| File name: | msicuu2.exe |
| Full analysis: | https://app.any.run/tasks/20b48fa8-b09b-4280-adf1-dde29603c181 |
| Verdict: | Suspicious activity |
| Analysis date: | September 26, 2019, 13:57:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | D5F4AB6063B3B3795B1C0F0CF30C7DFB |
| SHA1: | 23D3C4D0869769F424B1C0C54F18C50761CA2C14 |
| SHA256: | 08565FE3A18E051F9F557C219A51844DBAC4A6DEE9076EB8ECFED2A3137A3FE8 |
| SSDEEP: | 6144:dFfDAEl3nOvkGe/DDWGszKjV1eNHkG+ovUM3ep3Dx1RzSG:XwGDWGszKjV1eWGL5epTXRzSG |
MALICIOUS
Changes the autorun value in the registry
- msicuu2.exe (PID: 2960)
SUSPICIOUS
Executes scripts
- msicuu2.exe (PID: 2960)
Executable content was dropped or overwritten
- msicuu2.exe (PID: 2960)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (81.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.3) |
| .exe | | | Win64 Executable (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Win16/32 Executable Delphi generic (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:07:15 13:48:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 36864 |
| InitializedDataSize: | 306688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2723 |
| OSVersion: | 5 |
| ImageVersion: | 5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.71.1015.0 |
| ProductVersionNumber: | 4.71.1015.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.71.1015.0 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1995 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows NT(R) Operating System |
| ProductVersion: | 4.71.1015.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jul-1997 11:48:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.71.1015.0 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1995 |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows NT(R) Operating System |
| ProductVersion: | 4.71.1015.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Jul-1997 11:48:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 739 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008E48 | 0x00009000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48415 |
.data | 0x0000A000 | 0x00001C0C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0991 |
.rsrc | 0x0000C000 | 0x0004B000 | 0x0004AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88927 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41506 | 1000 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
66 | 1.7646 | 64 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.27164 | 1546 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.30764 | 1524 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
82 | 3.24912 | 792 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.26481 | 1272 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.1621 | 1316 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
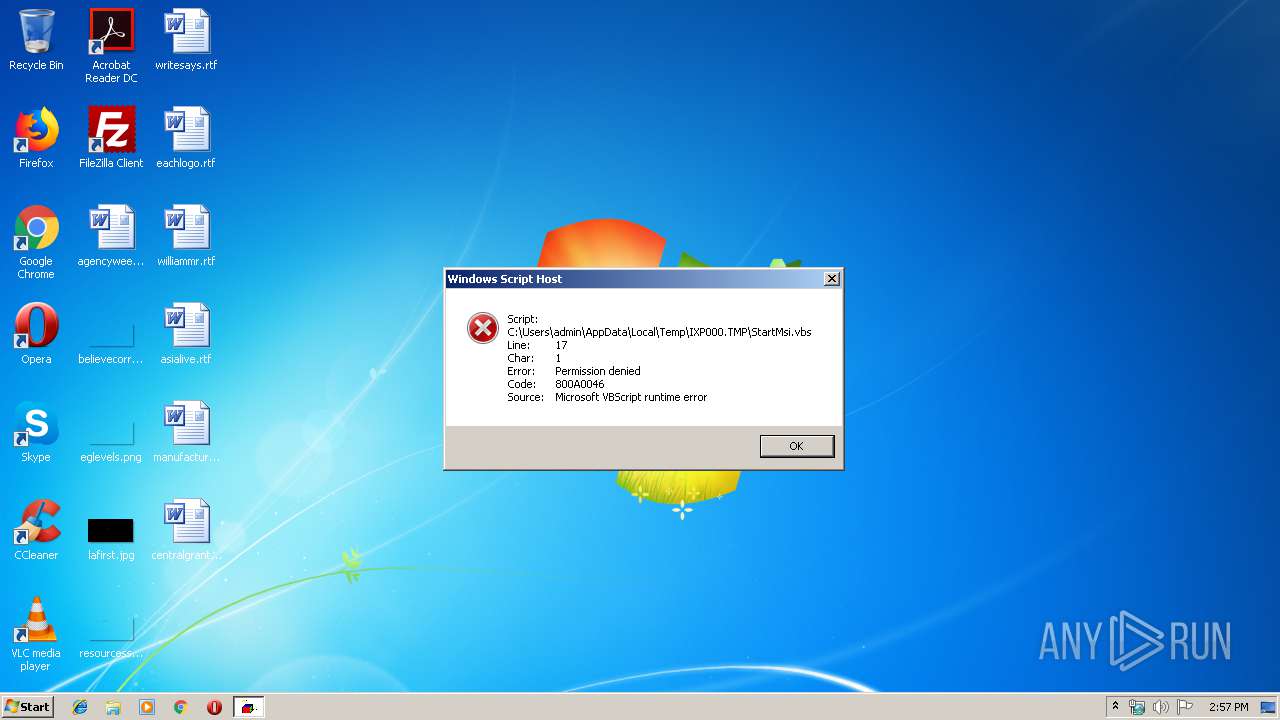
| 848 | wscript StartMsi.vbs | C:\Windows\system32\wscript.exe | — | msicuu2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\msicuu2.exe" | C:\Users\admin\AppData\Local\Temp\msicuu2.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
Total events
17
Read events
16
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2960) msicuu2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\msicuu.exe | executable | |
MD5:06109701320FB25F00E004110676A6F2 | SHA256:5900FF42650C5588E005BEA236783F0A5542E4C062EF37DD26CF073D233D287D | |||
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\StartMsi.vbs | text | |
MD5:71659E46173F3041A062E7A6893214DD | SHA256:2CF0D207AEB3E0B06D12082010D8477E8AD3E6FDBFBFBC24C131C605630B26DD | |||
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MsiZapU.exe | executable | |
MD5:27D4BCC325306B1415A89DE550528E04 | SHA256:C8089B1734F68420E912978AC0DD29D8772B1F527D2BFFBAAA9D3FAD9F4051E5 | |||
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\readme.txt | text | |
MD5:31F061B4053A587C987096ED824EFF76 | SHA256:8D1FE9D8241D4B15E57F067C55A6D770CDAD994FEDC050AA3891E74EDCF935DA | |||
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\msicuu.msi | executable | |
MD5:3DD4DDBF695EE30EF83E5EF4E40AE3FE | SHA256:6A83D34425923CD78C56B6970E237FA70702679D1ED84C3057AC38A4BB83F90D | |||
| 2960 | msicuu2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MsiZapA.exe | executable | |
MD5:8FF91F846A078660B415D84BBA98A003 | SHA256:F5B33D62B517B354C63A3A50F1E4859A9359D9F60C6E4408179960B4C15C5BCB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report