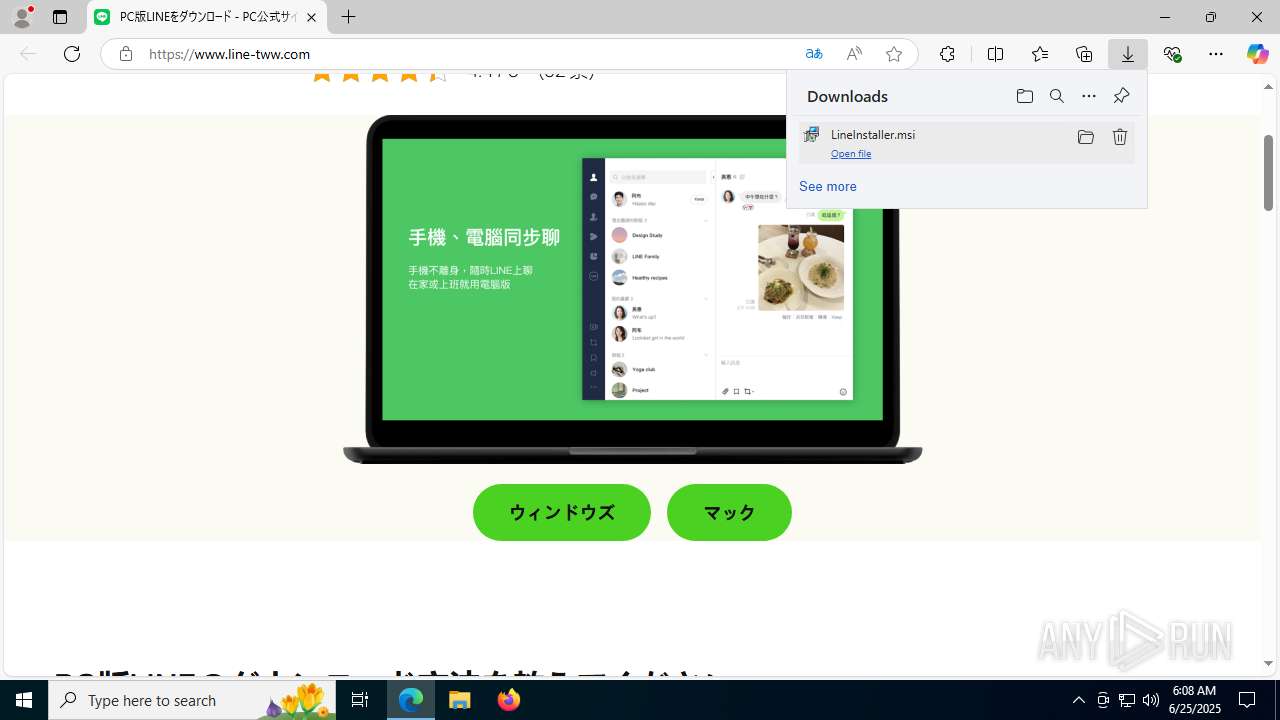
| URL: | https://www.line-tww.com/ |
| Full analysis: | https://app.any.run/tasks/78ca3f66-6a8e-4272-949c-483e2dd31c0b |
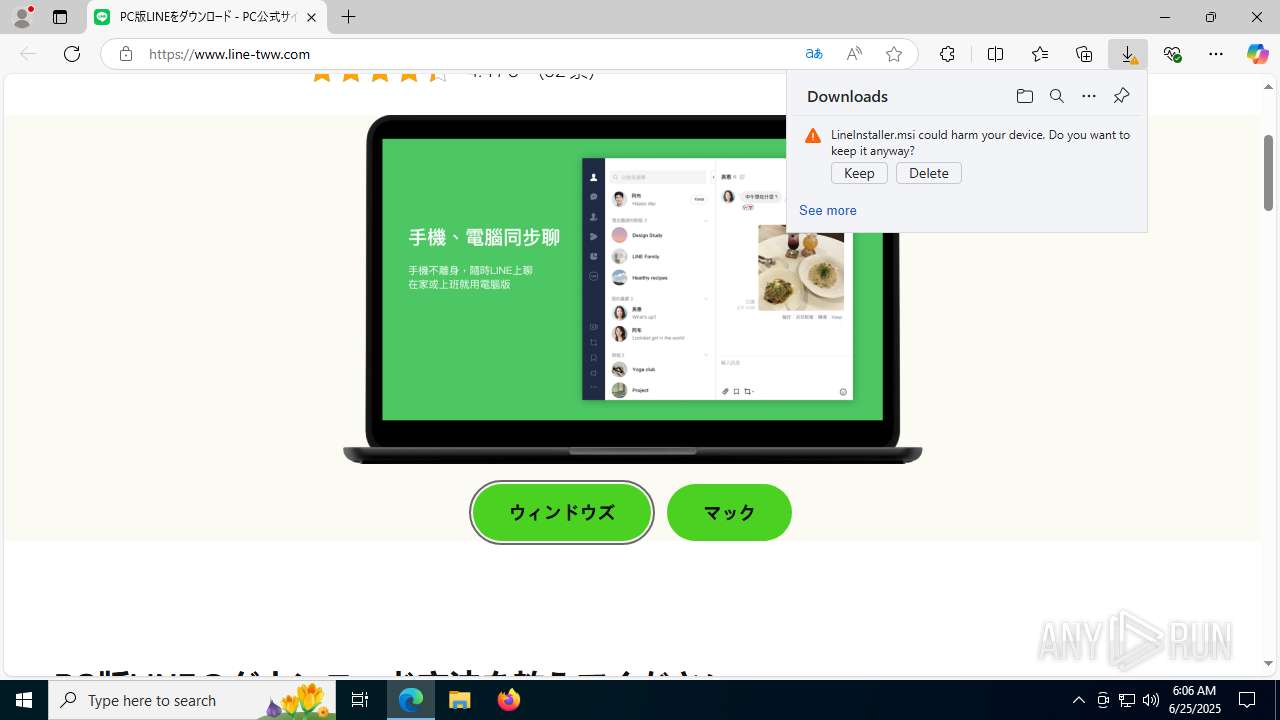
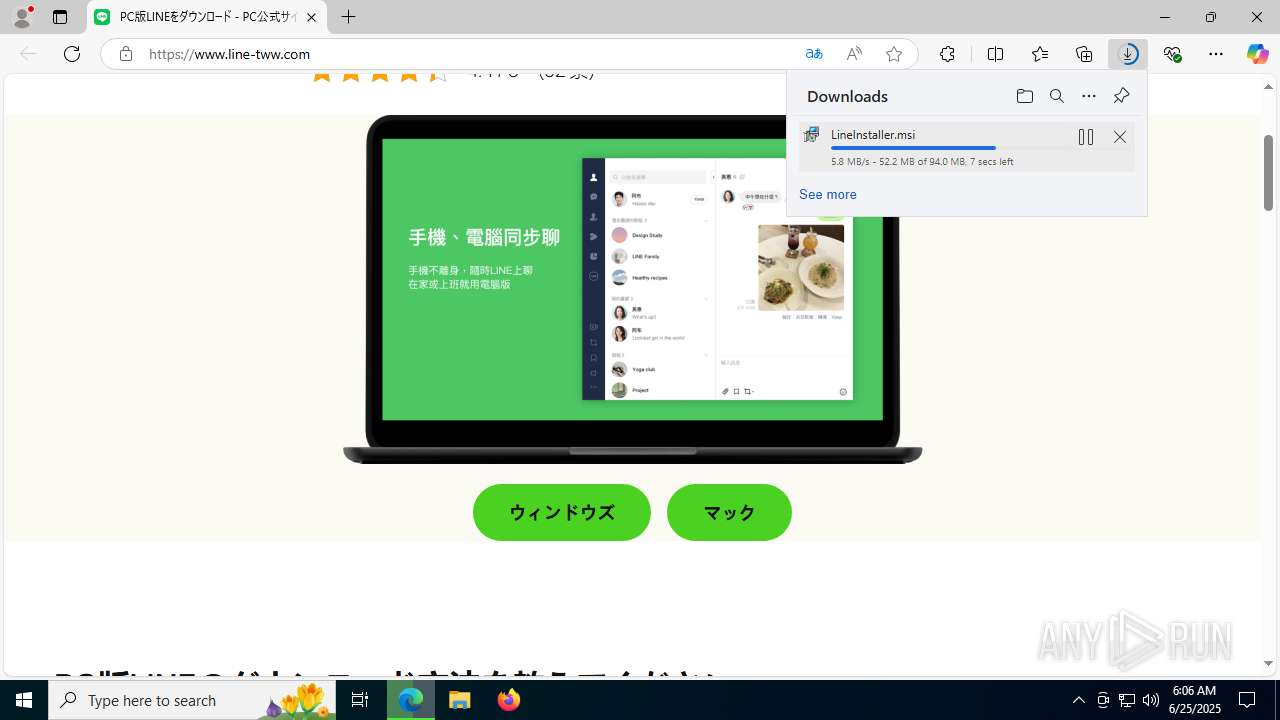
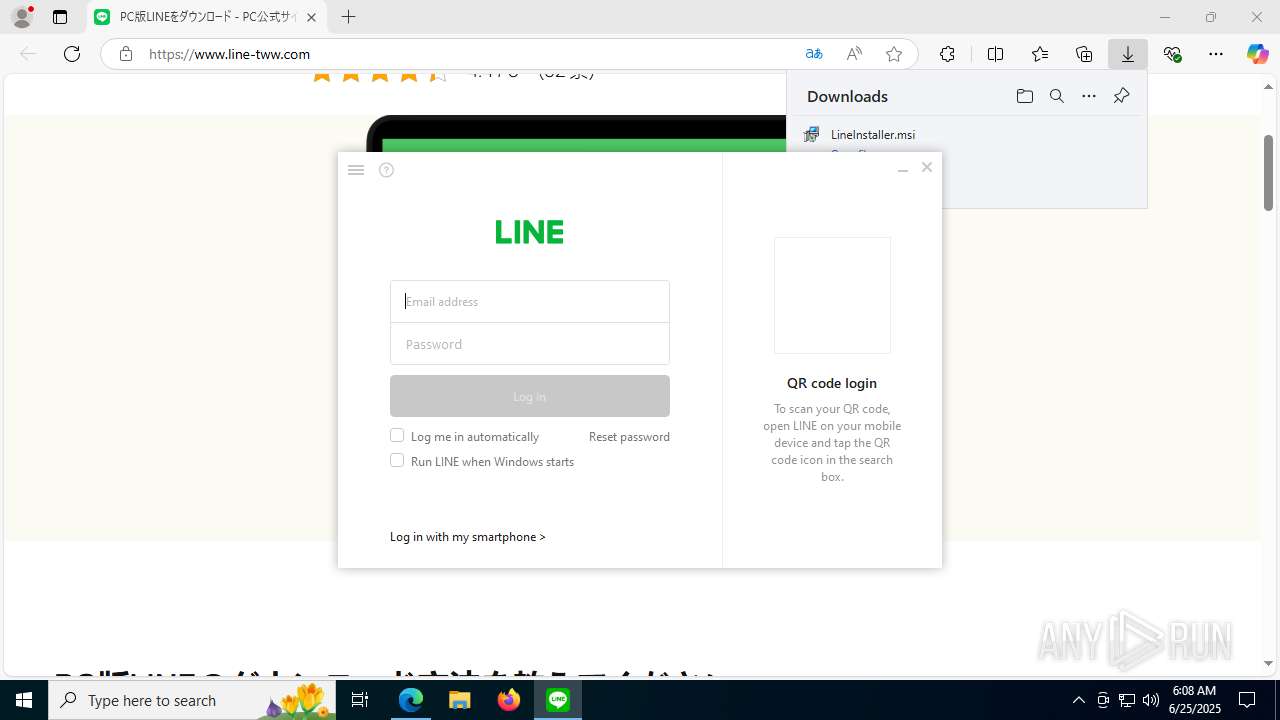
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2025, 06:05:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EBB8CFB9138811F94125F732F76DA4E6 |
| SHA1: | E571D9C250A040B63B5BDE4FAE22F5C7C075C8E7 |
| SHA256: | 08D07C500DB9E5904557F900252383AB4595F67E191AEE70F1E2DA5F3CF4BADC |
| SSDEEP: | 3:N8DSLI33:2OLY3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7248)
Executes as Windows Service
- VSSVC.exe (PID: 6584)
Process drops legitimate windows executable
- msiexec.exe (PID: 7248)
- msiexec.exe (PID: 5352)
- 749ju.exe (PID: 8148)
- LineInst_1679062.exe (PID: 6236)
Application launched itself
- msiexec.exe (PID: 7248)
The process drops C-runtime libraries
- msiexec.exe (PID: 5352)
- 749ju.exe (PID: 8148)
- LineInst_1679062.exe (PID: 6236)
Reads the date of Windows installation
- msiexec.exe (PID: 5352)
Executable content was dropped or overwritten
- 749ju.exe (PID: 8148)
- LineInst_1679062.exe (PID: 6236)
- LINE.exe (PID: 8172)
- LINE.exe (PID: 7208)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7312)
- msiexec.exe (PID: 5352)
- LineInst_1679062.exe (PID: 6236)
- LineLauncher.exe (PID: 3052)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
Executes application which crashes
- 749ju.exe (PID: 8148)
Malware-specific behavior (creating "System.dll" in Temp)
- LineInst_1679062.exe (PID: 6236)
Creates a software uninstall entry
- LineInst_1679062.exe (PID: 6236)
Reads the BIOS version
- LineAppMgr.exe (PID: 7856)
- LINE.exe (PID: 8172)
- LINE.exe (PID: 7208)
The process creates files with name similar to system file names
- LineInst_1679062.exe (PID: 6236)
INFO
Checks supported languages
- identity_helper.exe (PID: 6780)
- msiexec.exe (PID: 1216)
- msiexec.exe (PID: 7248)
- msiexec.exe (PID: 7312)
- msiexec.exe (PID: 5352)
- 749ju.exe (PID: 8148)
- LineInst.exe (PID: 5340)
- LineInst_1679062.exe (PID: 6236)
- LineLauncher.exe (PID: 3052)
- LineAppMgr.exe (PID: 7856)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
- LINE.exe (PID: 7208)
Reads Environment values
- identity_helper.exe (PID: 6780)
- msiexec.exe (PID: 7312)
- msiexec.exe (PID: 1216)
- LINE.exe (PID: 8172)
- LINE.exe (PID: 7208)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2780)
The sample compiled with english language support
- msiexec.exe (PID: 7212)
- msiexec.exe (PID: 7248)
- msiexec.exe (PID: 5352)
- 749ju.exe (PID: 8148)
- LineInst_1679062.exe (PID: 6236)
Application launched itself
- msedge.exe (PID: 2780)
Reads the computer name
- msiexec.exe (PID: 7312)
- identity_helper.exe (PID: 6780)
- msiexec.exe (PID: 1216)
- msiexec.exe (PID: 5352)
- msiexec.exe (PID: 7248)
- LineInst.exe (PID: 5340)
- LineInst_1679062.exe (PID: 6236)
- LineAppMgr.exe (PID: 7856)
- LineLauncher.exe (PID: 3052)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
- LINE.exe (PID: 7208)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7212)
- msiexec.exe (PID: 7248)
- msiexec.exe (PID: 5352)
Manages system restore points
- SrTasks.exe (PID: 7860)
The sample compiled with chinese language support
- msiexec.exe (PID: 7248)
Checks proxy server information
- msiexec.exe (PID: 5352)
- WerFault.exe (PID: 7996)
- LINE.exe (PID: 8172)
- slui.exe (PID: 8112)
- LINE.exe (PID: 7208)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5352)
- LineLauncher.exe (PID: 3052)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
- LINE.exe (PID: 7208)
Reads the software policy settings
- msiexec.exe (PID: 5352)
- WerFault.exe (PID: 7996)
- LineInst.exe (PID: 5340)
- slui.exe (PID: 8112)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
Creates files or folders in the user directory
- msiexec.exe (PID: 5352)
- 749ju.exe (PID: 8148)
- LineLauncher.exe (PID: 3052)
- LINE.exe (PID: 8172)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
- WerFault.exe (PID: 7996)
- LINE.exe (PID: 7208)
- LineInst_1679062.exe (PID: 6236)
Process checks computer location settings
- msiexec.exe (PID: 5352)
- msiexec.exe (PID: 7312)
- LineLauncher.exe (PID: 3052)
- LineUpdater.exe (PID: 8096)
- LineLauncher.exe (PID: 7296)
Create files in a temporary directory
- LineInst.exe (PID: 5340)
- LineInst_1679062.exe (PID: 6236)
- LINE.exe (PID: 8172)
- LINE.exe (PID: 7208)
Process checks whether UAC notifications are on
- LineInst_1679062.exe (PID: 6236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
196
Monitored processes
51
Malicious processes
5
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5344,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=4316 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5540,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=5560 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5296,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=5264 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | C:\Windows\syswow64\MsiExec.exe -Embedding 008C497816B47F3644CBE44D78BD88B0 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6332,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=6352 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7052,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=5516 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3556,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2204,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=2636 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2564,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=2944 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6588,i,17840348758585389002,6638347836808011229,262144 --variations-seed-version --mojo-platform-channel-handle=6884 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
23 825
Read events
23 548
Write events
253
Delete events
24
Modification events
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 65010A85F5962F00 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FF71D849-5CAB-4D5B-A6F3-14A6166FE6F1} | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {93B8DFE6-868C-48F7-BC73-16F43FEFC02A} | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {997E5C37-FBFE-41A9-8270-26988C5991CA} | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 562A5F85F5962F00 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
157
Suspicious files
179
Text files
75
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176755.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176764.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176764.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176784.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176764.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
86
DNS requests
83
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1984 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:3edPjwEXSRWhhPbX6DhAqM9J2mU2WqHCQEkj4CTDgfY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4664 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751249283&P2=404&P3=2&P4=ia9C%2fzIIIkAGT6Dcg6otiCWZ3TcFgTLxdMCt5ue%2b5OcQOCgKj7uGoJCghKqZbLa9juUoXSgpmrIyZkYOu9jQMw%3d%3d | unknown | — | — | whitelisted |
7556 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4664 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751249284&P2=404&P3=2&P4=PCw4jGnSKM5ad2paoFnaw8zzaLHw9HSWEQN81hxxDWceYj%2faXP04W8bxKZAb%2b4wInNOAIvQTrOUuI1Pmi9Y%2b1Q%3d%3d | unknown | — | — | whitelisted |
4664 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751249283&P2=404&P3=2&P4=ia9C%2fzIIIkAGT6Dcg6otiCWZ3TcFgTLxdMCt5ue%2b5OcQOCgKj7uGoJCghKqZbLa9juUoXSgpmrIyZkYOu9jQMw%3d%3d | unknown | — | — | whitelisted |
4664 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751249283&P2=404&P3=2&P4=ia9C%2fzIIIkAGT6Dcg6otiCWZ3TcFgTLxdMCt5ue%2b5OcQOCgKj7uGoJCghKqZbLa9juUoXSgpmrIyZkYOu9jQMw%3d%3d | unknown | — | — | whitelisted |
4664 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751249285&P2=404&P3=2&P4=AH6LpuTMVVUKMErv9cmz3qYMW%2fQehOOQYsTjN1dRsX68HIkfC%2fn5gpe9Gnpt%2bfPmXQY5Deu%2bIr2sFb749wabXA%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4112 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1984 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1984 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1984 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1984 | msedge.exe | 188.114.97.3:443 | www.line-tww.com | CLOUDFLARENET | NL | unknown |
1984 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.line-tww.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1984 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
1984 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
1984 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
1984 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
Process | Message |
|---|---|
msiexec.exe | UnPackZipToPath, success(1) |
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/9.9.0.3633/WtsApi32.dll"
|
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/9.9.0.3633/rpcrt4.dll"
|
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/rpcrt4.dll"
|
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/SHFolder.dll"
|
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/version.dll"
|
LINE.exe | [MODULE_VALIDATOR] moduleName : "rpcrt4.dll" 0
|
LINE.exe | [MODULE_VALIDATOR] module open failed : "C:/Users/admin/AppData/Local/LINE/bin/9.9.0.3633/SHFolder.dll"
|
LINE.exe | [MODULE_VALIDATOR] moduleName : "SHFolder.dll" 0
|
LINE.exe | [MODULE_VALIDATOR] moduleName : "version.dll" 0
|