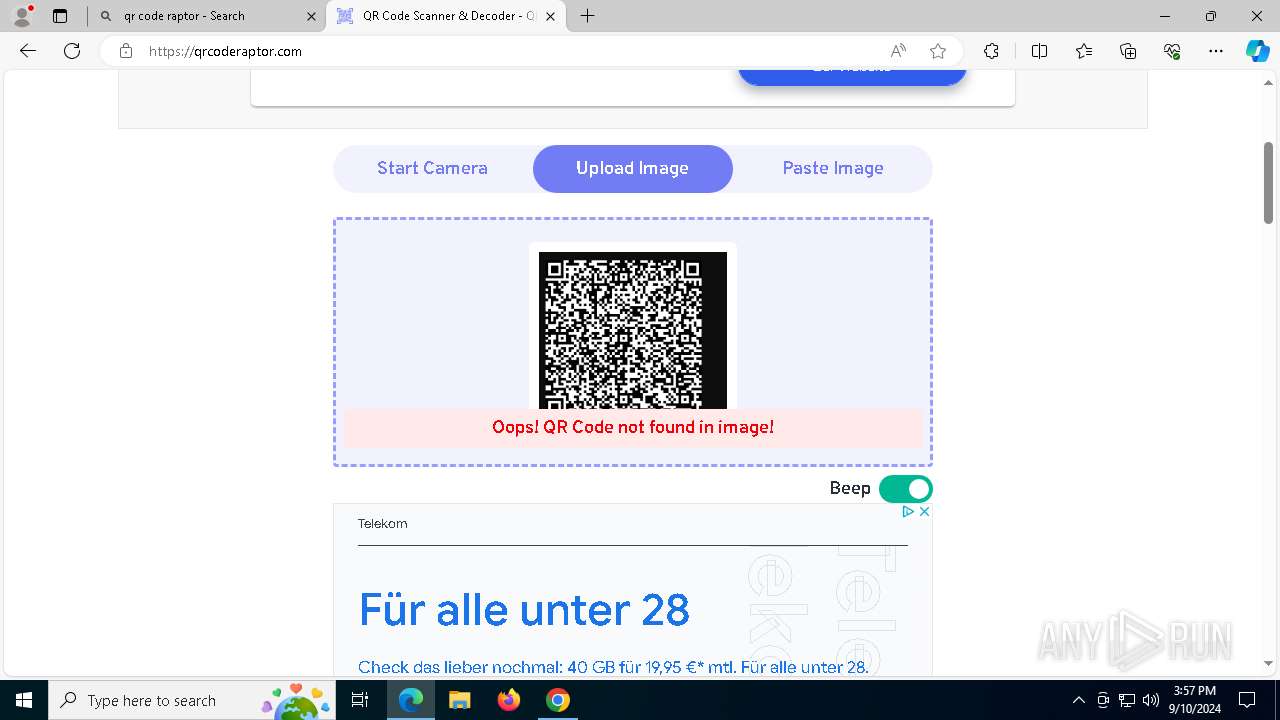
| URL: | https://qrcode.tec-it.com/API/QRCode?data=https%3A%2F%2Fwww.bing.com%2Fck%2Fa%3F%21%26%26p%3D4ed30224ac809bc0JmltdHM9MTcyMzQyMDgwMCZpZ3VpZD0zNjRmNjVlOC1lNTZjLTYxOWQtMTI1Ny03MTNlZTQyYTYwMTImaW5zaWQ9NTE0MQ%26ptn%3D3%26ver%3D2%26hsh%3D3%26fclid%3D364f65e8-e56c-619d-1257-713ee42a6012%26u%3Da1aHR0cDovL3d3dy40NDQzMTcuY29tLw%23aHR0cHM6Ly9pUjkuaGVhc3R5cGhlLmNvbS8zOGlJVHMv%2F |
| Full analysis: | https://app.any.run/tasks/3097fb23-ebe3-4e11-96ab-763132640884 |
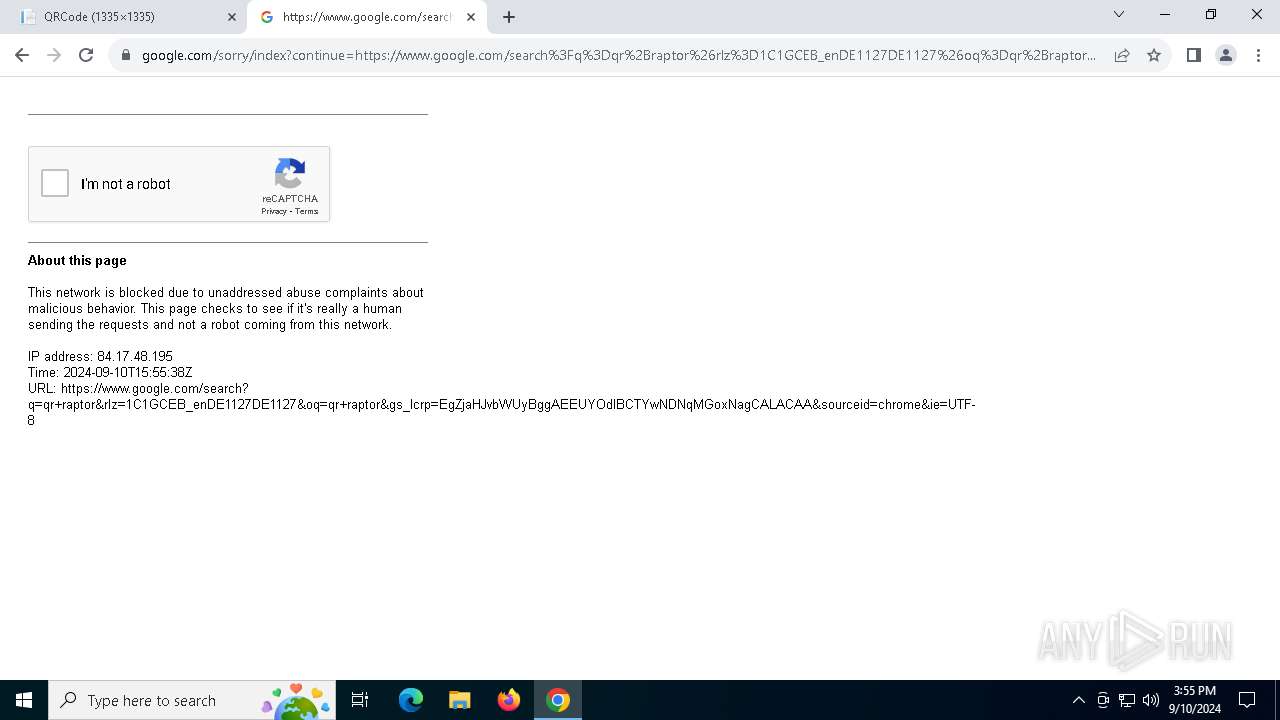
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2024, 15:53:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 23FD06EB2A9DB2B8E68AAD3403F5B2CF |
| SHA1: | D53702957C9808195080791EE140F60C1E58F294 |
| SHA256: | 08DA3376E263E8BE9CC88CFC5B20F0A091DD5FEF166E33DF9A97B084E7C4DBAE |
| SSDEEP: | 6:270S0fJnztFZqVzhRQJxyAHOggfj4BbnIoQ1UJItkSoA5gp4DCvz:27yfJn9uzh6xlSfjUMSJIGs1Gvz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- ScreenSketch.exe (PID: 4364)
- ScreenClippingHost.exe (PID: 1184)
INFO
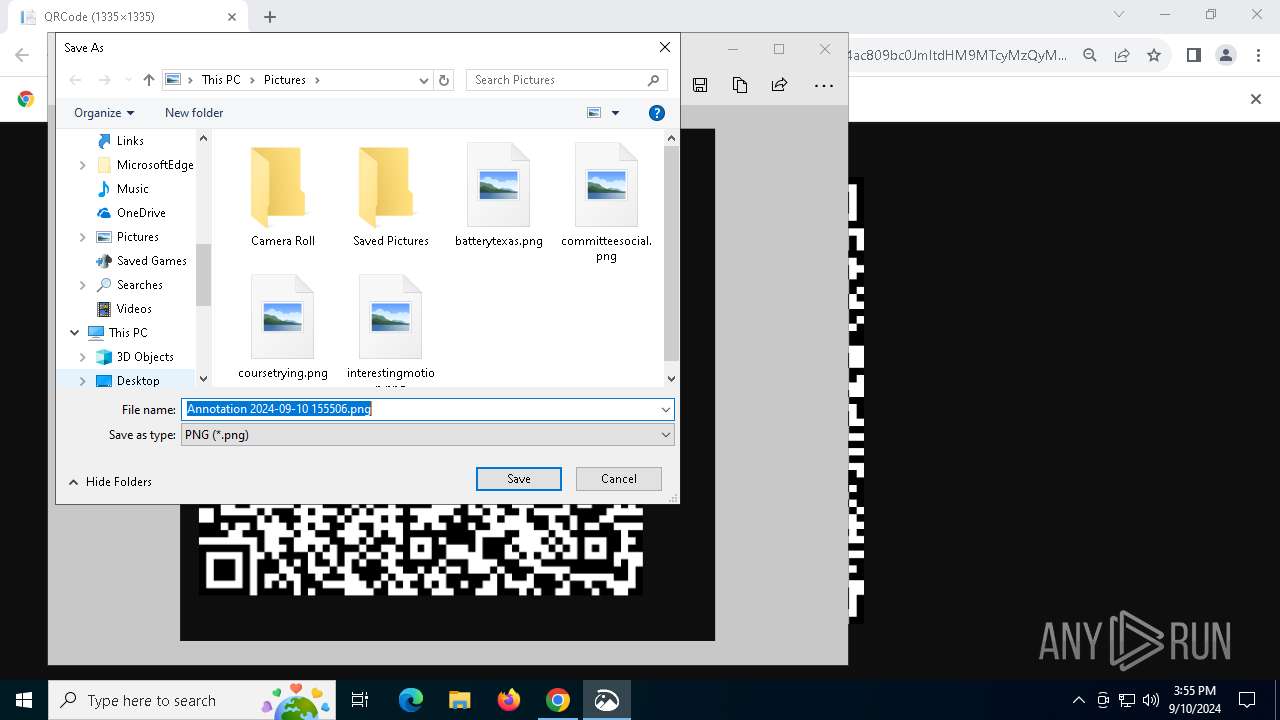
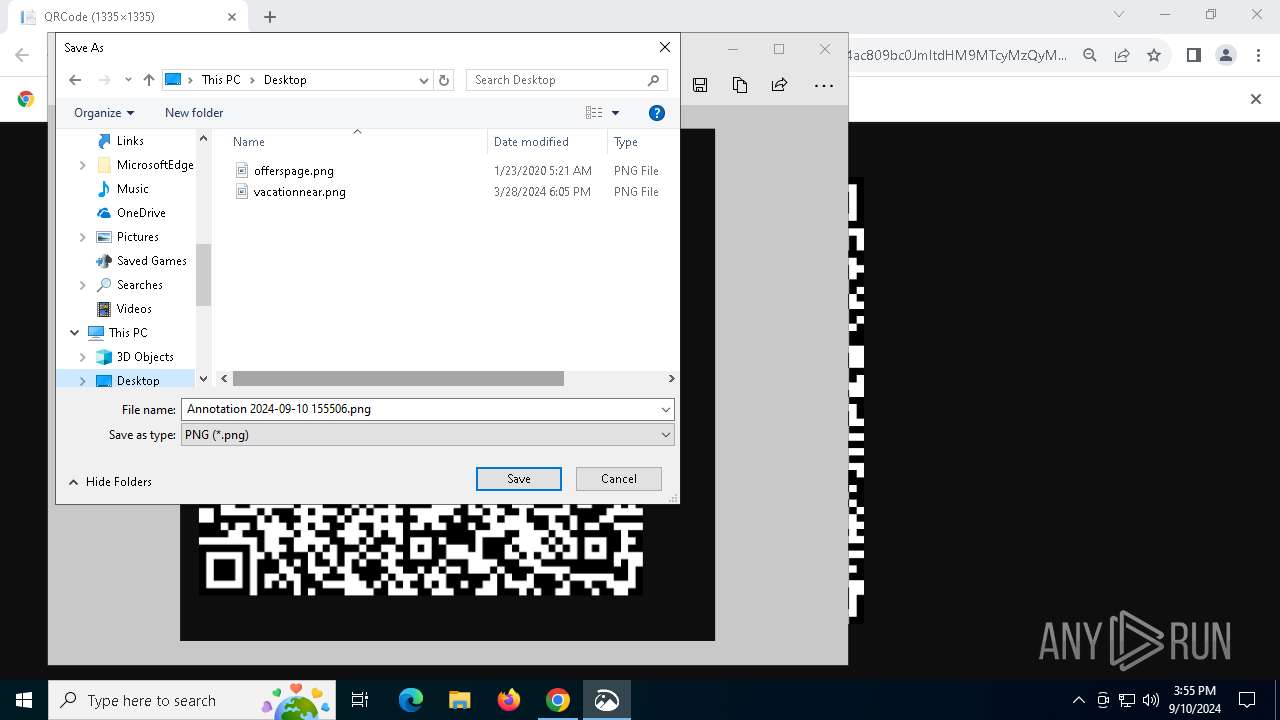
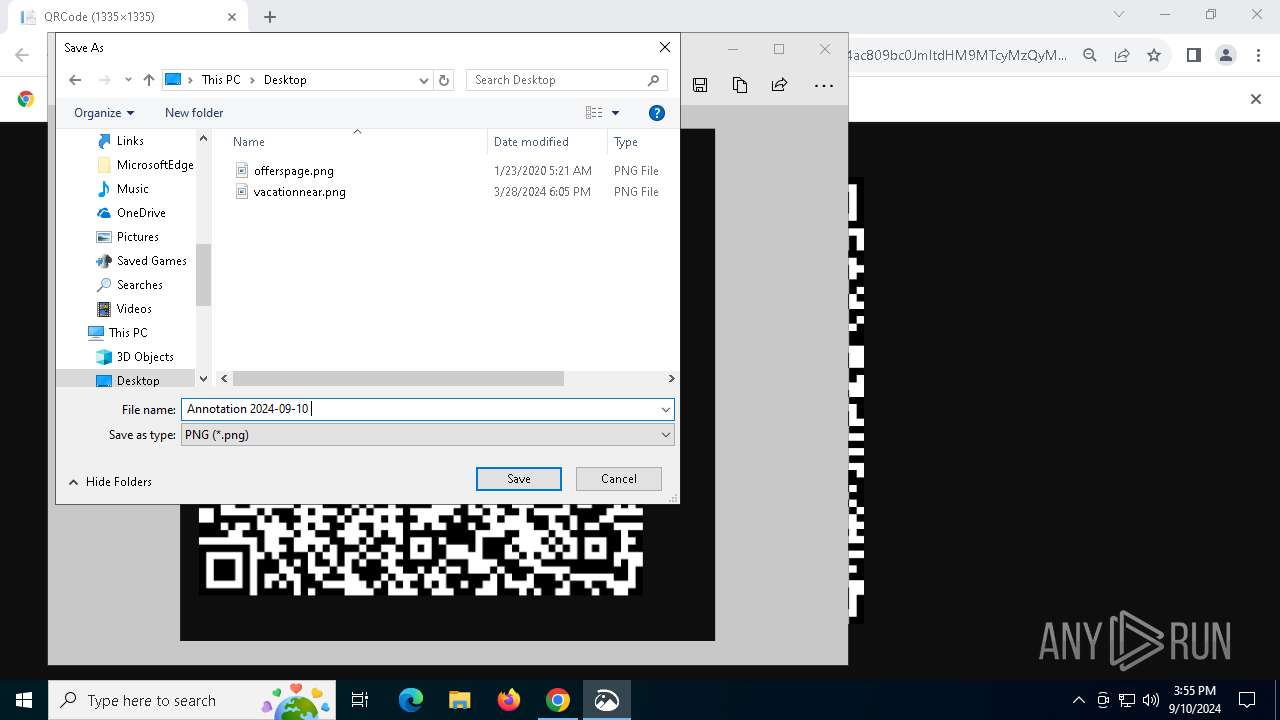
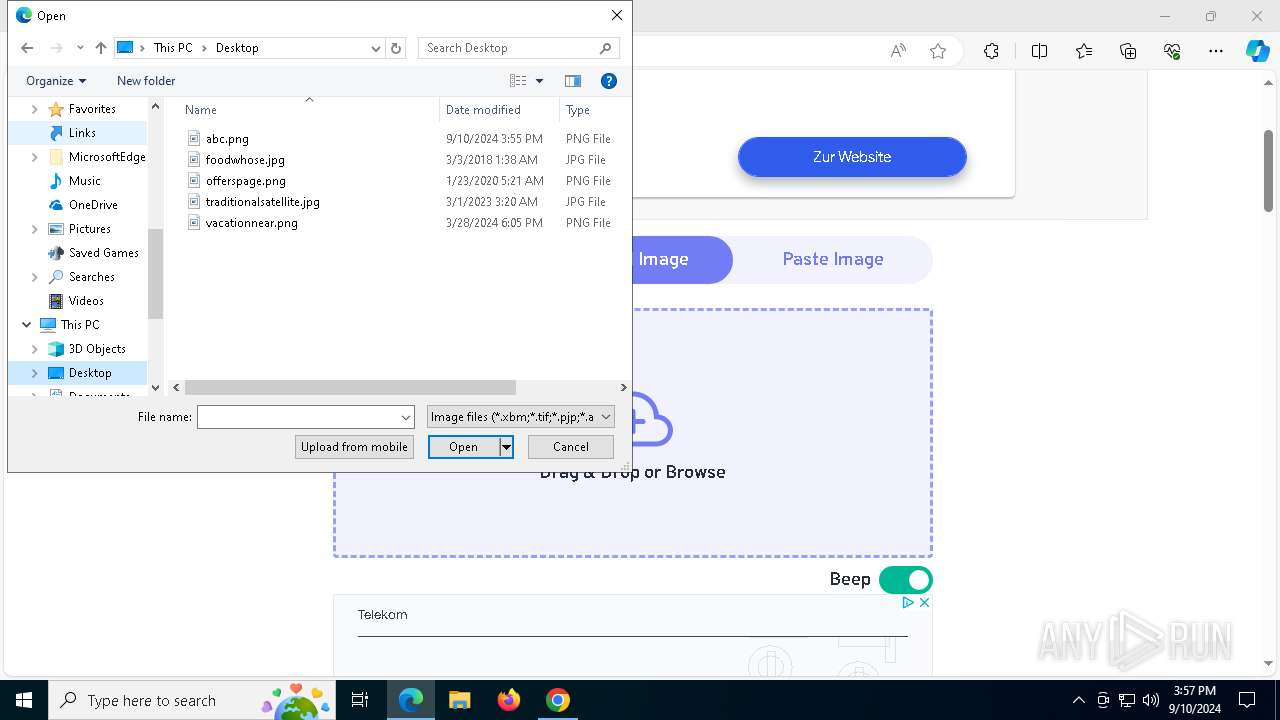
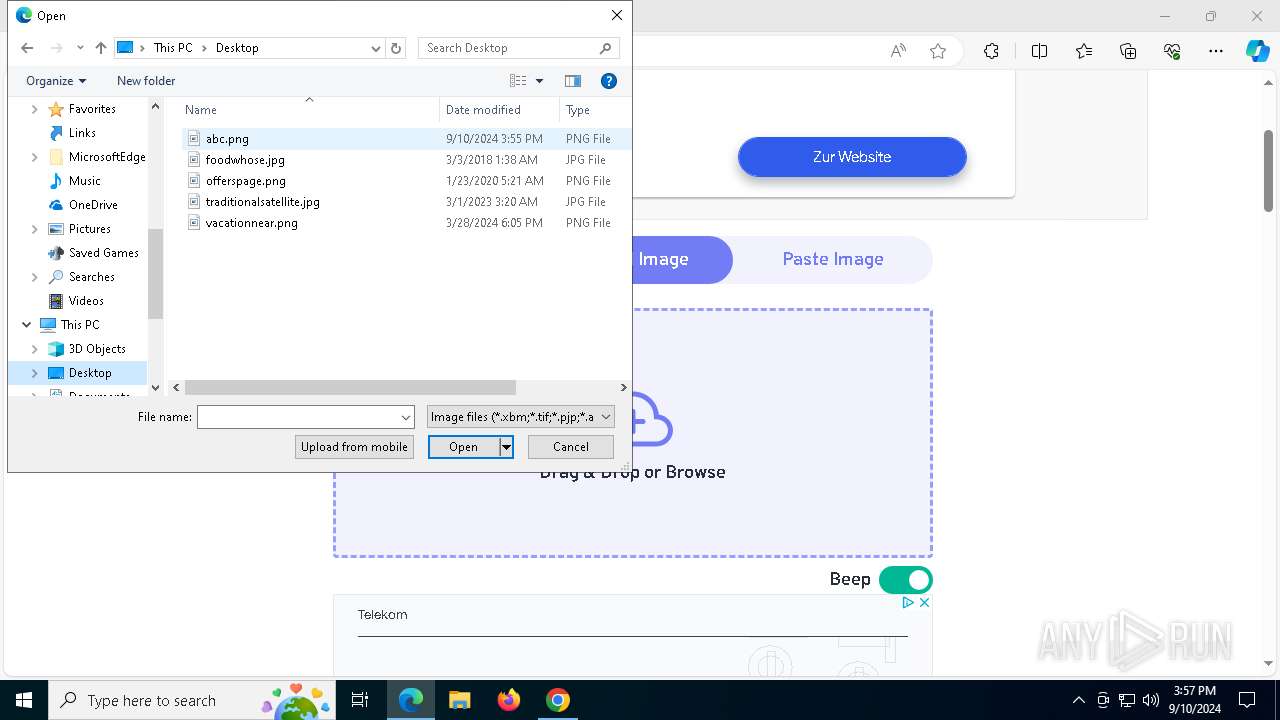
Creates files or folders in the user directory
- ScreenSketch.exe (PID: 4364)
Checks supported languages
- ScreenSketch.exe (PID: 4364)
- ScreenClippingHost.exe (PID: 1184)
- identity_helper.exe (PID: 7644)
Reads the computer name
- ScreenSketch.exe (PID: 4364)
- ScreenClippingHost.exe (PID: 1184)
- identity_helper.exe (PID: 7644)
Sends debugging messages
- ScreenSketch.exe (PID: 4364)
- msedge.exe (PID: 2328)
Reads security settings of Internet Explorer
- PickerHost.exe (PID: 3864)
Manual execution by a user
- msedge.exe (PID: 7104)
Reads Environment values
- identity_helper.exe (PID: 7644)
Application launched itself
- msedge.exe (PID: 7104)
- chrome.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
76
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=5408 --field-trial-handle=1880,i,10204943185786317893,5160484211132940470,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5060 --field-trial-handle=1880,i,10204943185786317893,5160484211132940470,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\ScreenClippingHost.exe" -ServerName:ScreenClipping.AppX6726kd2wrry6c6n8nc57a1zn08dmzmbt.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\ScreenClippingHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 1 Version: 123.29302.0.0 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5396 --field-trial-handle=1880,i,10204943185786317893,5160484211132940470,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5168 --field-trial-handle=1880,i,10204943185786317893,5160484211132940470,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2564 --field-trial-handle=2424,i,13136762230363707996,7140718987531382955,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://qrcode.tec-it.com/API/QRCode?data=https%3A%2F%2Fwww.bing.com%2Fck%2Fa%3F%21%26%26p%3D4ed30224ac809bc0JmltdHM9MTcyMzQyMDgwMCZpZ3VpZD0zNjRmNjVlOC1lNTZjLTYxOWQtMTI1Ny03MTNlZTQyYTYwMTImaW5zaWQ9NTE0MQ%26ptn%3D3%26ver%3D2%26hsh%3D3%26fclid%3D364f65e8-e56c-619d-1257-713ee42a6012%26u%3Da1aHR0cDovL3d3dy40NDQzMTcuY29tLw%23aHR0cHM6Ly9pUjkuaGVhc3R5cGhlLmNvbS8zOGlJVHMv%2F" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5592 --field-trial-handle=1880,i,10204943185786317893,5160484211132940470,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4188 --field-trial-handle=2424,i,13136762230363707996,7140718987531382955,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x258,0x230,0x250,0x218,0x310,0x7fffc3385fd8,0x7fffc3385fe4,0x7fffc3385ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
28 075
Read events
27 788
Write events
255
Delete events
32
Modification events
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4364) ScreenSketch.exe | Key: | \REGISTRY\A\{a457059c-cb26-8af5-11fb-4340e2240093}\LocalState |
| Operation: | write | Name: | Setting_PreferNewWindow |
Value: 00583239C79903DB01 | |||
| (PID) Process: | (4364) ScreenSketch.exe | Key: | \REGISTRY\A\{a457059c-cb26-8af5-11fb-4340e2240093}\LocalState |
| Operation: | write | Name: | Setting_ShowUnsavedChangesConfirmations |
Value: 00108C47C79903DB01 | |||
| (PID) Process: | (4364) ScreenSketch.exe | Key: | \REGISTRY\A\{a457059c-cb26-8af5-11fb-4340e2240093}\LocalState |
| Operation: | write | Name: | HasUserSeenSnipHintFlyout |
Value: 0189E554C89903DB01 | |||
| (PID) Process: | (4364) ScreenSketch.exe | Key: | \REGISTRY\A\{a457059c-cb26-8af5-11fb-4340e2240093}\LocalState |
| Operation: | write | Name: | Setting_LastFileCleanUp |
Value: 0000000000000000E3D59EC89903DB01 | |||
| (PID) Process: | (4364) ScreenSketch.exe | Key: | \REGISTRY\A\{a457059c-cb26-8af5-11fb-4340e2240093}\LocalState |
| Operation: | write | Name: | Setting_LastFileCleanUp |
Value: 53EA9FC89903DB01E3D59EC89903DB01 | |||
Executable files
21
Suspicious files
831
Text files
153
Unknown types
232
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12baec.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12badc.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\de7e0cc6-bf36-4b44-b951-f1602795fae4.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
201
DNS requests
204
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6276 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6276 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3708 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6224 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3908 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
3908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
3908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
3908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
3908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6224 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1332 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2208 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5164 | chrome.exe | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5164 | chrome.exe | 85.233.97.212:443 | qrcode.tec-it.com | KT-NET Communications GmbH | AT | whitelisted |
6224 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5164 | chrome.exe | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
qrcode.tec-it.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2180 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2180 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2180 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2180 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
msedge.exe | [0910/155711.440:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0910/155711.440:ERROR:device_ticket.cc(187)] The identity is null.
|
msedge.exe | [0910/155712.808:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0910/155712.808:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
|
msedge.exe | [0910/155712.808:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff85f0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0910/155712.808:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\SYSTEM32\ntdll.dll
|
msedge.exe | [0910/155712.810:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff6f10000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0910/155712.810:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNEL32.DLL
|
msedge.exe | [0910/155712.810:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff5da0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0910/155712.810:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNELBASE.dll
|