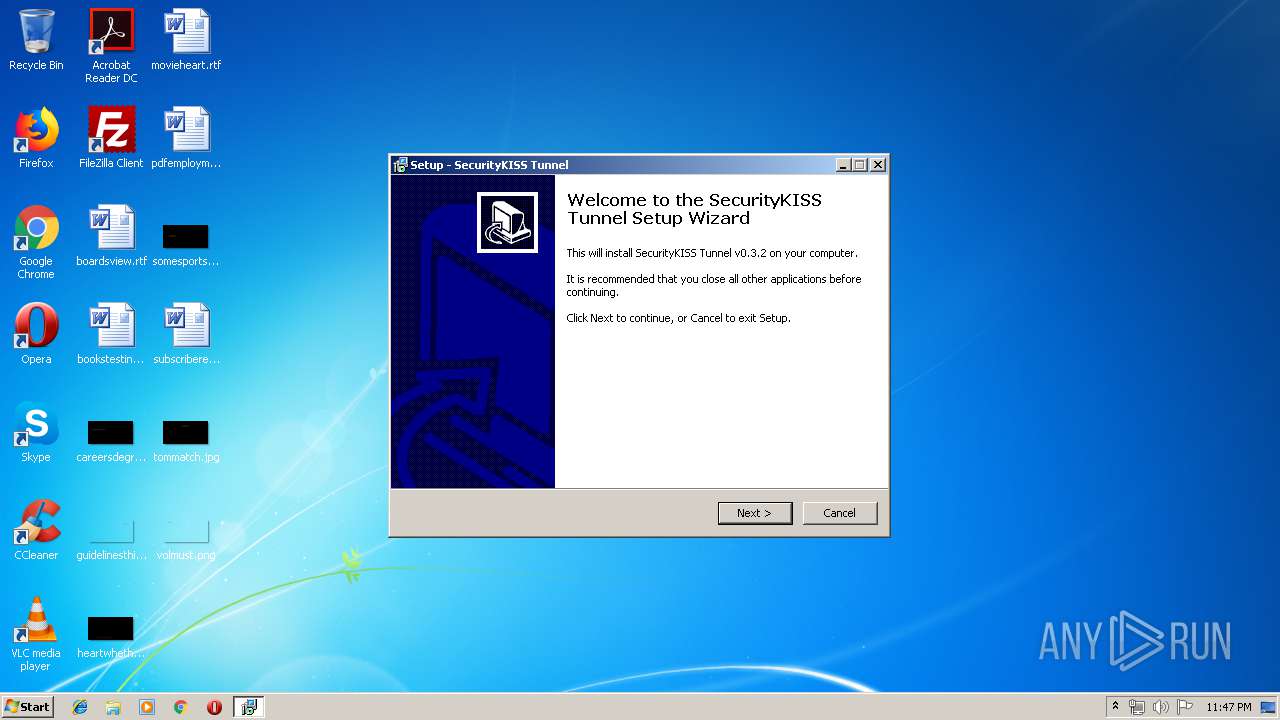
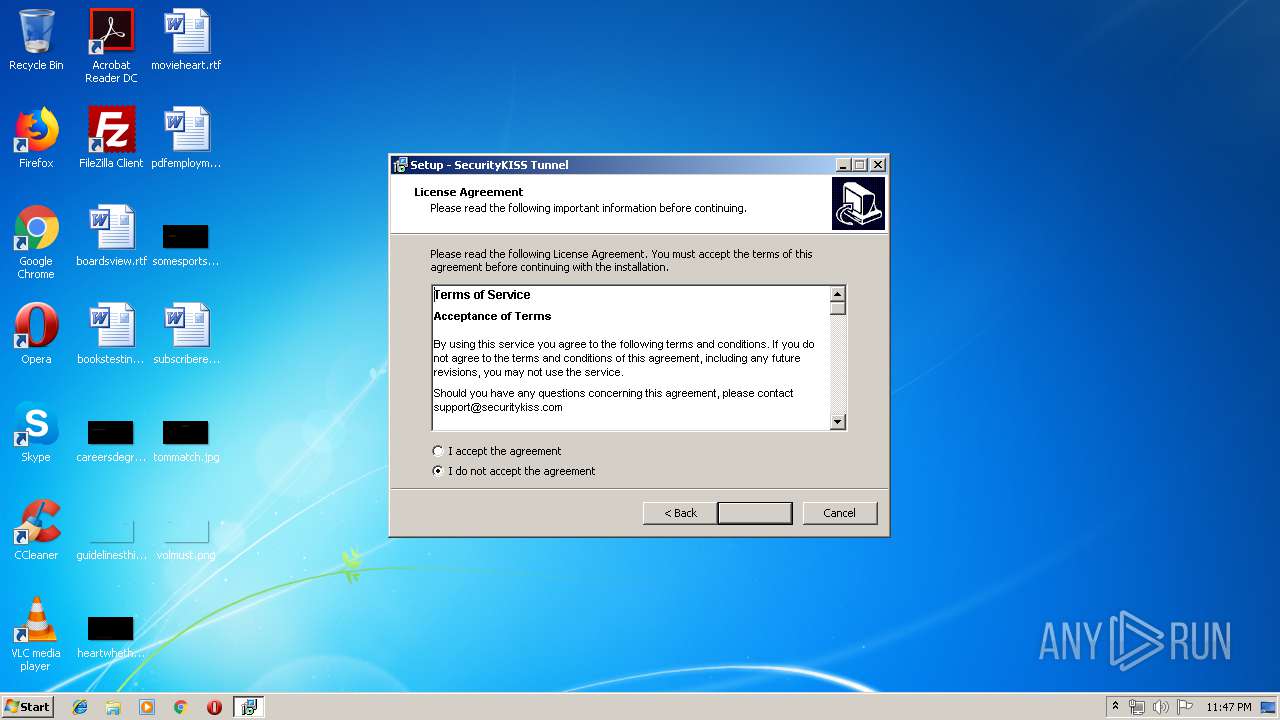
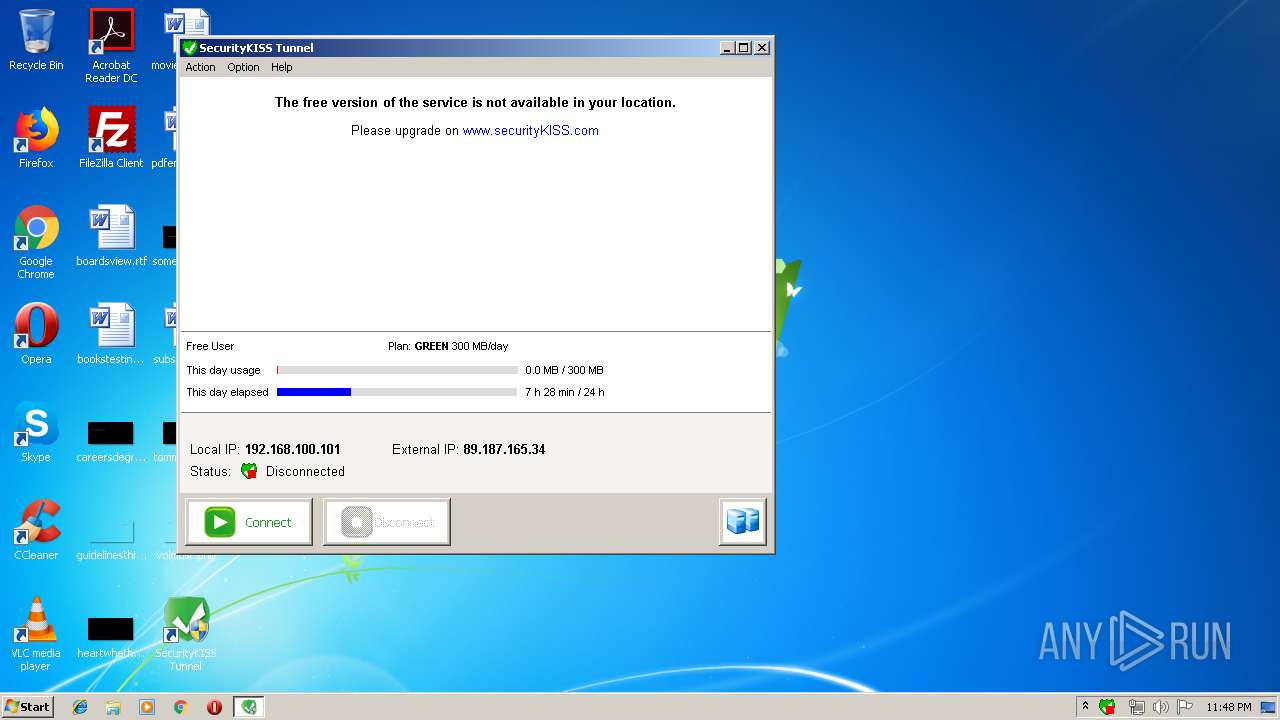
| File name: | VPN SecurityKISSsetup.exe |
| Full analysis: | https://app.any.run/tasks/5eb31e7f-2f6b-4438-82d3-6a5a05cba705 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2019, 22:47:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 574D92555BF5BC8C31205FBB5CA45690 |
| SHA1: | C7A0867B068B688A24CA2BE7F9306207BEE6F957 |
| SHA256: | 089B765C35187C9C3827CBA5CB5439CF556A5010BAE577B53BAE0A24F5E8F531 |
| SSDEEP: | 49152:f2Rg/feOqu/mpfJ4PTPoPrhj1K5/MFRvg2dzUp8Kj+qd1qapcqG:+A/SYP+y5/MFRvXdzUp8KKqd1Zg |
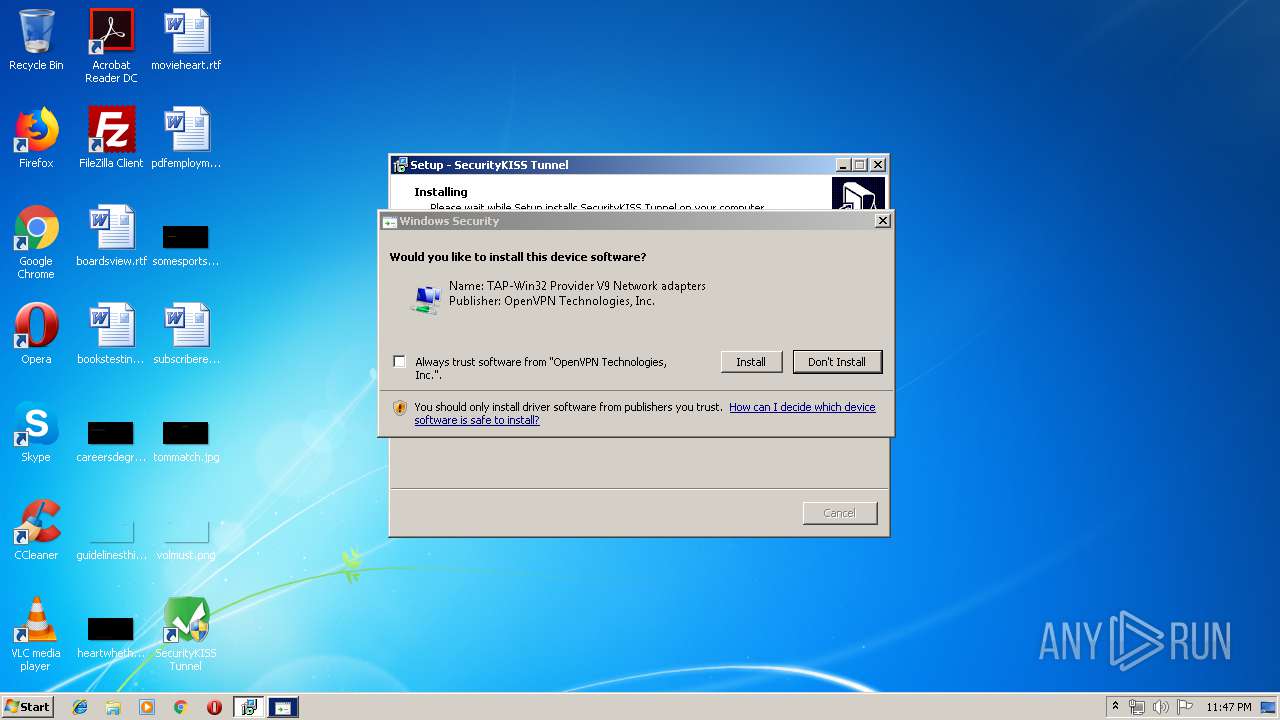
MALICIOUS
Application was dropped or rewritten from another process
- tapinstall.exe (PID: 2240)
- SecurityKISSTunnel.exe (PID: 3976)
- openvpn.exe (PID: 4000)
Loads dropped or rewritten executable
- openvpn.exe (PID: 4000)
SUSPICIOUS
Executable content was dropped or overwritten
- VPN SecurityKISSsetup.tmp (PID: 2320)
- VPN SecurityKISSsetup.exe (PID: 3724)
- VPN SecurityKISSsetup.exe (PID: 2948)
- tapinstall.exe (PID: 2240)
- DrvInst.exe (PID: 1044)
- DrvInst.exe (PID: 2180)
Uses TASKKILL.EXE to kill process
- VPN SecurityKISSsetup.tmp (PID: 2320)
- cmd.exe (PID: 2556)
Creates files in the Windows directory
- cmd.exe (PID: 2312)
- DrvInst.exe (PID: 1044)
- DrvInst.exe (PID: 2180)
Starts CMD.EXE for commands execution
- VPN SecurityKISSsetup.tmp (PID: 2320)
- SecurityKISSTunnel.exe (PID: 3976)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 2312)
- SecurityKISSTunnel.exe (PID: 3976)
- cmd.exe (PID: 2396)
Executed via COM
- DrvInst.exe (PID: 1044)
- DrvInst.exe (PID: 1700)
- DrvInst.exe (PID: 2180)
Removes files from Windows directory
- DrvInst.exe (PID: 1044)
- DrvInst.exe (PID: 2180)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 1044)
Creates files in the driver directory
- DrvInst.exe (PID: 1044)
- DrvInst.exe (PID: 2180)
Creates files in the program directory
- SecurityKISSTunnel.exe (PID: 3976)
- cmd.exe (PID: 2396)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2396)
Reads Windows owner or organization settings
- reg.exe (PID: 3612)
Reads Environment values
- reg.exe (PID: 3612)
Executed as Windows Service
- vssvc.exe (PID: 2376)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2396)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2396)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 2396)
Checks supported languages
- reg.exe (PID: 3212)
- reg.exe (PID: 4072)
INFO
Application was dropped or rewritten from another process
- VPN SecurityKISSsetup.tmp (PID: 2908)
- VPN SecurityKISSsetup.tmp (PID: 2320)
Creates a software uninstall entry
- VPN SecurityKISSsetup.tmp (PID: 2320)
Loads dropped or rewritten executable
- VPN SecurityKISSsetup.tmp (PID: 2320)
Searches for installed software
- DrvInst.exe (PID: 1044)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2376)
Creates files in the program directory
- VPN SecurityKISSsetup.tmp (PID: 2320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b60 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | SecurityKISS Tunnel Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | SecurityKISS Tunnel |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | SecurityKISS Tunnel Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | SecurityKISS Tunnel |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009280 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53893 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73987 |
BSS | 0x0000C000 | 0x00000E4C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.46345 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
84
Monitored processes
34
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{26feaa6a-8e90-12ee-29c9-fa6dedd2062c}\oemwin2k.inf" "0" "6d14a44ff" "00000394" "WinSta0\Default" "000005DC" "208" "c:\program files\securitykiss tunnel\openvpn\driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | ping -n 1 www.securitykiss.com | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | ping -n 1 217.147.94.149 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | systeminfo | C:\Windows\system32\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays system information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1544 | netstat -a -n | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1640 | route print 0.0.0.0 | C:\Windows\system32\route.exe | — | SecurityKISSTunnel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000003A4" "000005CC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | taskkill /F /IM openvpn.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "oemwin2k.inf:tap0901:tap0901.ndi:9.0.0.8:tap0901" "6d14a44ff" "00000394" "000003D4" "000003A4" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Program Files\SecurityKISS Tunnel\OpenVPN\bin\tapinstall.exe" install "C:\Program Files\SecurityKISS Tunnel\OpenVPN\driver\OemWin2k.inf" tap0901 | C:\Program Files\SecurityKISS Tunnel\OpenVPN\bin\tapinstall.exe | VPN SecurityKISSsetup.tmp | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
Total events
1 513
Read events
940
Write events
524
Delete events
49
Modification events
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files\SecurityKISS Tunnel\SecurityKISSTunnel.exe |
Value: WINXPSP2 RUNASADMIN | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files\SecurityKISS Tunnel\SecurityKISSTunnel.exe |
Value: WINXPSP2 RUNASADMIN | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.10 (a) | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\SecurityKISS Tunnel | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\SecurityKISS Tunnel\ | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: SecurityKISS Tunnel | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (2320) VPN SecurityKISSsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SecurityKISS Tunnel_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
Executable files
15
Suspicious files
21
Text files
390
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\is-S62TB.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\is-NCQ7T.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-V59PT.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-GN667.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-304UV.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-2TR2V.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-1MV07.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-9T50O.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-UT7AL.tmp | — | |
MD5:— | SHA256:— | |||
| 2320 | VPN SecurityKISSsetup.tmp | C:\Program Files\SecurityKISS Tunnel\cache\is-3IG0D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
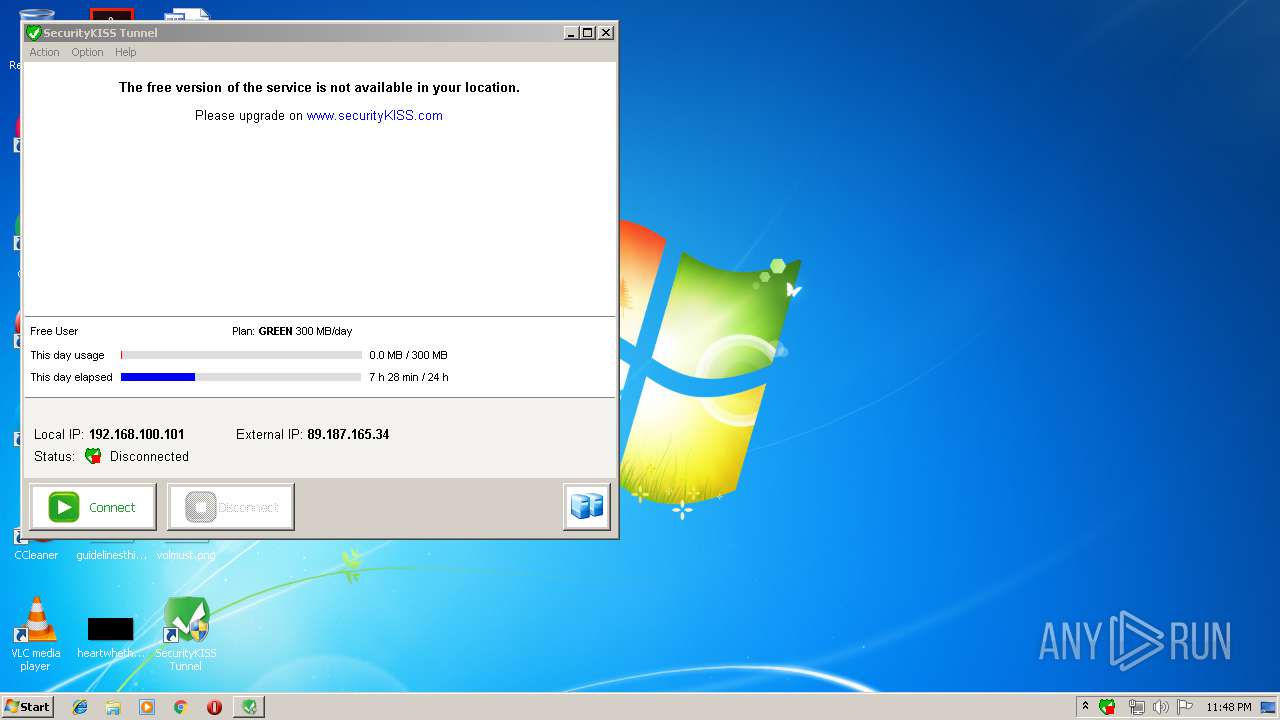
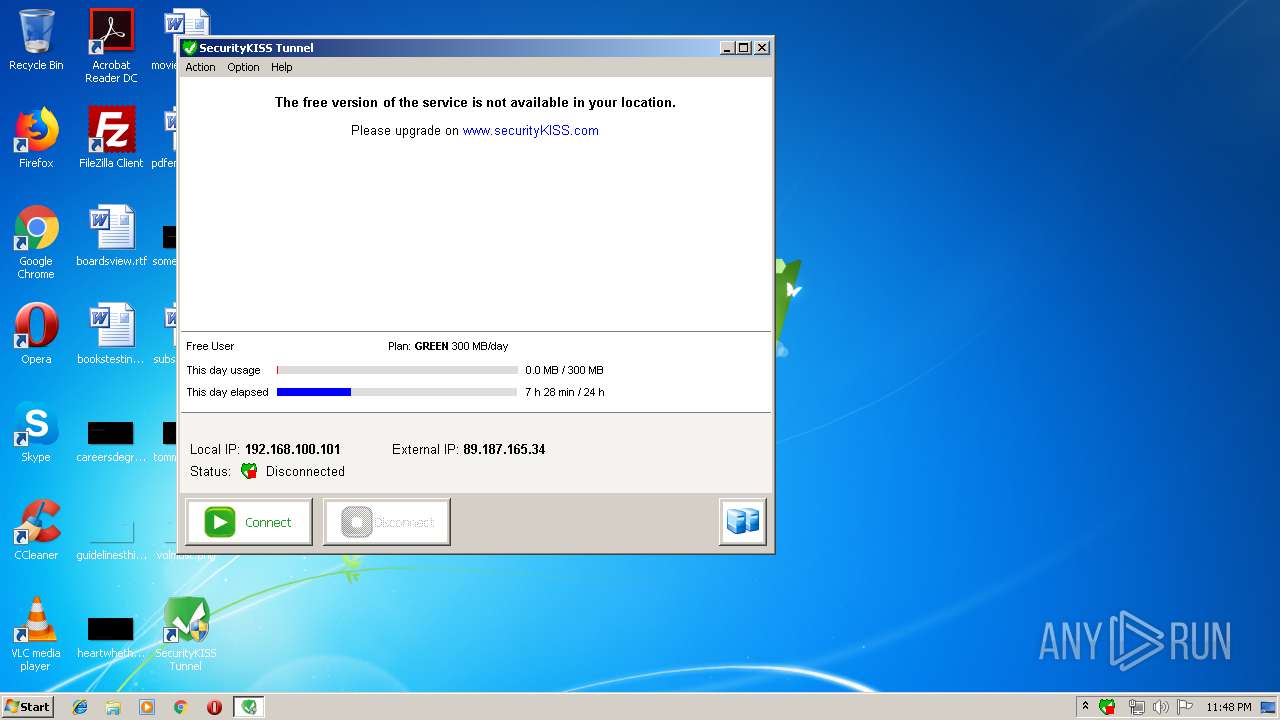
3976 | SecurityKISSTunnel.exe | GET | 200 | 91.216.93.19:80 | http://www.securitykiss.com/sk/app/usage.php?p=7f1429bcb62c1d83224ba6e13cb9ab2f4f359d7d6804b4958f13131b93b6a4ea | GB | html | 1.16 Kb | unknown |
3976 | SecurityKISSTunnel.exe | GET | 200 | 91.216.93.19:80 | http://www.securitykiss.com/sk/app/display.php?p=7f1429bcb62c1d83224ba6e13cb9ab2f4f359d7d6804b4958f13131b93b6a4ea | GB | html | 1.18 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
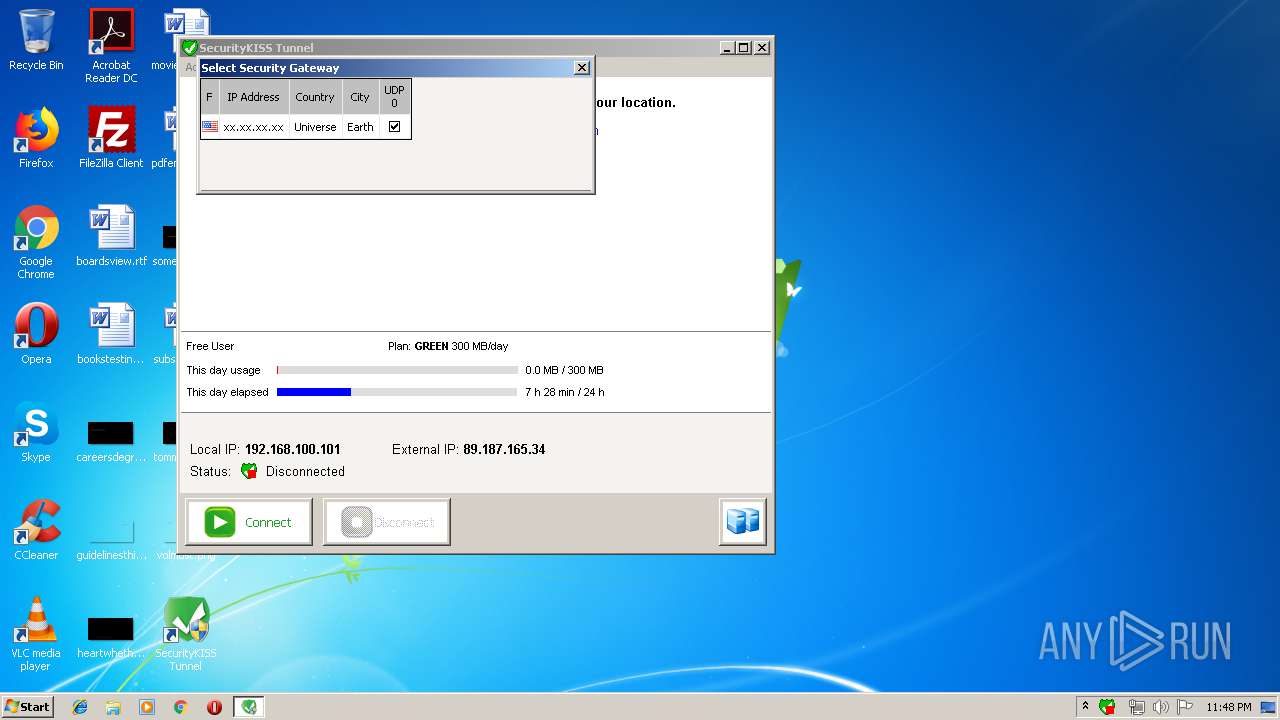
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | SecurityKISSTunnel.exe | 91.216.93.19:80 | www.securitykiss.com | VooServers Ltd | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.securitykiss.com |
| unknown |
Threats
Process | Message |
|---|---|
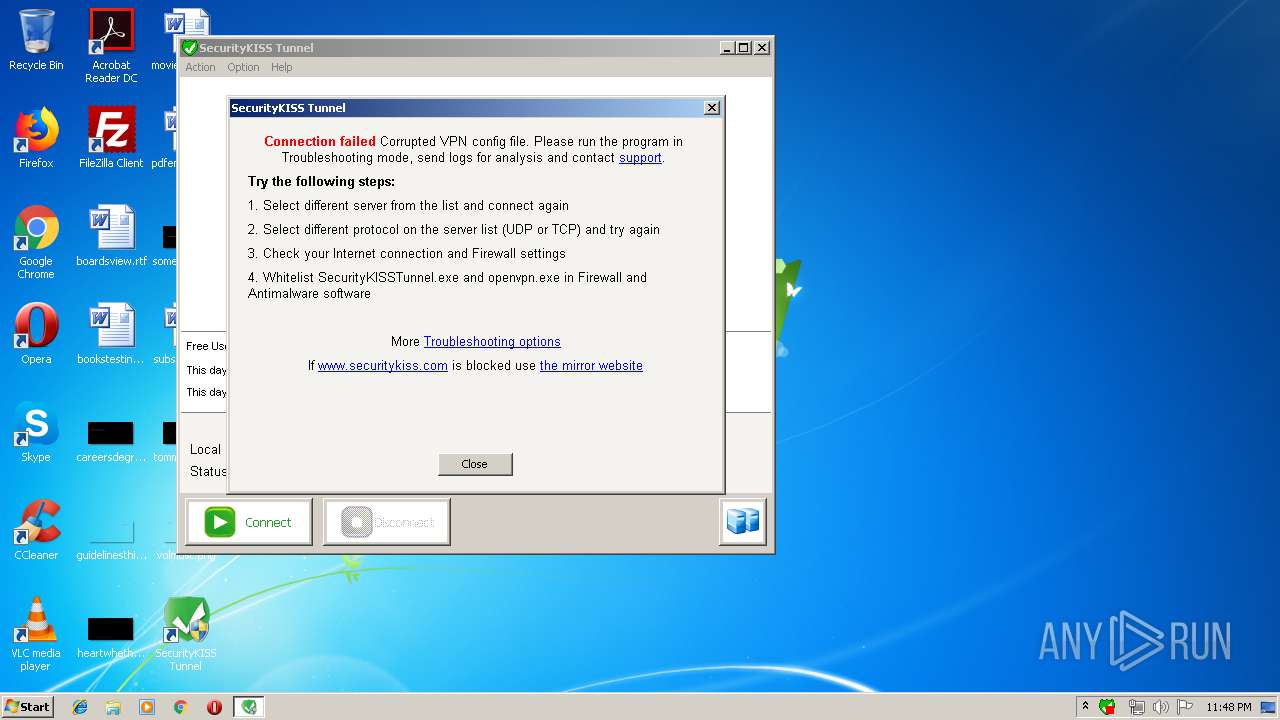
SecurityKISSTunnel.exe | FTH: (3976): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
openvpn.exe | FTH: (4000): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|