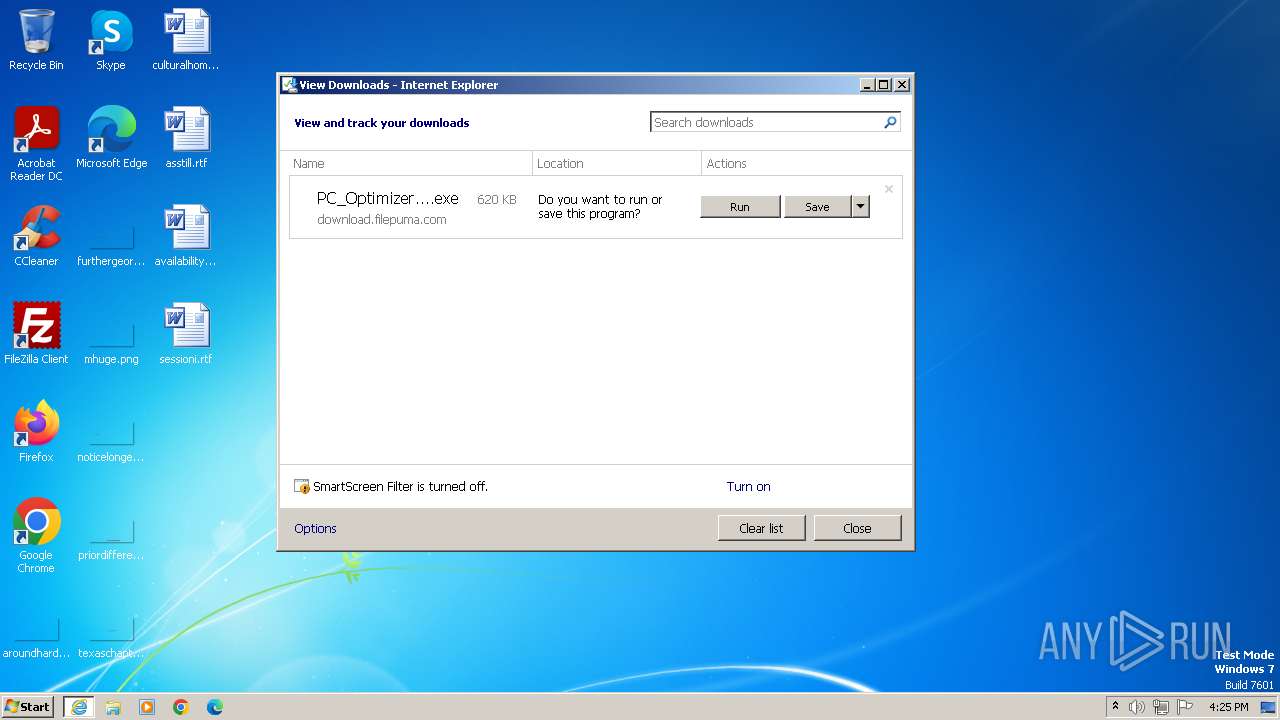
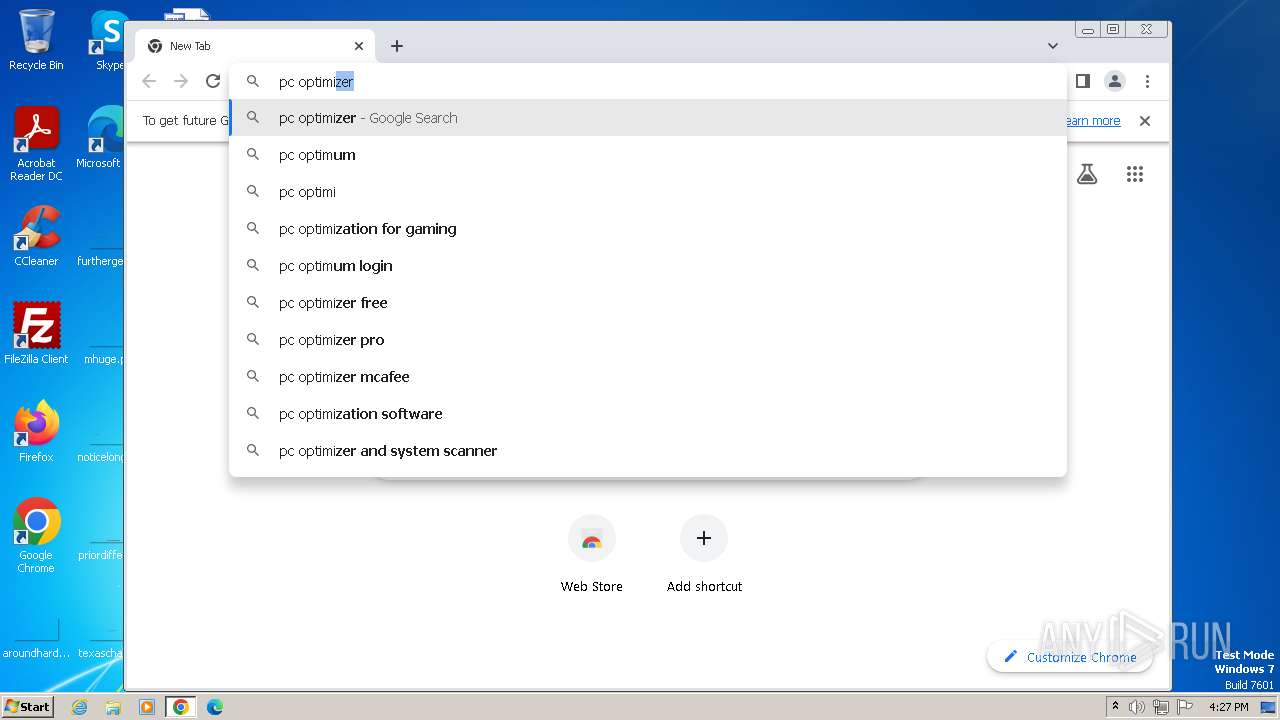
| URL: | https://download.filepuma.com/files/utilities/pc-optimizer-pro/PC_Optimizer_Pro_v7.0.7.1.exe |
| Full analysis: | https://app.any.run/tasks/1be0a43a-bde8-485d-80ec-93745371bde2 |
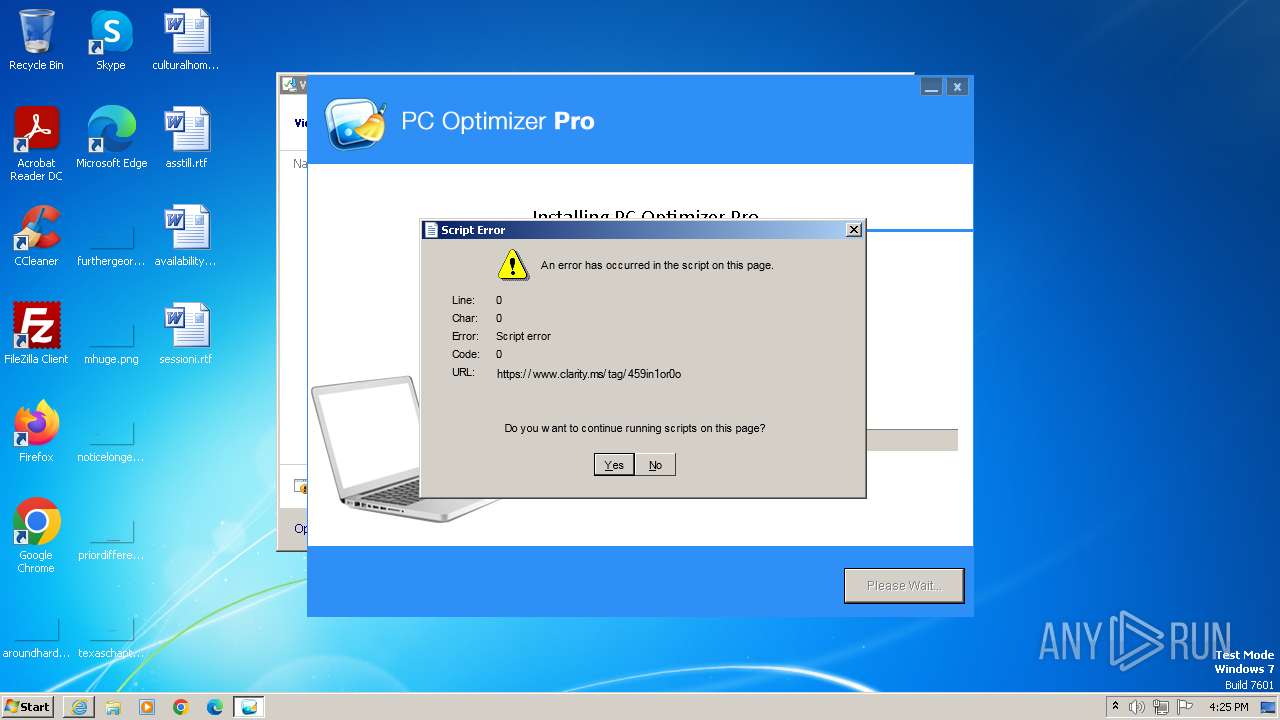
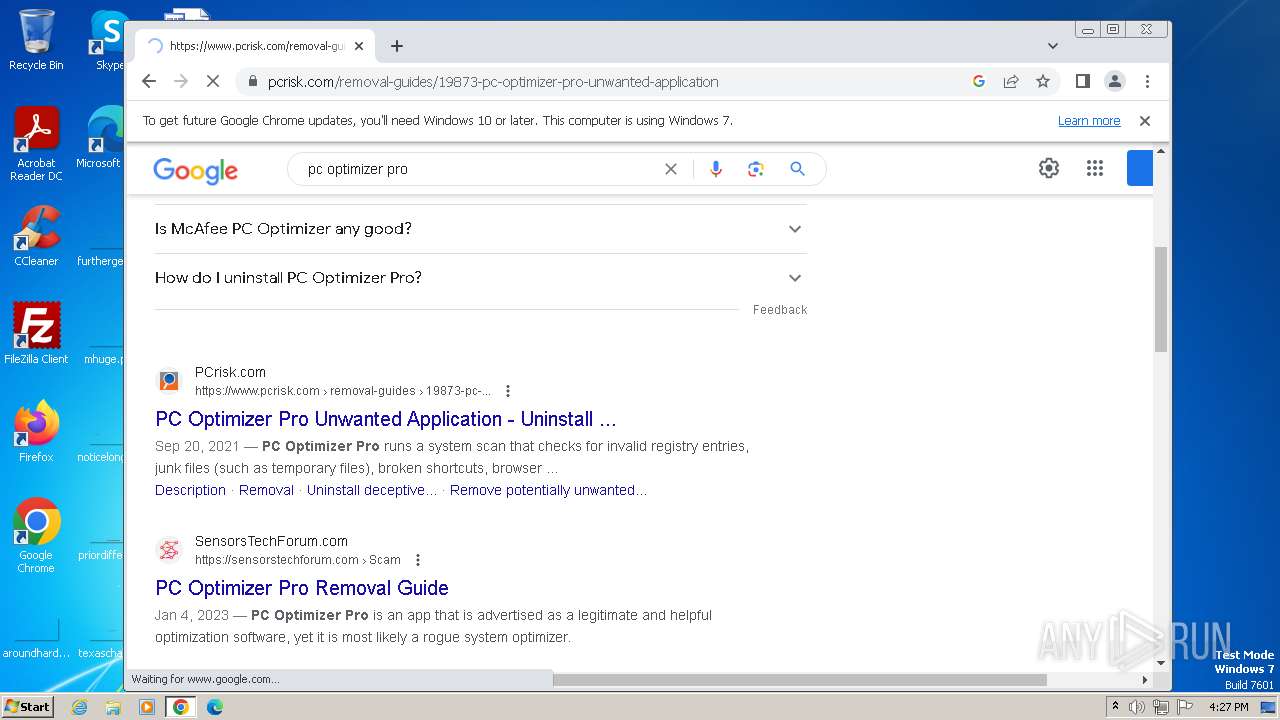
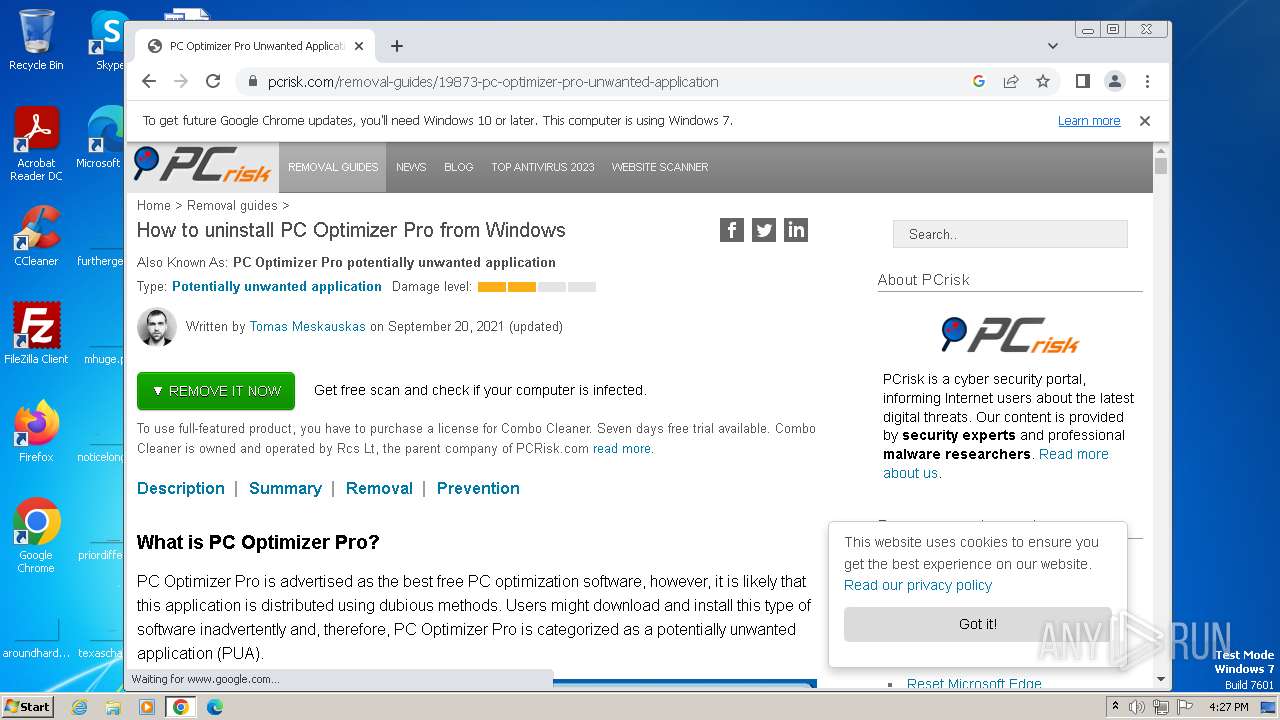
| Verdict: | Malicious activity |
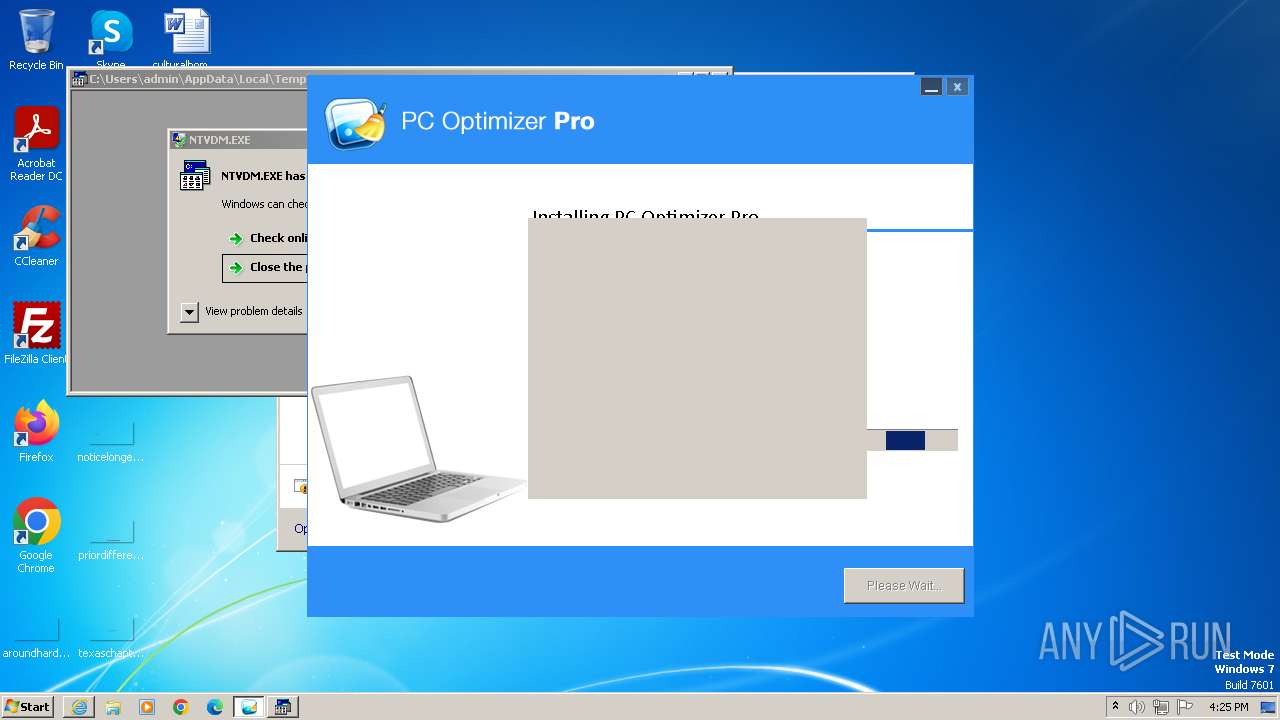
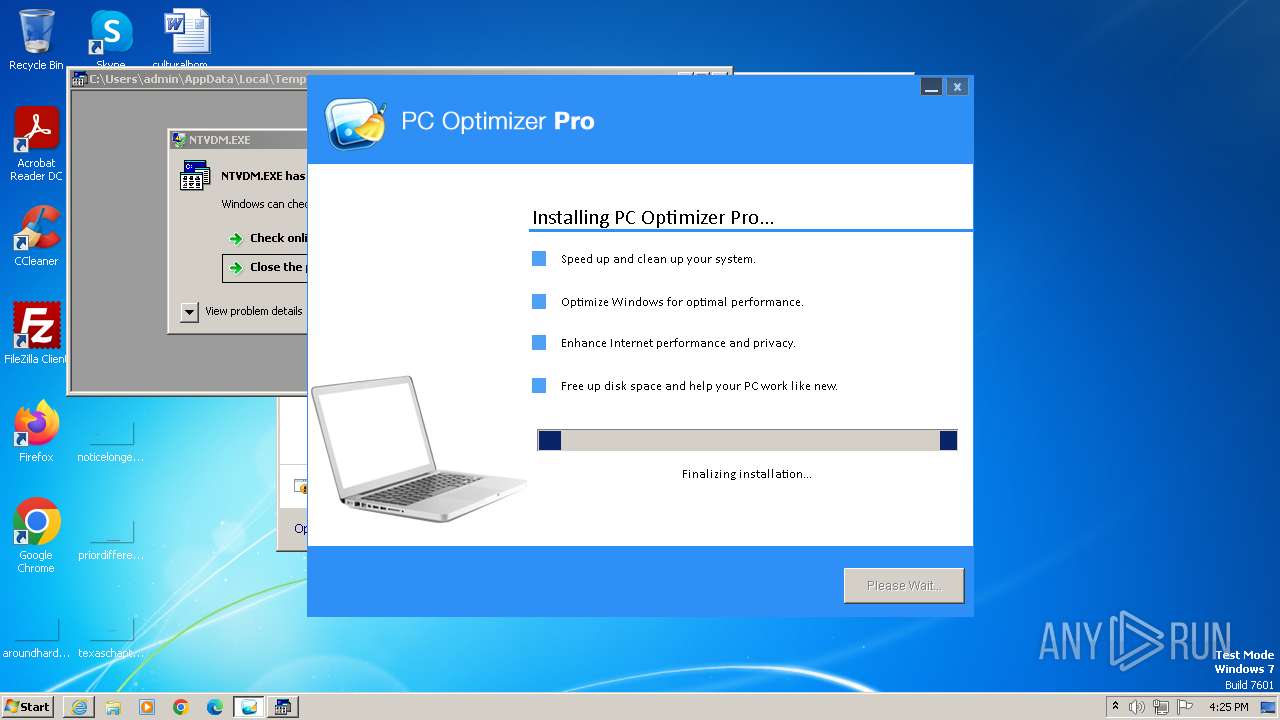
| Analysis date: | October 24, 2023, 15:25:08 |
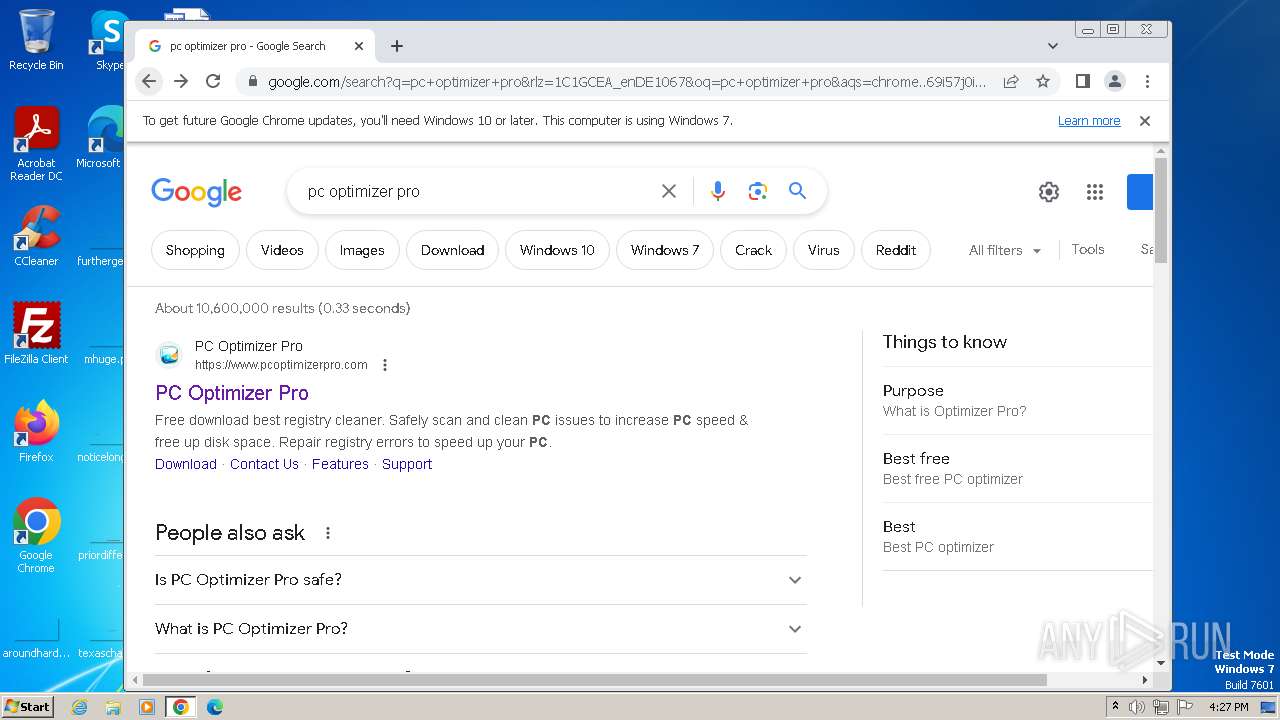
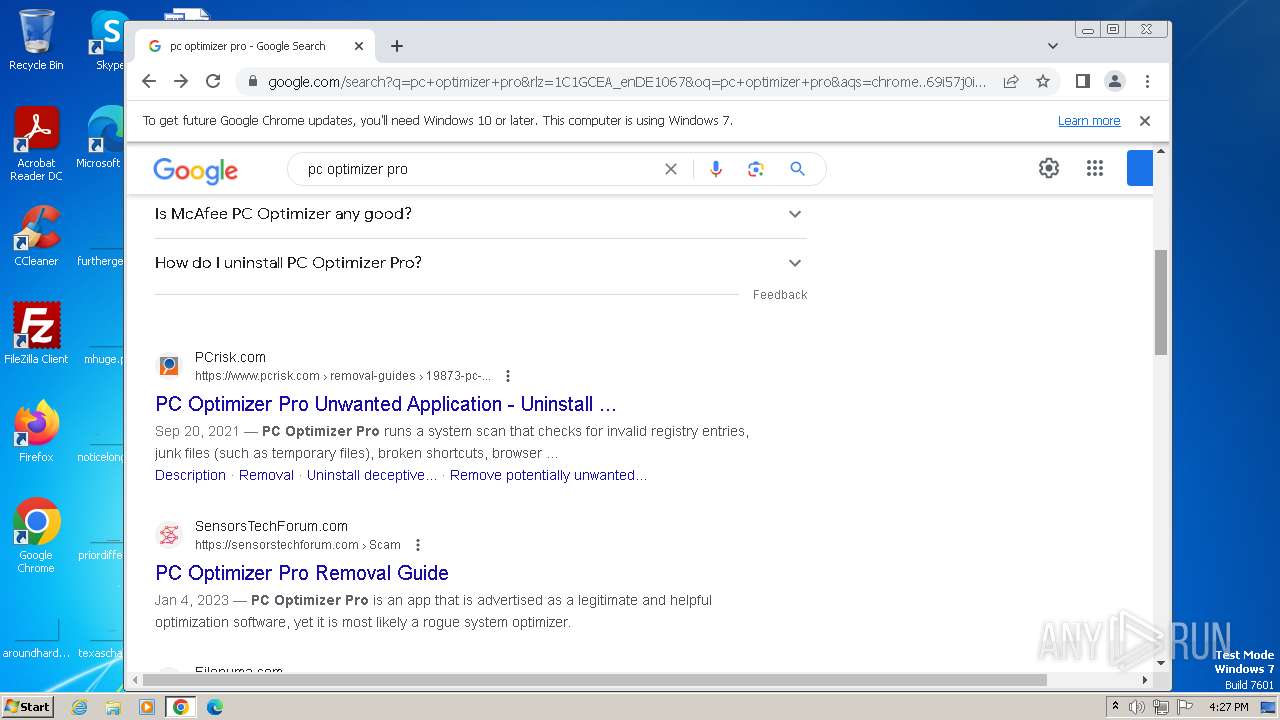
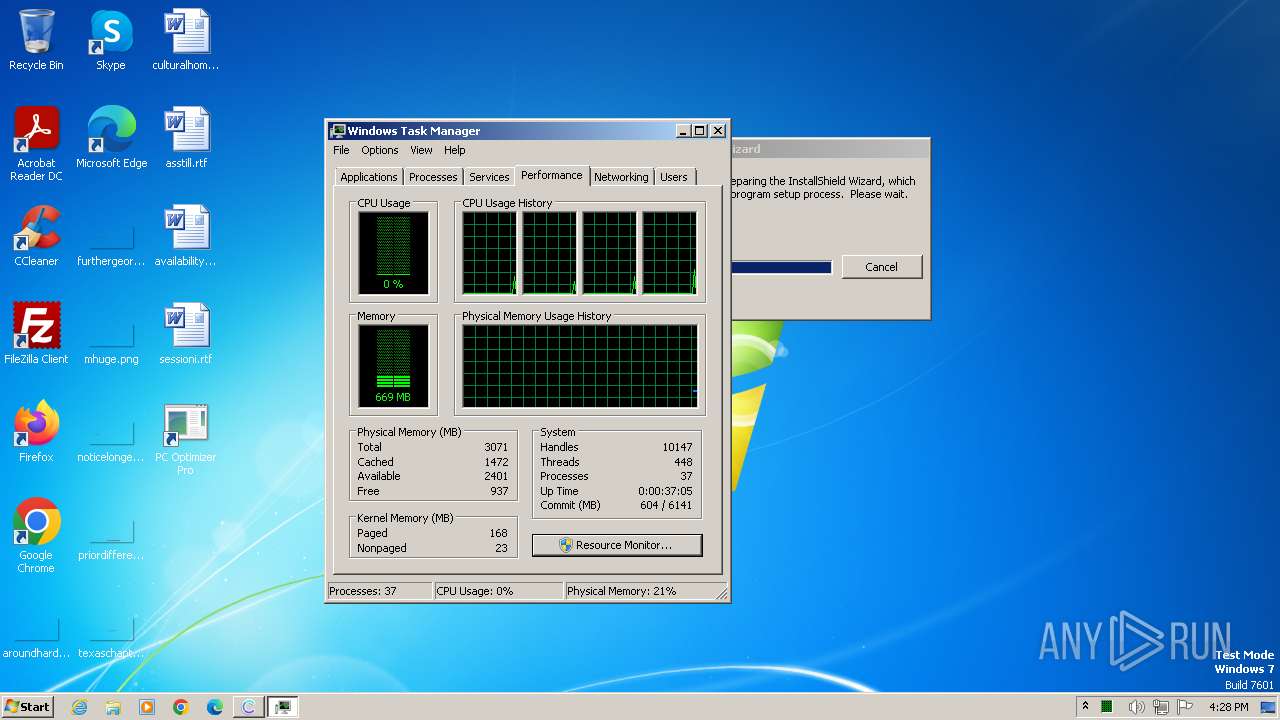
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 80A4986E21C1E5987941A5B3F12ECBFB |
| SHA1: | 988BE4099474CD5A277851A11CC2746FB68252CB |
| SHA256: | 085EDA9A8F30BAAFB4A4245CFA4C6410E932E13746FFCDD5307FC65D498AE782 |
| SSDEEP: | 3:N8SElQ6Q5LKKQKEIMRMzD/my6doJ:2SKcVKKQMP/njJ |
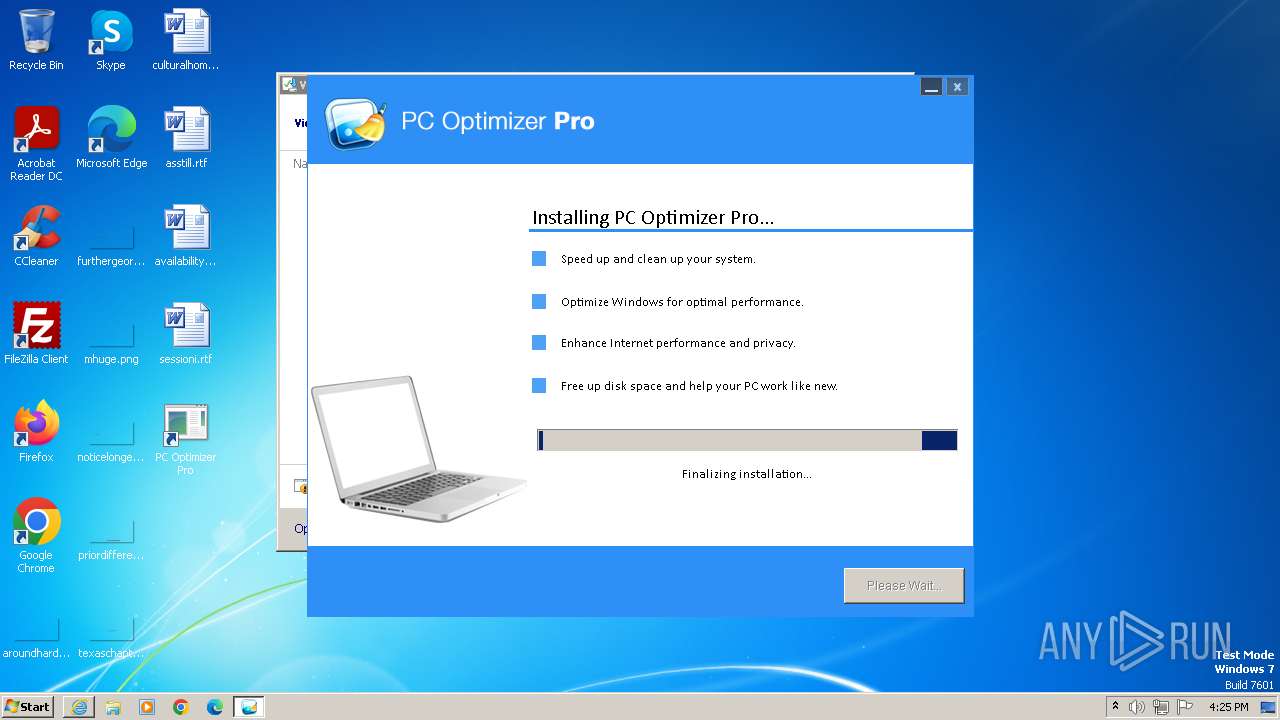
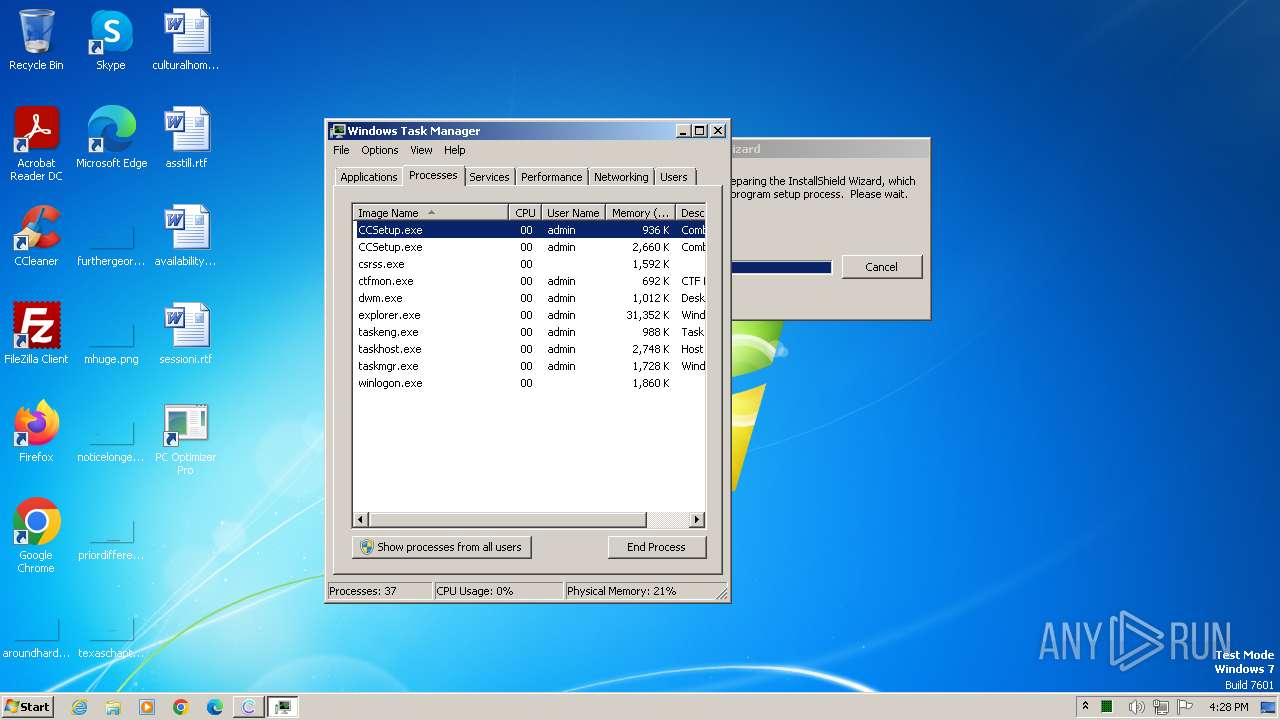
MALICIOUS
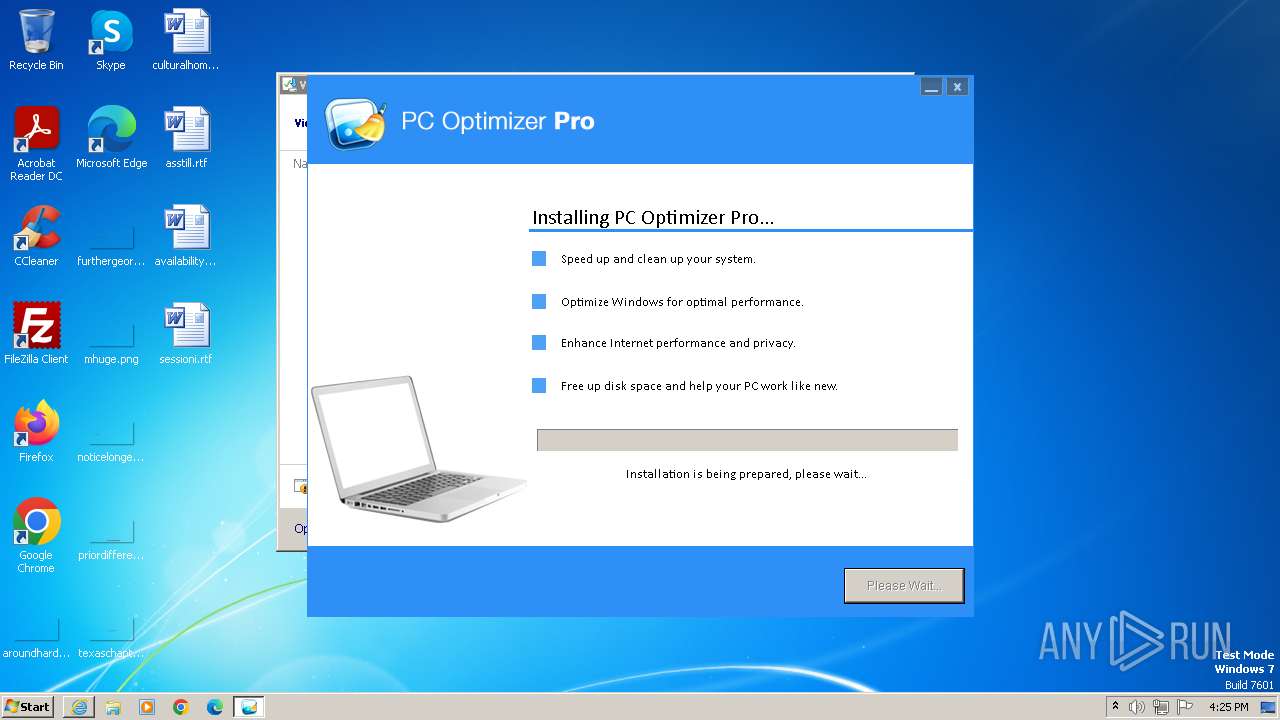
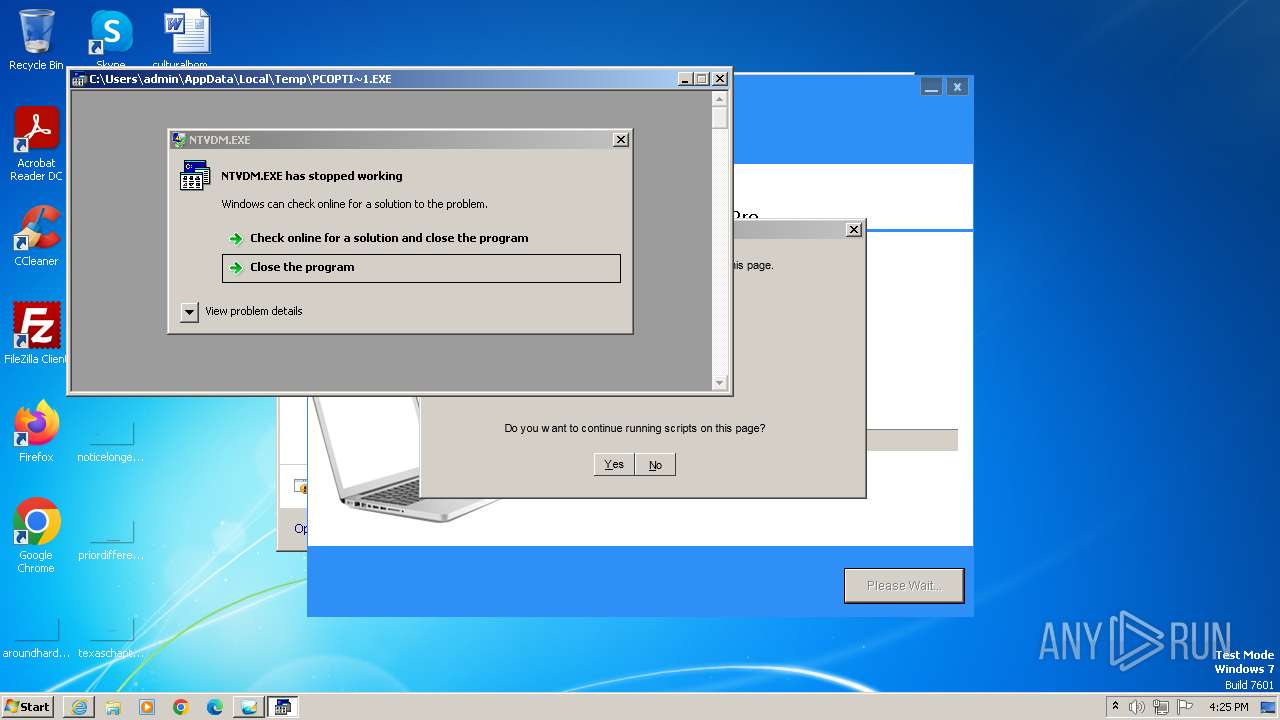
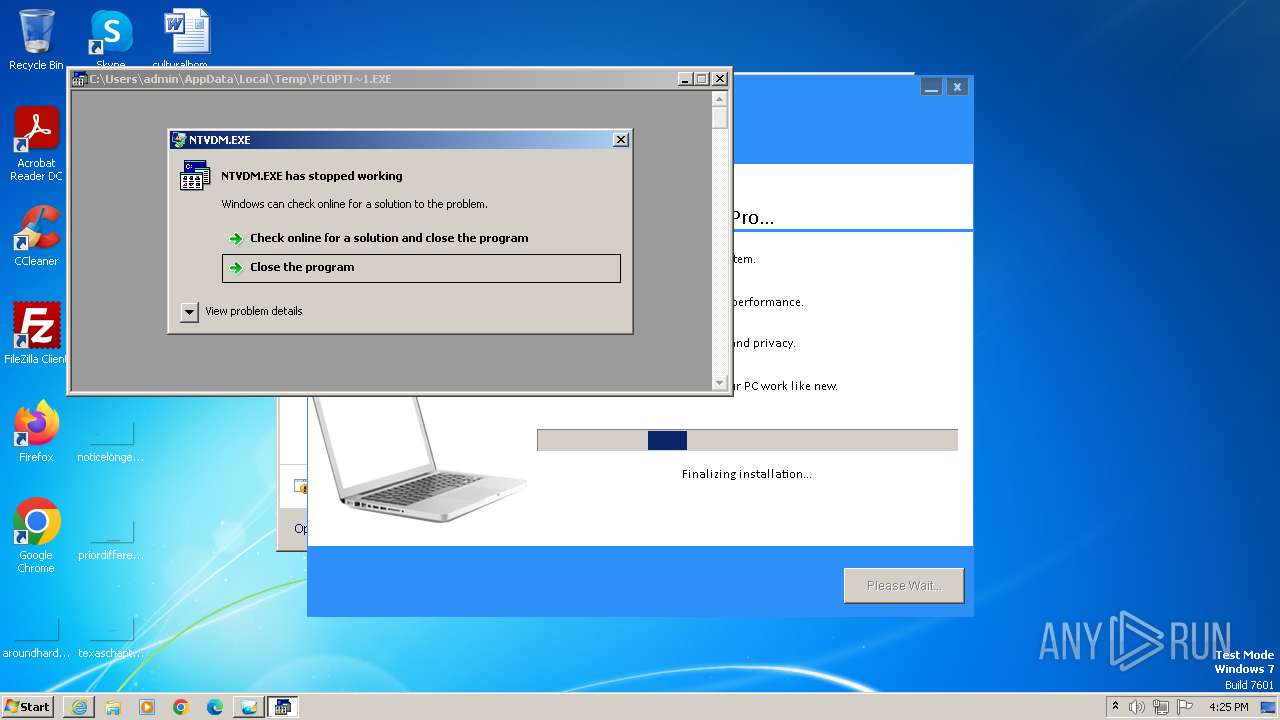
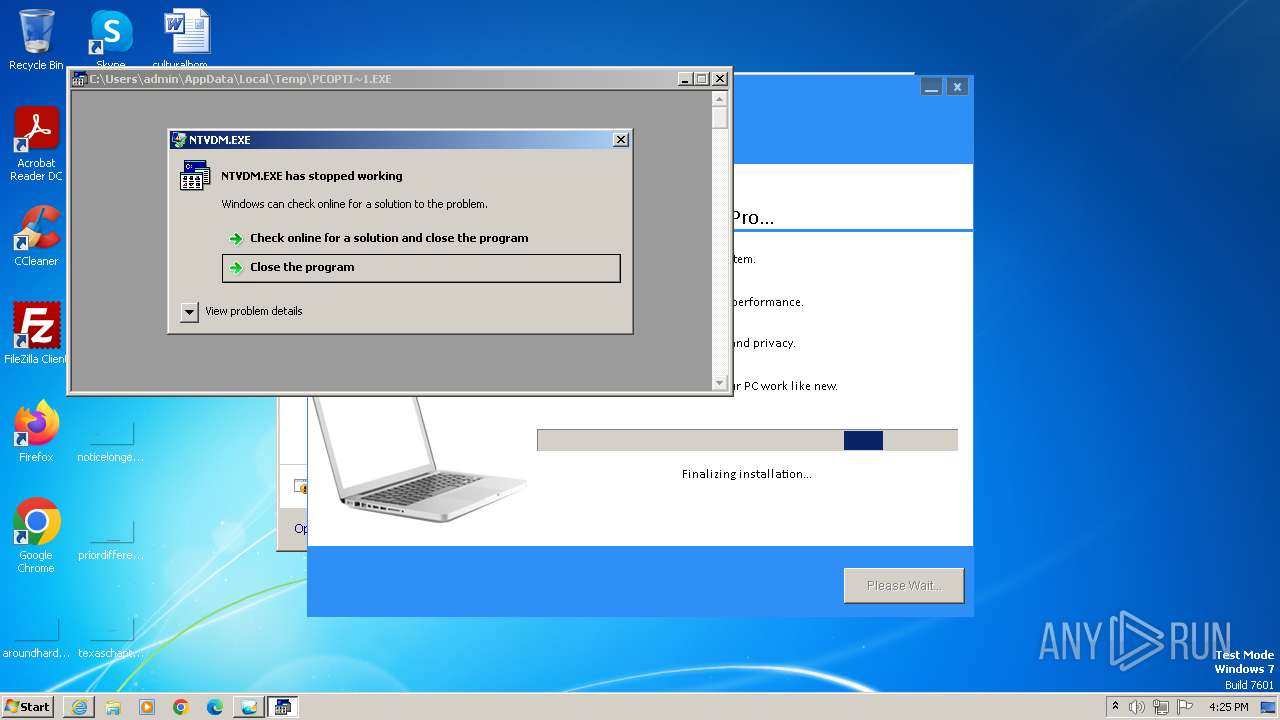
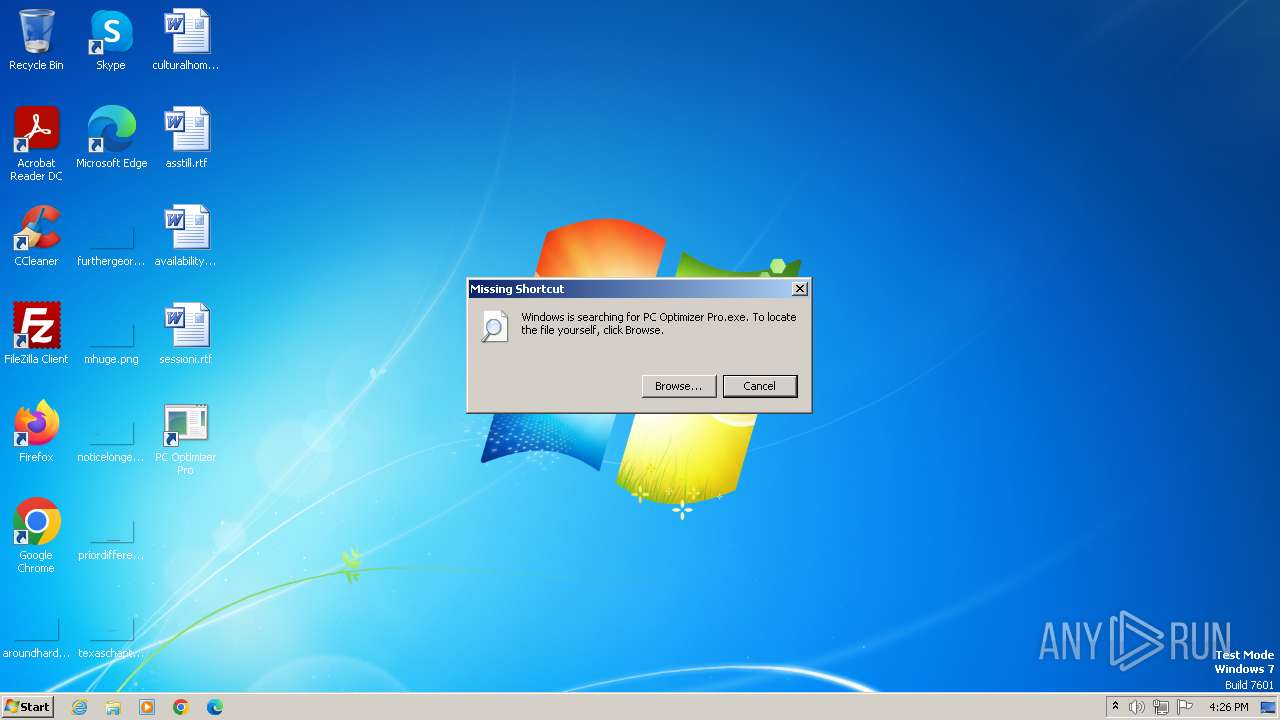
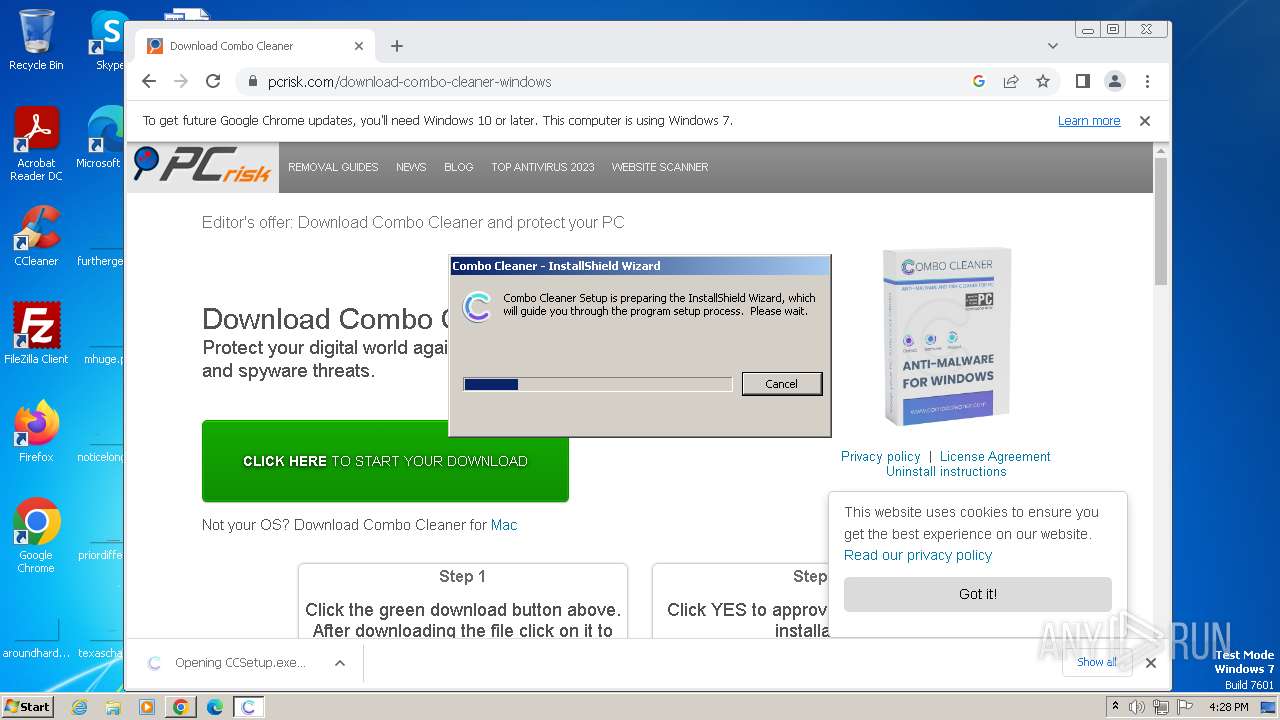
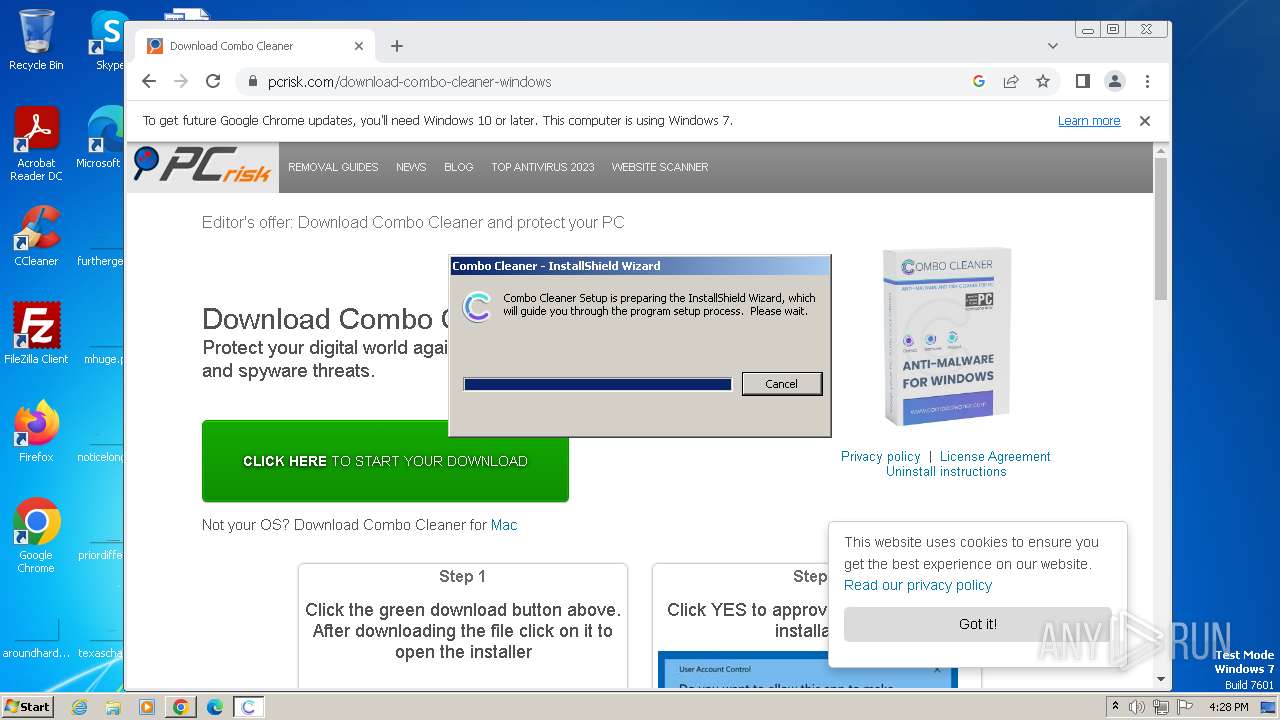
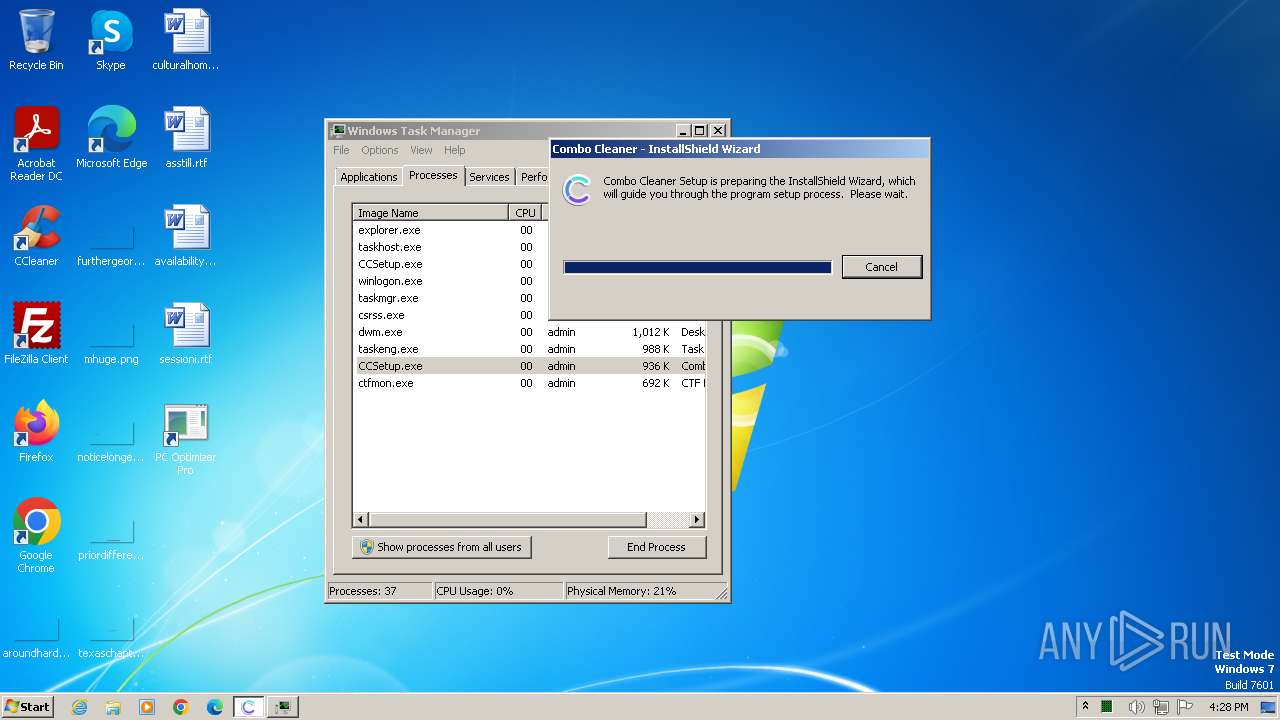
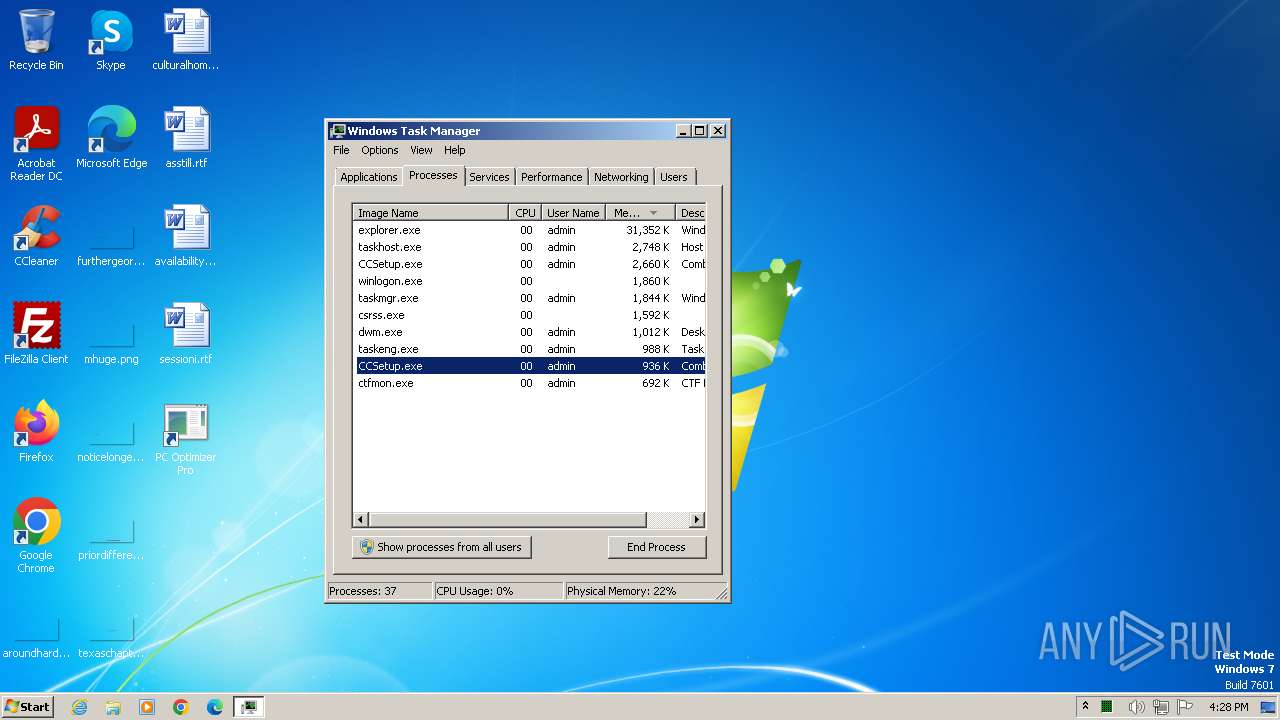
Application was dropped or rewritten from another process
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 3544)
- CCSetup.exe (PID: 1324)
- CCSetup.exe (PID: 1484)
- CCSetup.exe (PID: 3596)
Drops the executable file immediately after the start
- CCSetup.exe (PID: 1324)
SUSPICIOUS
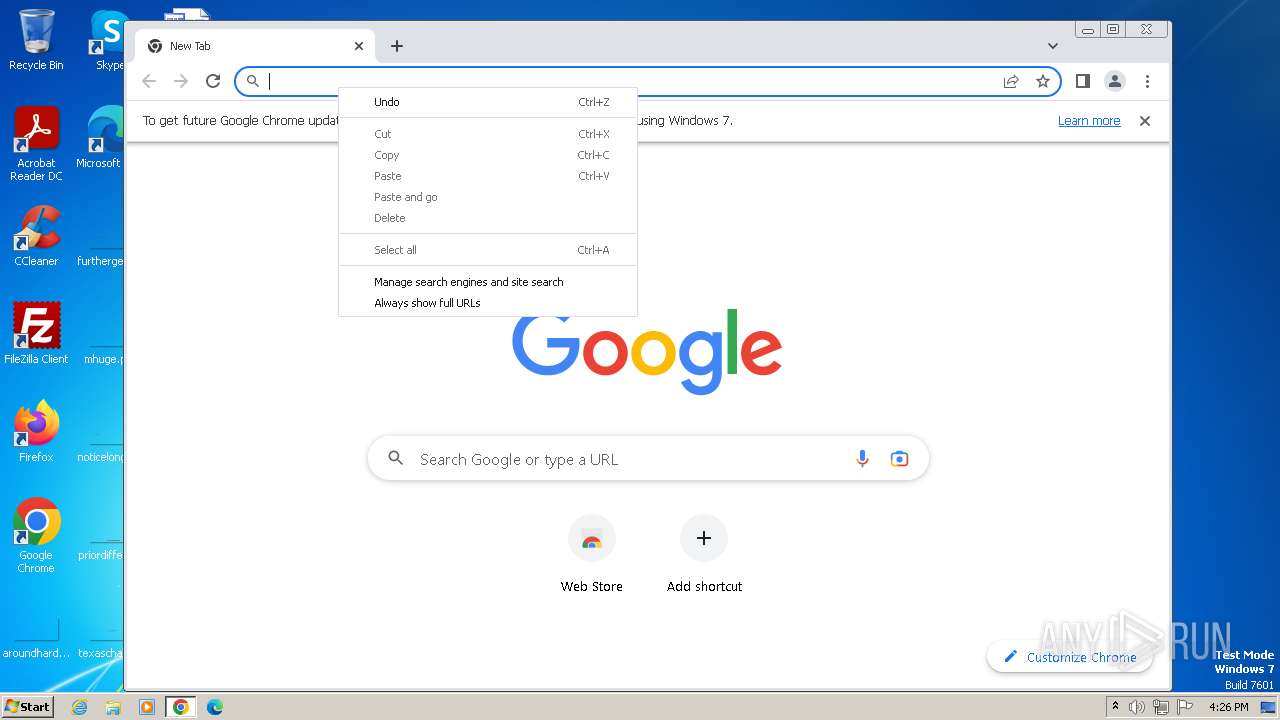
Reads the Internet Settings
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 3596)
Reads Microsoft Outlook installation path
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
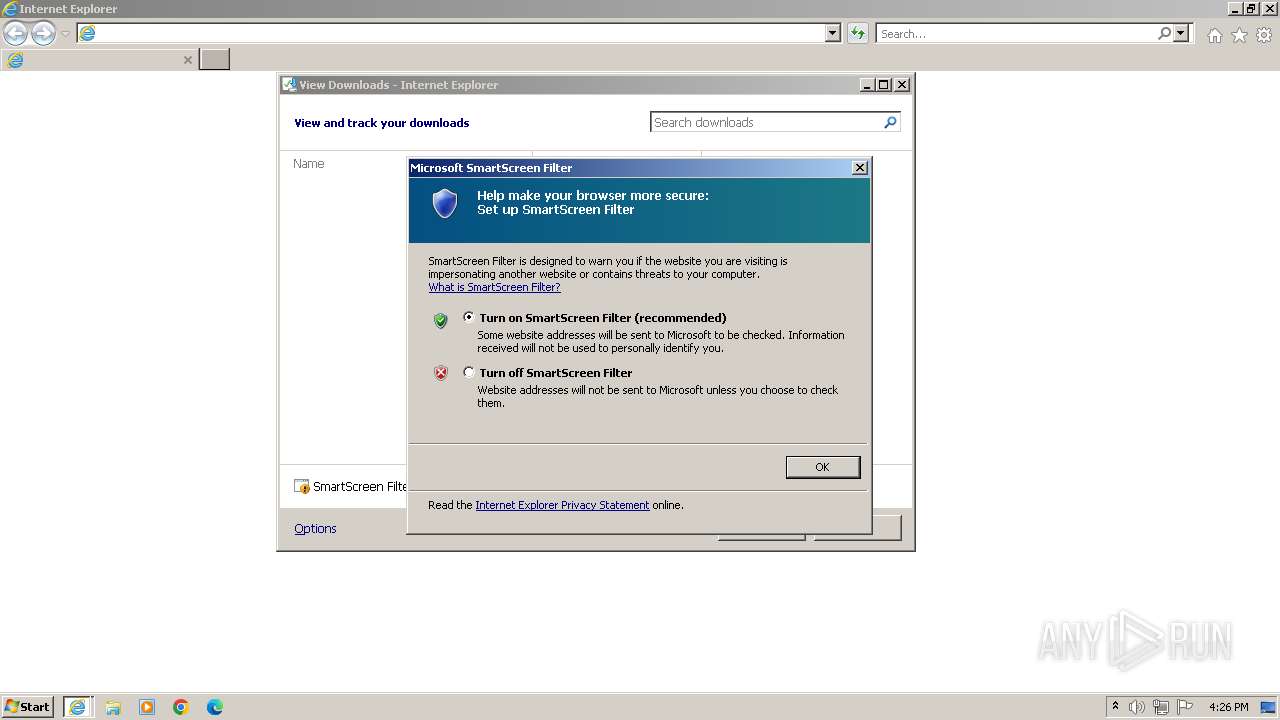
Reads security settings of Internet Explorer
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Reads settings of System Certificates
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Adds/modifies Windows certificates
- iexplore.exe (PID: 2472)
Process requests binary or script from the Internet
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Reads Internet Explorer settings
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Checks Windows Trust Settings
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Starts CMD.EXE for commands execution
- CCSetup.exe (PID: 3596)
The process deletes folder without confirmation
- CCSetup.exe (PID: 3596)
Starts itself from another location
- CCSetup.exe (PID: 1324)
INFO
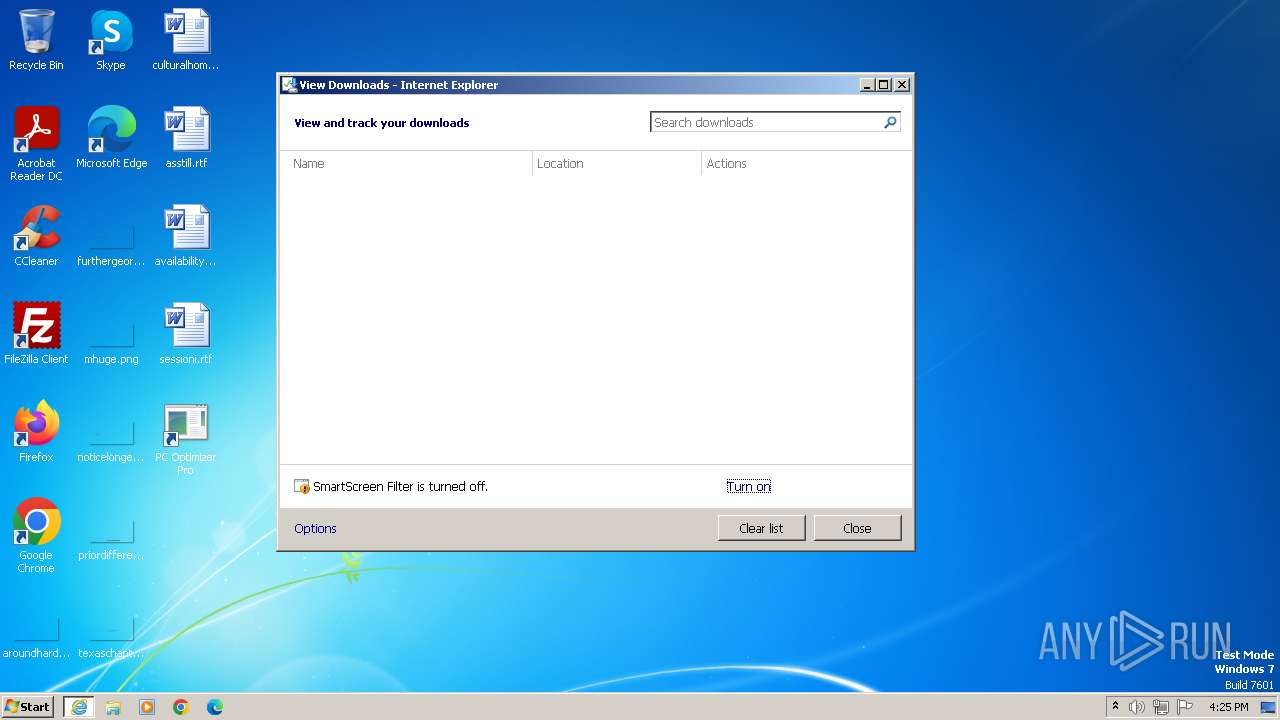
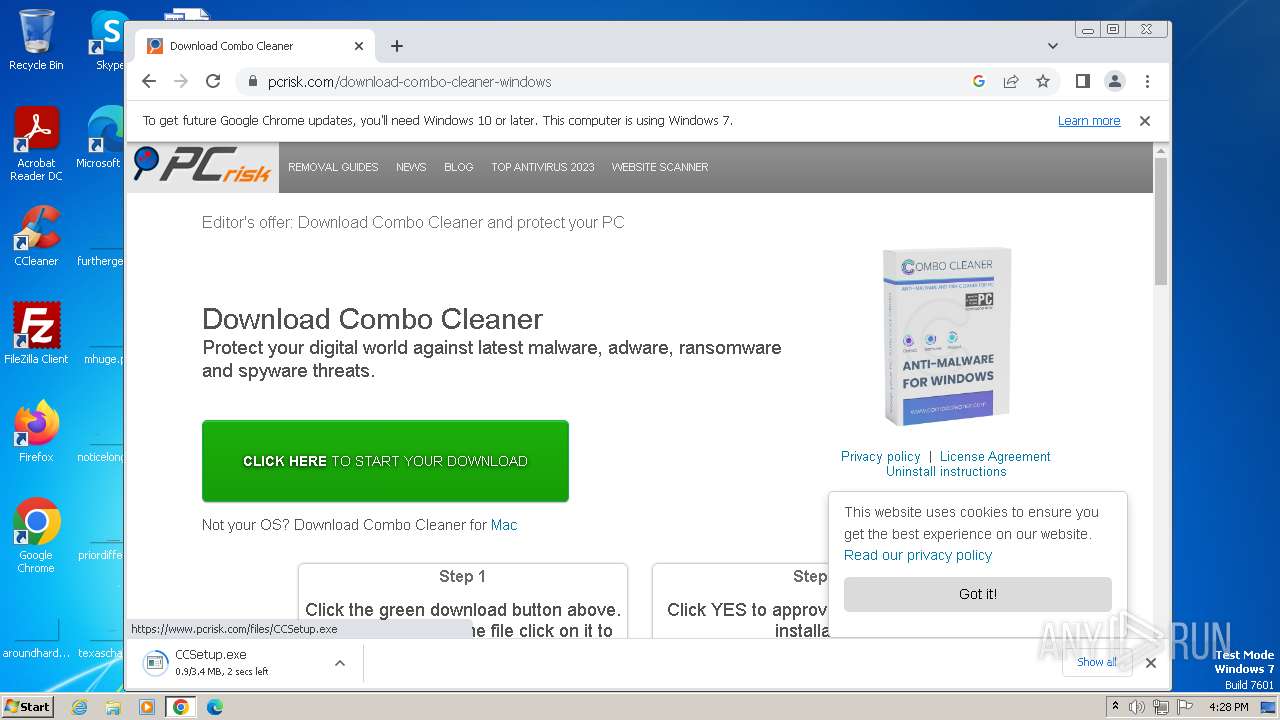
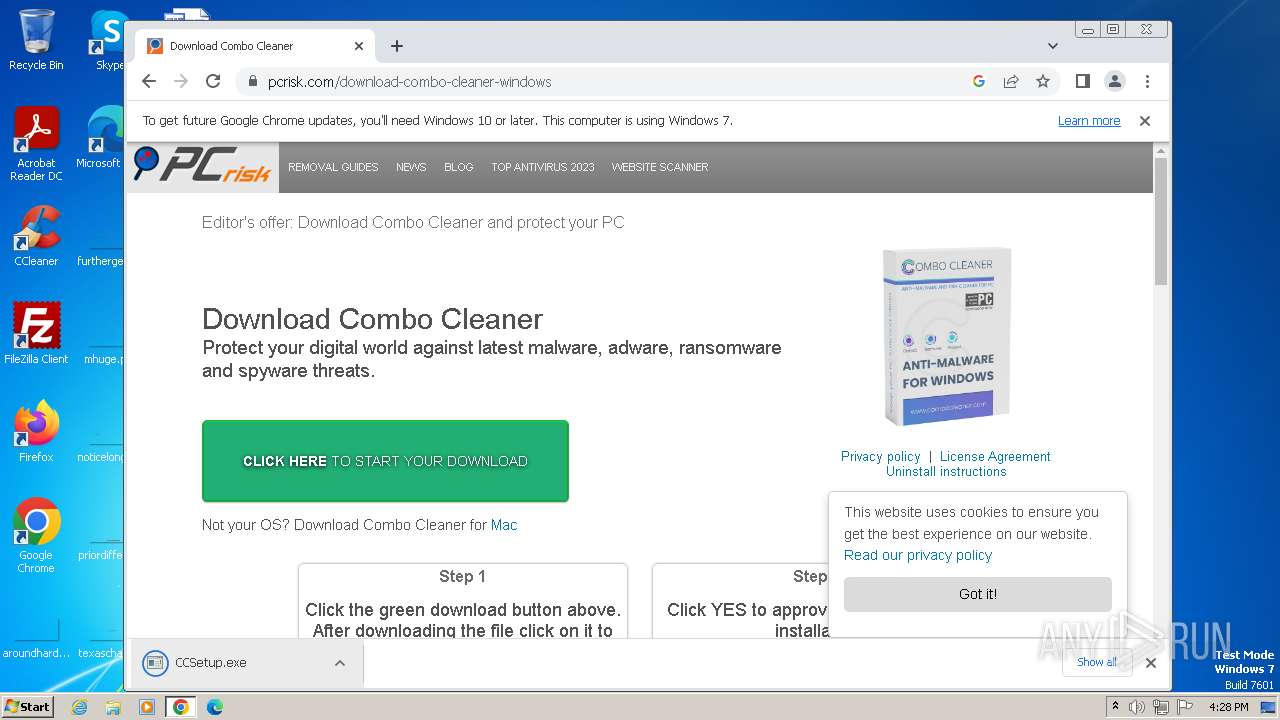
The process uses the downloaded file
- iexplore.exe (PID: 2472)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3300)
- CCSetup.exe (PID: 1324)
- chrome.exe (PID: 292)
Application launched itself
- iexplore.exe (PID: 2472)
- chrome.exe (PID: 3300)
- iexplore.exe (PID: 3984)
Checks supported languages
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 1324)
- CCSetup.exe (PID: 3596)
Reads the computer name
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 1324)
- CCSetup.exe (PID: 3596)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2472)
- iexplore.exe (PID: 4068)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3300)
Checks proxy server information
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 3596)
Reads the machine GUID from the registry
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 3596)
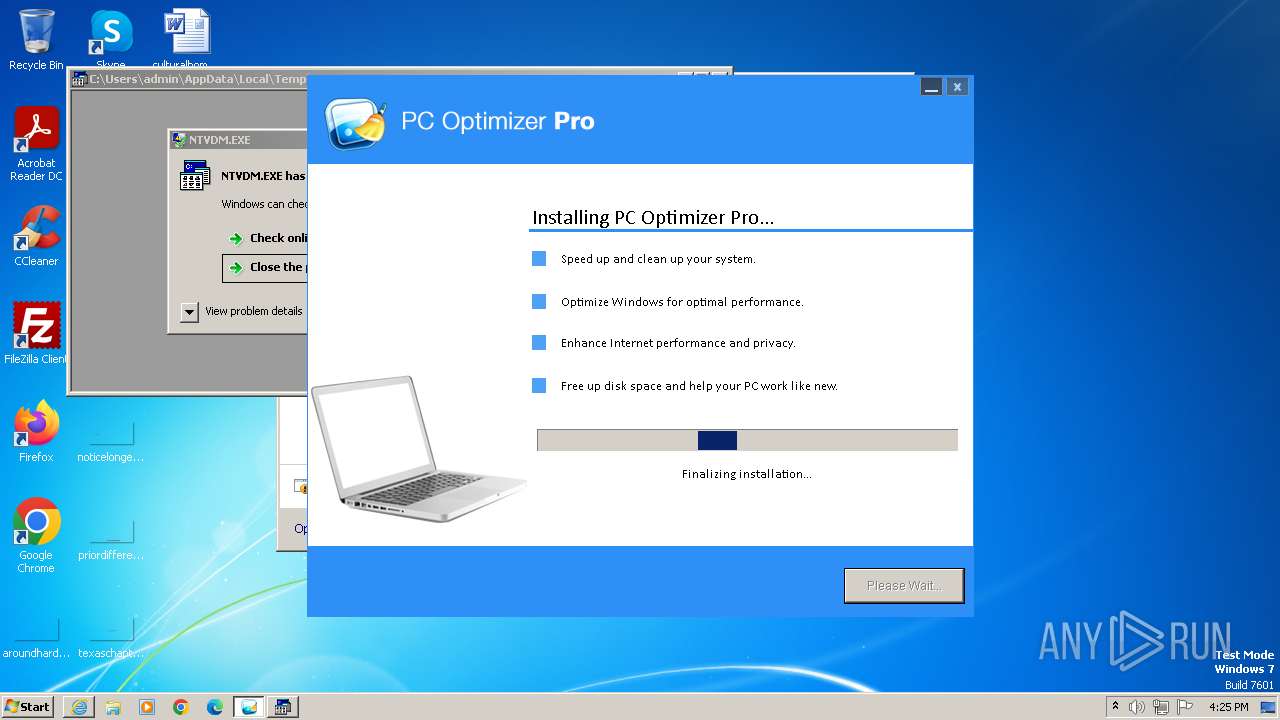
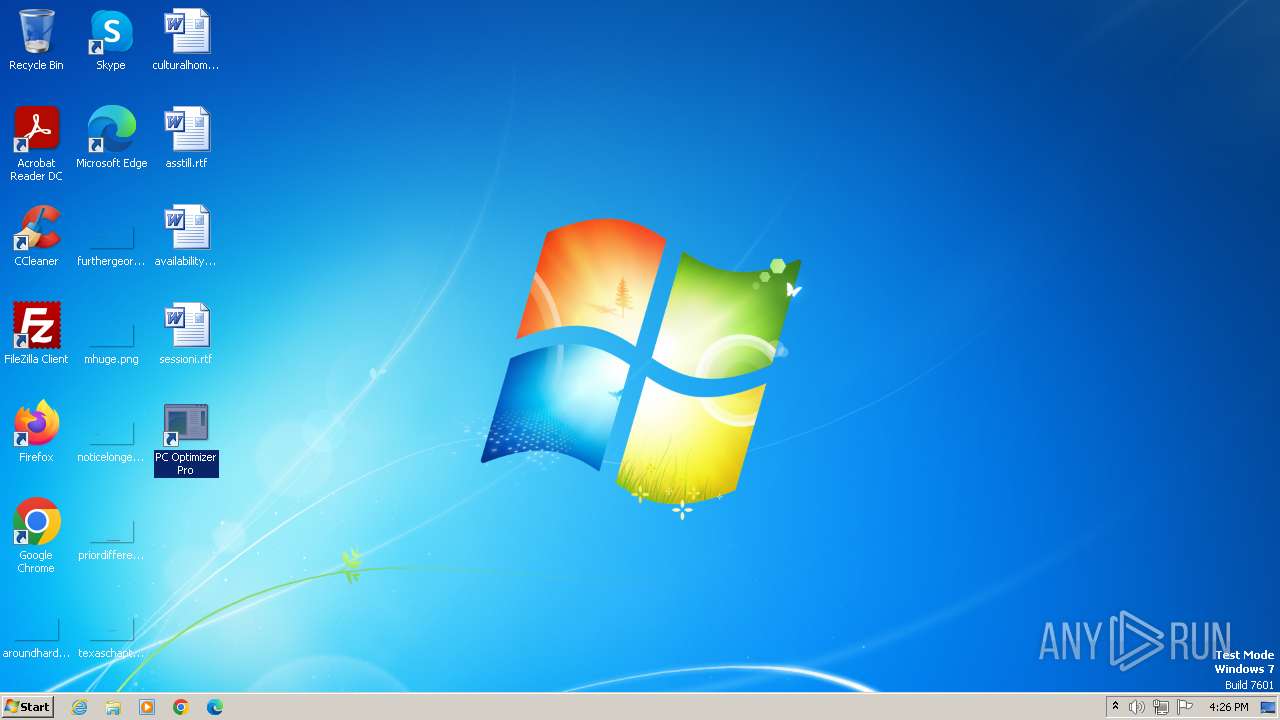
Creates files or folders in the user directory
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
Create files in a temporary directory
- PC_Optimizer_Pro_v7.0.7.1.exe (PID: 124)
- CCSetup.exe (PID: 1324)
- CCSetup.exe (PID: 3596)
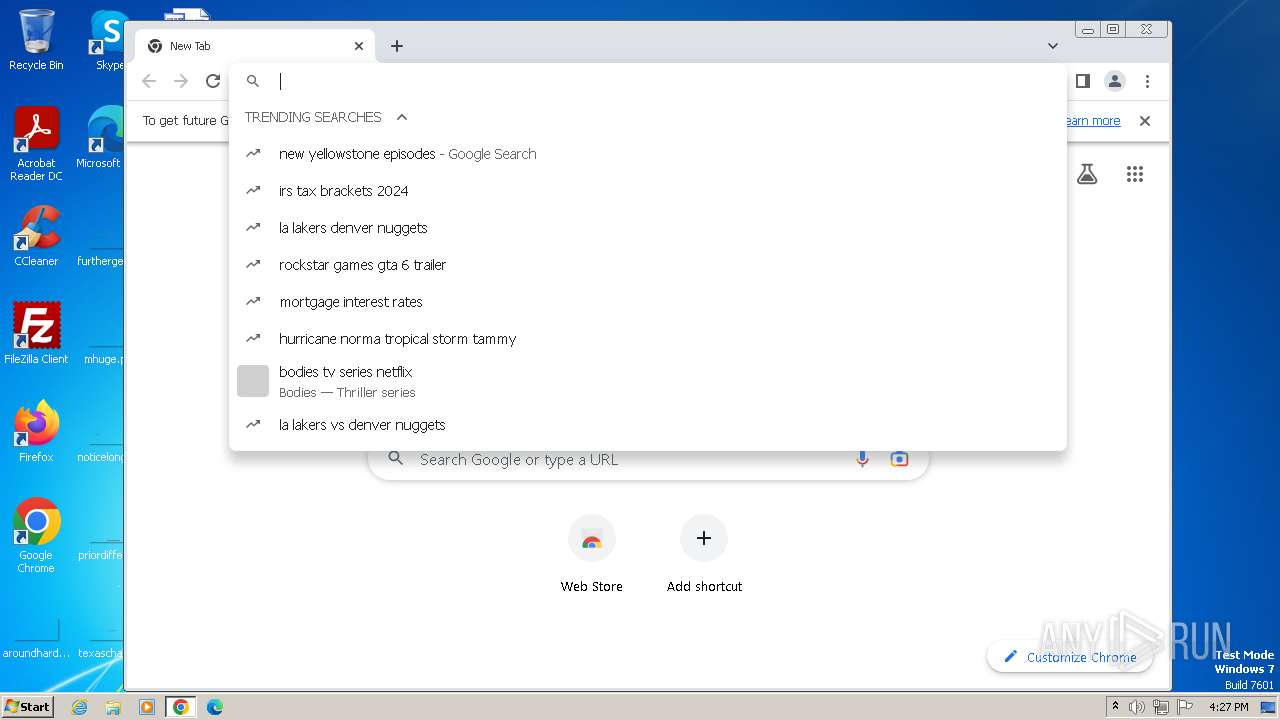
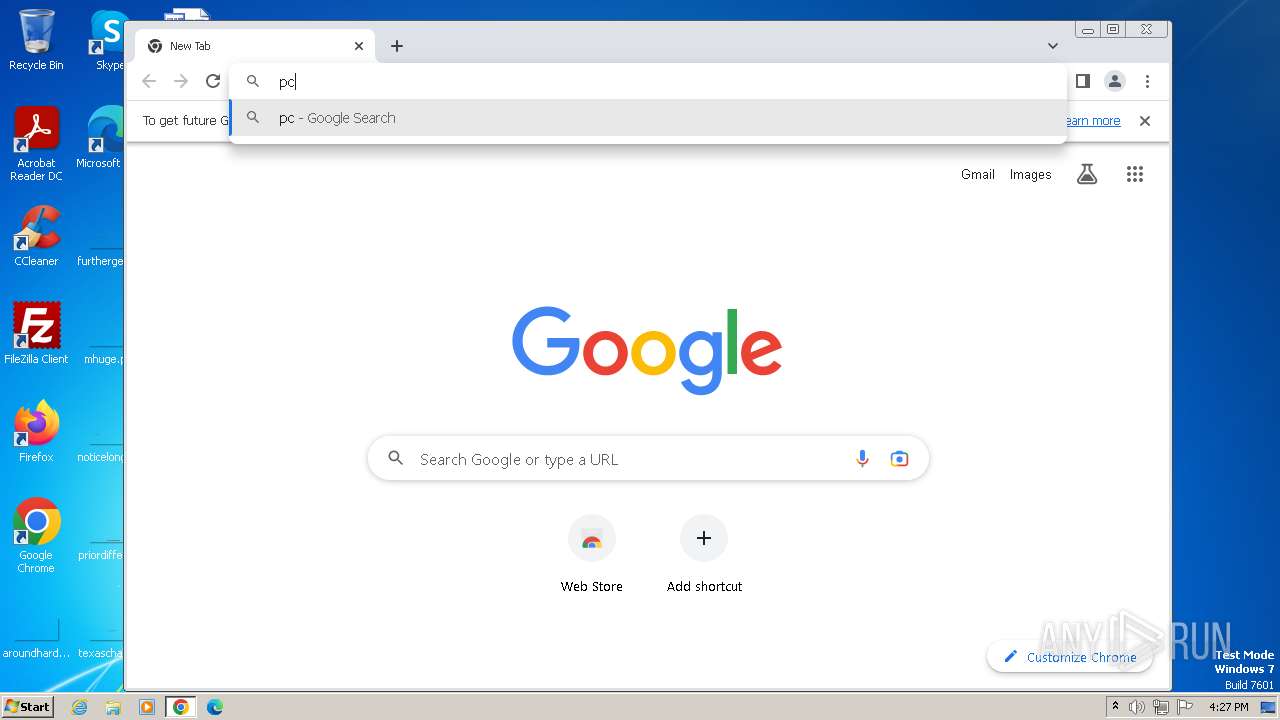
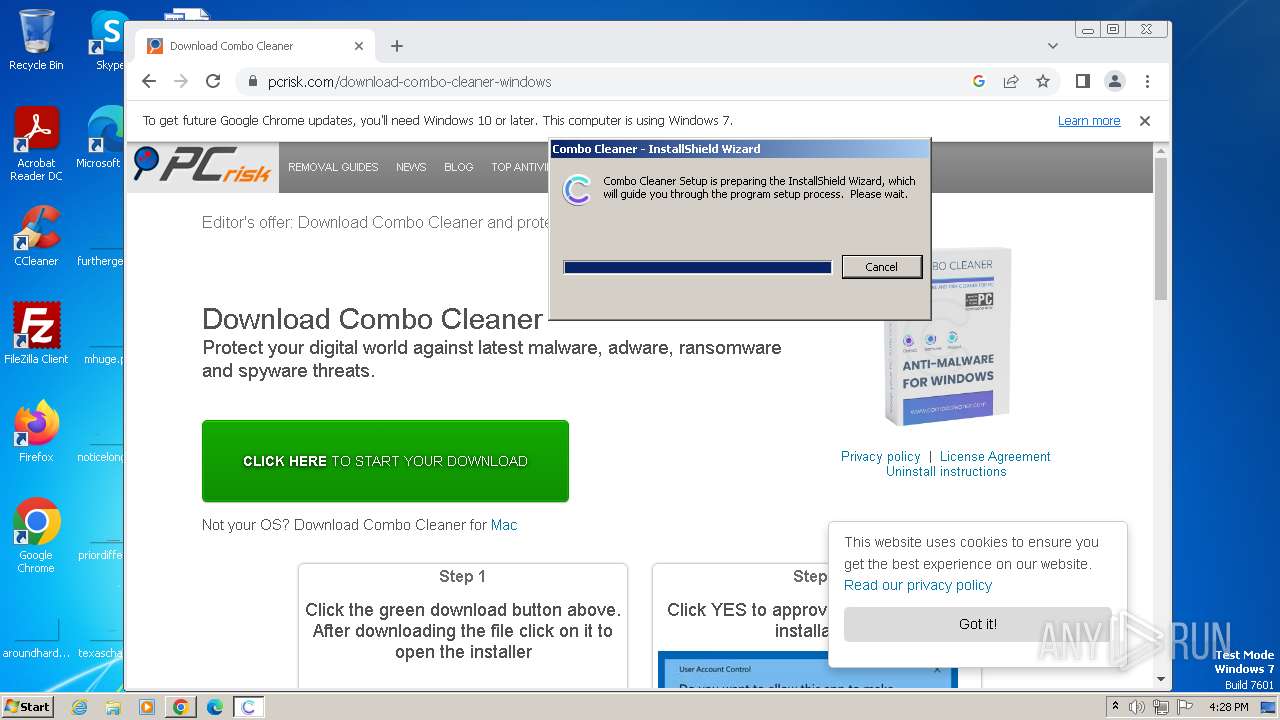
Manual execution by a user
- iexplore.exe (PID: 3984)
- chrome.exe (PID: 3300)
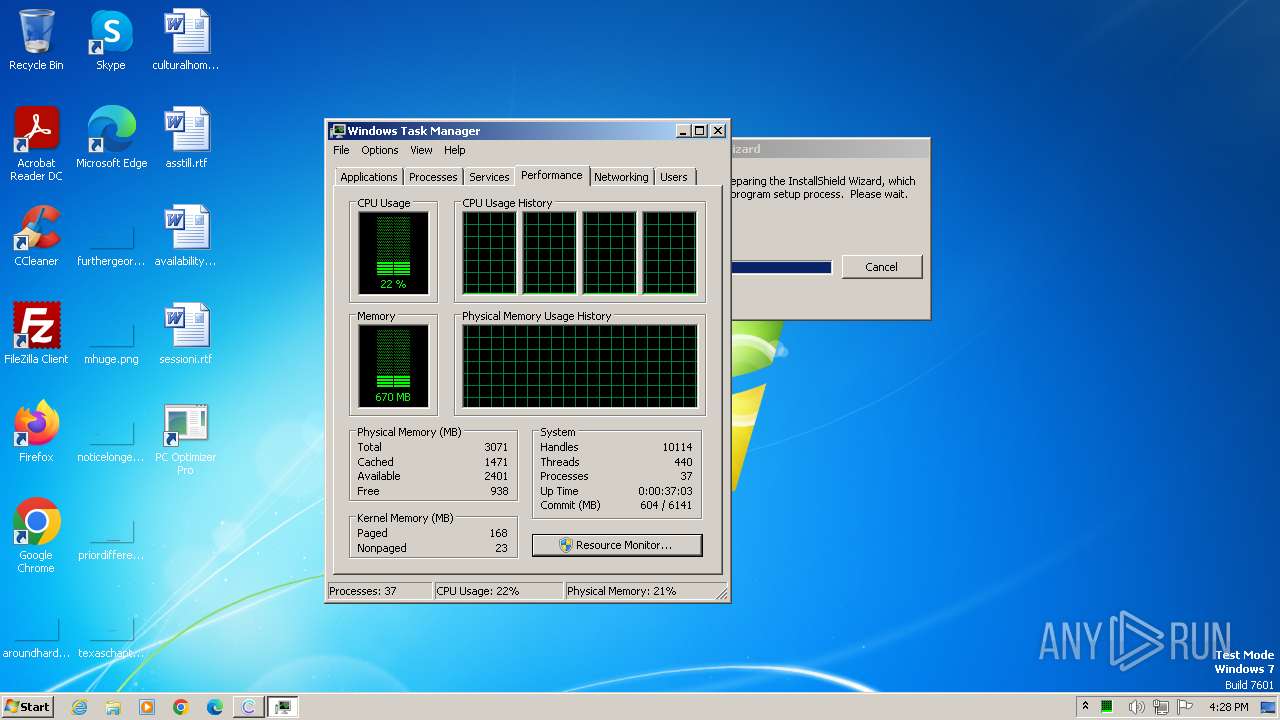
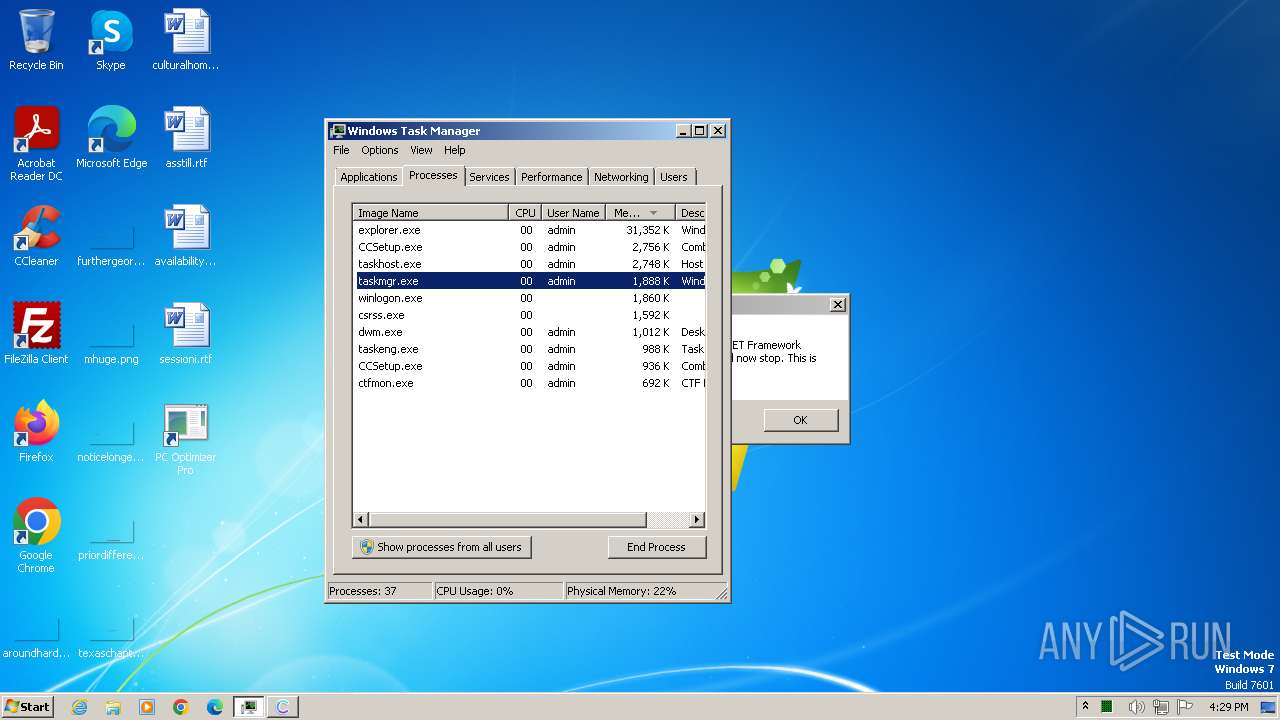
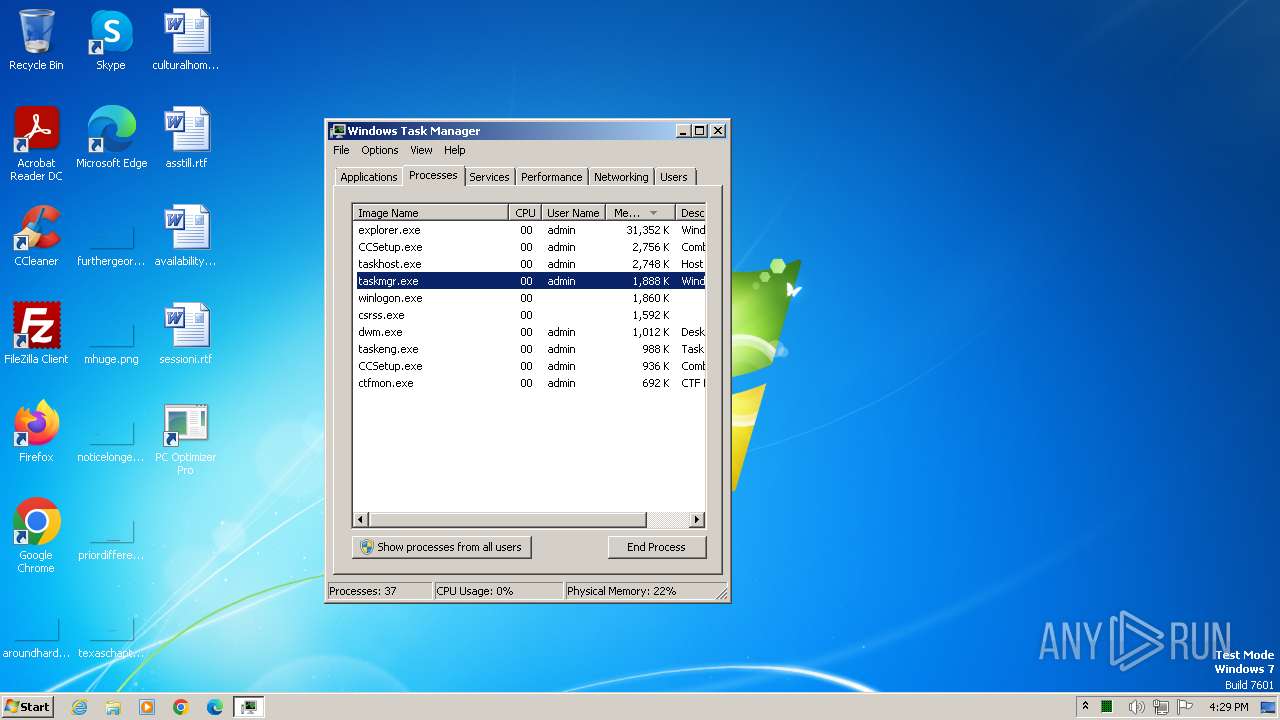
- taskmgr.exe (PID: 1840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
41
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PC_Optimizer_Pro_v7.0.7.1.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PC_Optimizer_Pro_v7.0.7.1.exe | iexplore.exe | ||||||||||||
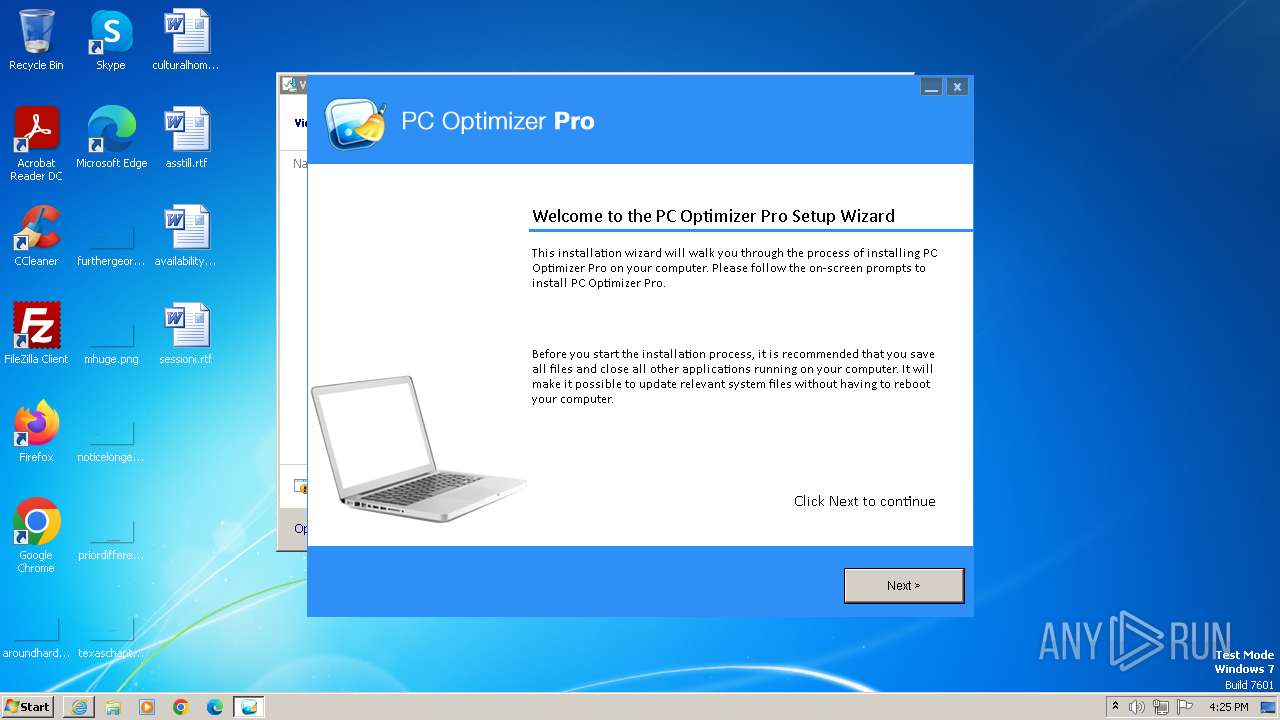
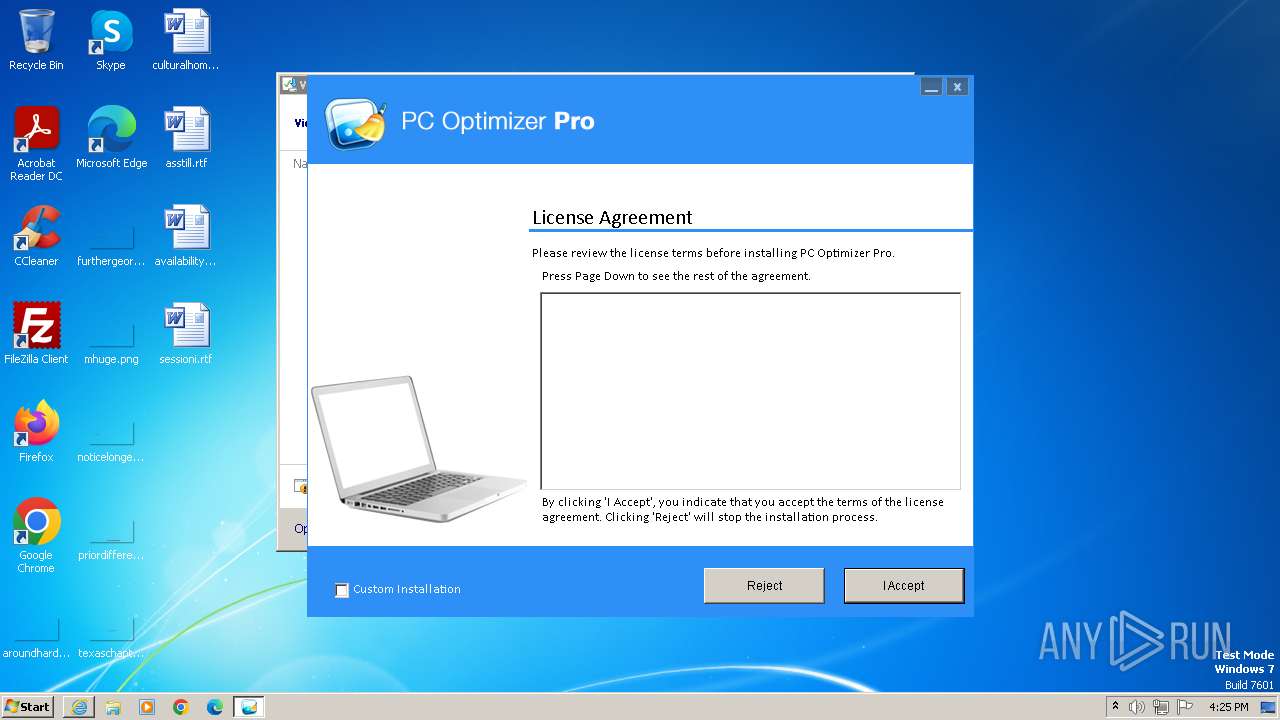
User: admin Company: Xportsoft Technologies Integrity Level: HIGH Description: PC Optimizer Pro Installer Exit code: 0 Version: 1.0.1.1 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4456 --field-trial-handle=1184,i,9519513660152238702,394184260323104533,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e0b8b38,0x6e0b8b48,0x6e0b8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3996 --field-trial-handle=1184,i,9519513660152238702,394184260323104533,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
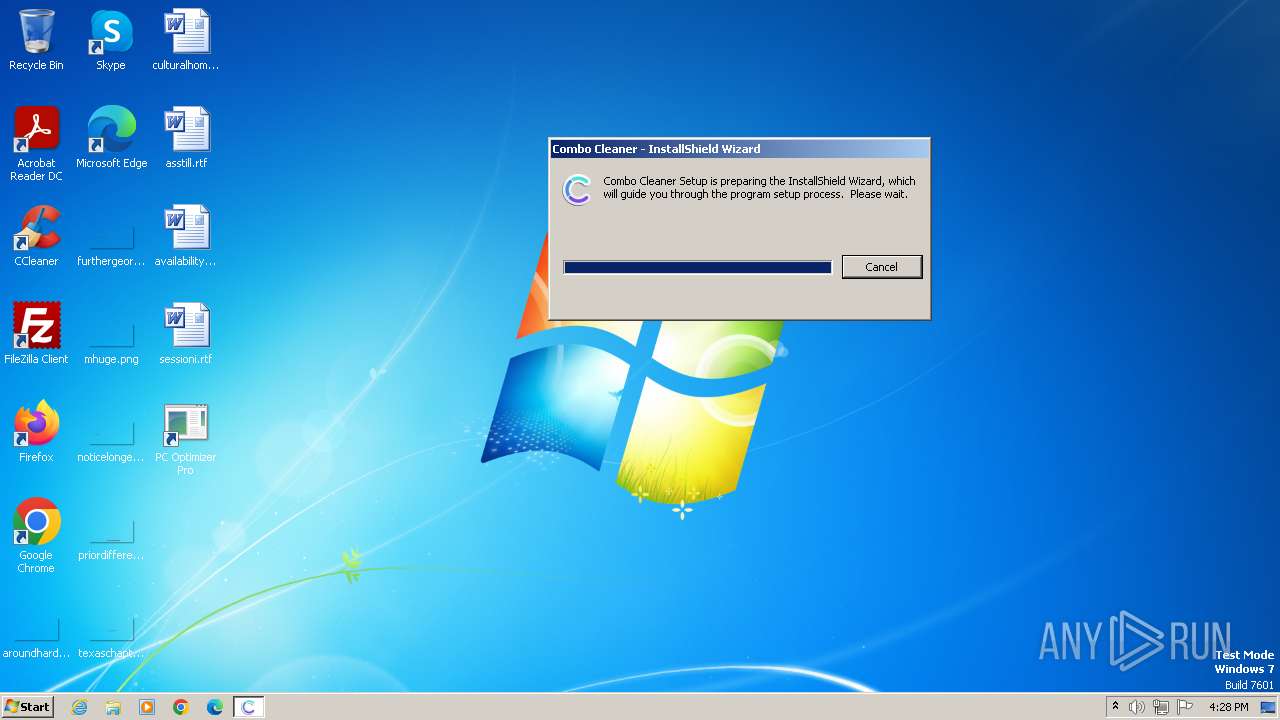
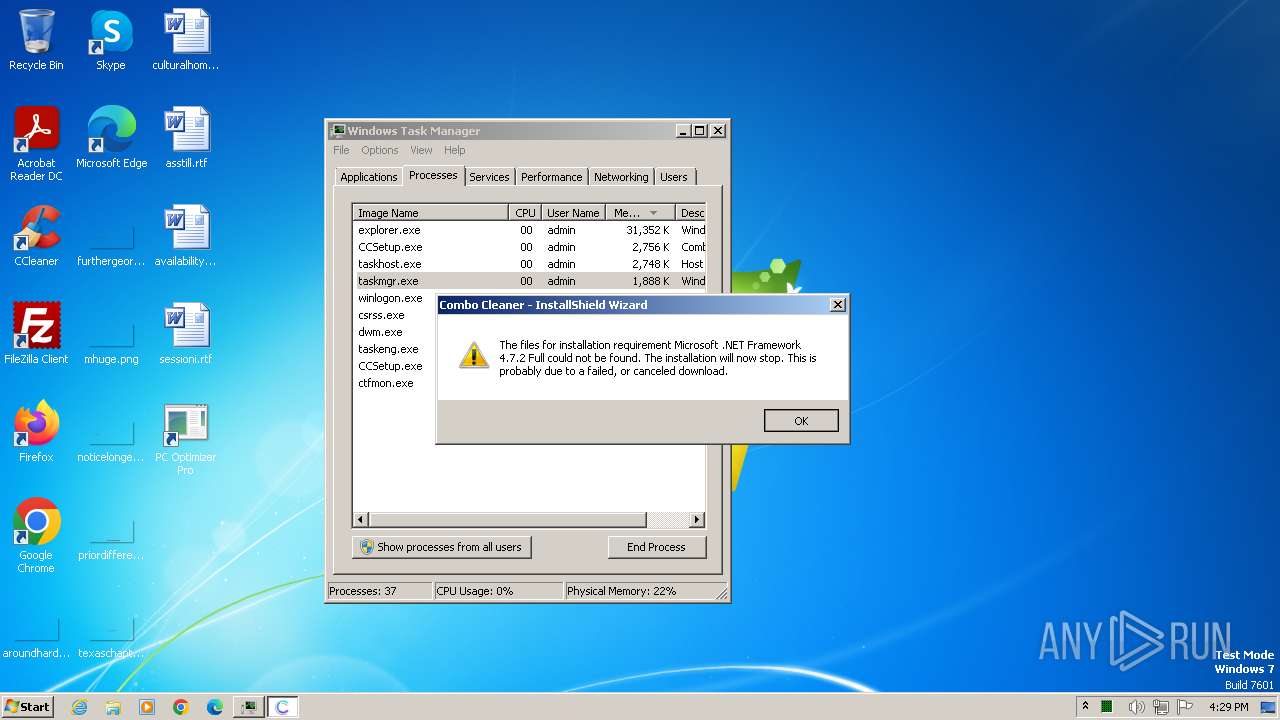
| 1324 | "C:\Users\admin\Downloads\CCSetup.exe" | C:\Users\admin\Downloads\CCSetup.exe | chrome.exe | ||||||||||||
User: admin Company: RCS LT Integrity Level: HIGH Description: Combo Cleaner Exit code: 4294967295 Version: 1.0.58.0 Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\Downloads\CCSetup.exe" | C:\Users\admin\Downloads\CCSetup.exe | — | chrome.exe | |||||||||||
User: admin Company: RCS LT Integrity Level: MEDIUM Description: Combo Cleaner Exit code: 3221226540 Version: 1.0.58.0 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1496 --field-trial-handle=1184,i,9519513660152238702,394184260323104533,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1132 --field-trial-handle=1184,i,9519513660152238702,394184260323104533,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1296 --field-trial-handle=1184,i,9519513660152238702,394184260323104533,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1840 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
38 818
Read events
38 468
Write events
339
Delete events
11
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
8
Suspicious files
237
Text files
91
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | PC_Optimizer_Pro_v7.0.7.1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\eula[1].htm | html | |
MD5:C085C16FBEC3D176C632782DCB98F03F | SHA256:07DBCBD59563C25802052A08F42B066FF5171FF593A2E842FBFCE04B8498B91F | |||
| 124 | PC_Optimizer_Pro_v7.0.7.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:7F95B1A23A518844C8618C4C41ACC610 | SHA256:02809BA8BA25718D08FF748725A4C628200521C709BD5F8C244EB0EAA6F1712A | |||
| 124 | PC_Optimizer_Pro_v7.0.7.1.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:555D1DFB610D4940135997A82A30ABF7 | SHA256:66F38A7B81FCD8A149121EDBFA062D754730ED4CB07D6F393BCC573AB3046B02 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF6F78A1C6247937B.TMP | binary | |
MD5:AD7A93E139971866E8771B6C45586B66 | SHA256:BB046F9EACD7043B42D59EF1767778CDC29B64D70483596F12977B4CECA37295 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{872635C3-7281-11EE-B150-12A9866C77DE}.dat | binary | |
MD5:68DE9C119E4C3D8E0B00DC5F66A61EAB | SHA256:0EDA5FB6585792BE7C2FC3EC309066457E4FC8BF66D52279CEA0A312BBA36D3F | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:DAE3D0AF5F3F96AF6459844B457A0ACE | SHA256:B31BFA0D586CB89F2452C2D02BDF2B4898C274E777CC271F7B4F19EDCE1863C2 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:27D2CCC0D3330A98F6E69CE73ABA7F61 | SHA256:55298A2501B9860039D1891DEE3FEE39E27AF942063C58166873D568C4EE1FAA | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\PC_Optimizer_Pro_v7.0.7.1[1].exe | executable | |
MD5:82AA131C0A887933E14AA776D8E3B796 | SHA256:075C3AD8A5097FA8CAD178B310ACDEE8A90305EFB5798257154724C806E51751 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:A2EB2A6569ACC6DB9F3BC4CF72F39A89 | SHA256:9115DA958A0ED178238E8B2A58F9A71D2649A58E4C519B65AFFF358665F8C942 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
111
DNS requests
131
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f96a15a63697bdc6 | unknown | compressed | 4.66 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?44b7f016ec3320f4 | unknown | compressed | 4.66 Kb | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?be79887c7a8f55ce | unknown | compressed | 61.6 Kb | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootca3.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRkNawYMzz%2BjKSfYbTyFR0AXuhs6QQUq7bb1waeN6wwhgeRcMecxBmxeMACEwdzEmaE1XfA%2FPjTo0K%2BqG%2BU%2FI8%3D | unknown | binary | 839 b | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEVPiCzvQdHKEiO6fm6h1os%3D | unknown | binary | 471 b | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCiqTpRpOc3bRIUpkAuvtnV | unknown | binary | 472 b | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEowz8xPdLX1MG5U07e%2BCsM%3D | unknown | binary | 1.51 Kb | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c16a8f115b227458 | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4068 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4068 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
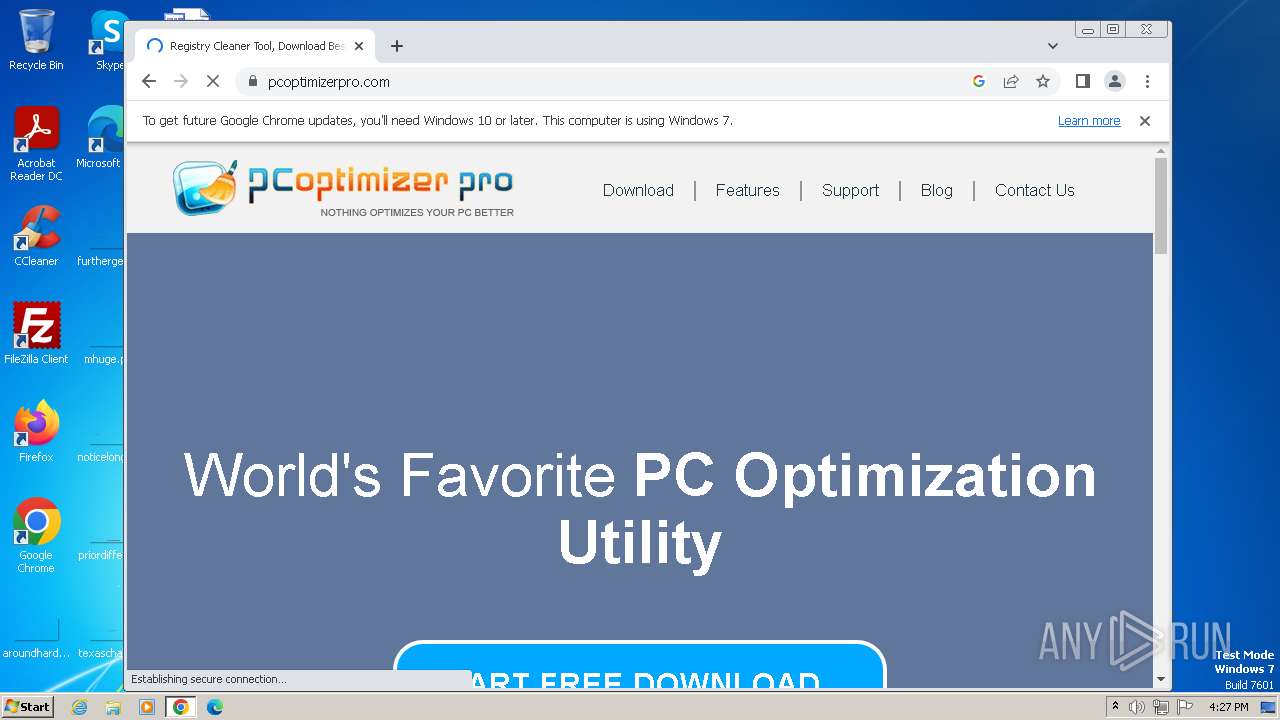
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 50.63.8.124:80 | www.pcoptimizerpro.com | GO-DADDY-COM-LLC | US | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 50.63.8.124:443 | www.pcoptimizerpro.com | GO-DADDY-COM-LLC | US | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 104.18.15.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | unknown |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 142.250.185.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
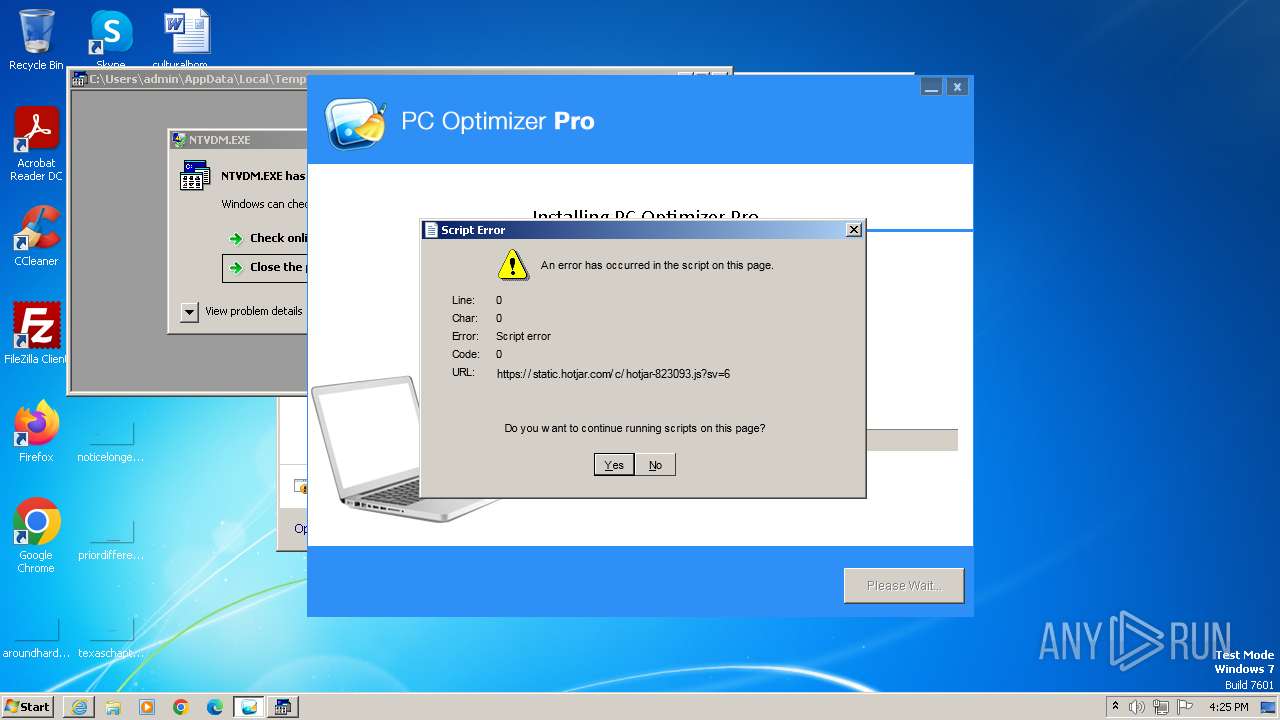
124 | PC_Optimizer_Pro_v7.0.7.1.exe | 13.107.246.45:443 | www.clarity.ms | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.pcoptimizerpro.com |
| unknown |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.clarity.ms |
| whitelisted |
oss.maxcdn.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
124 | PC_Optimizer_Pro_v7.0.7.1.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | A Network Trojan was detected | ET MALWARE Potential Dridex.Maldoc Minimal Executable Request |
124 | PC_Optimizer_Pro_v7.0.7.1.exe | A Network Trojan was detected | ET MALWARE Potential Dridex.Maldoc Minimal Executable Request |
1940 | chrome.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3596 | CCSetup.exe | Misc activity | ET INFO Installshield One Click Install User-Agent Toys File |
Process | Message |
|---|---|
PC_Optimizer_Pro_v7.0.7.1.exe | http://www.pcoptimizerpro.com/STD1/32/PCOptimizerProSetup.exe |
PC_Optimizer_Pro_v7.0.7.1.exe |
C:\Users\admin\AppData\Local\Temp\PCOptimizerProSetup.exe
http://www.pcoptimizerpro.com/STD1/32/PCOptimizerProSetup.exe |
PC_Optimizer_Pro_v7.0.7.1.exe | C:\Program Files\PC Optimizer Pro\PC Optimizer Pro.exe |