| File name: | Correo.msg |
| Full analysis: | https://app.any.run/tasks/92931d5c-4f5d-46af-8914-2262fa6e6d21 |
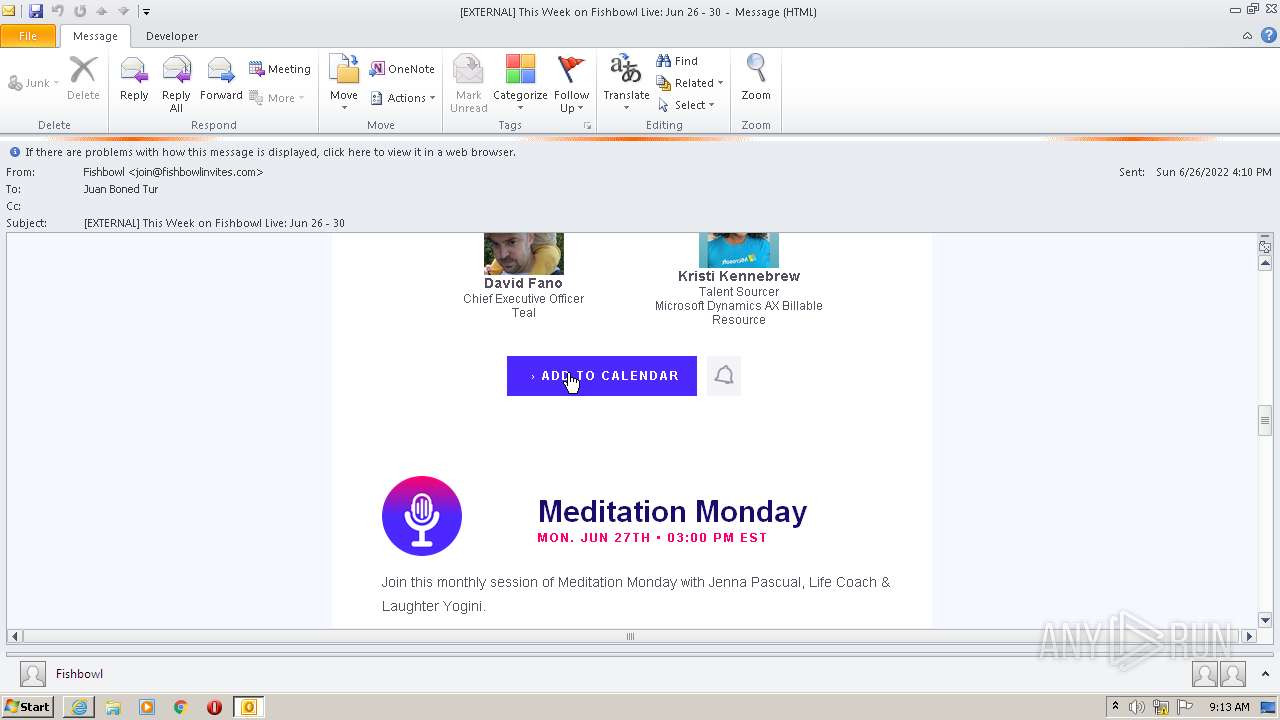
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 08:10:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | AA64C38D2211F8416F836B97F23E3E5A |
| SHA1: | E7F2D21C433550624AE17073E1376DBA94B9C4F1 |
| SHA256: | 08A8A0328E959B40A9905ED491FA71ED36A601046A313E8F0598C1AC3B0CA46A |
| SSDEEP: | 3072:BGTzC8aLXOKzZ2UFdSzq/5NcCF+4gAjyw9vLIifQWZ2PYL4q/hh:MTOxOcsUF8zq/S4wq/ |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2596)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2596)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 956)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 2596)
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 2664)
Checks supported languages
- OUTLOOK.EXE (PID: 2596)
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 956)
Checks Windows Trust Settings
- OUTLOOK.EXE (PID: 2596)
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 956)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2596)
- iexplore.exe (PID: 2204)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2596)
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 956)
Searches for installed software
- OUTLOOK.EXE (PID: 2596)
Changes internet zones settings
- iexplore.exe (PID: 2204)
Application launched itself
- iexplore.exe (PID: 2204)
Reads internet explorer settings
- iexplore.exe (PID: 1380)
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 956)
Reads the date of Windows installation
- iexplore.exe (PID: 2204)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2204)
Changes settings of System certificates
- iexplore.exe (PID: 2204)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (45.3) |
|---|---|---|
| .oft | | | Outlook Form Template (26.5) |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2204 CREDAT:3413271 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2204 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
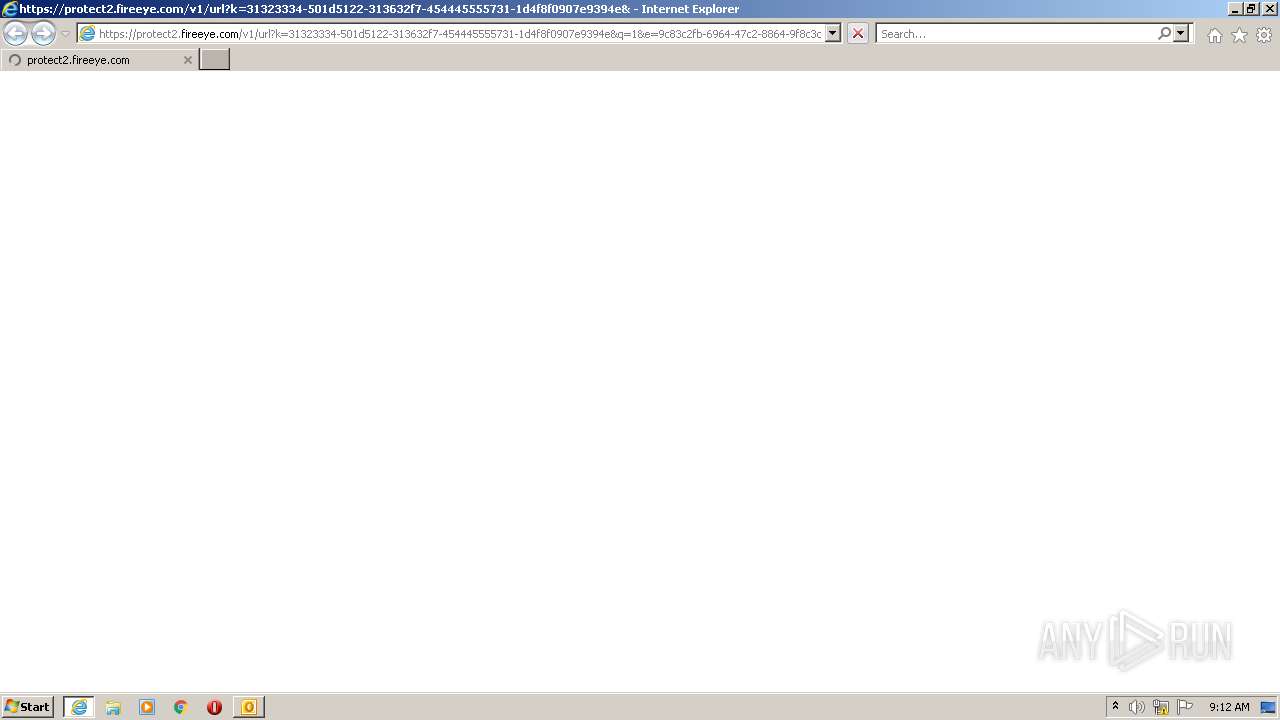
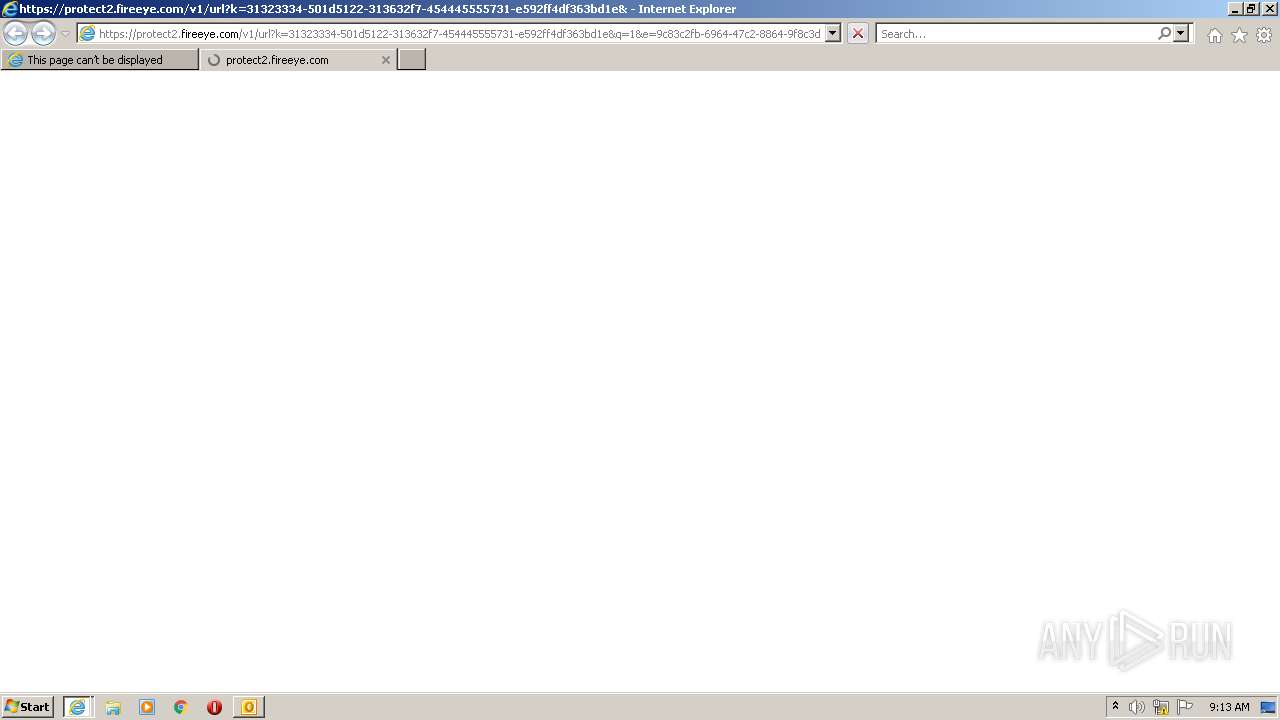
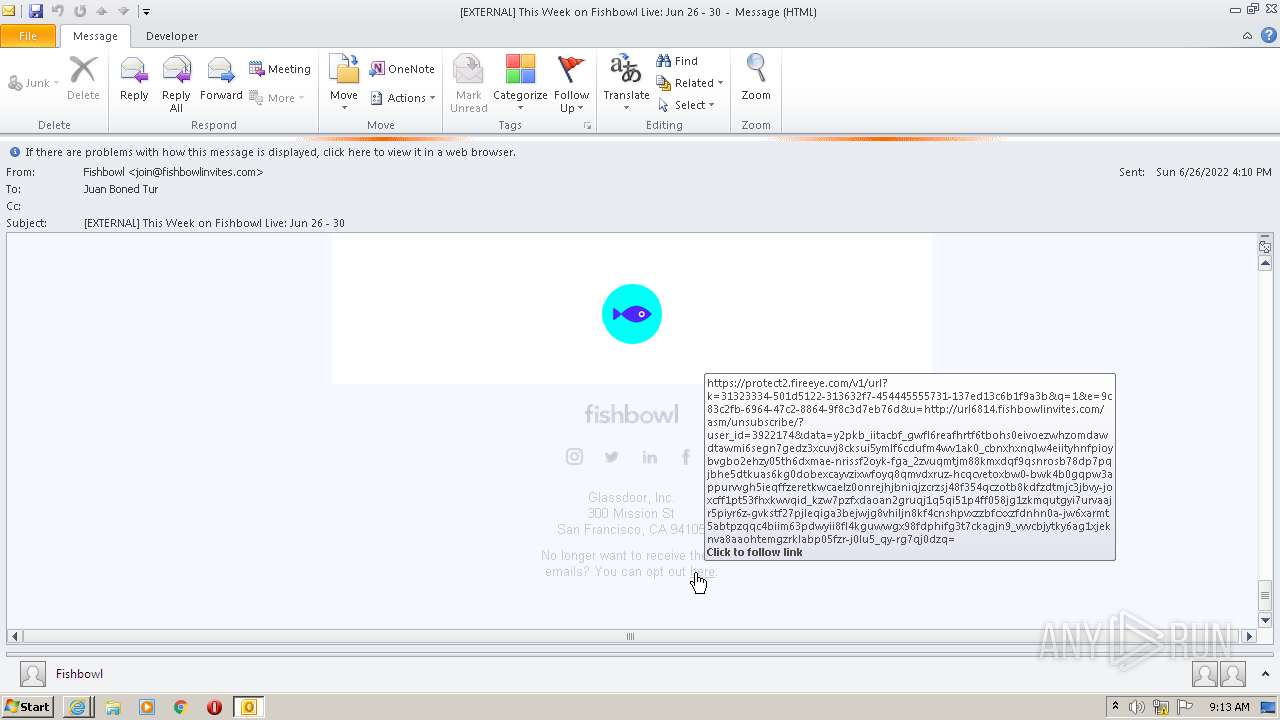
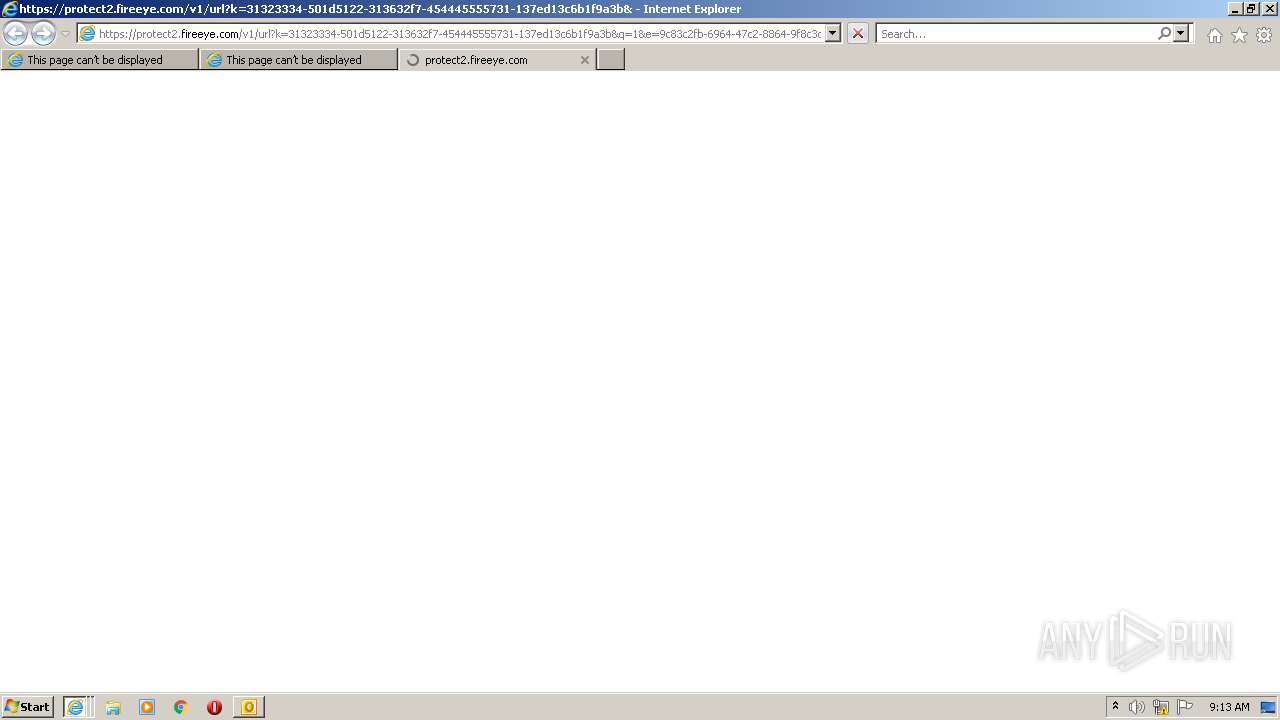
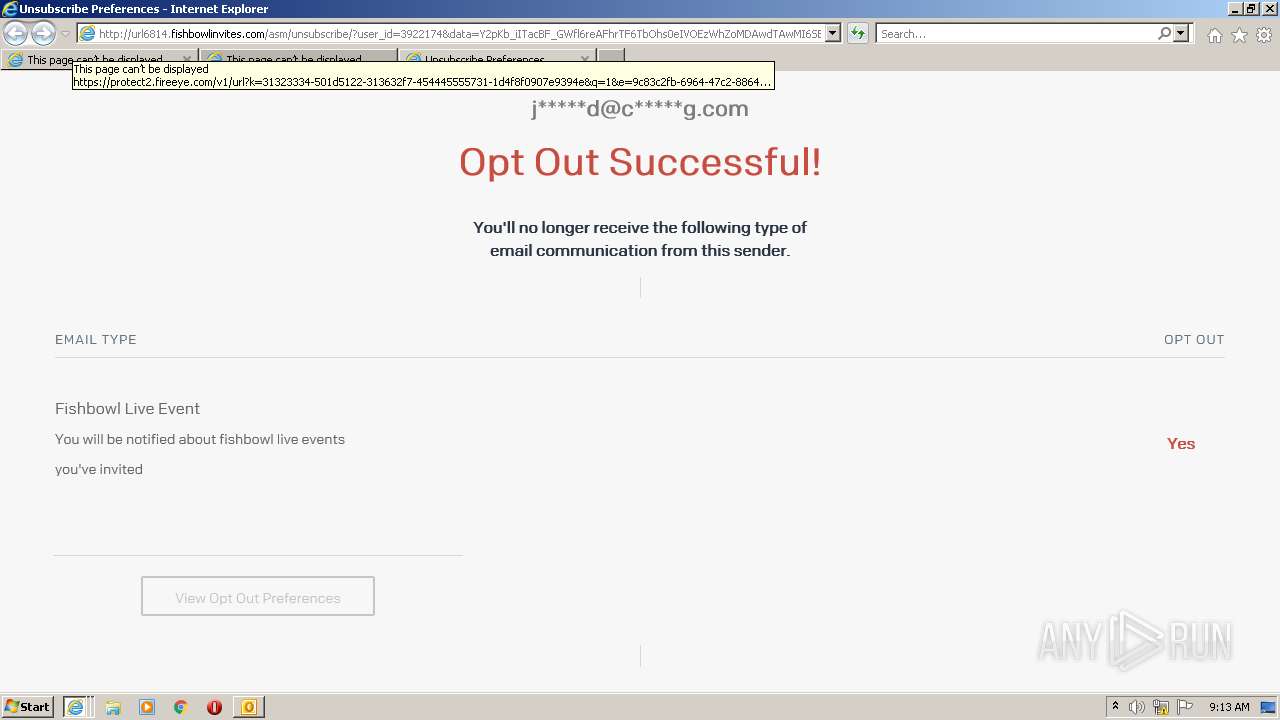
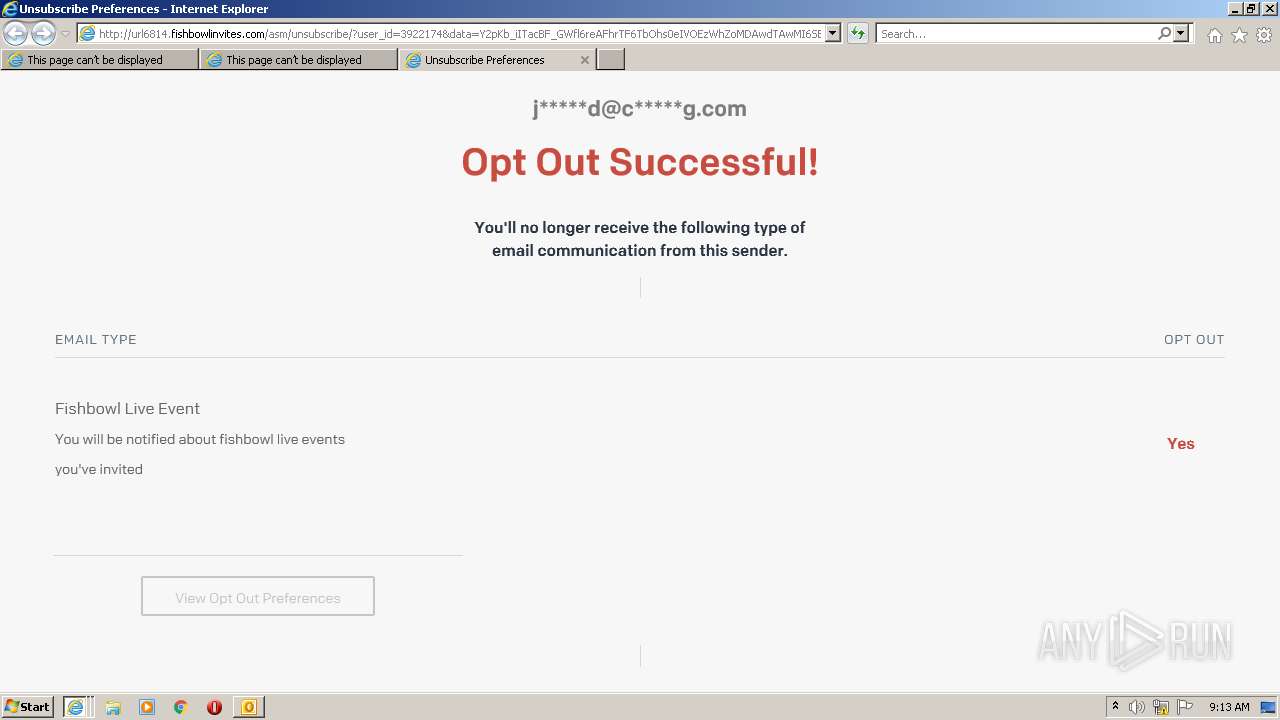
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" https://protect2.fireeye.com/v1/url?k=31323334-501d5122-313632f7-454445555731-1d4f8f0907e9394e&q=1&e=9c83c2fb-6964-47c2-8864-9f8c3d7eb76d&u=https%3A%2F%2Fjoinfishbowl.com%2Flive_trkptkoga5 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Correo.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2204 CREDAT:660747 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
34 874
Read events
34 083
Write events
766
Delete events
25
Modification events
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2596) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
23
Text files
59
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5C7E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_059556B24D7ED4478EF9A4E41AAEC333.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_107963688EA810478306D5DA2DAB7A10.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_7A0376D5E8E713409A8975AE18231867.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_CB070ECFE3B6434FB9D8C431ACF96B3F.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
52
DNS requests
20
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2204 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2596 | OUTLOOK.EXE | GET | 200 | 18.66.107.167:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | der | 660 b | whitelisted |
2596 | OUTLOOK.EXE | GET | 200 | 13.32.118.119:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2596 | OUTLOOK.EXE | GET | 200 | 18.66.242.155:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2204 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2596 | OUTLOOK.EXE | GET | 200 | 143.204.101.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2596 | OUTLOOK.EXE | GET | 200 | 167.89.123.124:80 | http://url6814.fishbowlinvites.com/wf/open?upn=nAITq6FnM0Z-2BzwYFZ6zErXhbXV8wfg2mOpXkRr7zKoBMvzO1RhsFHolJewPeGQJKzjg-2B-2FcYZZLWbqjpk9eTVn0n0xWxyMxIh3giAcqN7pQe5GFFjZ7v9OweDeCcRWPHSufuduLgQt2G2cqqJa7kXB5tk5koo8-2BdNZgkdm2RSHrMCqNOKYj0idOZ9SrScbbfdPhgG6mXtT8OGKSpPzr0iH-2FBjn8S-2F7eLNPFeFPptE5woGusxleM31jHxxYvBDm9VF3luidl7c2upKNkjsP4Jl0y04rP5LufY-2F5KMv-2BvKmDd9ohAz6S1Y5fcf-2BcpqC-2FLr2E-2BlmcXheJDRlkddd7z7zW-2FKBLOEB-2FYO7hqVK7d3vgj-2FR3kF-2BMBfMv-2FM-2BiQAfPnasnPY99lPdcbXg9ezzMkH-2FSfzI1vrjiVMFj8nHrp6-2FUyM-3D | US | image | 43 b | suspicious |
2204 | iexplore.exe | GET | 404 | 167.89.118.52:80 | http://url6814.fishbowlinvites.com/favicon.ico | US | html | 162 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2596 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2596 | OUTLOOK.EXE | 18.66.248.58:443 | dslntlv9vhjr4.cloudfront.net | Massachusetts Institute of Technology | US | suspicious |
2596 | OUTLOOK.EXE | 167.89.123.124:80 | url6814.fishbowlinvites.com | SendGrid, Inc. | US | suspicious |
2596 | OUTLOOK.EXE | 18.66.107.167:80 | crl.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
1380 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2204 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1380 | iexplore.exe | 13.57.99.90:443 | joinfishbowl.com | Amazon.com, Inc. | US | suspicious |
2664 | iexplore.exe | 162.159.246.125:443 | protect2.fireeye.com | Cloudflare Inc | — | suspicious |
2664 | iexplore.exe | 13.57.99.90:443 | joinfishbowl.com | Amazon.com, Inc. | US | suspicious |
2204 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dslntlv9vhjr4.cloudfront.net |
| whitelisted |
url6814.fishbowlinvites.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
crl.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
protect2.fireeye.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2664 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2664 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |