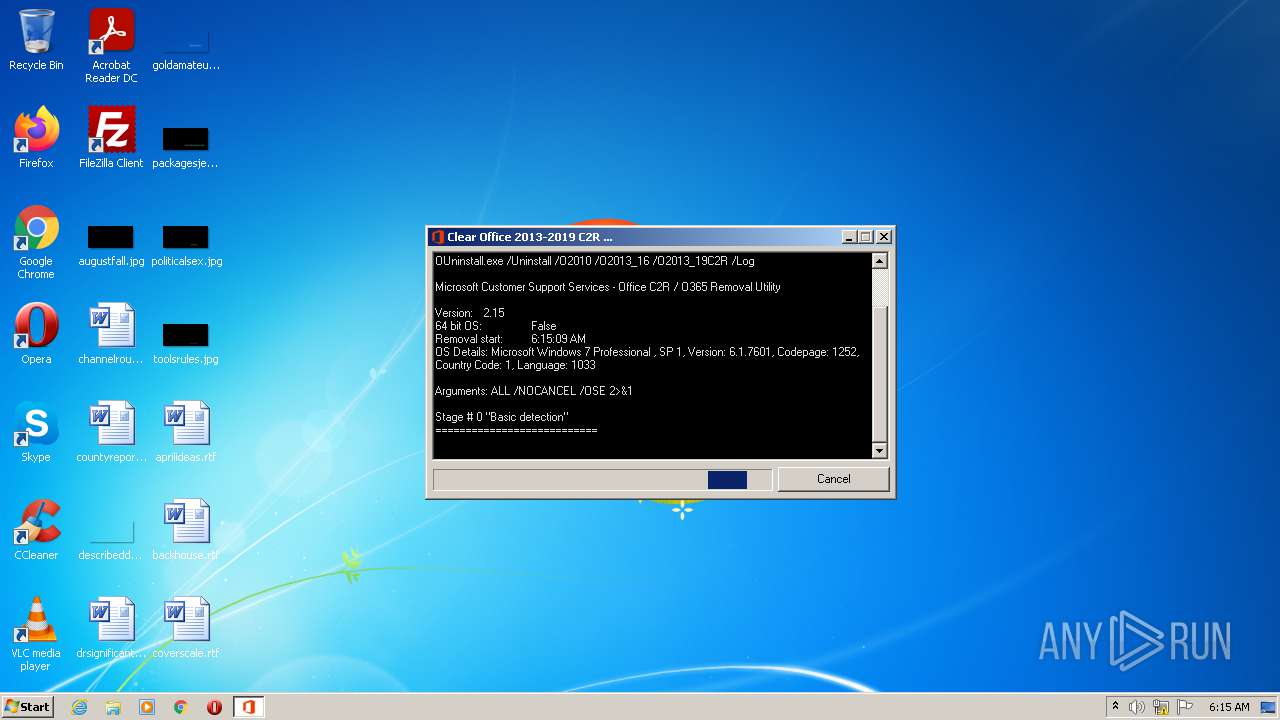
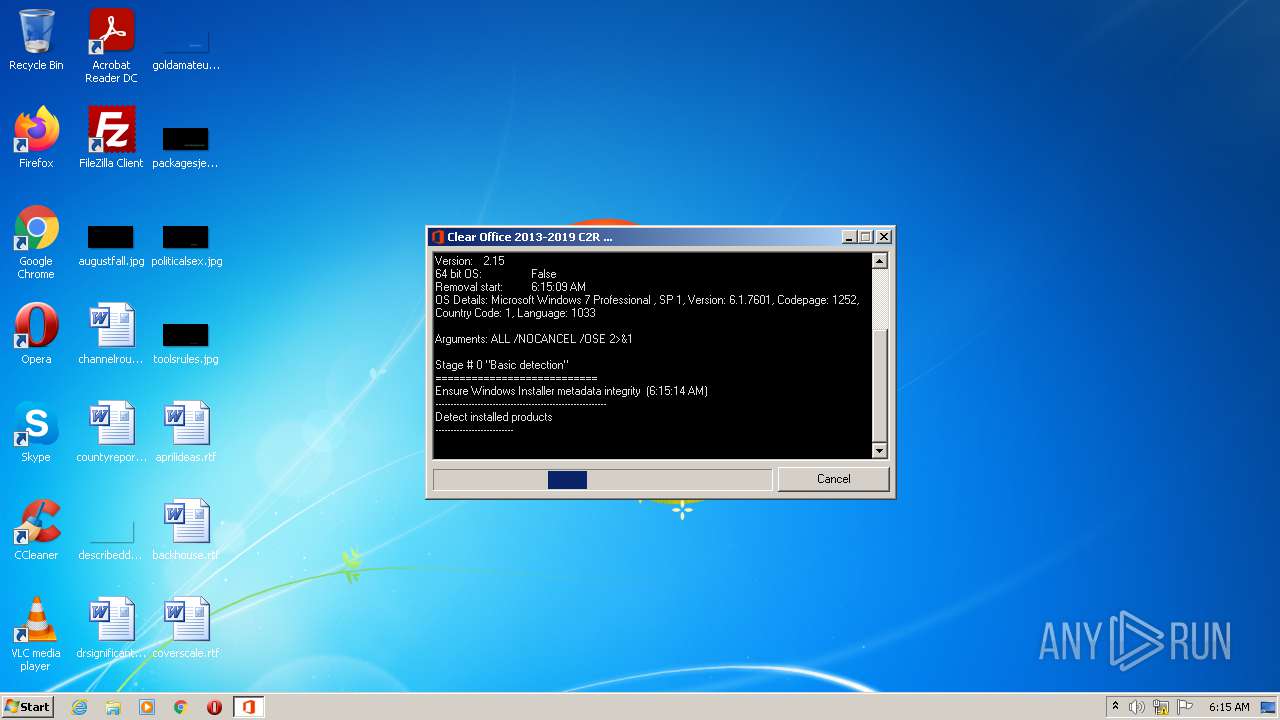
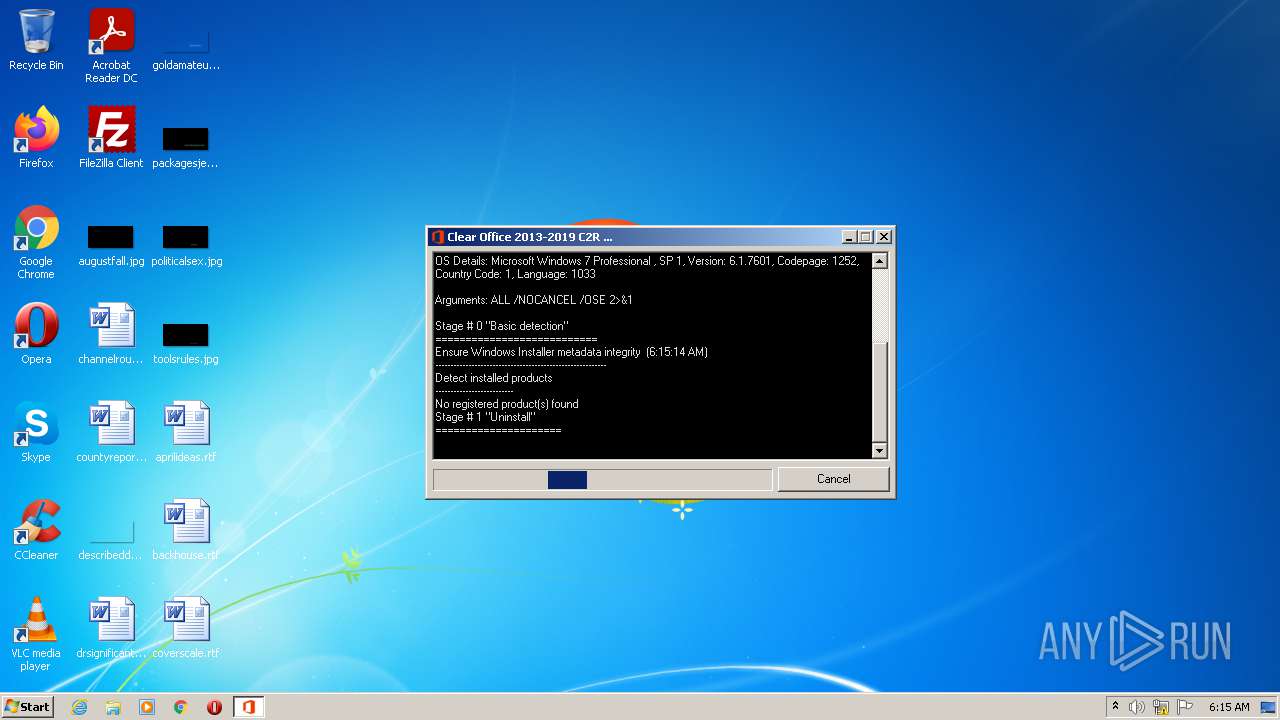
| File name: | OUninstall.exe |
| Full analysis: | https://app.any.run/tasks/a67619a3-8493-4109-90c9-aab8e99be981 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2021, 05:14:56 |
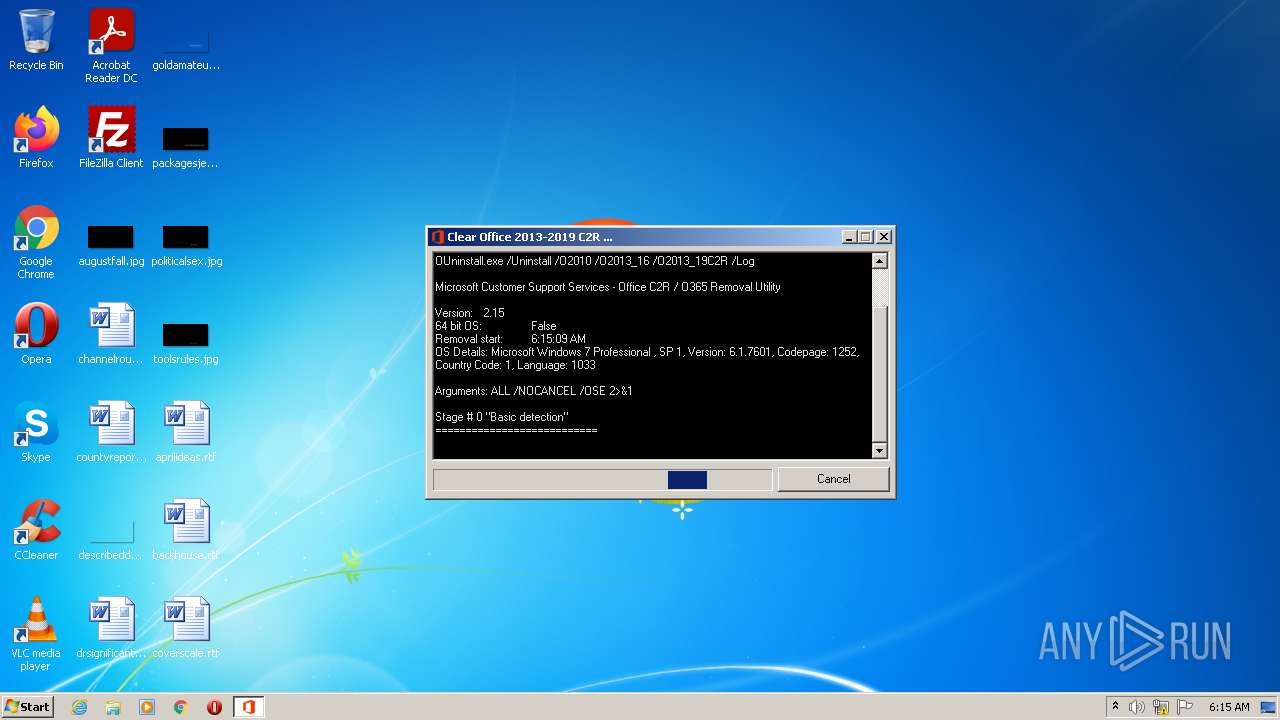
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 552047A49EC6D4F0FCC14937EA4473D3 |
| SHA1: | EF2558A409F3646E6E1A43F4F9723867E3719DAD |
| SHA256: | 08C90CDC4EE6C36644FA3B1C27ABA7CB2B650BF884E68EFA8E074B0E7E0EE647 |
| SSDEEP: | 24576:lbmHE1eD70YfgNbuJbbya4yveIksGanbSpkXPuiXRO1f+wE:d2IYfYbKvb4y/Gan3/3X0f+R |
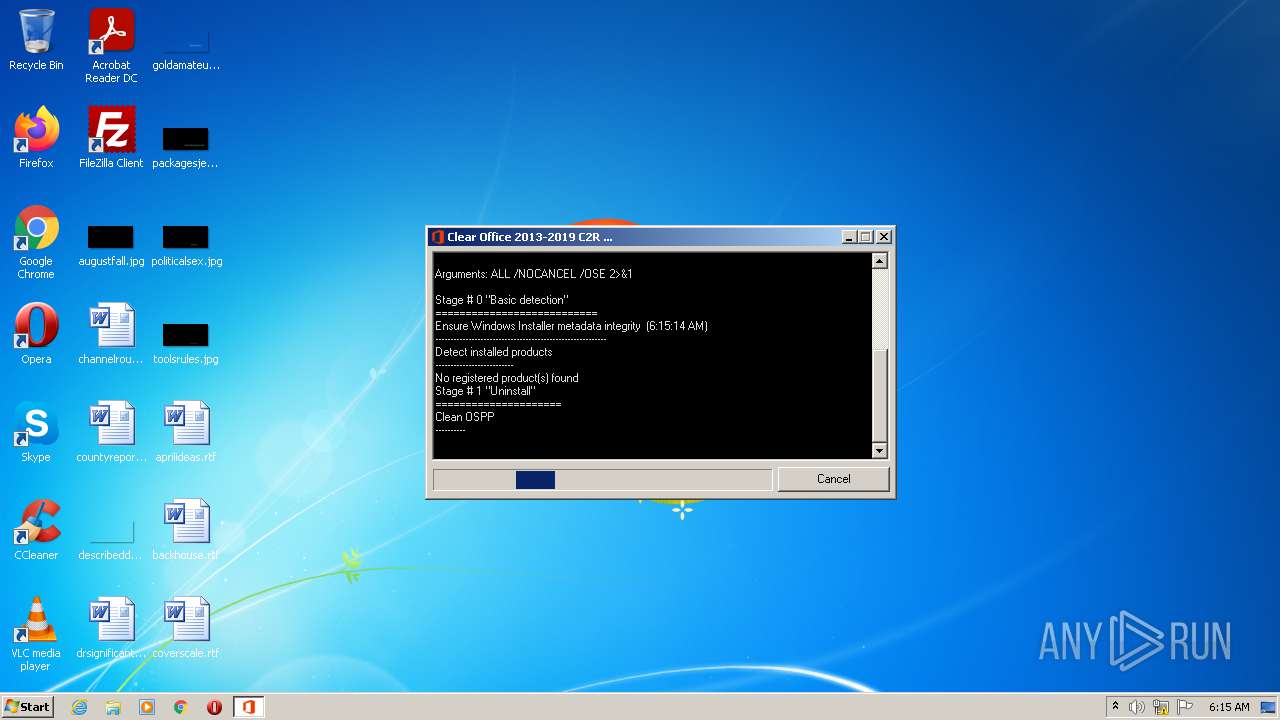
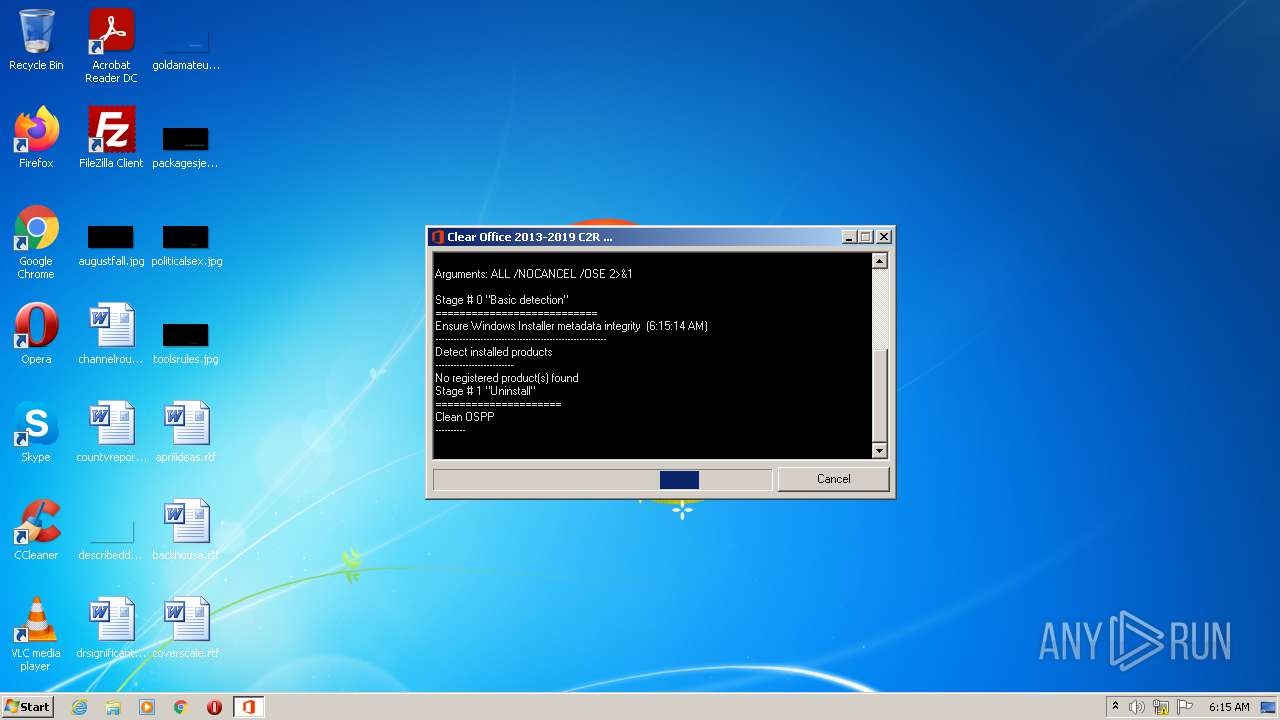
MALICIOUS
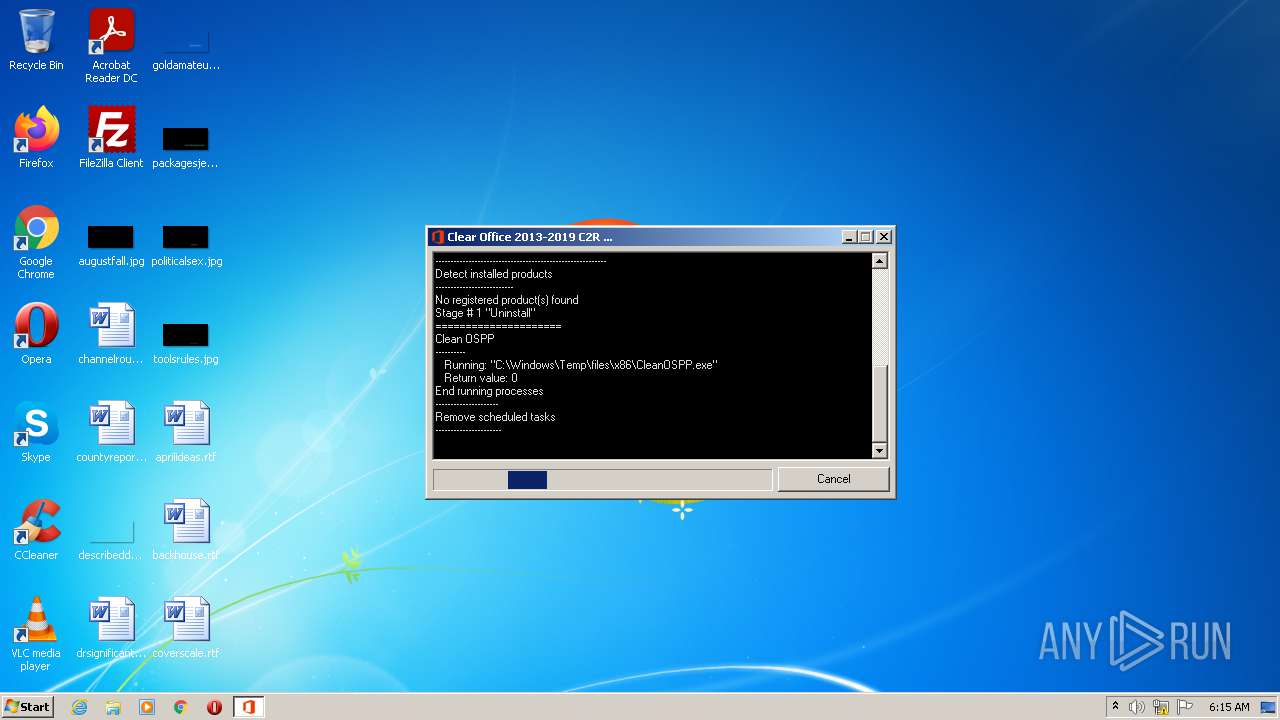
Drops executable file immediately after starts
- files.exe (PID: 2516)
Application was dropped or rewritten from another process
- files.exe (PID: 2516)
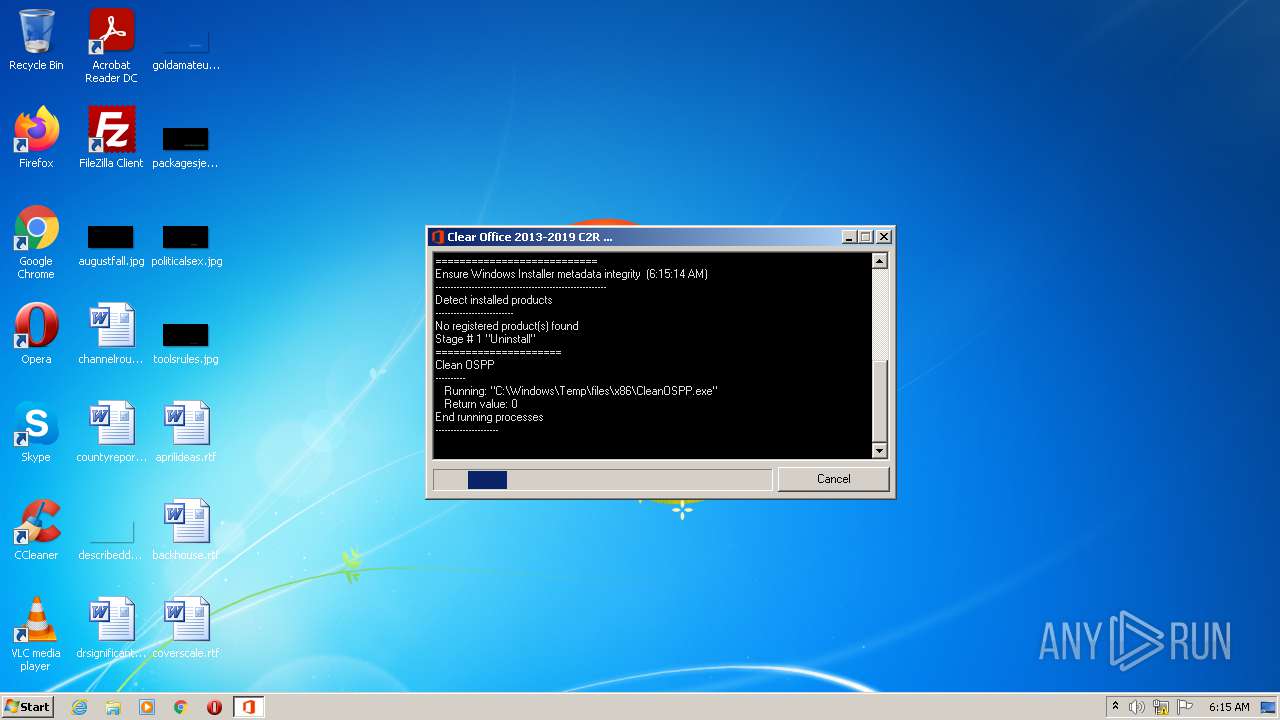
- CleanOSPP.exe (PID: 2028)
Loads dropped or rewritten executable
- CleanOSPP.exe (PID: 2028)
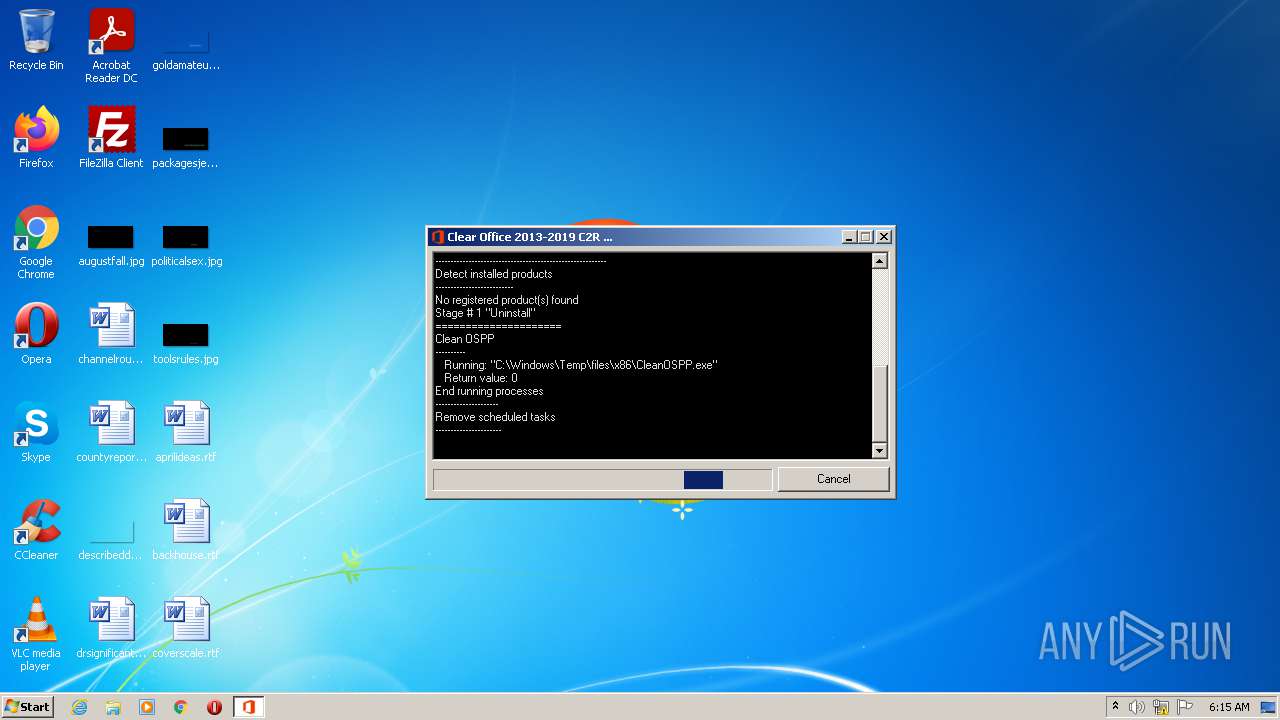
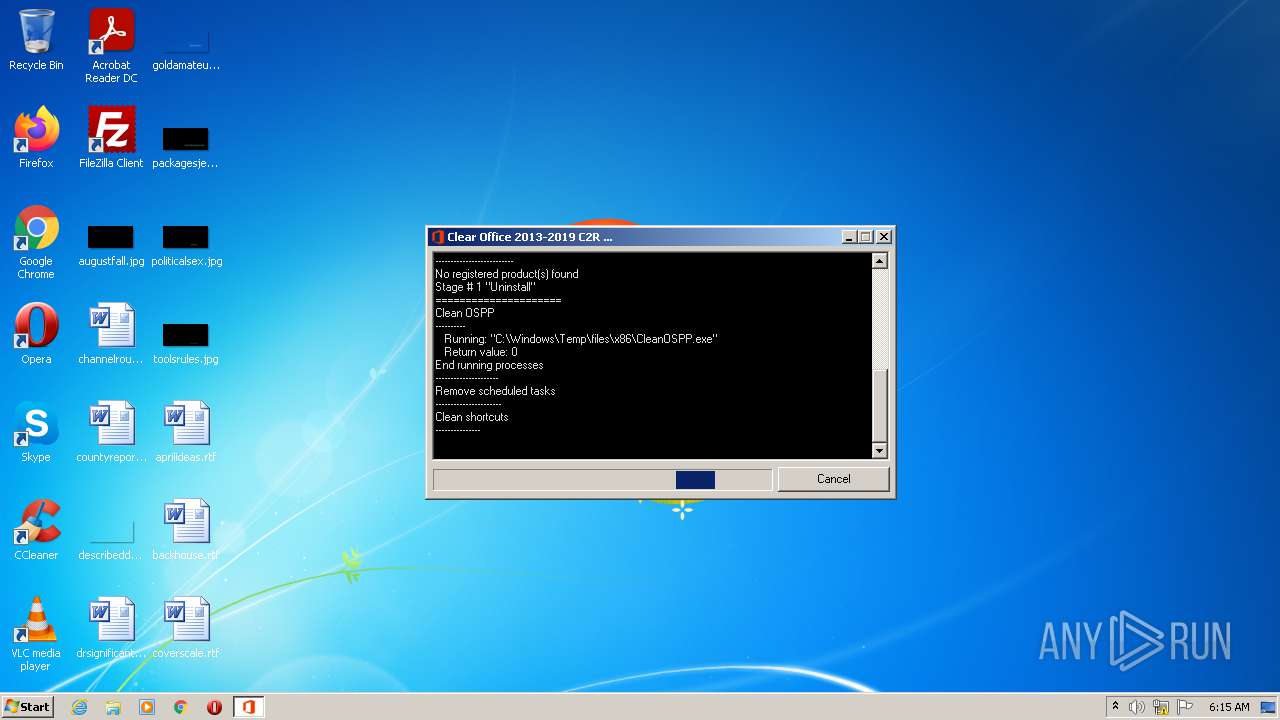
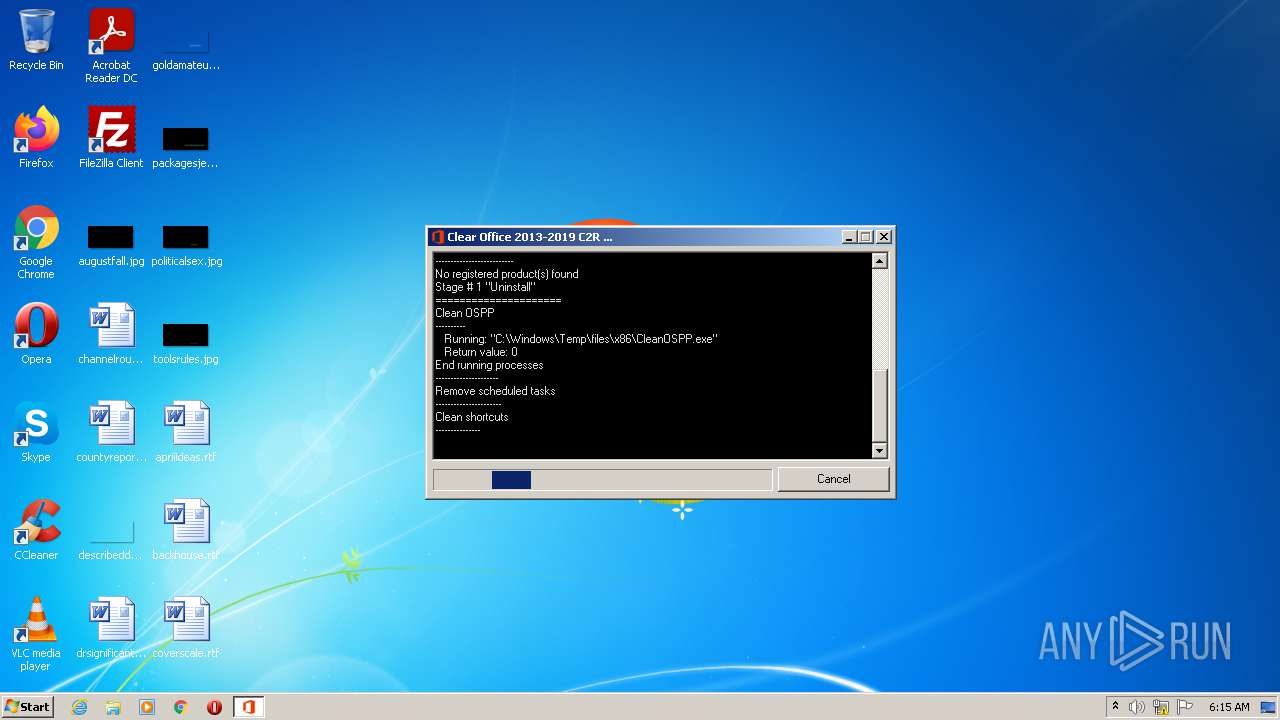
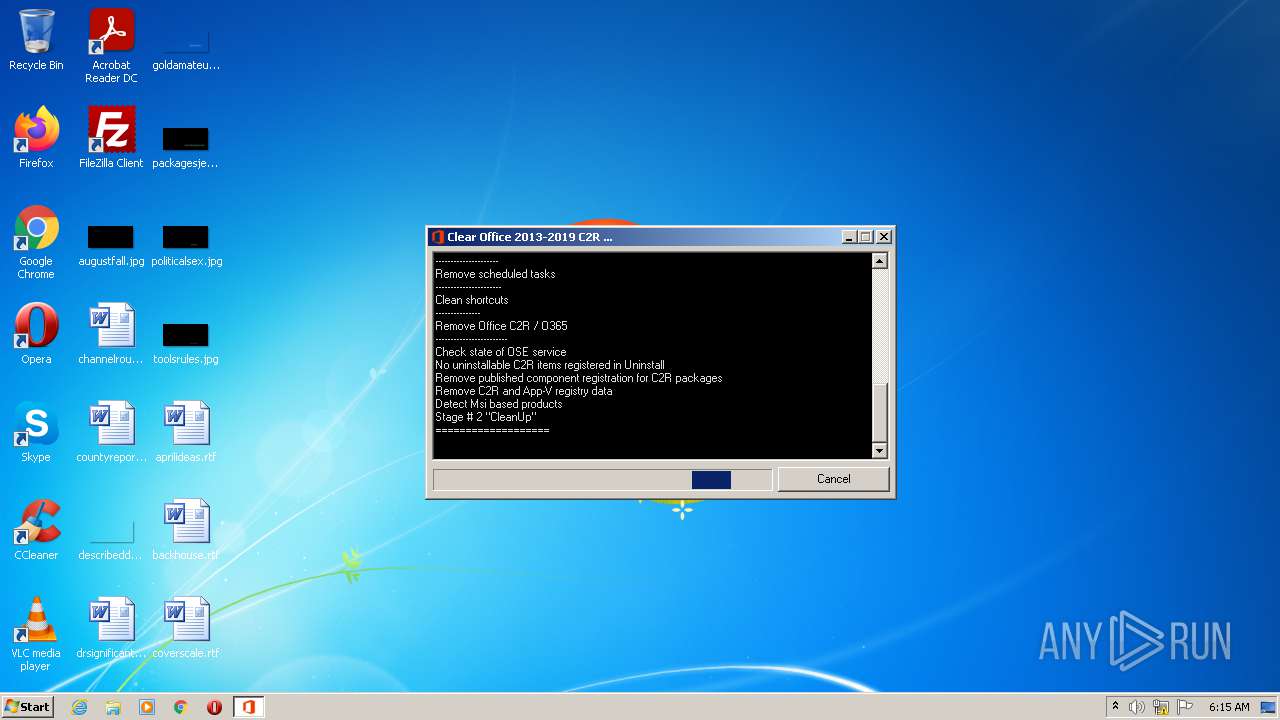
Uses Task Scheduler to run other applications
- cscript.exe (PID: 2684)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1508)
- schtasks.exe (PID: 2900)
- schtasks.exe (PID: 1000)
- schtasks.exe (PID: 3992)
- schtasks.exe (PID: 900)
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 1036)
- schtasks.exe (PID: 372)
- schtasks.exe (PID: 3512)
- schtasks.exe (PID: 2240)
- schtasks.exe (PID: 1564)
- schtasks.exe (PID: 2208)
- schtasks.exe (PID: 3432)
- schtasks.exe (PID: 2064)
- schtasks.exe (PID: 3772)
- schtasks.exe (PID: 2060)
- schtasks.exe (PID: 3220)
- schtasks.exe (PID: 712)
- schtasks.exe (PID: 3492)
- schtasks.exe (PID: 3228)
- schtasks.exe (PID: 3012)
Starts NET.EXE for service management
- cmd.exe (PID: 404)
SUSPICIOUS
Creates files in the Windows directory
- OUninstall.exe (PID: 3544)
- files.exe (PID: 2516)
Checks supported languages
- OUninstall.exe (PID: 3544)
- cmd.exe (PID: 2692)
- files.exe (PID: 2516)
- cscript.exe (PID: 2684)
- CleanOSPP.exe (PID: 2028)
- cmd.exe (PID: 404)
Executable content was dropped or overwritten
- files.exe (PID: 2516)
- OUninstall.exe (PID: 3544)
Starts CMD.EXE for commands execution
- OUninstall.exe (PID: 3544)
- cscript.exe (PID: 2684)
Drops a file that was compiled in debug mode
- files.exe (PID: 2516)
Removes files from Windows directory
- OUninstall.exe (PID: 3544)
Executes scripts
- OUninstall.exe (PID: 3544)
Reads the computer name
- cscript.exe (PID: 2684)
- CleanOSPP.exe (PID: 2028)
INFO
Checks Windows Trust Settings
- cscript.exe (PID: 2684)
Reads Microsoft Office registry keys
- CleanOSPP.exe (PID: 2028)
Checks supported languages
- schtasks.exe (PID: 1000)
- schtasks.exe (PID: 1508)
- schtasks.exe (PID: 3512)
- schtasks.exe (PID: 2900)
- schtasks.exe (PID: 3992)
- schtasks.exe (PID: 900)
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 1036)
- schtasks.exe (PID: 372)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 1564)
- schtasks.exe (PID: 2240)
- schtasks.exe (PID: 2208)
- net.exe (PID: 1160)
- net1.exe (PID: 1644)
- schtasks.exe (PID: 3432)
- schtasks.exe (PID: 2064)
- schtasks.exe (PID: 712)
- schtasks.exe (PID: 3492)
- schtasks.exe (PID: 3772)
- schtasks.exe (PID: 2060)
- schtasks.exe (PID: 3220)
- schtasks.exe (PID: 3012)
- schtasks.exe (PID: 3228)
Reads the computer name
- schtasks.exe (PID: 1508)
- schtasks.exe (PID: 2900)
- schtasks.exe (PID: 1000)
- schtasks.exe (PID: 3992)
- schtasks.exe (PID: 3512)
- schtasks.exe (PID: 900)
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 372)
- schtasks.exe (PID: 1036)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 2240)
- net1.exe (PID: 1644)
- schtasks.exe (PID: 3432)
- schtasks.exe (PID: 1564)
- schtasks.exe (PID: 2208)
- schtasks.exe (PID: 3772)
- schtasks.exe (PID: 2060)
- schtasks.exe (PID: 3220)
- schtasks.exe (PID: 712)
- schtasks.exe (PID: 2064)
- schtasks.exe (PID: 3492)
- schtasks.exe (PID: 3228)
- schtasks.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:02 10:31:30+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 987136 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 1789952 |
| EntryPoint: | 0x2a63e0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
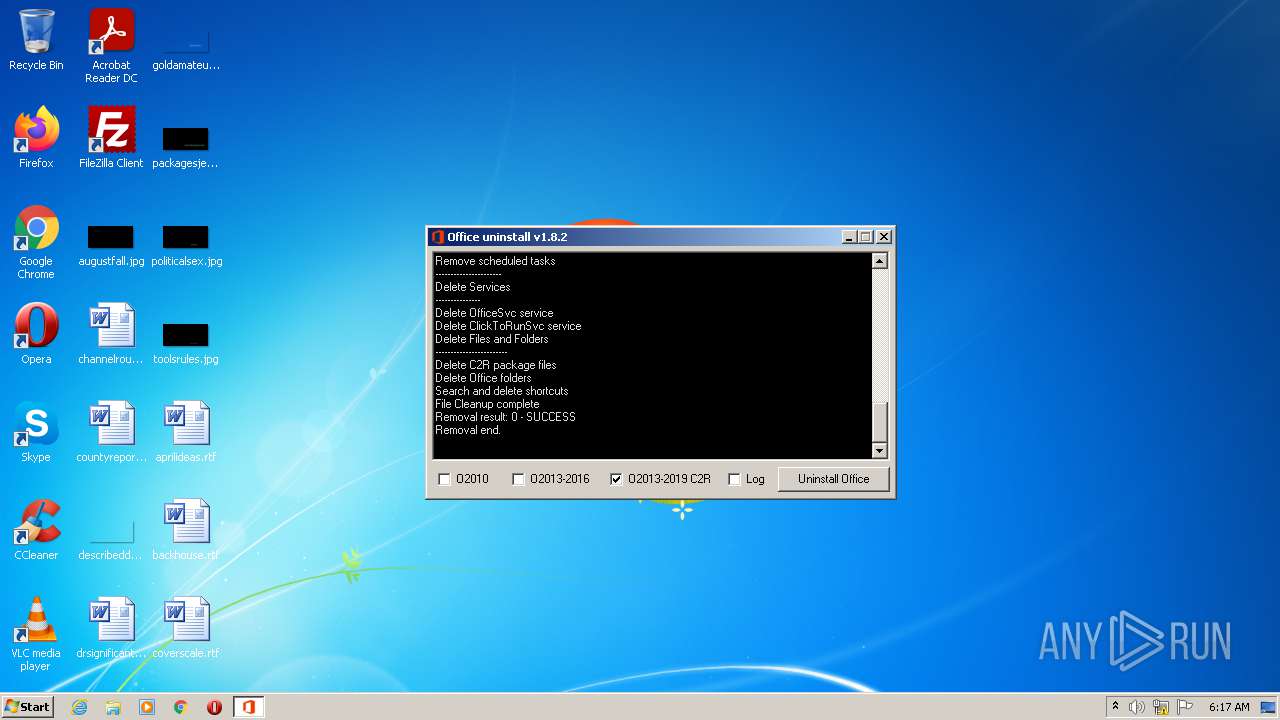
| FileVersionNumber: | 1.8.2.0 |
| ProductVersionNumber: | 1.8.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
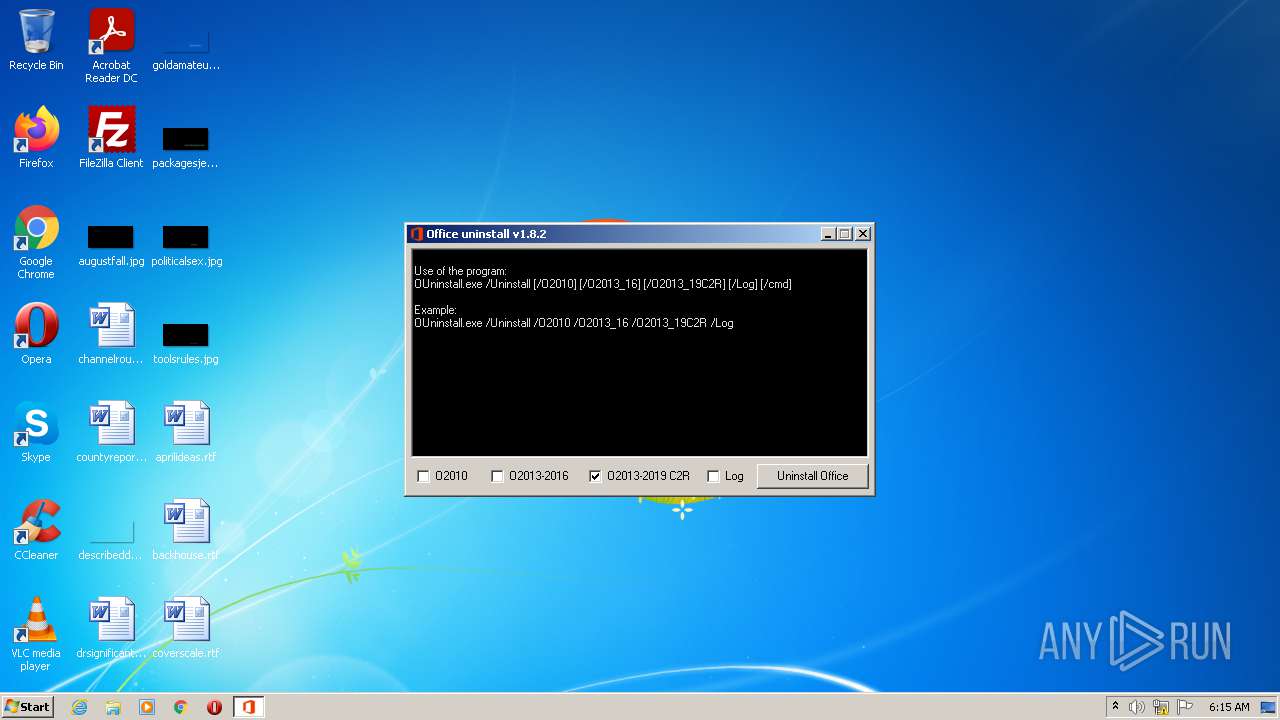
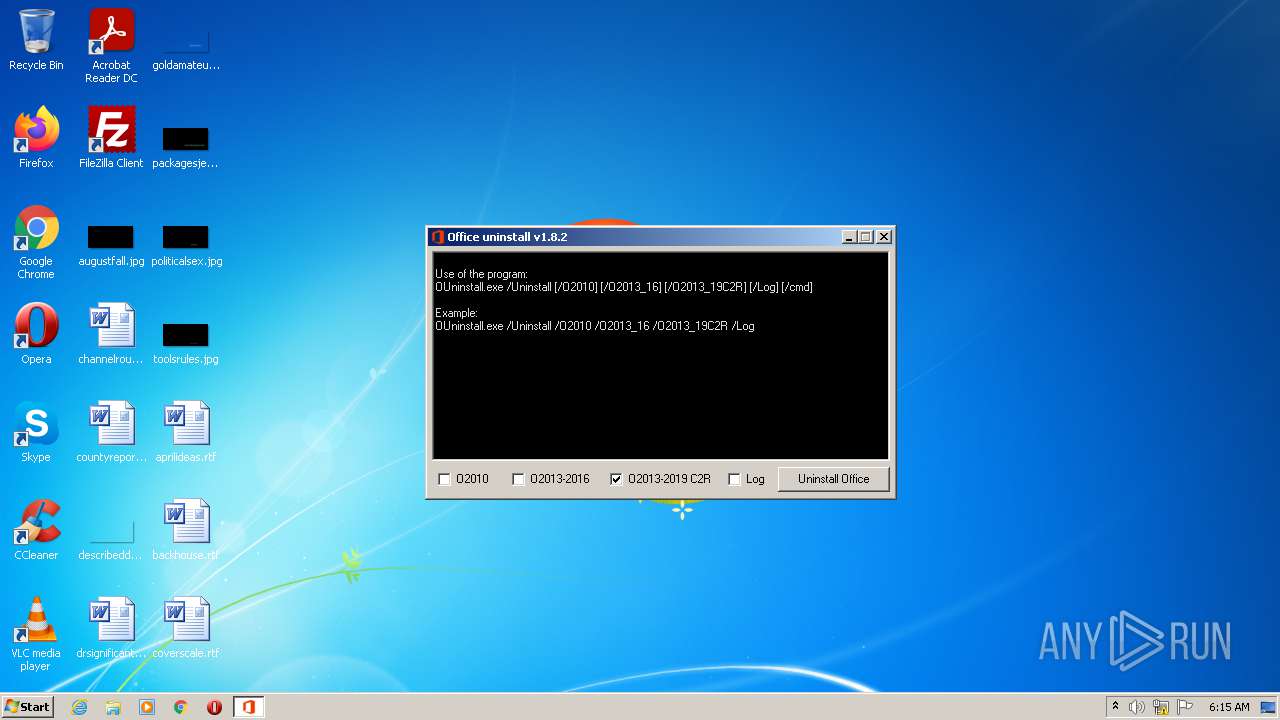
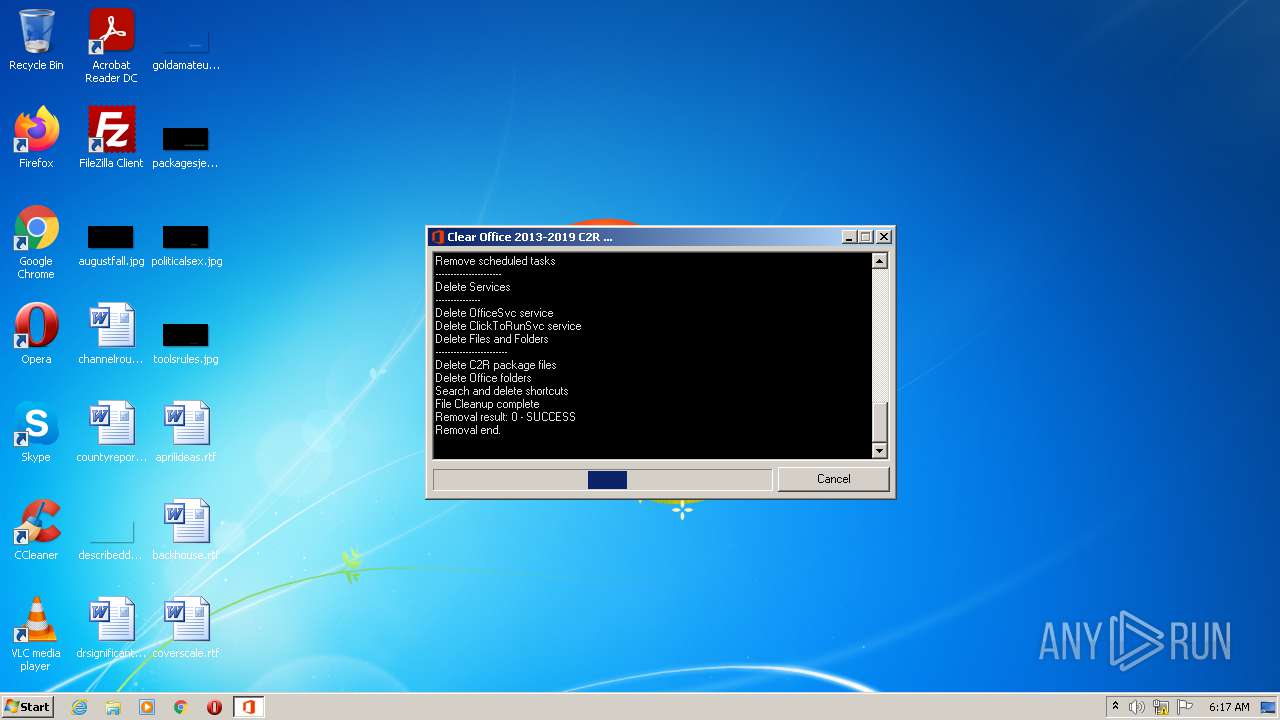
| ProductName: | Office 2010-2013-2016-2019 Uninstall |
| FileDescription: | Office 2010-2013-2016-2019 Uninstall |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2019 08:31:30 |
| Detected languages: |
|
| ProductName: | Office 2010-2013-2016-2019 Uninstall |
| FileDescription: | Office 2010-2013-2016-2019 Uninstall |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Oct-2019 08:31:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001B5000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001B6000 | 0x000F1000 | 0x000F0600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.84112 |
.rsrc | 0x002A7000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.96516 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
106
Monitored processes
35
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Windows\System32\schtasks.exe" /Delete /TN "\Microsoft\Office\Office Automatic Updates" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | "C:\Windows\System32\schtasks.exe" /Delete /TN "Office Background Streaming" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | "C:\Windows\System32\cmd.exe" /c net stop msiserver | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 712 | "C:\Windows\System32\schtasks.exe" /Delete /TN "\Microsoft\Office\OfficeTelemetryAgentFallBack" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Windows\System32\schtasks.exe" /Delete /TN "\Microsoft\Office\OfficeTelemetryAgentFallBack" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | "C:\Windows\System32\schtasks.exe" /Delete /TN C2RAppVLoggingStart /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | "C:\Windows\System32\schtasks.exe" /Delete /TN "\Microsoft\Office\OfficeTelemetryAgentLogOn" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | net stop msiserver | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | "C:\Windows\System32\schtasks.exe" /Delete /TN "Office Subscription Maintenance" /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1508 | "C:\Windows\System32\schtasks.exe" /Delete /TN FF_INTEGRATEDstreamSchedule /F | C:\Windows\System32\schtasks.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 026
Read events
1 000
Write events
26
Delete events
0
Modification events
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @"%systemroot%\system32\windowspowershell\v1.0\powershell.exe",-111 |
Value: Performs object-based (command-line) functions | |||
| (PID) Process: | (2684) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-738 |
Value: Start Internet Explorer without ActiveX controls or browser extensions. | |||
Executable files
5
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | OUninstall.exe | C:\Windows\Temp\files\OffScrubC2R.vbs | binary | |
MD5:E5CB0DC373006226AE1102E4EEC46811 | SHA256:2001F018DED30D79BD58F45DC18A9ECDC354AA30BEA02451CA297415A65EC1FD | |||
| 3544 | OUninstall.exe | C:\Windows\Temp\files\files.exe | executable | |
MD5:4776BC8E76B191C962F21BC8FB514FA5 | SHA256:3253269C607D6712398D1FA10C53CC1467633E5D3E58373EBDA9F6FA5CCC1D69 | |||
| 2516 | files.exe | C:\Windows\Temp\files\x86\cleanospp.exe | executable | |
MD5:5FD363D52D04AC200CD24F3BCC903200 | SHA256:3FDEFE2AD092A9A7FE0EDF0AC4DC2DE7E5B9CE6A0804F6511C06564194966CF9 | |||
| 2516 | files.exe | C:\Windows\Temp\files\x64\cleanospp.exe | executable | |
MD5:162AB955CB2F002A73C1530AA796477F | SHA256:5CE462E5F34065FC878362BA58617FAB28C22D631B9D836DDDCF43FB1AD4DE6E | |||
| 2516 | files.exe | C:\Windows\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 2684 | cscript.exe | C:\Users\admin\AppData\Local\Temp\OffScrubC2R\ScrubRetValFile.txt | text | |
MD5:07DDC9B29E487769E638DA3E8277818E | SHA256:44119689FD681E69B50FF356FACCD21BC3DFBA827564DC1540910E7EE4FED75E | |||
| 2516 | files.exe | C:\Windows\Temp\files\x86\msvcr100.dll | executable | |
MD5:BF38660A9125935658CFA3E53FDC7D65 | SHA256:60C06E0FA4449314DA3A0A87C1A9D9577DF99226F943637E06F61188E5862EFA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | svchost.exe | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |
— | — | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |