| URL: | https://doc-0o-5o-docs.googleusercontent.com/docs/securesc/ha0ro937gcuc7l7deffksulhg5h7mbp1/jqip7vm7o6flmbaqghqt6amspc5b7i66/1558368000000/12685595860439926623/*/1CKwT-loVivwmNZy7sNT3Gg4W_hht__ZX?e=download |
| Full analysis: | https://app.any.run/tasks/3b68f5be-4223-4efd-bbd3-db546b69d8bb |
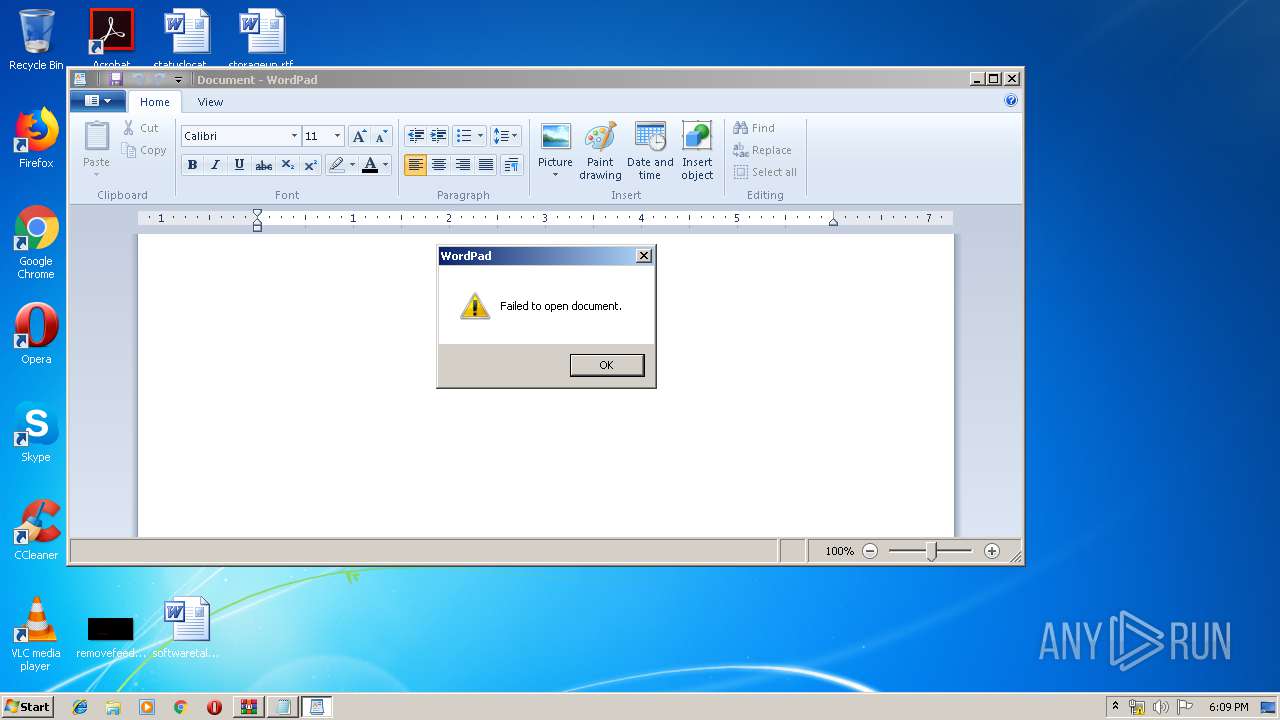
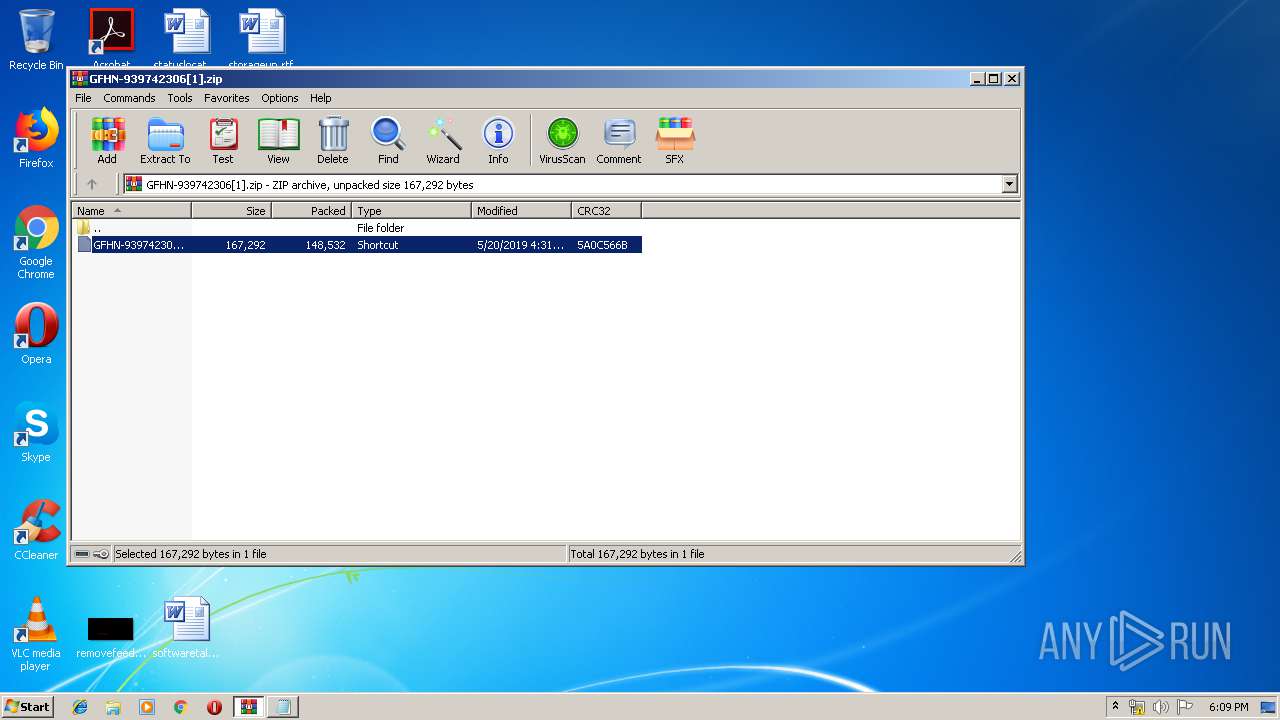
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 17:09:00 |
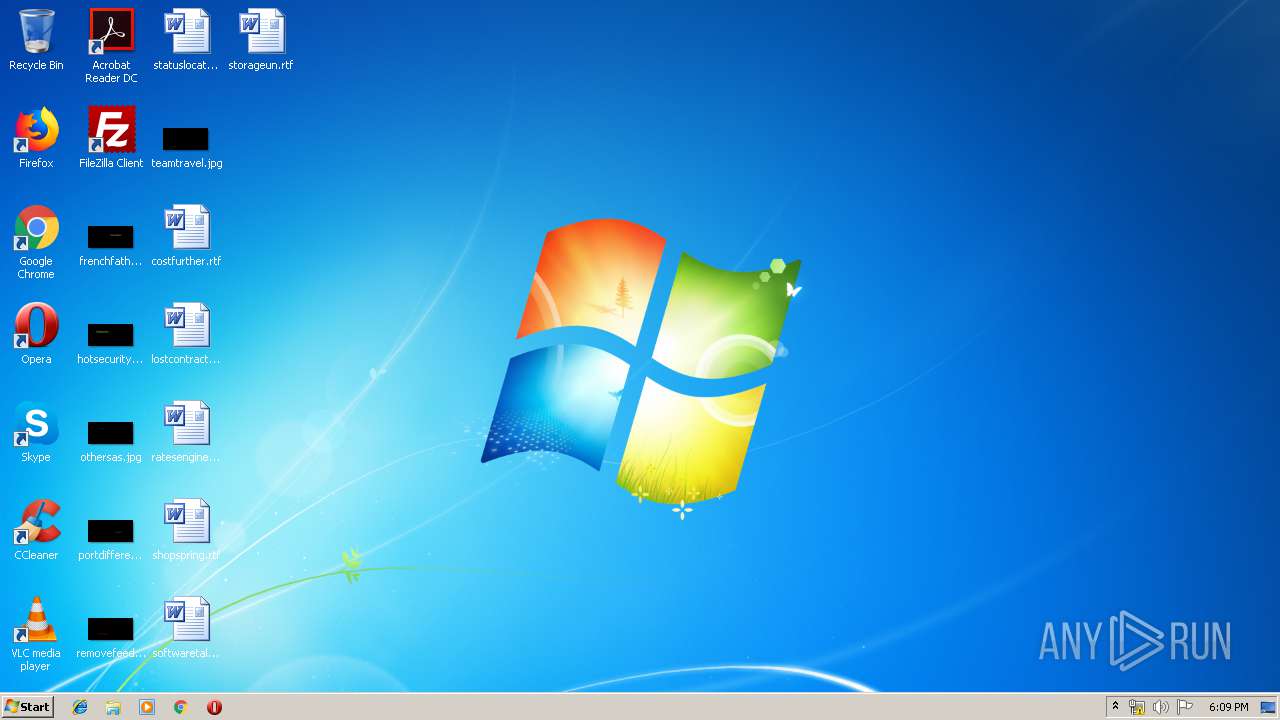
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CBFCD237FDAB4683C72FA7D9E9CC5BDC |
| SHA1: | E3D4A23736A6A91F0AEA7721C6B073108A245522 |
| SHA256: | 08BE69F1115FAAE727E4277CF205A021ACBA0E4E3987E0717265FB76336A05DF |
| SSDEEP: | 6:2SfVvCGNHBTCezTp48Dy5m3853MUmomWM3DLI:2W6GNHBT5ztdGj3hRyE |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3224)
- cmd.exe (PID: 3880)
- cmd.exe (PID: 2796)
Application was dropped or rewritten from another process
- D.exe (PID: 1824)
- D.exe (PID: 1532)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 1480)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 1728)
- cmd.exe (PID: 1976)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 3720)
Known privilege escalation attack
- DllHost.exe (PID: 3132)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 1532)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2744)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 2920)
- powershell.exe (PID: 1492)
- powershell.exe (PID: 1396)
Executable content was dropped or overwritten
- powershell.exe (PID: 2744)
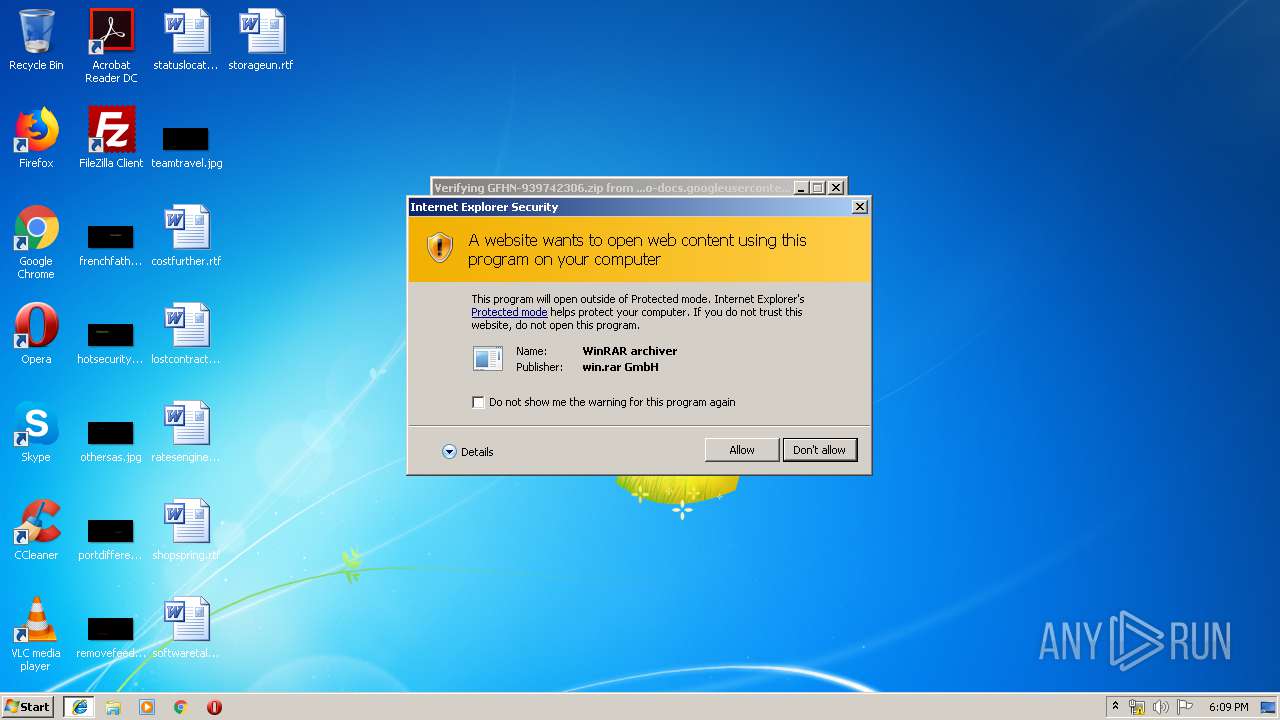
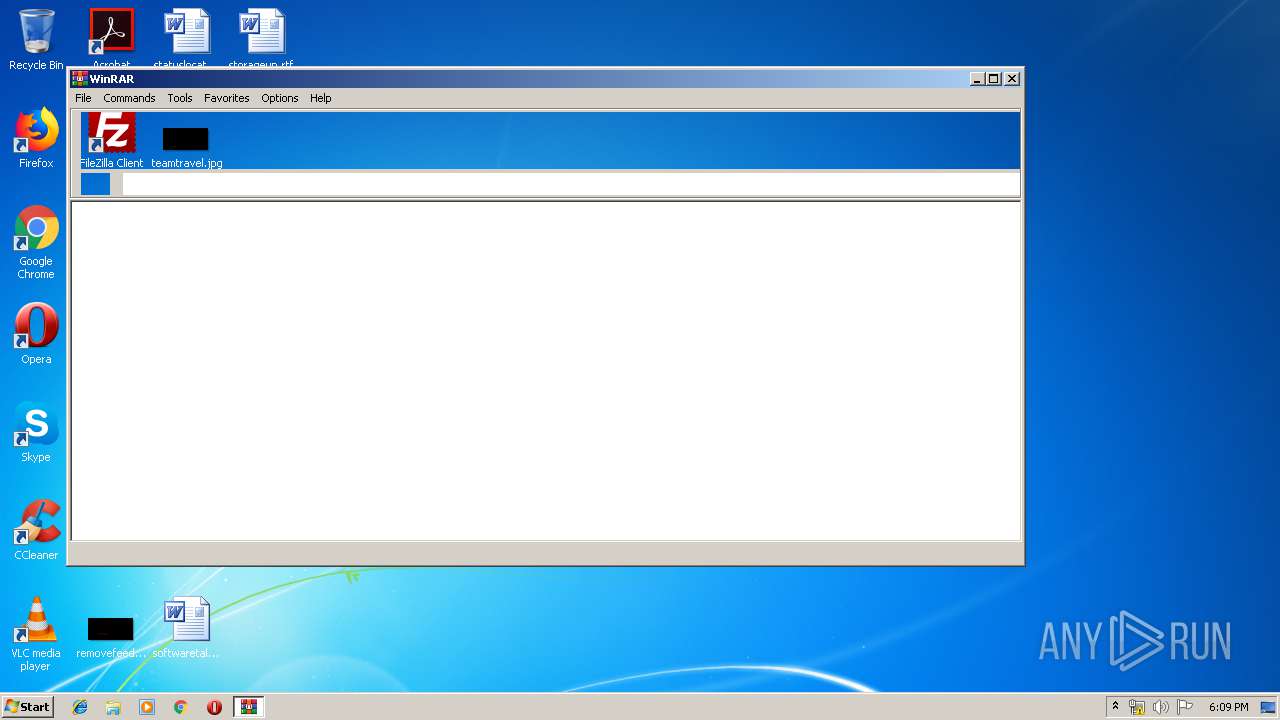
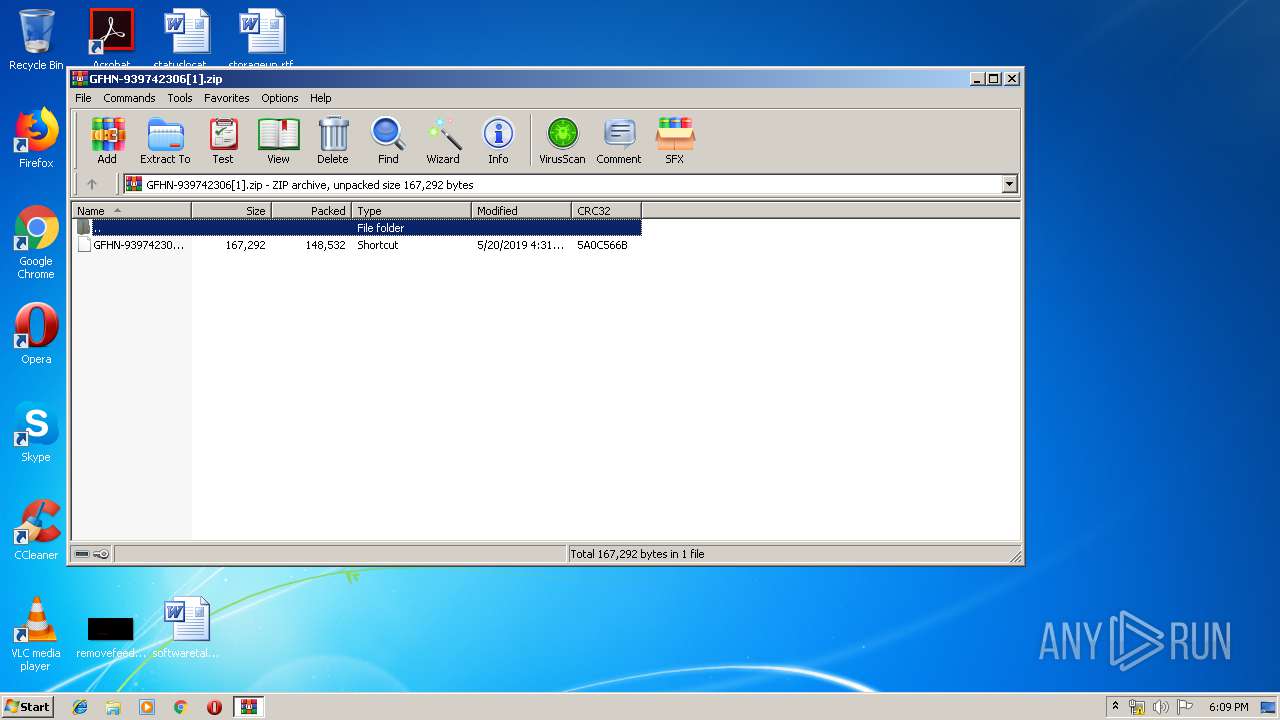
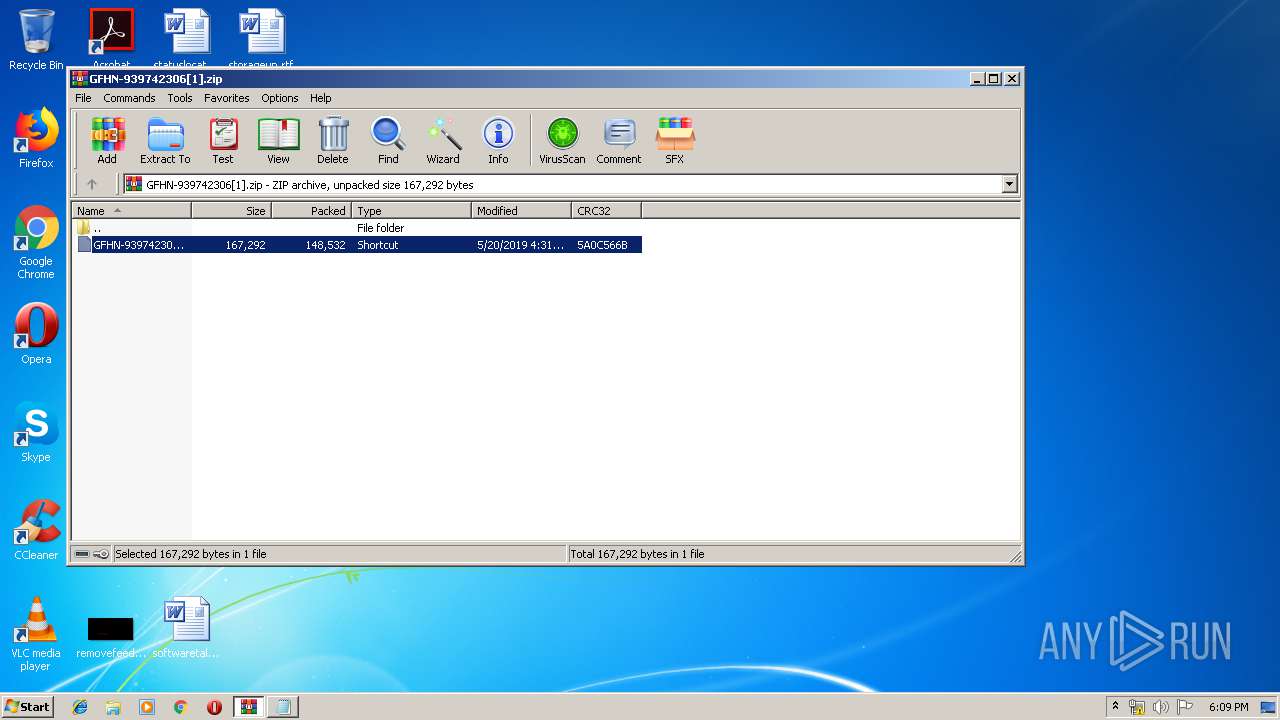
Starts CMD.EXE for commands execution
- D.exe (PID: 1824)
- D.exe (PID: 1532)
- WinRAR.exe (PID: 3676)
Executes PowerShell scripts
- cmd.exe (PID: 636)
- cmd.exe (PID: 3608)
Executed via COM
- DllHost.exe (PID: 3132)
INFO
Application launched itself
- iexplore.exe (PID: 3368)
Reads settings of System Certificates
- powershell.exe (PID: 2744)
- iexplore.exe (PID: 3368)
Creates files in the user directory
- iexplore.exe (PID: 2884)
Changes internet zones settings
- iexplore.exe (PID: 3368)
Changes settings of System certificates
- iexplore.exe (PID: 3368)
Reads Internet Cache Settings
- iexplore.exe (PID: 3368)
- iexplore.exe (PID: 2884)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
33
Malicious processes
8
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1492 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\AppData\Local\Temp\D.exe" | C:\Users\admin\AppData\Local\Temp\D.exe | — | DllHost.exe | |||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: HIGH Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
| 1728 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1824 | C:\Users\admin\AppData\Local\Temp/d | C:\Users\admin\AppData\Local\Temp\D.exe | — | cmd.exe | |||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
| 1976 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2008 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 643
Read events
2 233
Write events
404
Delete events
6
Modification events
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {01F6C0E9-7B22-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050001001400110009001500DB02 | |||
Executable files
1
Suspicious files
14
Text files
10
Unknown types
6
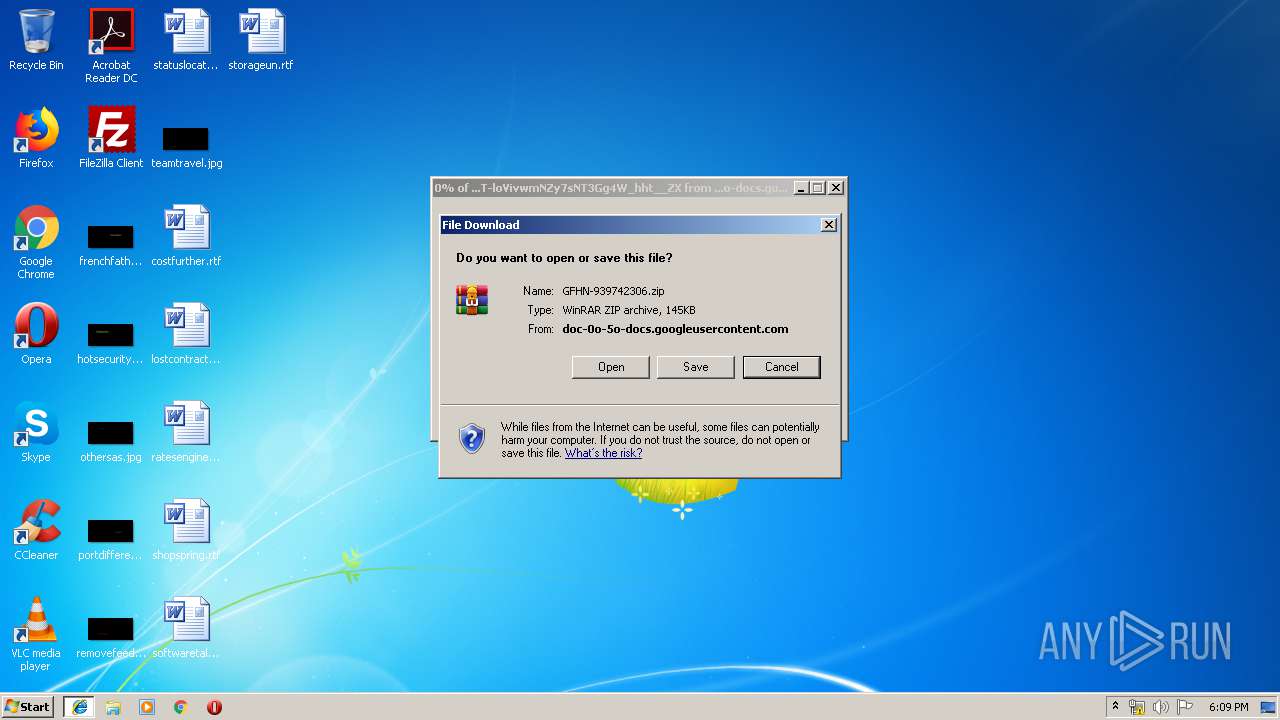
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF50AB3CB598DC942C.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4E8347E081F0FFCE.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{01F6C0E9-7B22-11E9-A09E-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QMOF15WRK4WUG626CJWA.temp | — | |
MD5:— | SHA256:— | |||
| 2884 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{01F6C0EA-7B22-11E9-A09E-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2884 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KWXW1CAXKRGOPC26LDRQ.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
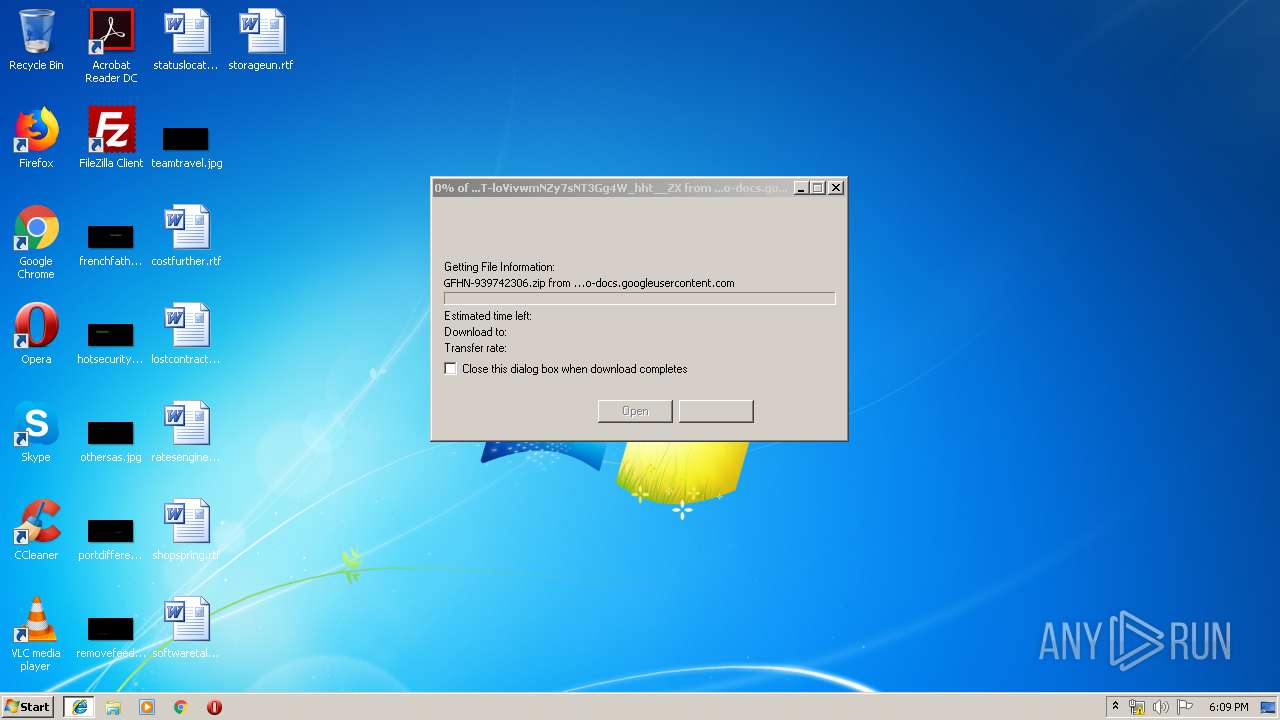
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3368 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | iexplore.exe | 172.217.22.33:443 | doc-0o-5o-docs.googleusercontent.com | Google Inc. | US | whitelisted |
3368 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2744 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
doc-0o-5o-docs.googleusercontent.com |
| shared |
www.bing.com |
| whitelisted |
www.braintrainersuk.com |
| malicious |