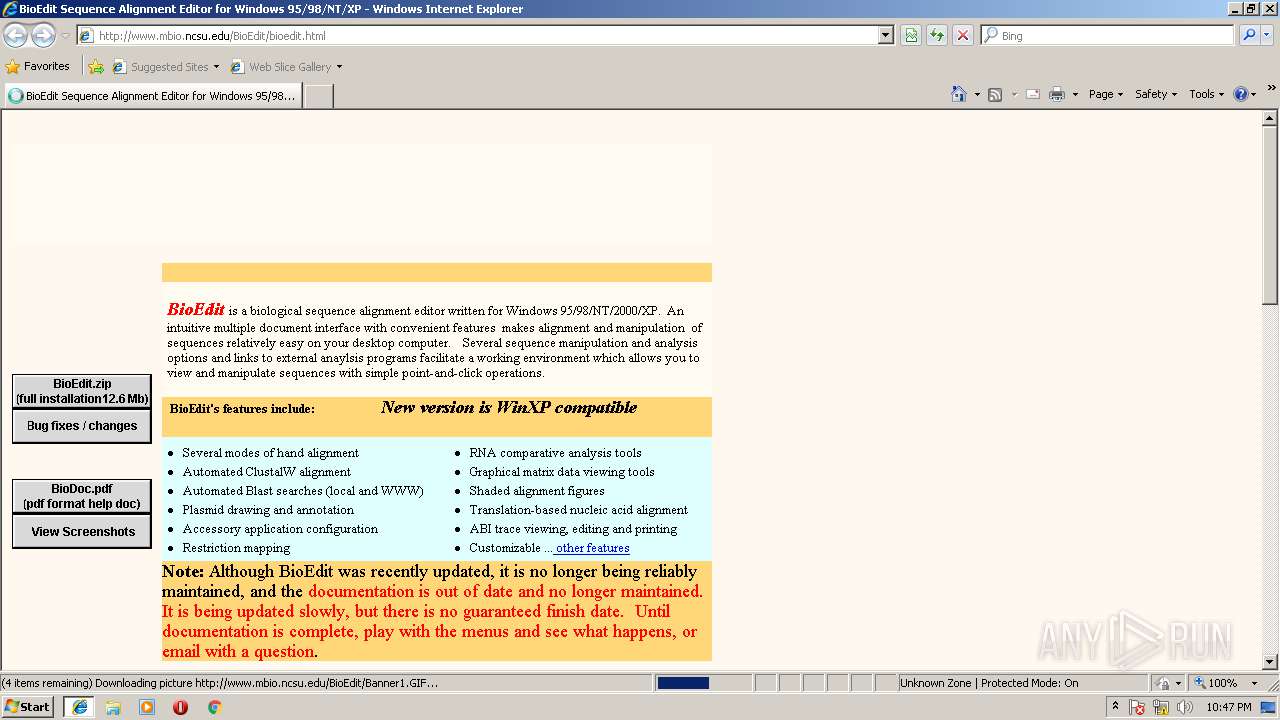
| URL: | http://www.mbio.ncsu.edu/BioEdit/bioedit.html |
| Full analysis: | https://app.any.run/tasks/a36ec5e0-bcda-4f8f-9265-d89c74695d18 |
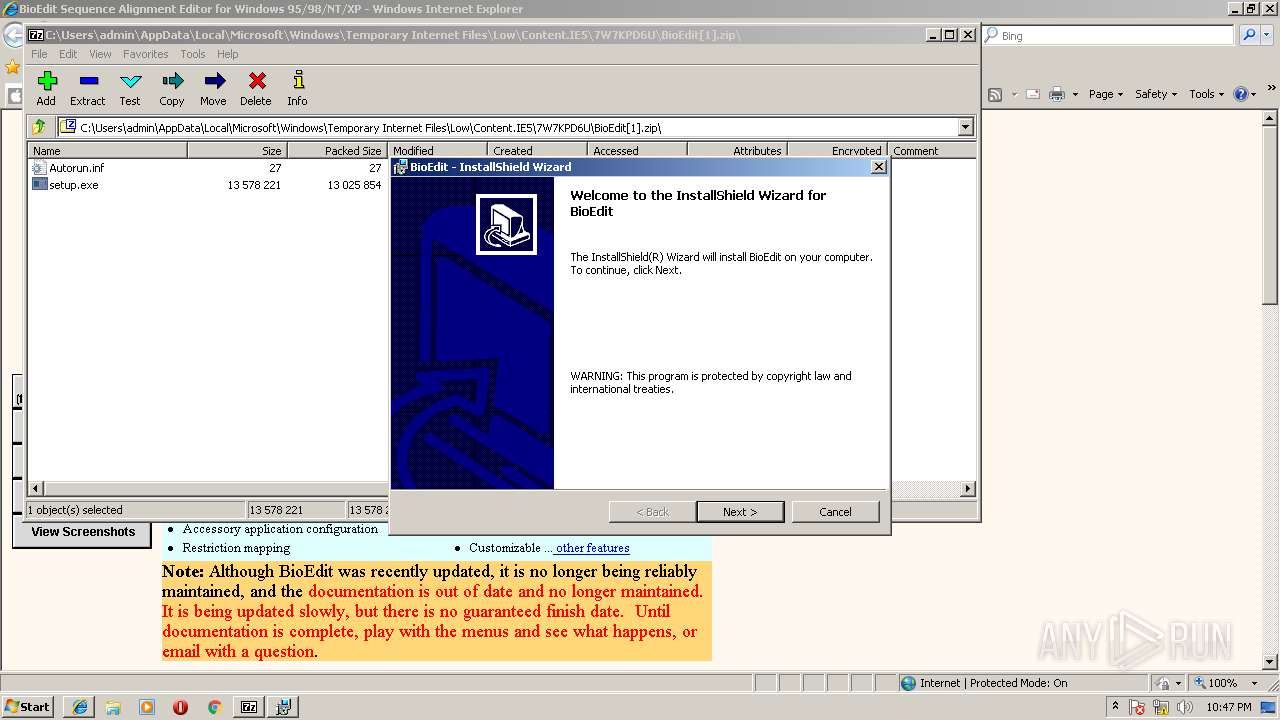
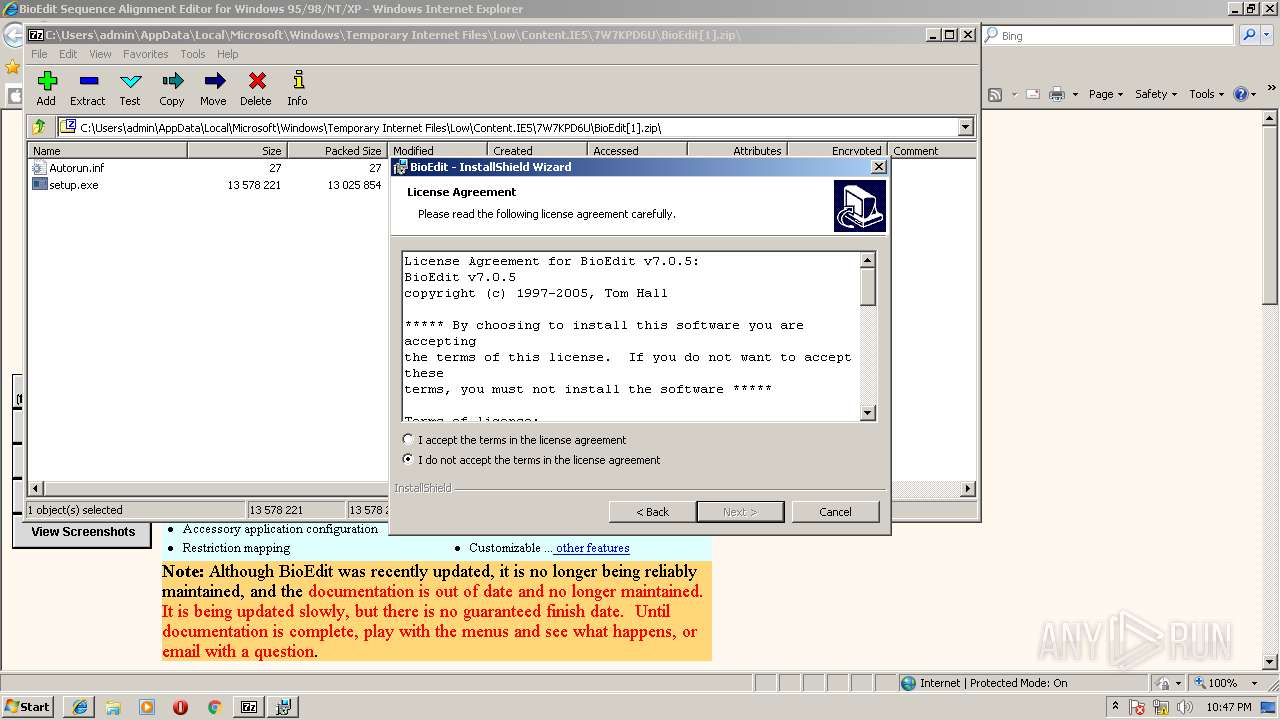
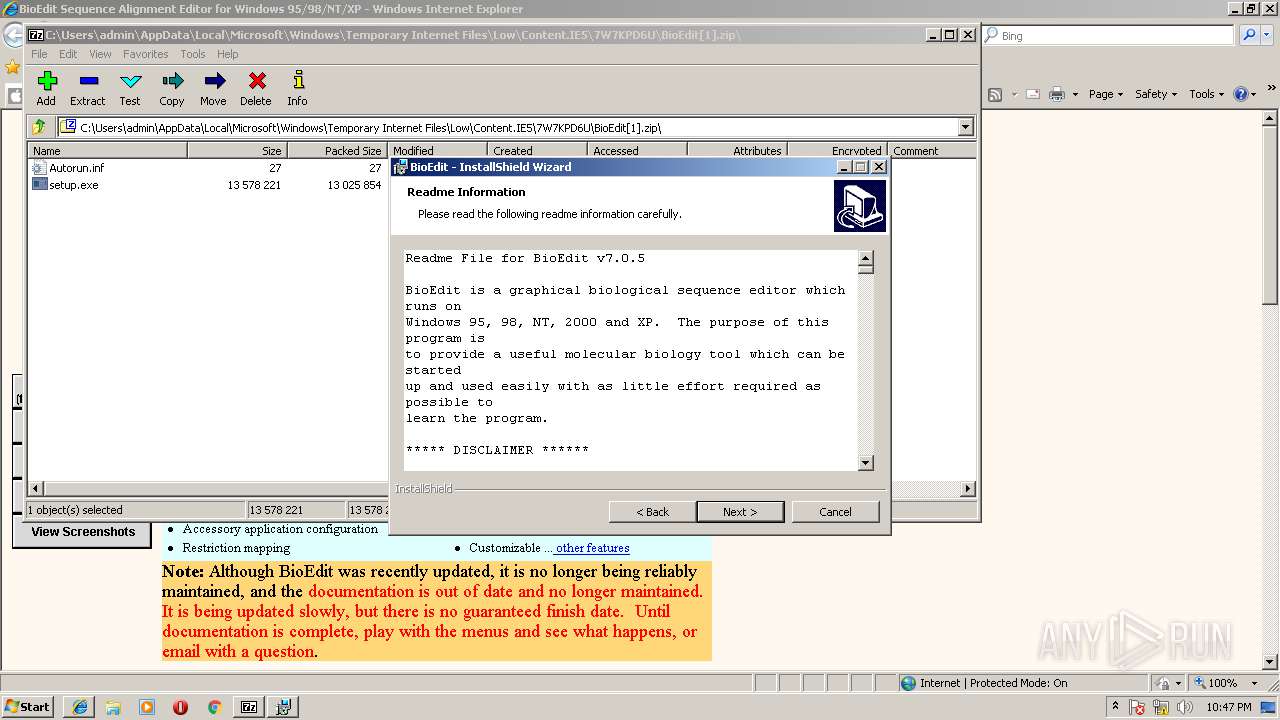
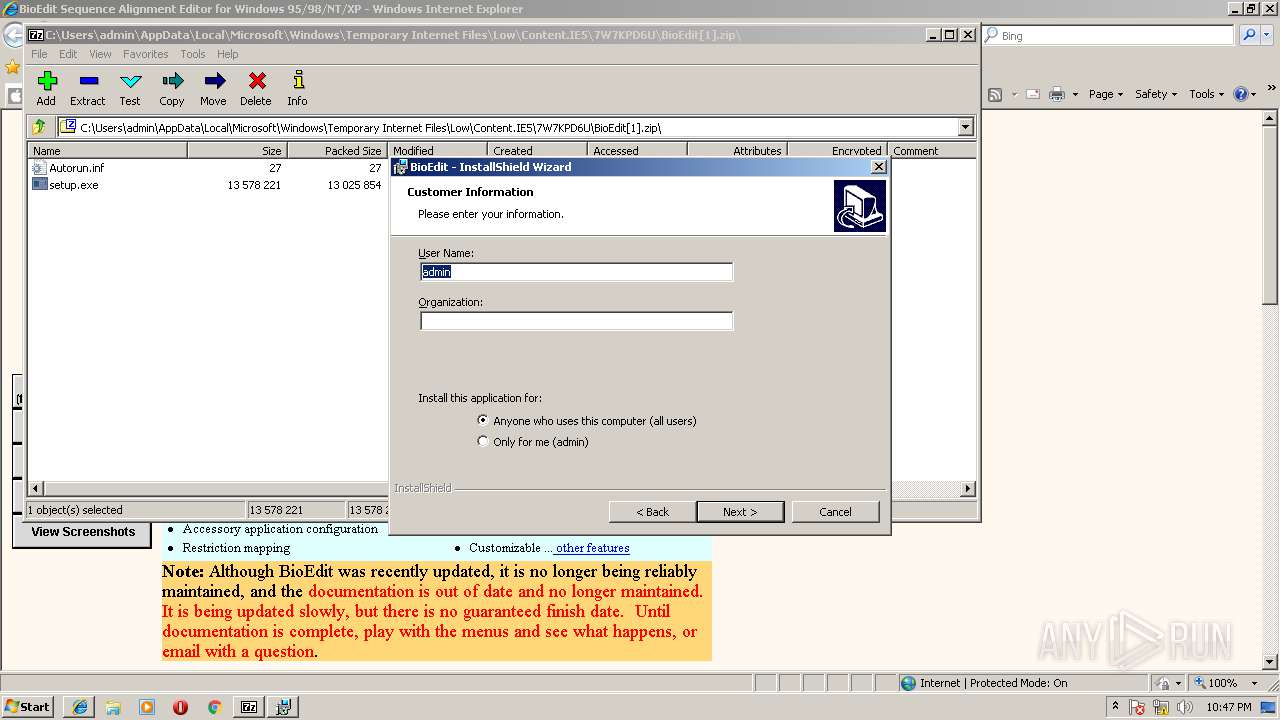
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2018, 21:46:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5B99D803E4863529CB8C390804A026EF |
| SHA1: | 3EE25BC012174A8AAF6353B9AFE29760D54E9CAA |
| SHA256: | 08543430A997588582AE40EE92ADCED7B17B2BCE4DC59AFAC68226FCB8A18431 |
| SSDEEP: | 3:N1KJS4KLLBQ0BQw6P0:Cc4QFQ488 |
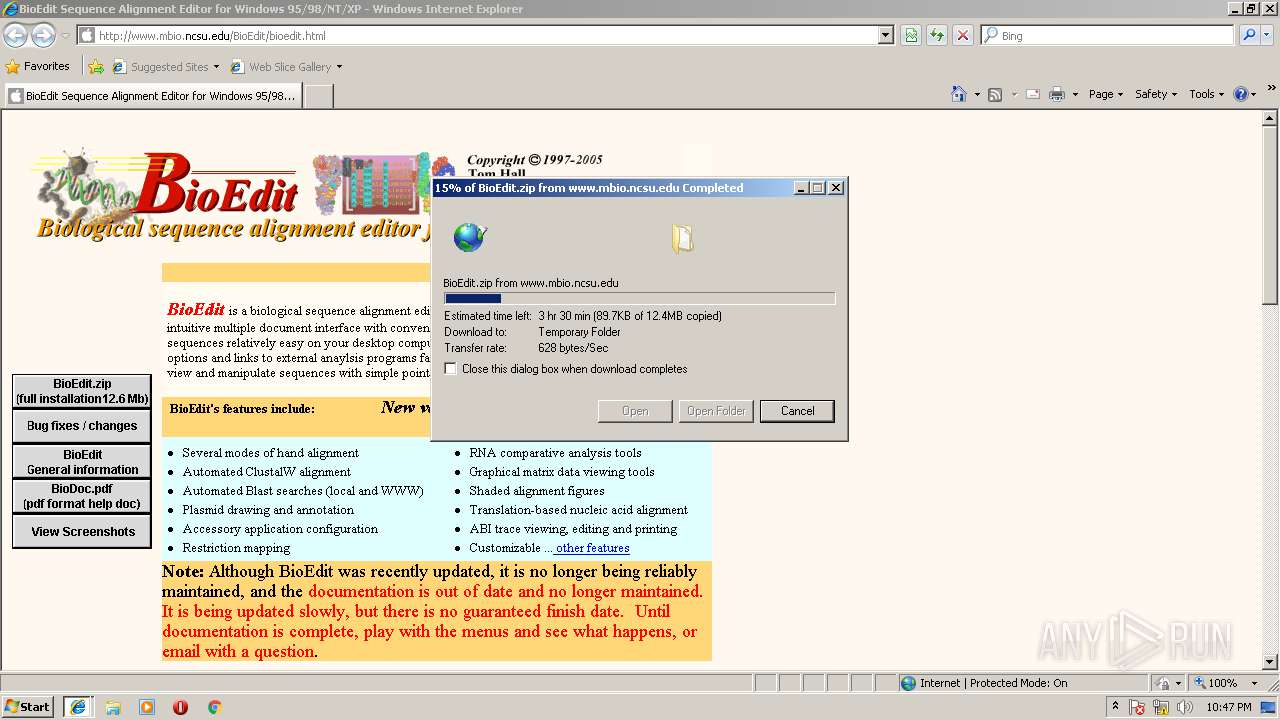
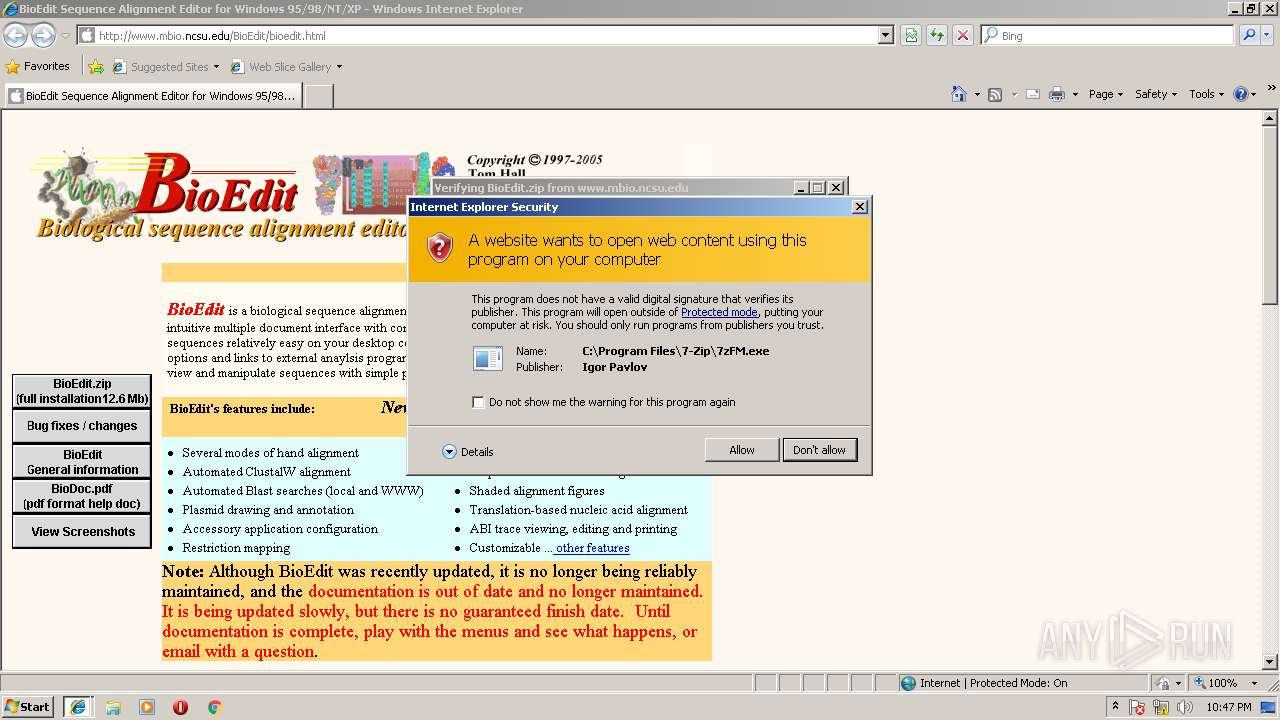
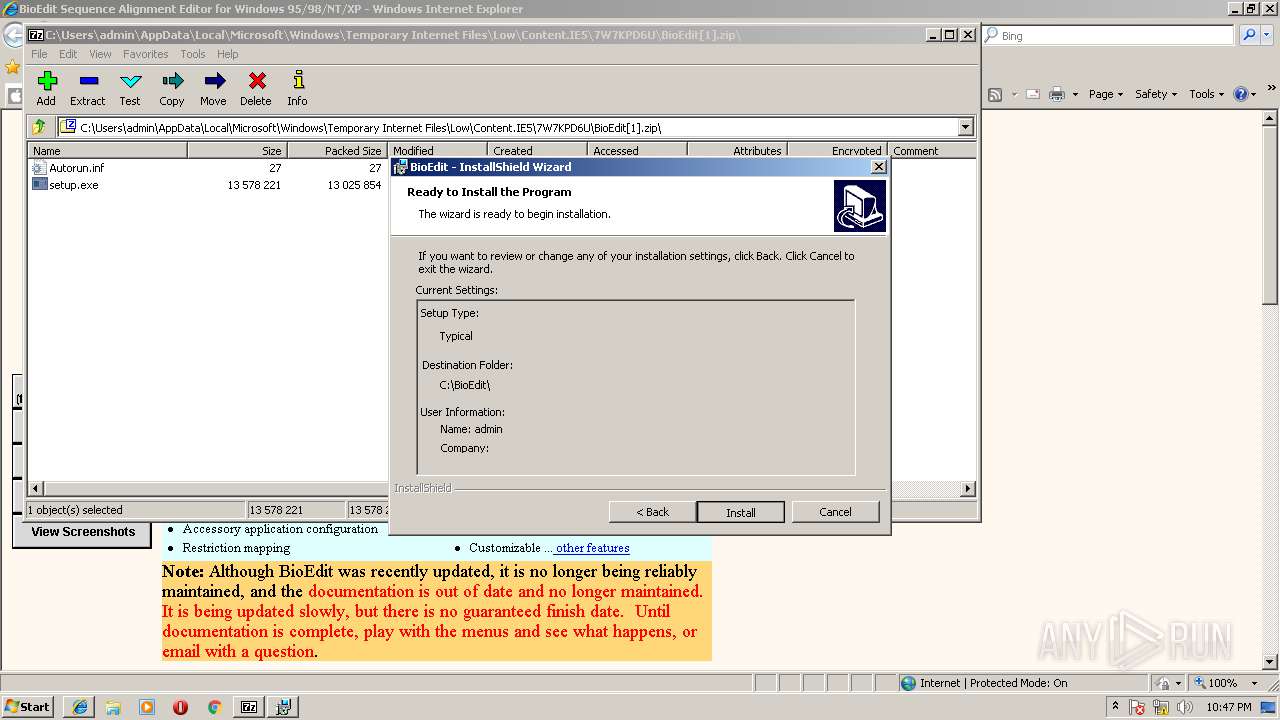
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 3092)
- setup.exe (PID: 2096)
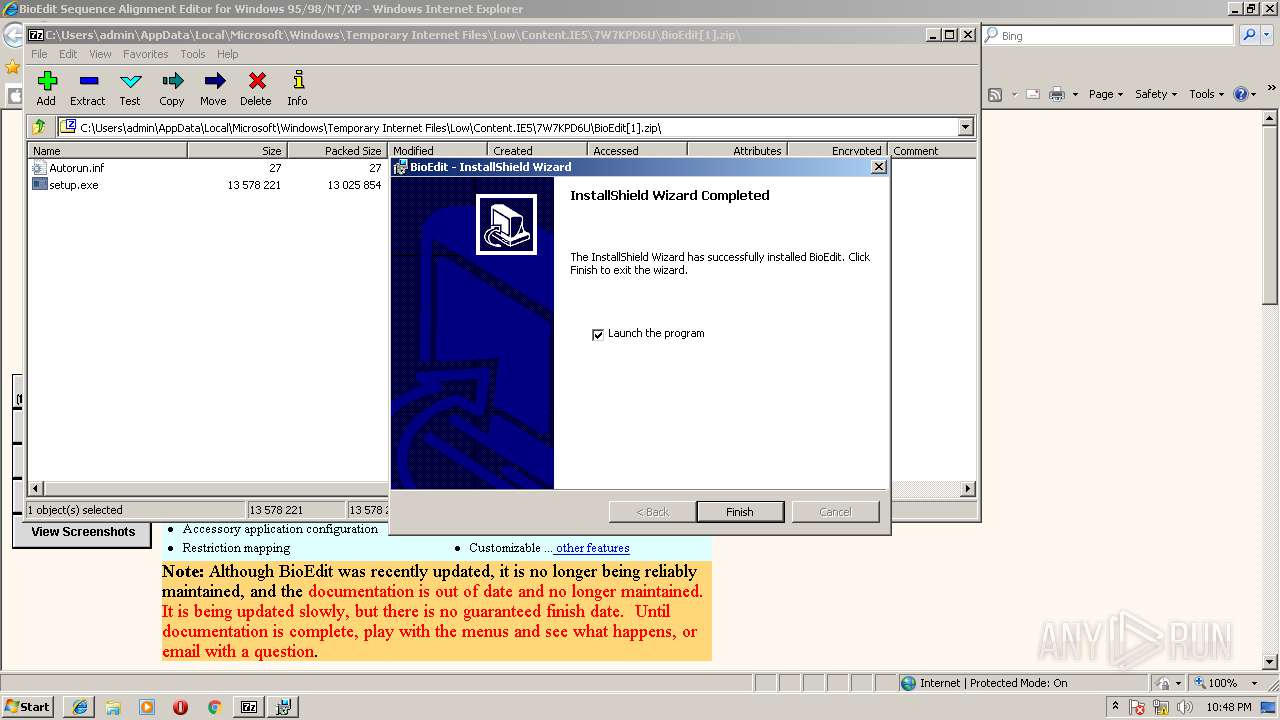
- BioEdit.exe (PID: 2180)
SUSPICIOUS
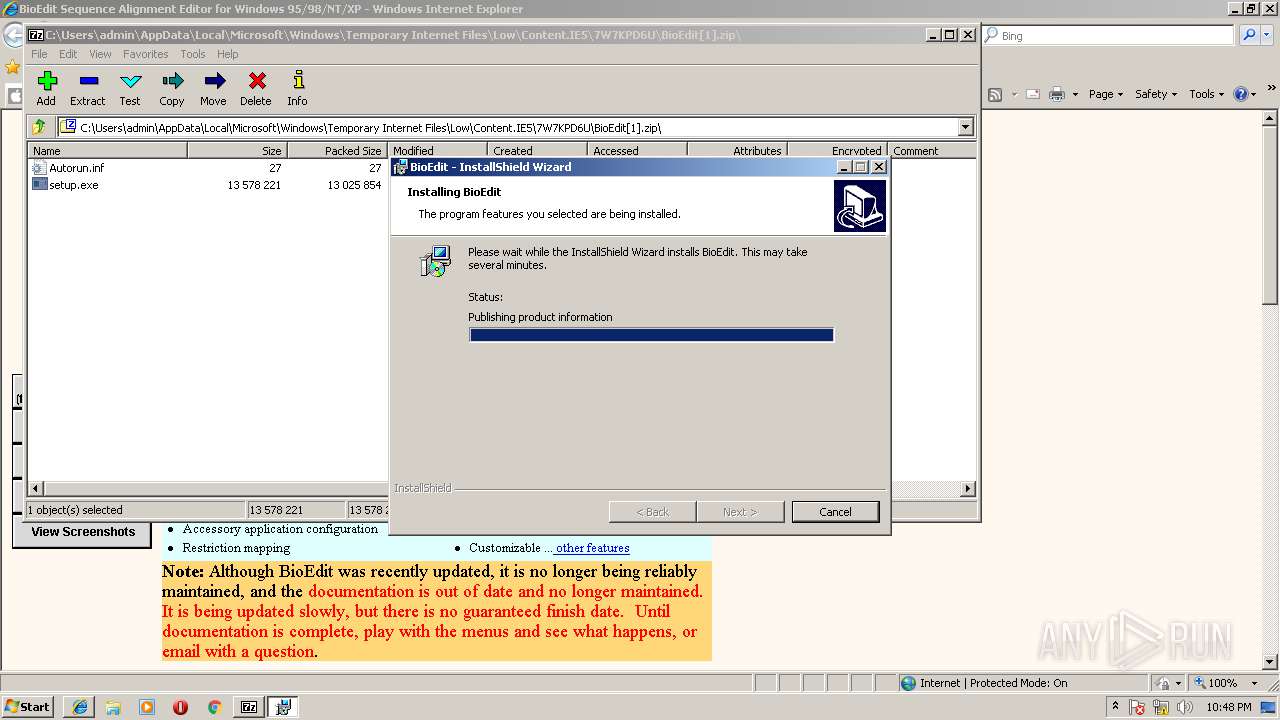
Starts Microsoft Installer
- setup.exe (PID: 2096)
Executable content was dropped or overwritten
- 7zFM.exe (PID: 3560)
- msiexec.exe (PID: 1516)
- MSIEXEC.EXE (PID: 3488)
Modifies the open verb of a shell class
- msiexec.exe (PID: 1516)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3472)
- iexplore.exe (PID: 3112)
Reads internet explorer settings
- iexplore.exe (PID: 3472)
Changes internet zones settings
- iexplore.exe (PID: 3112)
Creates files in the user directory
- iexplore.exe (PID: 3472)
- iexplore.exe (PID: 3112)
Dropped object may contain URL's
- iexplore.exe (PID: 3472)
- iexplore.exe (PID: 3112)
- msiexec.exe (PID: 1516)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3260)
Creates or modifies windows services
- msiexec.exe (PID: 1516)
- vssvc.exe (PID: 3260)
Creates files in the program directory
- msiexec.exe (PID: 1516)
Creates a software uninstall entry
- msiexec.exe (PID: 1516)
Application launched itself
- msiexec.exe (PID: 1516)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
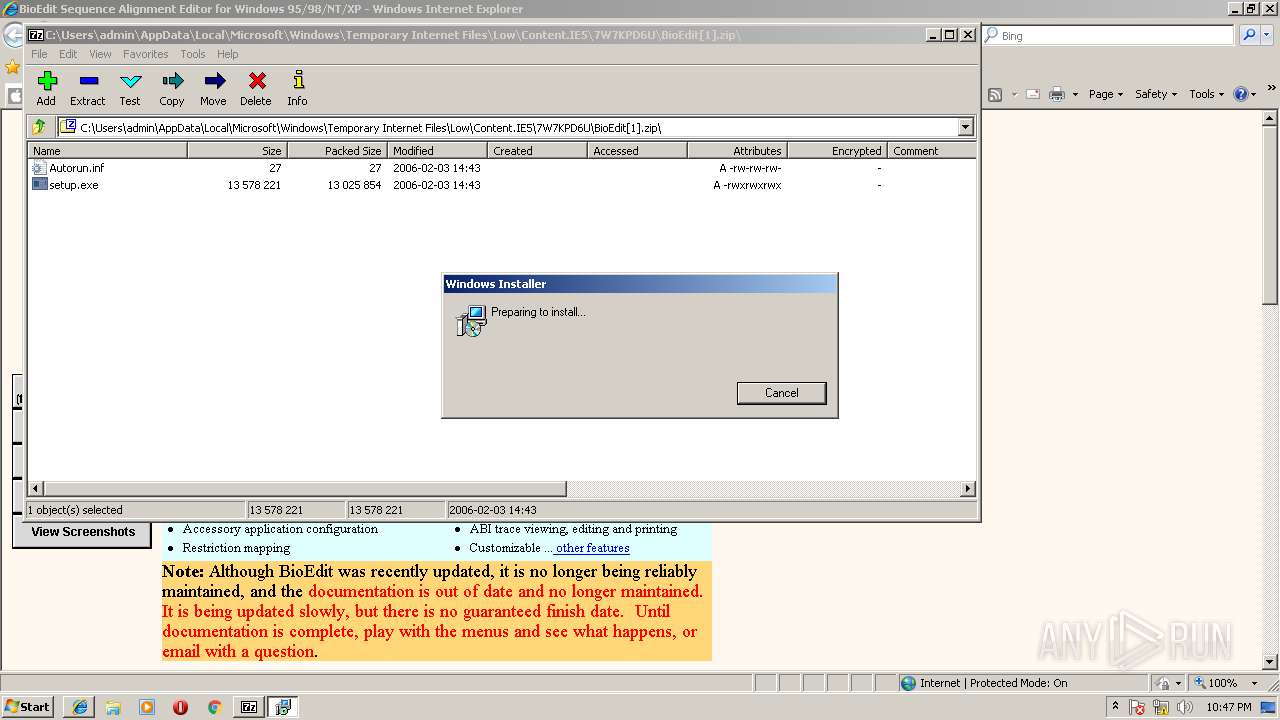
| 1516 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | C:\Windows\system32\MsiExec.exe -Embedding F586B24ED95F515EAA47B6D063DC8185 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
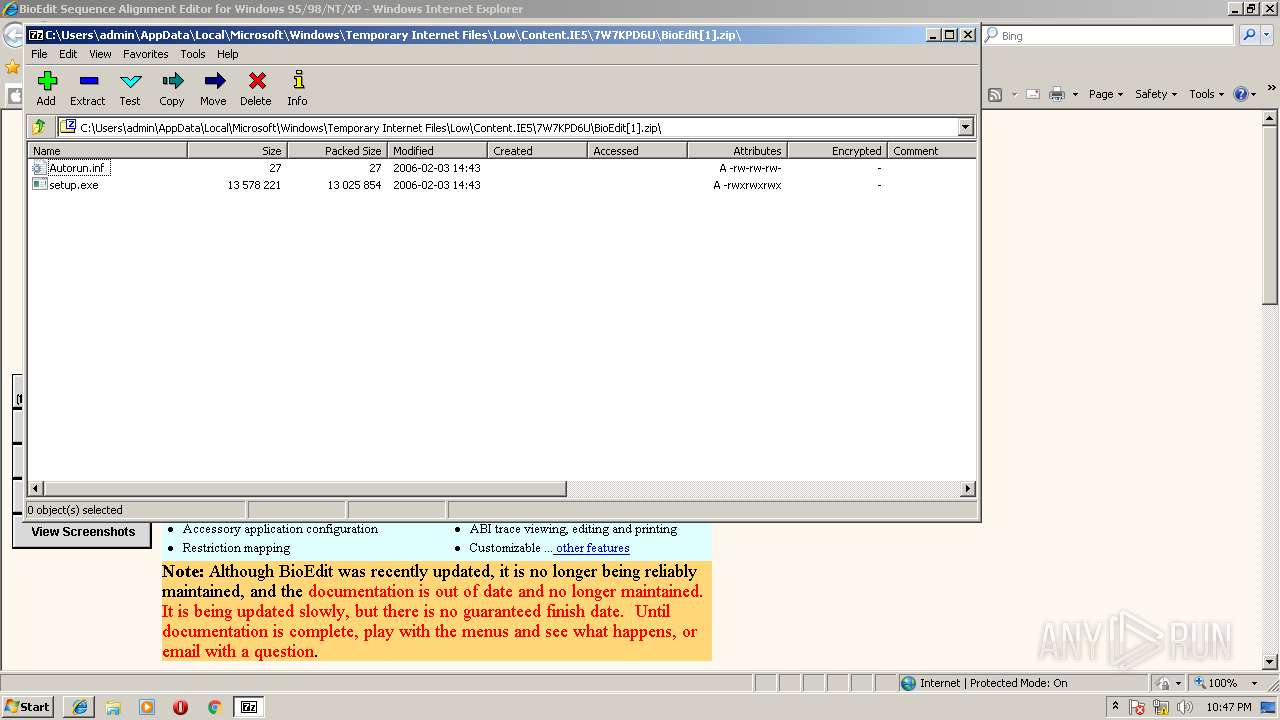
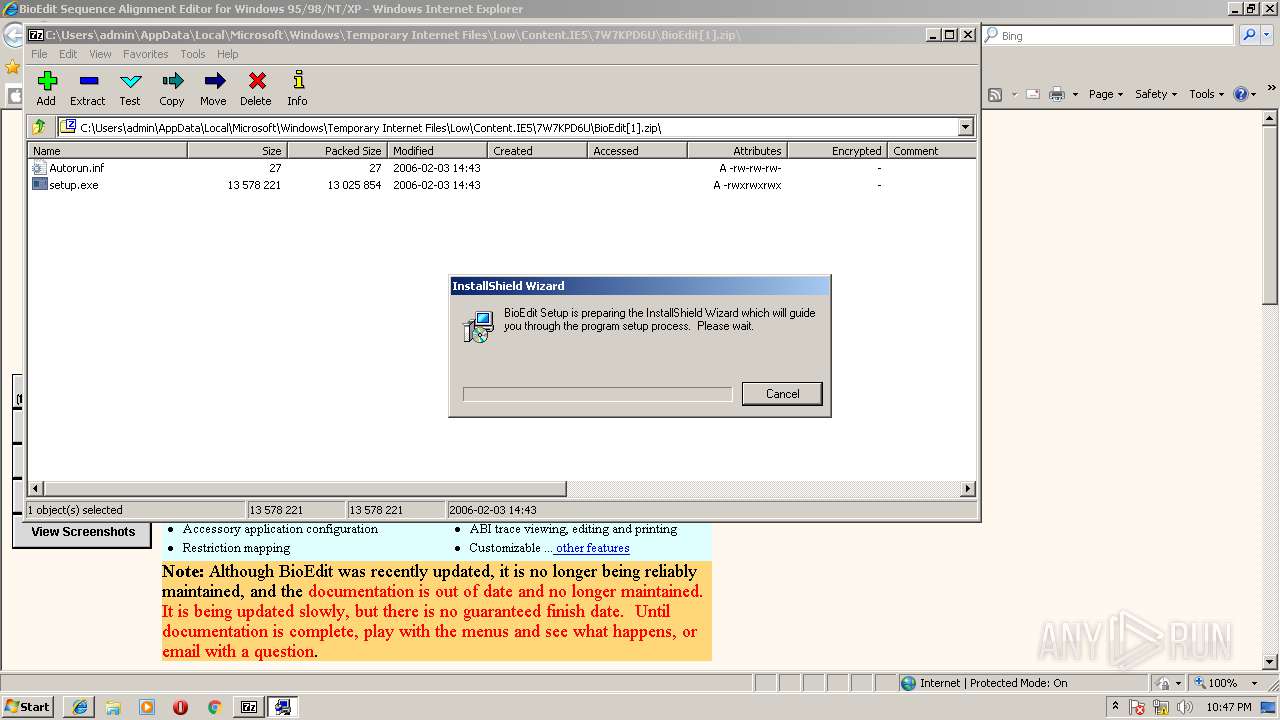
| 2096 | "C:\Users\admin\AppData\Local\Temp\7zO8EDE4354\setup.exe" | C:\Users\admin\AppData\Local\Temp\7zO8EDE4354\setup.exe | 7zFM.exe | ||||||||||||
User: admin Company: Installshield Software Corporation Integrity Level: HIGH Description: Setup Launcher Exit code: 0 Version: 3.03.19 Modules
| |||||||||||||||
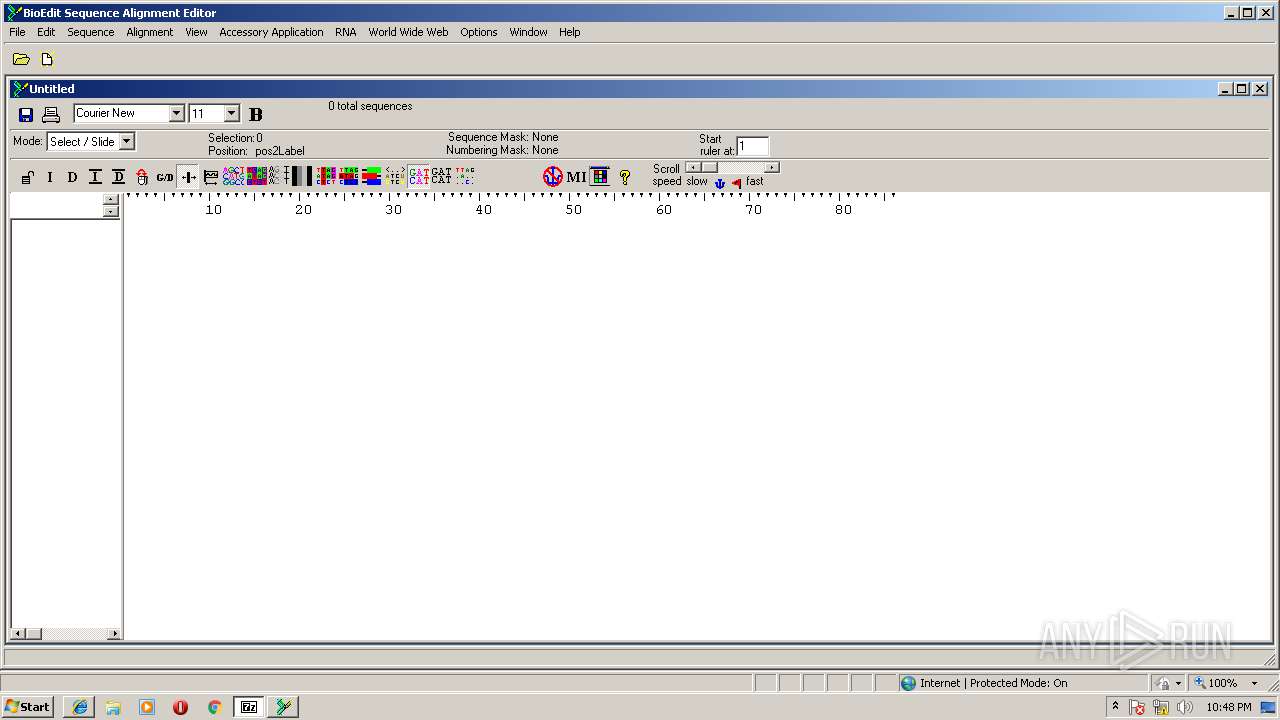
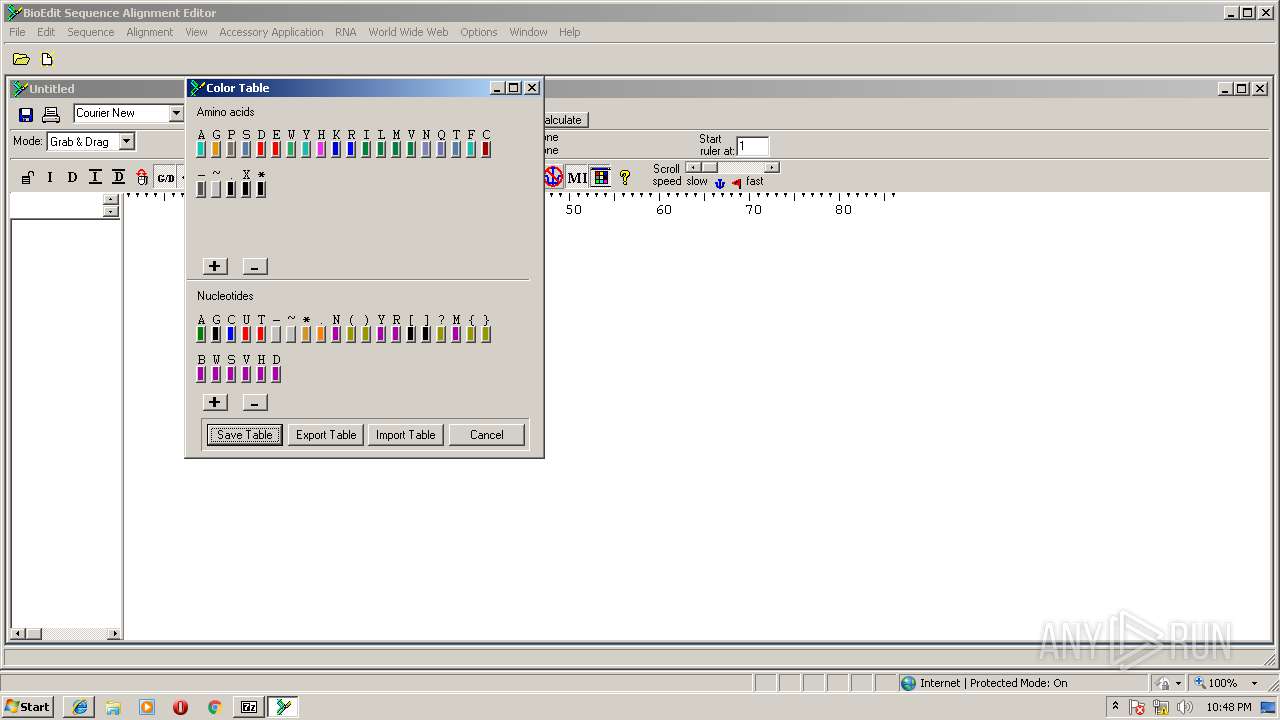
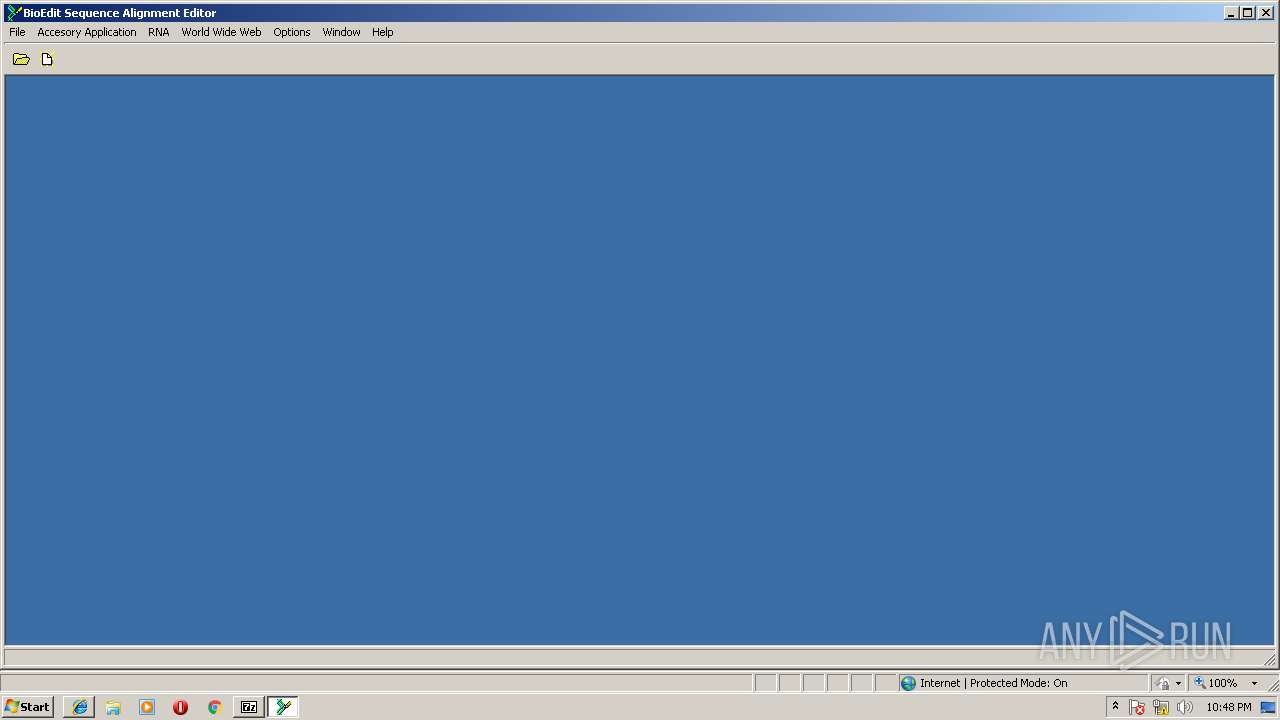
| 2180 | "C:\BioEdit\BioEdit.exe" | C:\BioEdit\BioEdit.exe | — | MsiExec.exe | |||||||||||
User: admin Integrity Level: HIGH Description: BioEdit Sequence Alignment Editor Exit code: 0 Version: 7.0.5.3 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\7zO8EDE4354\setup.exe" | C:\Users\admin\AppData\Local\Temp\7zO8EDE4354\setup.exe | — | 7zFM.exe | |||||||||||
User: admin Company: Installshield Software Corporation Integrity Level: MEDIUM Description: Setup Launcher Exit code: 3221226540 Version: 3.03.19 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3112 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\_is4DA2\BioEdit.msi" | C:\Windows\system32\MSIEXEC.EXE | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
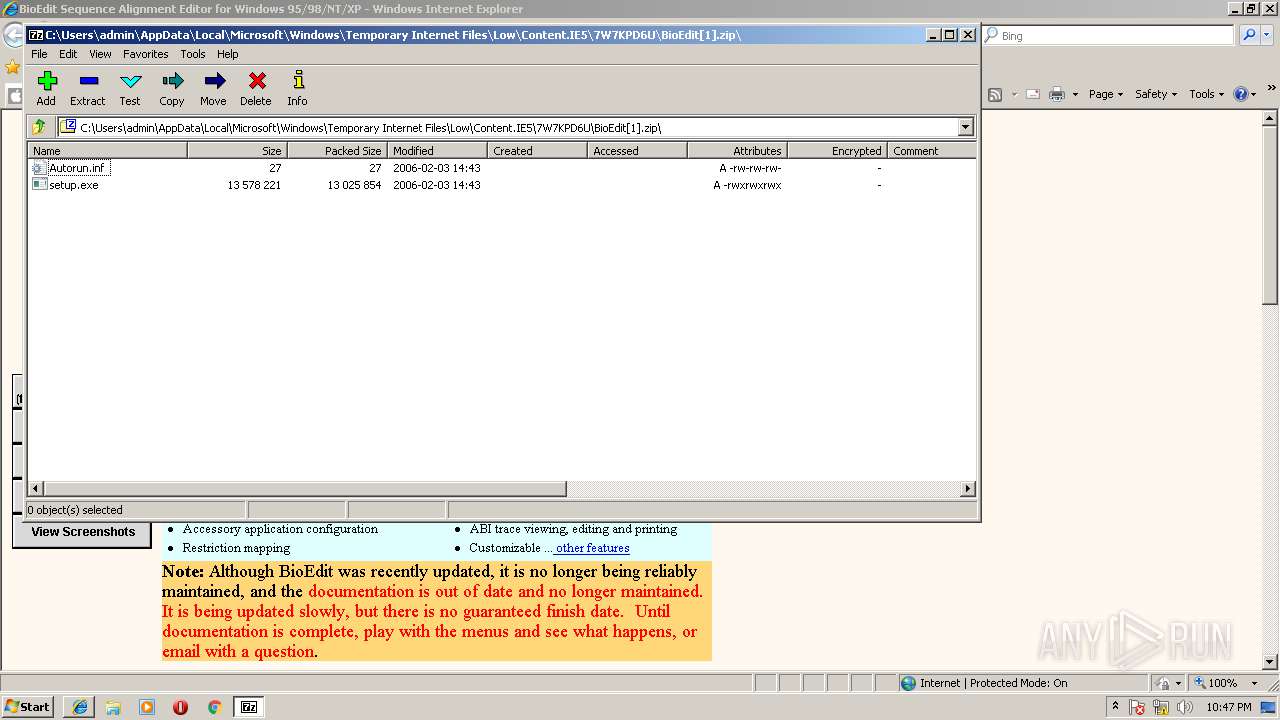
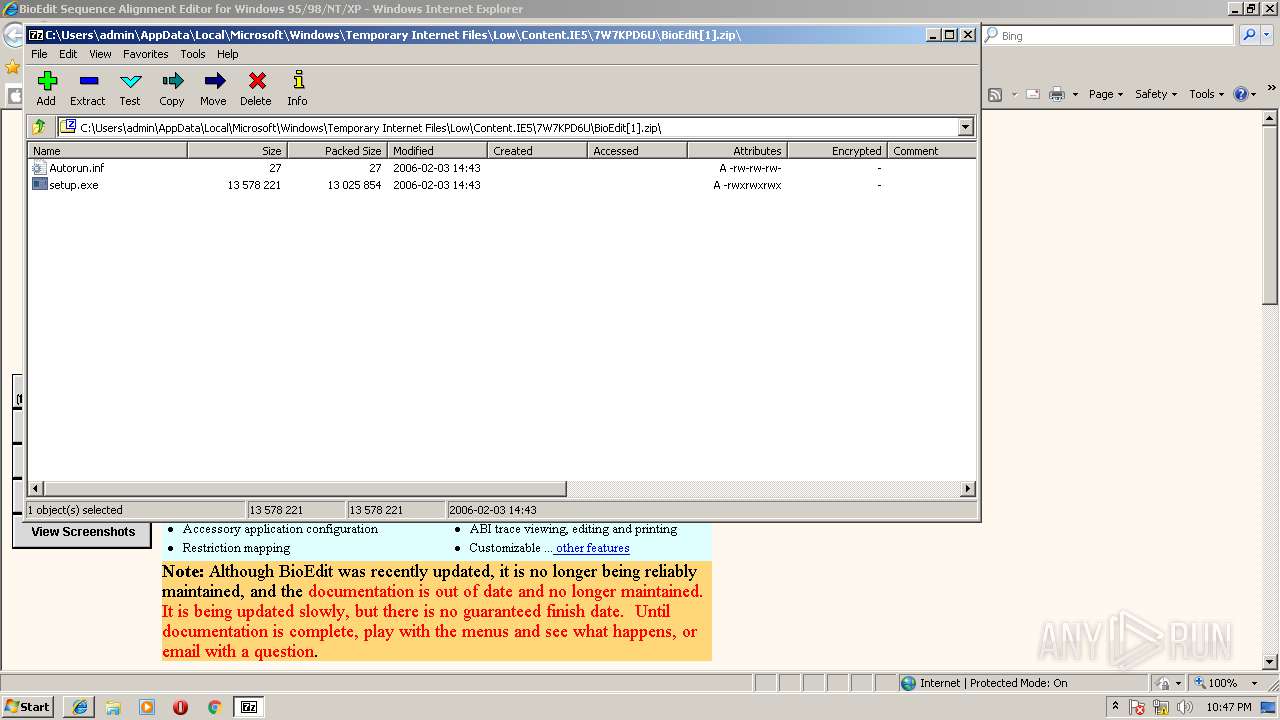
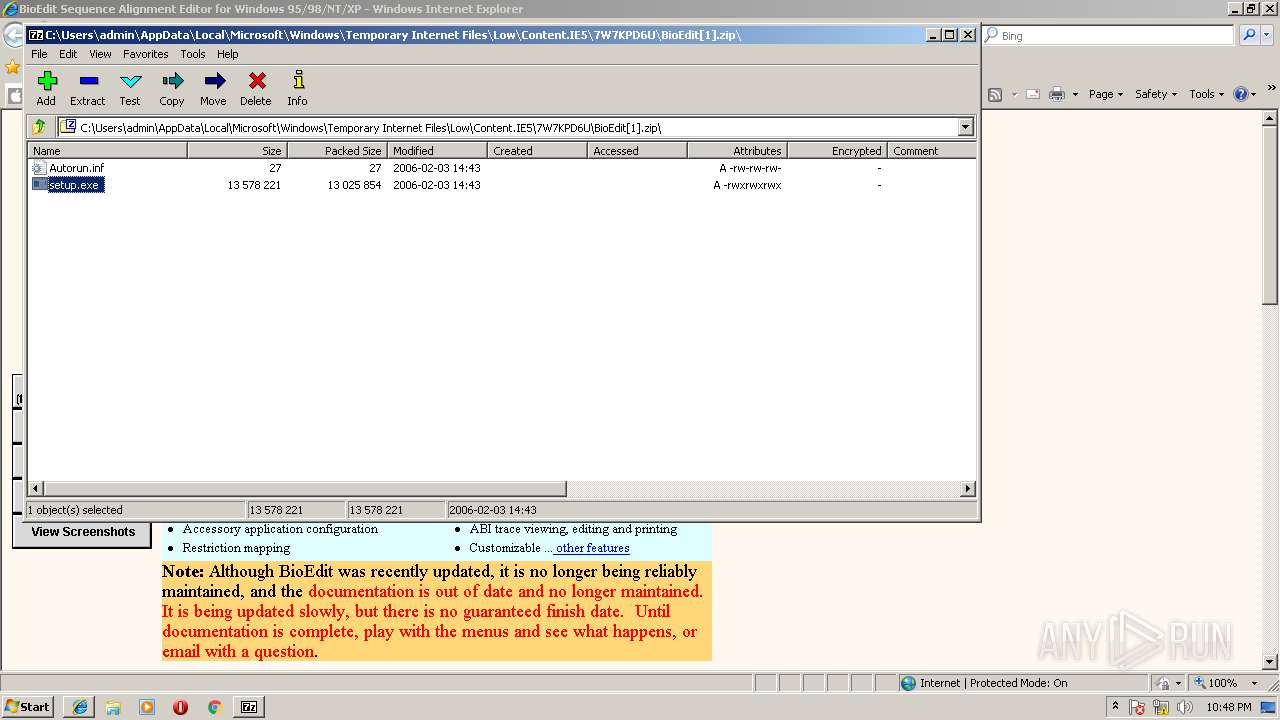
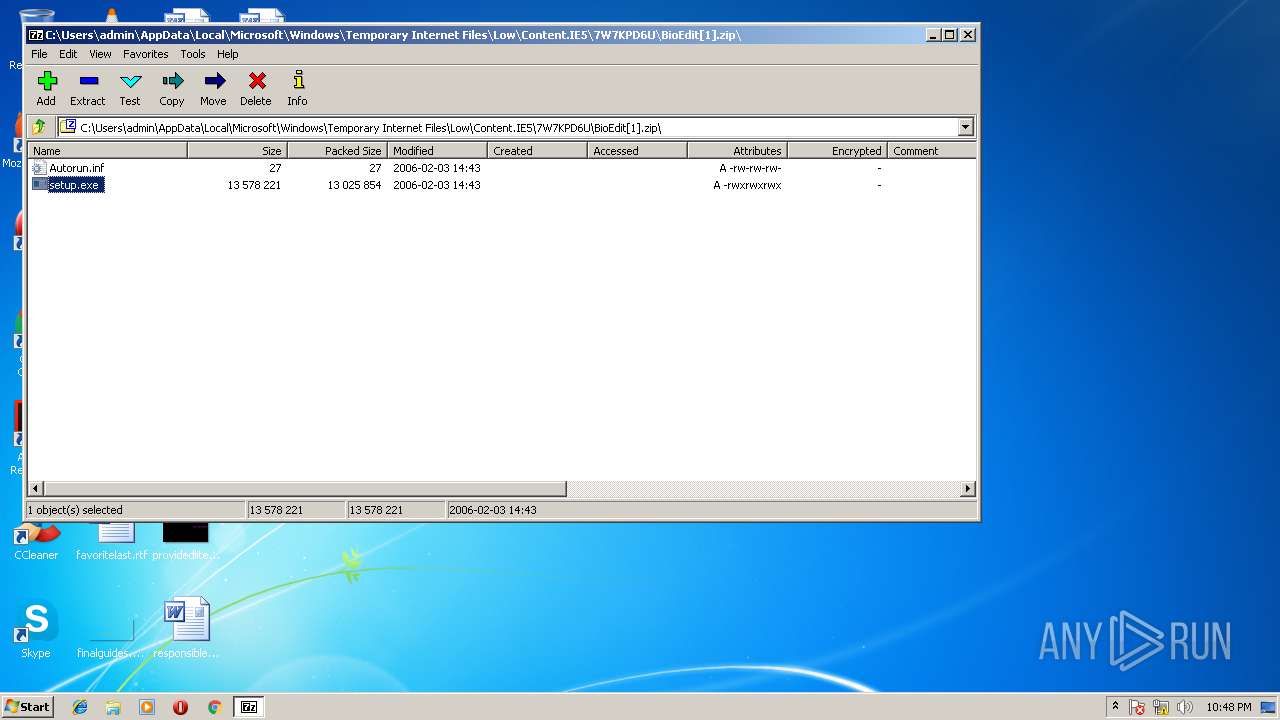
| 3560 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\BioEdit[1].zip" | C:\Program Files\7-Zip\7zFM.exe | iexplore.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
Total events
2 036
Read events
1 547
Write events
474
Delete events
15
Modification events
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {7ADFA06B-6B65-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (3112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E20706000500080015002F000400A101 | |||
Executable files
27
Suspicious files
12
Text files
82
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3112 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\upgrade1[1].gif | image | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\changes2[1].gif | image | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\full2[1].gif | image | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\info2[1].gif | image | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\bioedit[1].htm | html | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\full1[1].gif | image | |
MD5:— | SHA256:— | |||
| 3472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\pdf2[1].gif | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
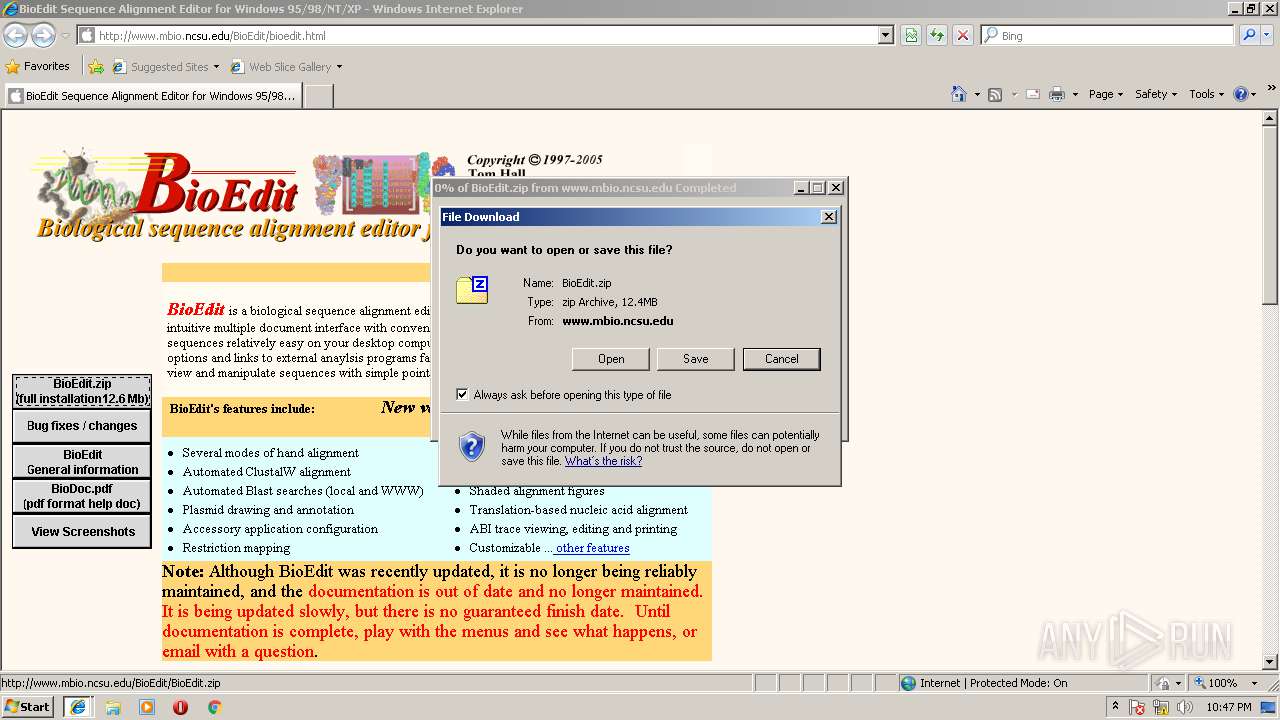
HTTP(S) requests
24
TCP/UDP connections
24
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/upgrade2.gif | US | image | 347 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/full2.gif | US | image | 1.33 Kb | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/doc2.gif | US | image | 500 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/screenShots2.gif | US | image | 410 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/screenShots1.gif | US | image | 381 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/full1.gif | US | image | 1.32 Kb | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/b_search.gif | US | image | 1.38 Kb | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/clear.GIF | US | image | 55 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/upgrade1.gif | US | image | 315 b | unknown |
3472 | iexplore.exe | GET | 200 | 152.1.106.104:80 | http://www.mbio.ncsu.edu/BioEdit/changes2.gif | US | image | 421 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3472 | iexplore.exe | 152.1.106.104:80 | www.mbio.ncsu.edu | North Carolina State University | US | unknown |
3112 | iexplore.exe | 152.1.106.104:80 | www.mbio.ncsu.edu | North Carolina State University | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.mbio.ncsu.edu |
| unknown |