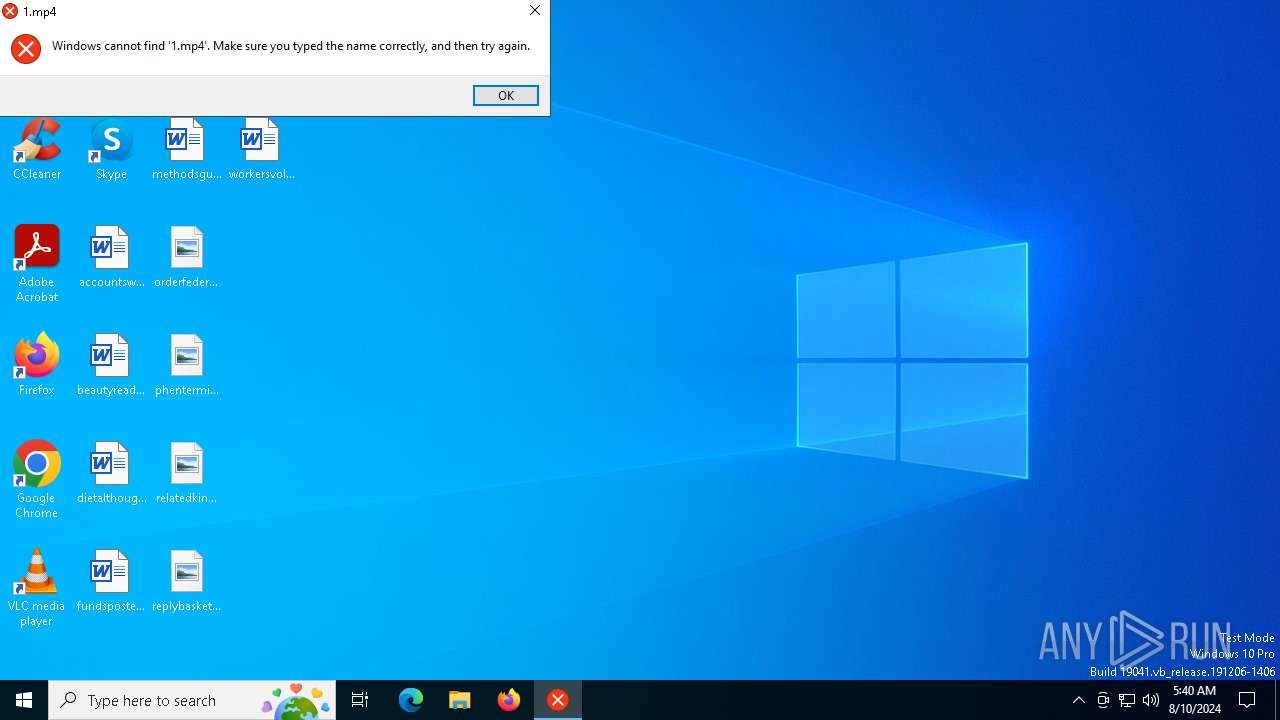
| File name: | 123.mp4.com |
| Full analysis: | https://app.any.run/tasks/43fbdc83-f46c-4c3e-b70a-110975479cde |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2024, 05:40:31 |
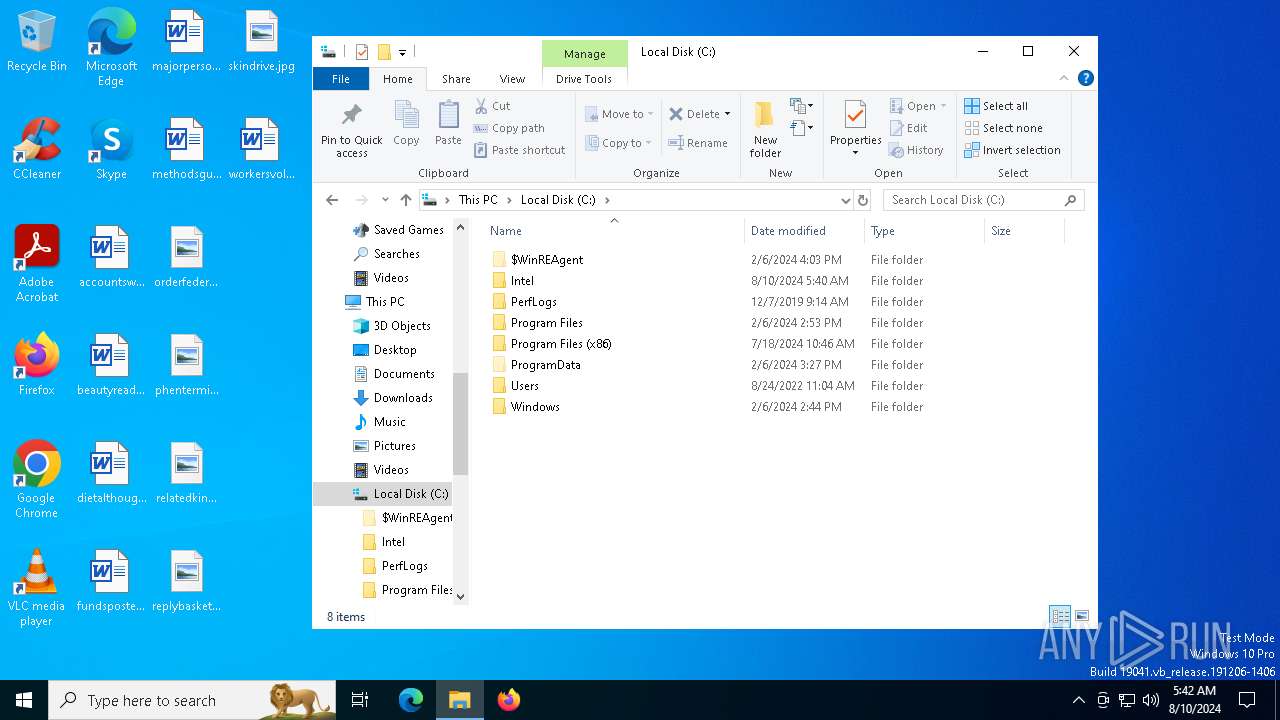
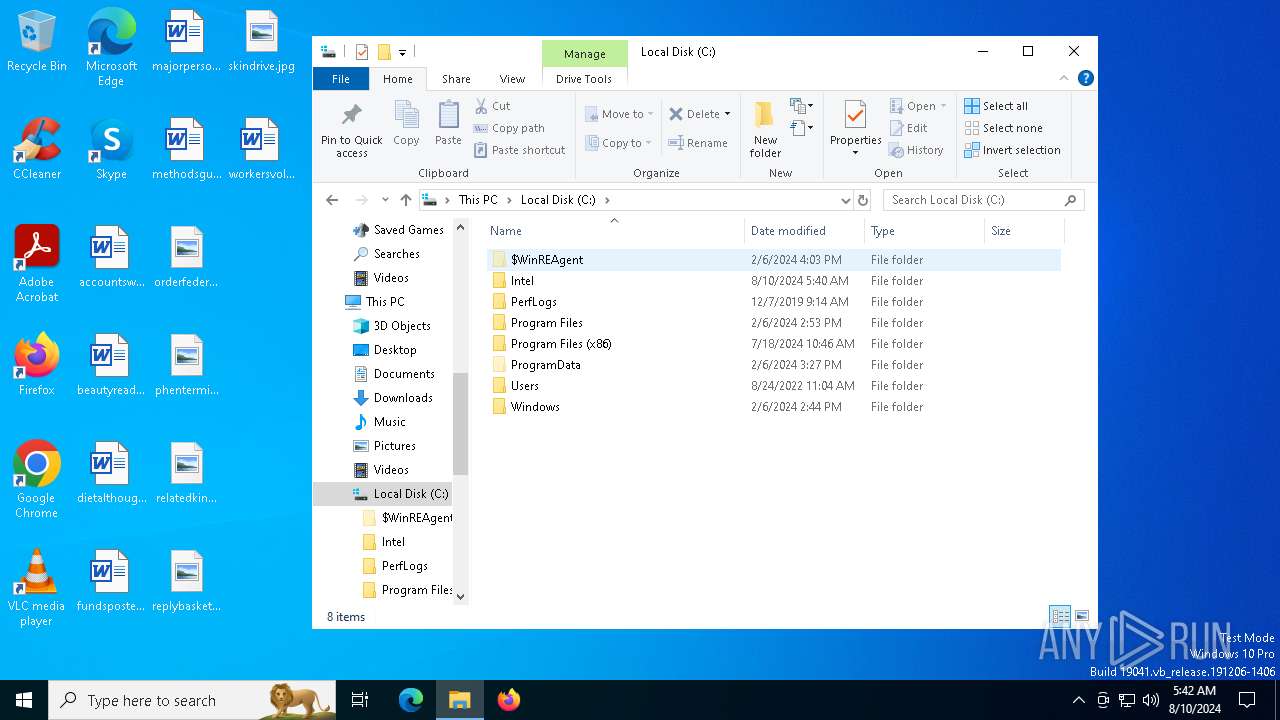
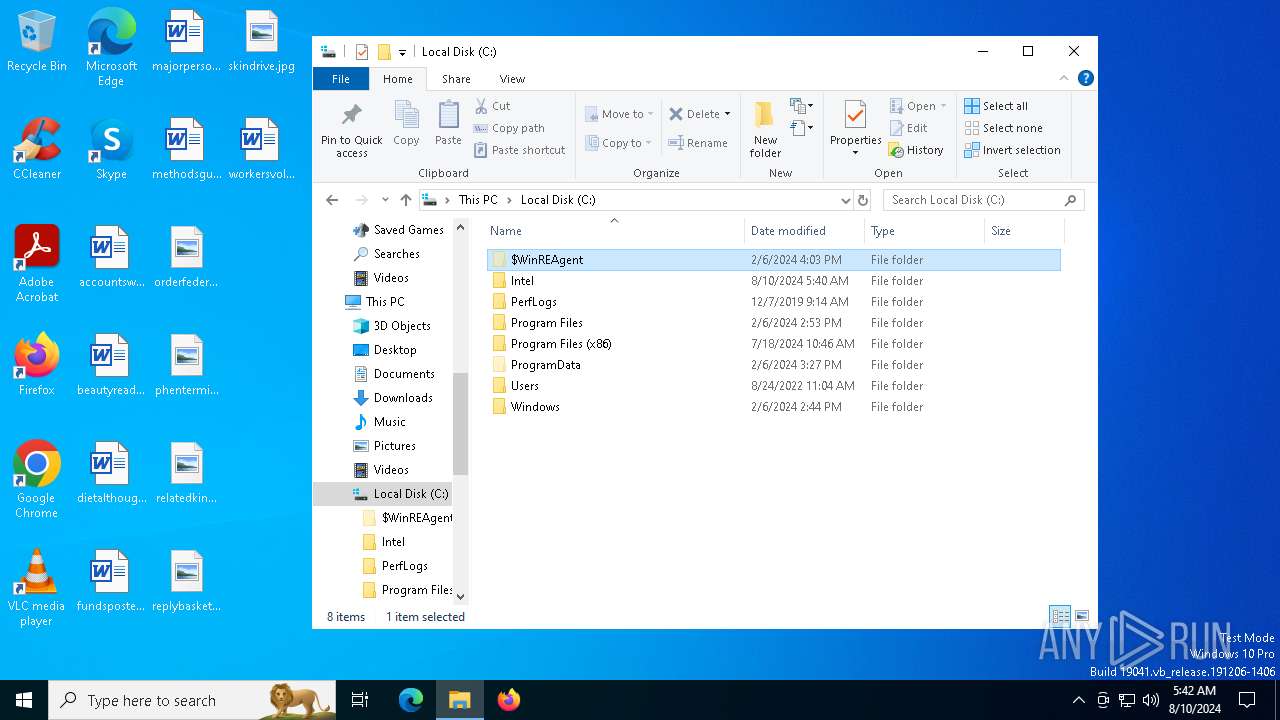
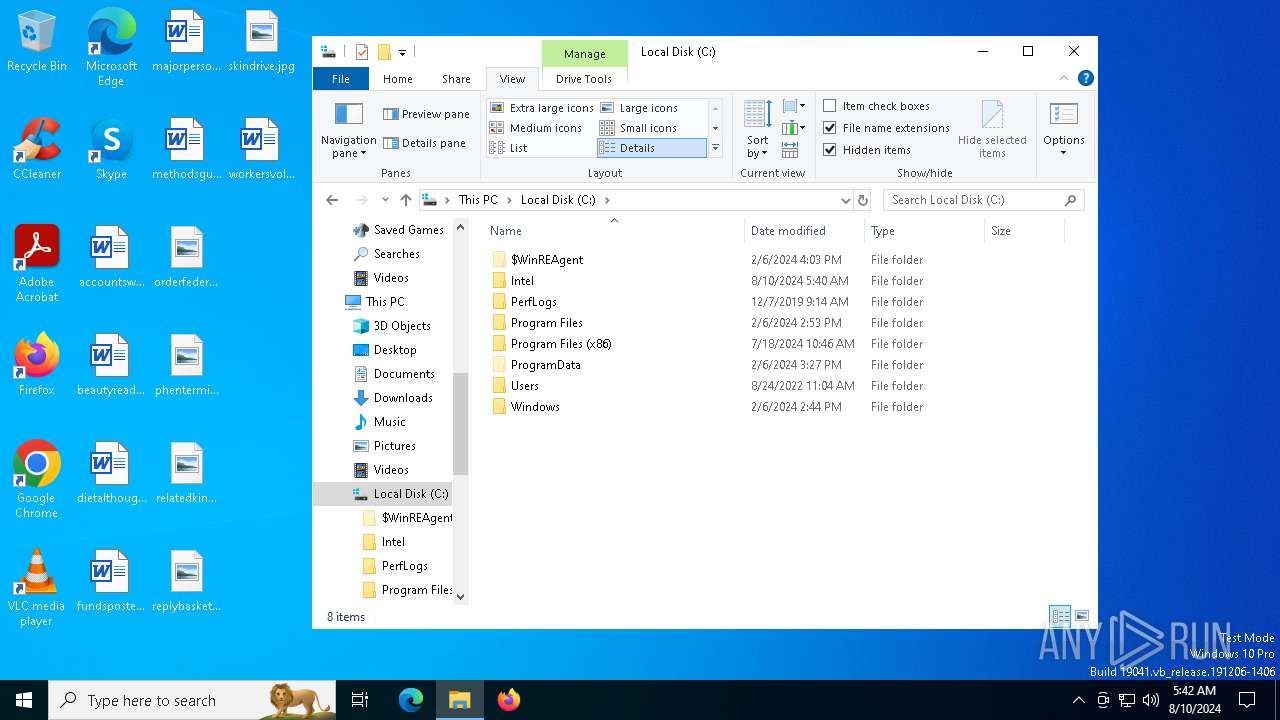
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2BA3AE37A42B8003E84FE4715EF3D4AE |
| SHA1: | A6F8DB48A9C57E1D0C10805D2F4DD28D1D21857E |
| SHA256: | 0890B13CCA1C232CD79E908AD5CC5F694E61188F37284BF4F70F0F824528DFF9 |
| SSDEEP: | 49152:0AY58PktlvGBEntOOwh+SKEjqJ2vEfs7cvP22krYv8siEEMxfhWZsFykOn1O93+U:0AY5AsPOzQOjVpf2/0sFTBhTIRnYF4Qz |
MALICIOUS
Scans artifacts that could help determine the target
- AliWifiProc.exe (PID: 6484)
SUSPICIOUS
Process drops legitimate windows executable
- 123.mp4.com.exe (PID: 6488)
The process drops C-runtime libraries
- 123.mp4.com.exe (PID: 6488)
Drops the executable file immediately after the start
- 123.mp4.com.exe (PID: 6488)
Executable content was dropped or overwritten
- 123.mp4.com.exe (PID: 6488)
- xcopy.exe (PID: 6904)
Reads the date of Windows installation
- 123.mp4.com.exe (PID: 6488)
- google.com (PID: 6576)
- MCPCBox.exe (PID: 6628)
- AliWifiProc.exe (PID: 6484)
Reads security settings of Internet Explorer
- google.com (PID: 6576)
- 123.mp4.com.exe (PID: 6488)
- MCPCBox.exe (PID: 6628)
- AliWifiProc.exe (PID: 6484)
Starts application with an unusual extension
- 123.mp4.com.exe (PID: 6488)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6748)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6748)
- cmd.exe (PID: 6388)
Executes as Windows Service
- dbfenautoupdate.exe (PID: 6408)
Starts CMD.EXE for commands execution
- AliWifiProc.exe (PID: 6484)
- MCPCBox.exe (PID: 6628)
Executing commands from a ".bat" file
- MCPCBox.exe (PID: 6628)
- AliWifiProc.exe (PID: 6484)
Creates or modifies Windows services
- AliWifiProc.exe (PID: 6484)
INFO
Reads the computer name
- 123.mp4.com.exe (PID: 6488)
- MCPCBox.exe (PID: 6628)
- google.com (PID: 6576)
- SEWanClt.exe (PID: 7116)
- AliWifiProc.exe (PID: 6484)
- dbfenautoupdate.exe (PID: 6408)
- vlc.exe (PID: 4604)
Checks supported languages
- 123.mp4.com.exe (PID: 6488)
- MCPCBox.exe (PID: 6628)
- google.com (PID: 6576)
- AliWifiProc.exe (PID: 6484)
- SEWanClt.exe (PID: 7116)
- dbfenautoupdate.exe (PID: 6408)
- vlc.exe (PID: 4604)
Process checks computer location settings
- google.com (PID: 6576)
- 123.mp4.com.exe (PID: 6488)
- MCPCBox.exe (PID: 6628)
- AliWifiProc.exe (PID: 6484)
Checks proxy server information
- AliWifiProc.exe (PID: 6484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 111104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
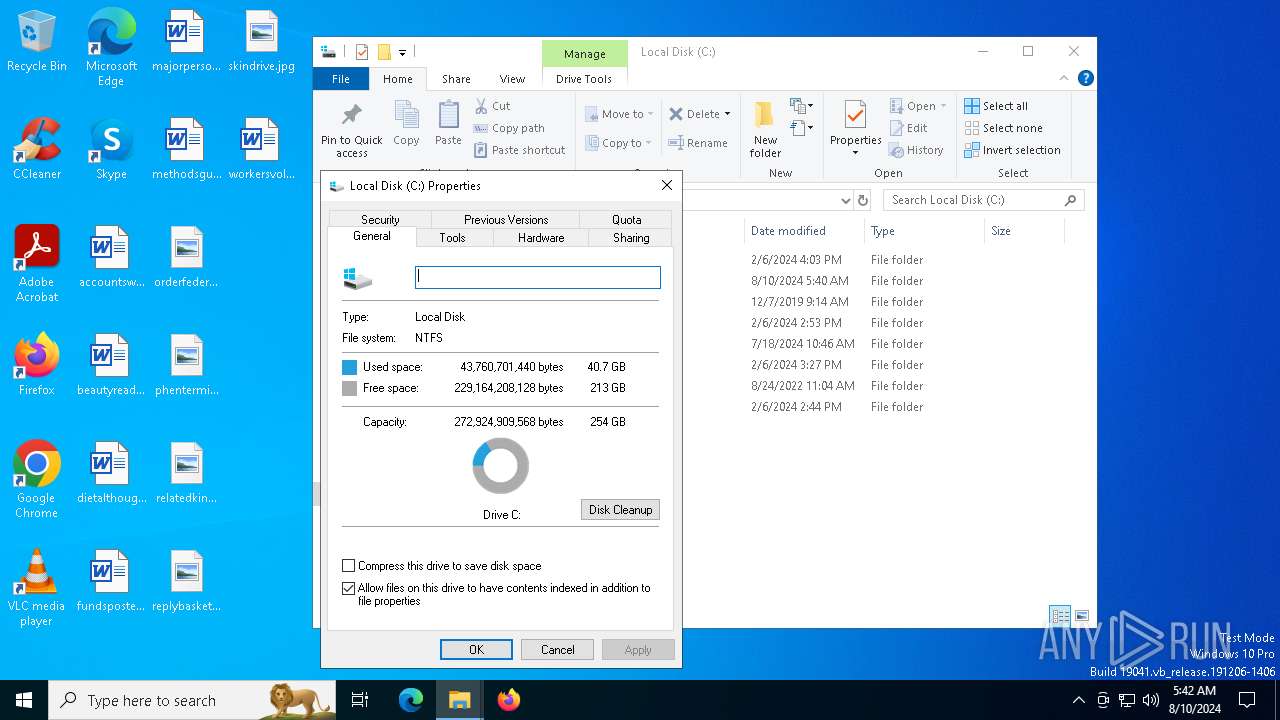
Total processes
157
Monitored processes
23
Malicious processes
1
Suspicious processes
4
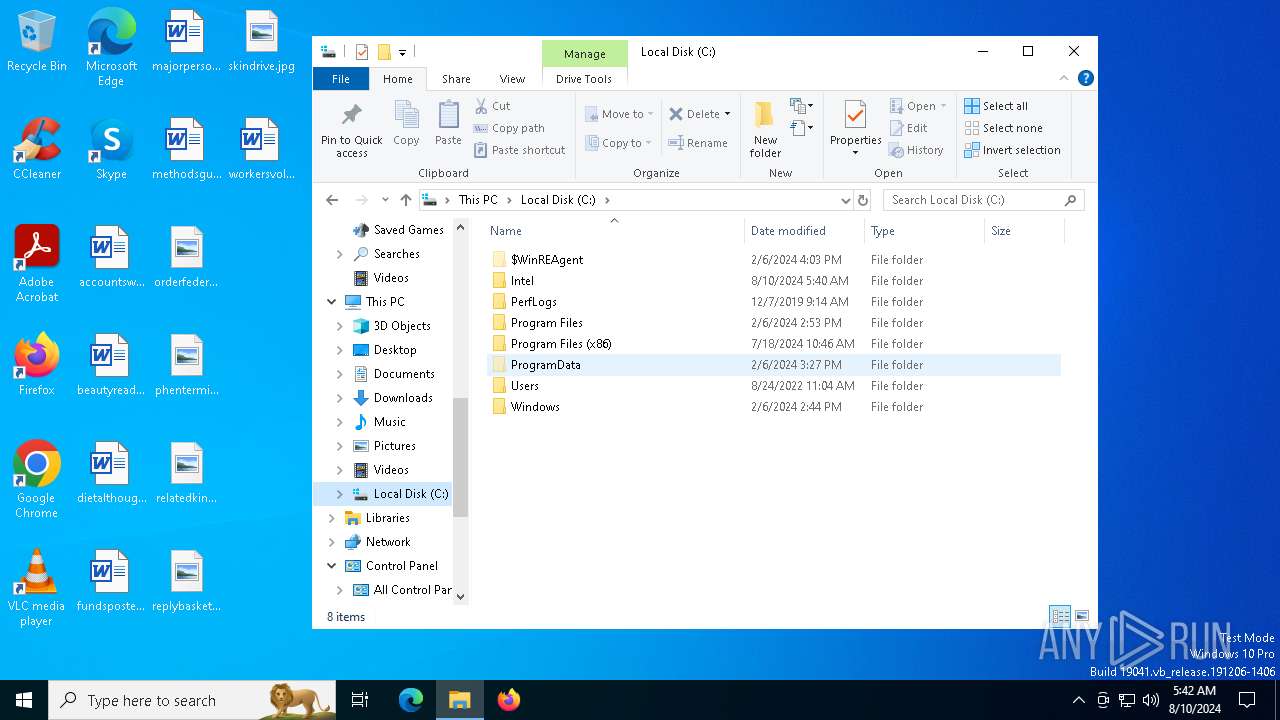
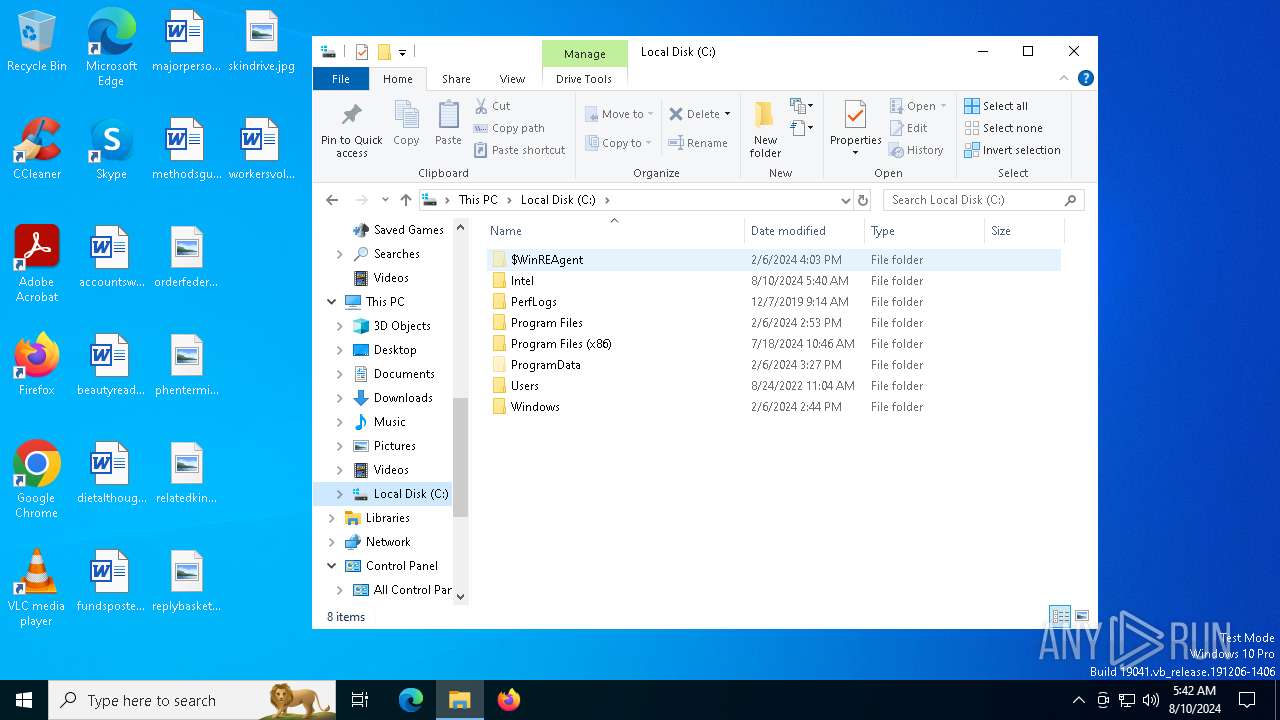
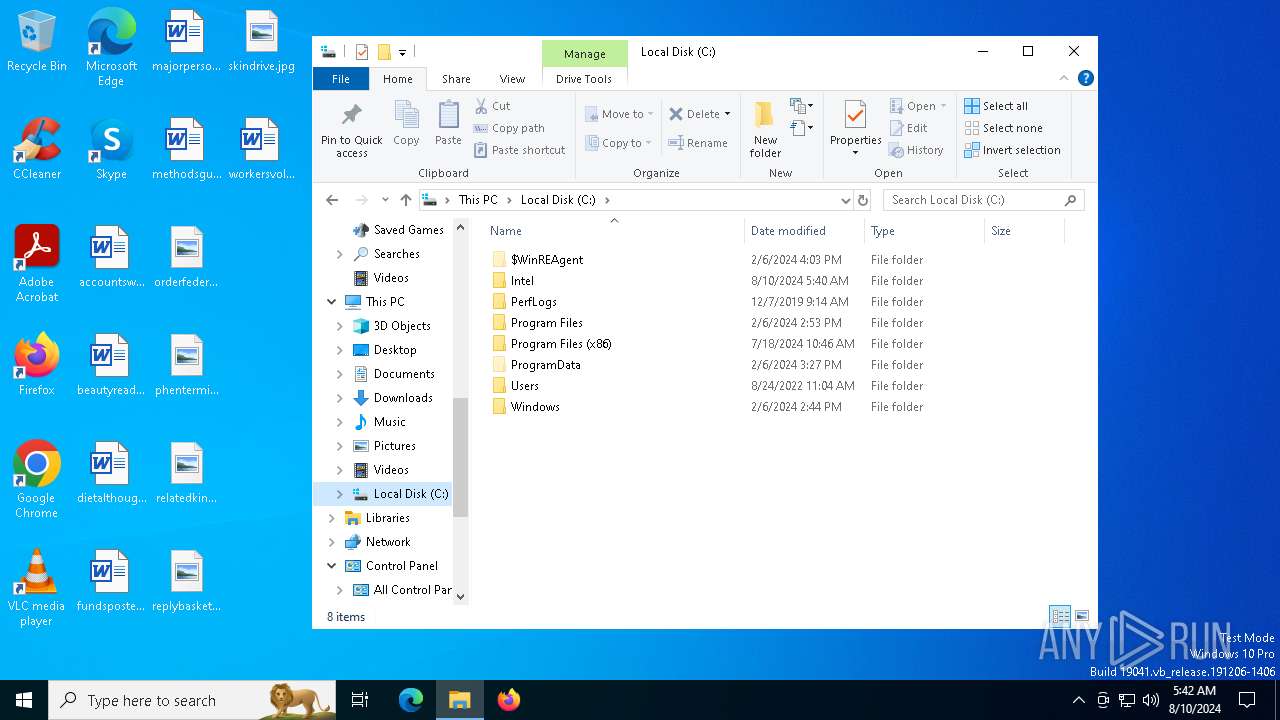
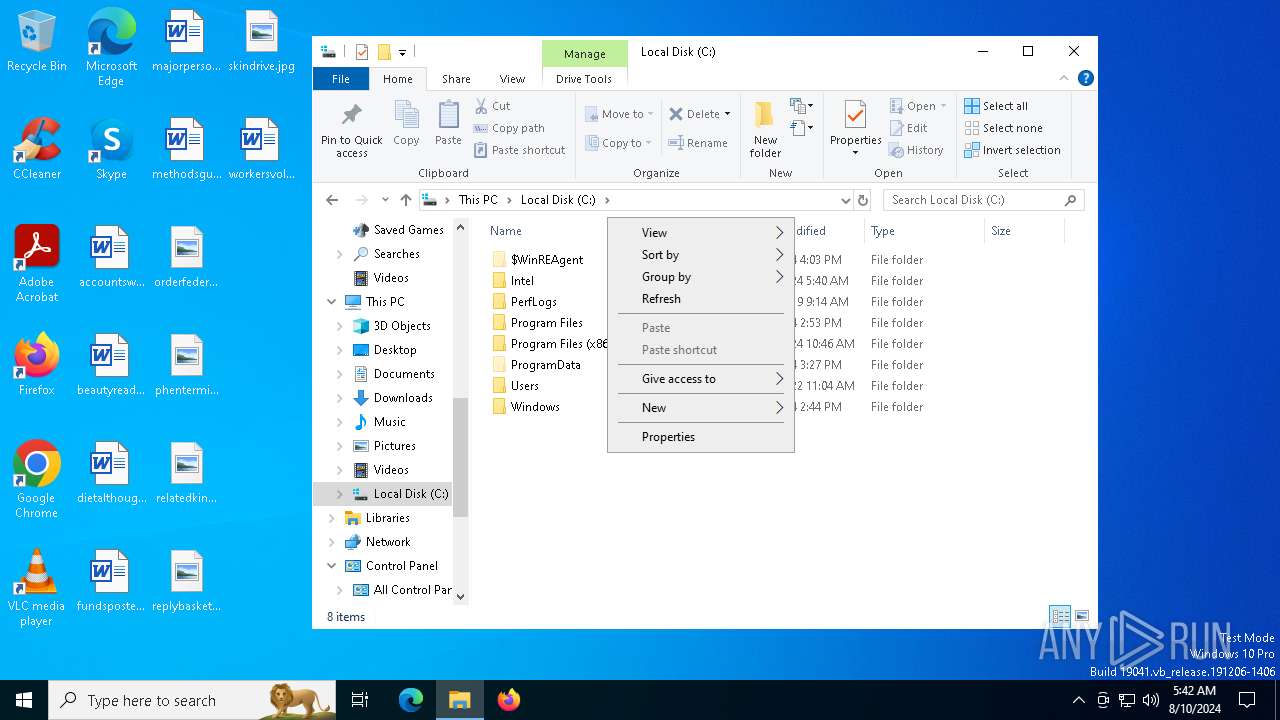
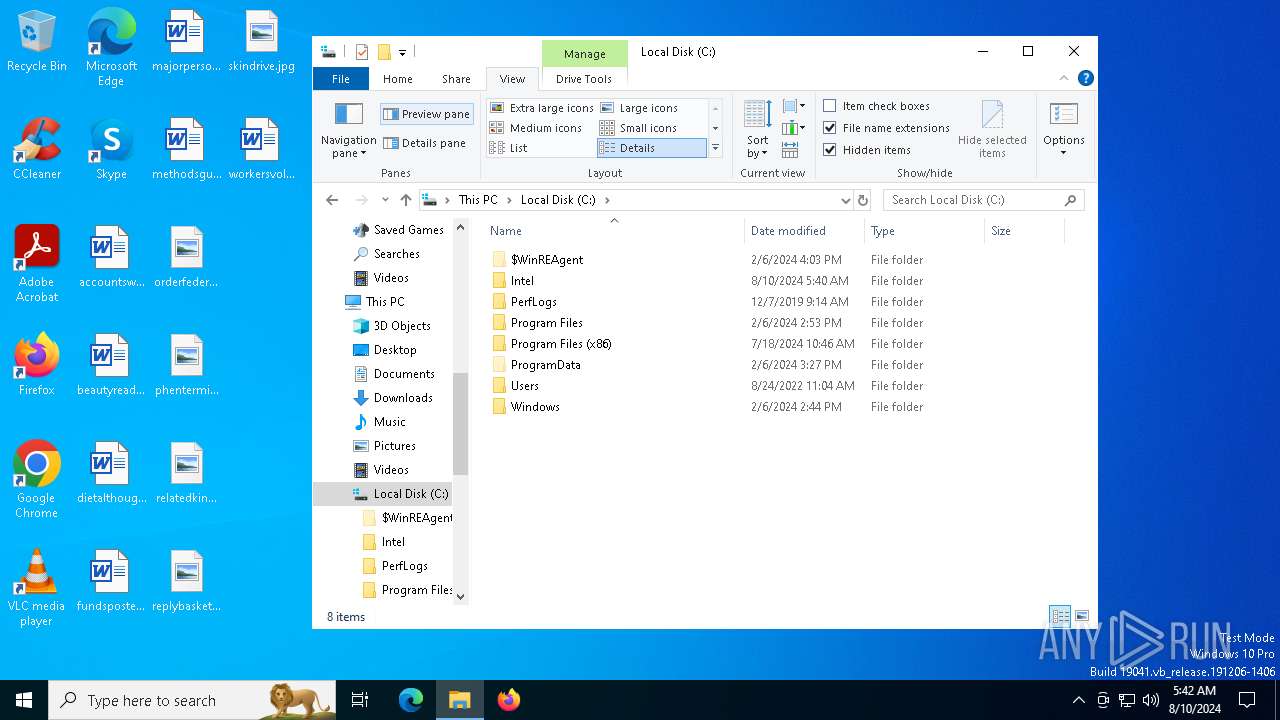
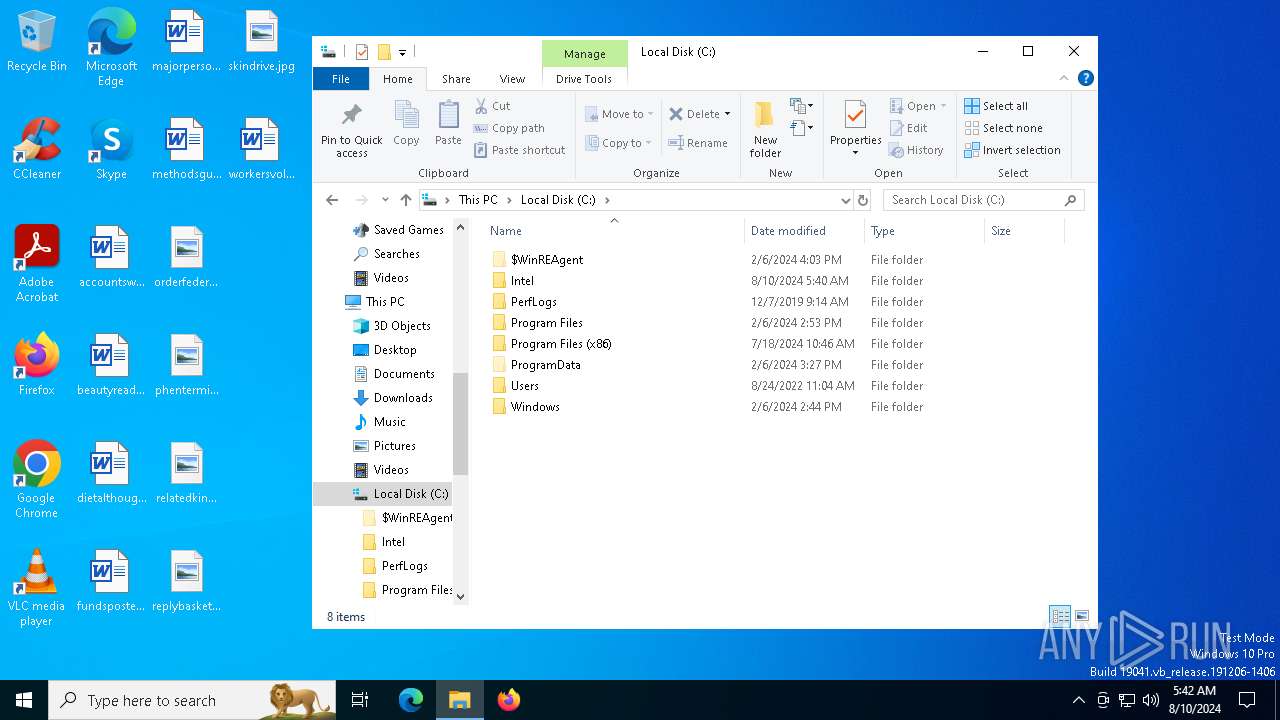
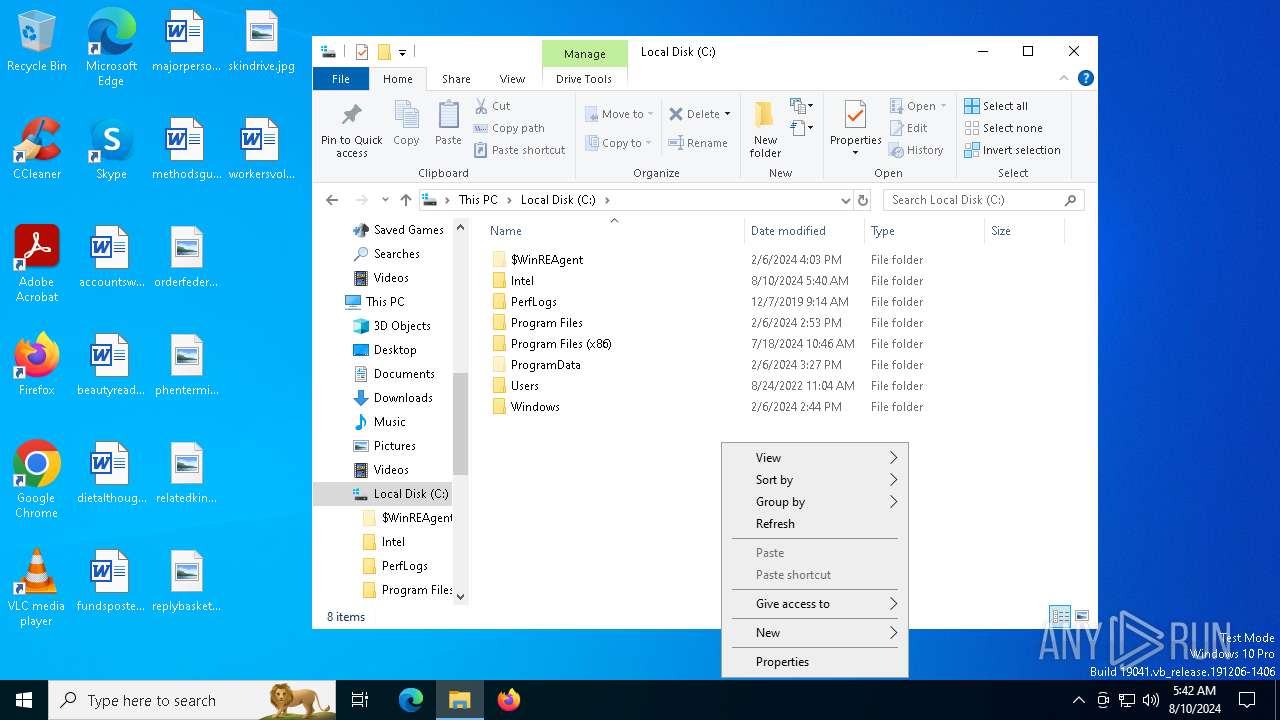
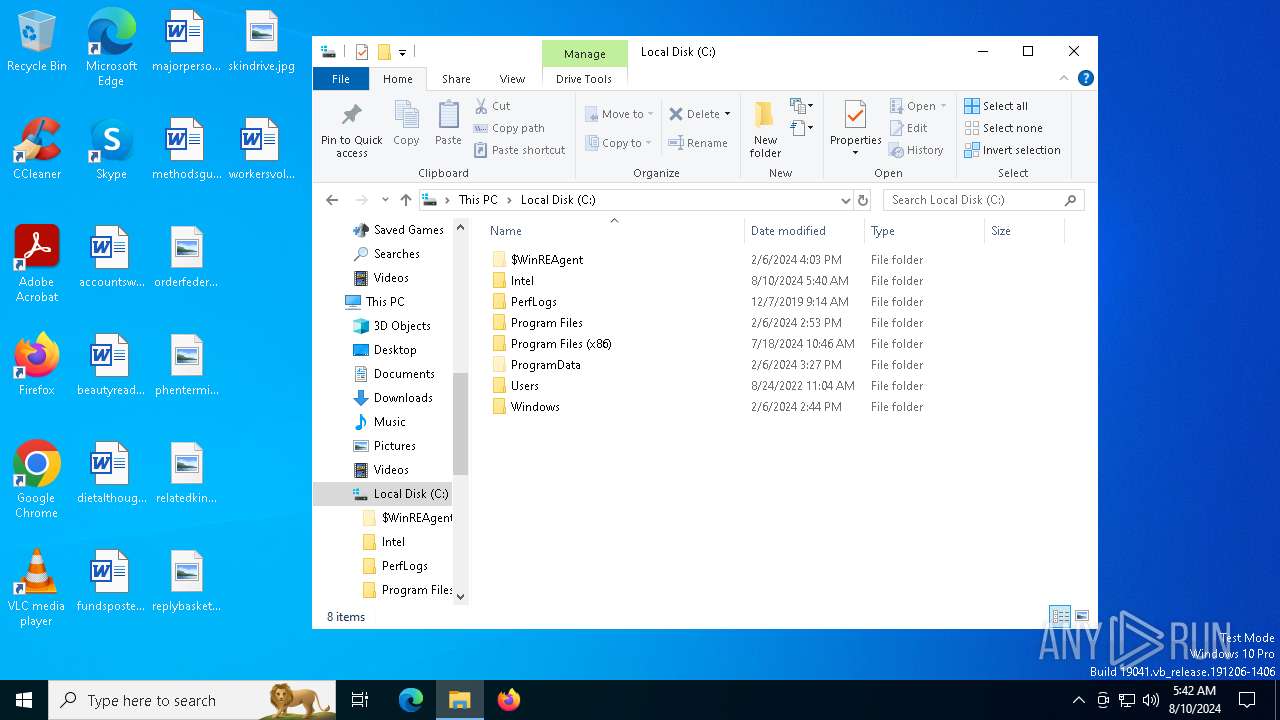
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | attrib -h "C:\WanSync\Client\RC.bat" | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | attrib +s +a +h +r C:\WanSync | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
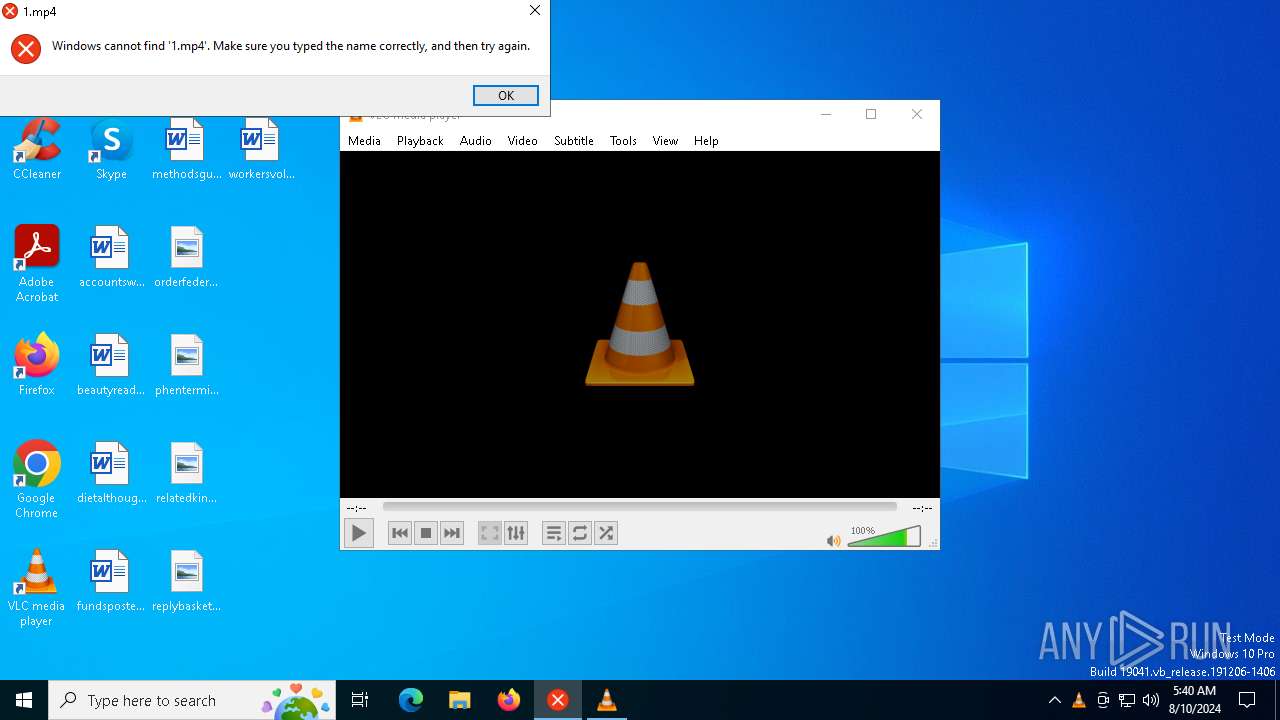
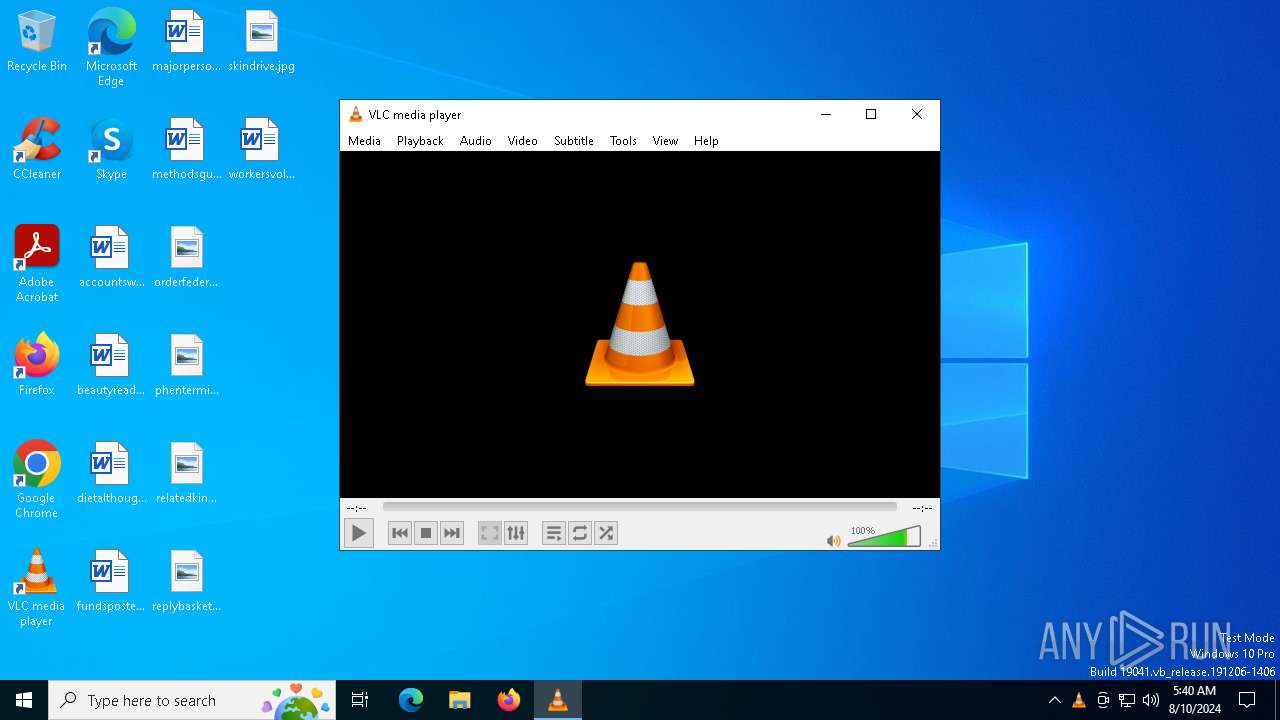
| 4604 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\WanSync\Client\yy.mp4" | C:\Program Files\VideoLAN\VLC\vlc.exe | cmd.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
| 5484 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\cmd.exe /c ""C:\WanSync\Client\RC.bat" " | C:\Windows\SysWOW64\cmd.exe | — | AliWifiProc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
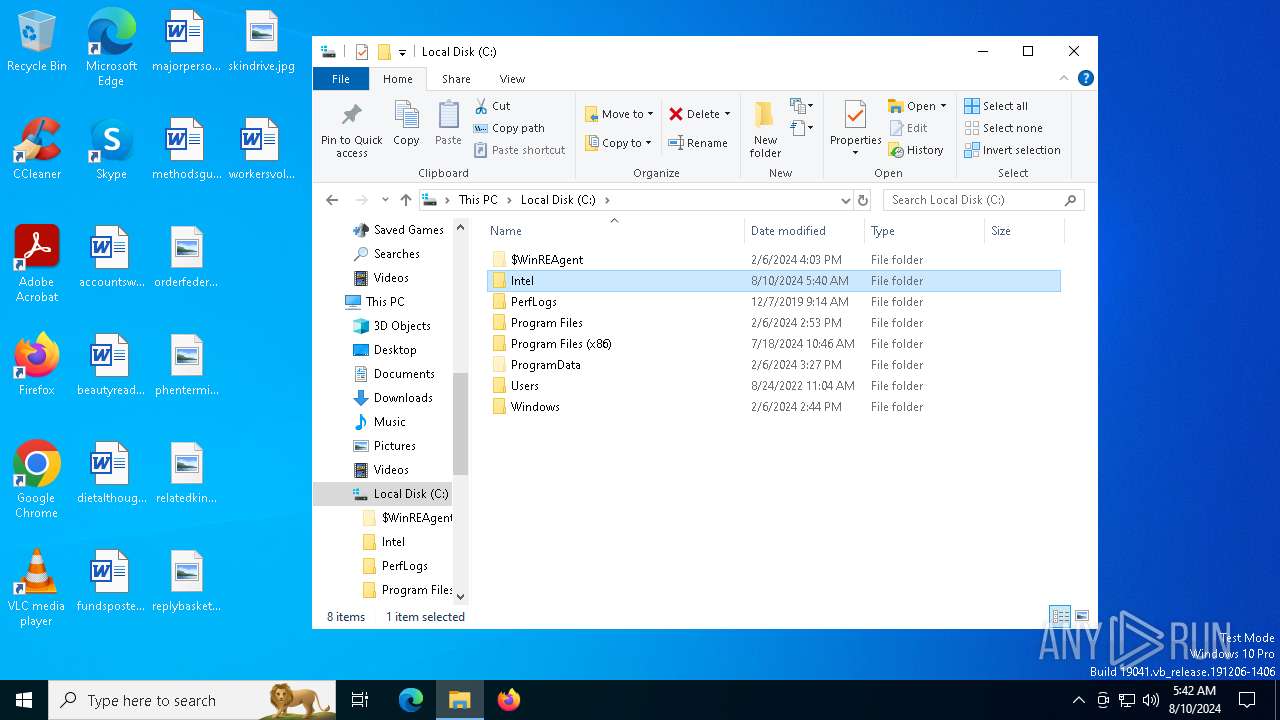
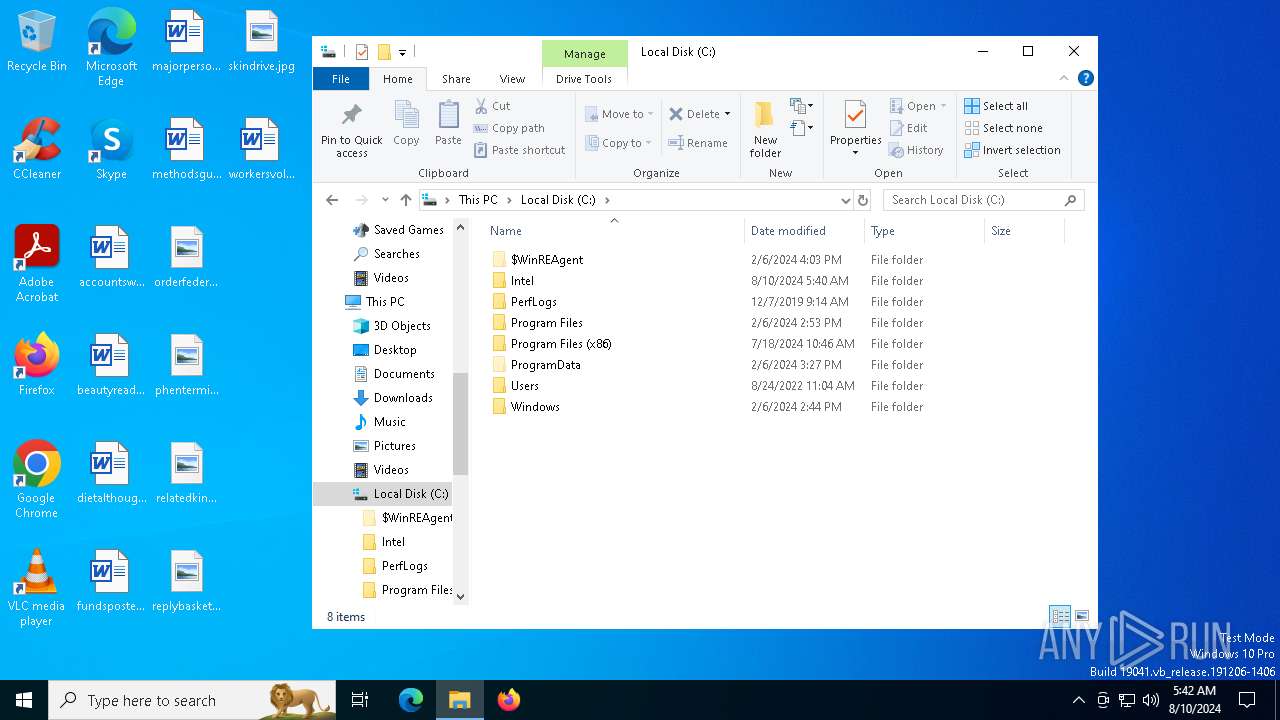
| 6408 | "C:\WanSync\Client\dbfenautoupdate.exe" | C:\WanSync\Client\dbfenautoupdate.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: AliWifiService Application Version: 1,0,1,179 Modules
| |||||||||||||||
| 6484 | "C:\WanSync\Client\AliWifiProc.exe" | C:\WanSync\Client\AliWifiProc.exe | dbfenautoupdate.exe | ||||||||||||
User: admin Company: MyDrivers Integrity Level: HIGH Description: 软件精灵轻量核心服务,提供软件升级提醒功能 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 6488 | "C:\Users\admin\AppData\Local\Temp\123.mp4.com.exe" | C:\Users\admin\AppData\Local\Temp\123.mp4.com.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
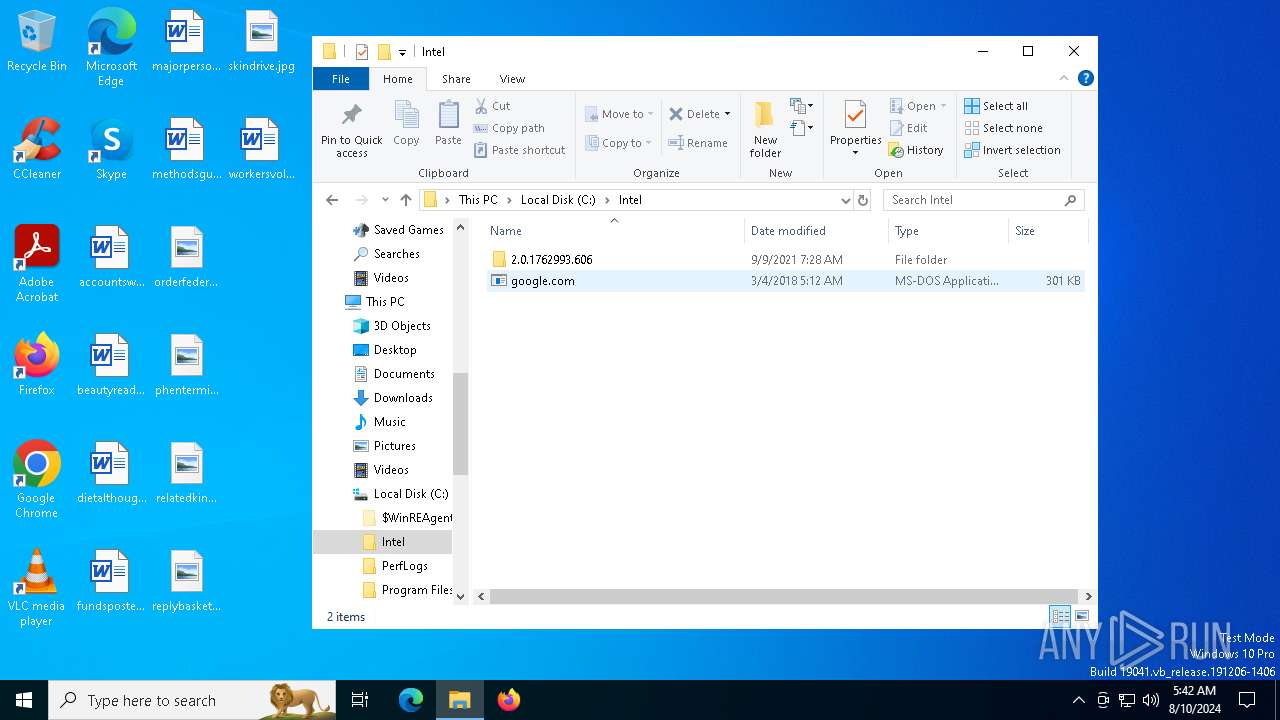
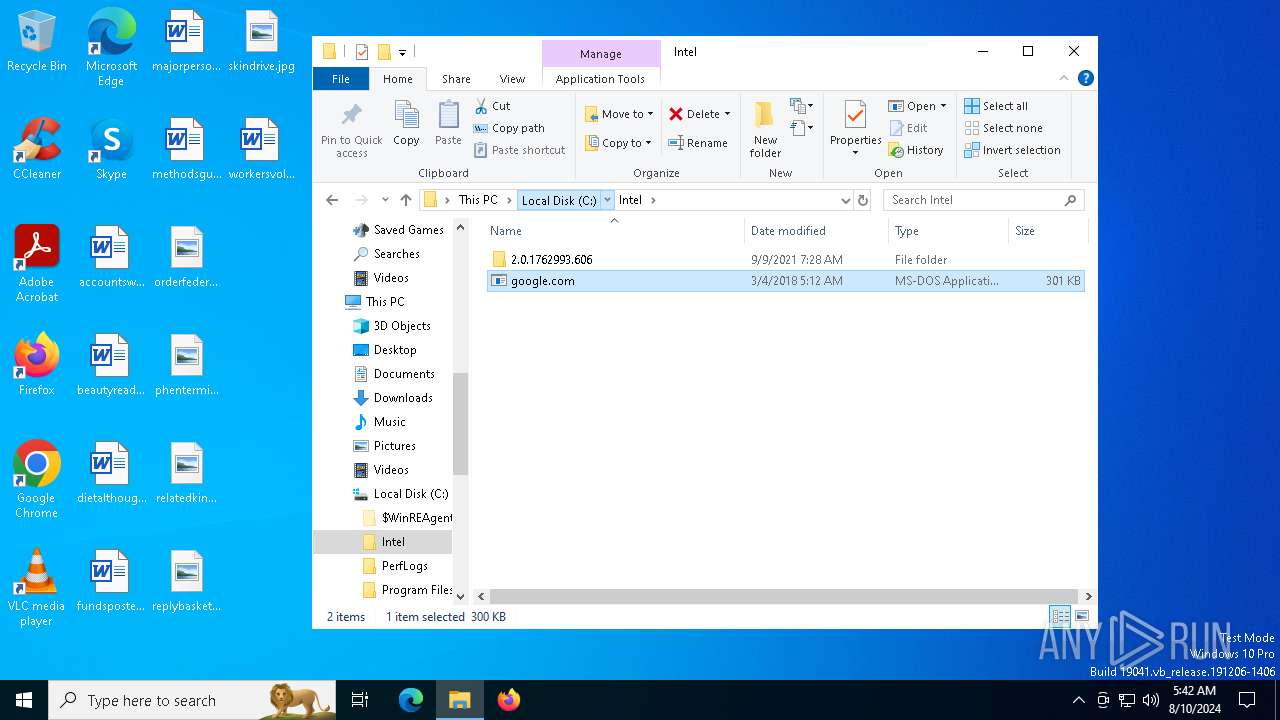
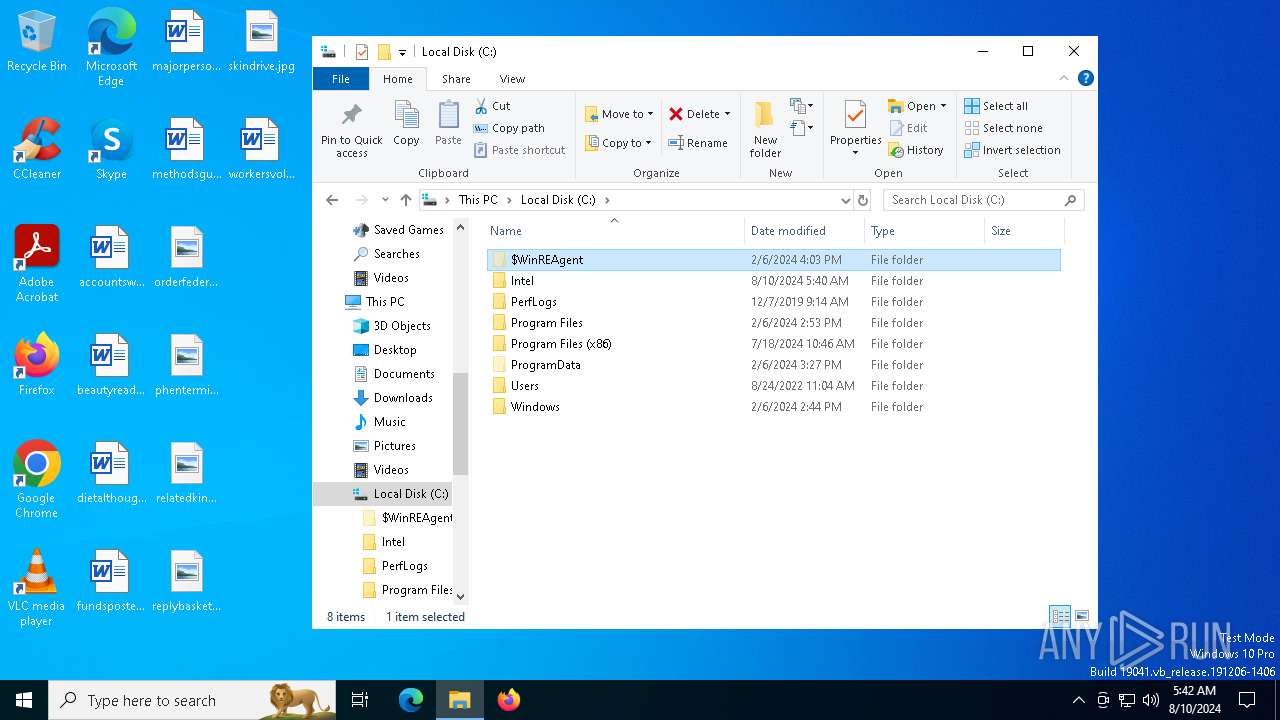
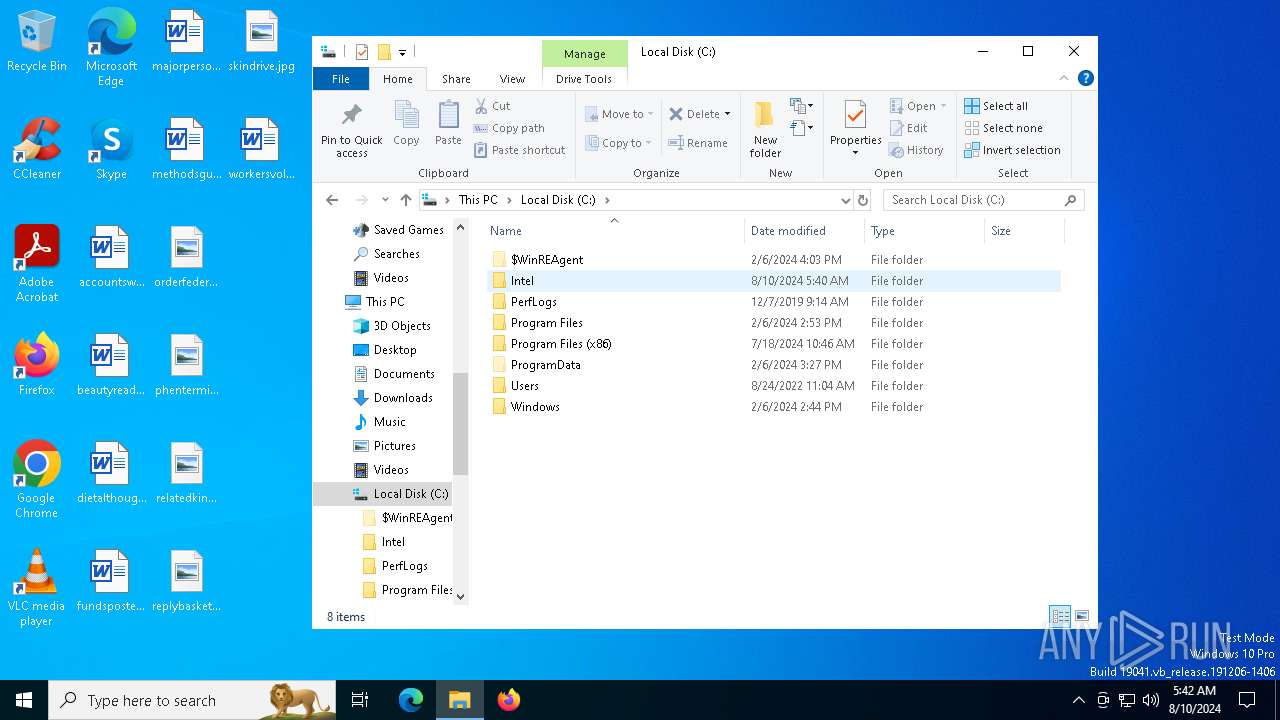
| 6576 | "C:\Intel\google.com" | C:\Intel\google.com | — | 123.mp4.com.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MCPCBox Exit code: 0 Version: 2017.08.31.606 Modules
| |||||||||||||||
Total events
9 274
Read events
9 217
Write events
57
Delete events
0
Modification events
| (PID) Process: | (6488) 123.mp4.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6488) 123.mp4.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6488) 123.mp4.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6488) 123.mp4.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6488) 123.mp4.com.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ndfapi.dll,-40001 |
Value: Windows Network Diagnostics | |||
| (PID) Process: | (6576) google.com | Key: | HKEY_CLASSES_ROOT\mcpcbox |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (6576) google.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6576) google.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6576) google.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6576) google.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
14
Suspicious files
3
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
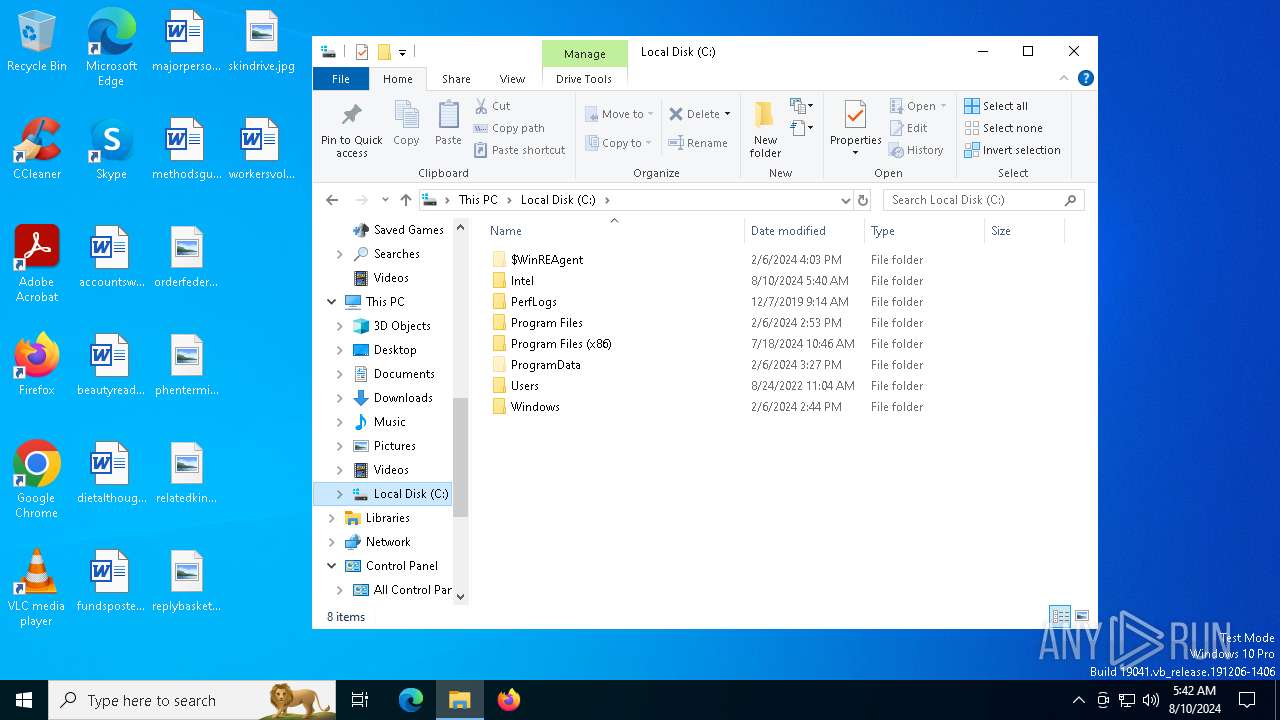
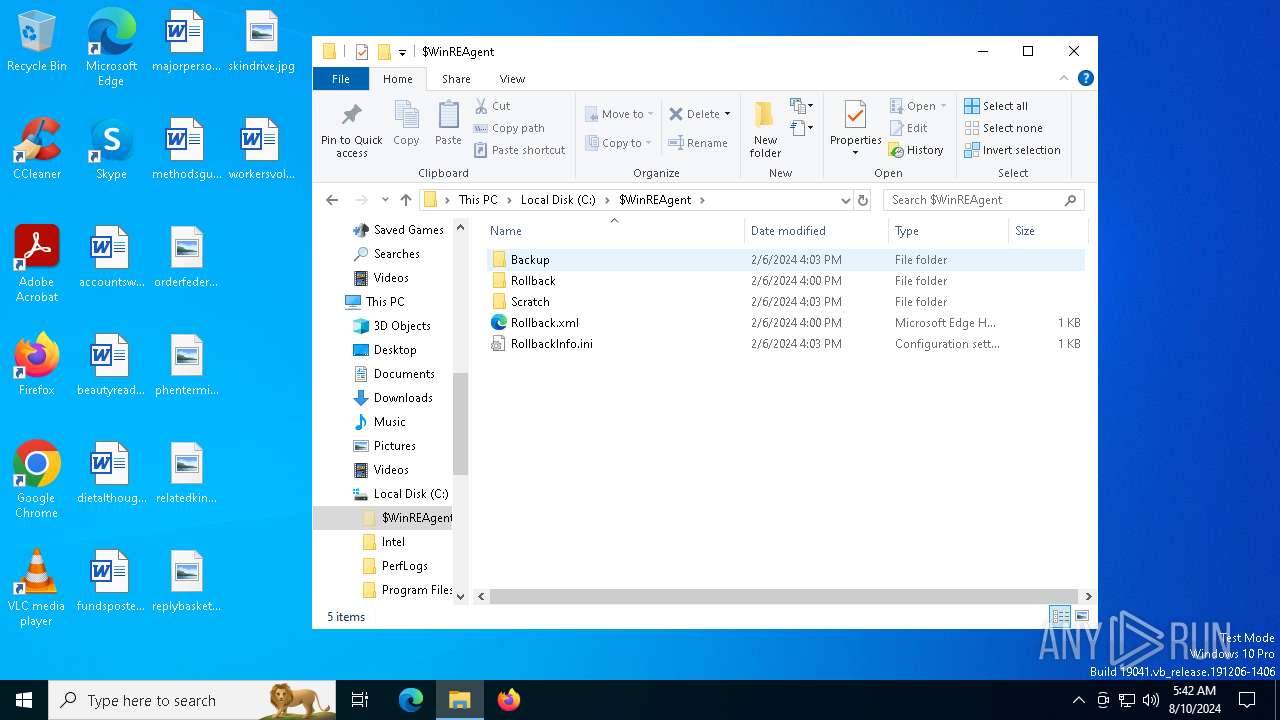
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\Client\SEWanClt.exe | executable | |
MD5:25A454C925DEA42A5525932F67088558 | SHA256:E2D34959A9CF0923361ED527ABDE5582A788CBB424DD7ACEBD6362624030C9EC | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\Client\RC.bat | text | |
MD5:844964C360C87BA5BEF984F32B1C268D | SHA256:6FBD9AAED70A4C66EC1D7CCC25E7C1414E5870DD9E2C84C9E871E40F69158B20 | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\au.log | text | |
MD5:A1A5C1B8879C9C8D4C5507BC3AE6A72B | SHA256:9D54F5B7B8B722D82518B1F3112F78E89EF0B4087CB5BDFBC2B2DB08307F886E | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\msvcr100.dll | executable | |
MD5:0E37FBFA79D349D672456923EC5FBBE3 | SHA256:8793353461826FBD48F25EA8B835BE204B758CE7510DB2AF631B28850355BD18 | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\Client\dbfenautoupdate.exe | executable | |
MD5:C02C6DDB0745307C5E2D26D584382B63 | SHA256:543B2B12228940F5D0FEFDD8B372126A213B3D36FC0B5A642582FEAEF6E46CFF | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\luancher.ico | text | |
MD5:B9D7476191569B1A335A7CF62BD28B28 | SHA256:DB3435D01D647CAE27821F397D4315215BDE18E70BFCEE2D07E60EE068DD9B8A | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\luancher.bat | text | |
MD5:B9D7476191569B1A335A7CF62BD28B28 | SHA256:DB3435D01D647CAE27821F397D4315215BDE18E70BFCEE2D07E60EE068DD9B8A | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\Client\AliWifiProc.exe | executable | |
MD5:3AAD16CB92612770FB63F461625CF2BC | SHA256:2AF90B11C775842FAAAB2F7DDA49D2C1D41B32D965115A08858E3E53C583997A | |||
| 4604 | vlc.exe | — | ||
MD5:— | SHA256:— | |||
| 6488 | 123.mp4.com.exe | C:\Intel\2.0.1762993.606\Client\SoftBase.dll | executable | |
MD5:EA4E57B66FD51E85385EB87552493B00 | SHA256:49C25089CA589D10E5A397C1283FF2BE952F9EF8F141395B59B2E30BD886CCBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
42
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5140 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6732 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6484 | AliWifiProc.exe | GET | 302 | 43.129.2.81:80 | http://users.qzone.qq.com/fcg-bin/cgi_get_portrait.fcg?uins=?M7~QQ#:1746473722 | unknown | — | — | whitelisted |
6484 | AliWifiProc.exe | GET | 302 | 43.129.2.81:80 | http://users.qzone.qq.com/fcg-bin/cgi_get_portrait.fcg?uins=?M7~QQ#:1746473722 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3980 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5140 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
minsnia.com |
| unknown |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|