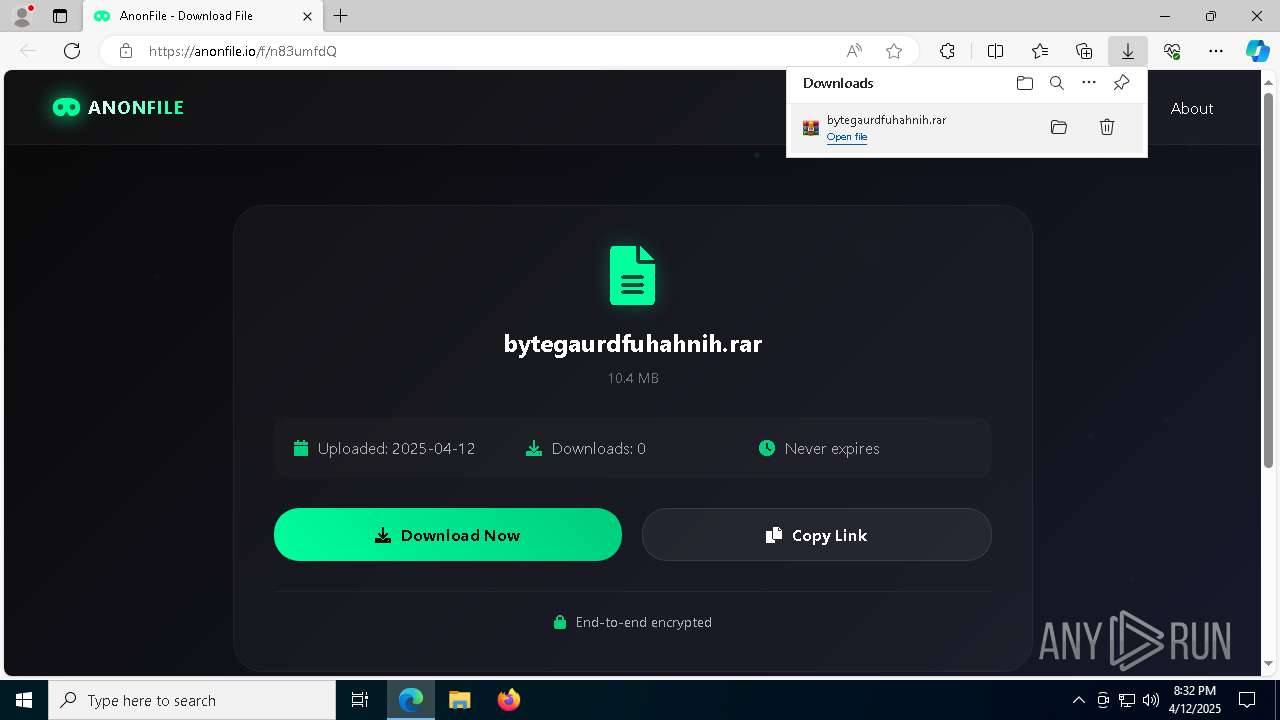
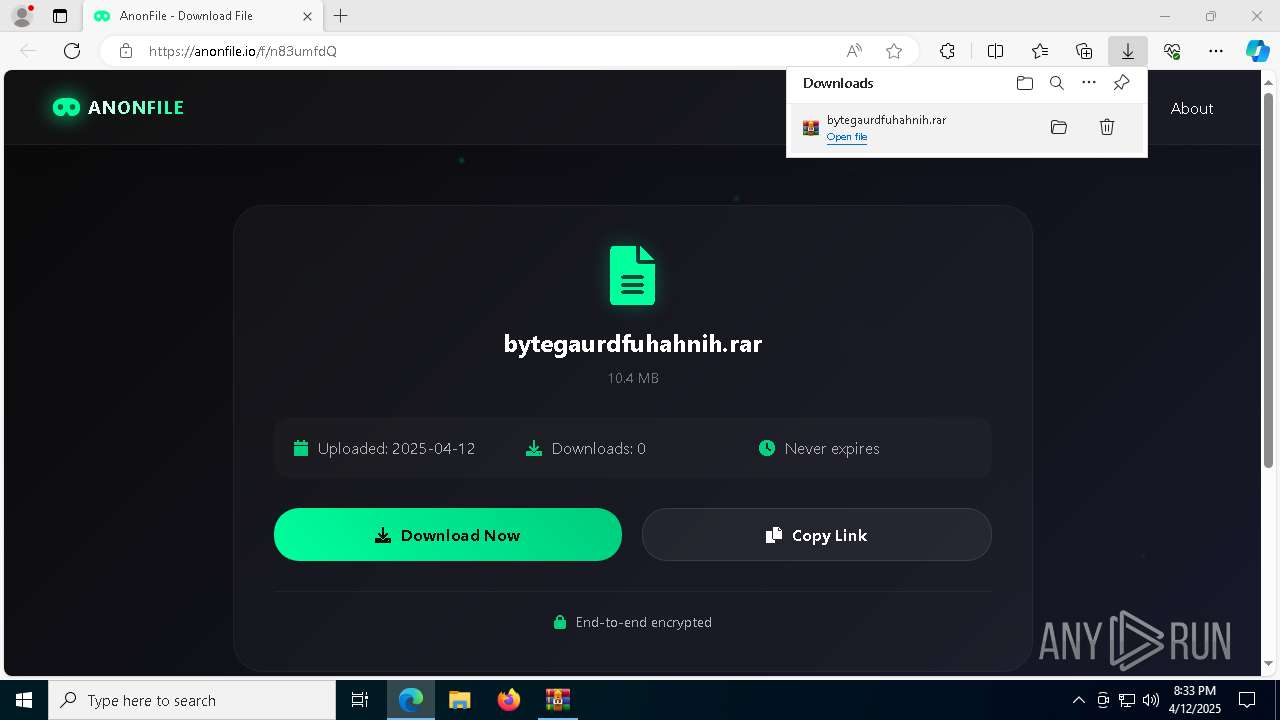
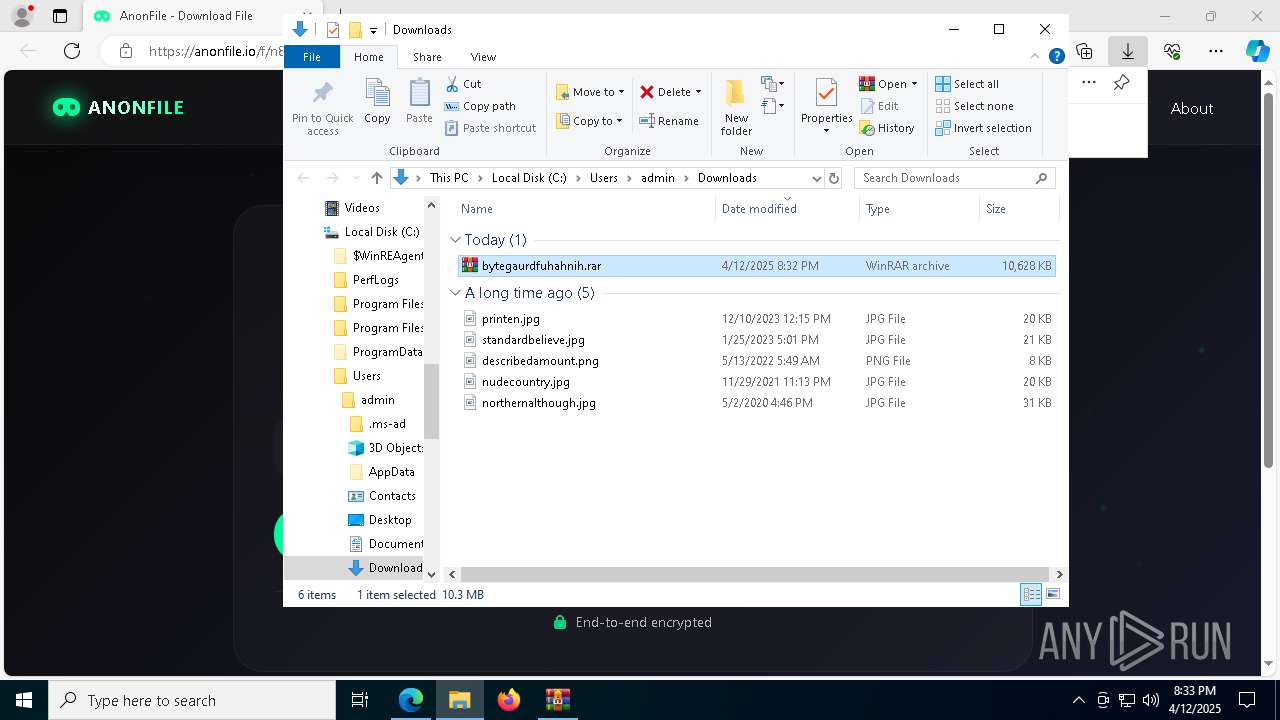
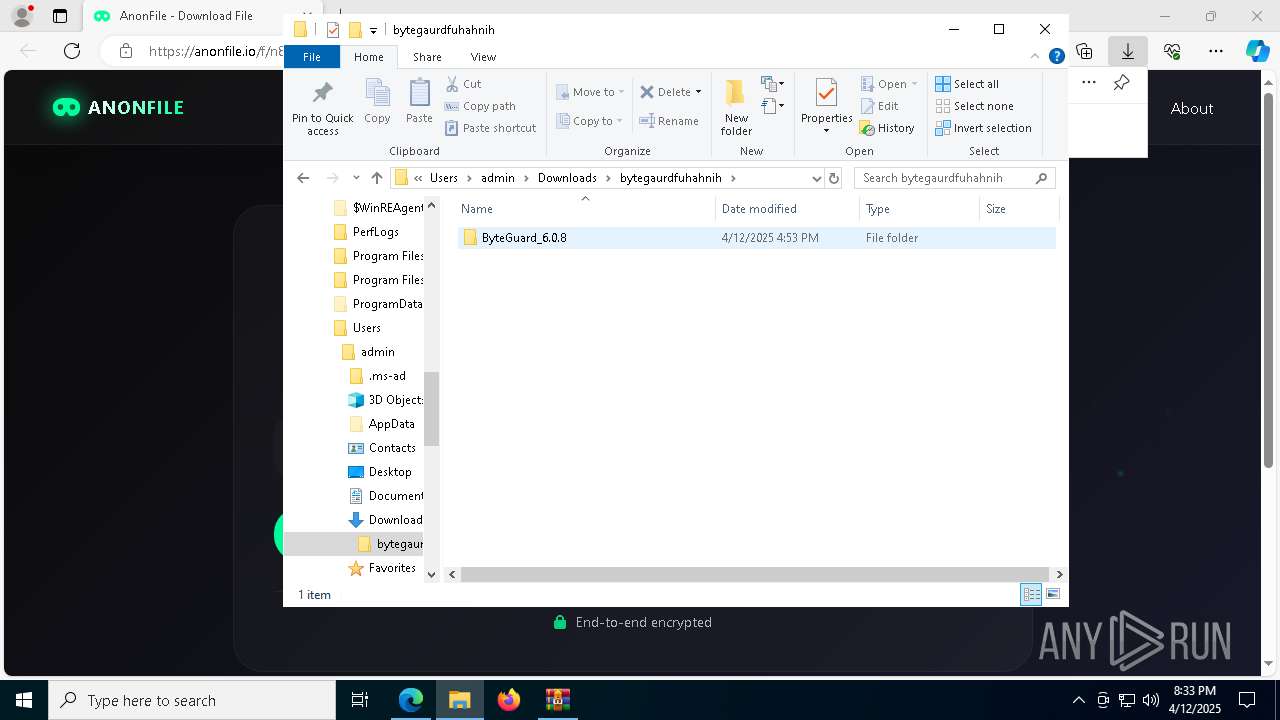
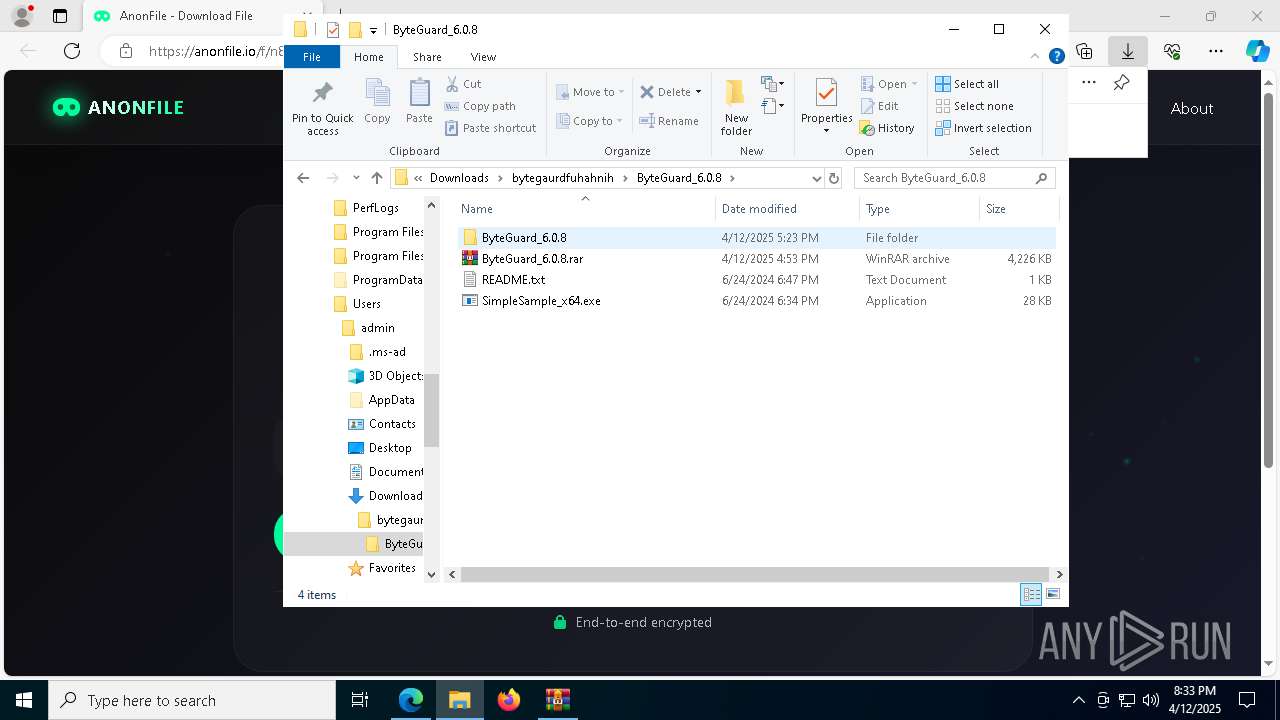
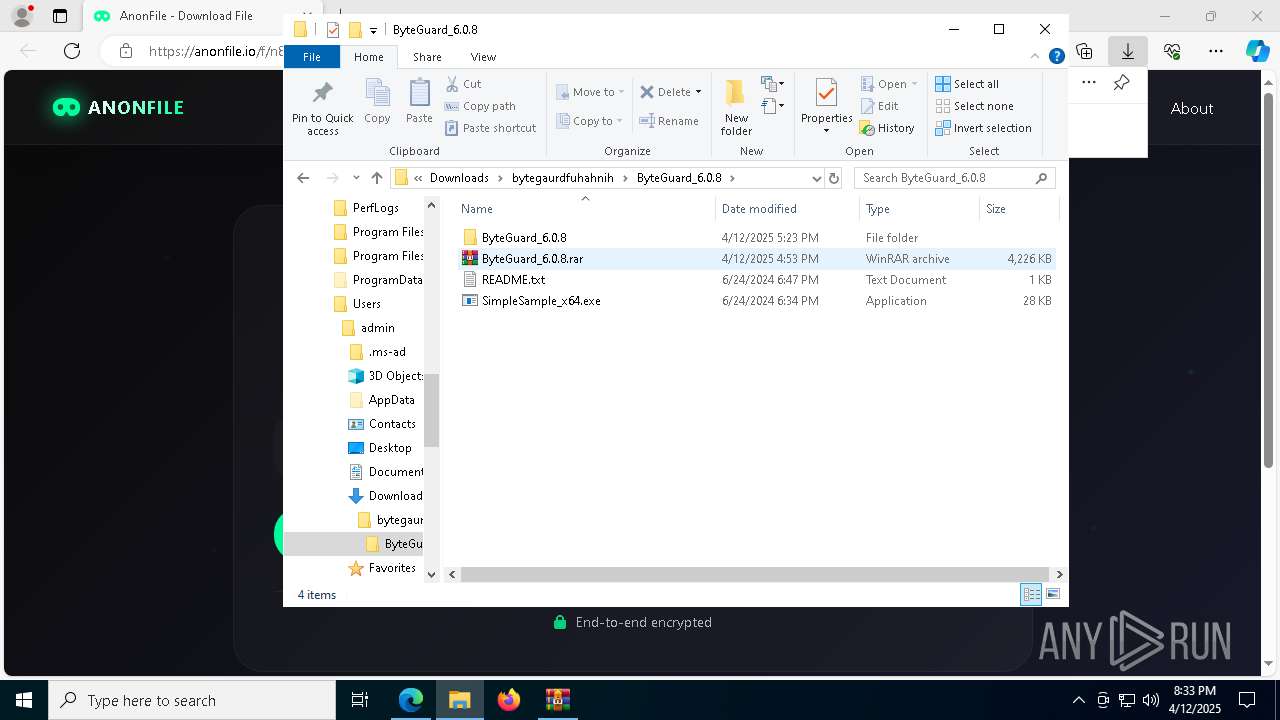
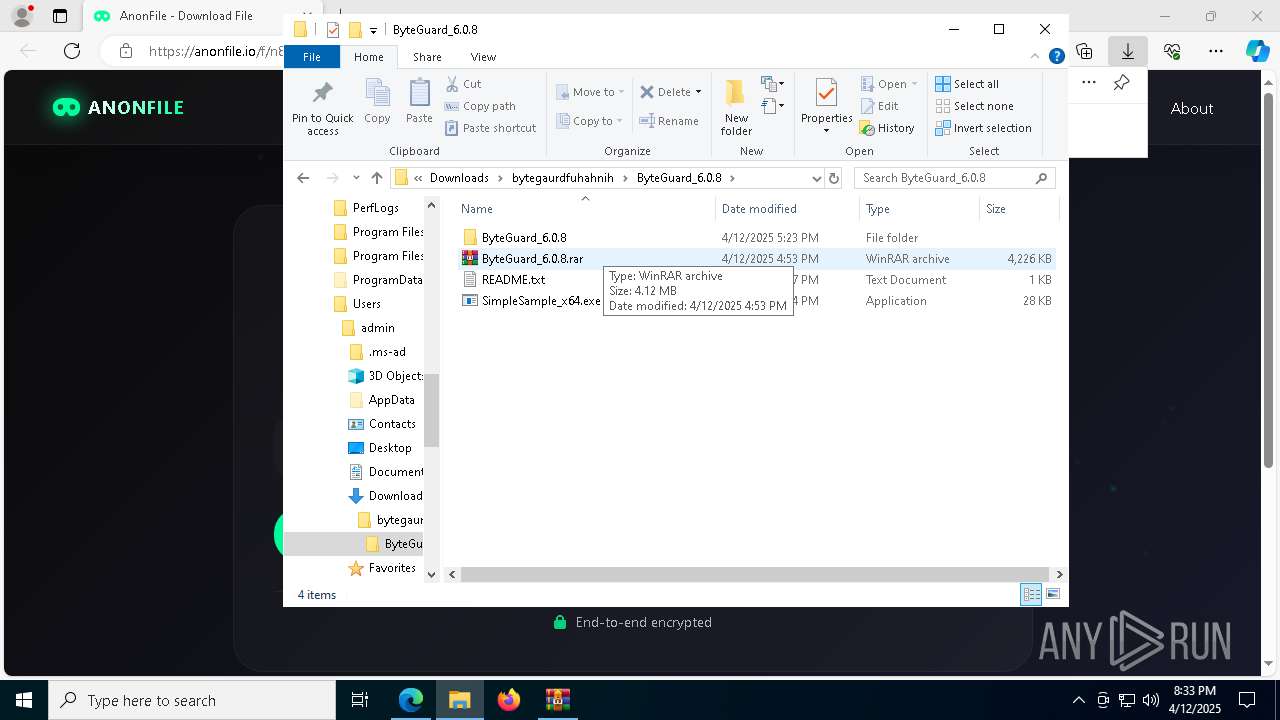
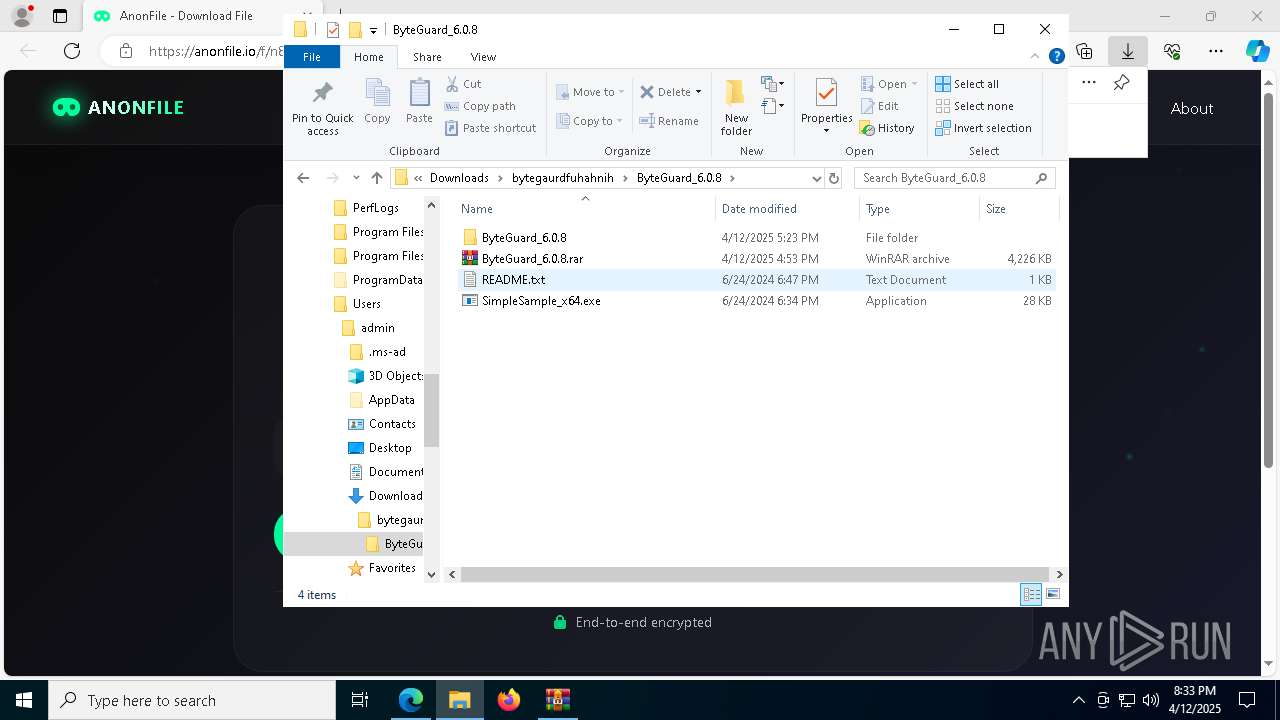
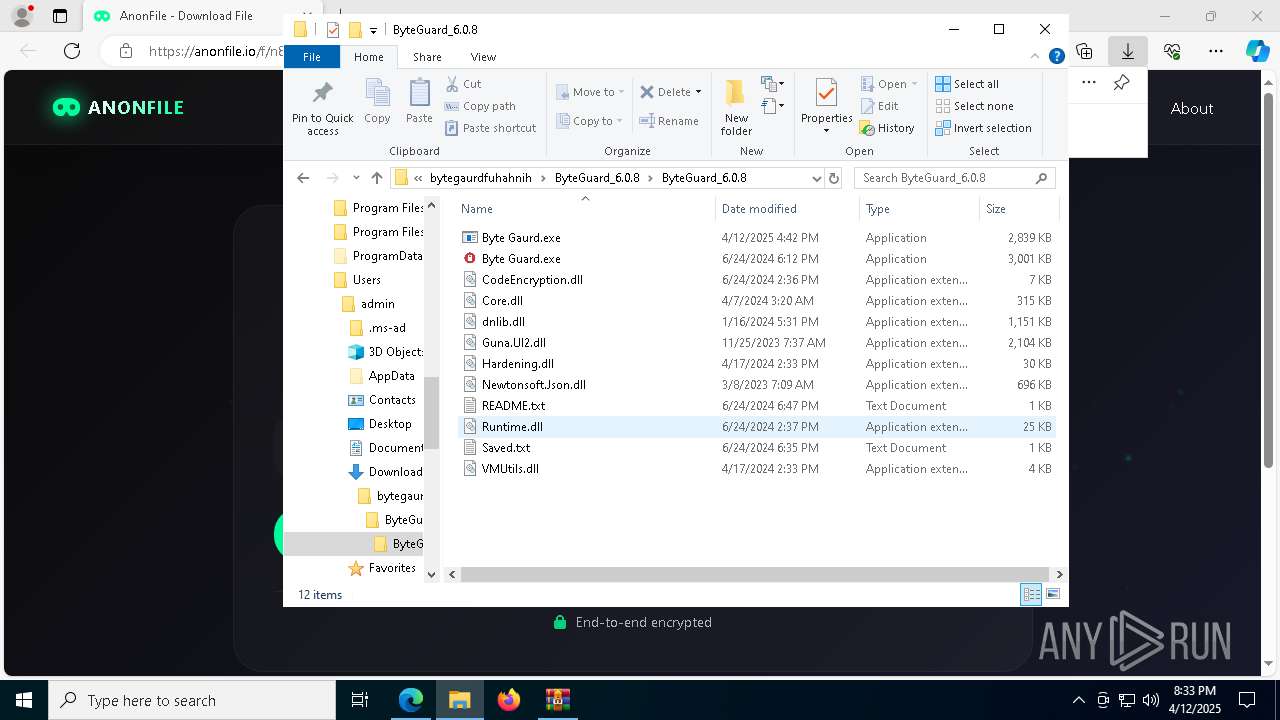
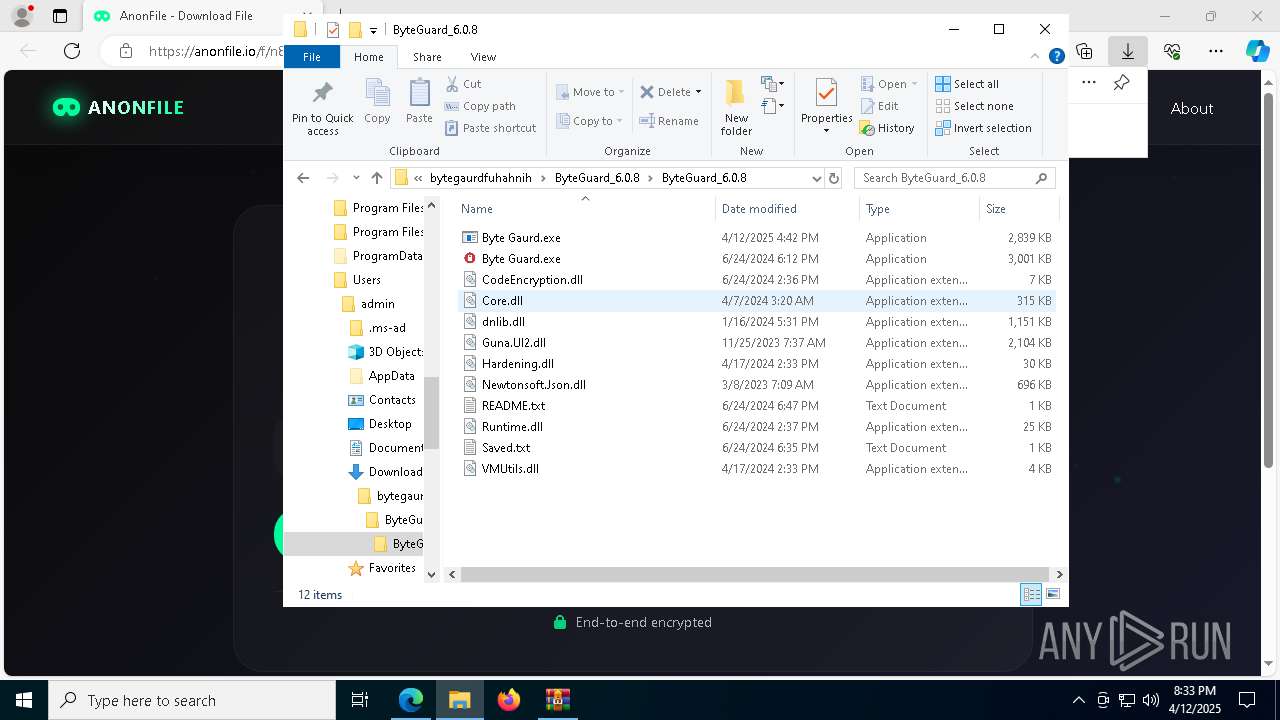
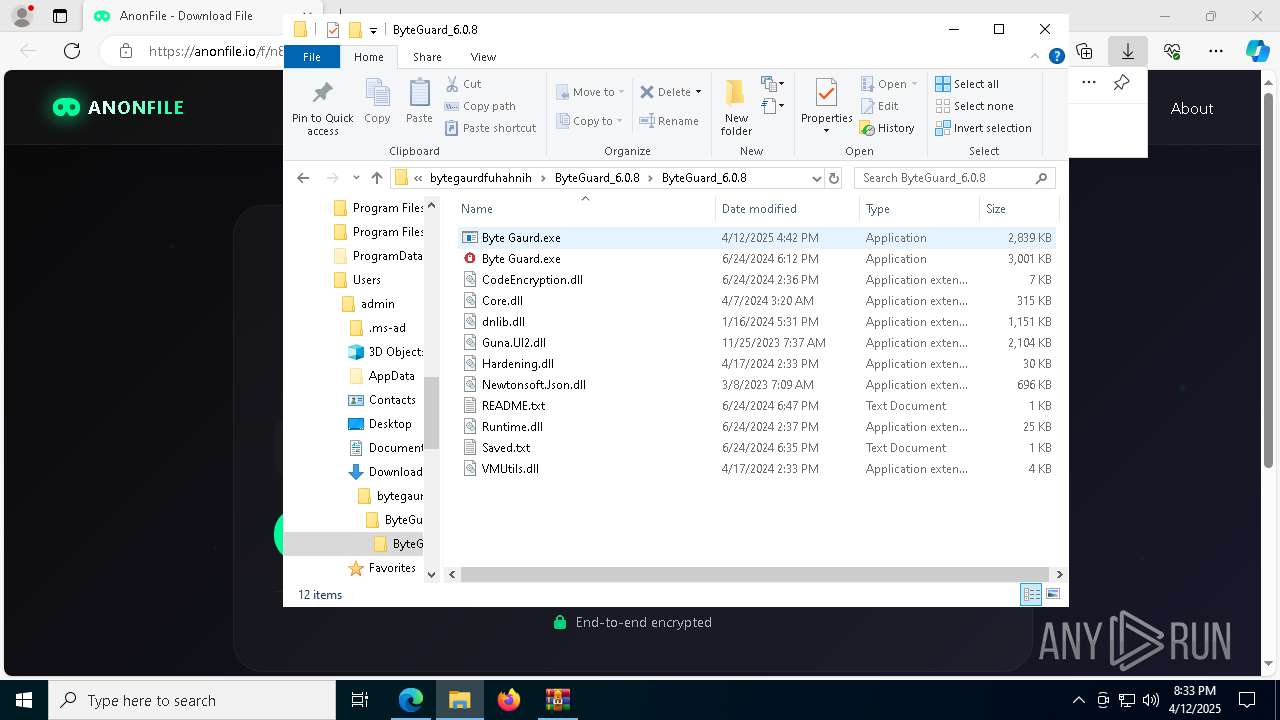
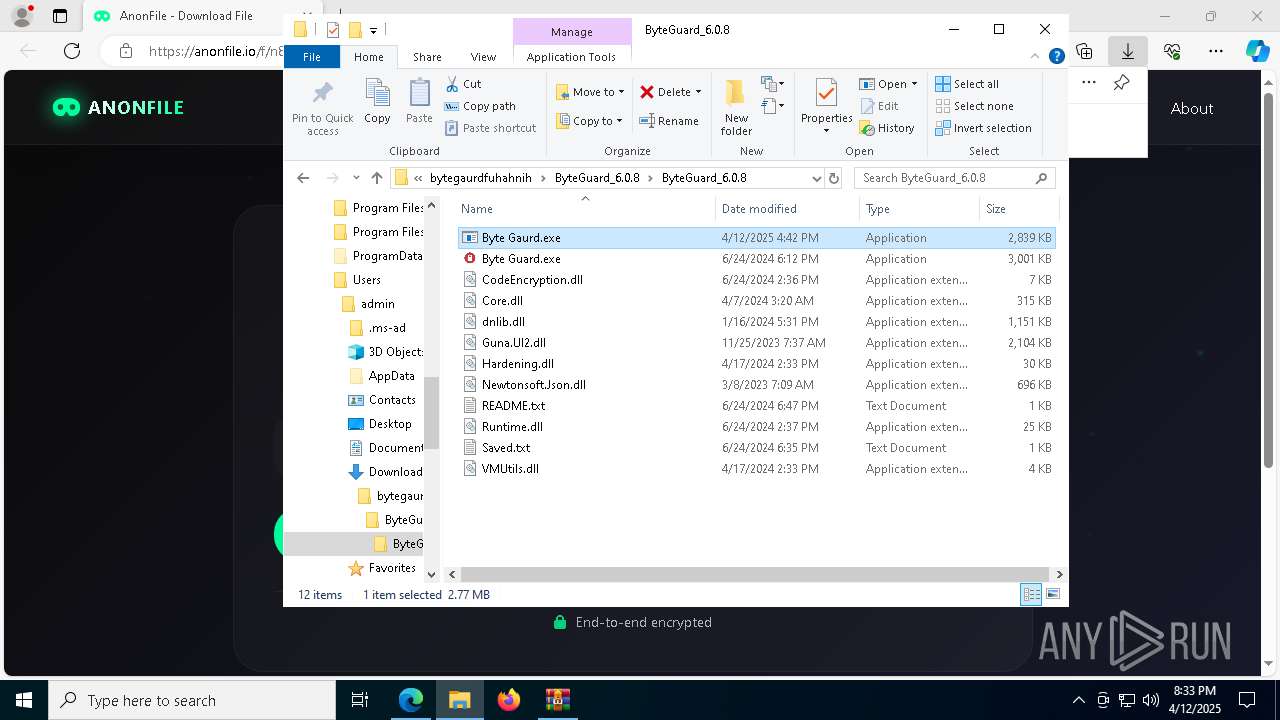
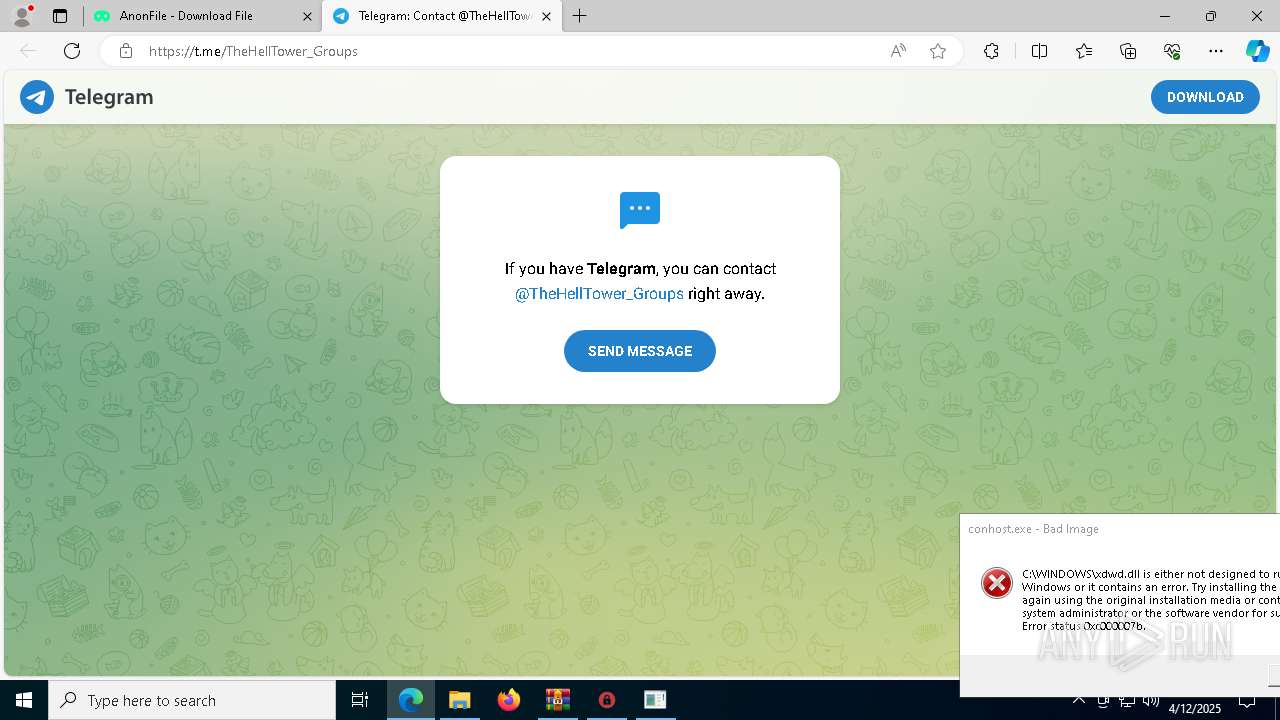
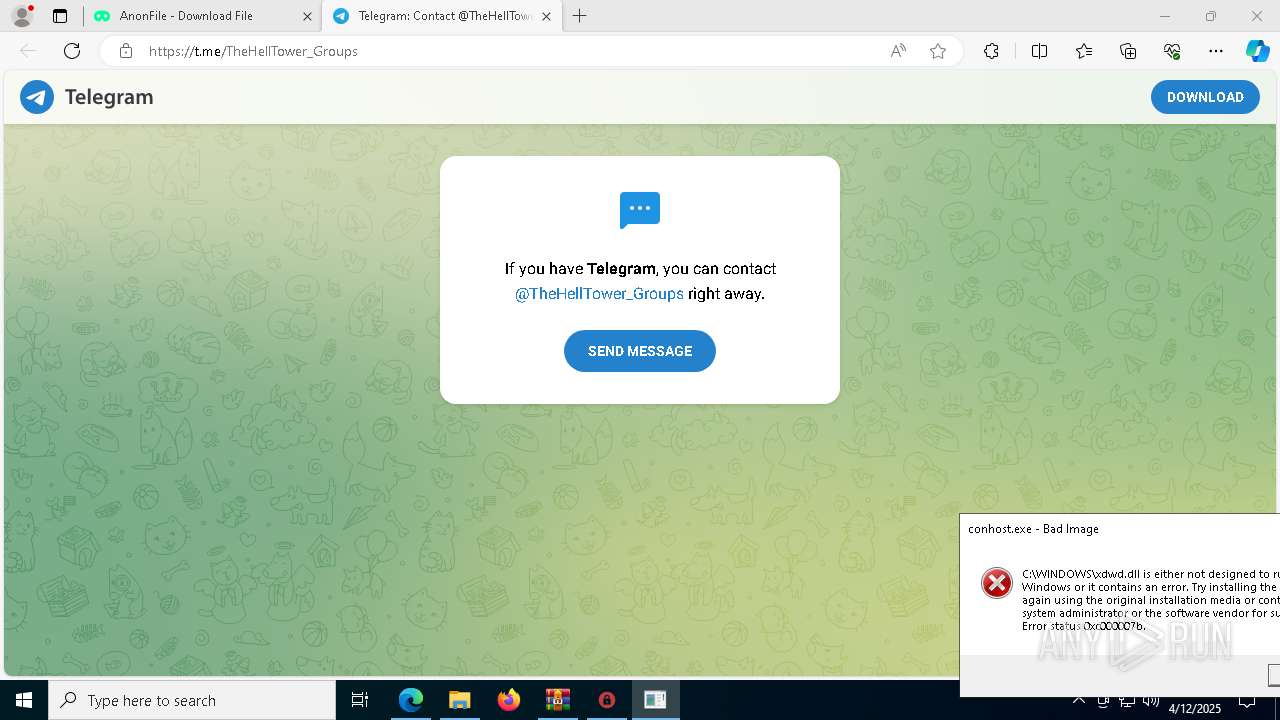
| URL: | https://anonfile.io/f/n83umfdQ |
| Full analysis: | https://app.any.run/tasks/cd6c3f5e-765e-41ec-be8b-6a769c0fff6d |
| Verdict: | Malicious activity |
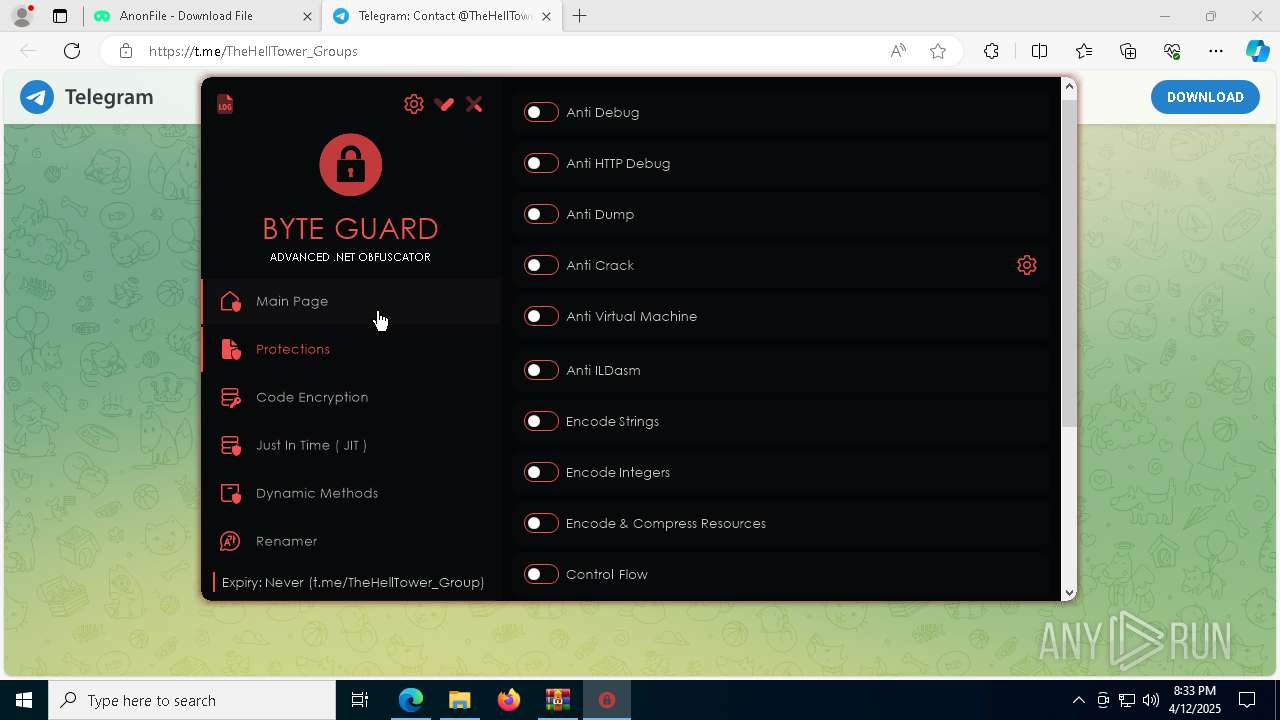
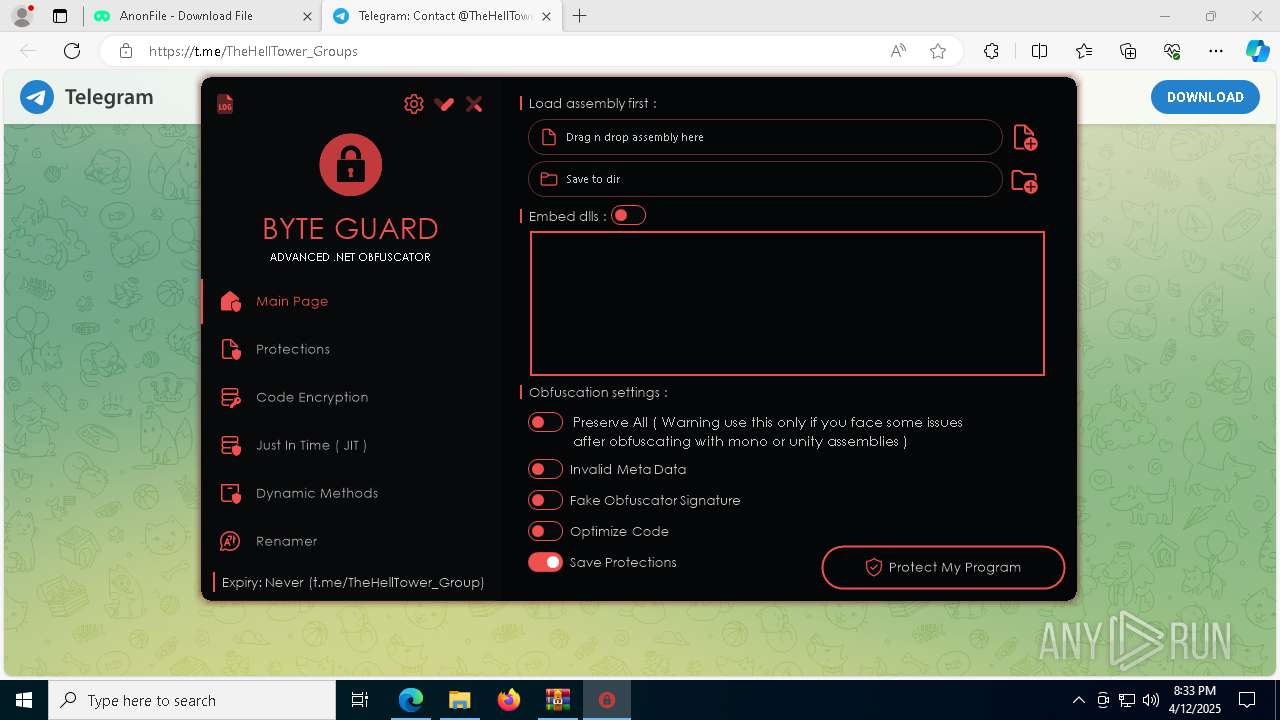
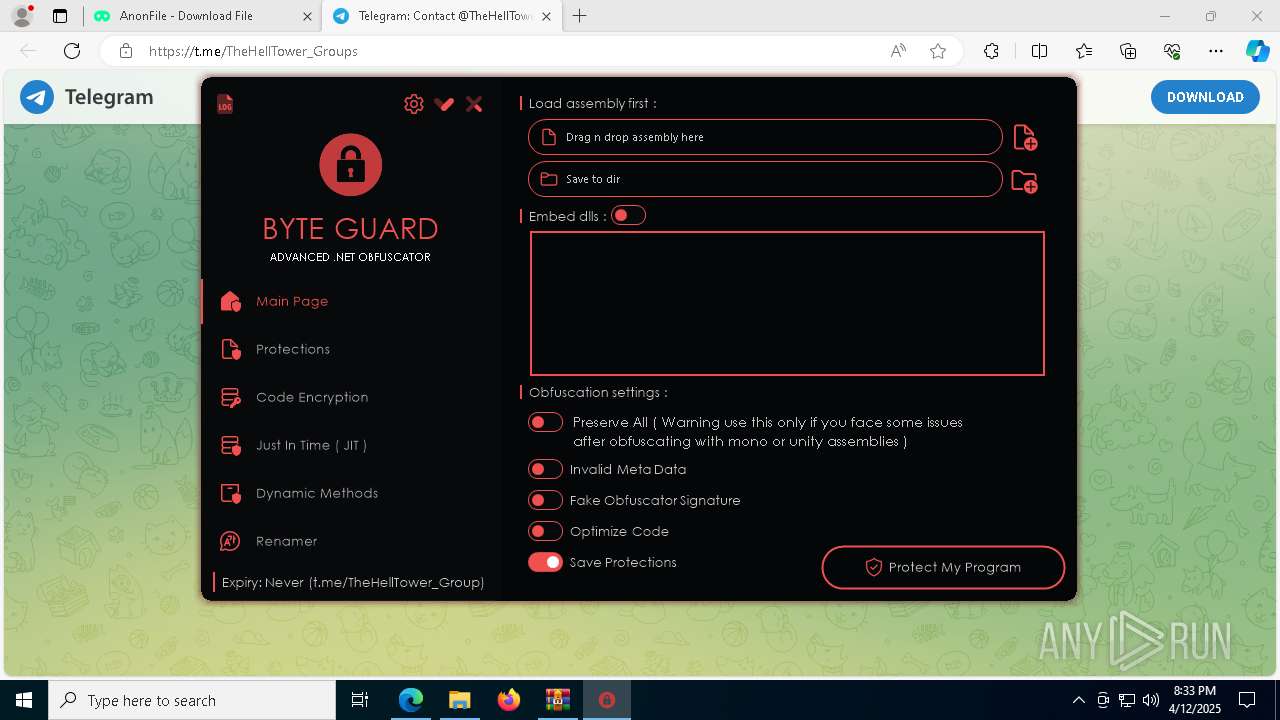
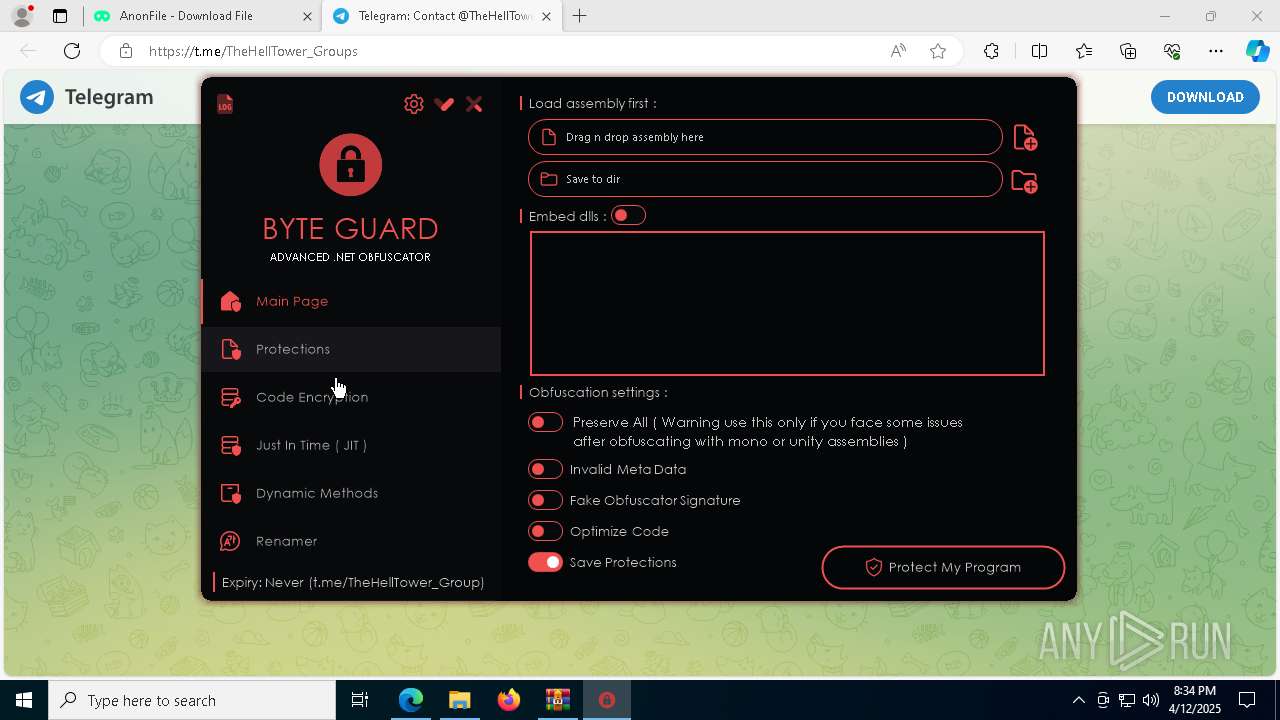
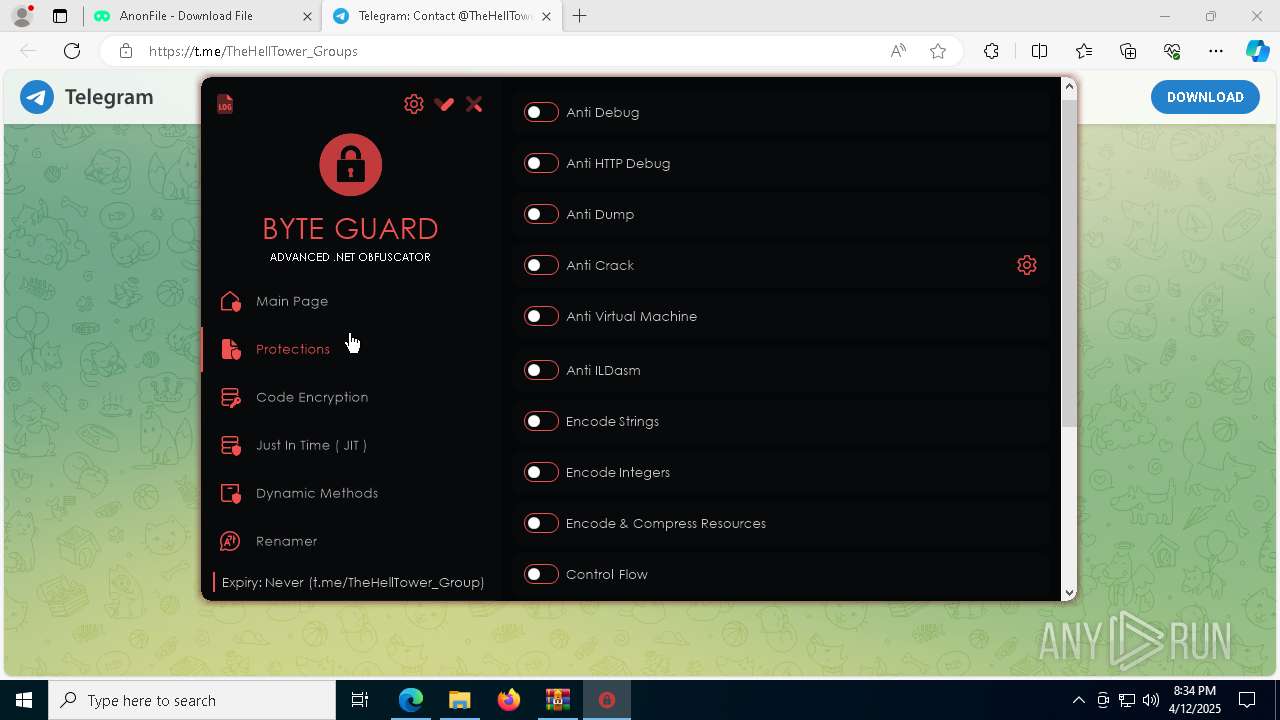
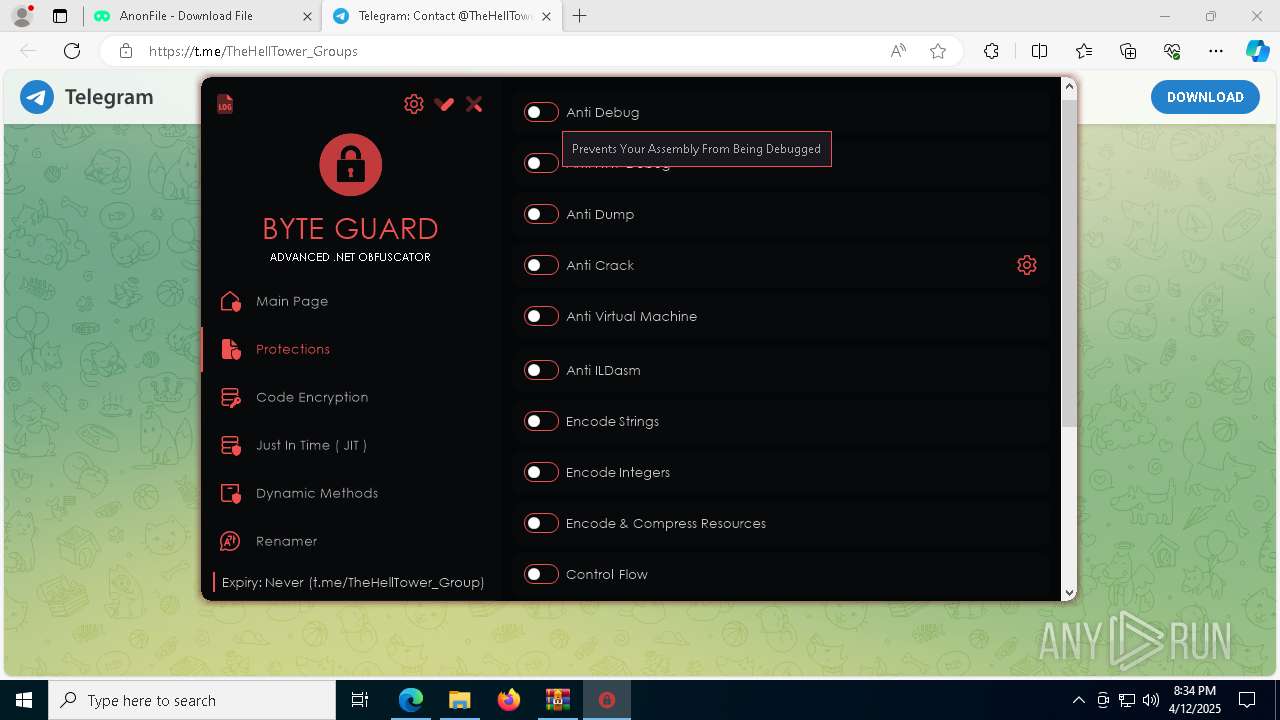
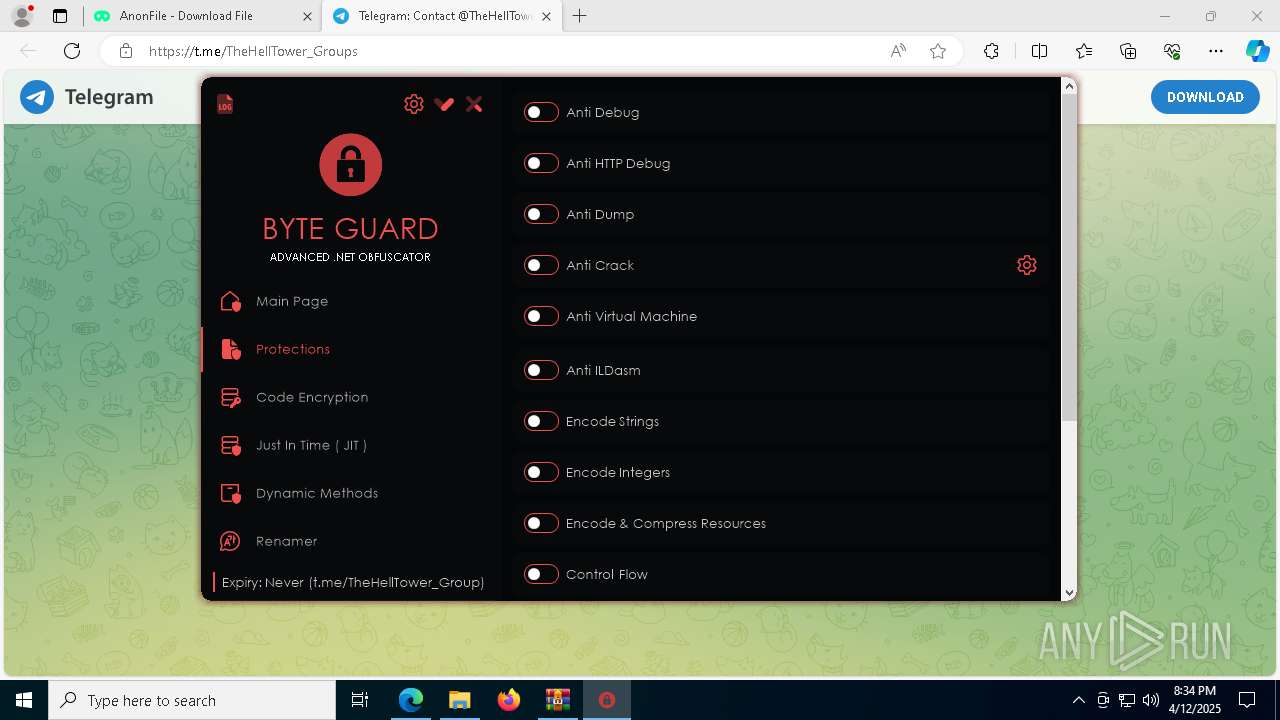
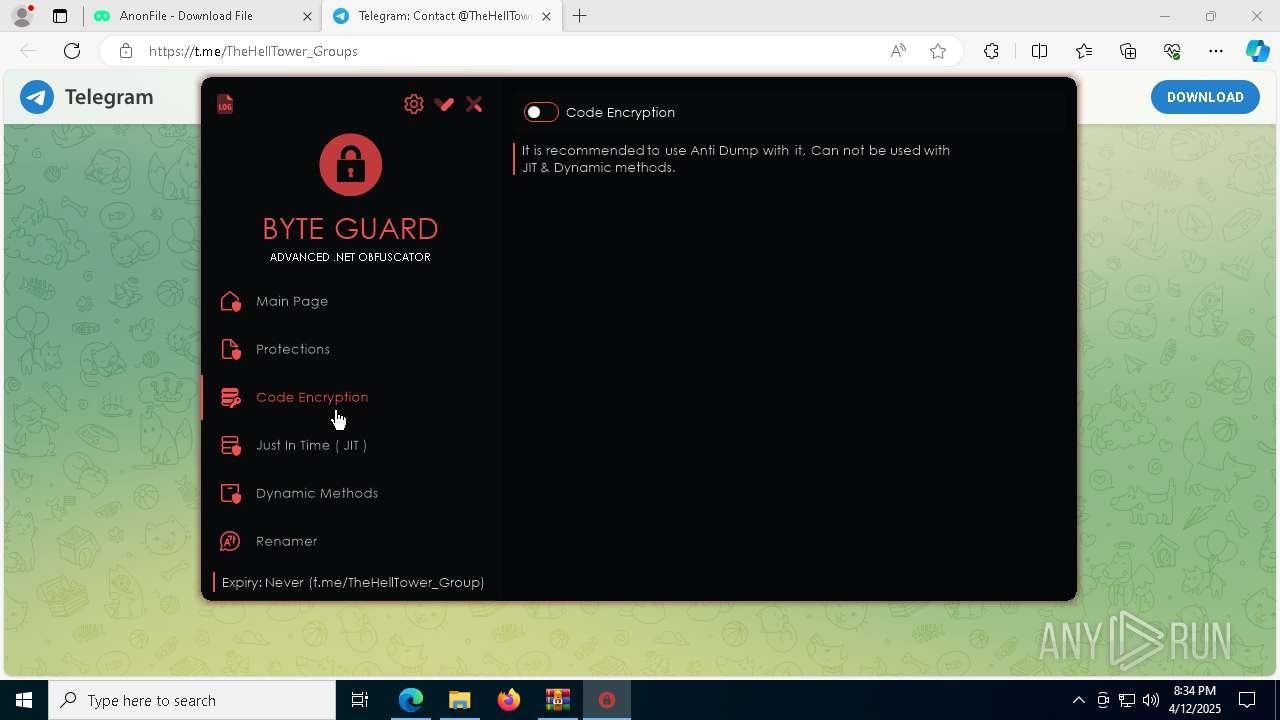
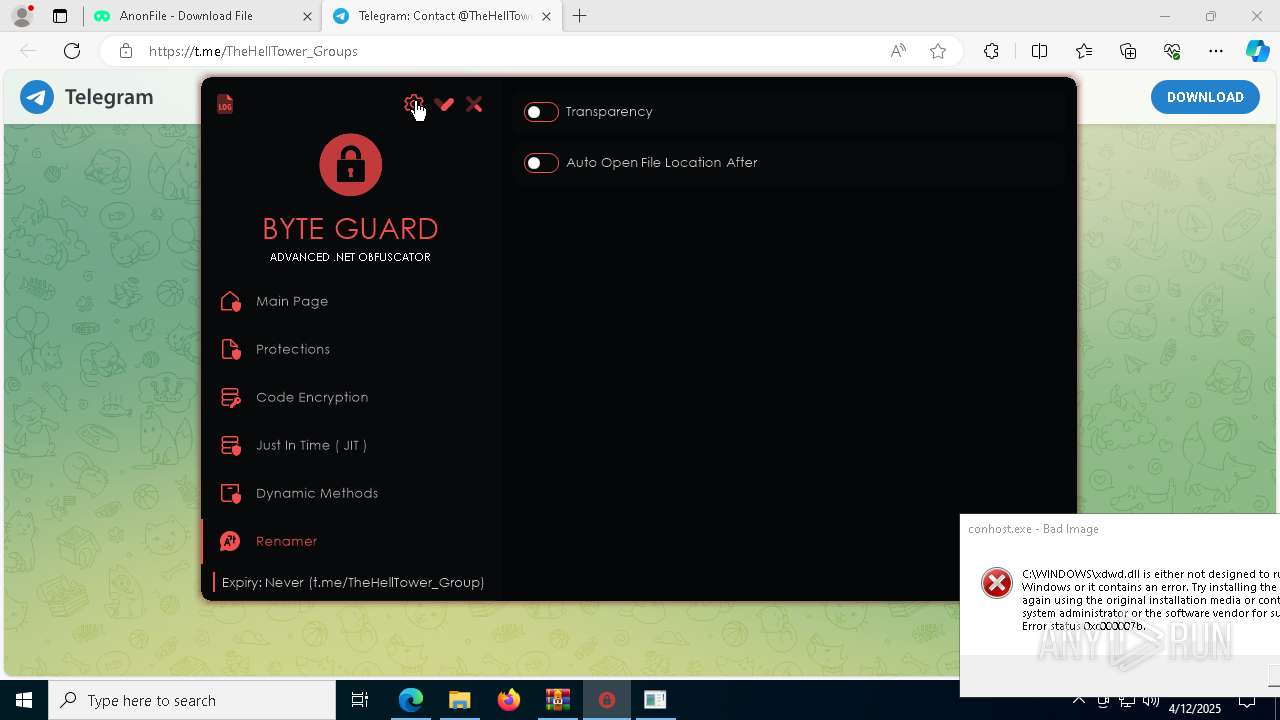
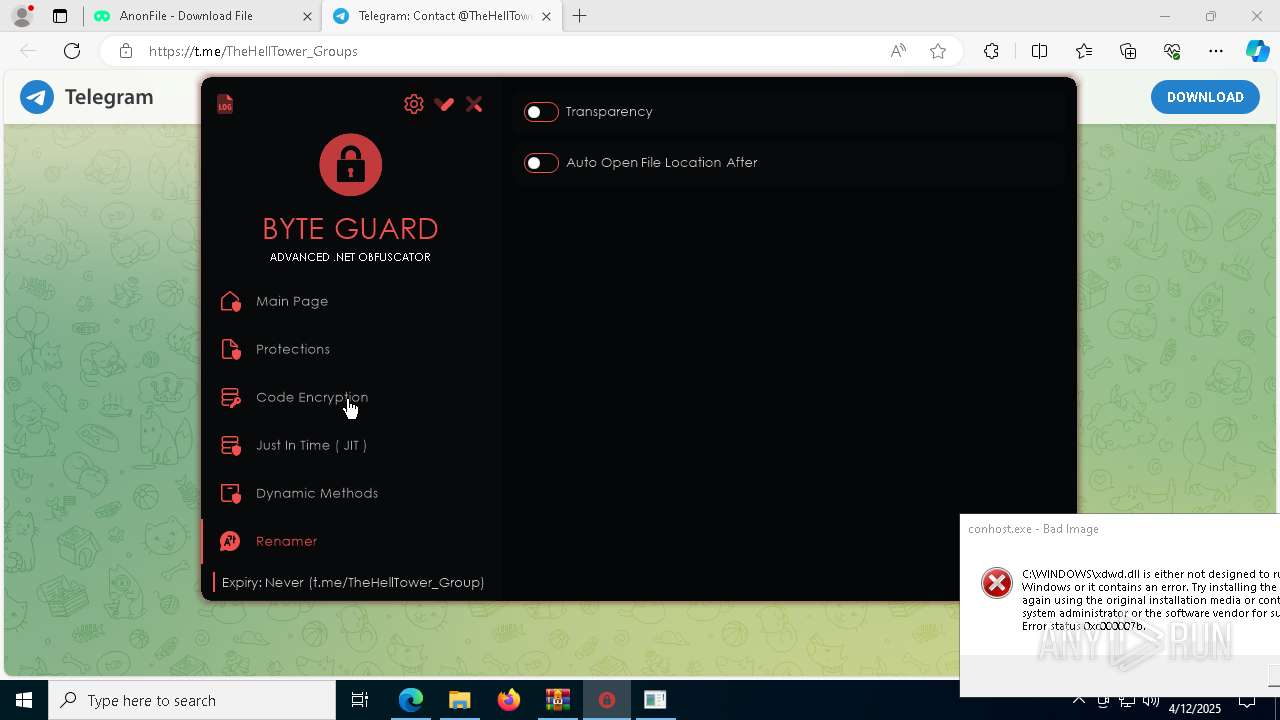
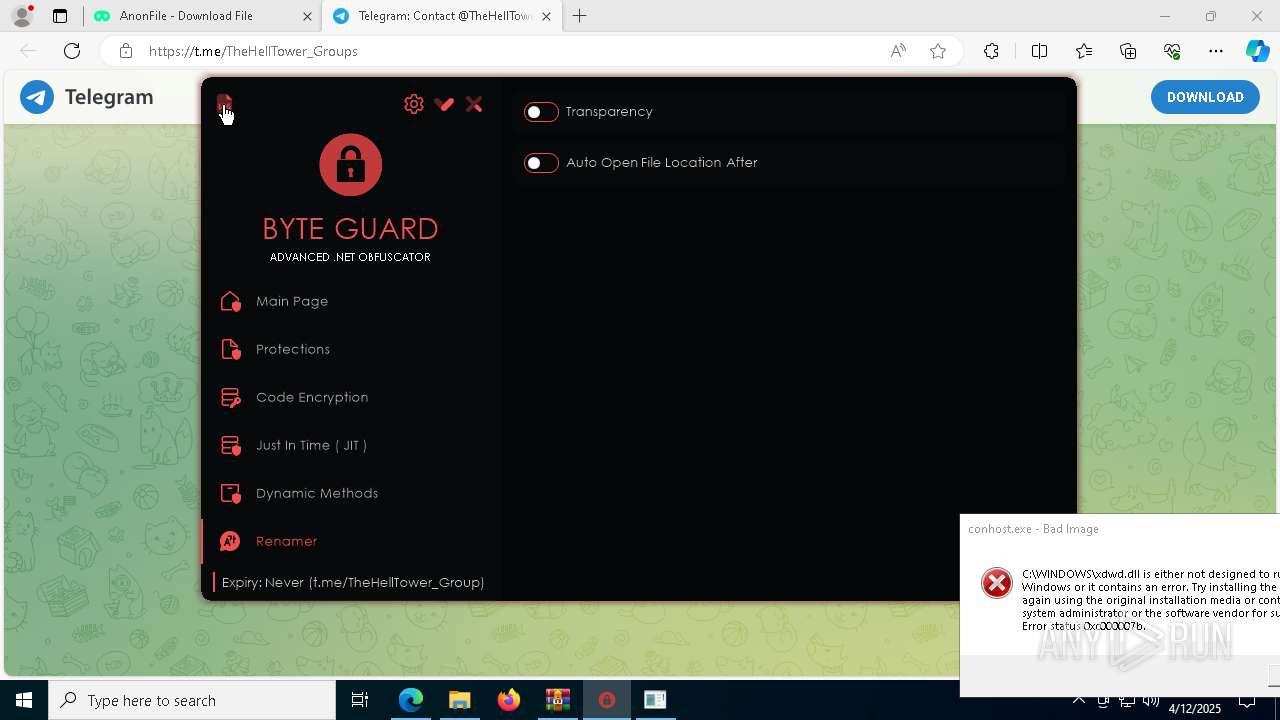
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 12, 2025, 20:32:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
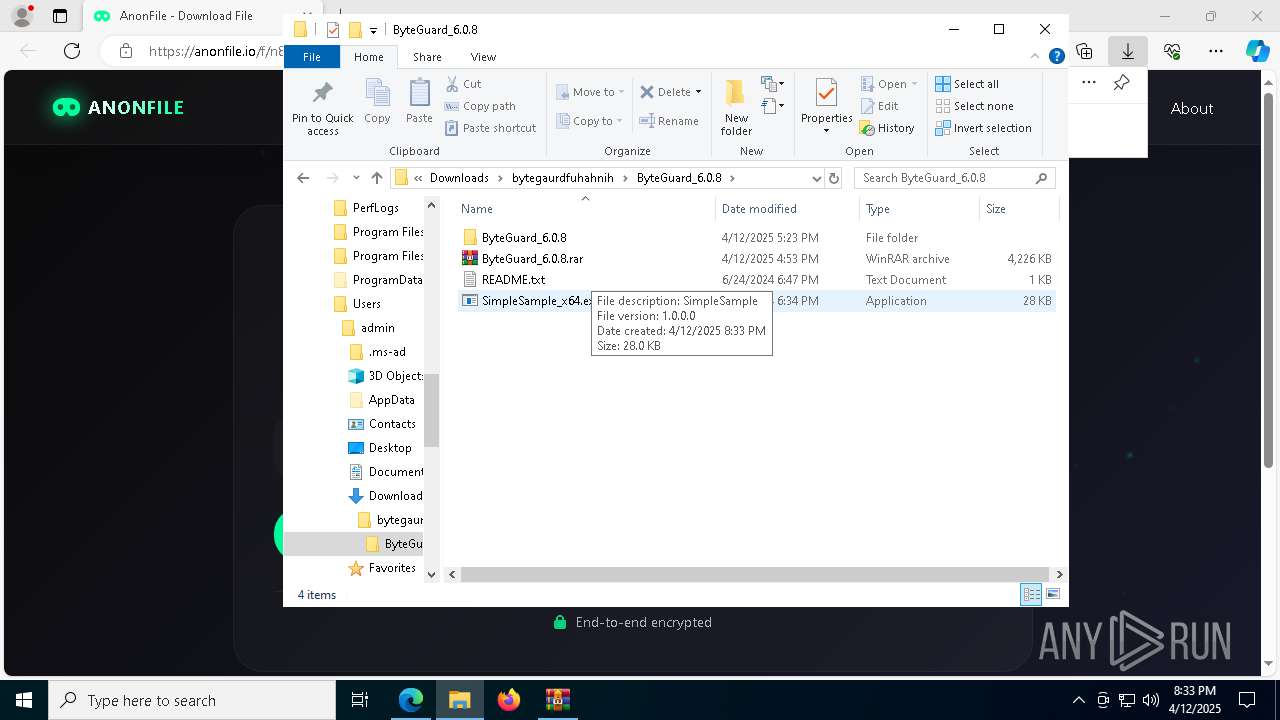
| MD5: | C4A10C1E13A6BC42025A888EEFC334A1 |
| SHA1: | 0E6EBAB49BCFDF6E426EDE04A0489F590519E59A |
| SHA256: | 089AE40CFB721663A388353C53FC86363B5C6097E7FB68B8468F7DBF7BC7B301 |
| SSDEEP: | 3:N8RMQLG2:2qeG2 |
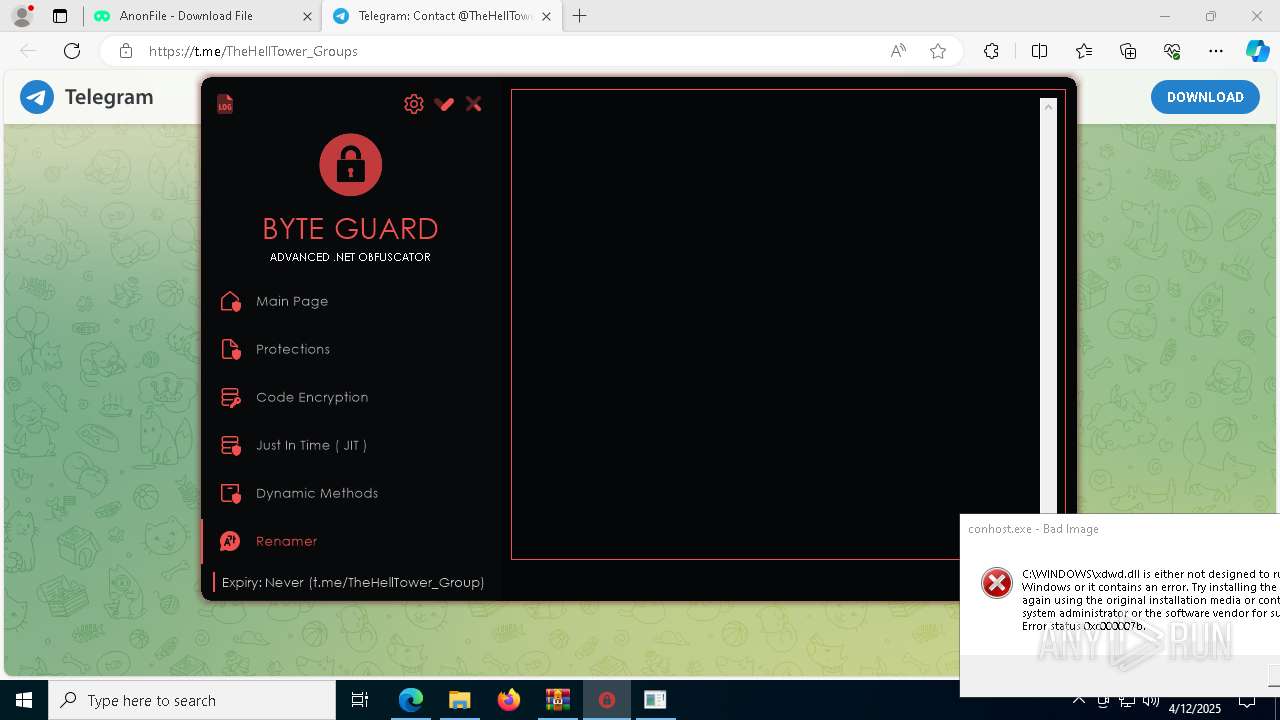
MALICIOUS
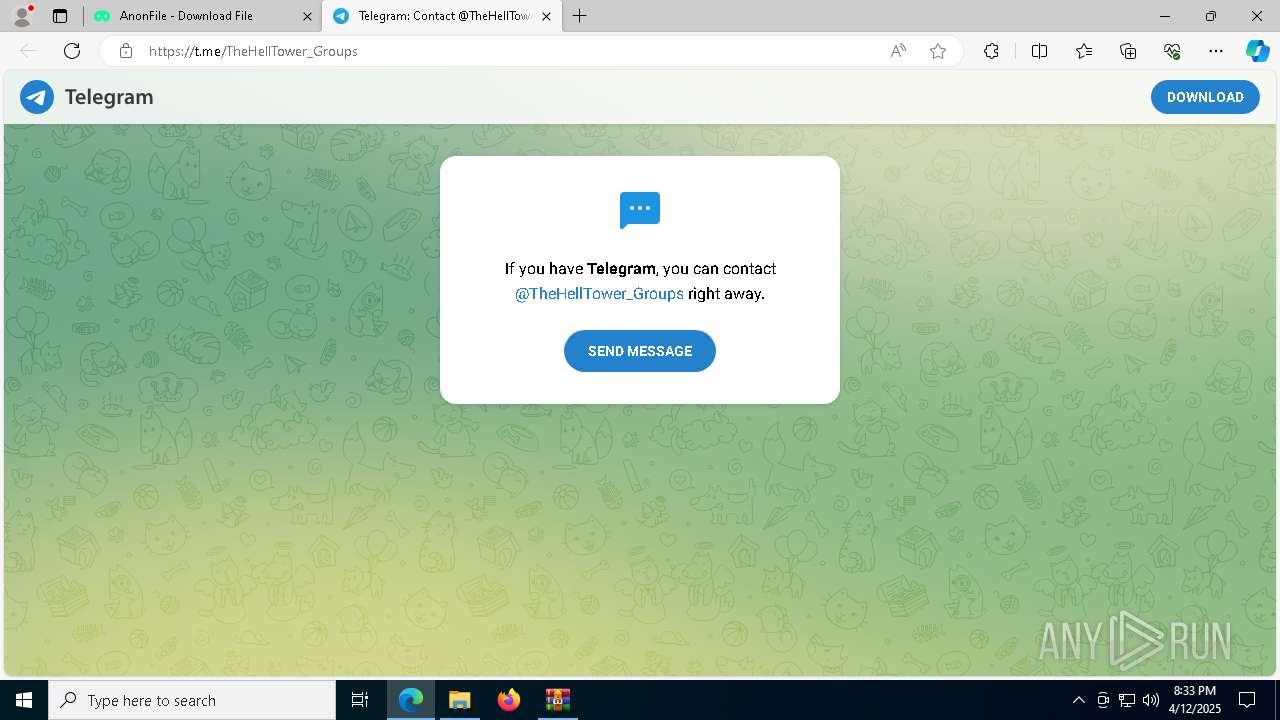
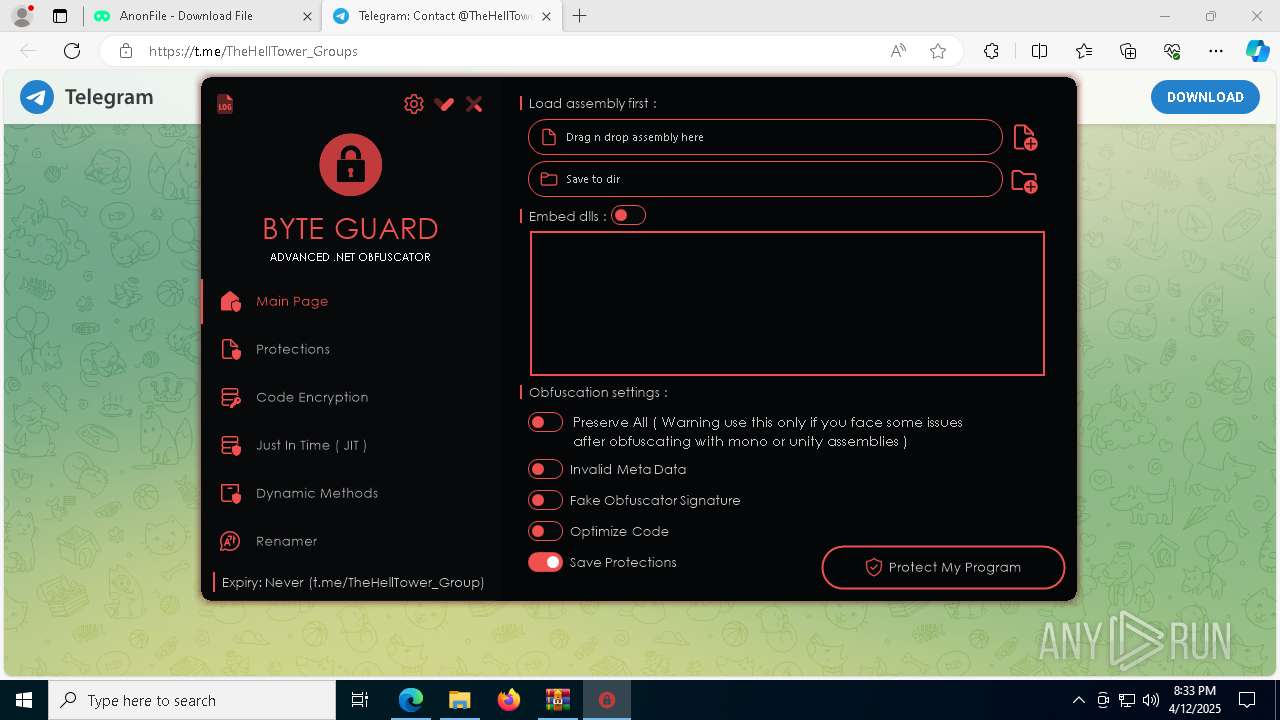
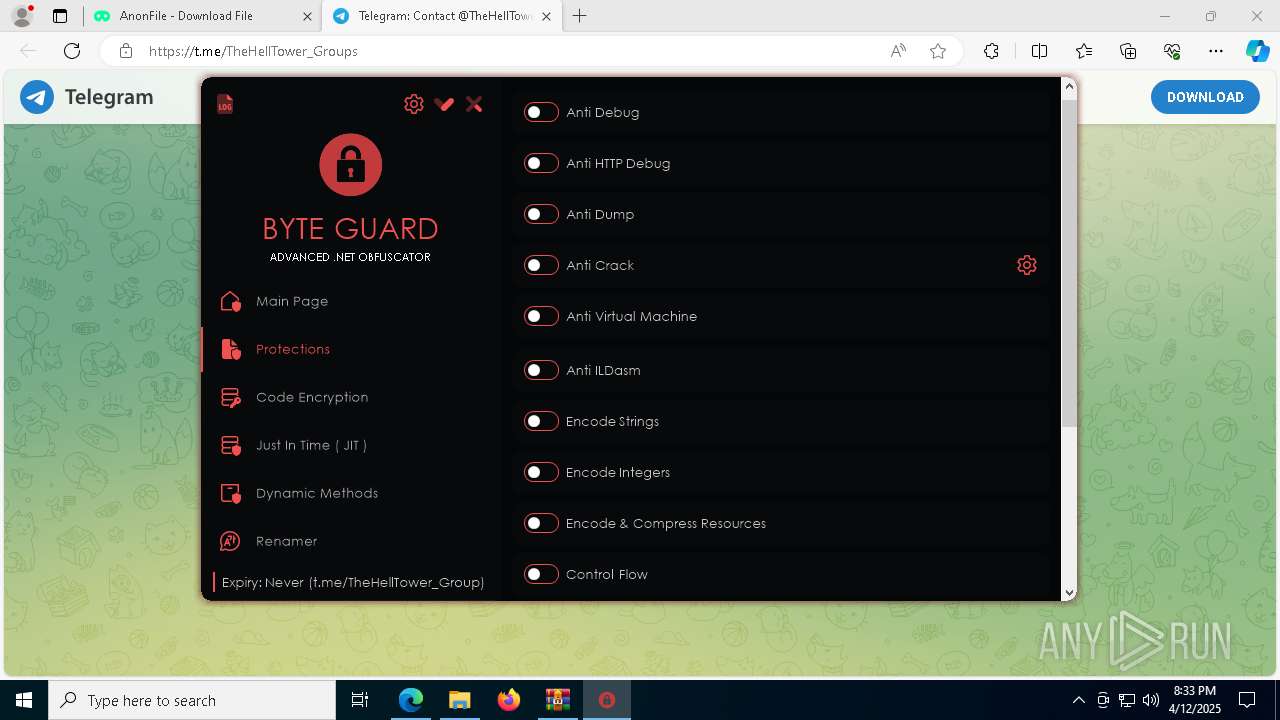
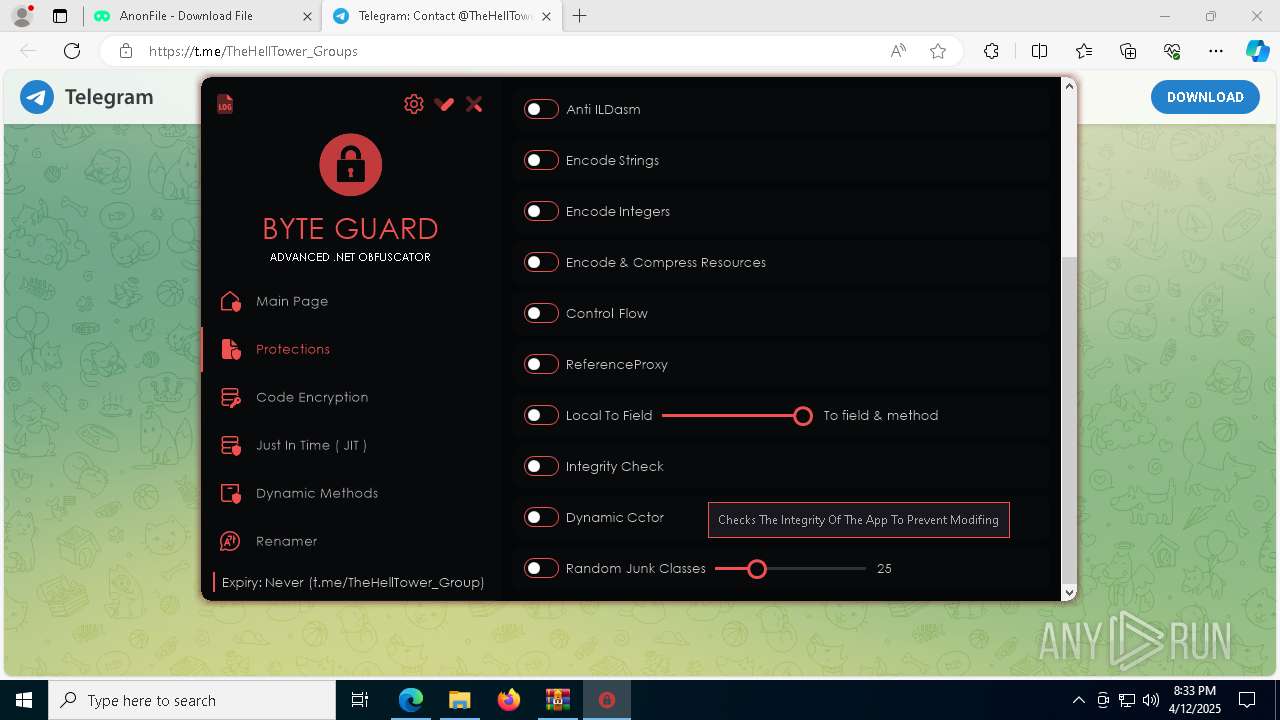
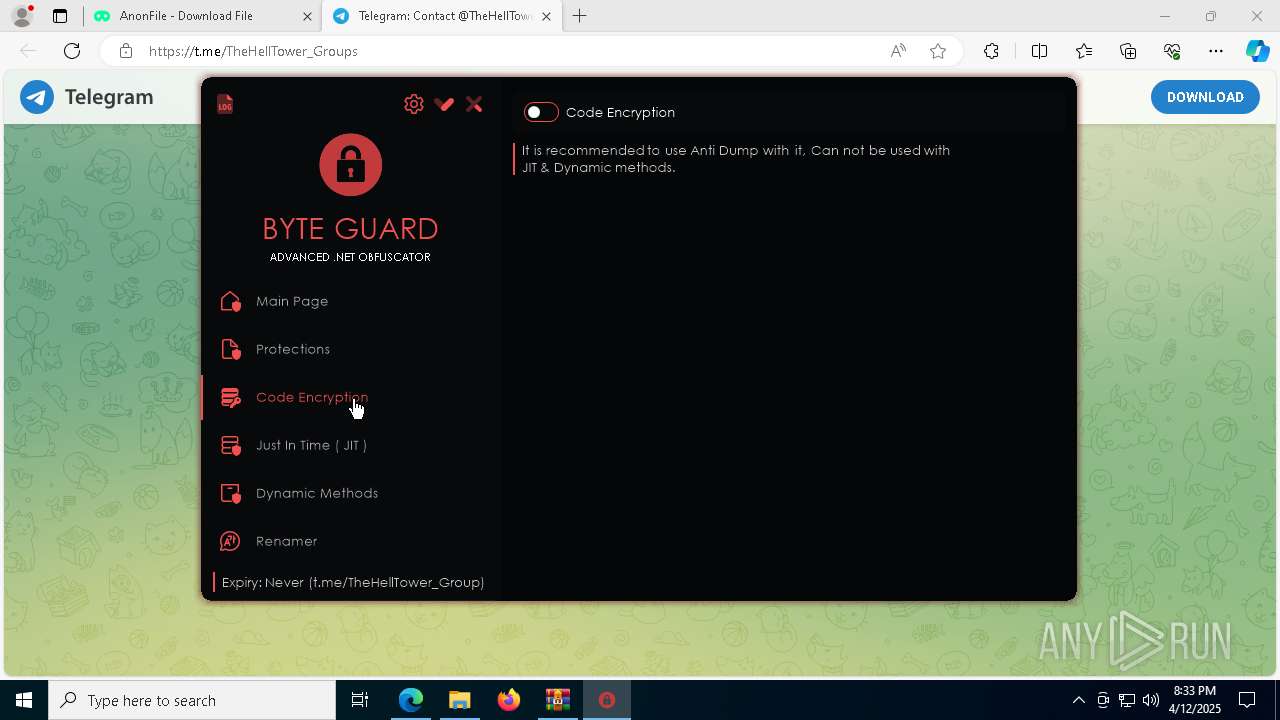
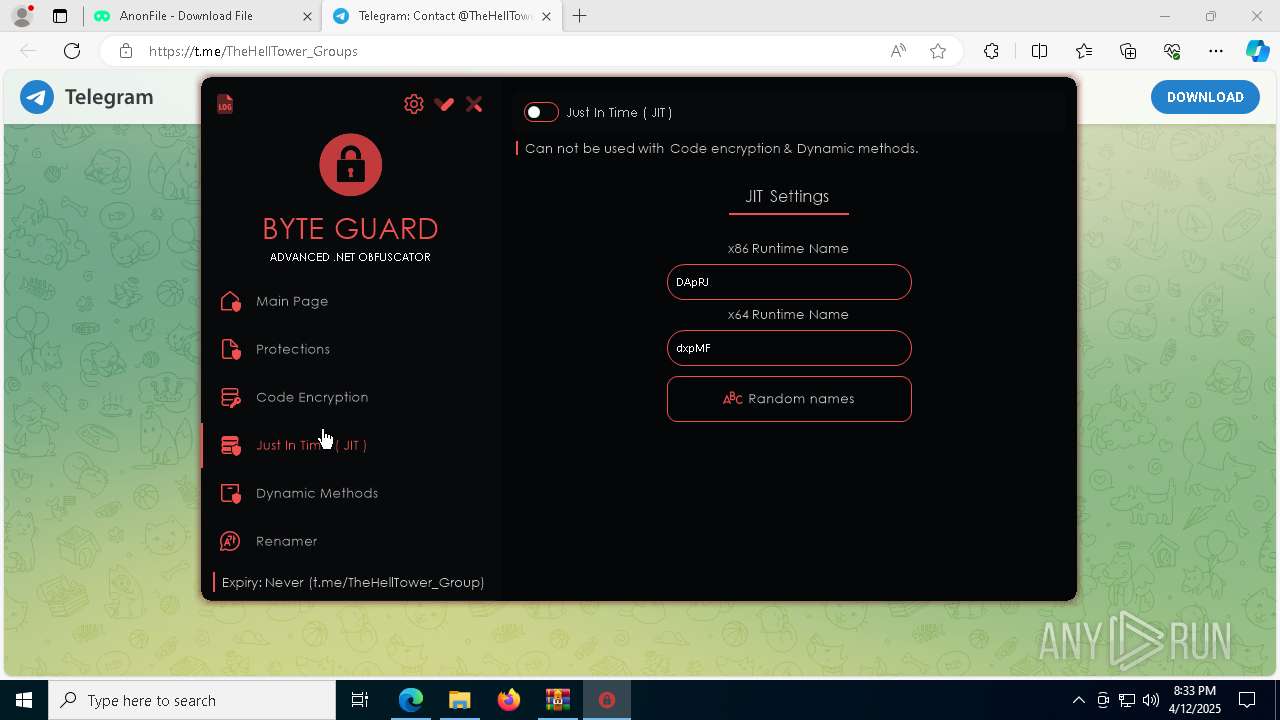
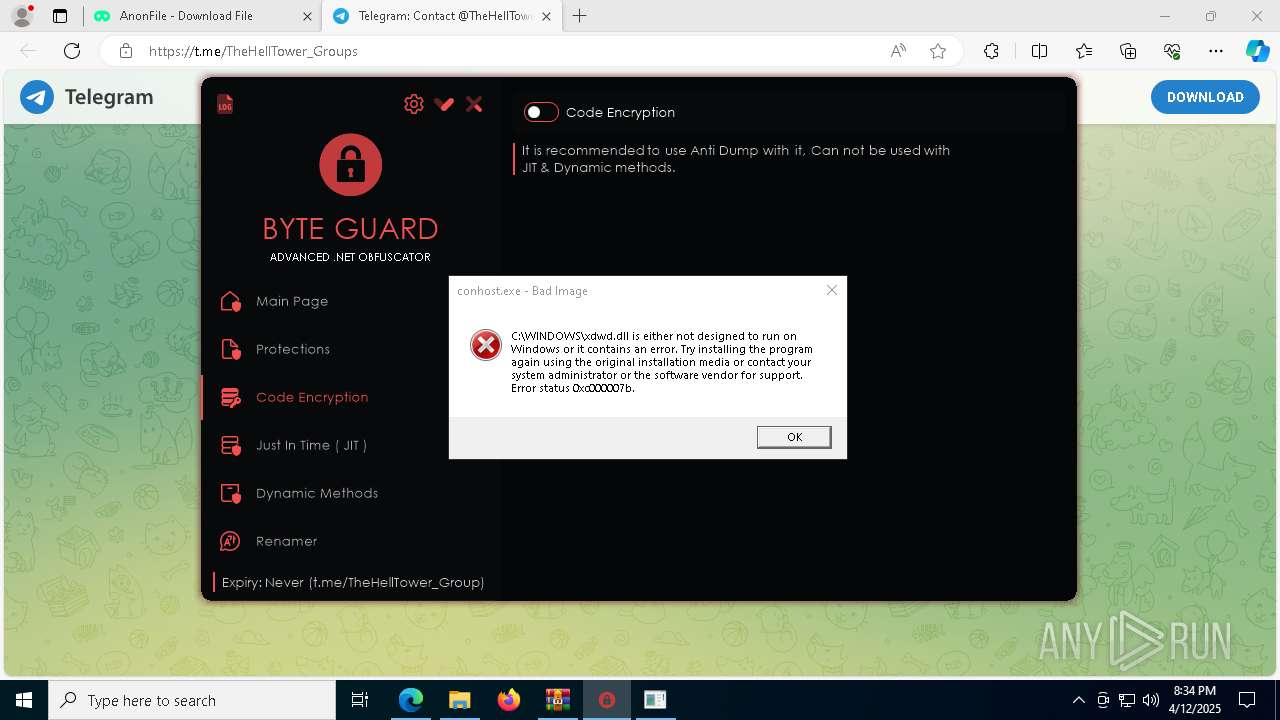
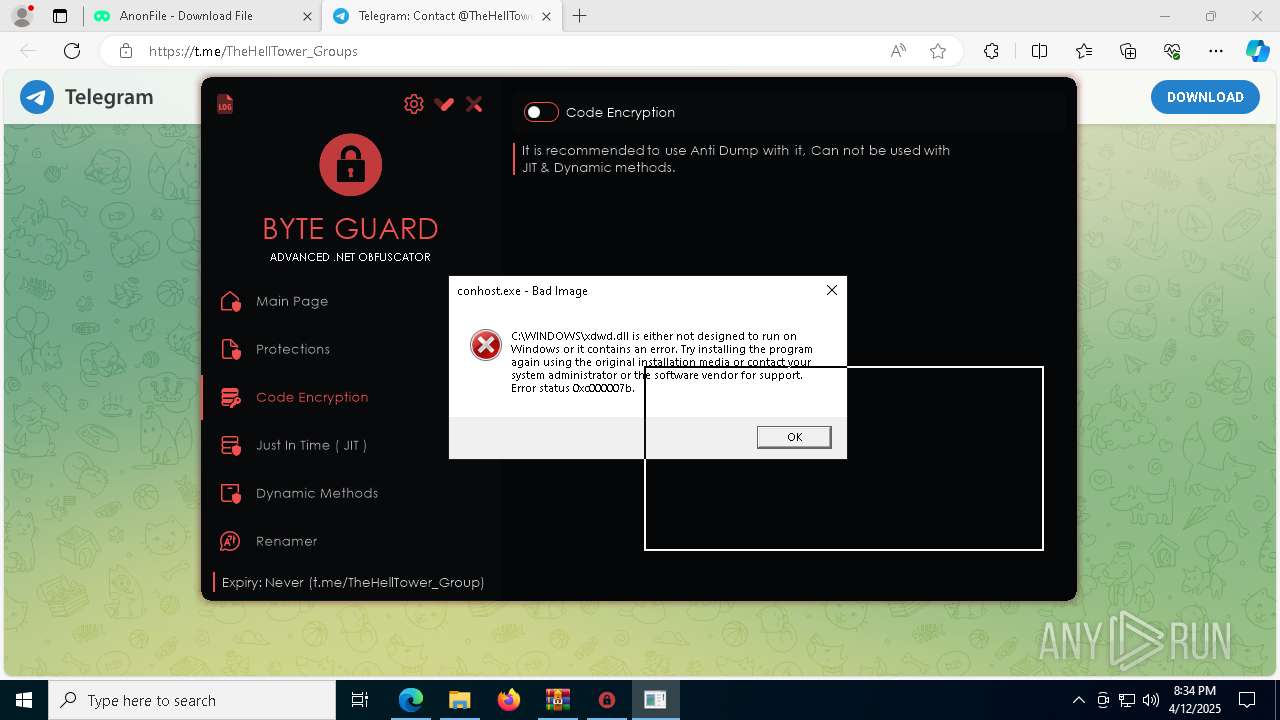
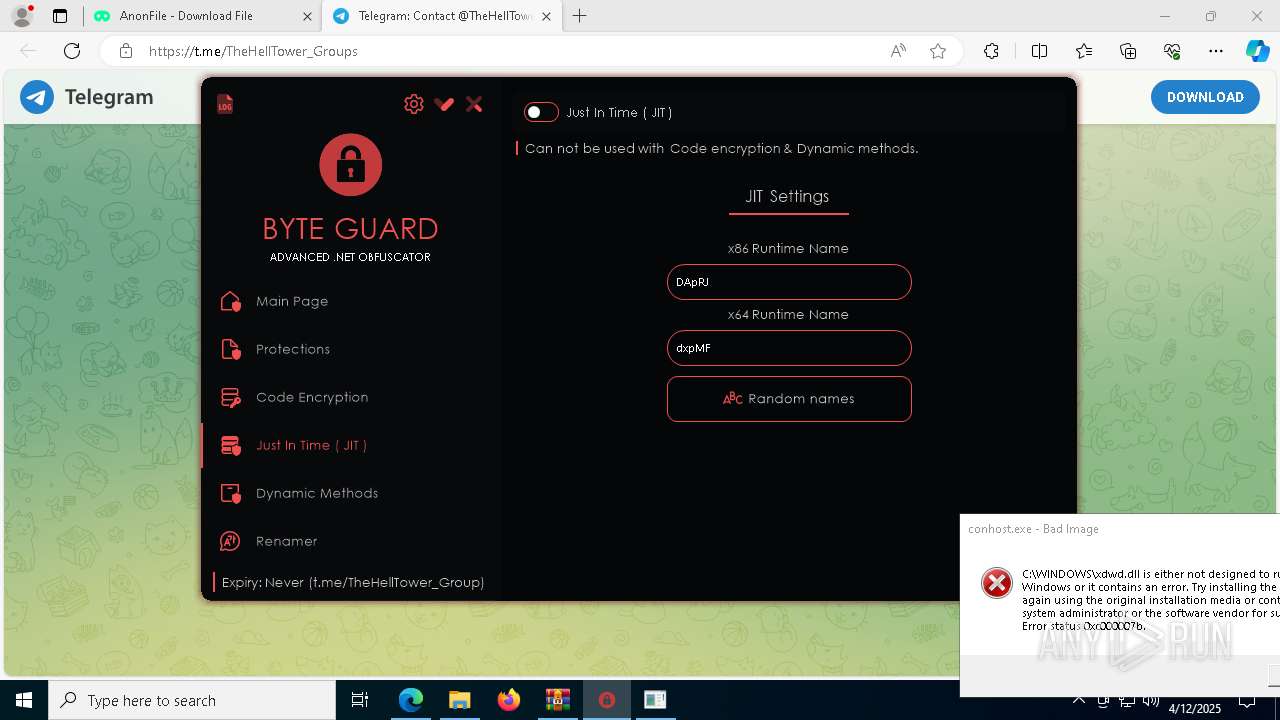
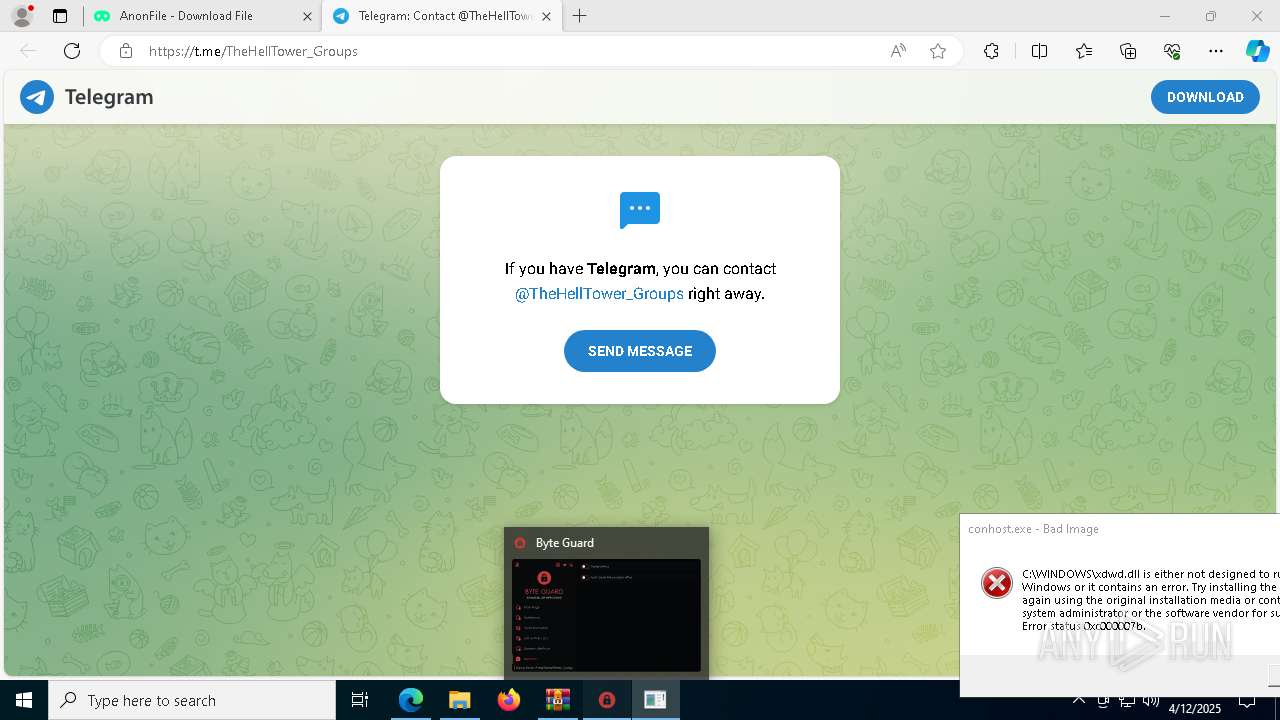
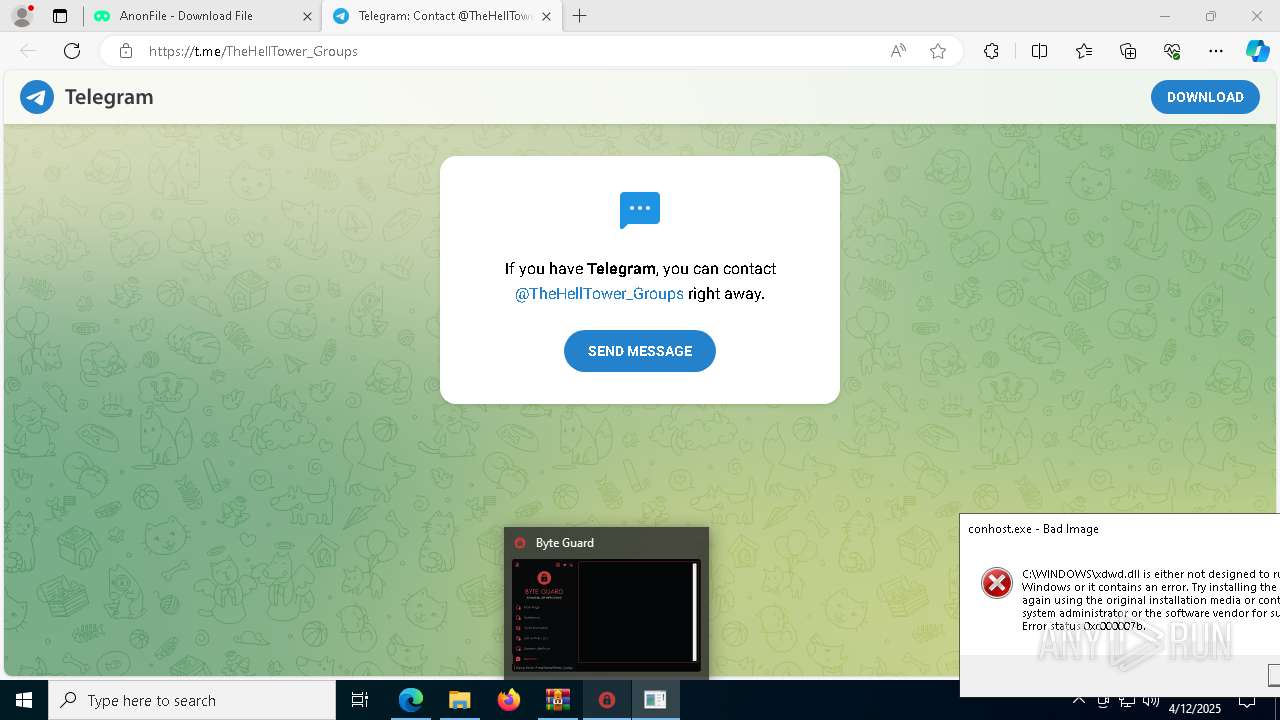
SHEETRAT has been detected (YARA)
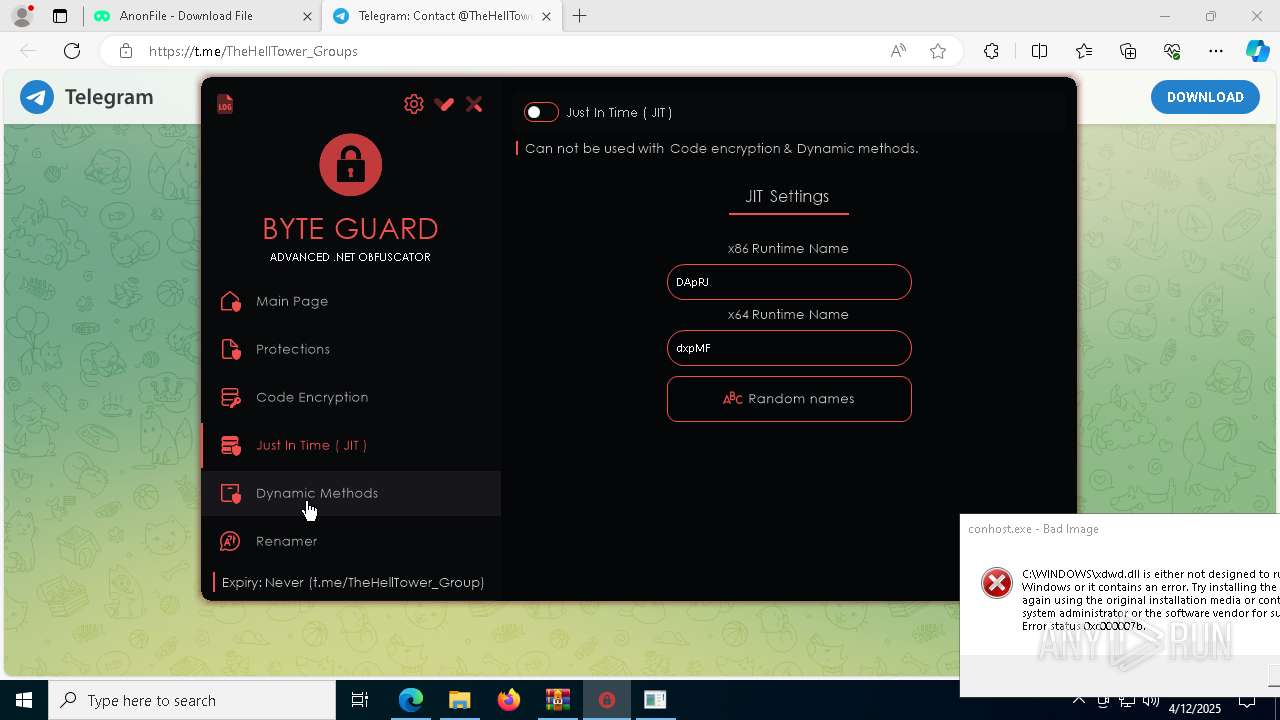
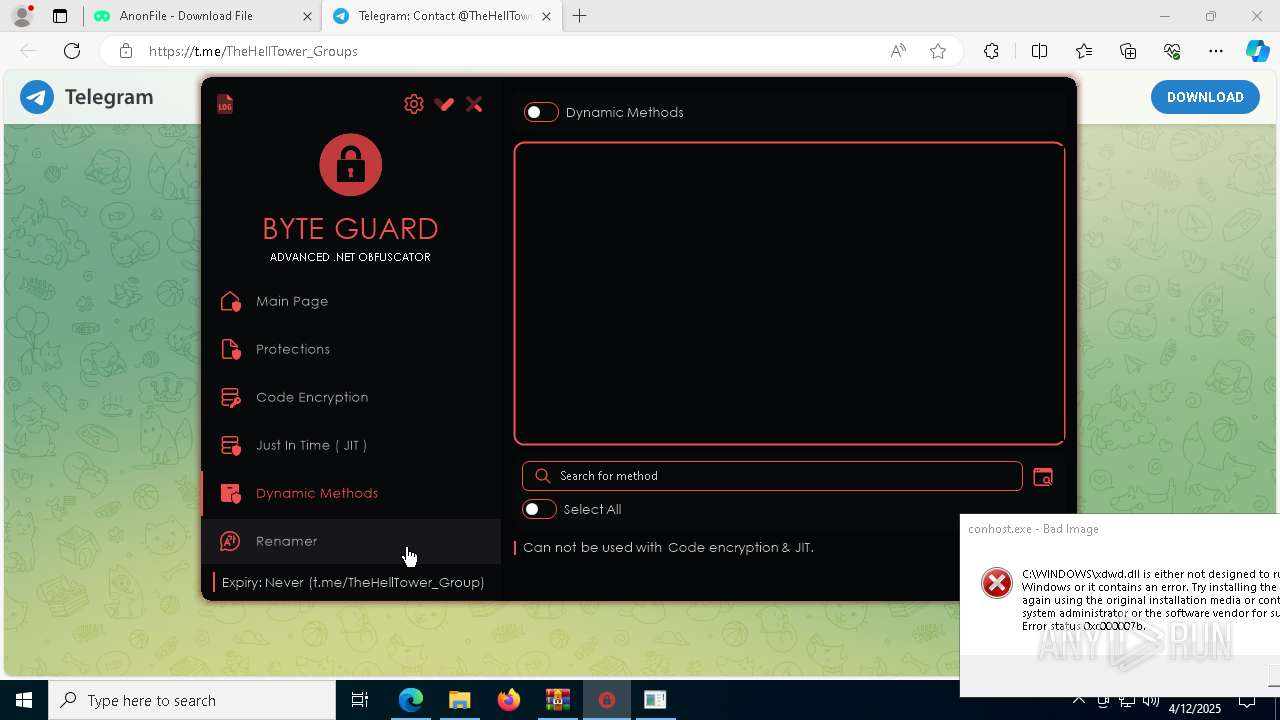
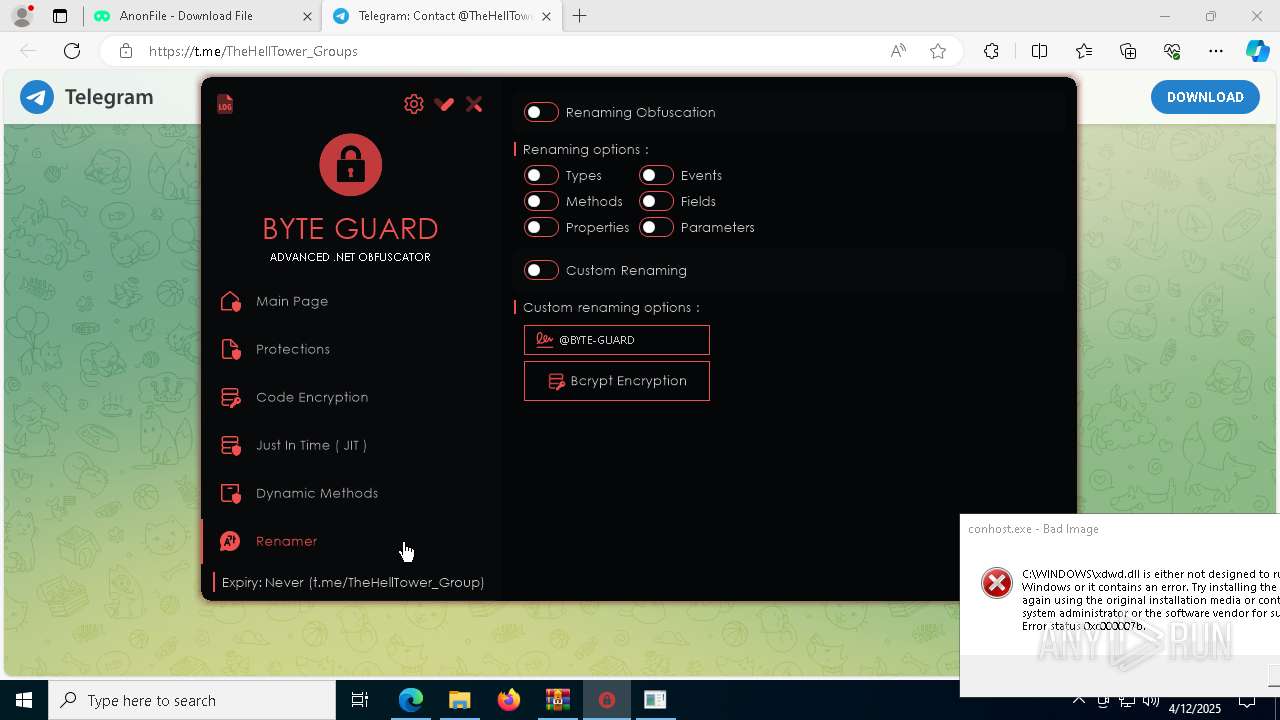
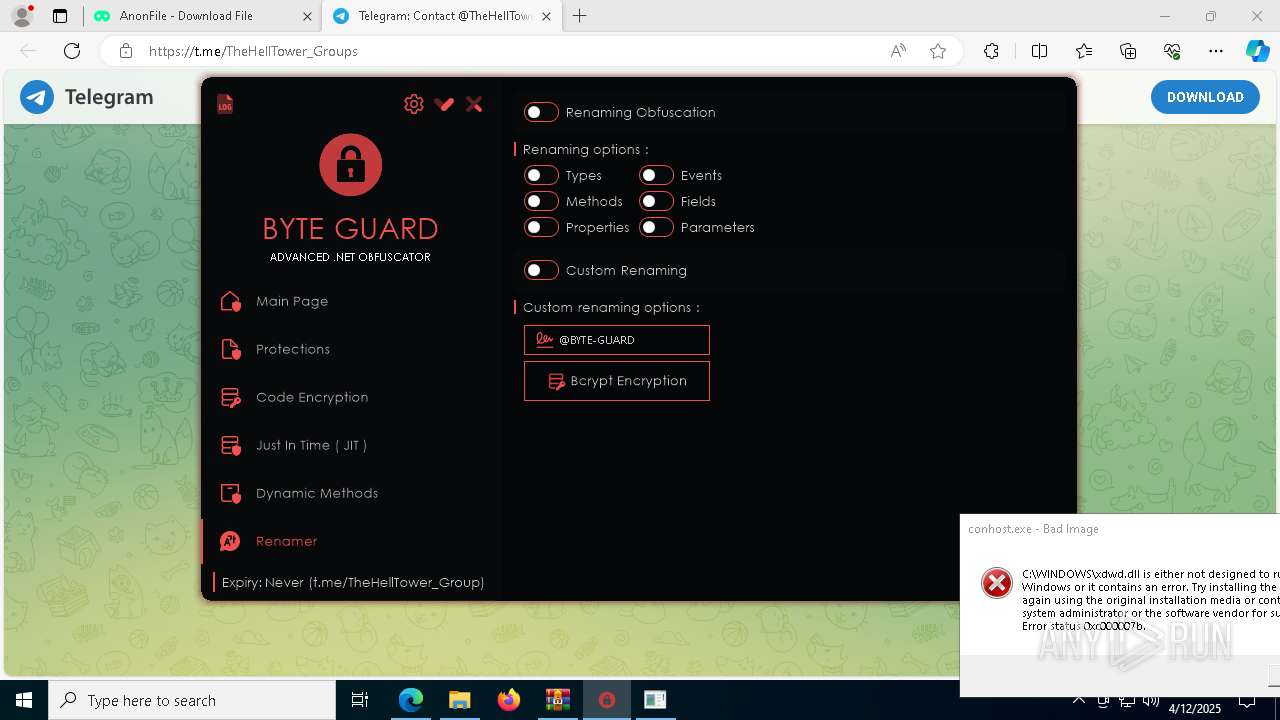
- Byte Guard.exe (PID: 7924)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 4112)
SHEETRAT mutex has been found
- Client-THT.exe (PID: 4728)
Changes the login/logoff helper path in the registry
- Client-THT.exe (PID: 4728)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6768)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 232)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 3016)
Changes the AppInit_DLLs value (autorun option)
- Client-THT.exe (PID: 4728)
Changes the autorun value in the registry
- Client-THT.exe (PID: 4728)
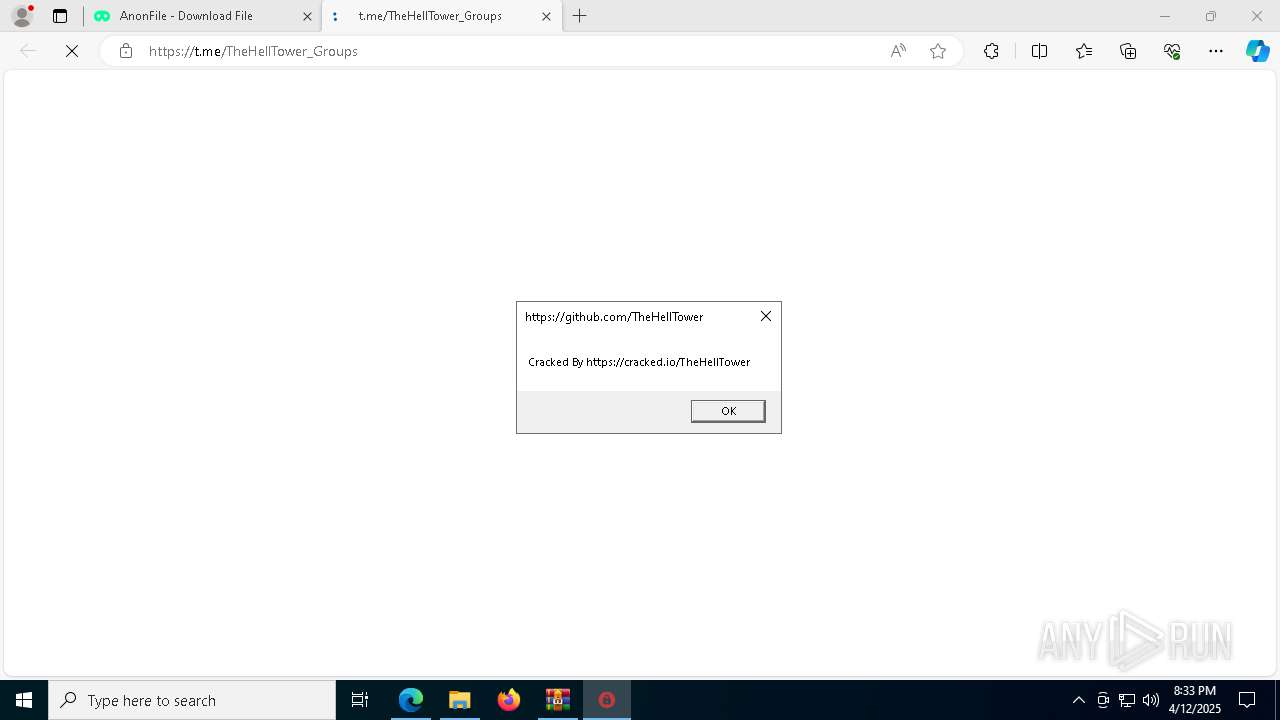
Connects to the CnC server
- Client-THT.exe (PID: 4728)
DARKCRYSTAL has been detected (SURICATA)
- Client-THT.exe (PID: 4728)
XORed URL has been found (YARA)
- Client-THT.exe (PID: 4728)
SHEETRAT has been detected (SURICATA)
- Client-THT.exe (PID: 4728)
SUSPICIOUS
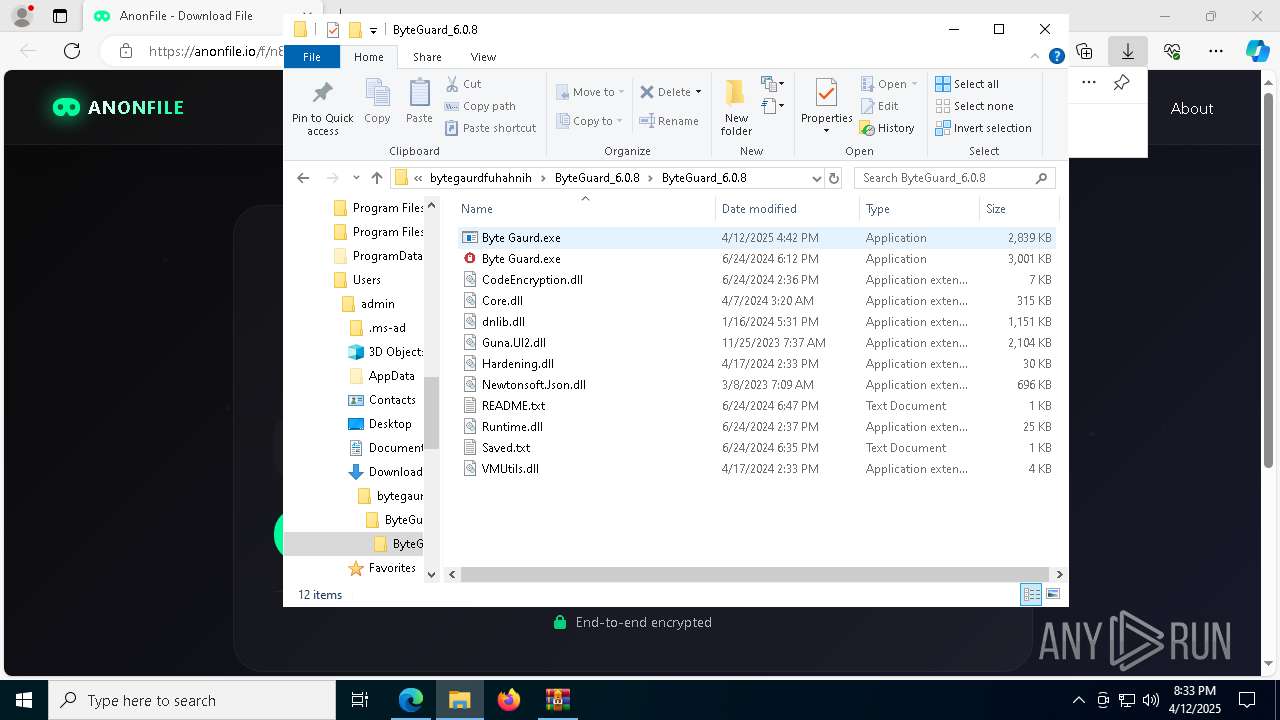
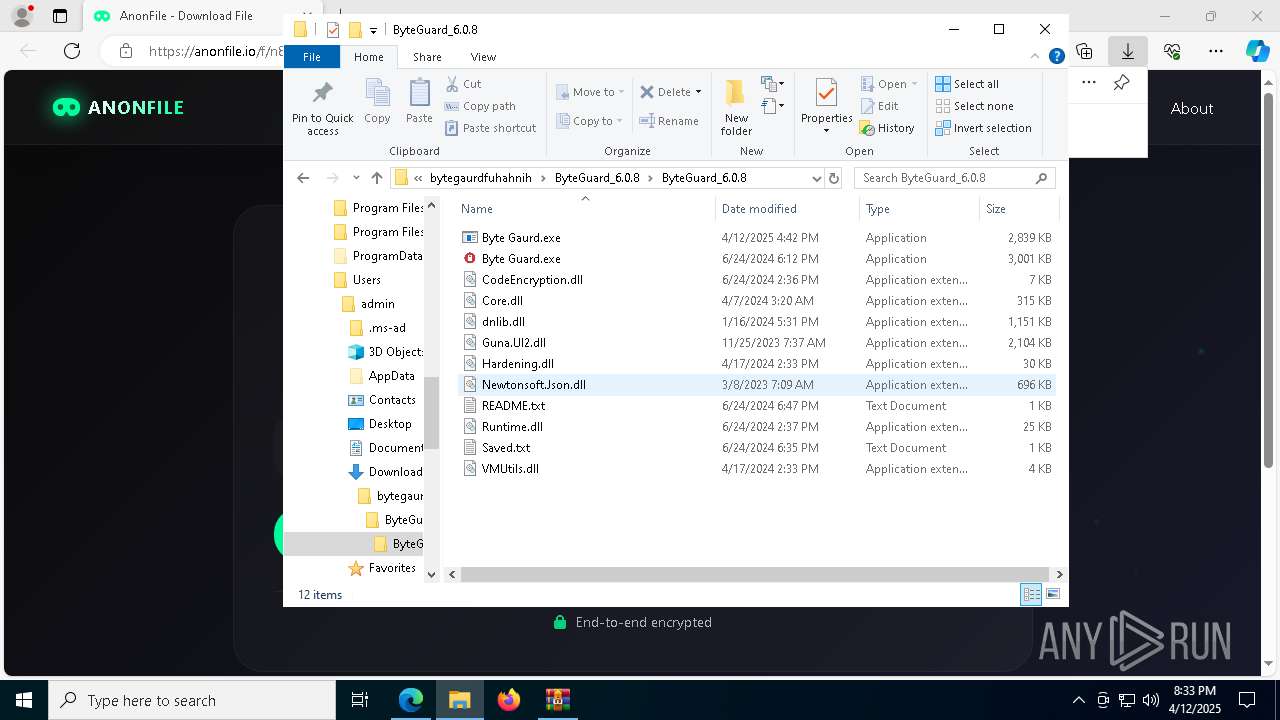
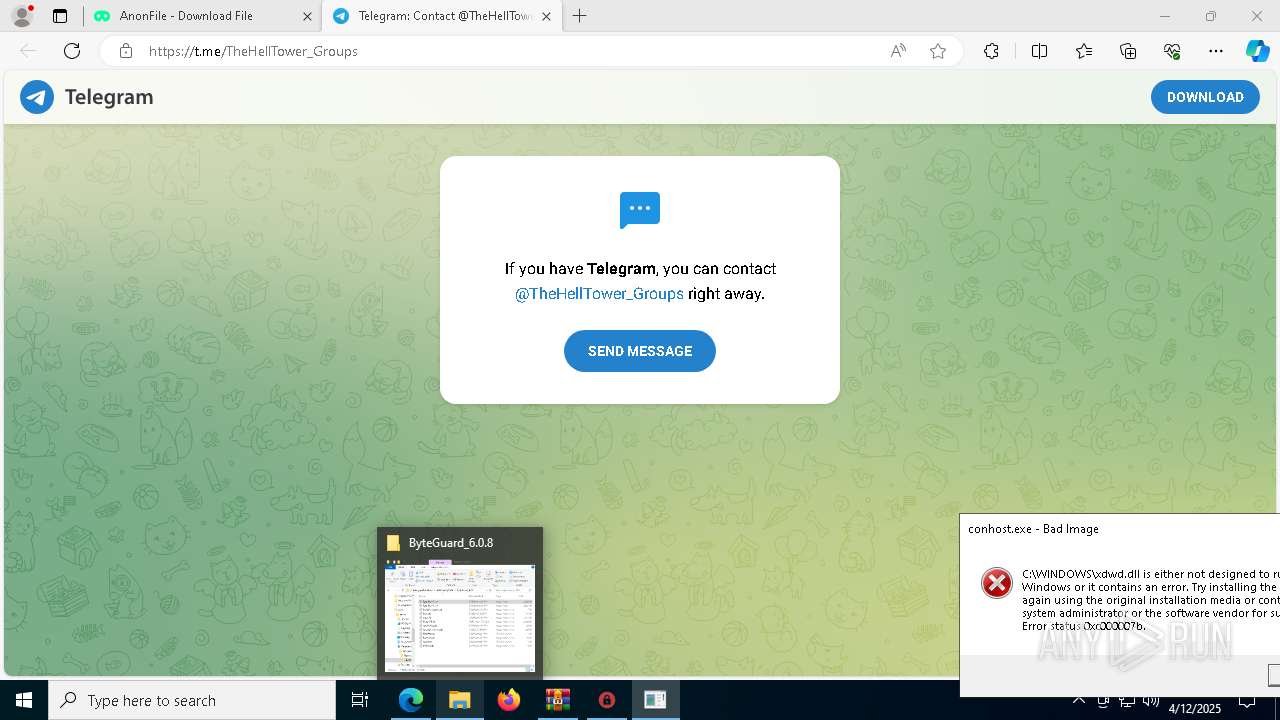
Executable content was dropped or overwritten
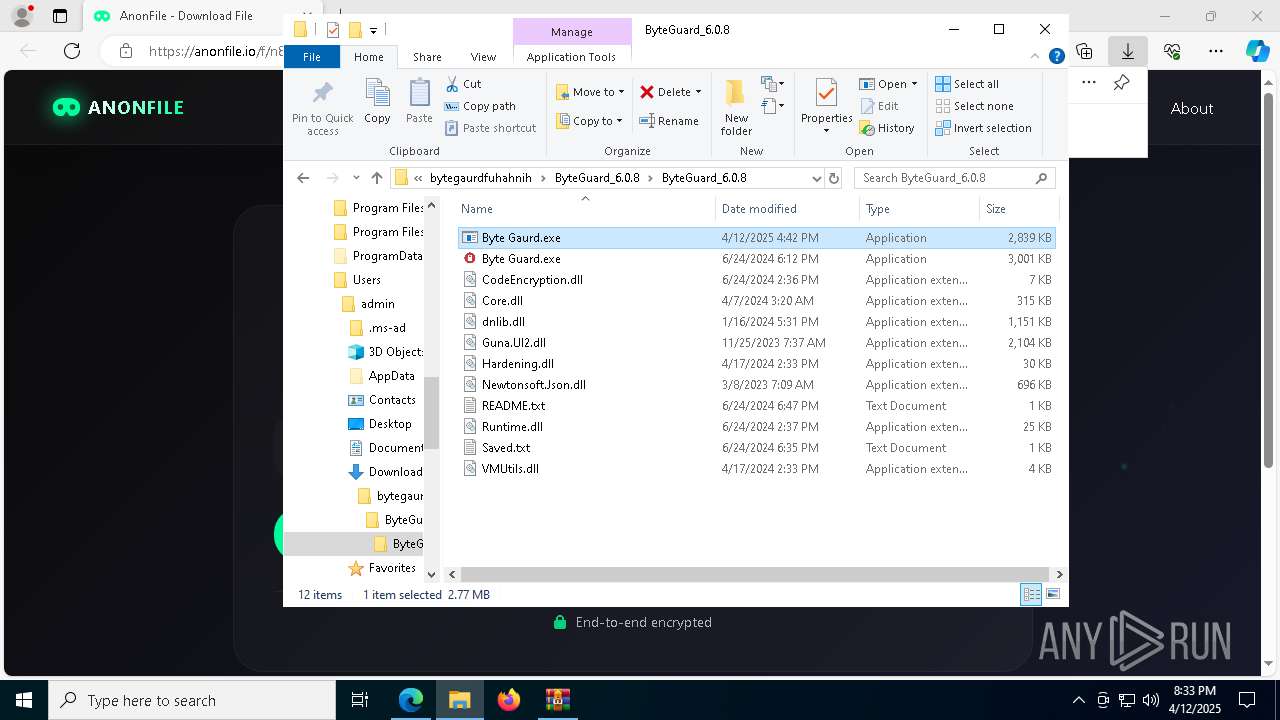
- Byte Gaurd.exe (PID: 7996)
- Client-THT.exe (PID: 4728)
Reads security settings of Internet Explorer
- Byte Gaurd.exe (PID: 7996)
- Byte Guard.exe (PID: 7924)
- Client-THT.exe (PID: 7904)
Reads the date of Windows installation
- Client-THT.exe (PID: 7904)
Application launched itself
- Client-THT.exe (PID: 7904)
- Client-THT.exe (PID: 4728)
There is functionality for taking screenshot (YARA)
- Byte Guard.exe (PID: 7924)
Starts CMD.EXE for commands execution
- Client-THT.exe (PID: 4728)
Connects to unusual port
- Client-THT.exe (PID: 4728)
Executes as Windows Service
- WmiApSrv.exe (PID: 7740)
The process checks if it is being run in the virtual environment
- Client-THT.exe (PID: 4728)
Contacting a server suspected of hosting an CnC
- Client-THT.exe (PID: 4728)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 1676)
Reads Environment values
- identity_helper.exe (PID: 2568)
Create files in a temporary directory
- Byte Gaurd.exe (PID: 7996)
Checks supported languages
- identity_helper.exe (PID: 2568)
- Byte Gaurd.exe (PID: 7996)
- Client-THT.exe (PID: 7904)
- Byte Guard.exe (PID: 7924)
- Client-THT.exe (PID: 4728)
- Client-THT.exe (PID: 300)
Reads the computer name
- identity_helper.exe (PID: 2568)
- Byte Gaurd.exe (PID: 7996)
- Client-THT.exe (PID: 7904)
- Byte Guard.exe (PID: 7924)
- Client-THT.exe (PID: 4728)
Reads the software policy settings
- slui.exe (PID: 8036)
- slui.exe (PID: 6208)
Process checks computer location settings
- Byte Gaurd.exe (PID: 7996)
- Client-THT.exe (PID: 7904)
Reads the machine GUID from the registry
- Client-THT.exe (PID: 7904)
- Byte Guard.exe (PID: 7924)
- Client-THT.exe (PID: 4728)
Creates files or folders in the user directory
- Client-THT.exe (PID: 4728)
Reads the time zone
- Client-THT.exe (PID: 4728)
Reads CPU info
- Client-THT.exe (PID: 4728)
Checks proxy server information
- slui.exe (PID: 6208)
The sample compiled with english language support
- msedge.exe (PID: 6572)
Executable content was dropped or overwritten
- msedge.exe (PID: 6572)
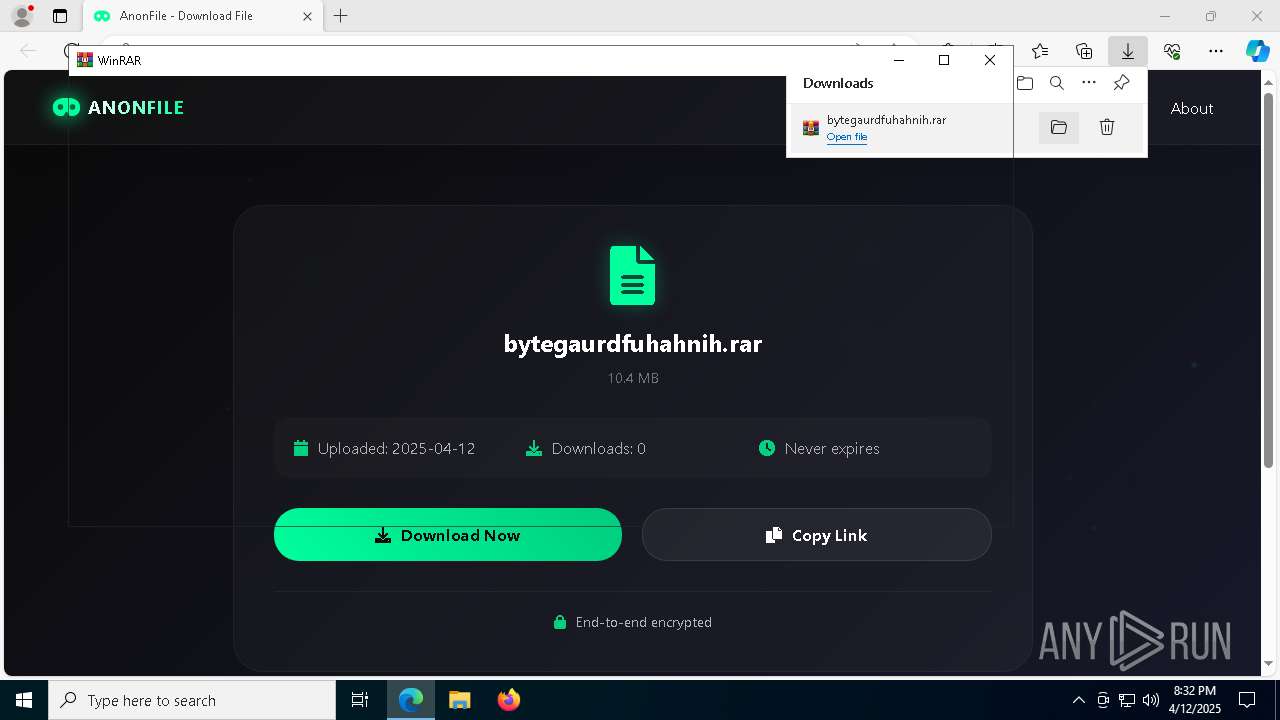
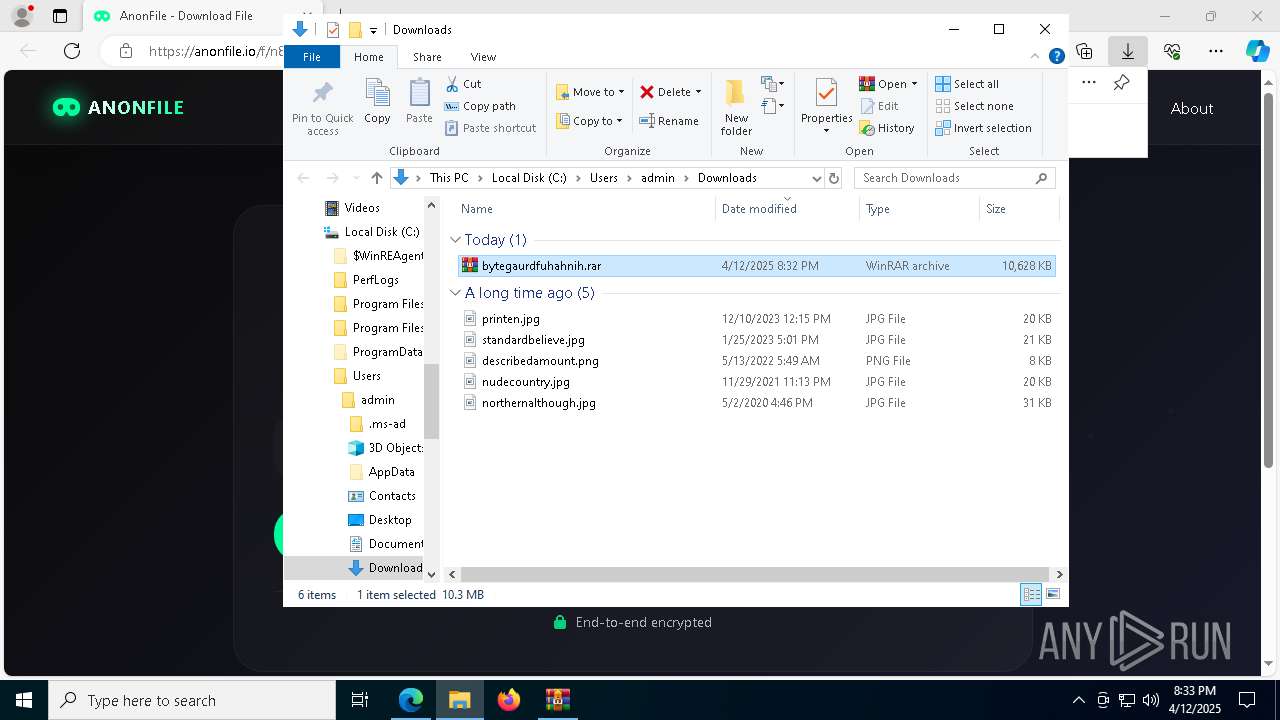
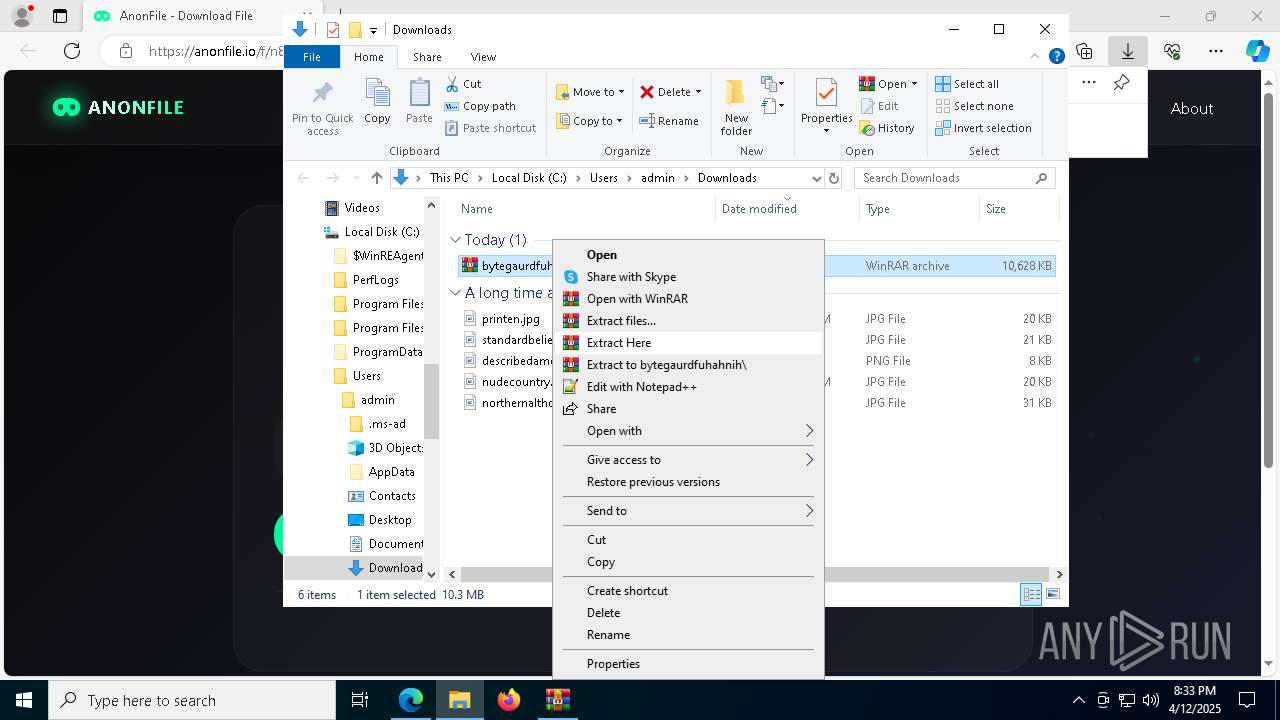
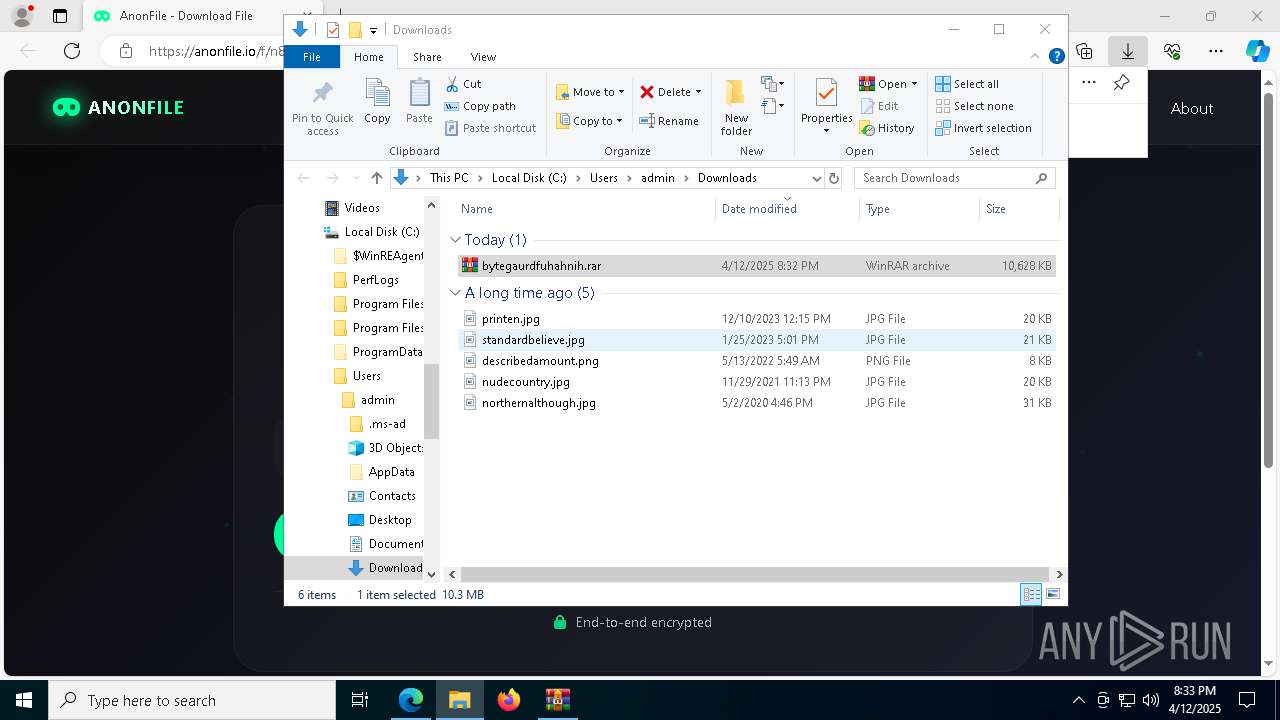
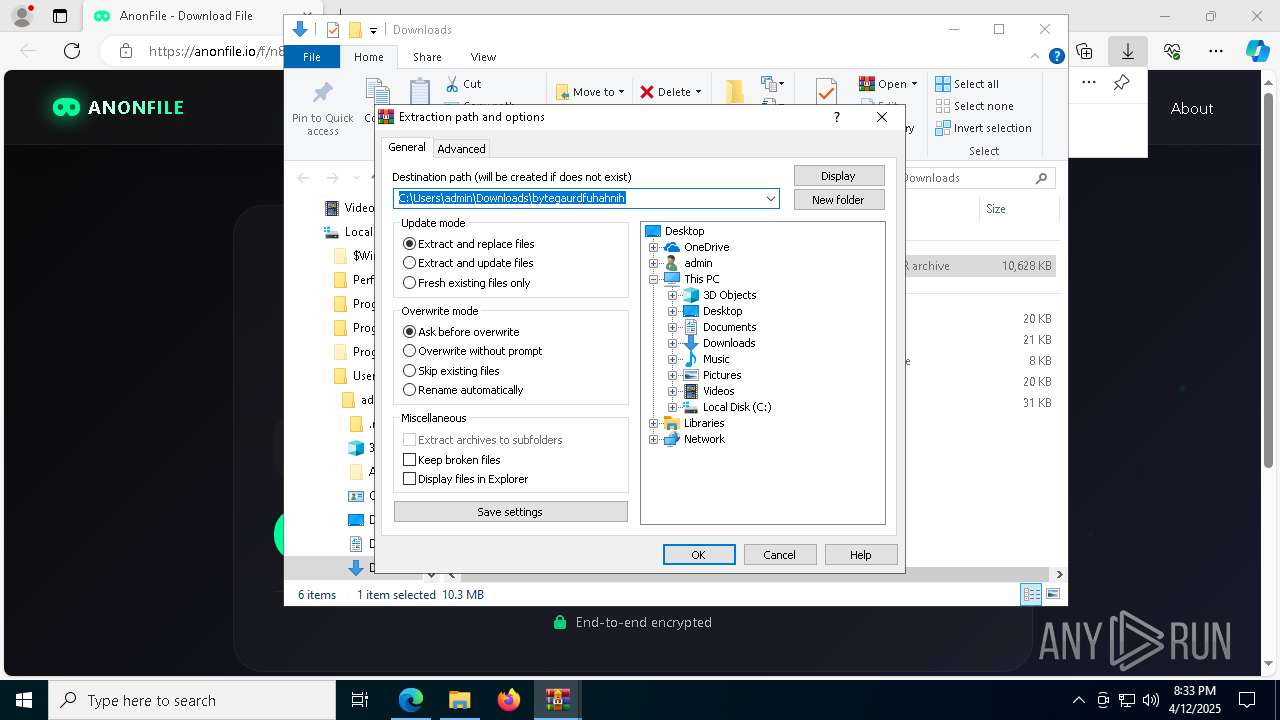
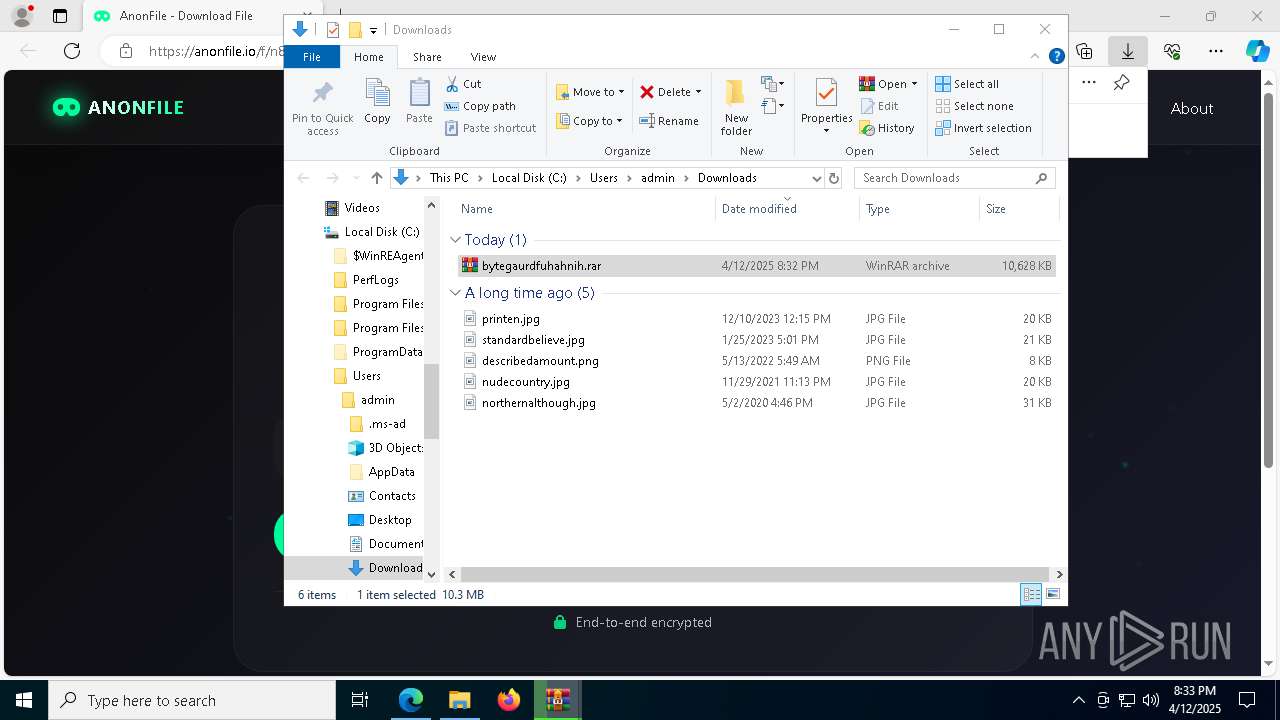
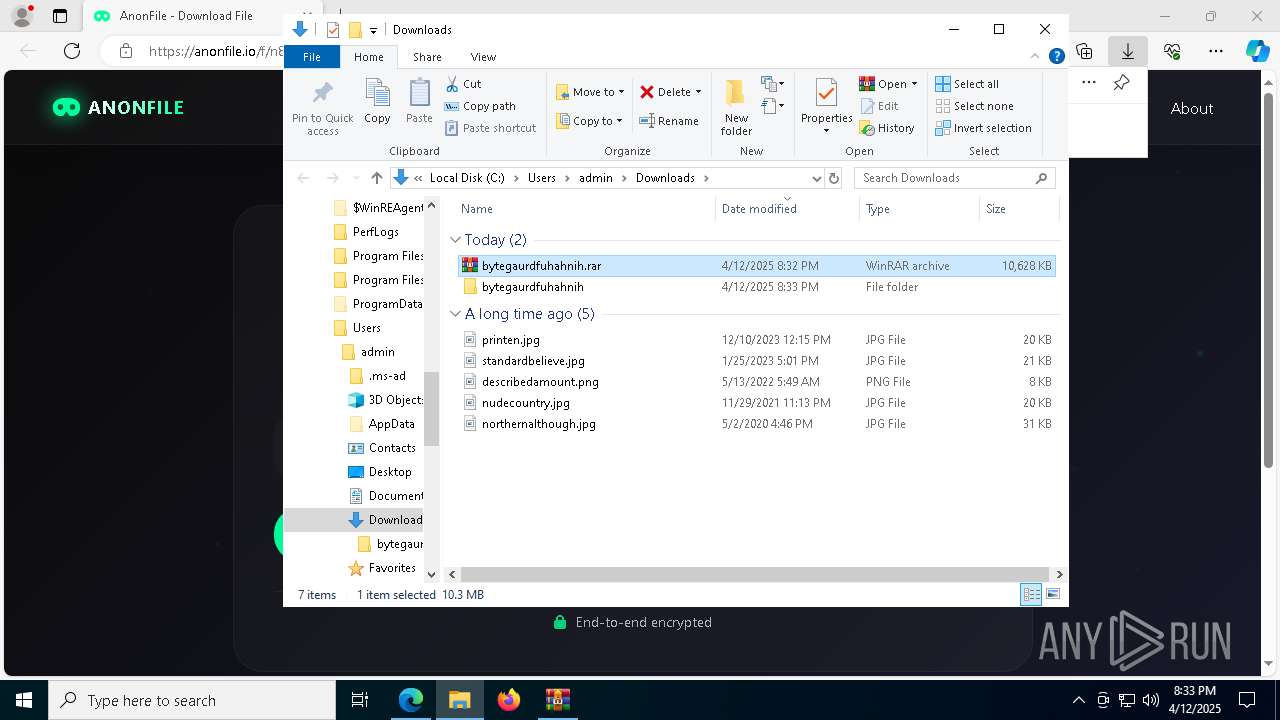
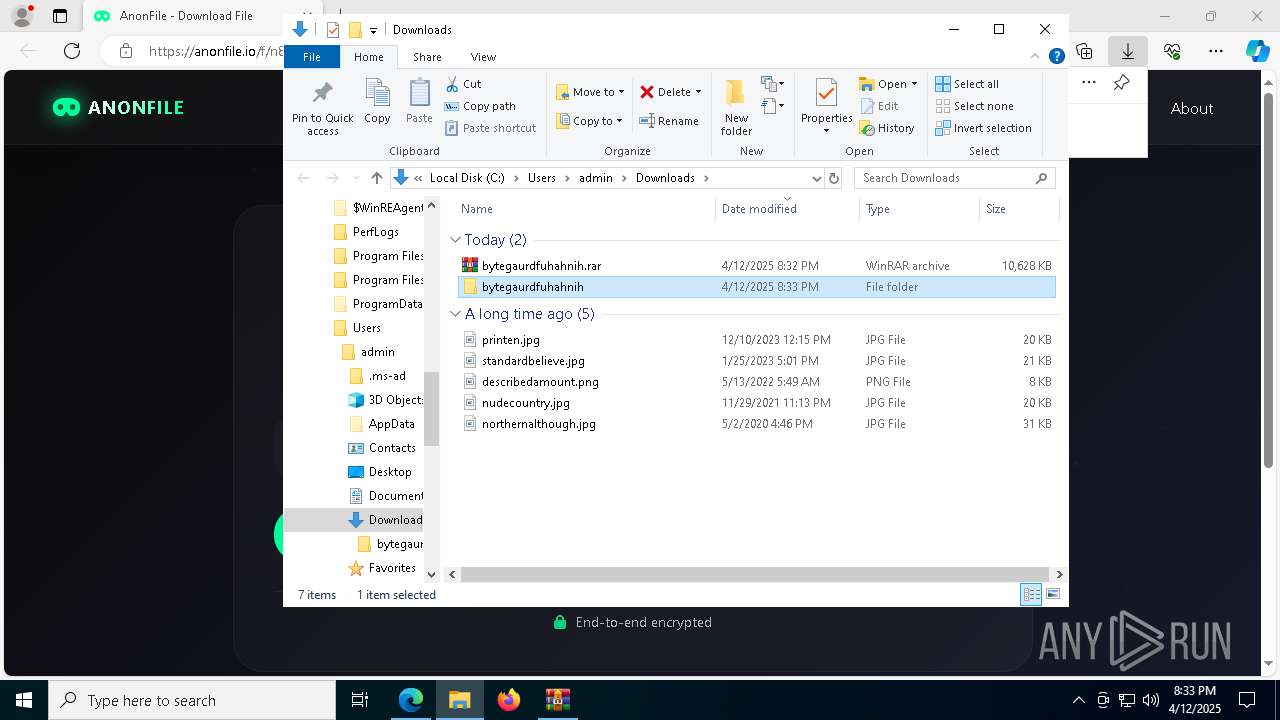
- WinRAR.exe (PID: 1760)
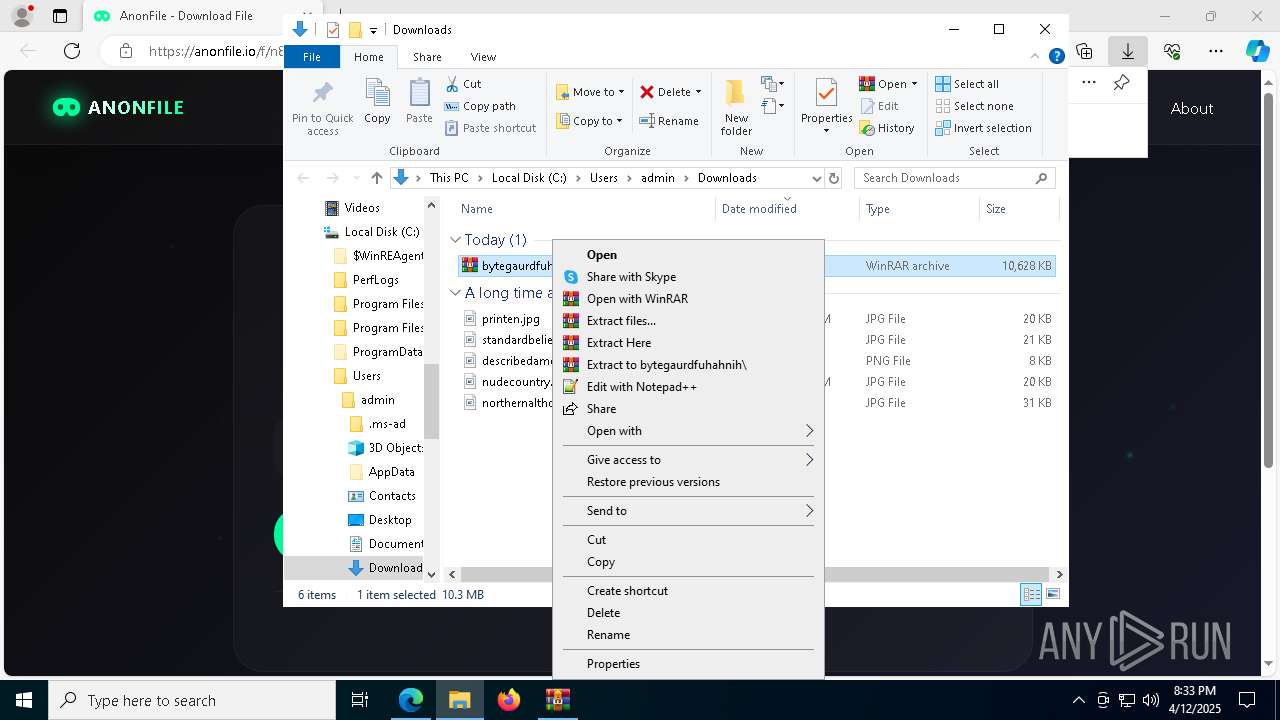
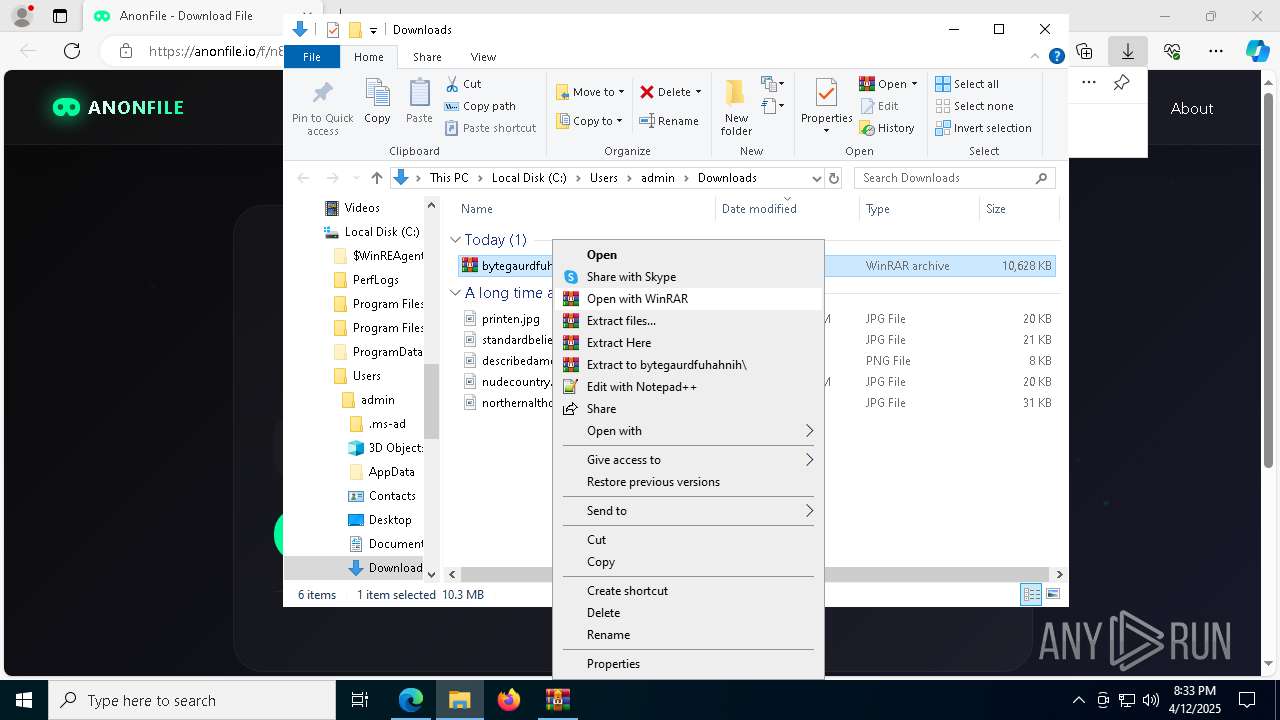
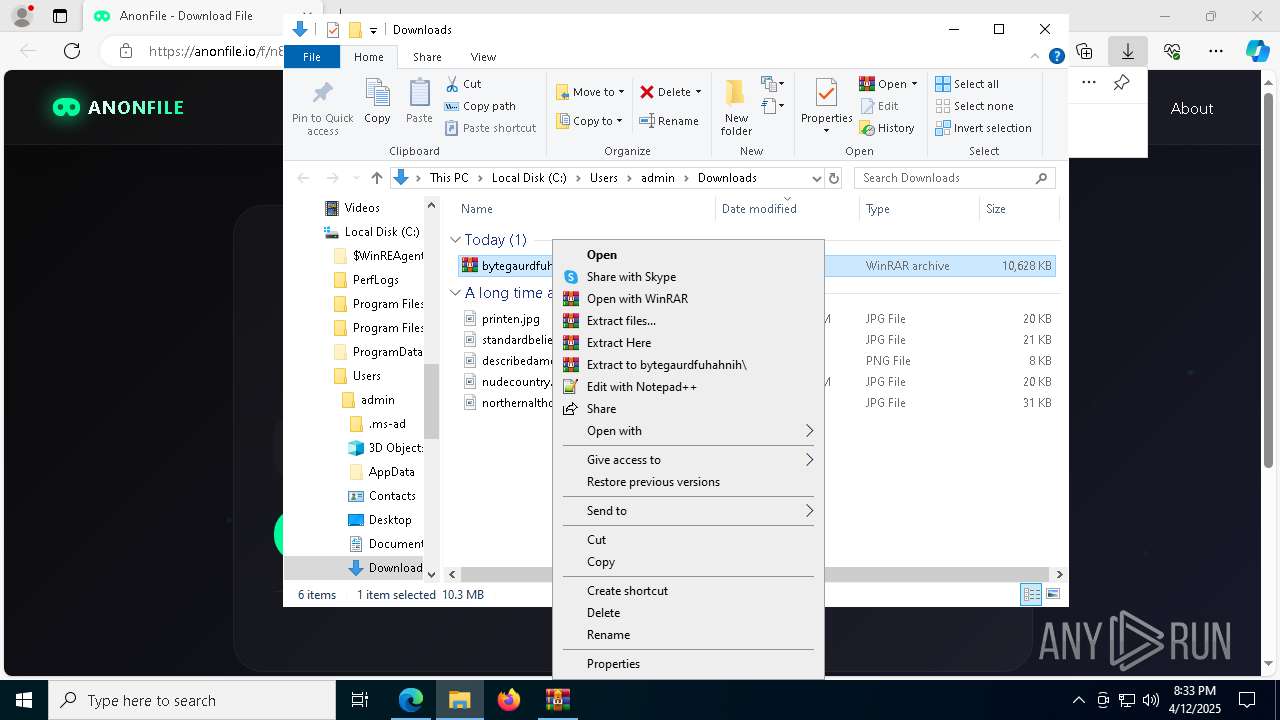
Manual execution by a user
- Byte Gaurd.exe (PID: 7996)
- WinRAR.exe (PID: 1760)
Autorun file from Downloads
- msedge.exe (PID: 6872)
Application launched itself
- msedge.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
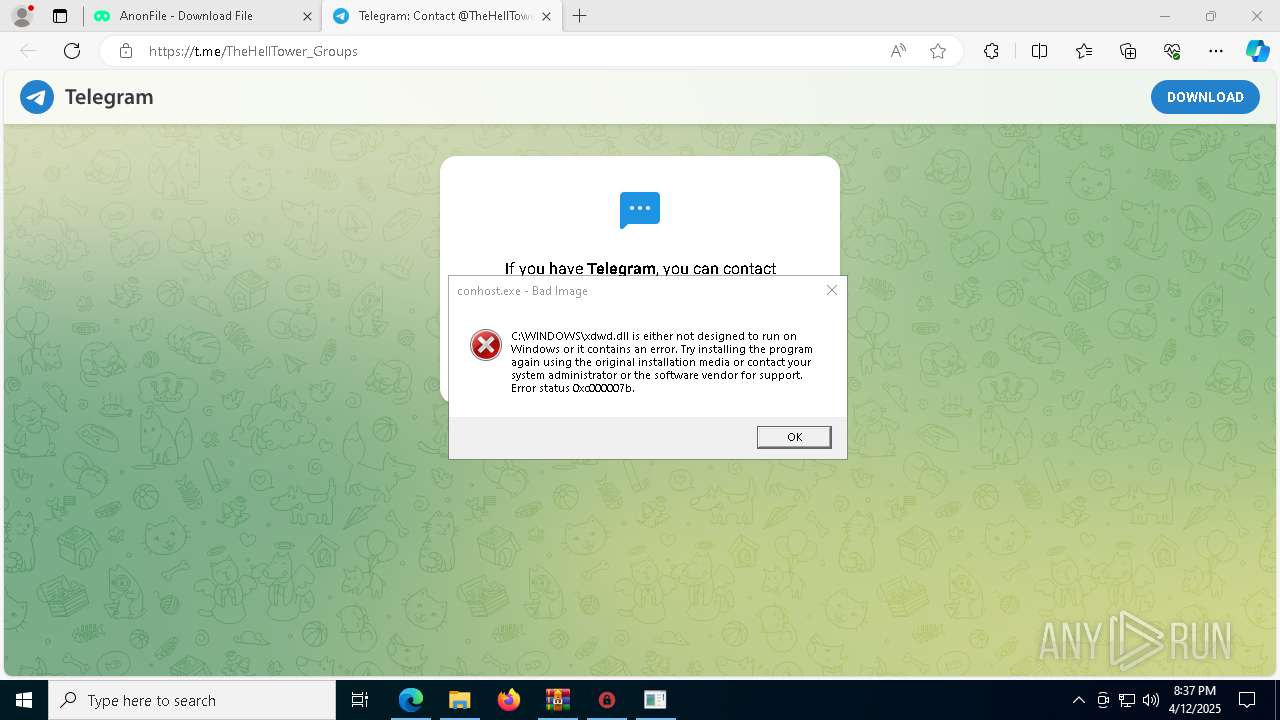
xor-url
(PID) Process(4728) Client-THT.exe
Decrypted-URLs (1)http://marketdedamoroza.webhop.me/index.html
Total processes
344
Monitored processes
200
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "XAMPP" /tr "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\xdwdGreenshot.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Client-THT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "XAMPP" /tr "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\xdwdGreenshot.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Client-THT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
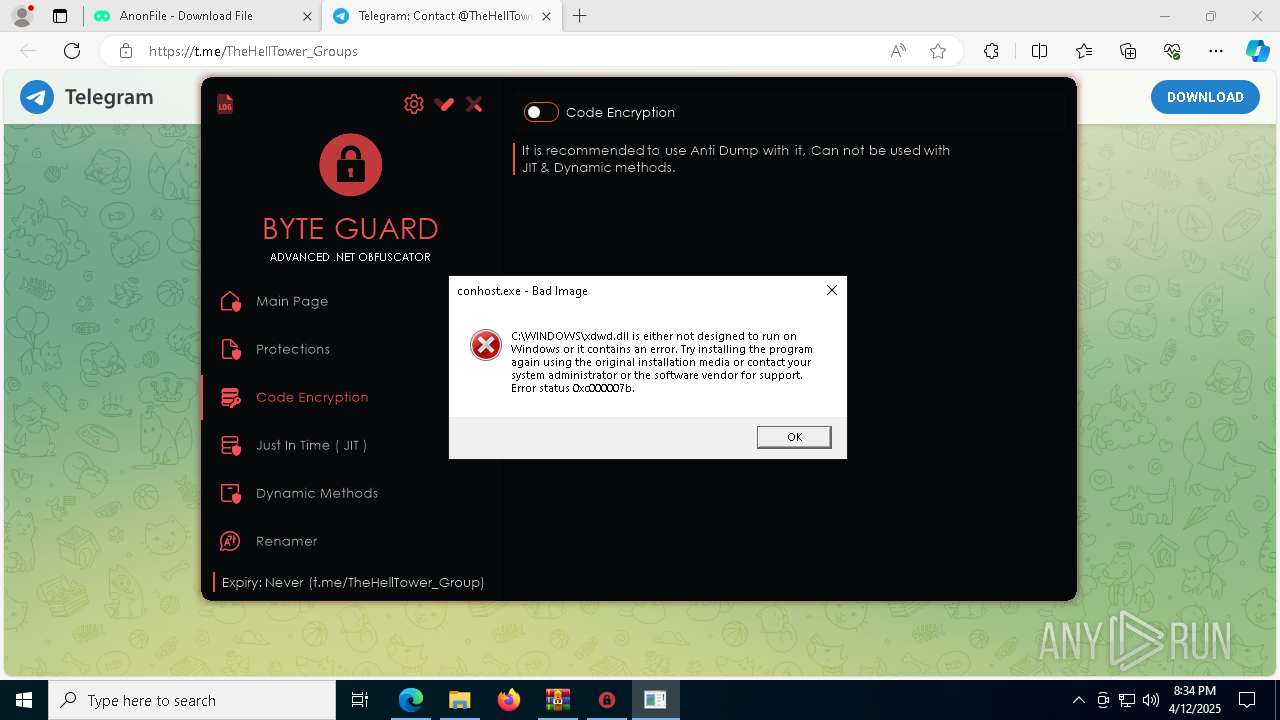
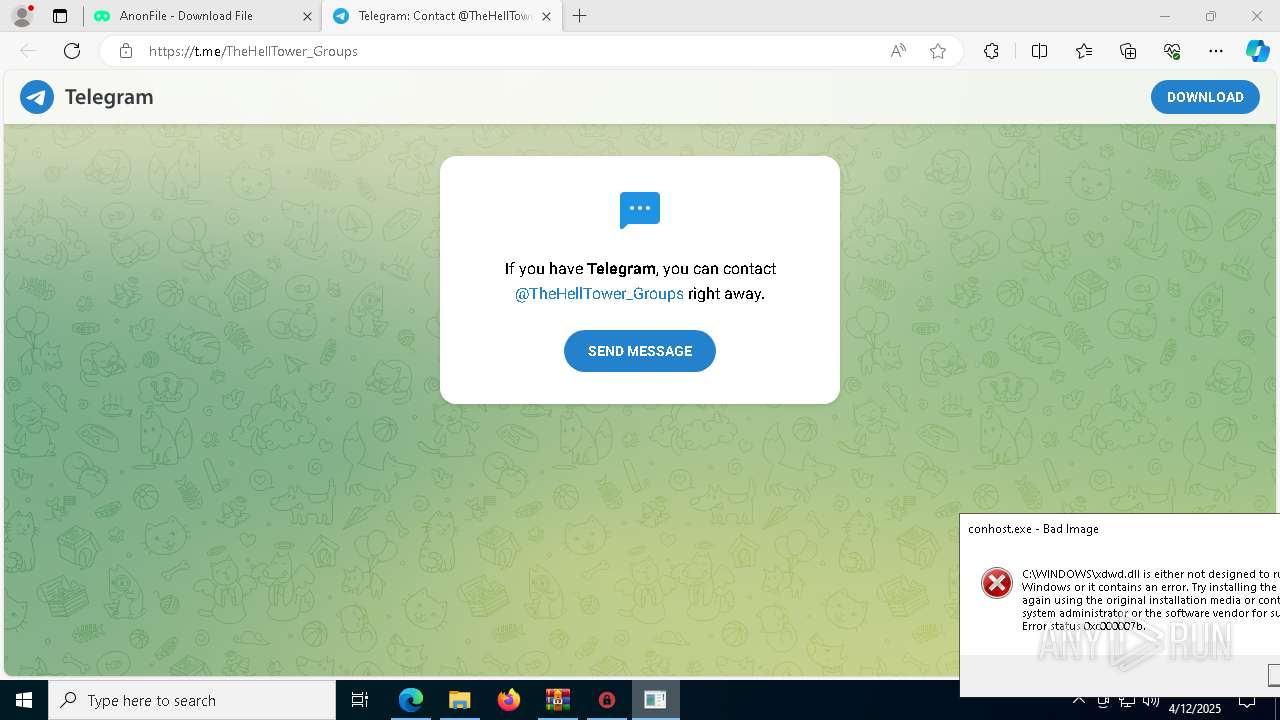
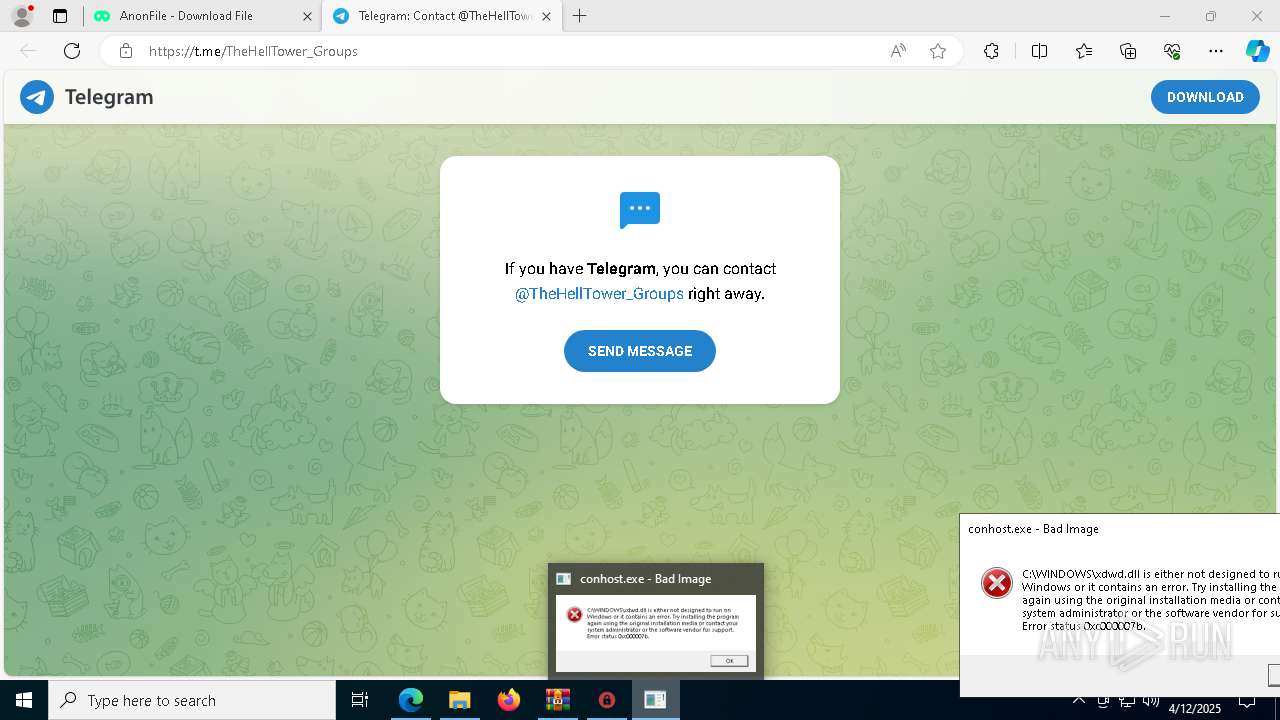
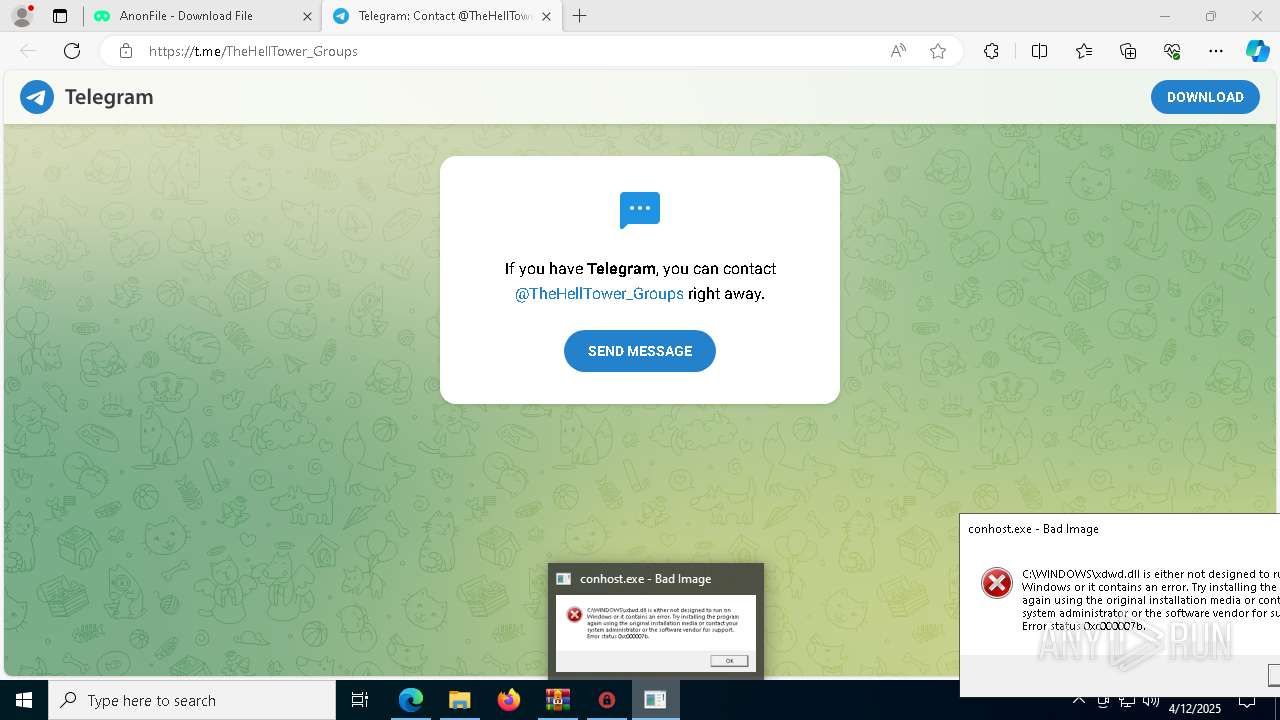
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3152 --field-trial-handle=2292,i,8675514399719005316,13037324670958746295,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | C:\Users\admin\AppData\Local\Temp\Client-THT.exe /WithTokenOf:TrustedInstaller.exe | C:\Users\admin\AppData\Local\Temp\Client-THT.exe | Client-THT.exe | ||||||||||||
User: SYSTEM Company: Avast Antivirus Upgrade Integrity Level: SYSTEM Description: IntelliJ IDEA Version: 108.43.192.43 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7376 --field-trial-handle=2292,i,8675514399719005316,13037324670958746295,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | SchTaSKs /create /f /sc minute /mo -1 /tn "XAMPP" /tr "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\xdwdGreenshot.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1424 --field-trial-handle=2292,i,8675514399719005316,13037324670958746295,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 626
Read events
17 549
Write events
64
Delete events
13
Modification events
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 716CA7FF30912F00 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 075DF0FF30912F00 | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {55145863-B83F-42B8-86C1-2996DA1063F3} | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A8502ABA-A54A-4A7A-A4DA-328BDE4AF4B4} | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {229C3536-ACB0-4755-B203-40AF2014A3F4} | |||
| (PID) Process: | (1676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {24881F1E-B141-4239-A2B1-5A9609F44481} | |||
Executable files
30
Suspicious files
576
Text files
98
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d36f.TMP | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d36f.TMP | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d37e.TMP | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d38e.TMP | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d3ad.TMP | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
85
DNS requests
86
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7216 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744956049&P2=404&P3=2&P4=mAXV%2f6PsBKnYAczNmnDe6AzTNRj%2bgj4DhCvXer7qsNj3yZdIpN13DI2uiaTzDZW1aznCWzZsp%2bTcTVL1%2b8%2fPlQ%3d%3d | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744956049&P2=404&P3=2&P4=mAXV%2f6PsBKnYAczNmnDe6AzTNRj%2bgj4DhCvXer7qsNj3yZdIpN13DI2uiaTzDZW1aznCWzZsp%2bTcTVL1%2b8%2fPlQ%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744956049&P2=404&P3=2&P4=mAXV%2f6PsBKnYAczNmnDe6AzTNRj%2bgj4DhCvXer7qsNj3yZdIpN13DI2uiaTzDZW1aznCWzZsp%2bTcTVL1%2b8%2fPlQ%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744956051&P2=404&P3=2&P4=MocDRlCAjf1LOBvziOZgYALIXSQalOPCjKzmeNA0iJ2j1Ijh0HdTkU%2bd4BU6%2fZ%2bk%2fVR%2boLUMHtFx42idzL2s6A%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744956051&P2=404&P3=2&P4=MocDRlCAjf1LOBvziOZgYALIXSQalOPCjKzmeNA0iJ2j1Ijh0HdTkU%2bd4BU6%2fZ%2bk%2fVR%2boLUMHtFx42idzL2s6A%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744956051&P2=404&P3=2&P4=MocDRlCAjf1LOBvziOZgYALIXSQalOPCjKzmeNA0iJ2j1Ijh0HdTkU%2bd4BU6%2fZ%2bk%2fVR%2boLUMHtFx42idzL2s6A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1676 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
anonfile.io |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
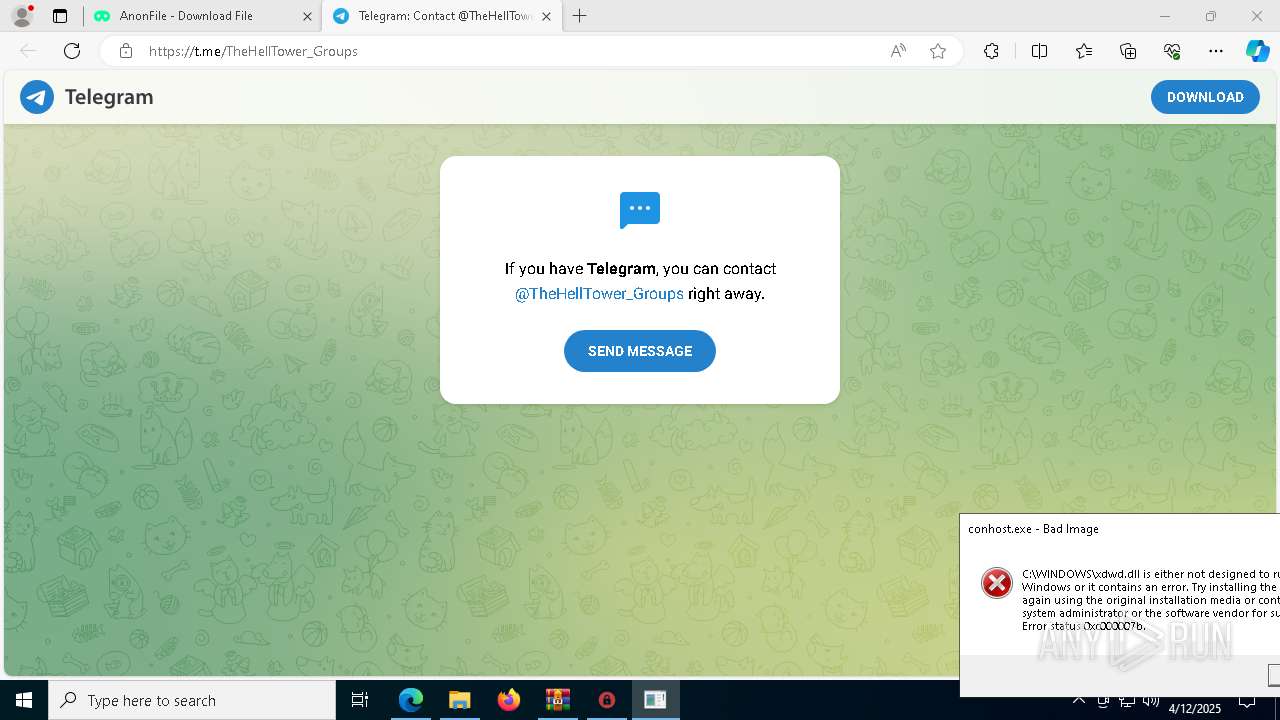
7380 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7380 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
4728 | Client-THT.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
4728 | Client-THT.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] SheetRat (Ping) |
4728 | Client-THT.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
4728 | Client-THT.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
4728 | Client-THT.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
4728 | Client-THT.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |