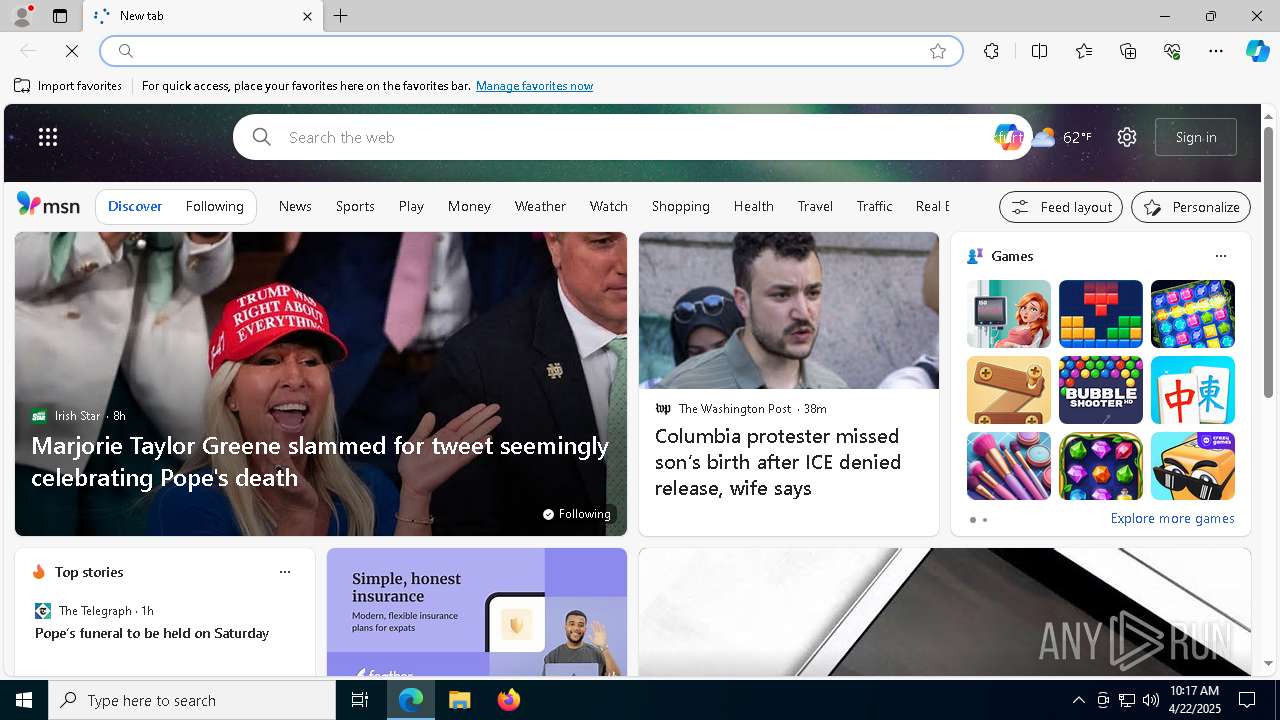
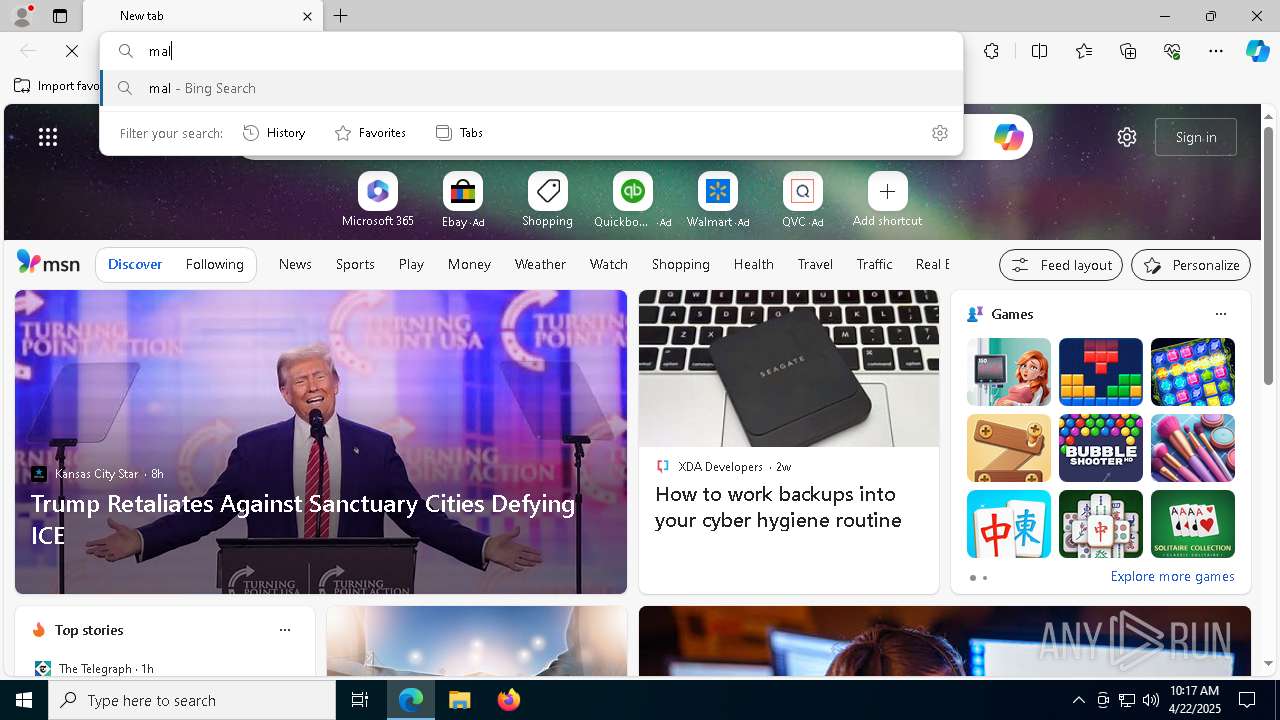
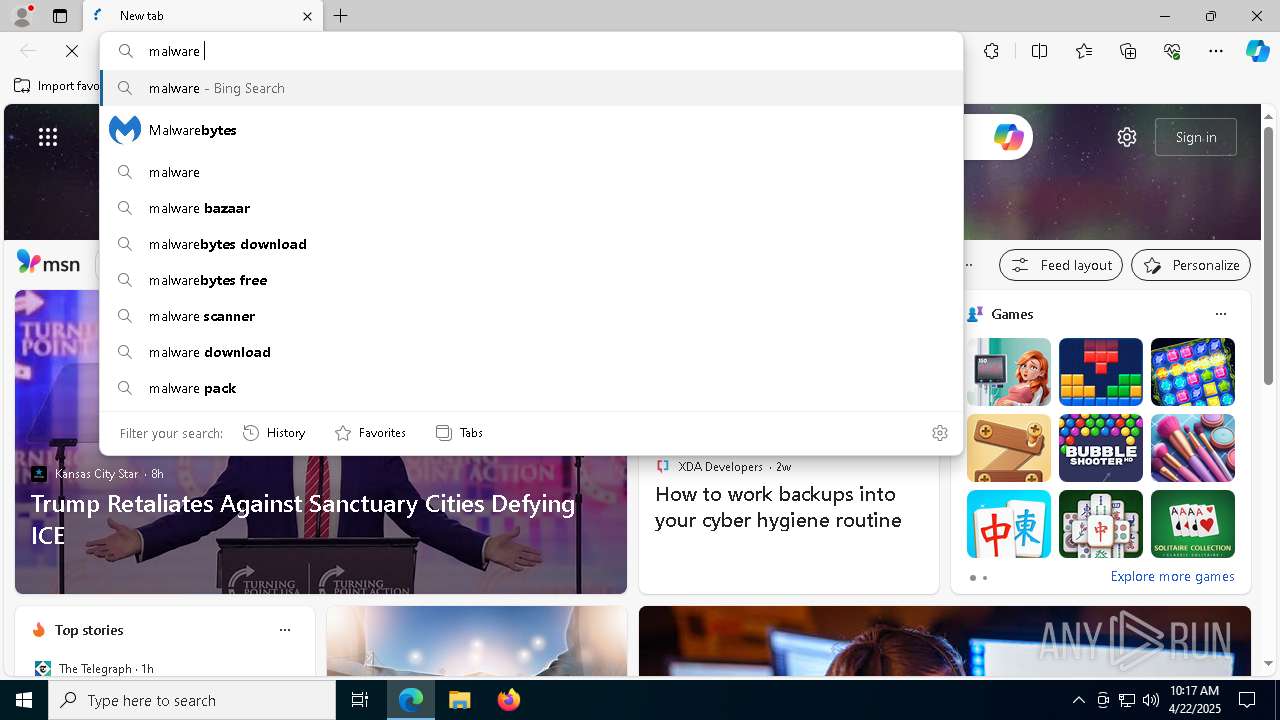
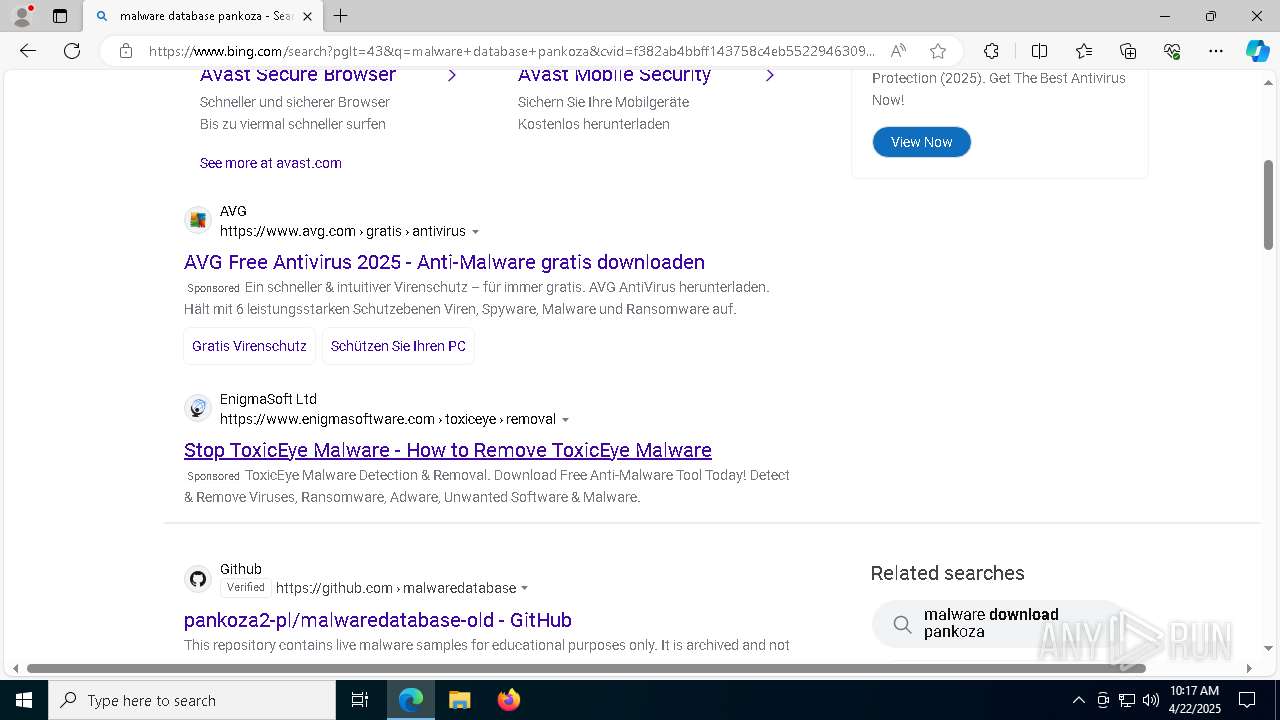
| URL: | pish.me |
| Full analysis: | https://app.any.run/tasks/c93d3f73-8cd9-476d-b6fc-ccec1e42bc17 |
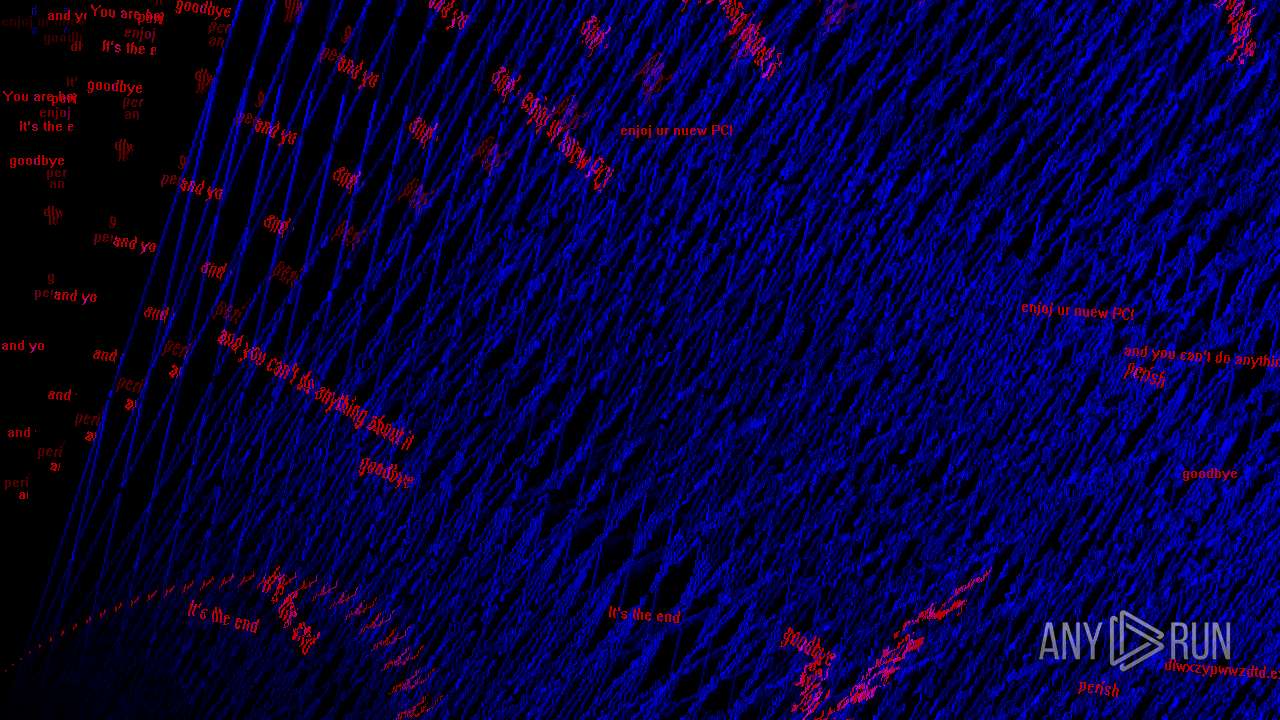
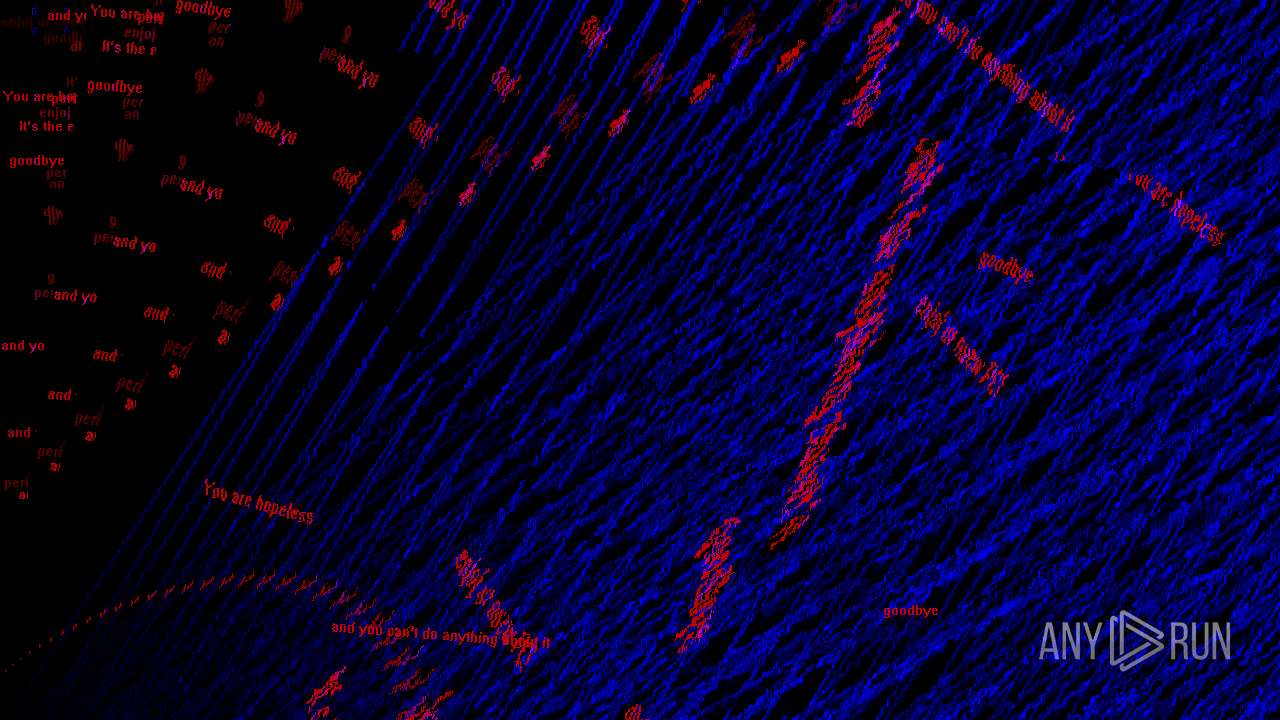
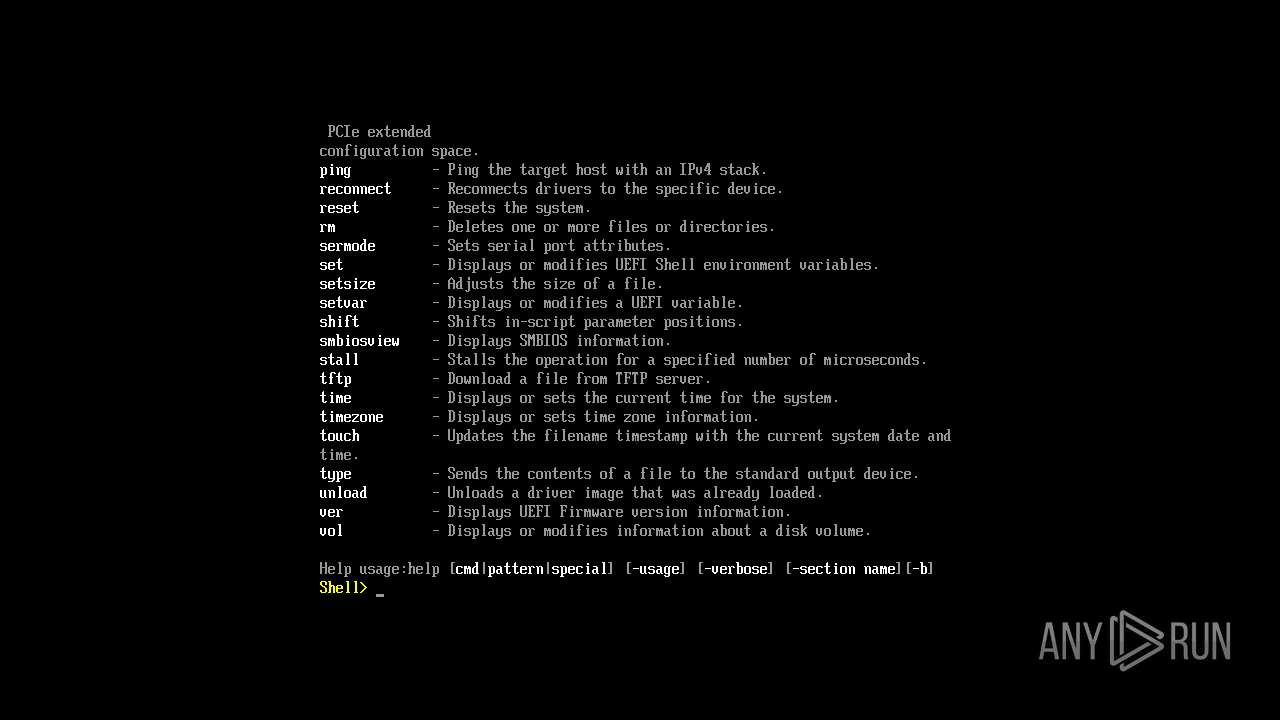
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2025, 10:17:26 |
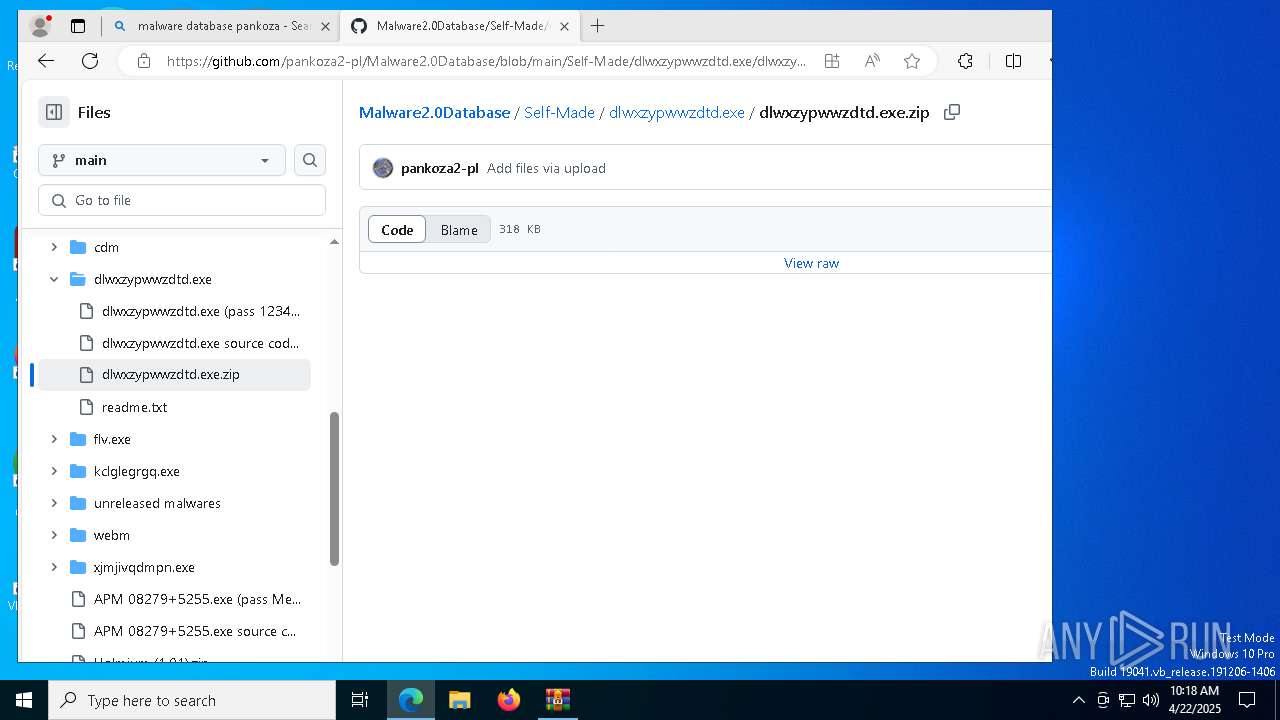
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 21478F3ADB653D91529B11600B589456 |
| SHA1: | 7844ACA1A4BA6280821ED5A3002DA6D04839A9D5 |
| SHA256: | 08D1F146BD1A7A9C5437EF97ABC739CAE441B4C1D352B181CFA6F502EE0A8BB0 |
| SSDEEP: | 3:bL9:bL9 |
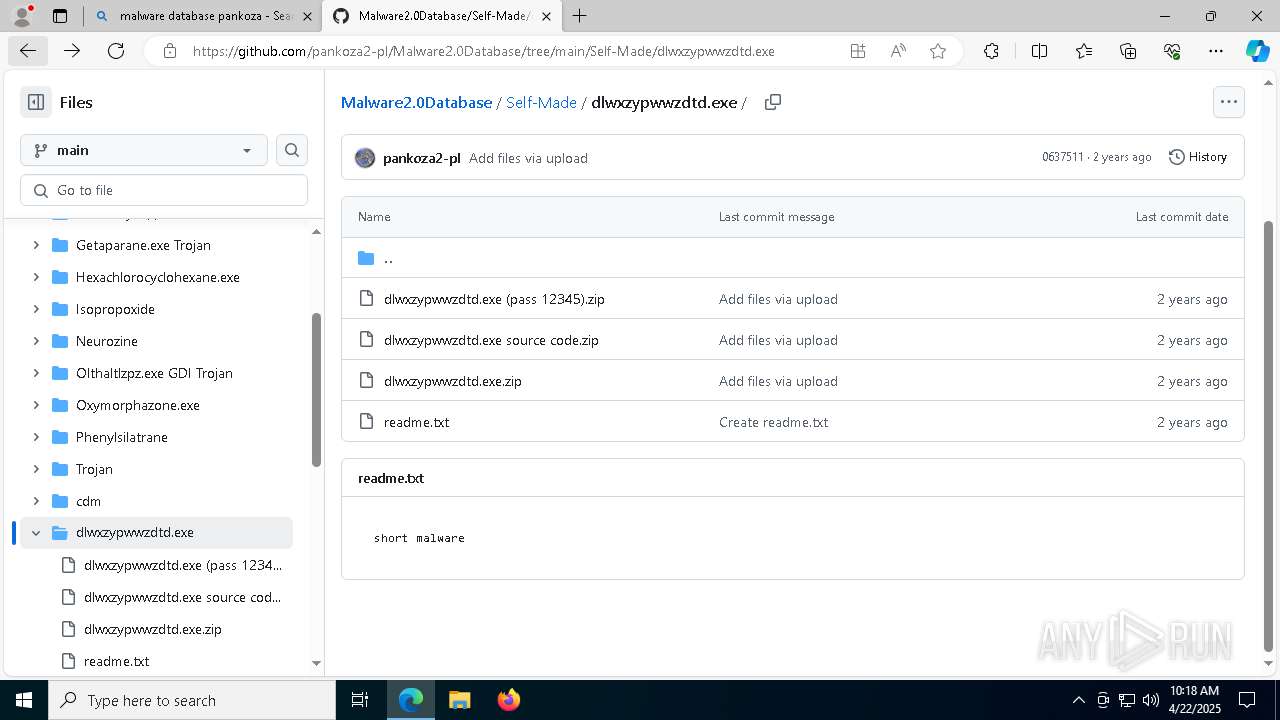
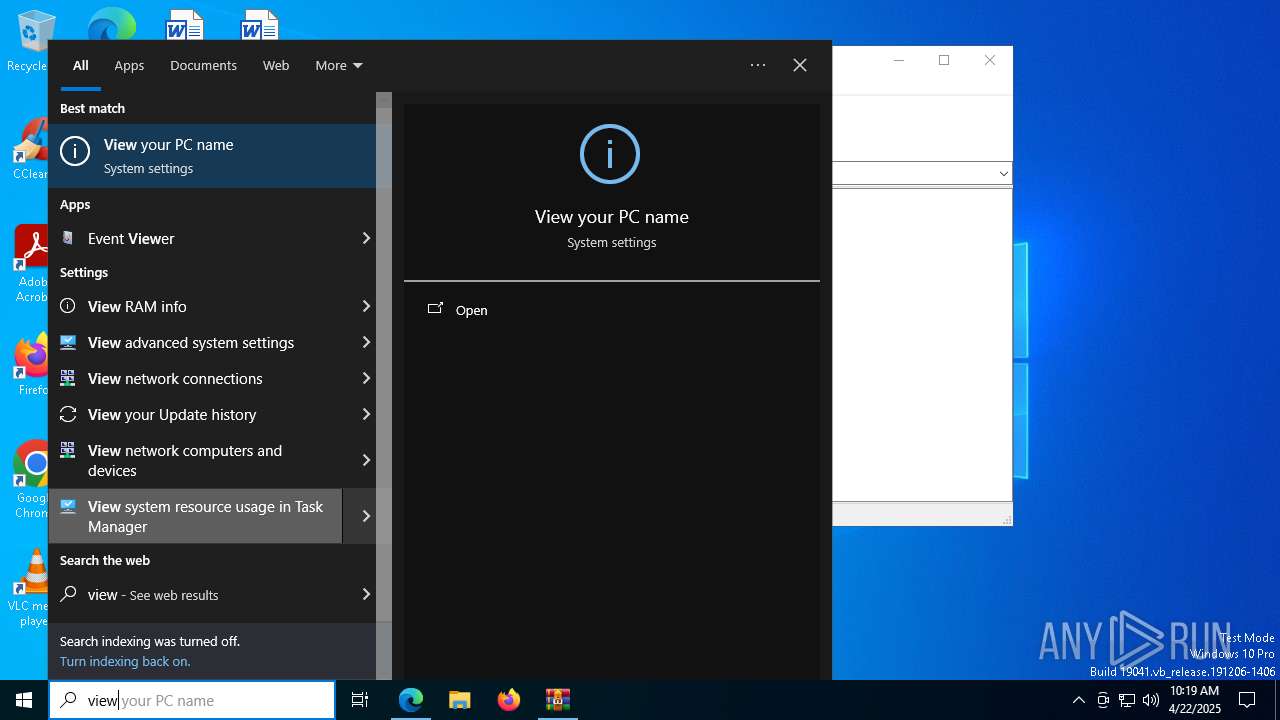
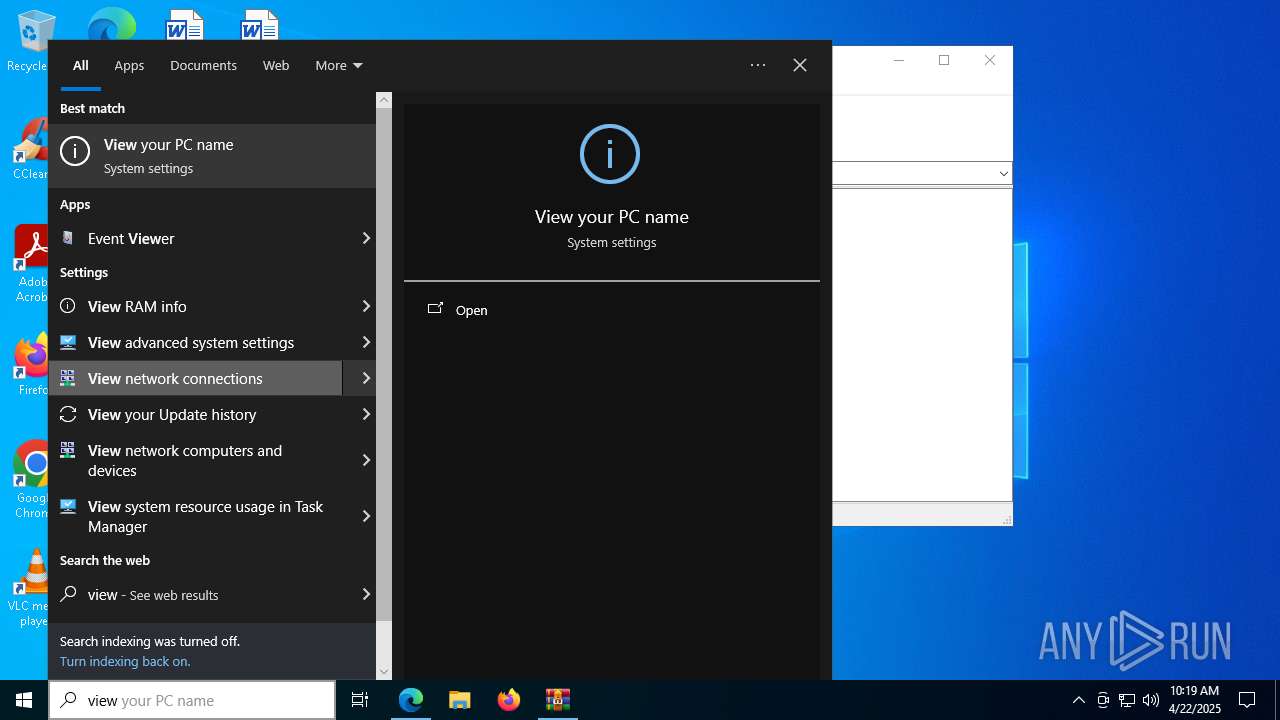
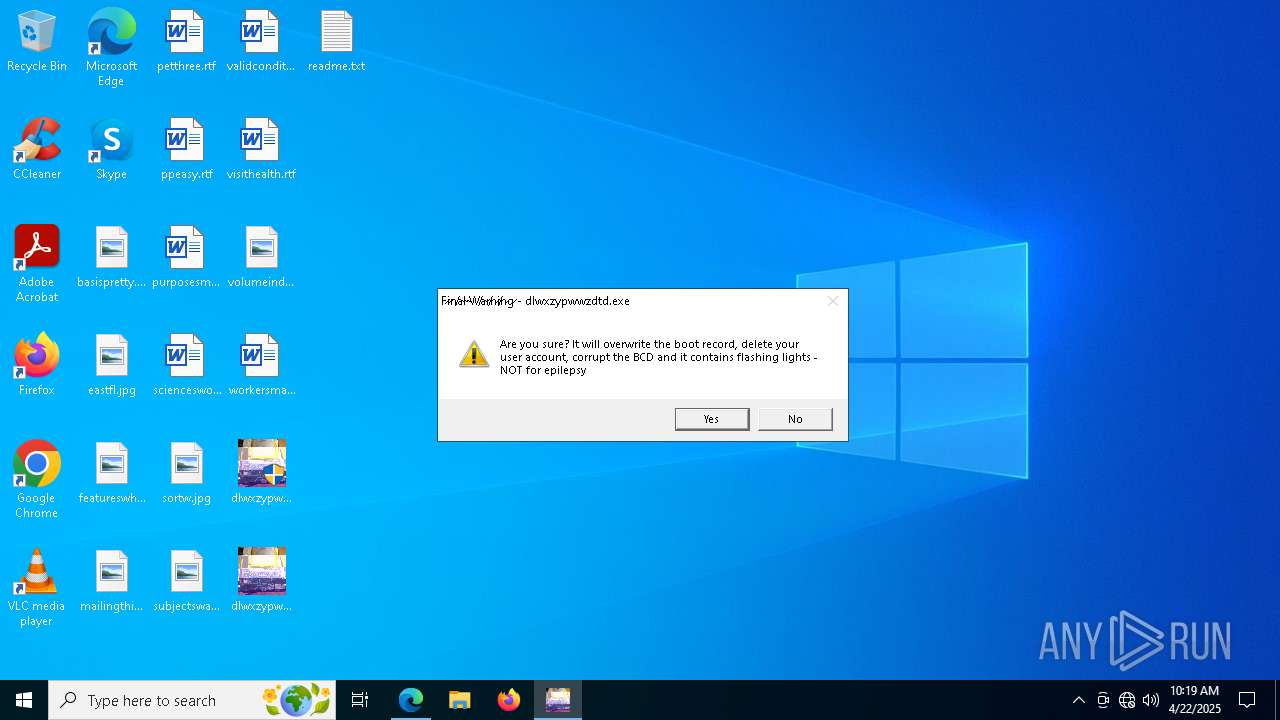
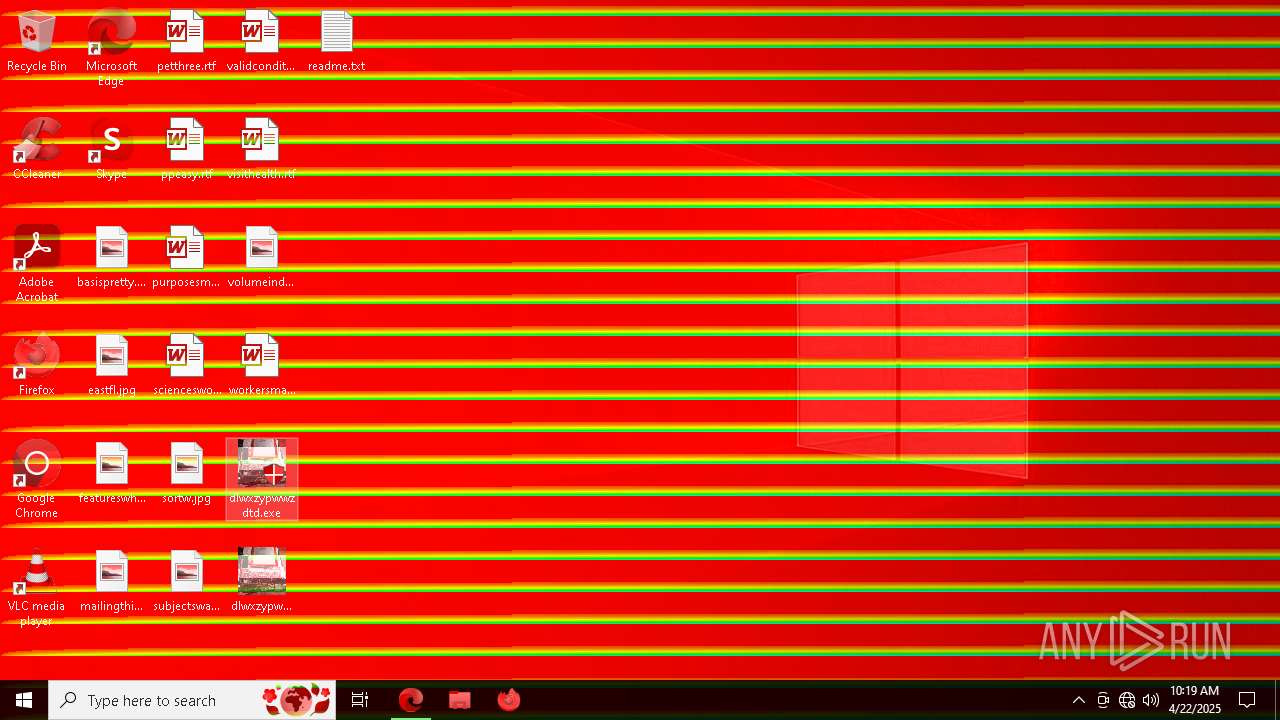
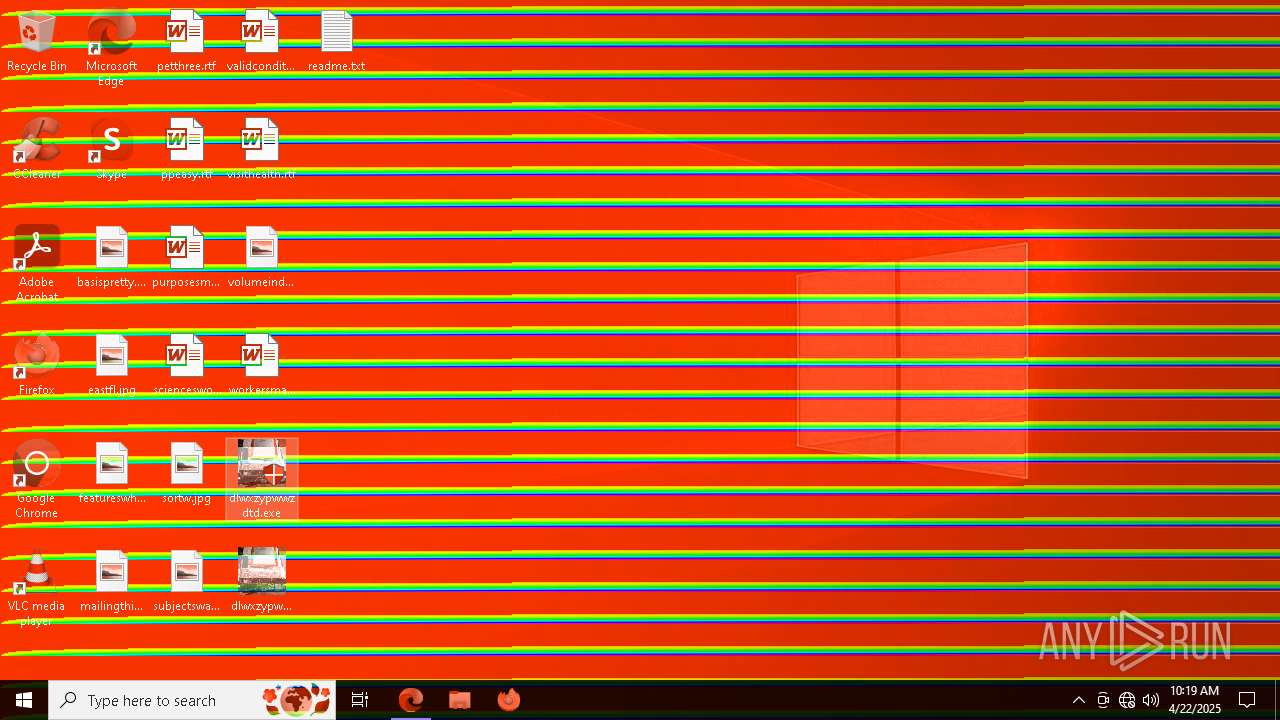
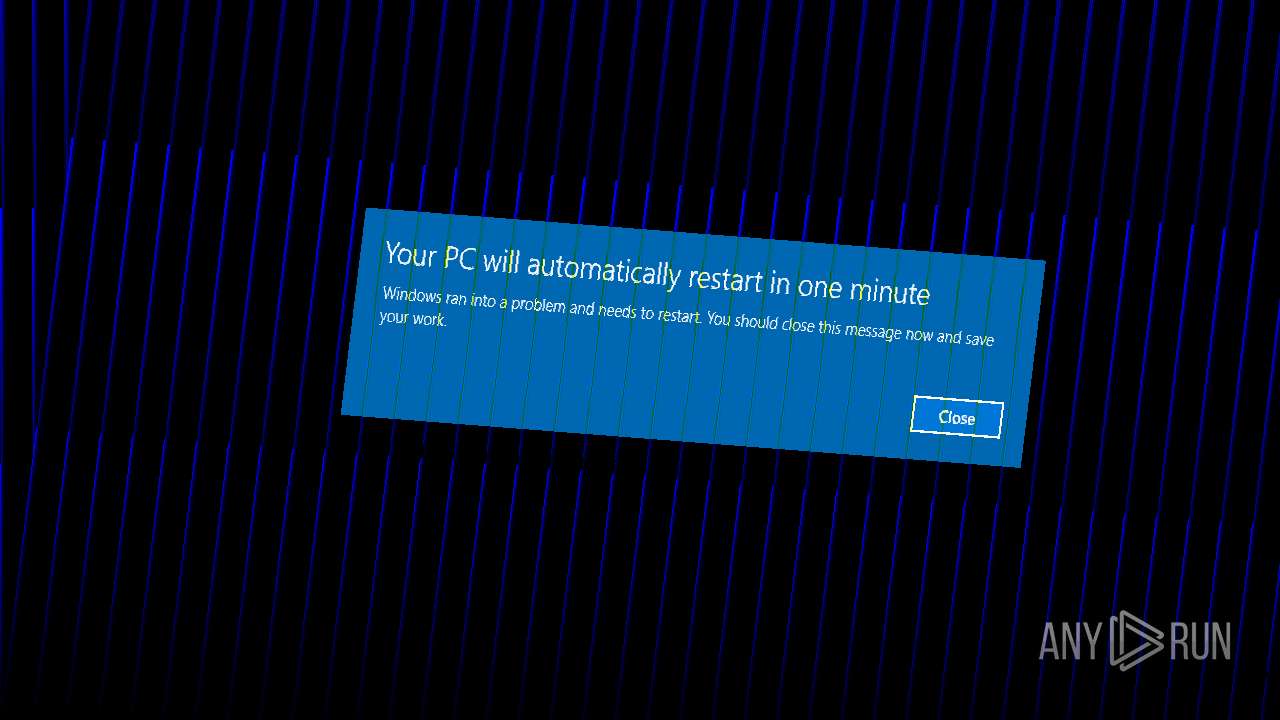
MALICIOUS
Disables task manager
- reg.exe (PID: 3300)
Disables the Run the Start menu
- reg.exe (PID: 7916)
Disables the LogOff the Start menu
- reg.exe (PID: 8944)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 5204)
- cmd.exe (PID: 7508)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8076)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 3800)
Starts CMD.EXE for commands execution
- dlwxzypwwzdtd.exe (PID: 3976)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 976)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 6300)
There is functionality for taking screenshot (YARA)
- dlwxzypwwzdtd.exe (PID: 3976)
INFO
Checks supported languages
- identity_helper.exe (PID: 5404)
- dlwxzypwwzdtd.exe (PID: 3976)
Reads Environment values
- identity_helper.exe (PID: 5404)
Application launched itself
- msedge.exe (PID: 6808)
Reads the computer name
- identity_helper.exe (PID: 5404)
- dlwxzypwwzdtd.exe (PID: 3976)
Reads the software policy settings
- slui.exe (PID: 3768)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6808)
Disables trace logs
- explorer.exe (PID: 8956)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 8956)
Reads security settings of Internet Explorer
- explorer.exe (PID: 8956)
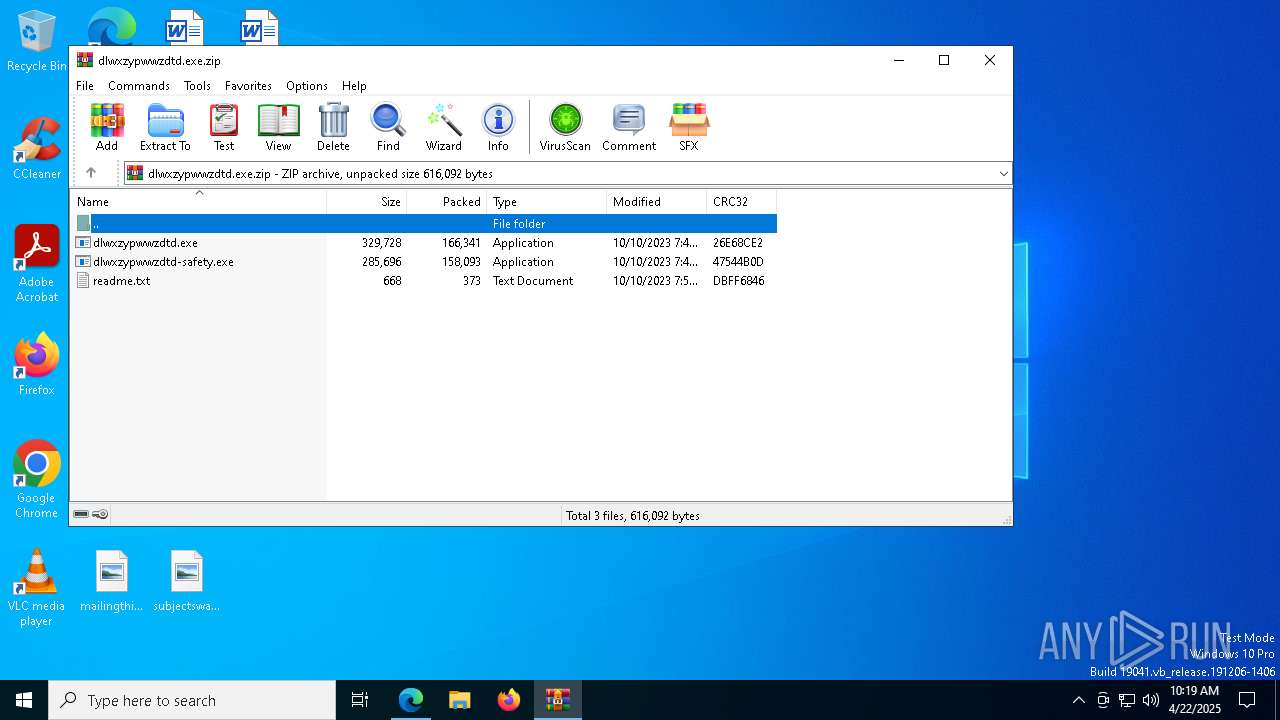
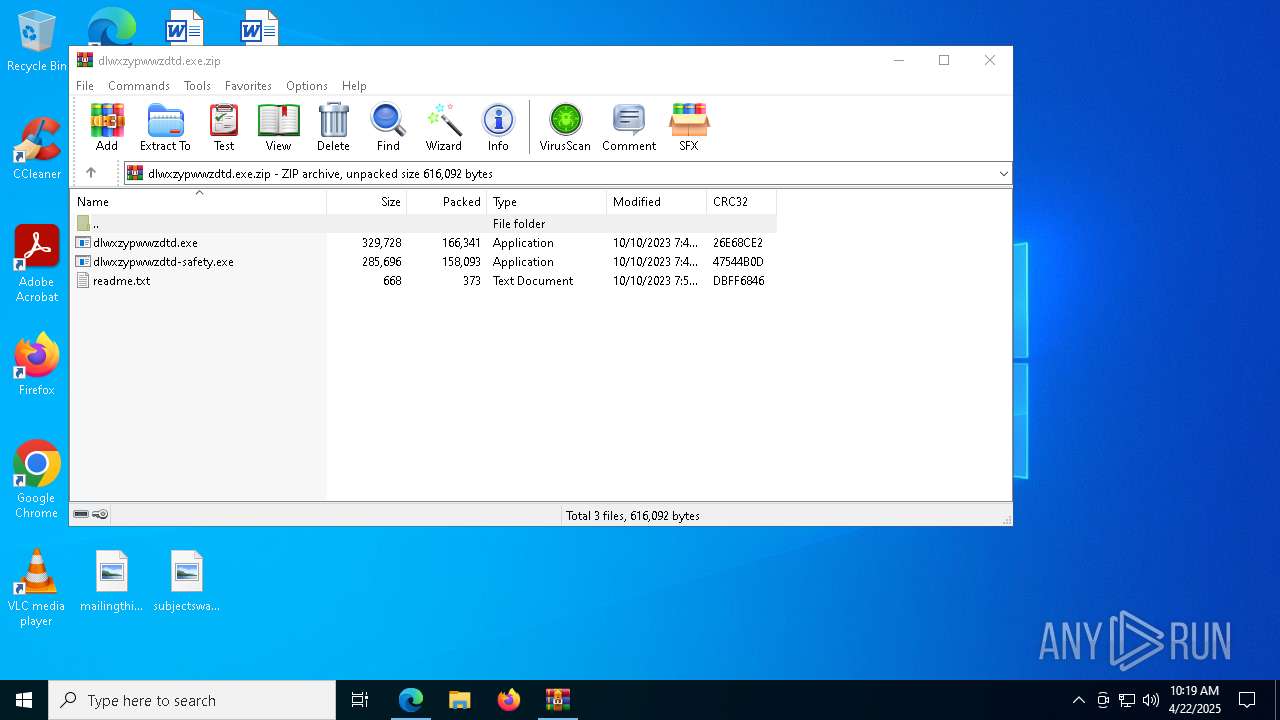
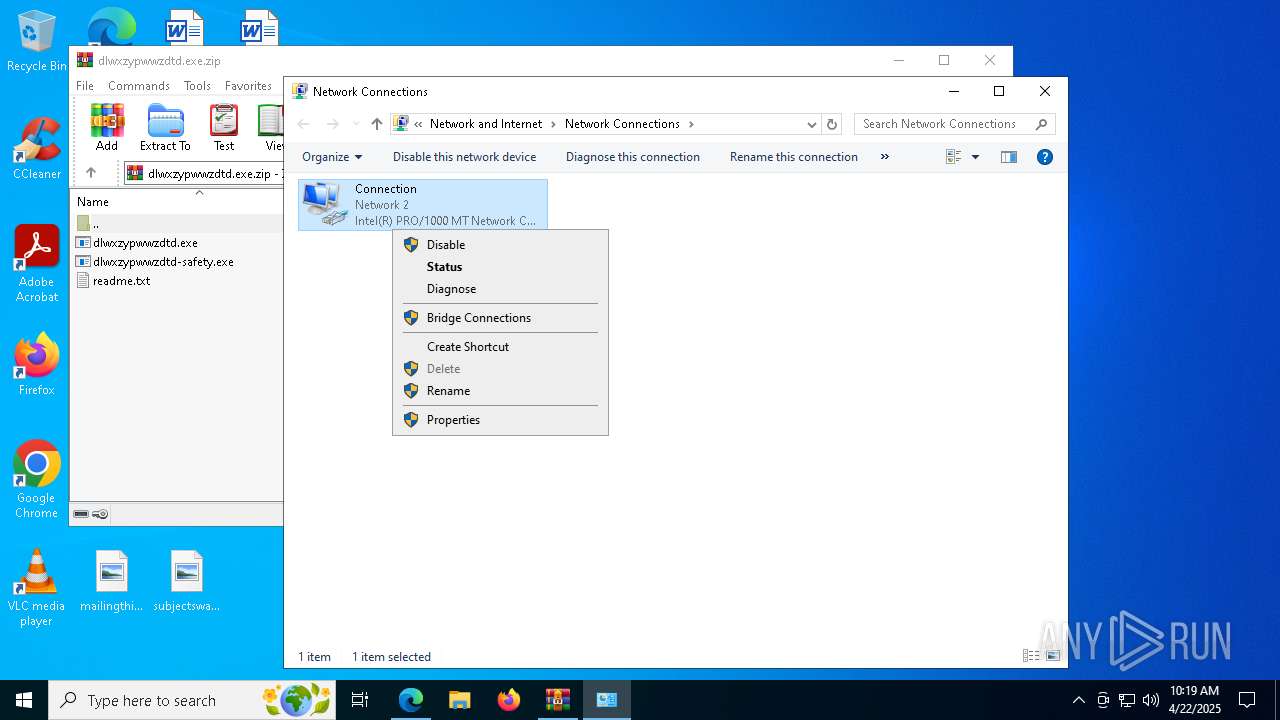
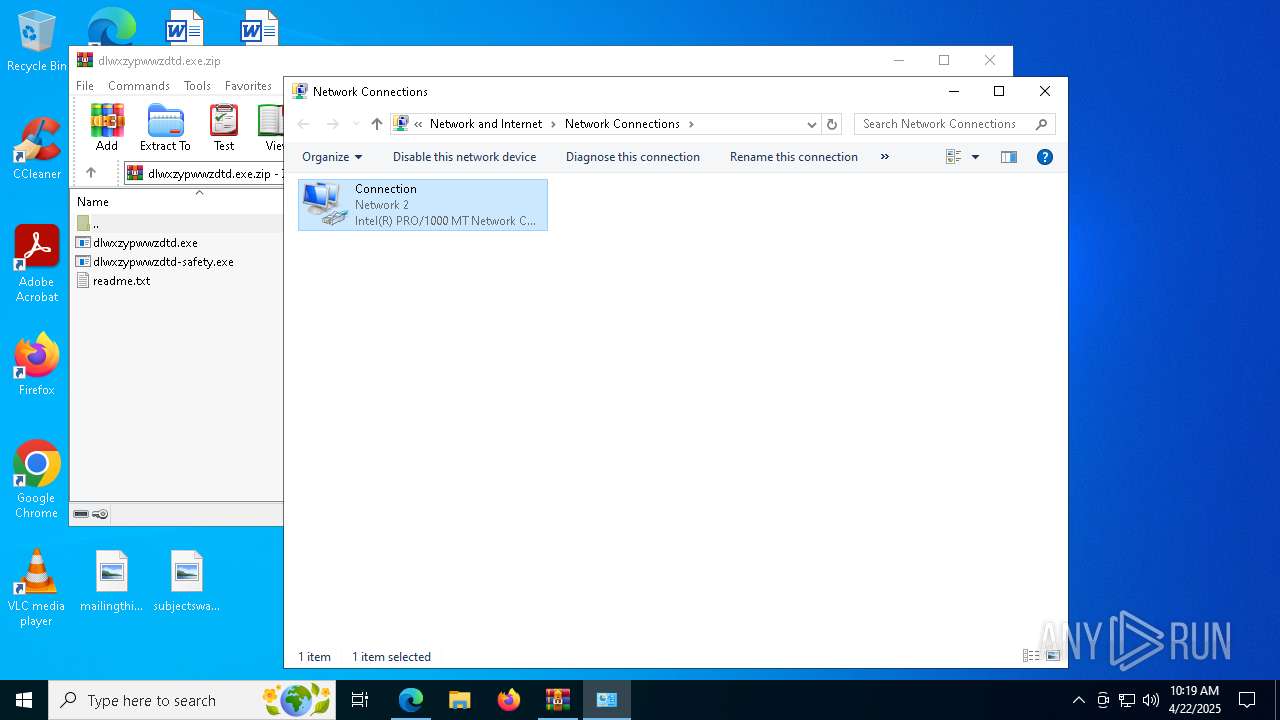
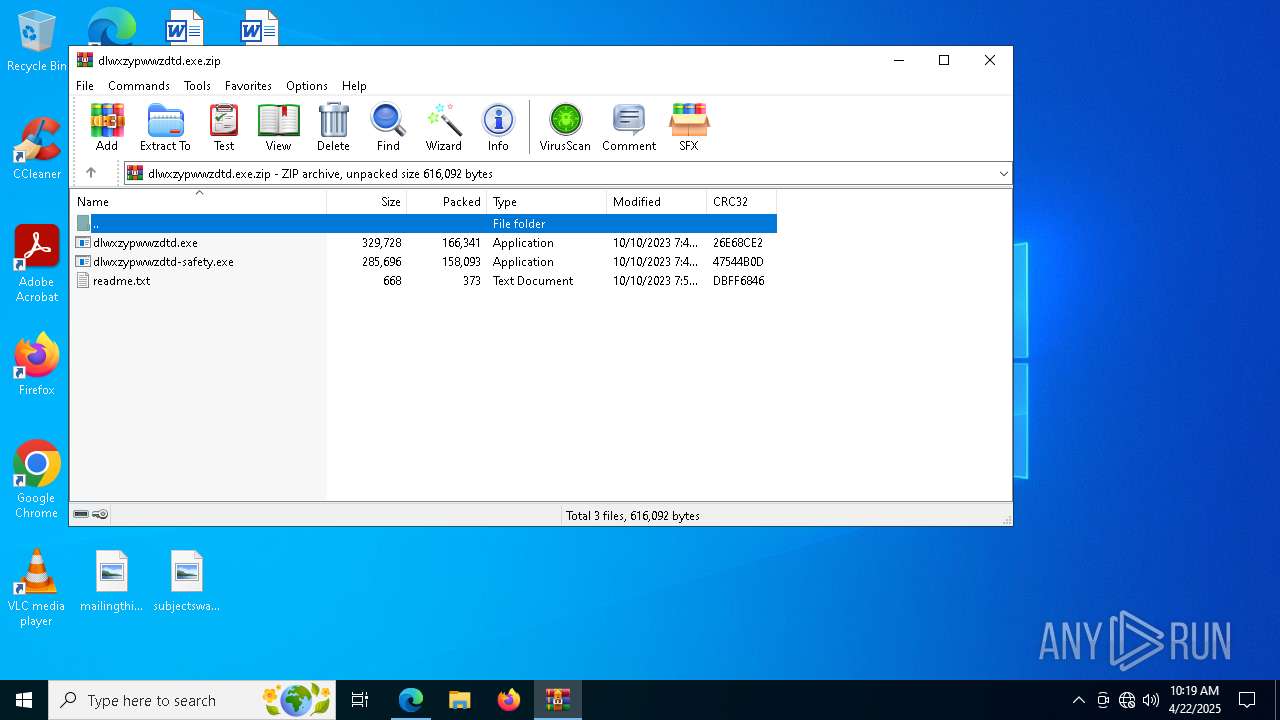
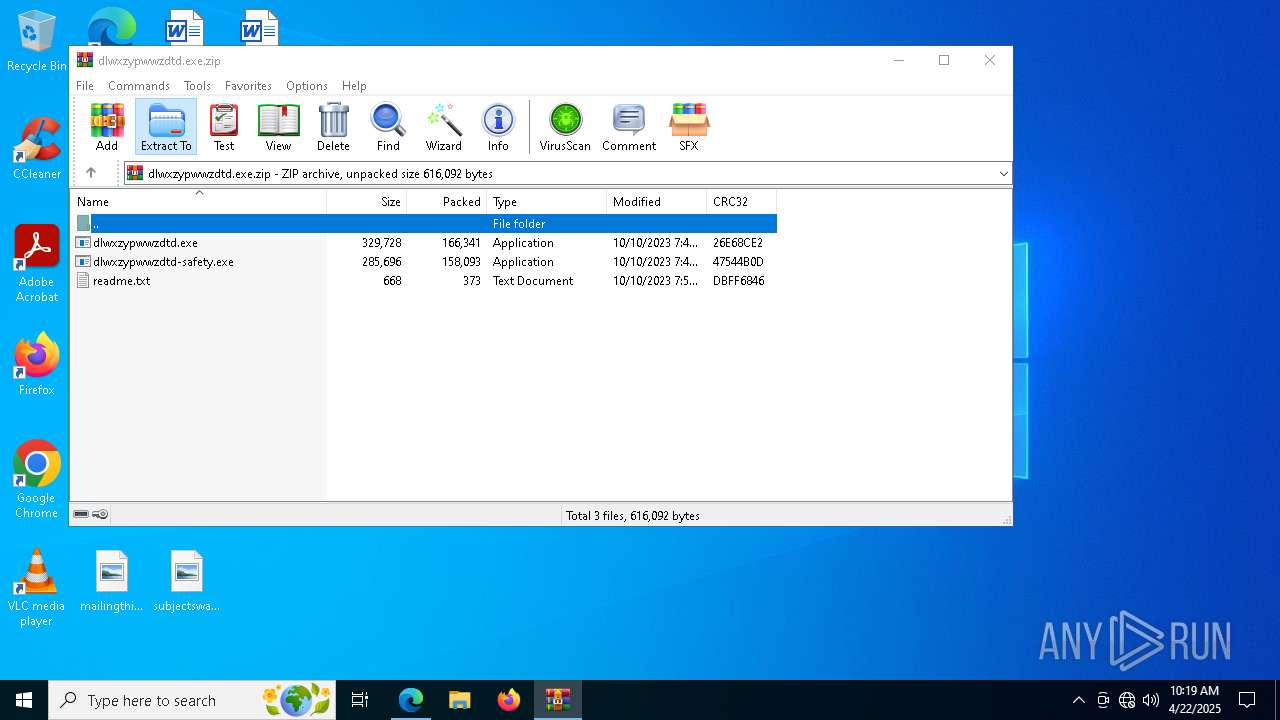
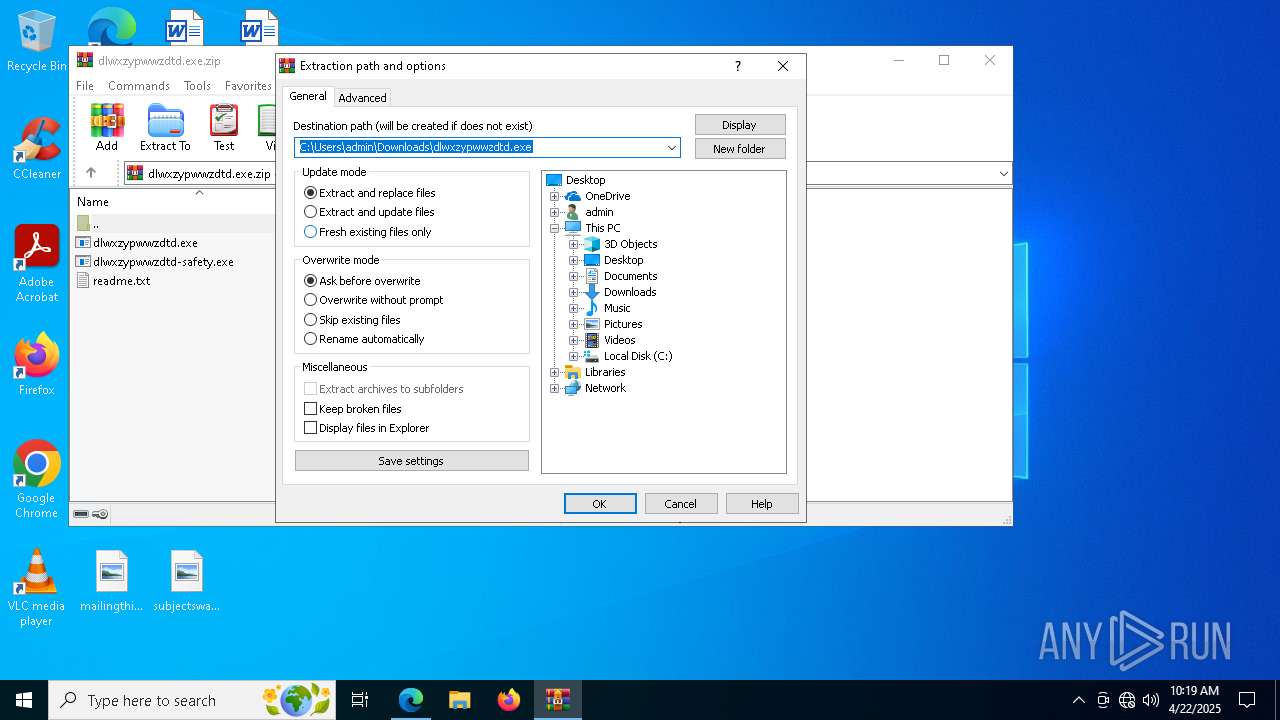
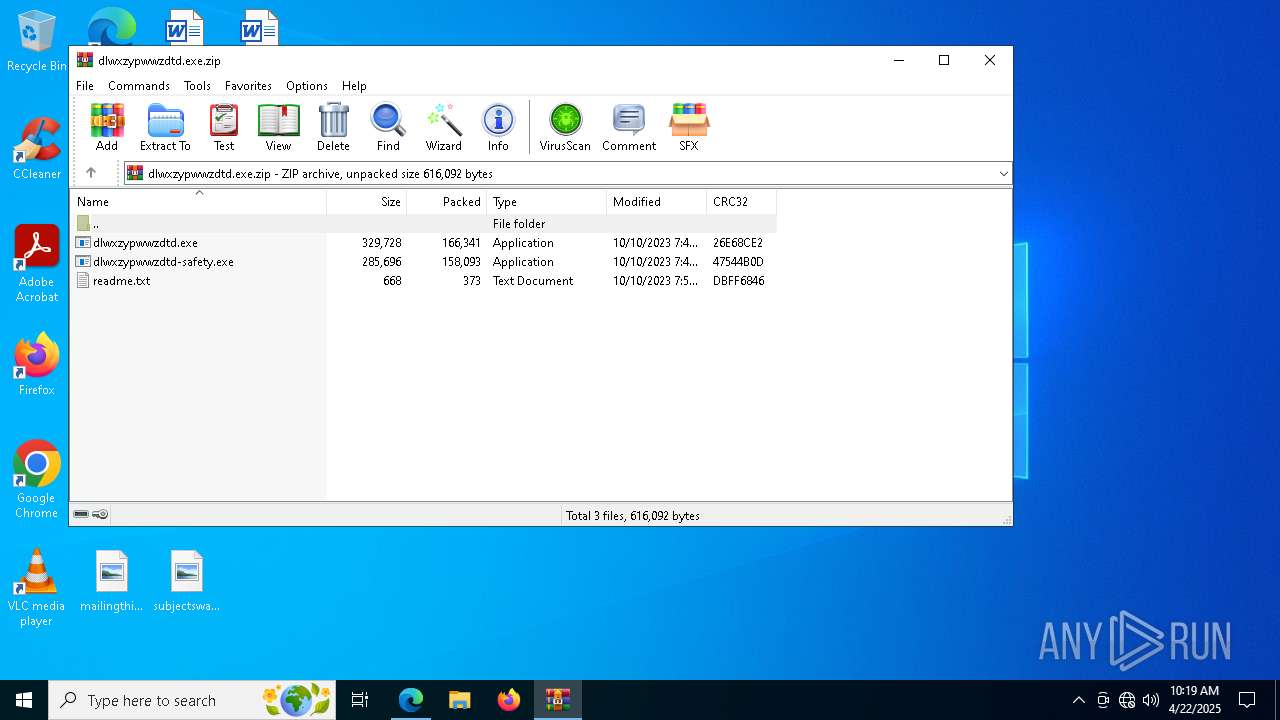
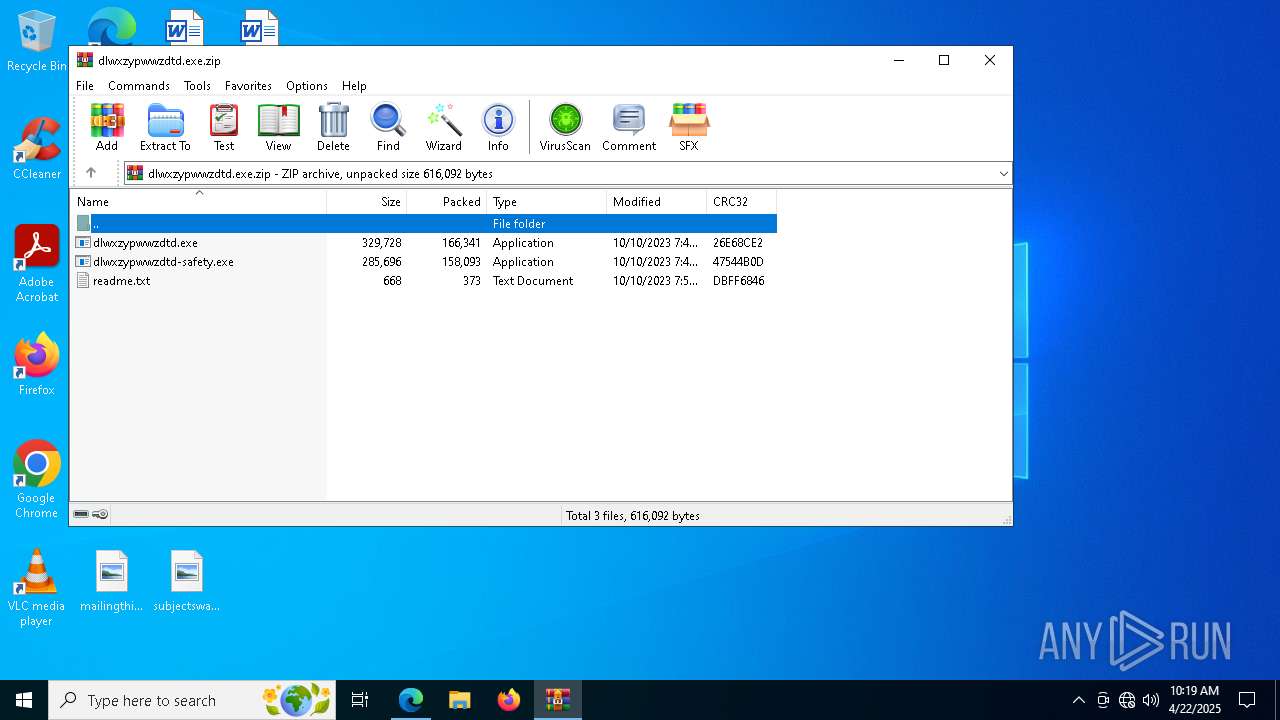
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9156)
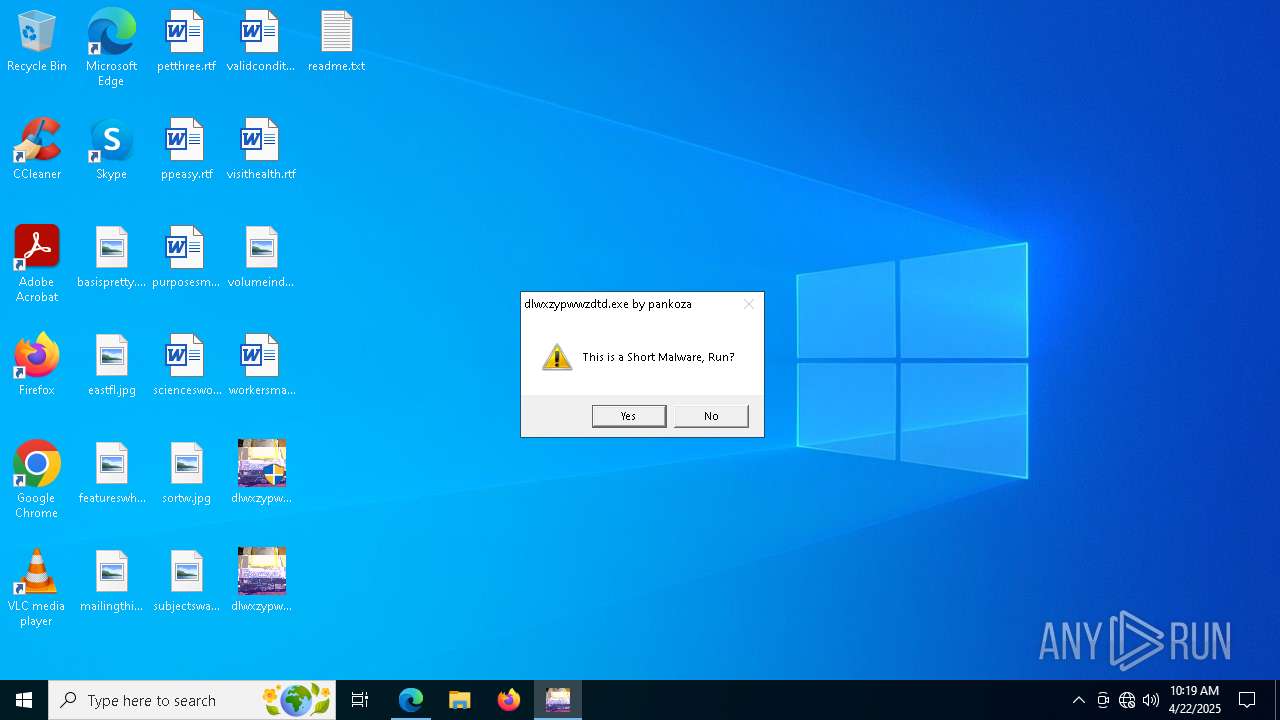
Manual execution by a user
- dlwxzypwwzdtd.exe (PID: 1760)
- dlwxzypwwzdtd.exe (PID: 3976)
Checks proxy server information
- slui.exe (PID: 7688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
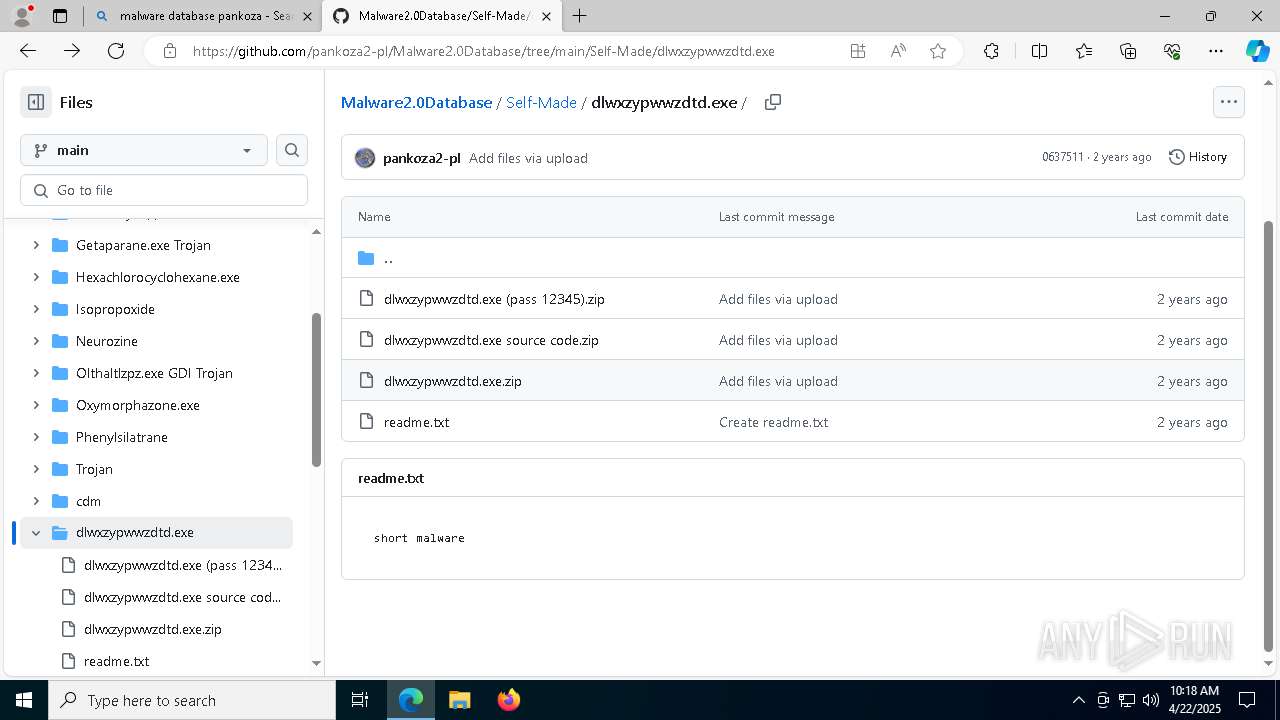
Total processes
241
Monitored processes
103
Malicious processes
2
Suspicious processes
1
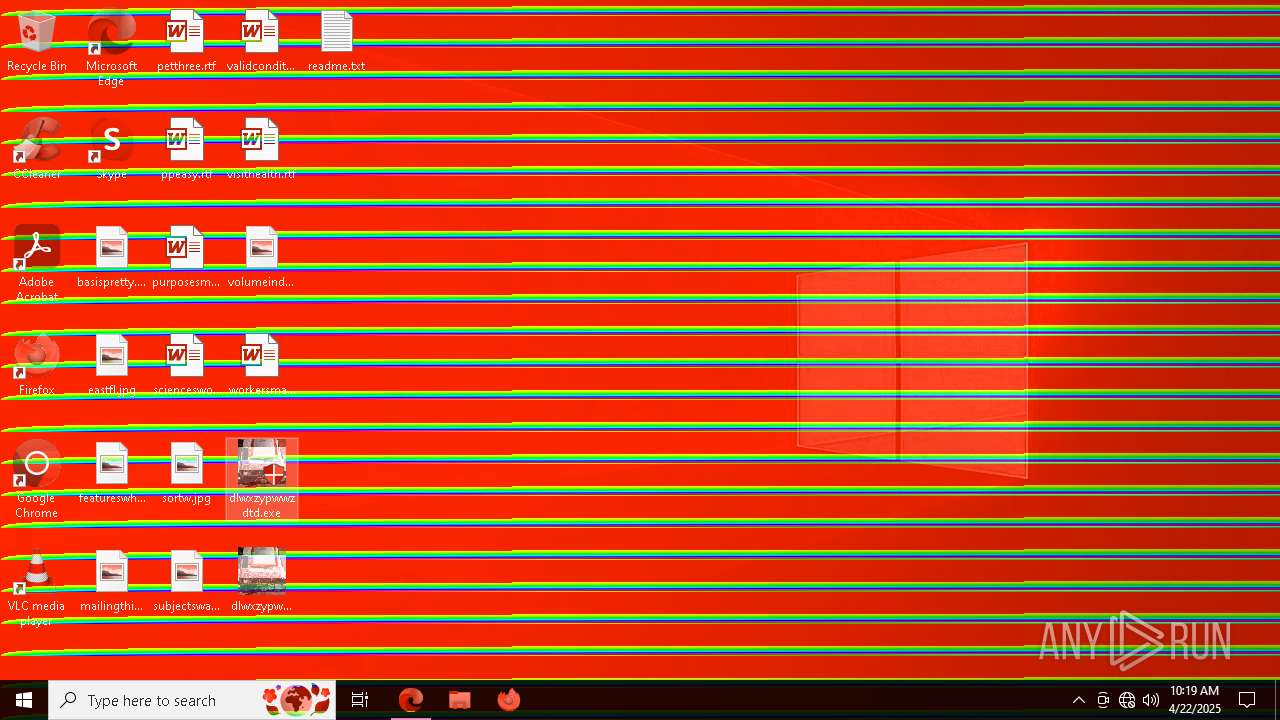
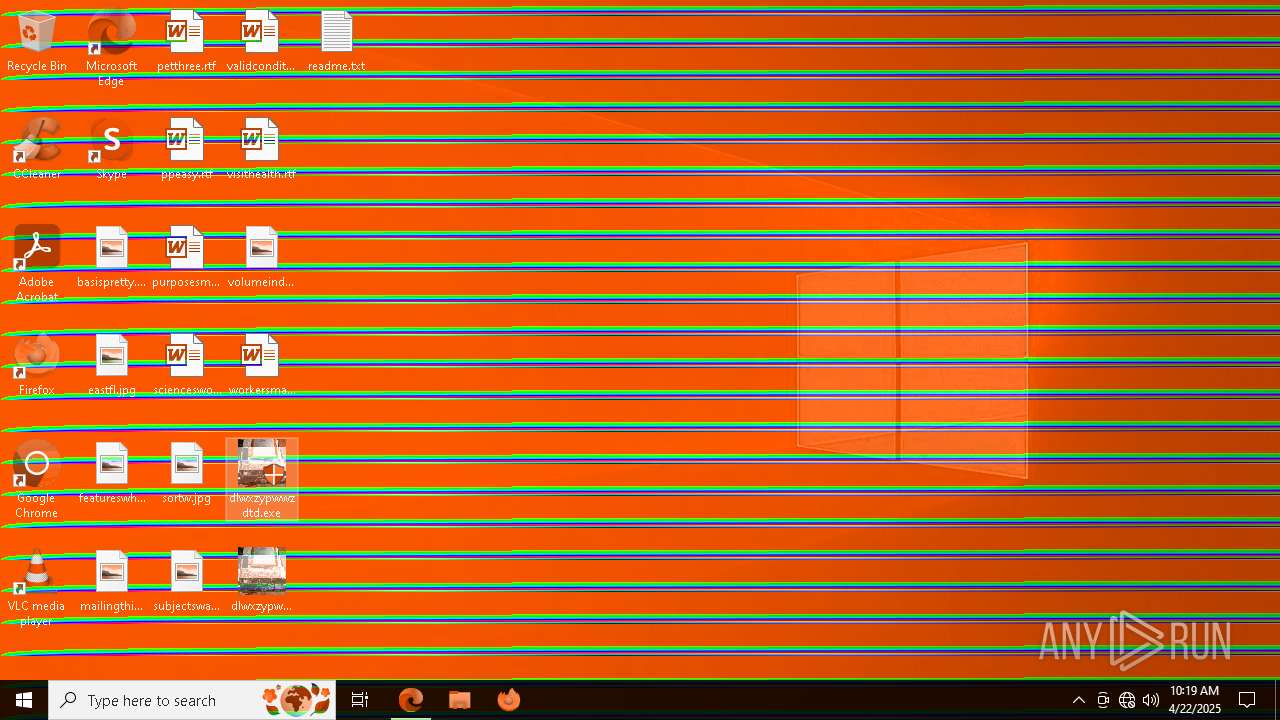
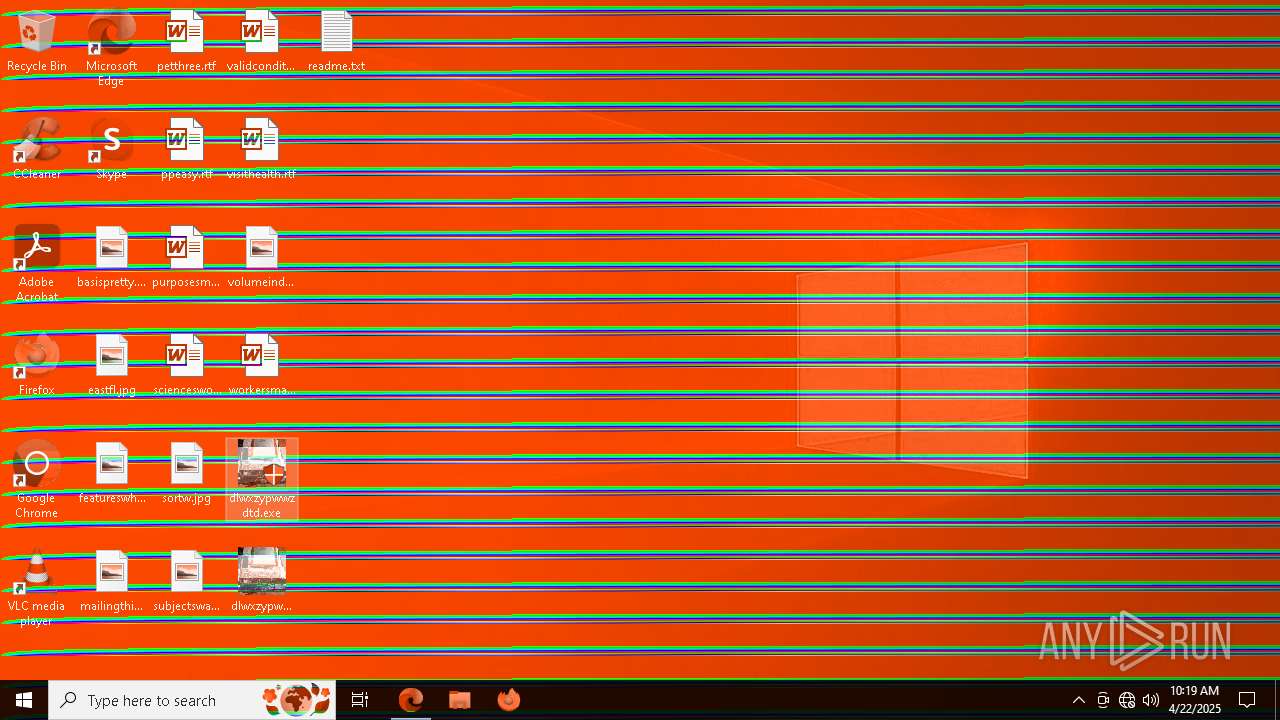
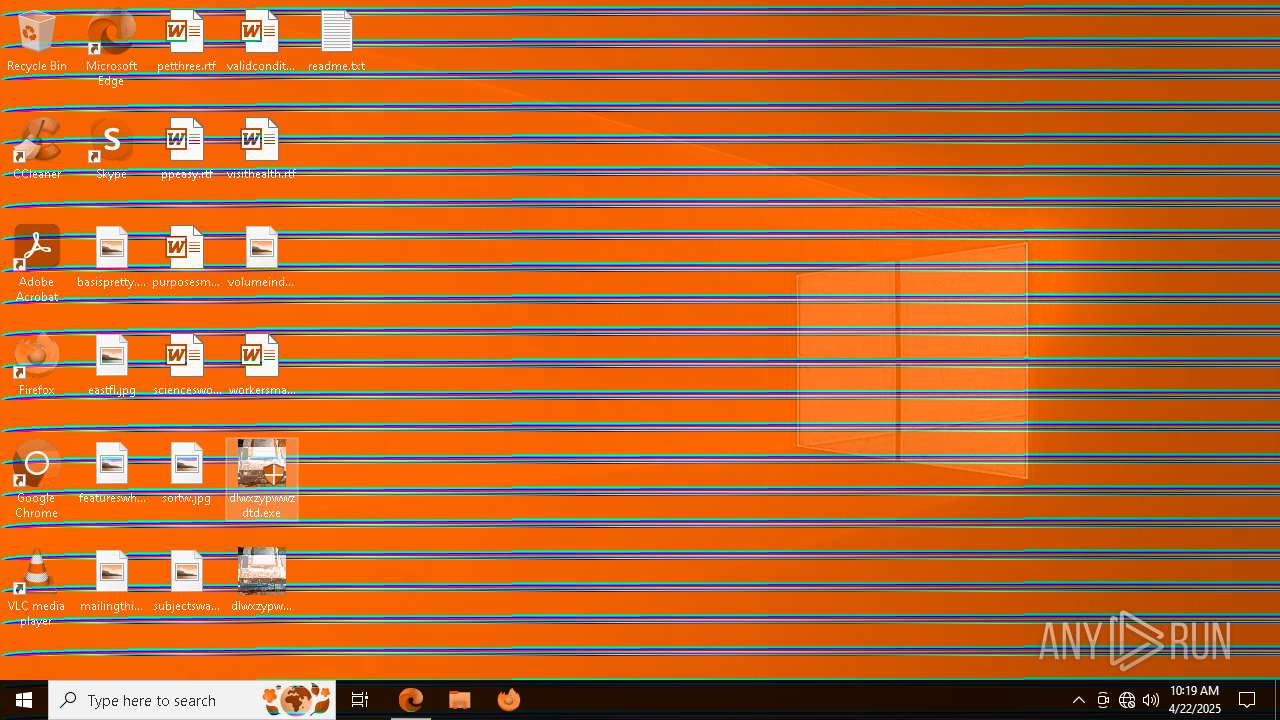
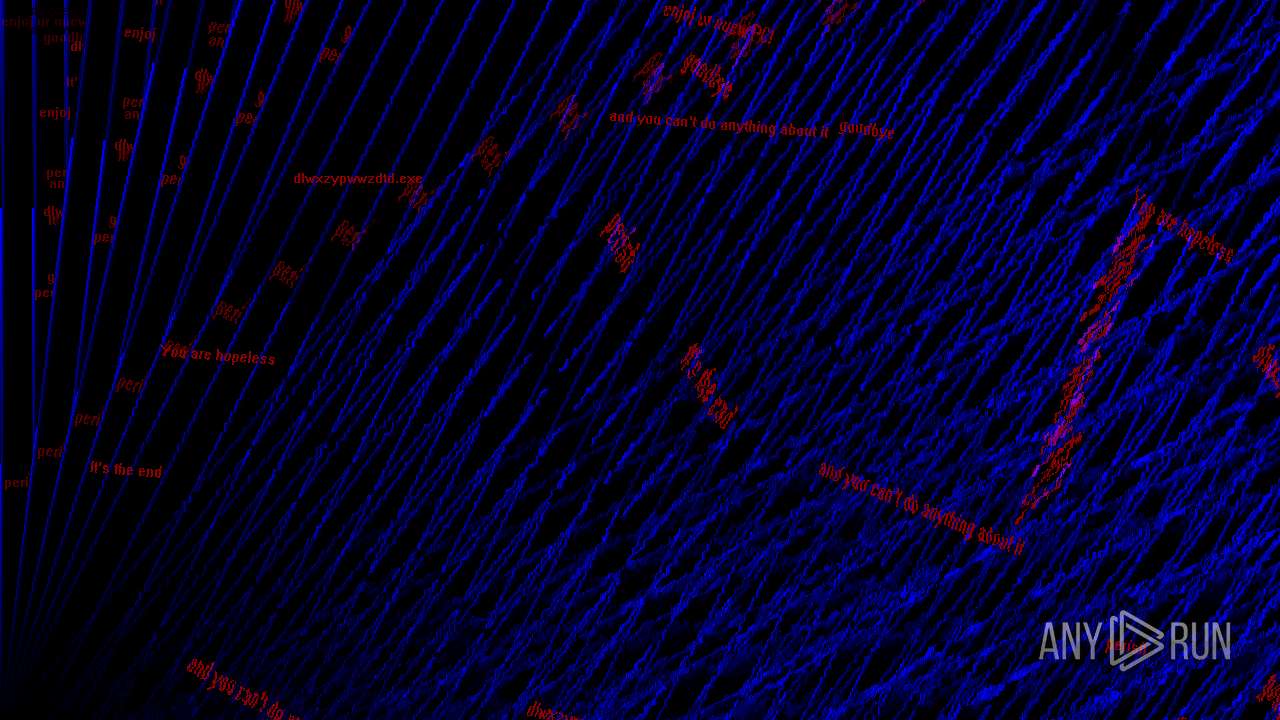
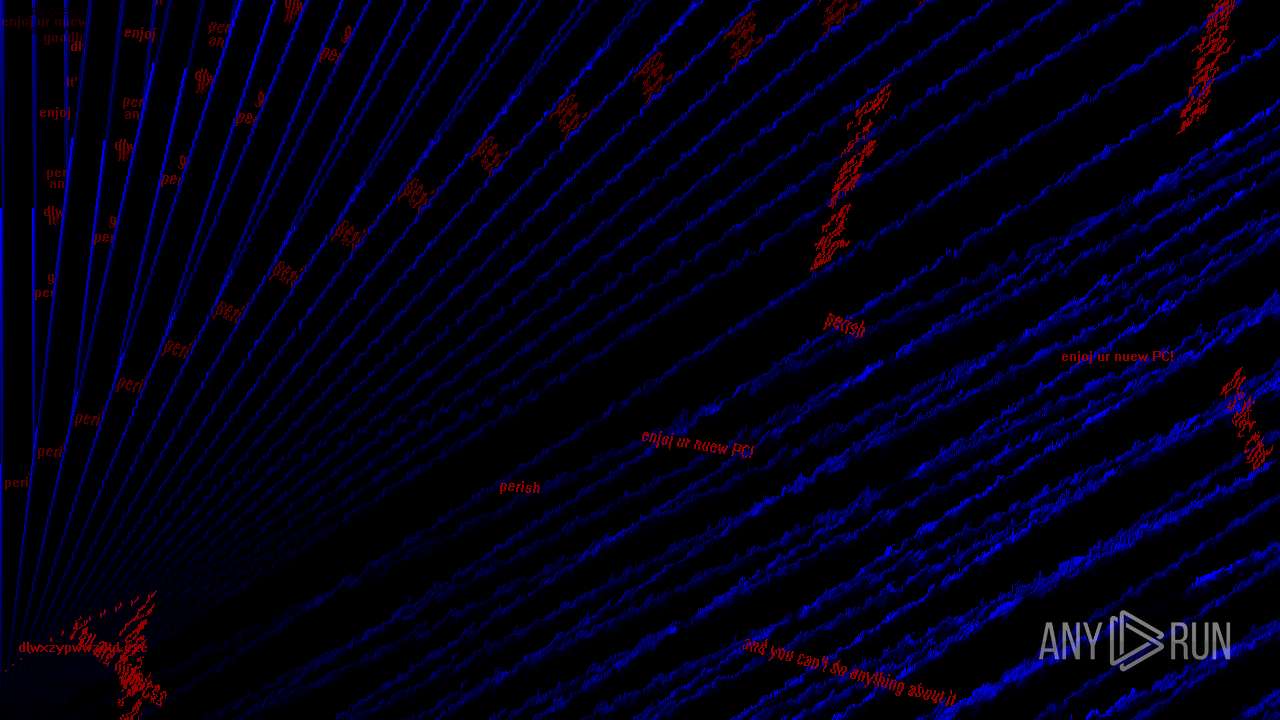
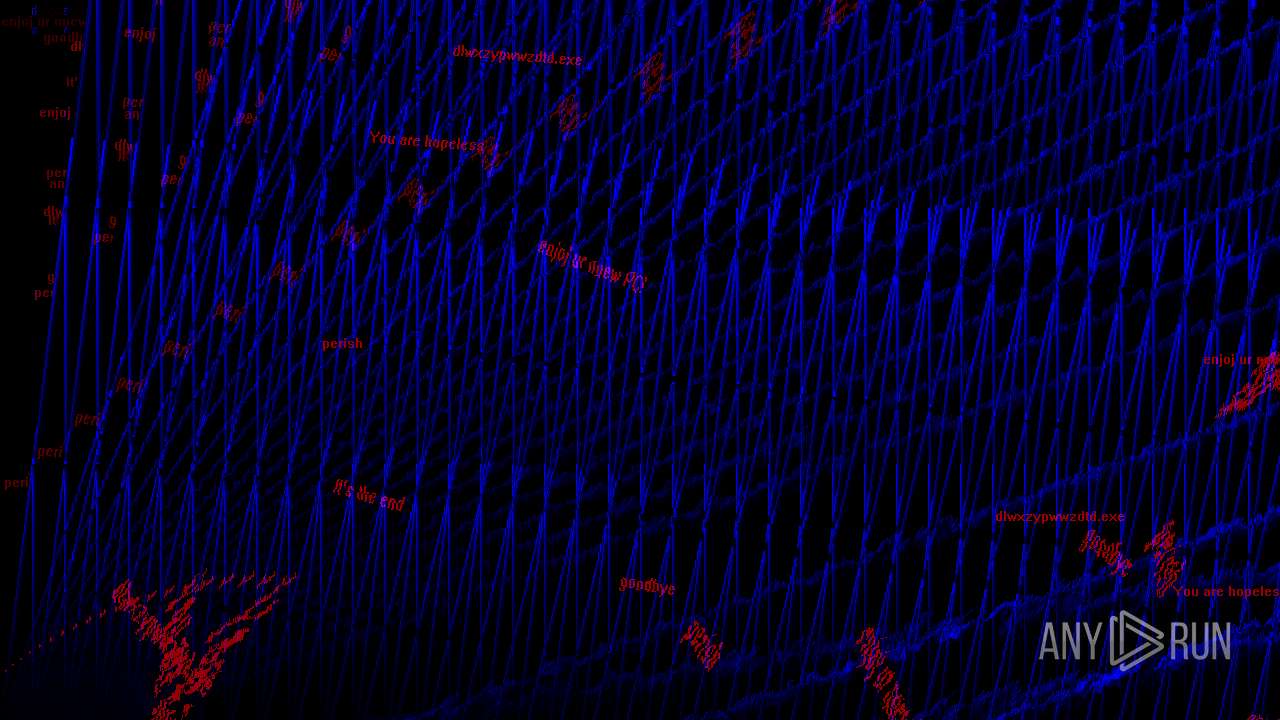
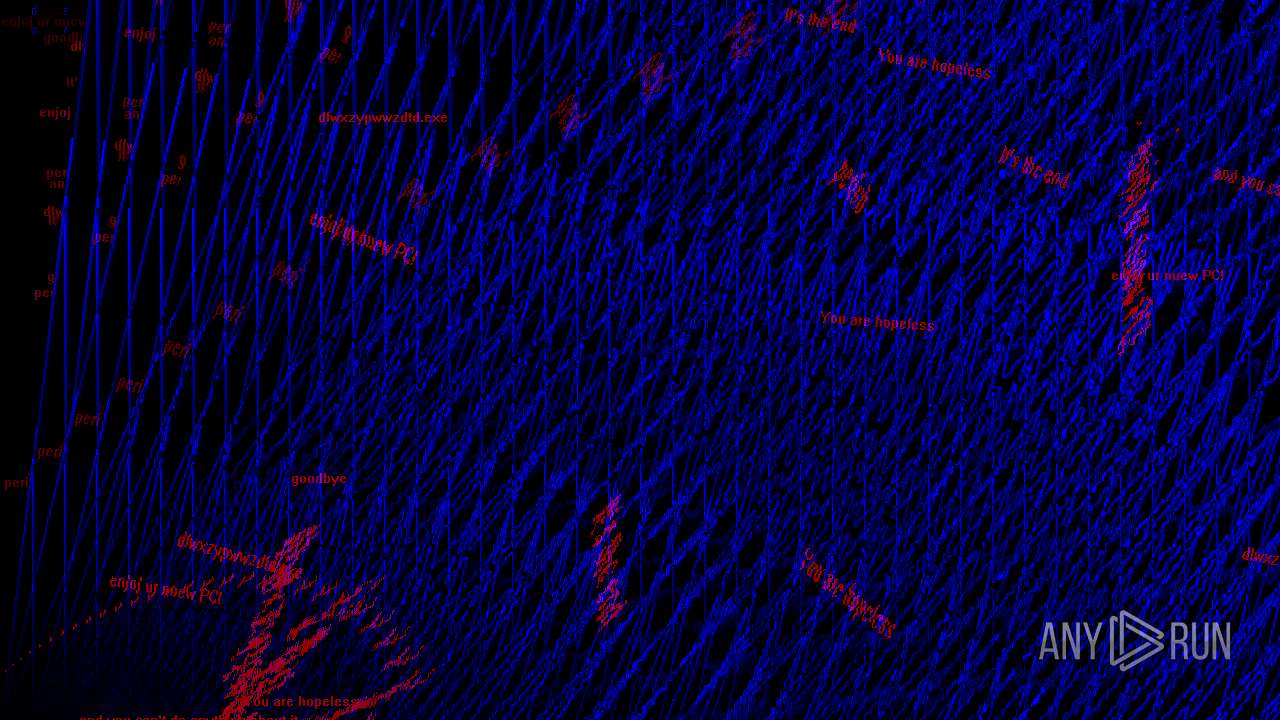
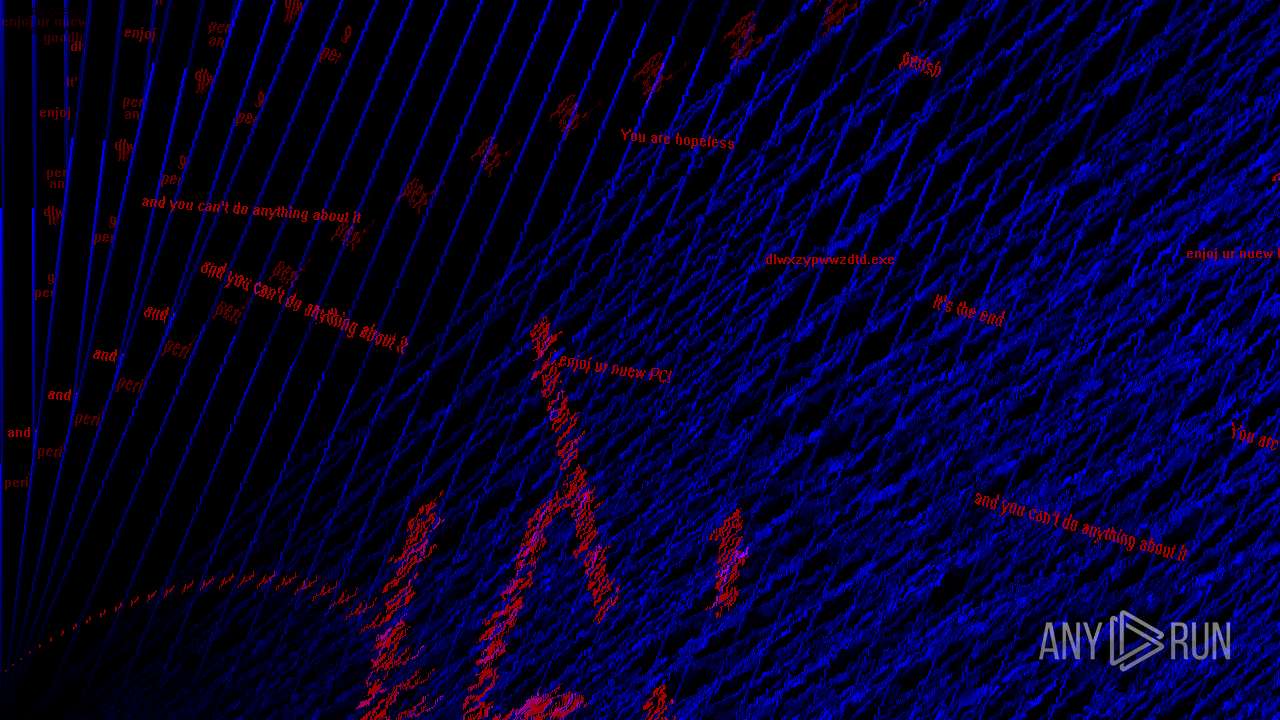
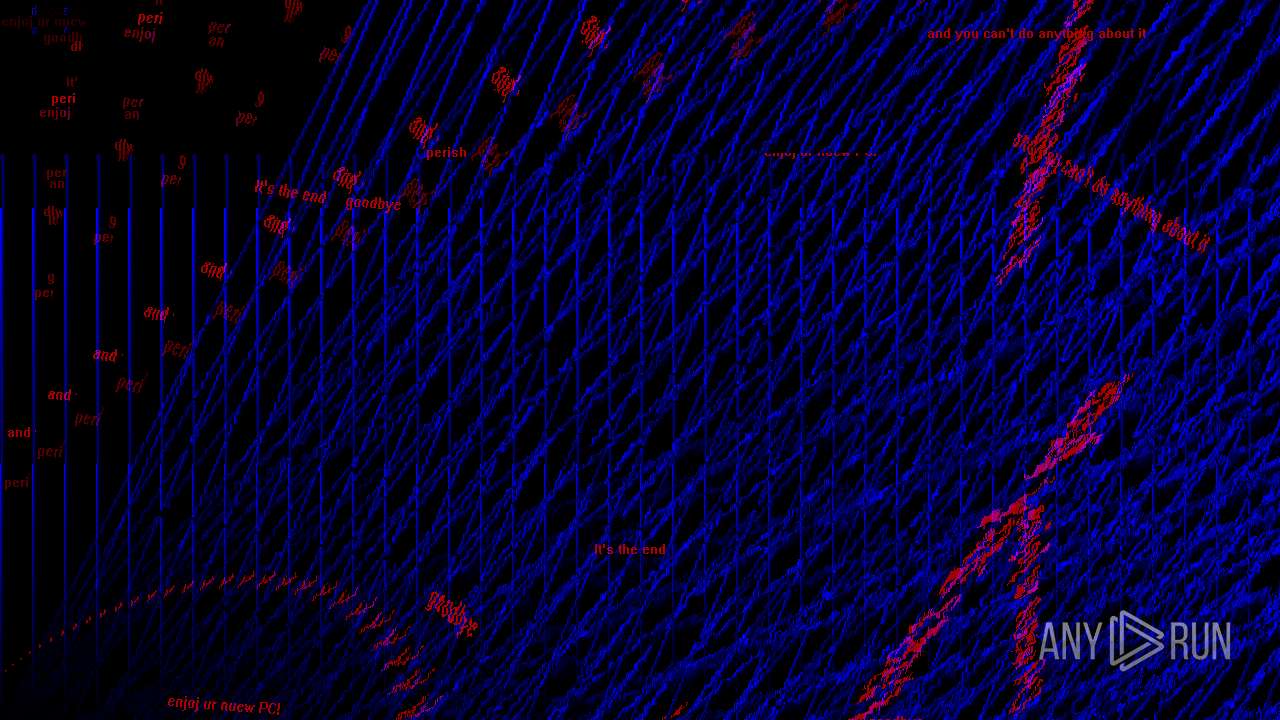
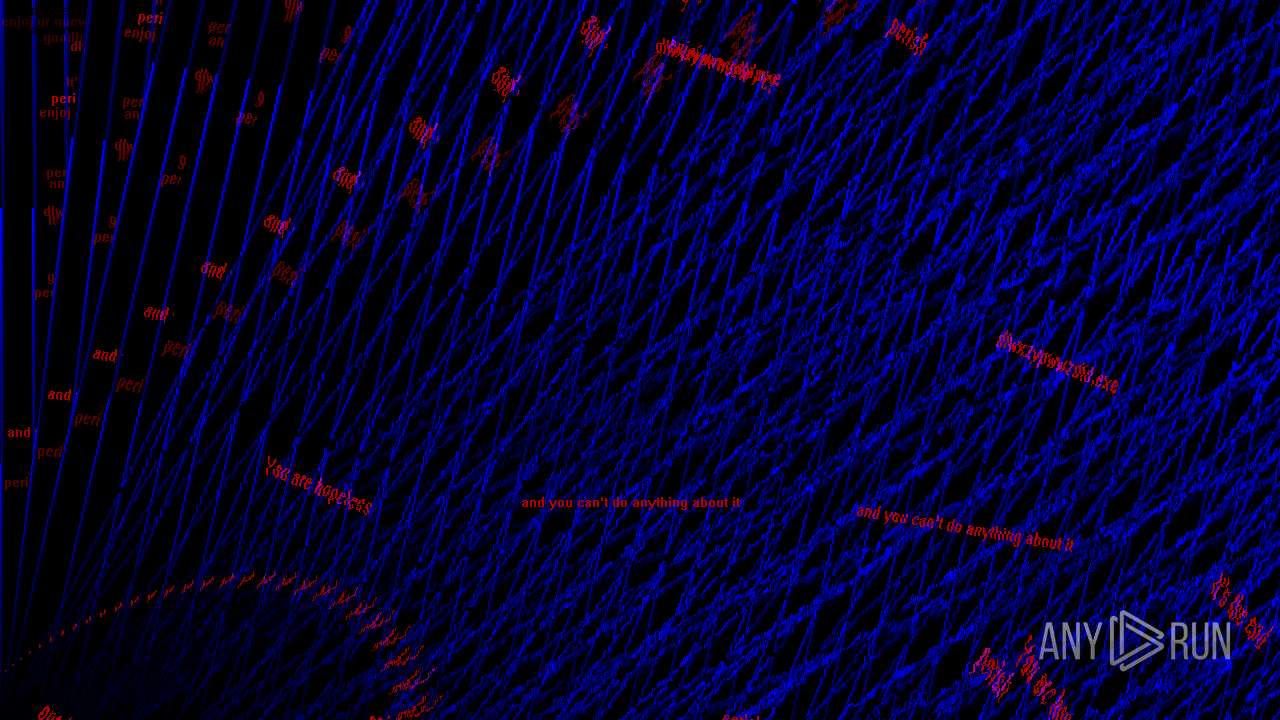
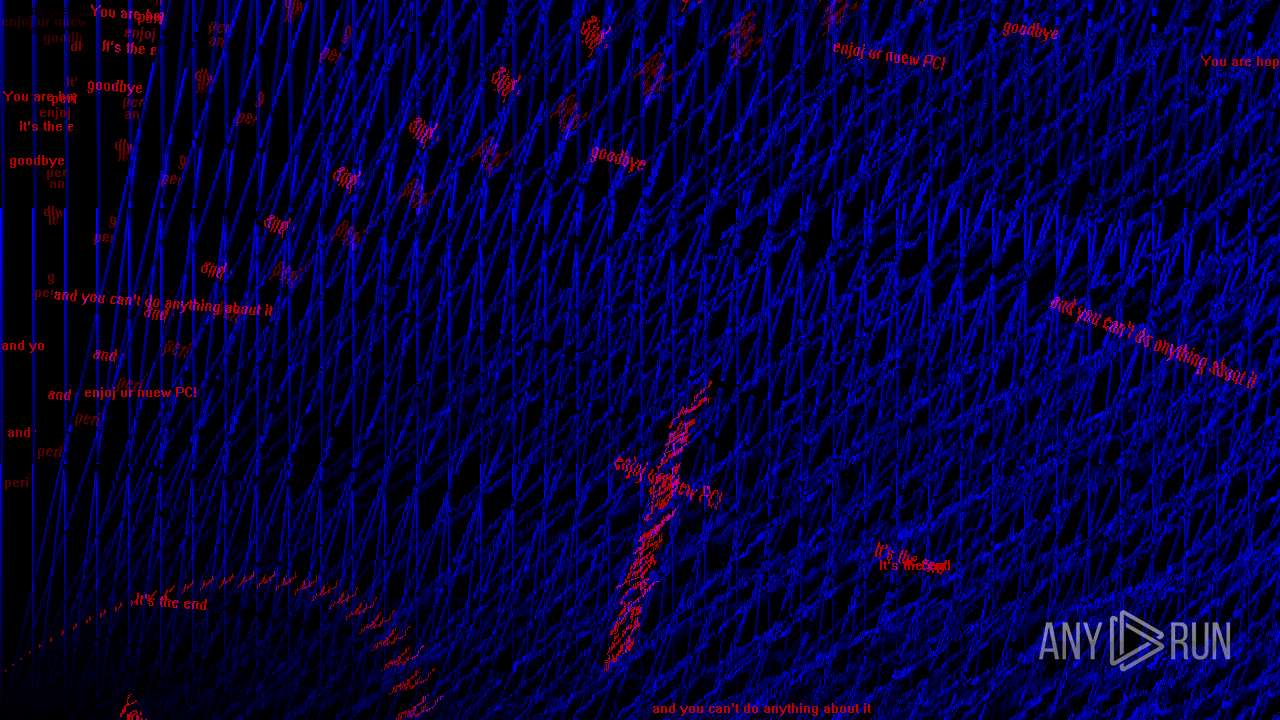
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5344 --field-trial-handle=2384,i,3248149229277465542,12875132098596546601,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | C:\WINDOWS\system32\cmd.exe /c reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer /v NoLogoff /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | dlwxzypwwzdtd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableLockWorkstation /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5744 --field-trial-handle=2384,i,3248149229277465542,12875132098596546601,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6648 --field-trial-handle=2384,i,3248149229277465542,12875132098596546601,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
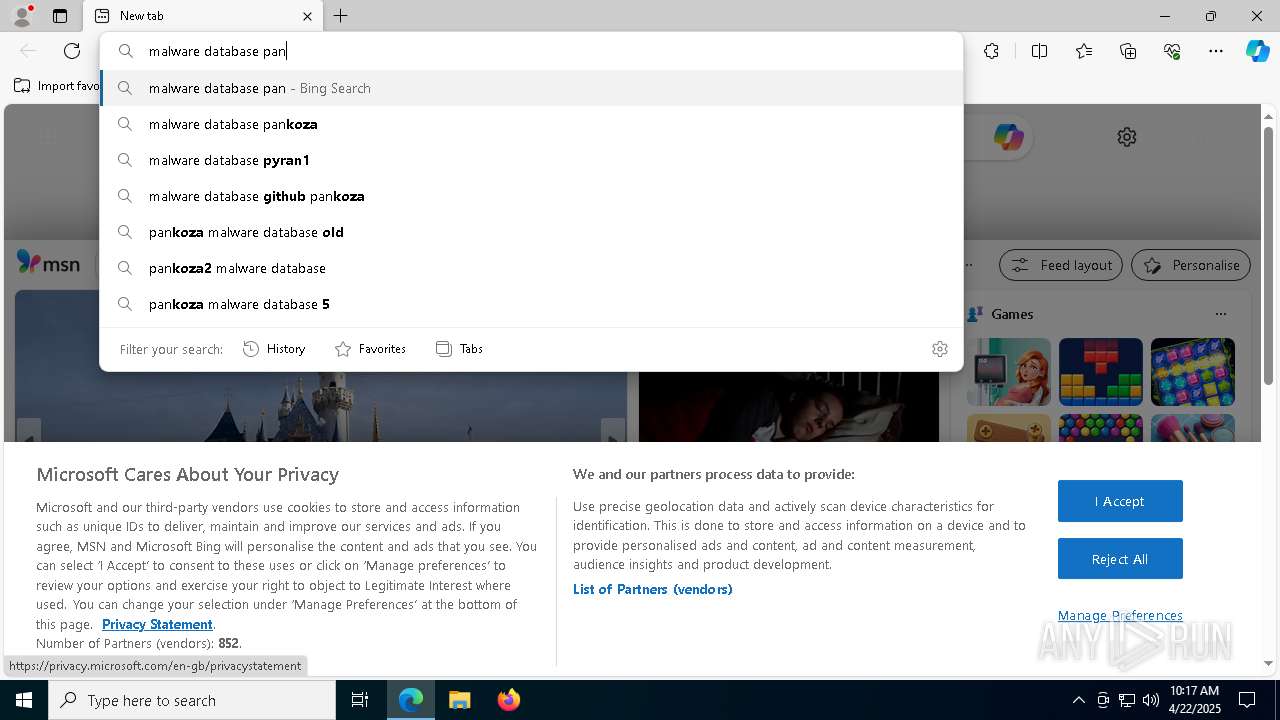
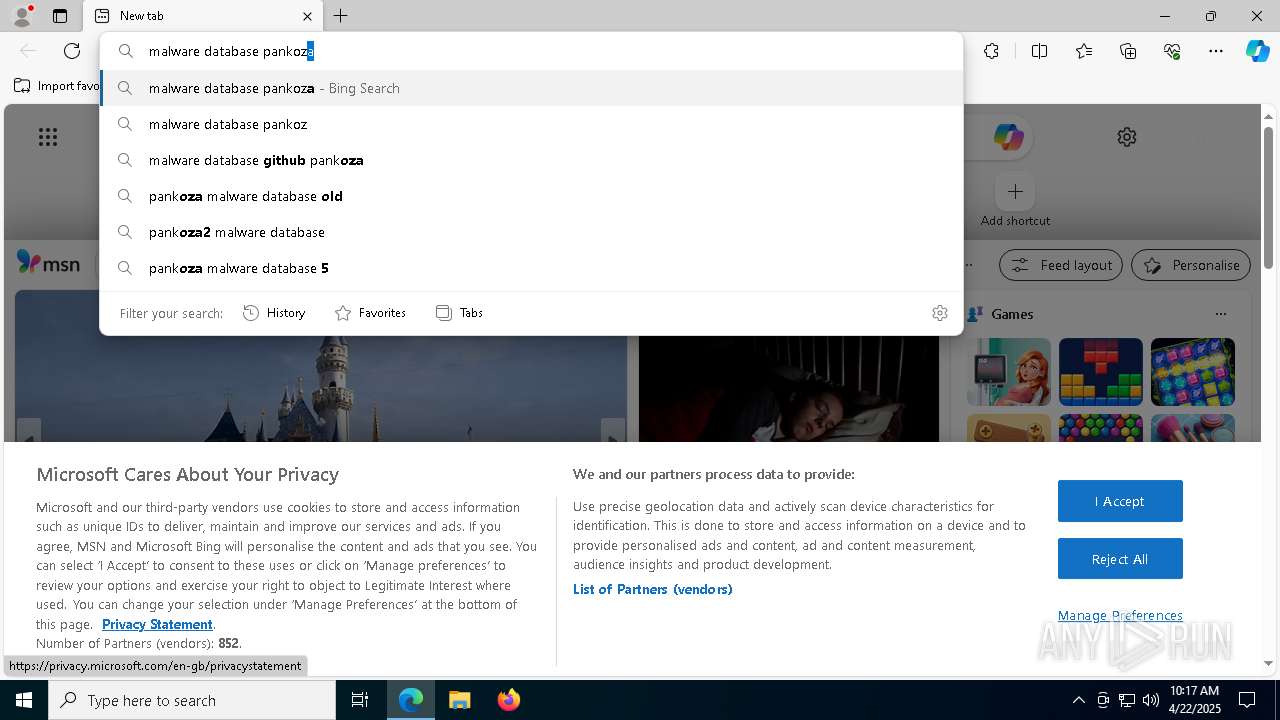
| 1760 | "C:\Users\admin\Desktop\dlwxzypwwzdtd.exe" | C:\Users\admin\Desktop\dlwxzypwwzdtd.exe | — | explorer.exe | |||||||||||
User: admin Company: pan koza 2 Integrity Level: MEDIUM Description: Free GTA VI Leaked Exit code: 3221226540 Version: 6.6.6.6 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7568 --field-trial-handle=2384,i,3248149229277465542,12875132098596546601,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
13 082
Read events
12 940
Write events
128
Delete events
14
Modification events
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 30F89193F1912F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6BDD1A5D-5D88-470E-A624-5666209CBB42} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A89CC6F6-CB25-47E6-8373-66E57395EA4D} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8E640671-AA72-4096-977A-04BCC701BBE5} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 686B7093F1912F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6BA311D4-D3EA-4E12-9D7D-E765A593DB72} | |||
Executable files
41
Suspicious files
749
Text files
120
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c1ac.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c1bb.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c1bb.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c7f5.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
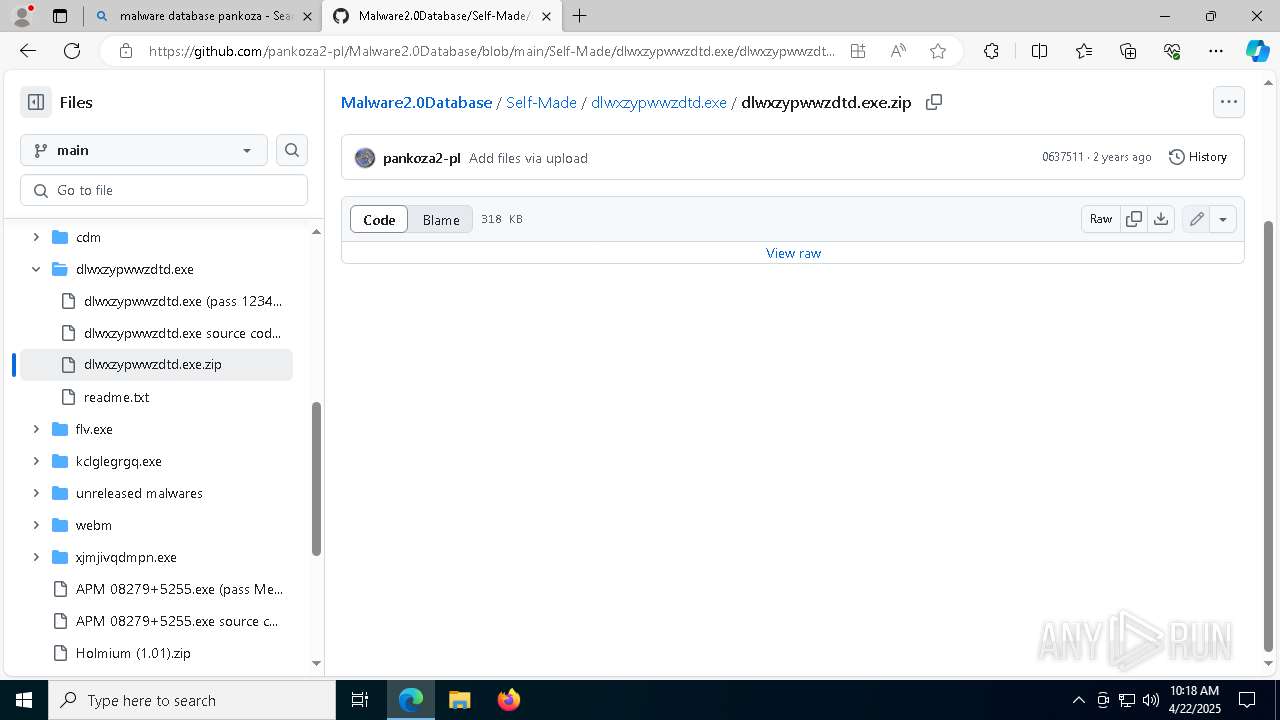
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
153
DNS requests
164
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8152 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745621491&P2=404&P3=2&P4=GGAkBkh4vO1ymkZ%2bz5cD5QDdV0Zpor6MJdhW2PLsLEu161zMkDUSJwUbr7VSybOpP63xLbwlUyeW4BERRXYkiw%3d%3d | unknown | — | — | whitelisted |
8152 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745621491&P2=404&P3=2&P4=GGAkBkh4vO1ymkZ%2bz5cD5QDdV0Zpor6MJdhW2PLsLEu161zMkDUSJwUbr7VSybOpP63xLbwlUyeW4BERRXYkiw%3d%3d | unknown | — | — | whitelisted |
8152 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745621491&P2=404&P3=2&P4=GGAkBkh4vO1ymkZ%2bz5cD5QDdV0Zpor6MJdhW2PLsLEu161zMkDUSJwUbr7VSybOpP63xLbwlUyeW4BERRXYkiw%3d%3d | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8152 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745621491&P2=404&P3=2&P4=GGAkBkh4vO1ymkZ%2bz5cD5QDdV0Zpor6MJdhW2PLsLEu161zMkDUSJwUbr7VSybOpP63xLbwlUyeW4BERRXYkiw%3d%3d | unknown | — | — | whitelisted |
8152 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1745621492&P2=404&P3=2&P4=cKnMxGldZhSlK%2bU9b3Ngncfao%2bRocA%2bBCGZUtjzg35PhmQXQxUKktl8A8C6W7vfkavL4nL%2buW0%2bQNSV9X3lCbg%3d%3d | unknown | — | — | whitelisted |
8152 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1745621492&P2=404&P3=2&P4=cKnMxGldZhSlK%2bU9b3Ngncfao%2bRocA%2bBCGZUtjzg35PhmQXQxUKktl8A8C6W7vfkavL4nL%2buW0%2bQNSV9X3lCbg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
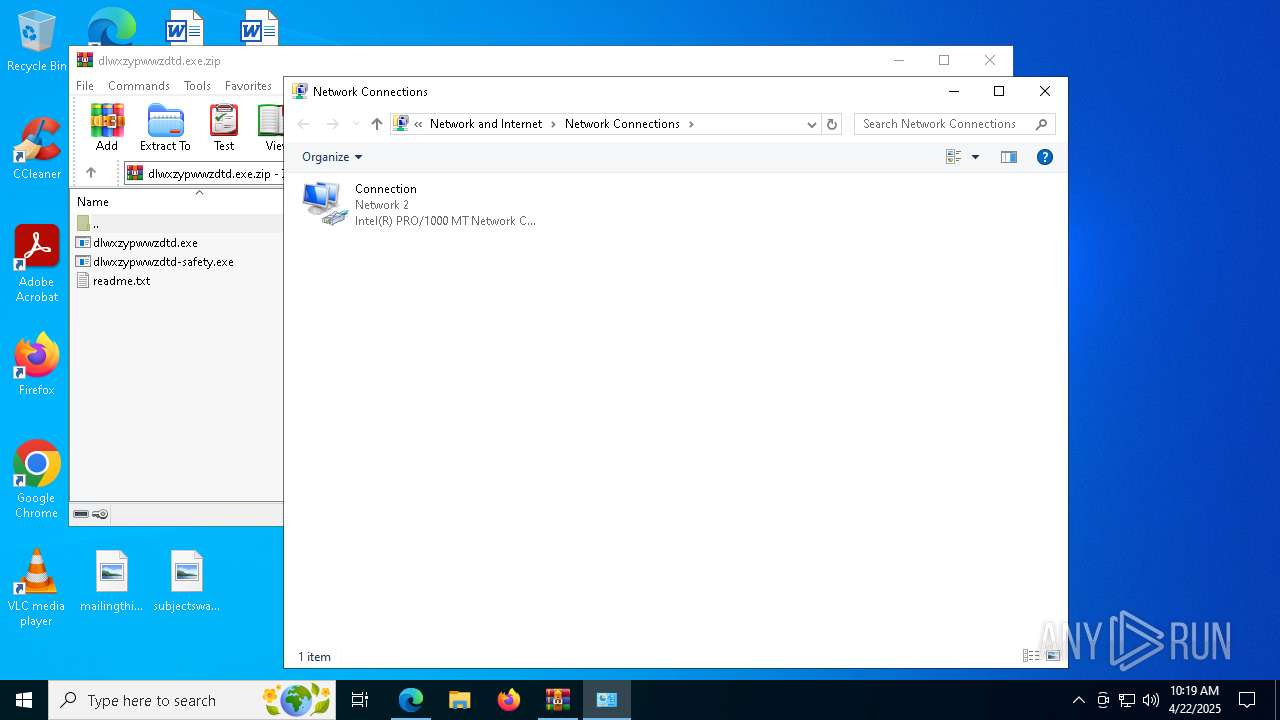
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7304 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6808 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7304 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7304 | msedge.exe | 40.90.65.53:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7304 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pish.me |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
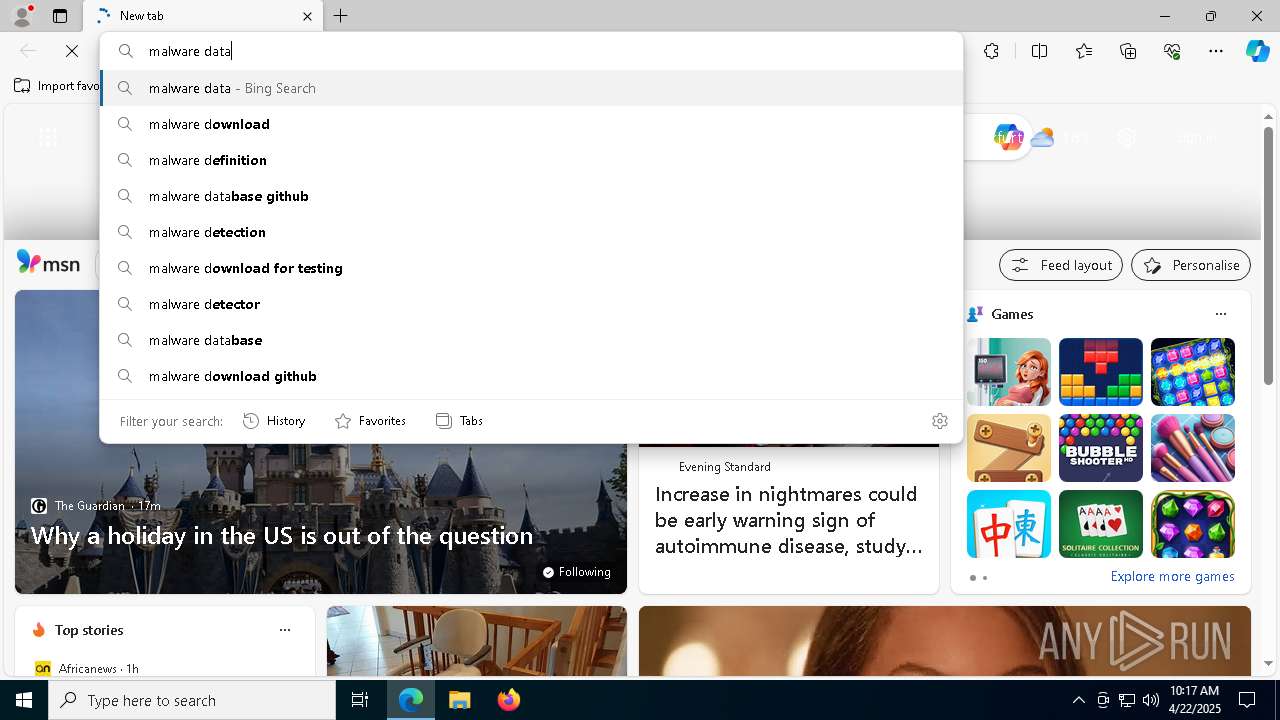
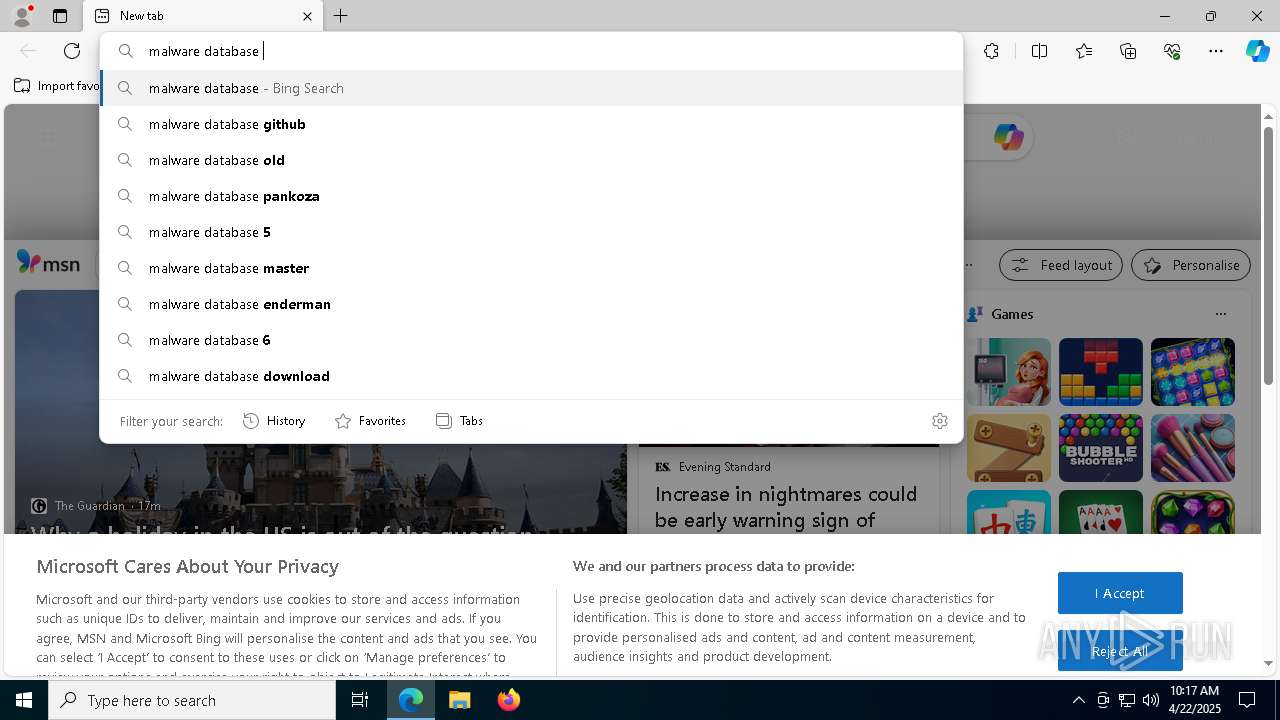
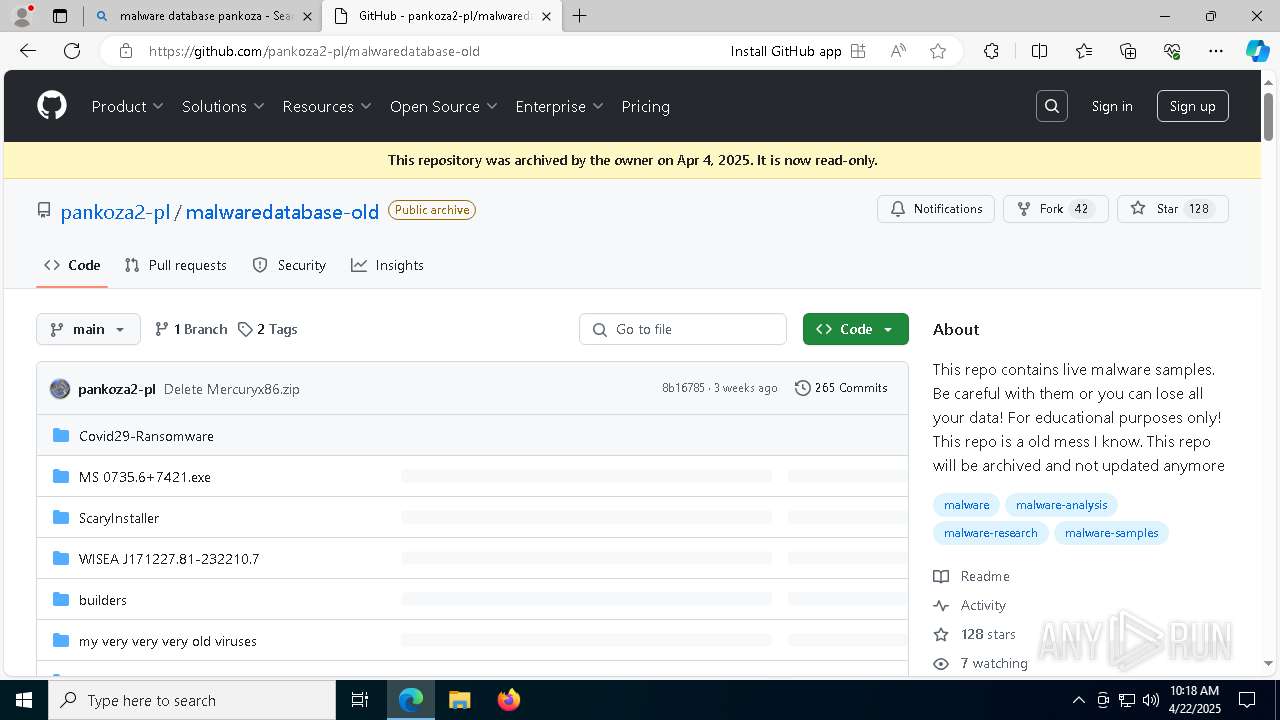
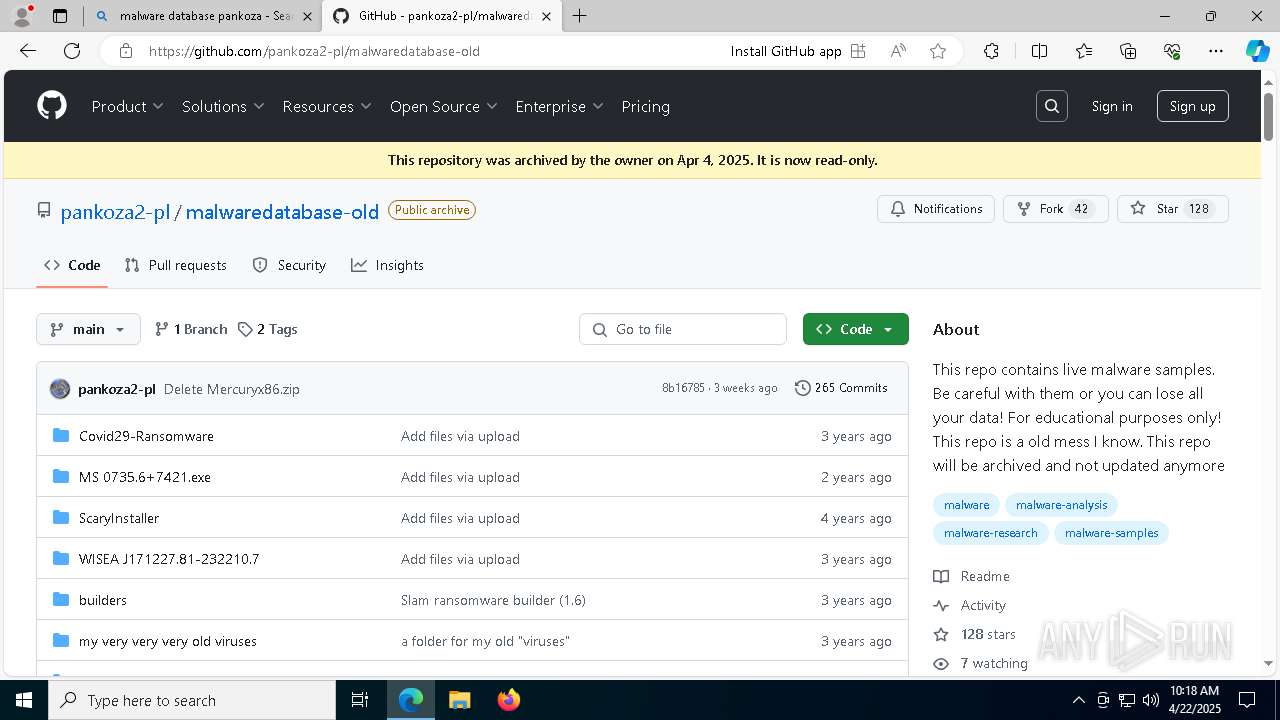
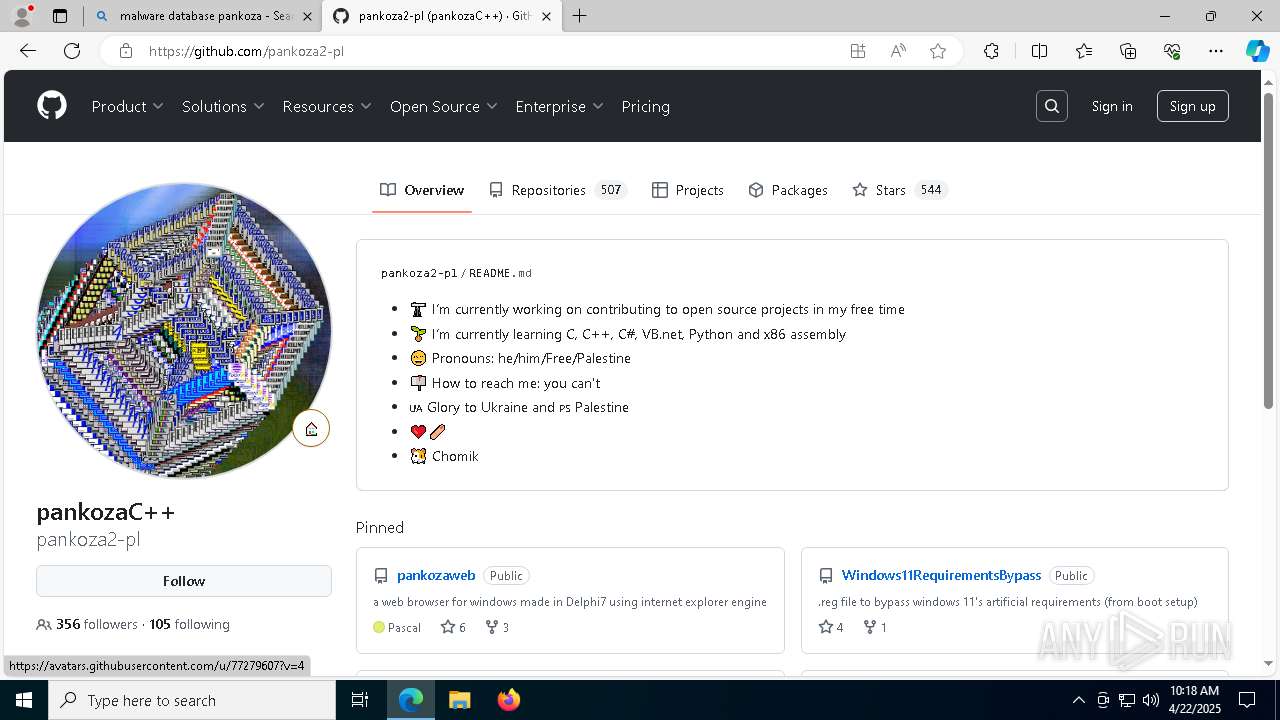
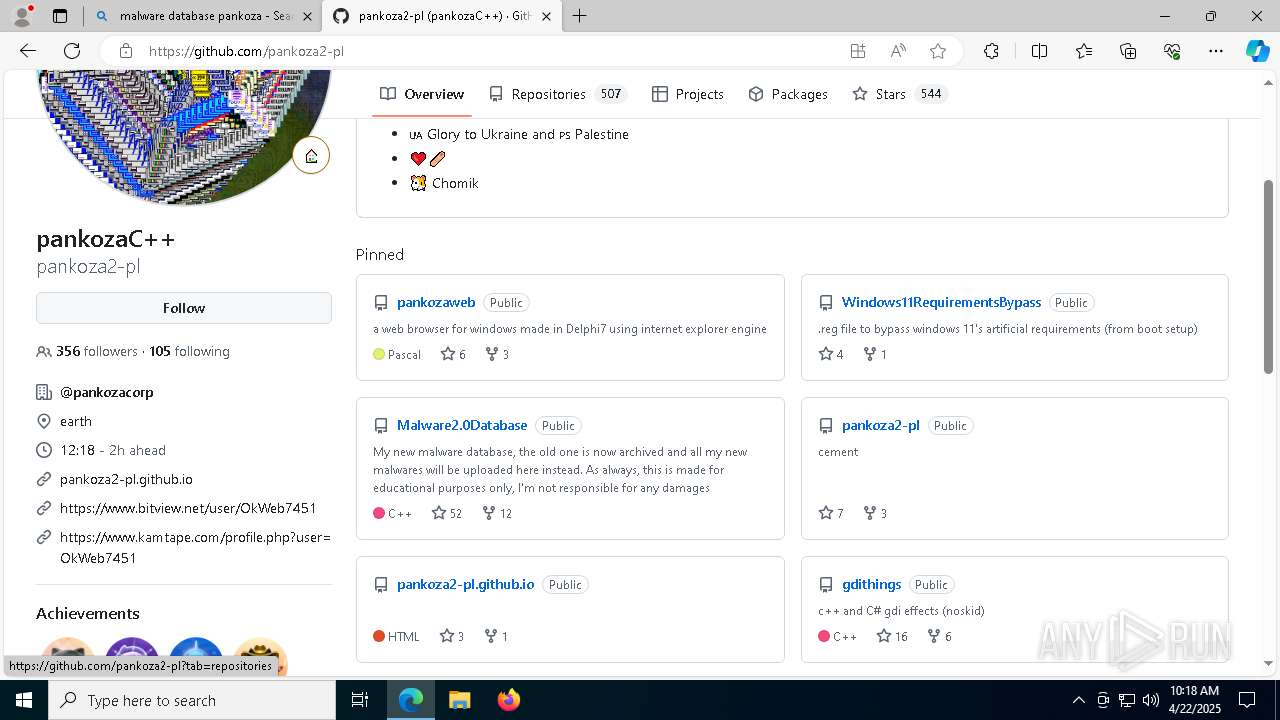
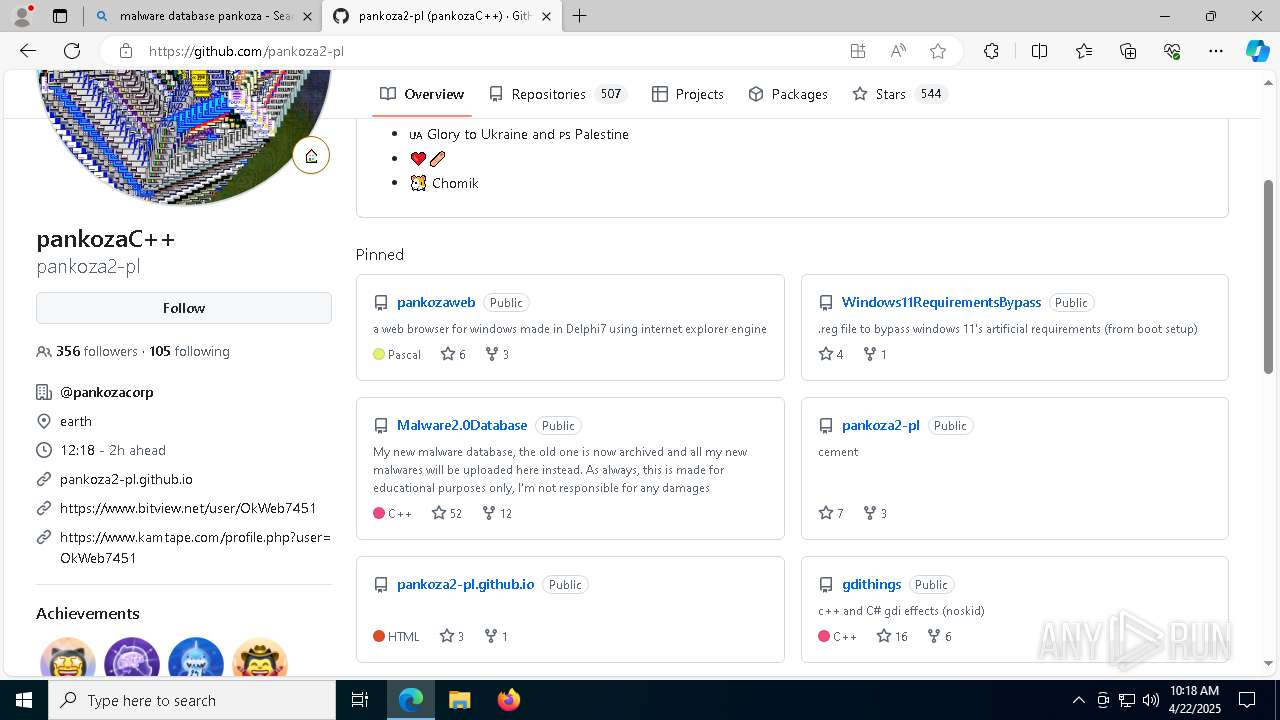
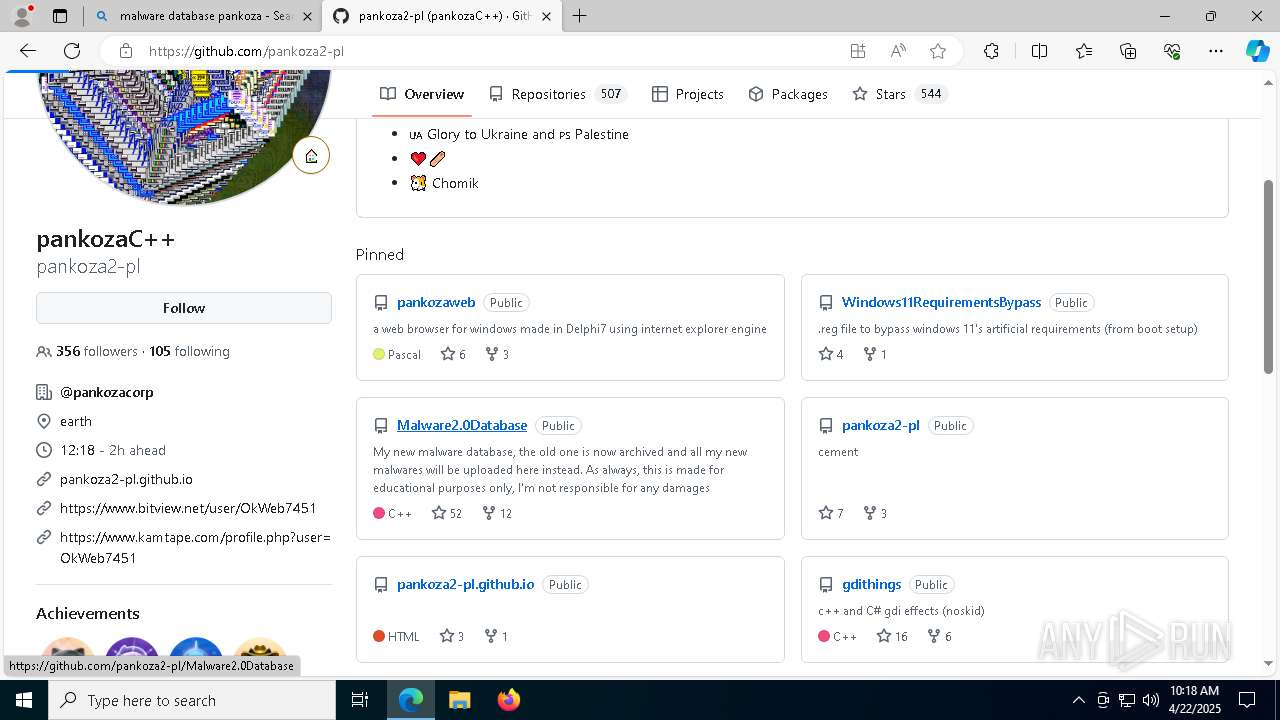
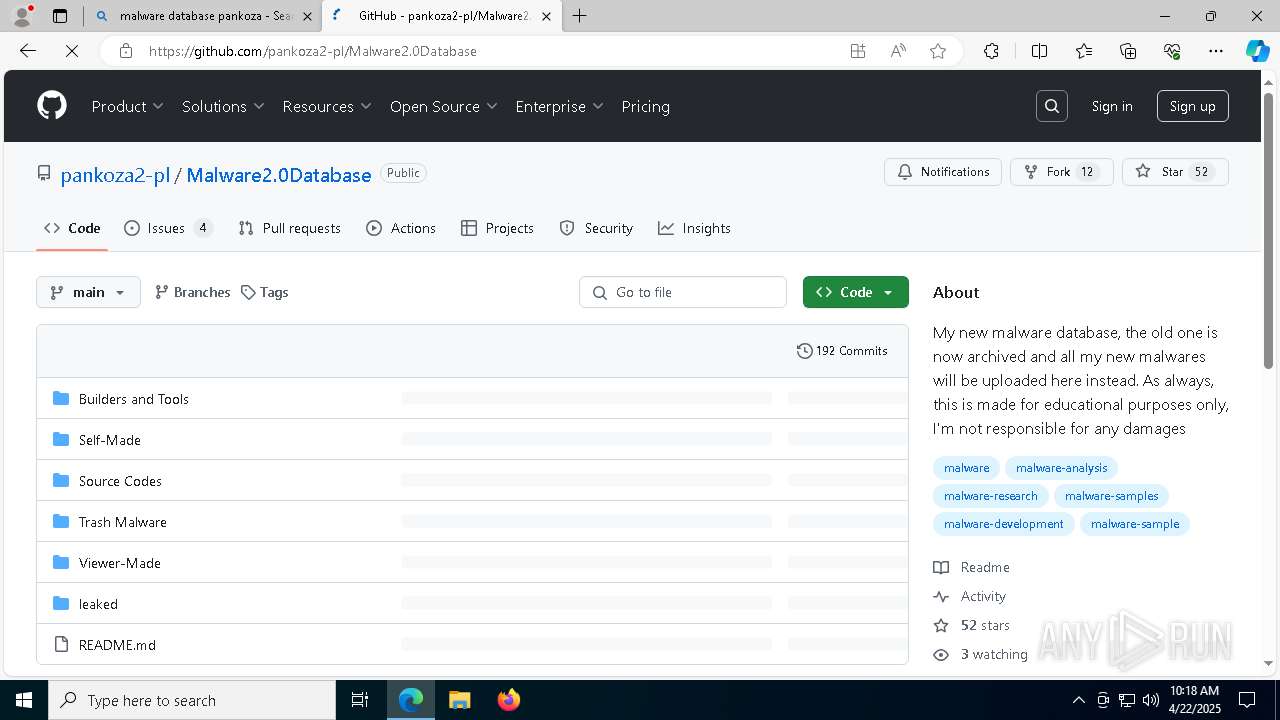
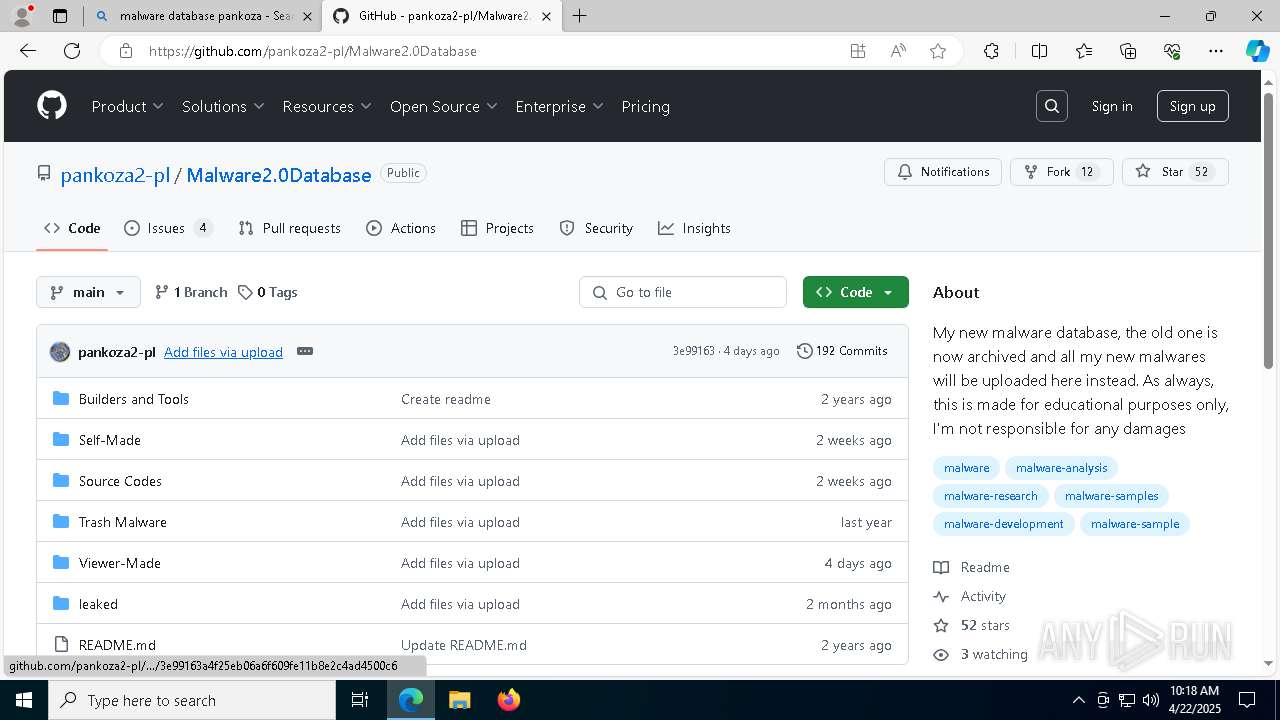
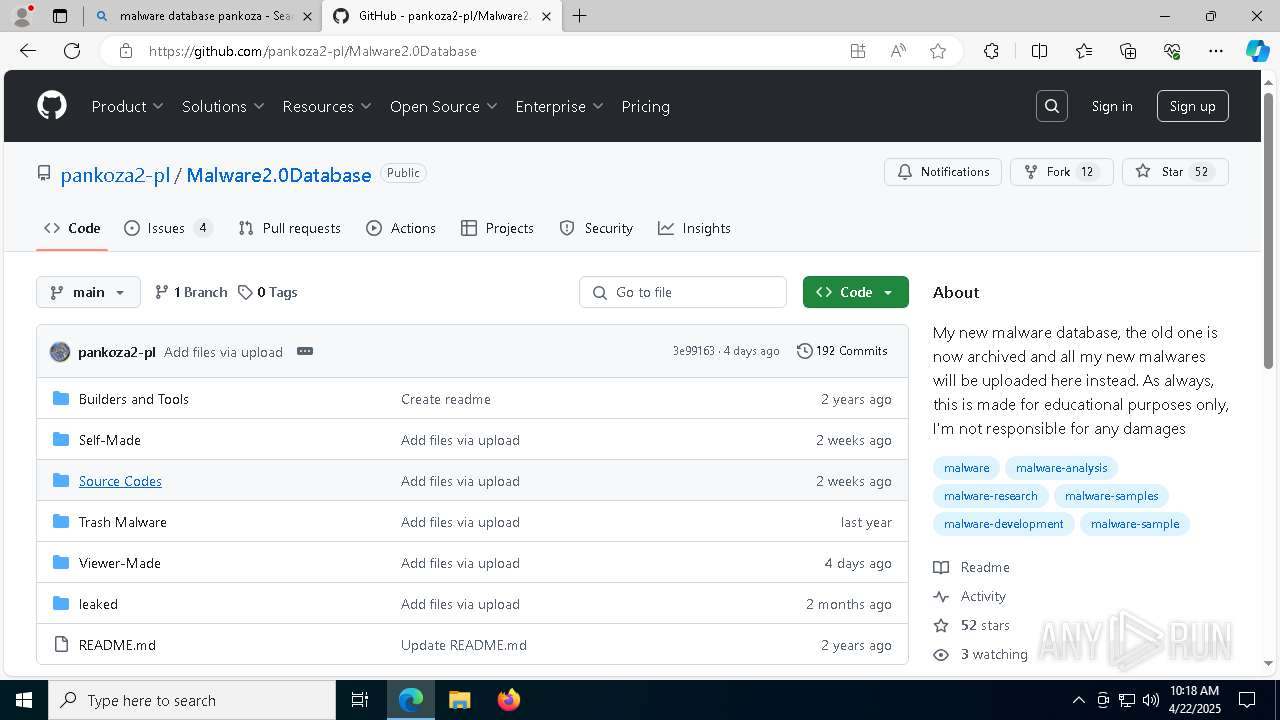
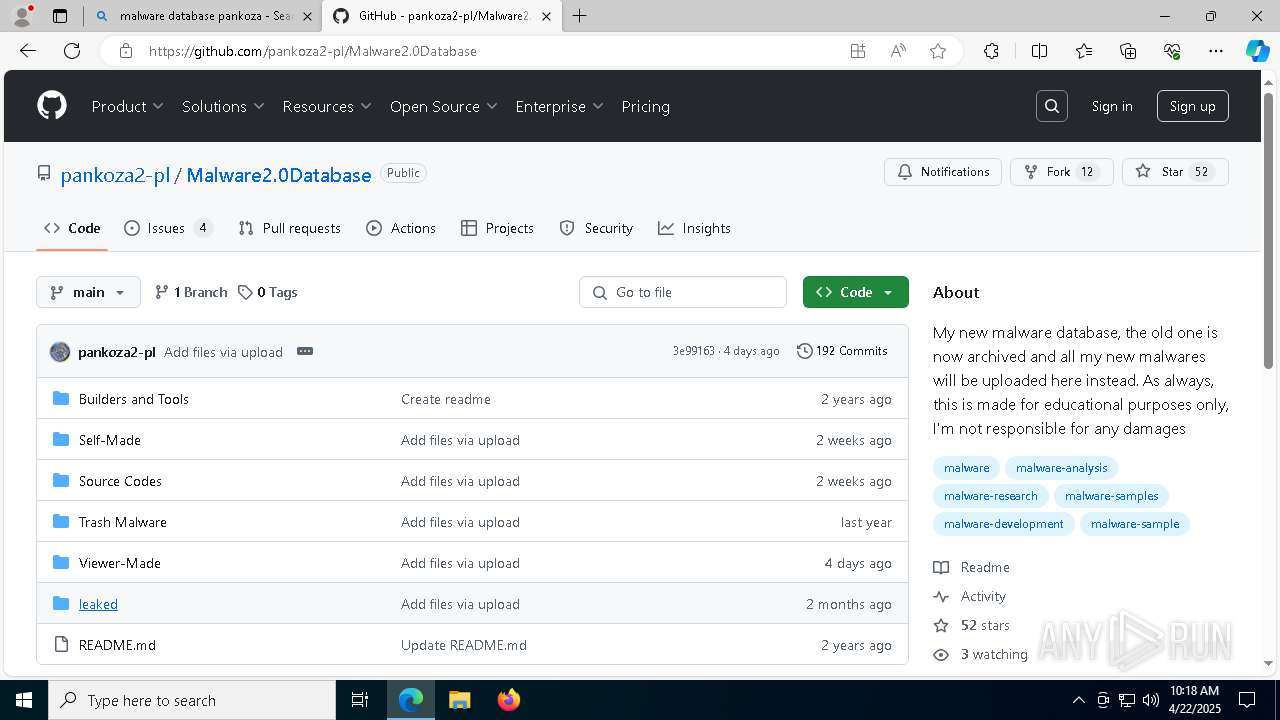
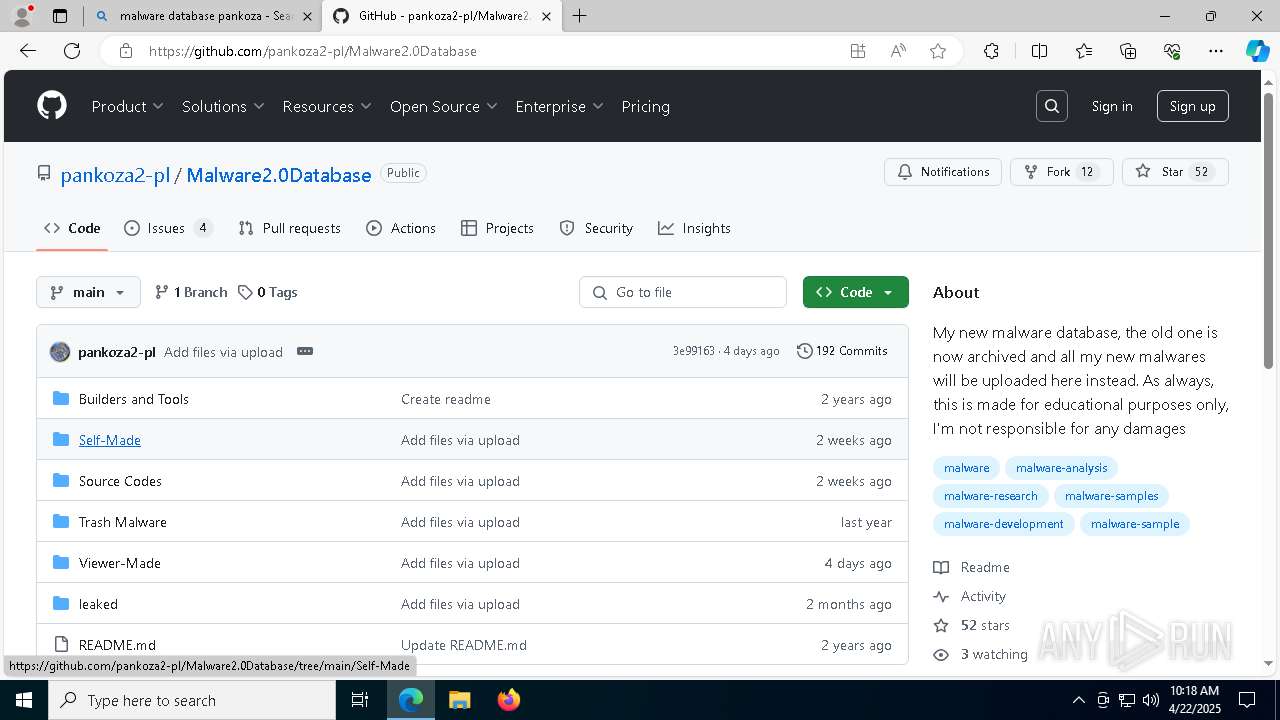
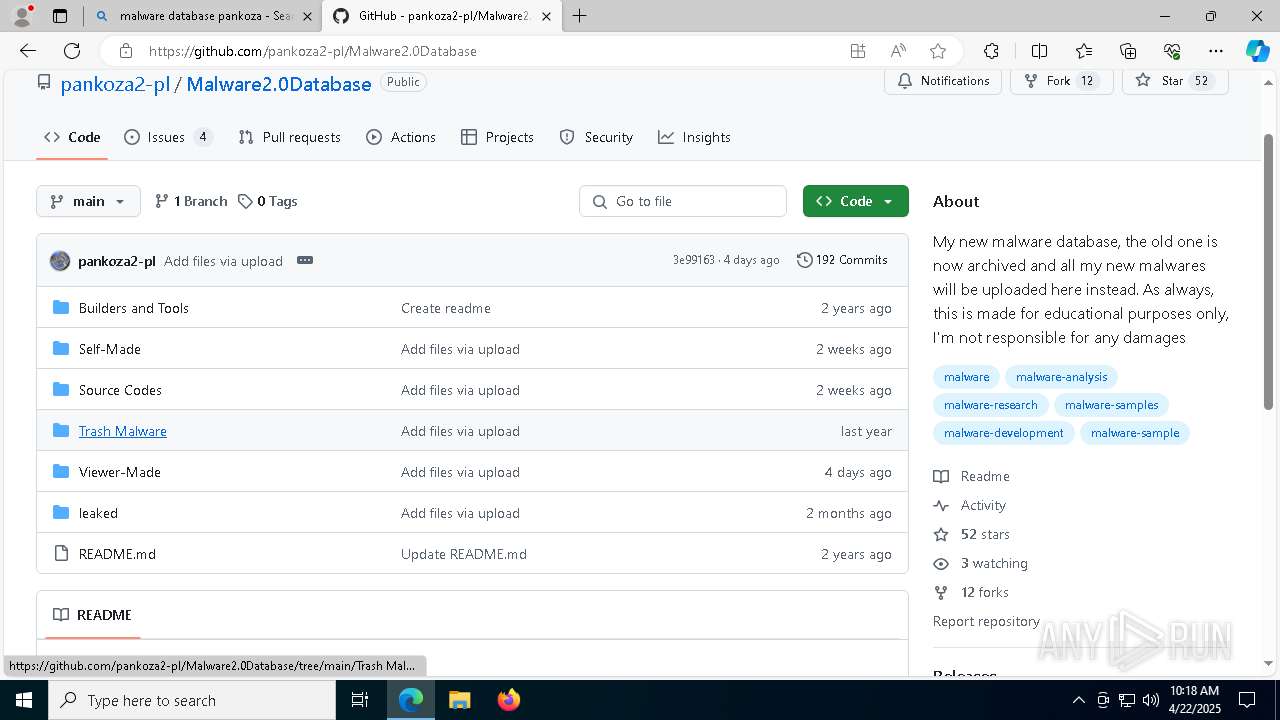
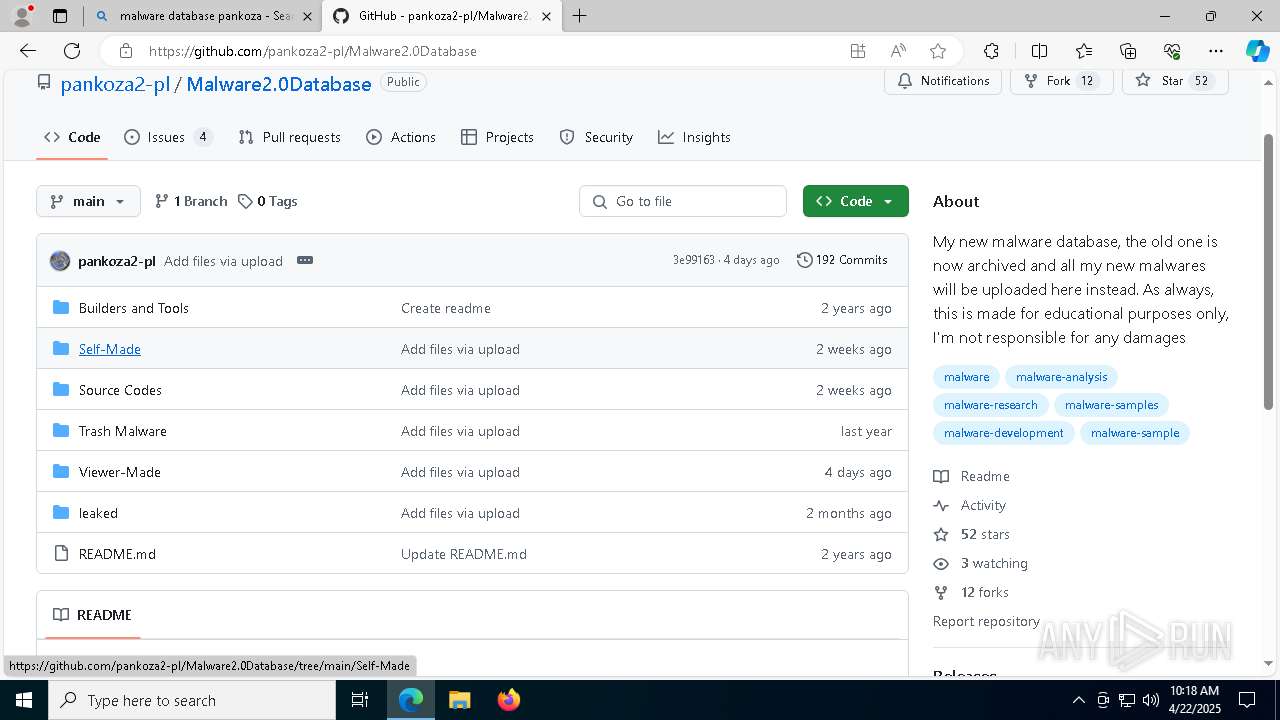
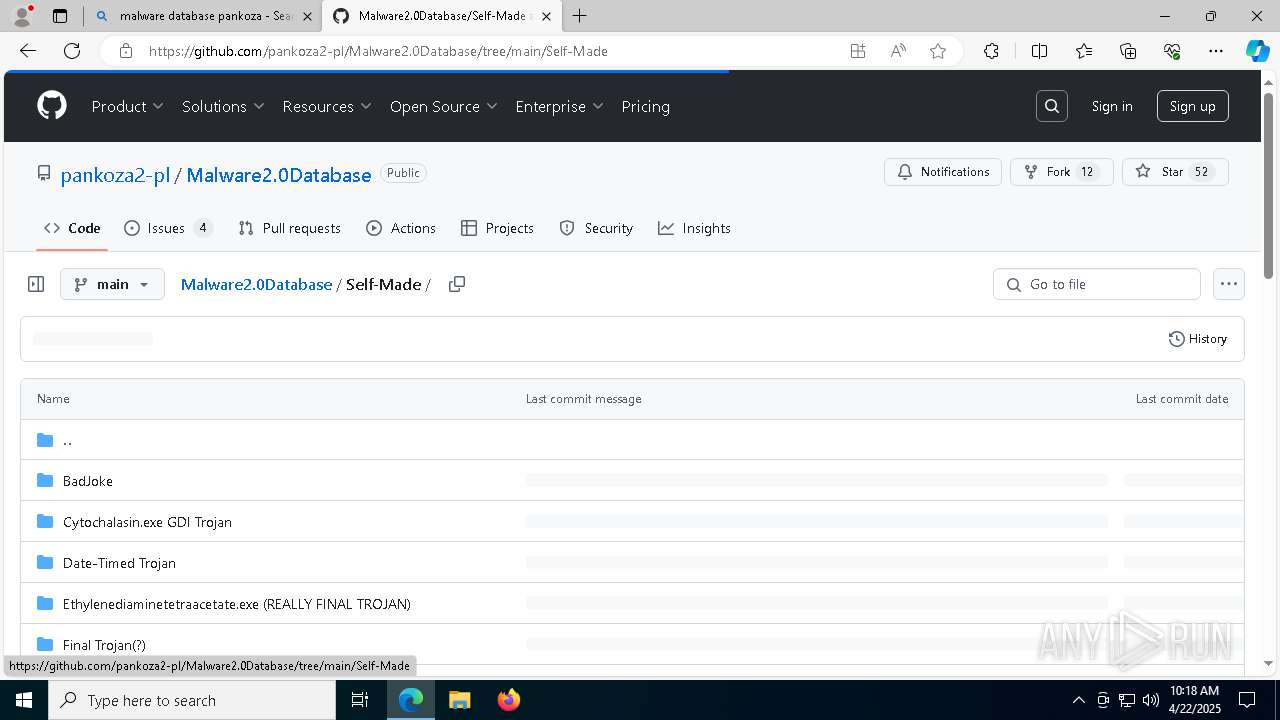
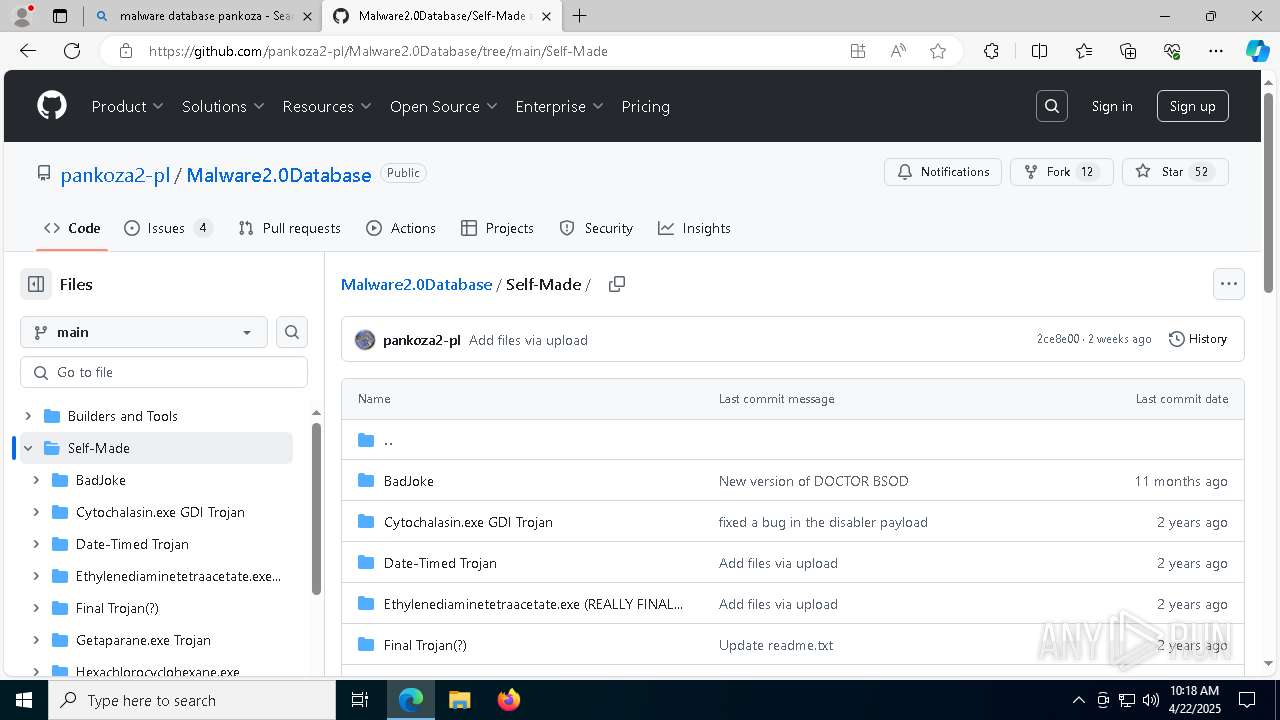
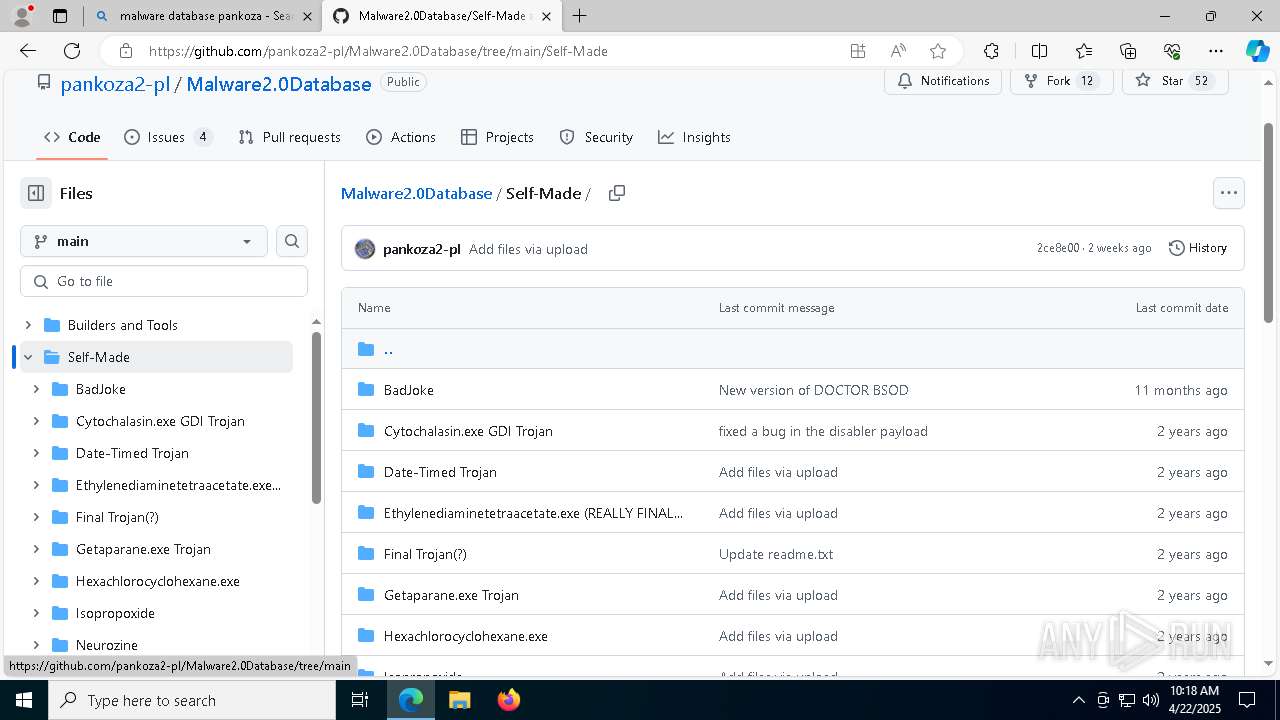
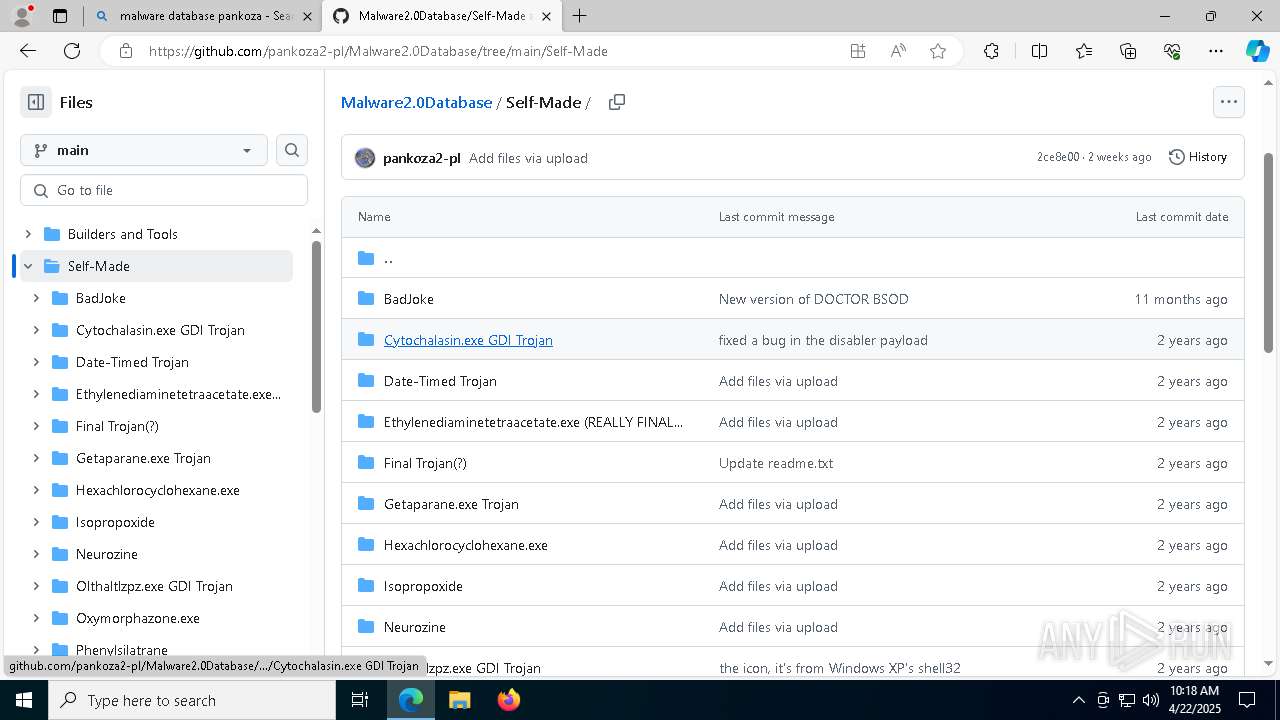
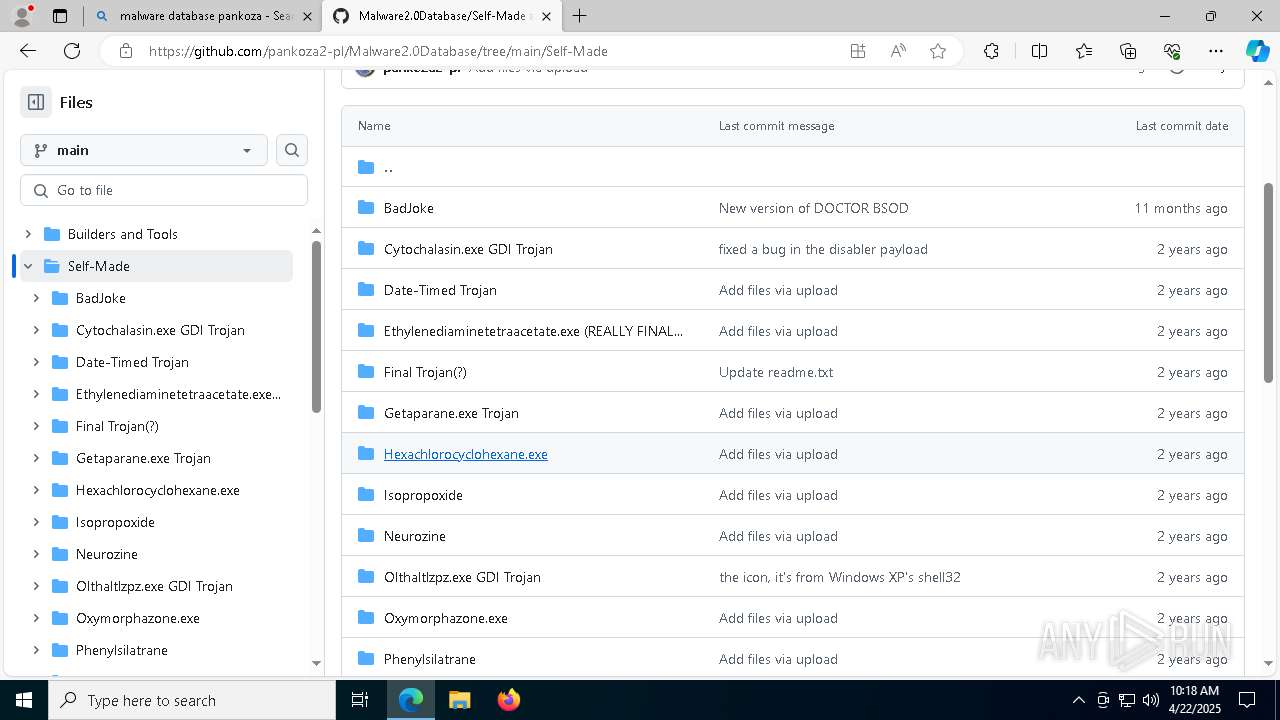
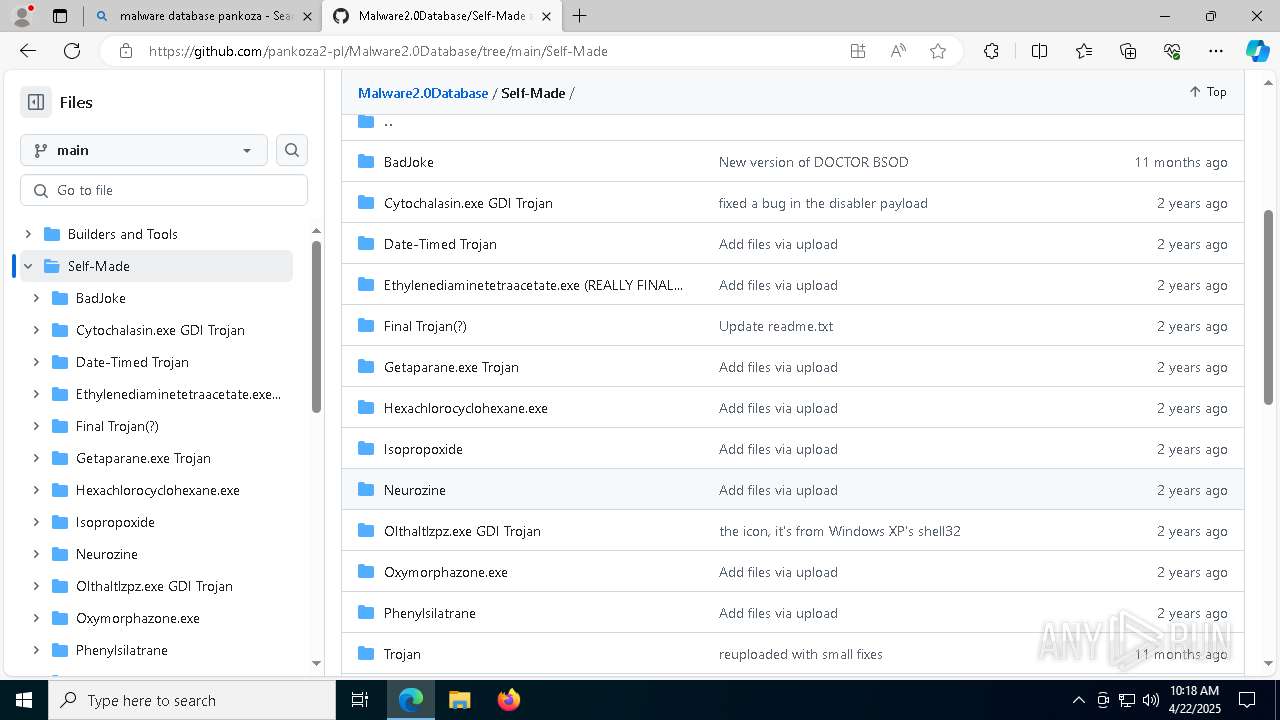
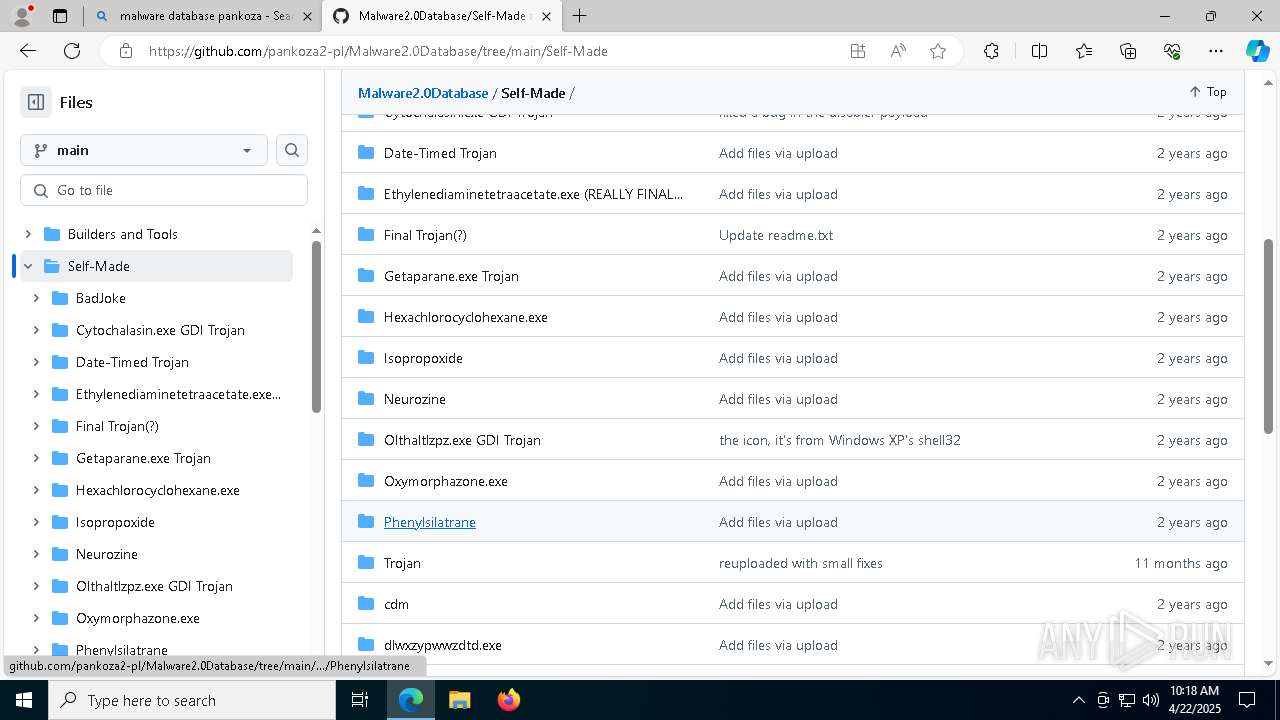
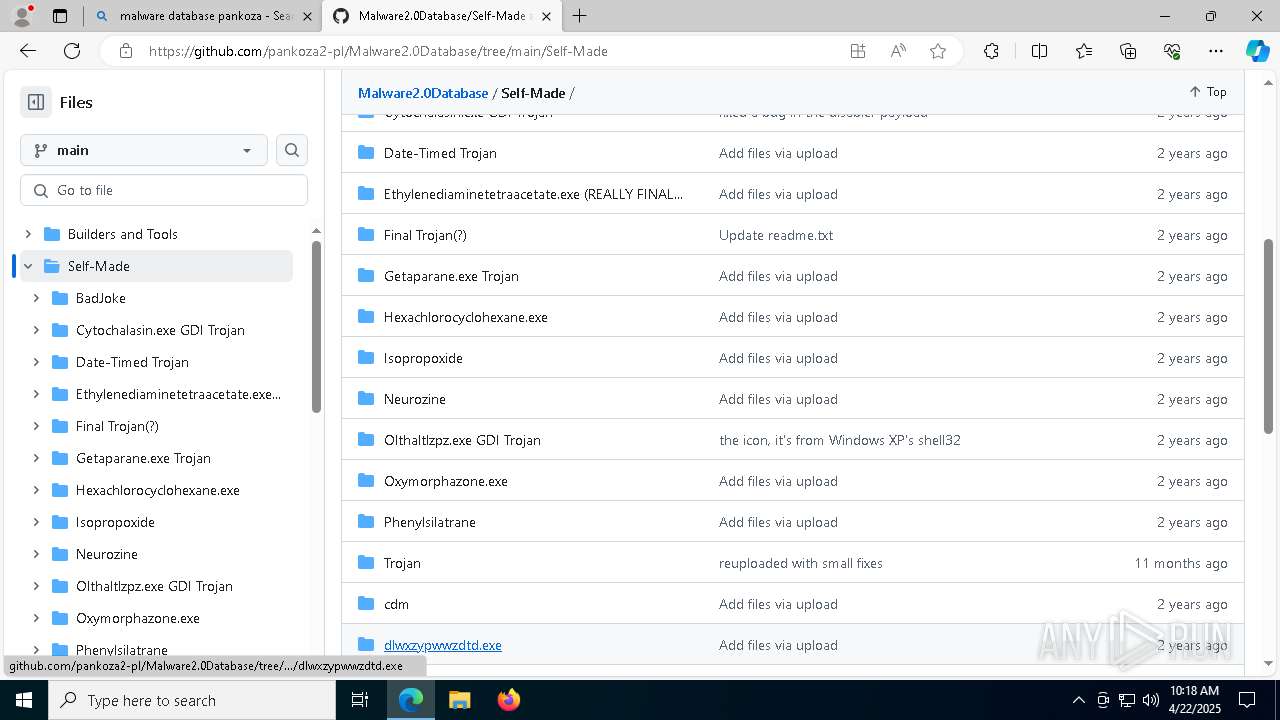
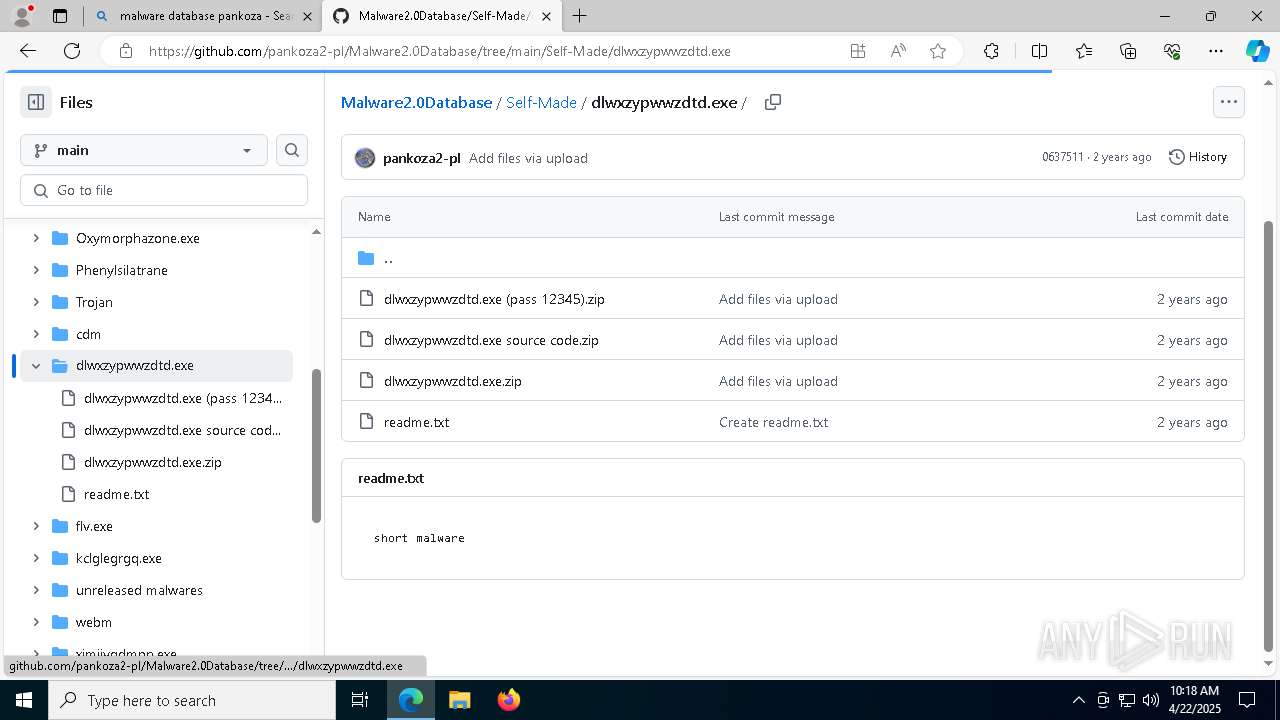
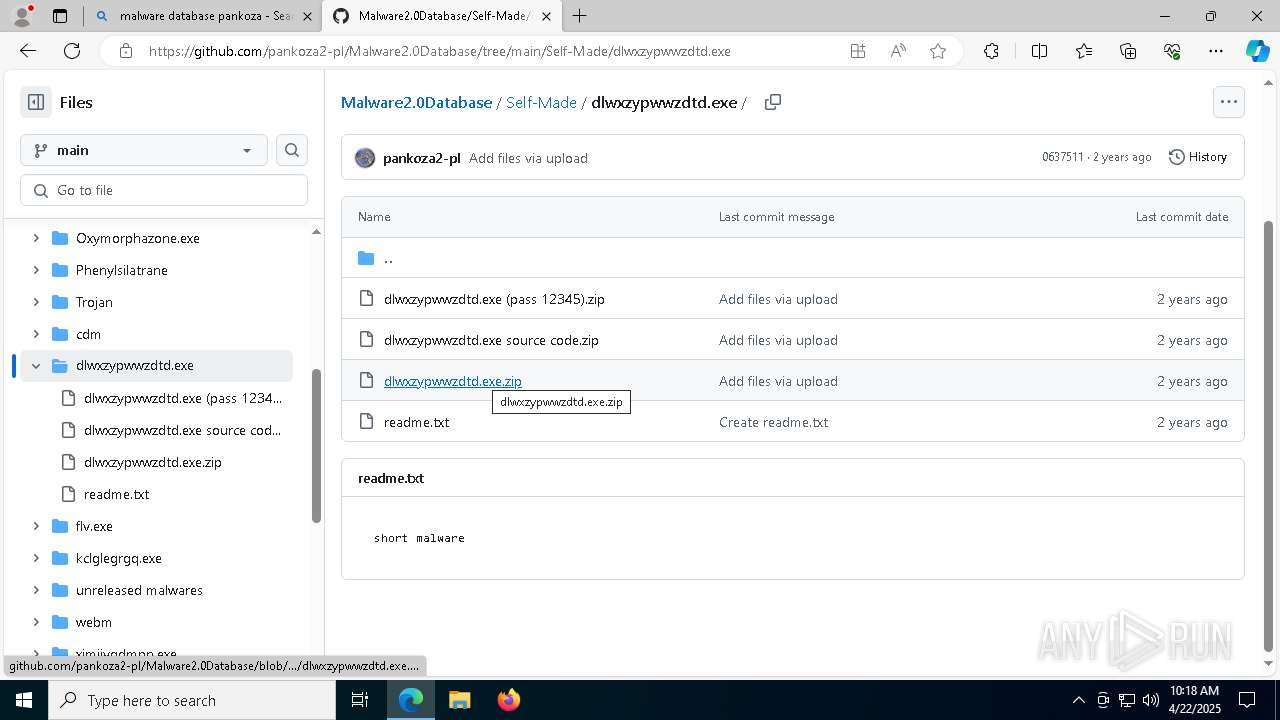
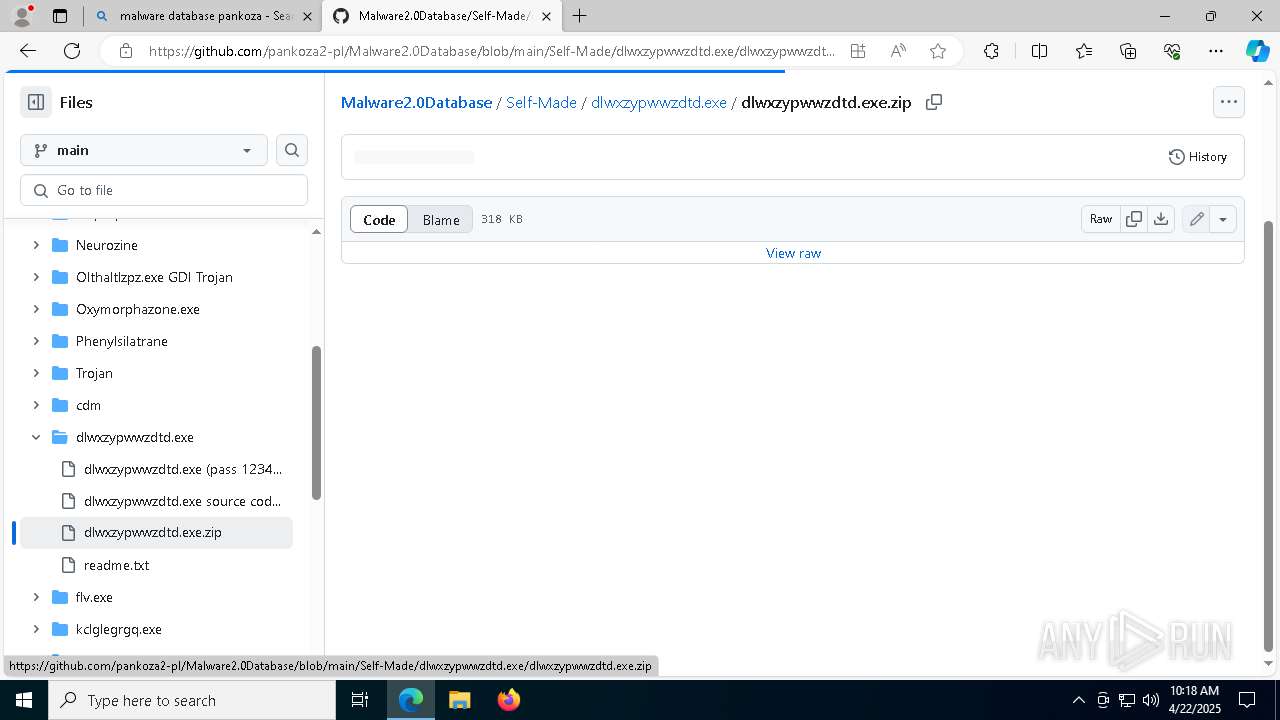
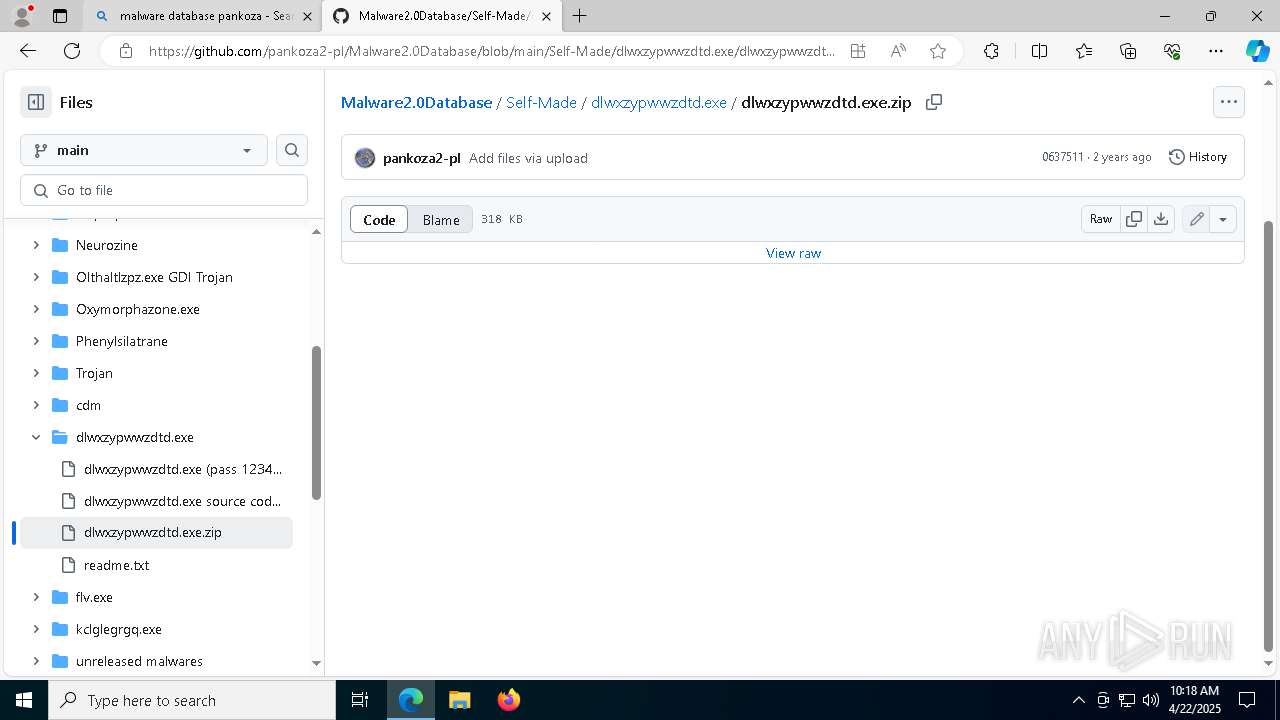
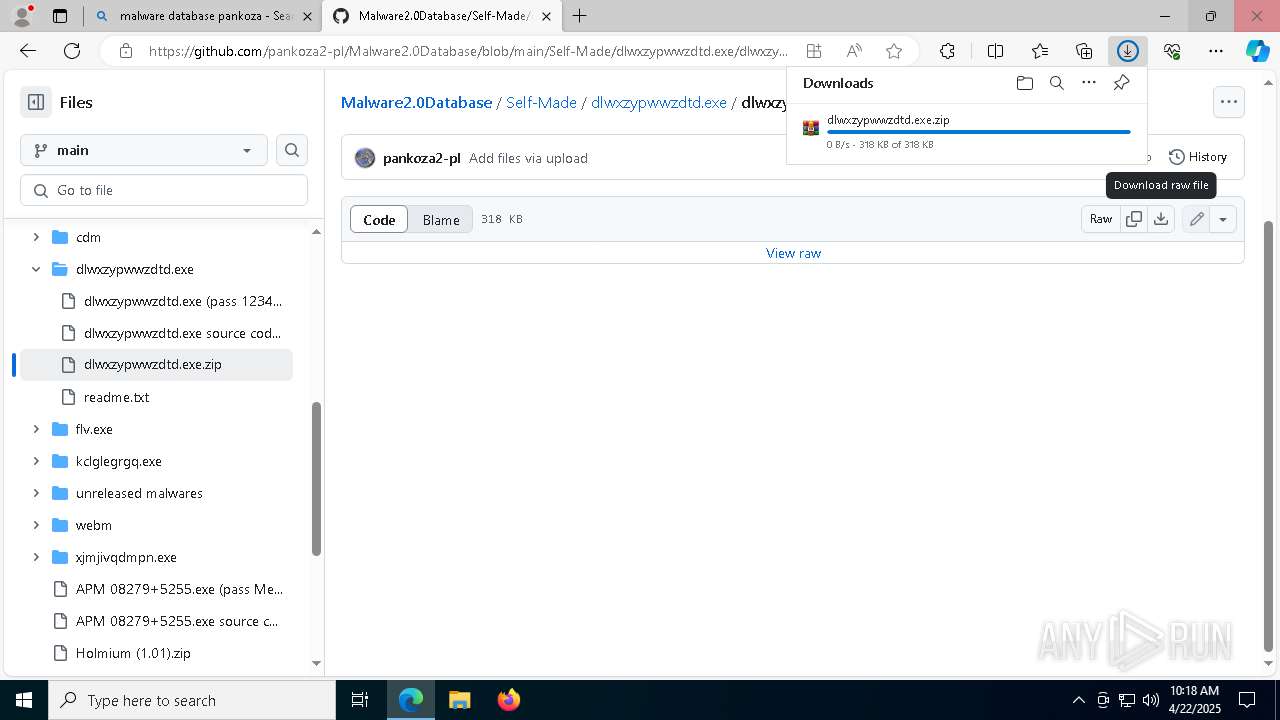
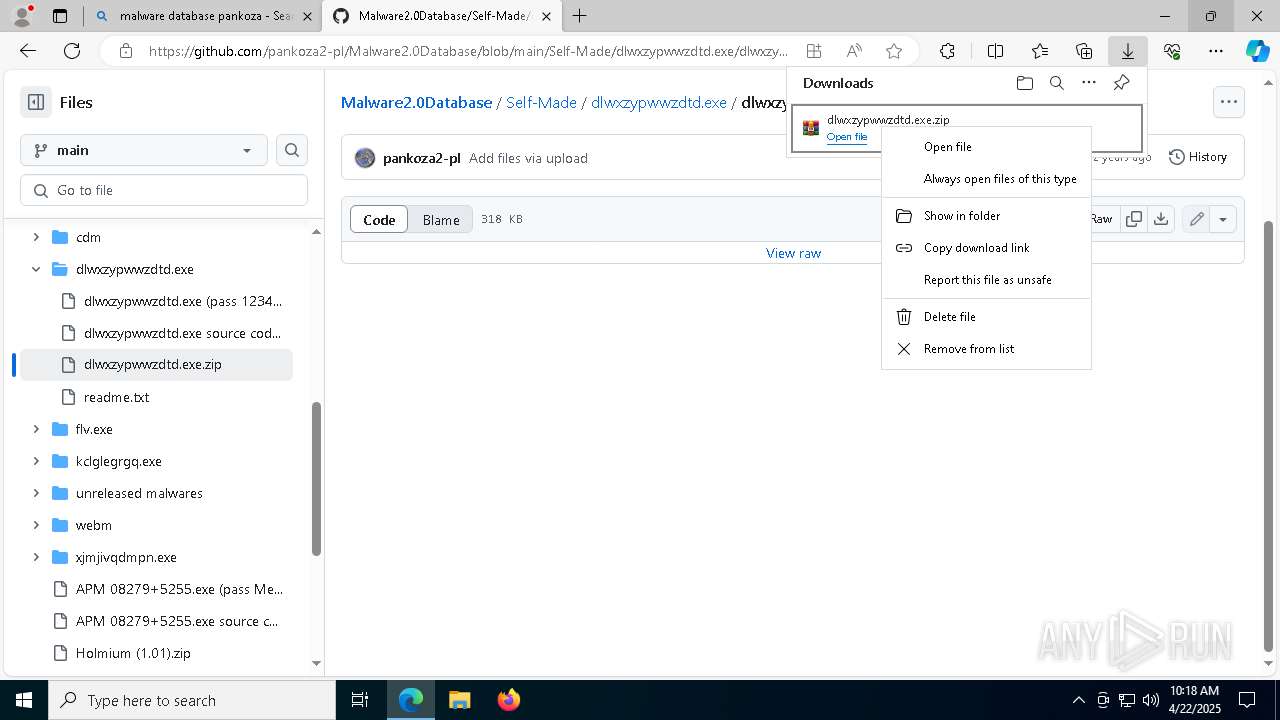
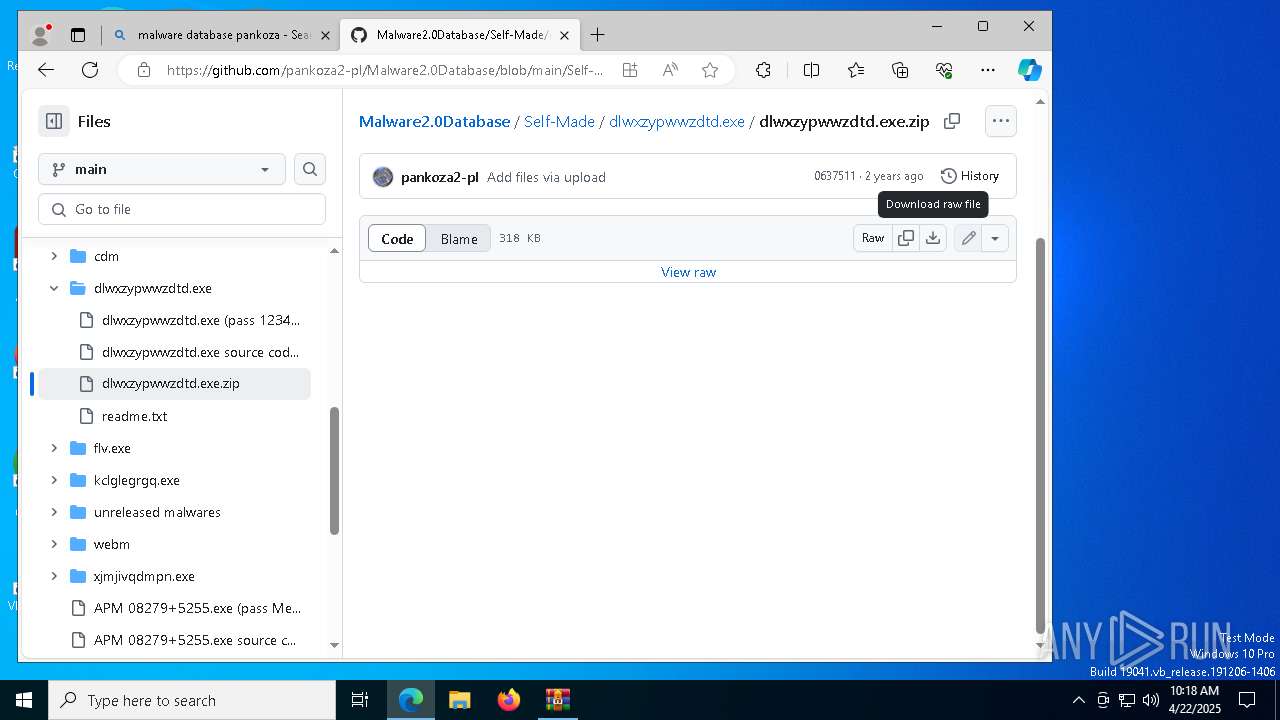
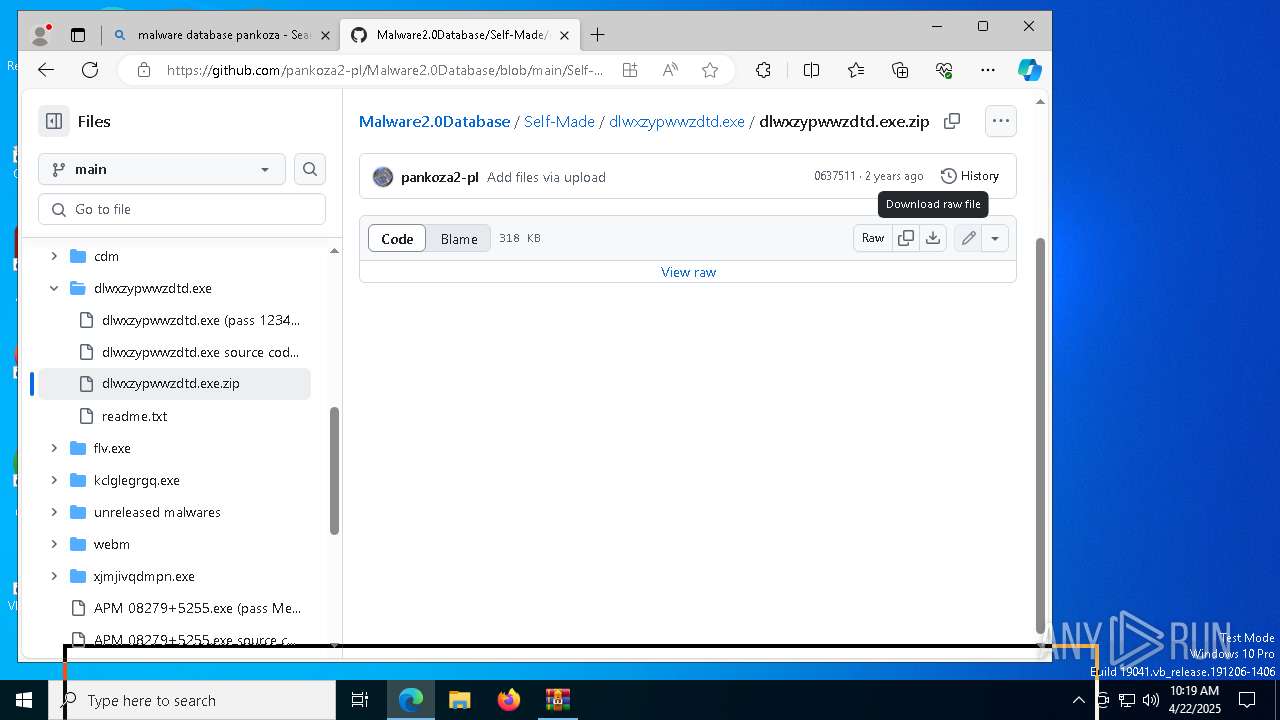
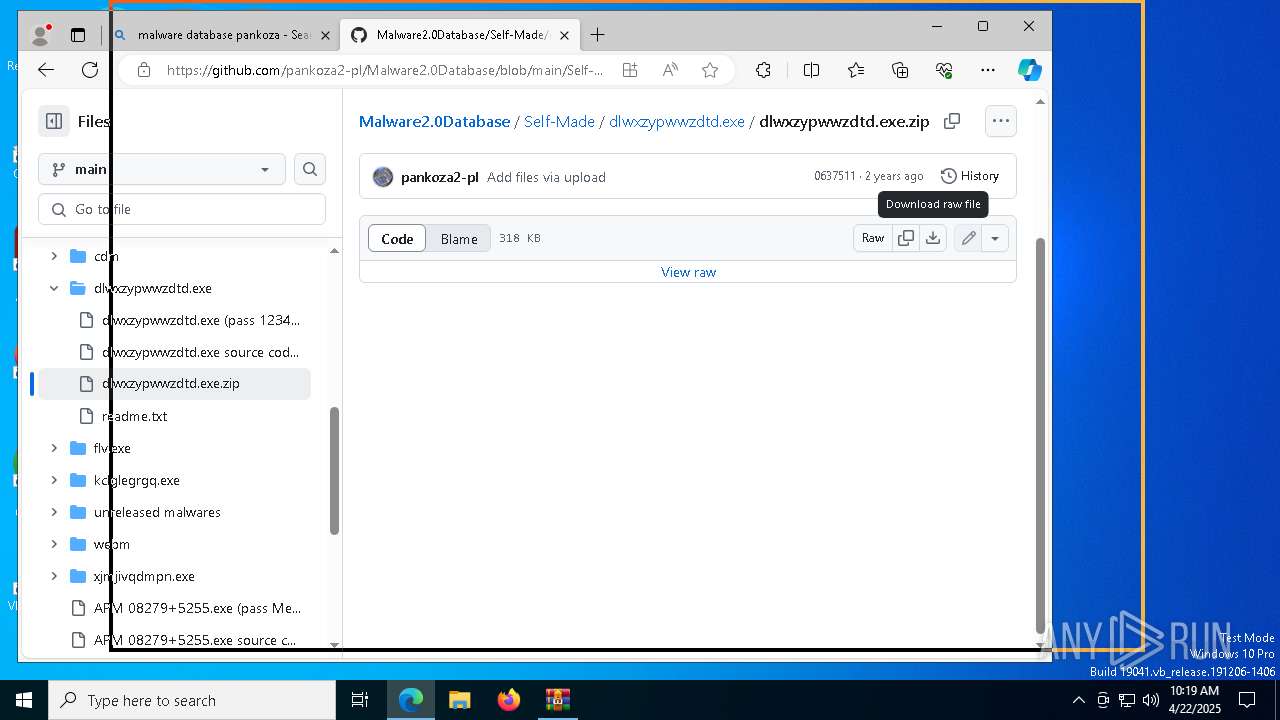
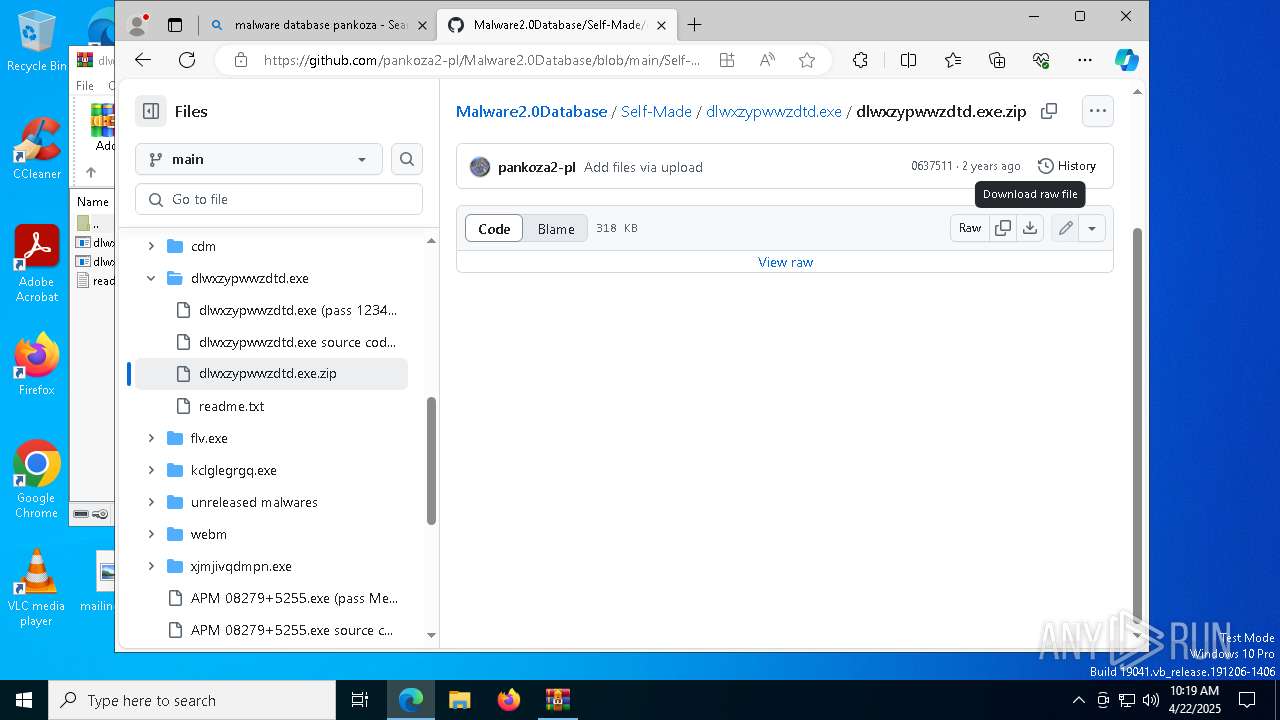
7304 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7304 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |