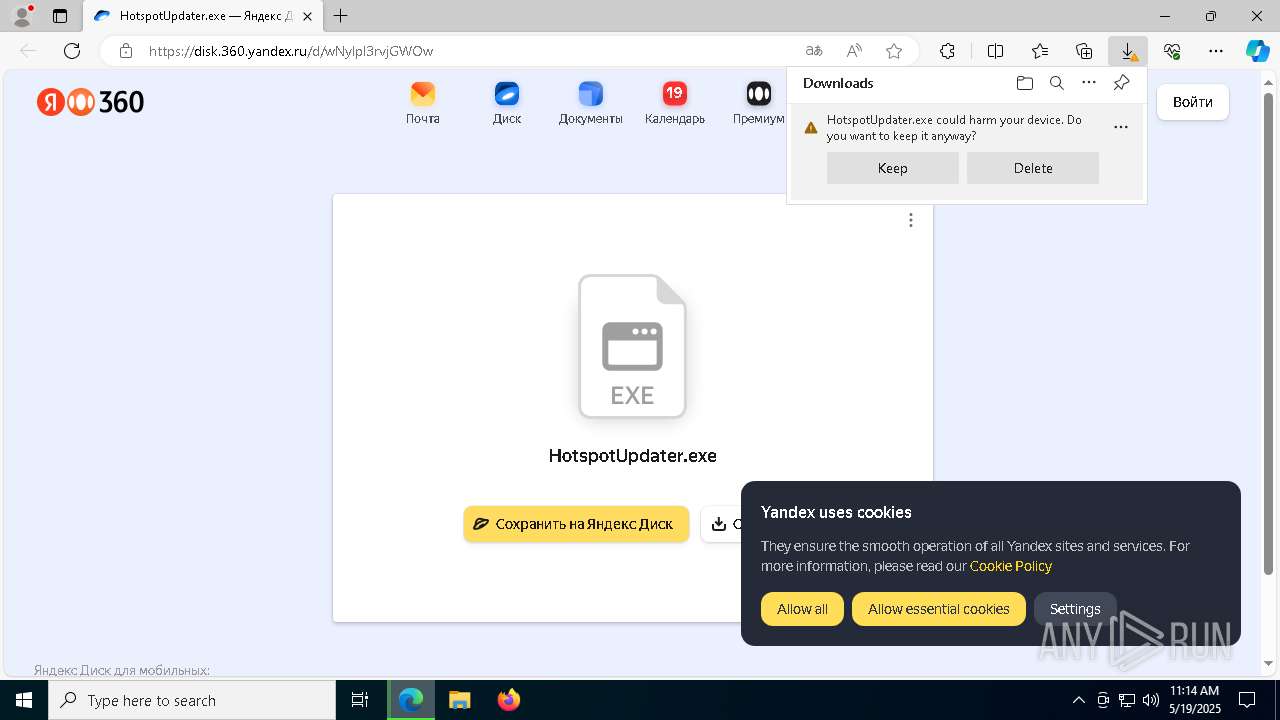
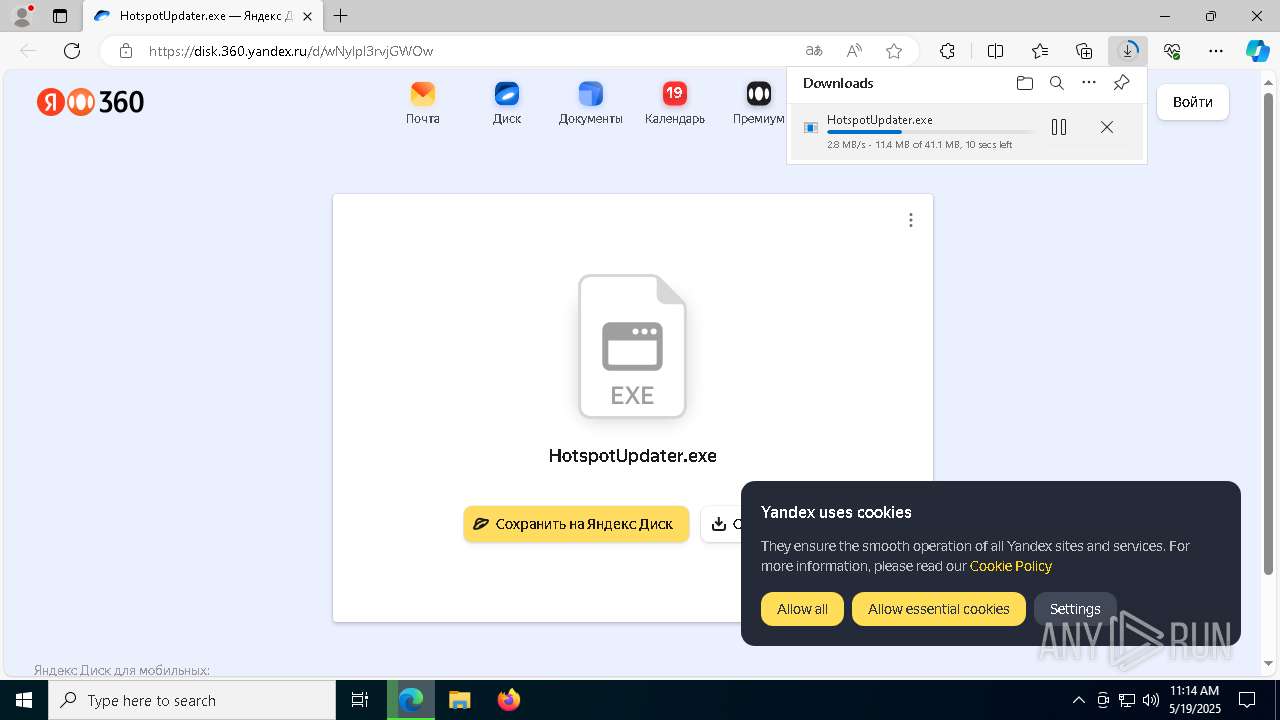
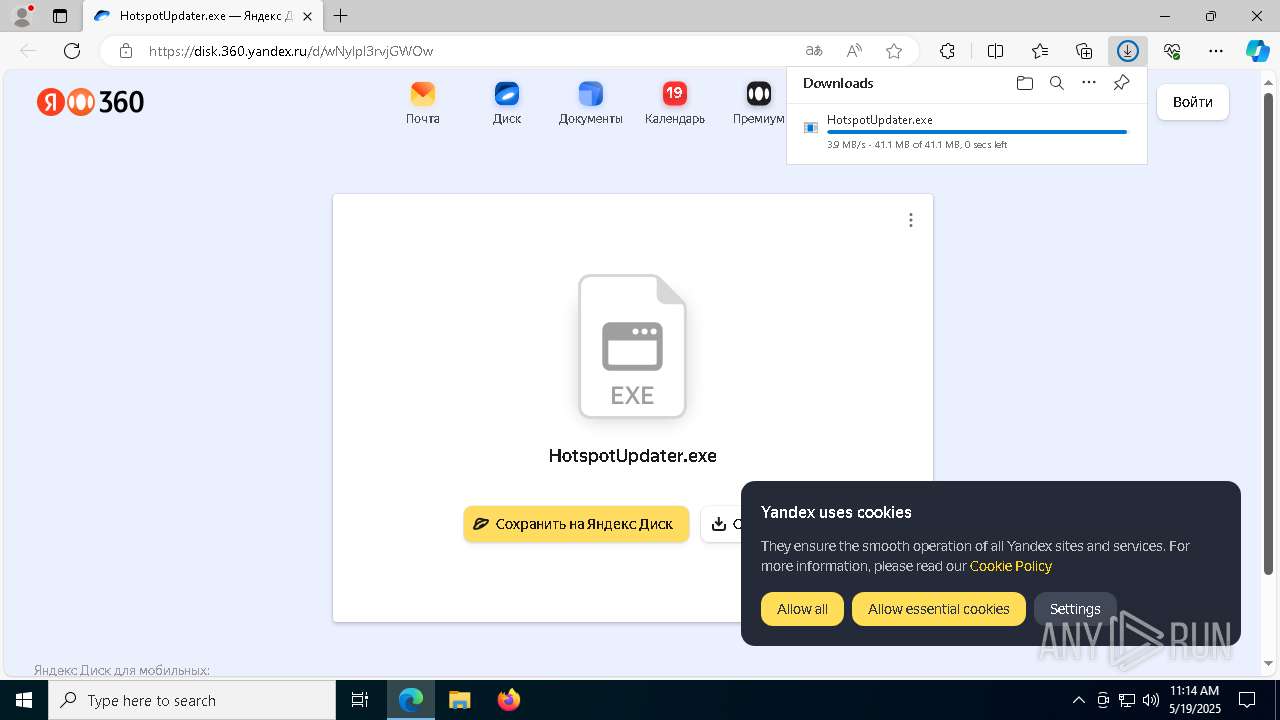
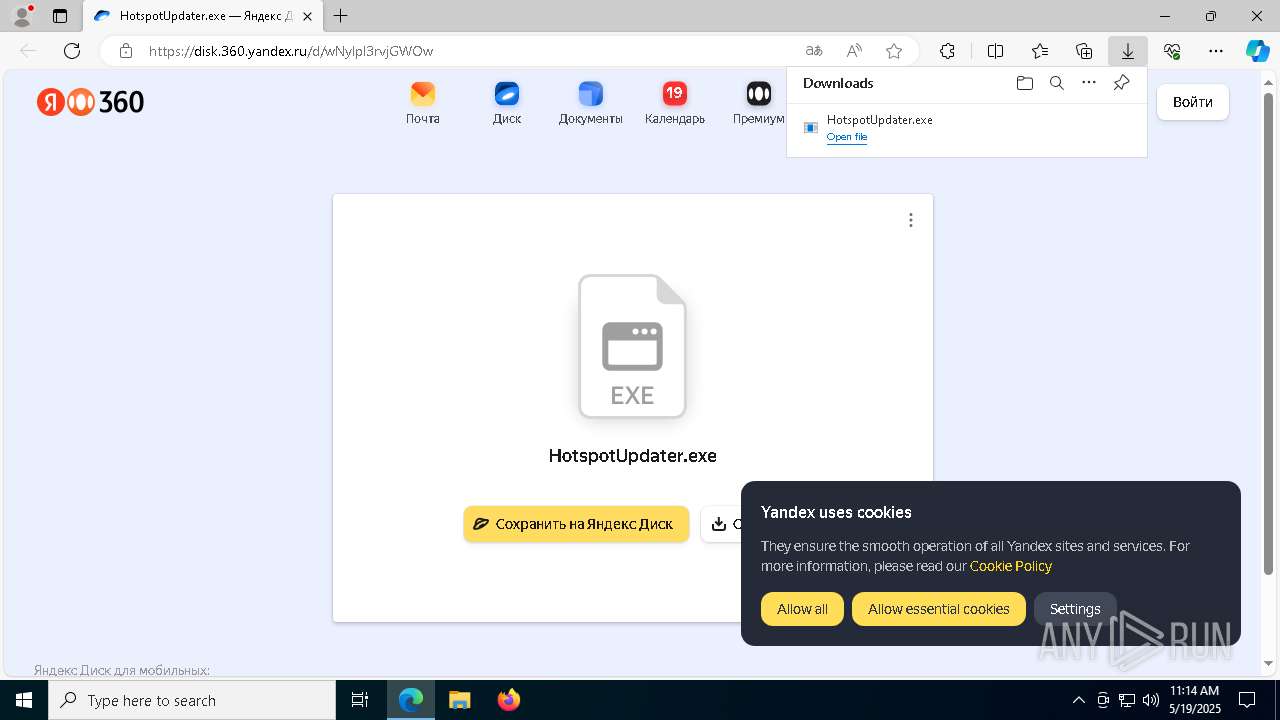
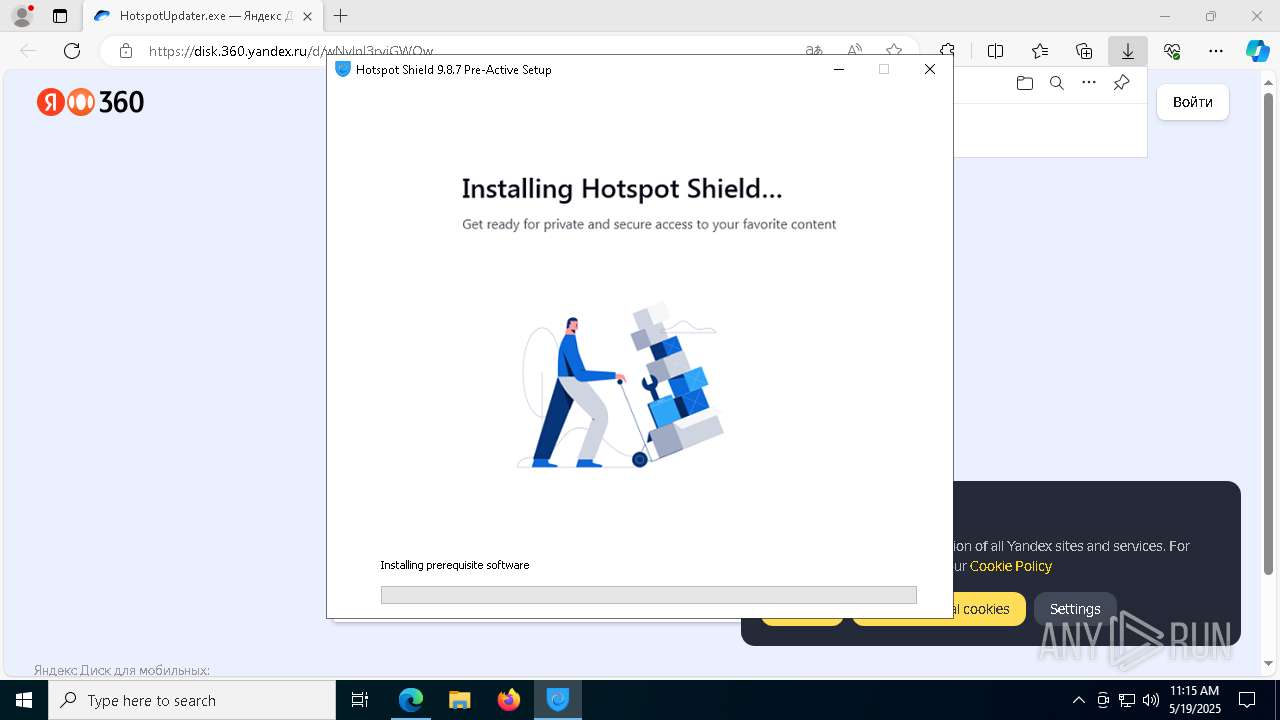
| URL: | https://disk.360.yandex.ru/d/wNylpl3rvjGWOw |
| Full analysis: | https://app.any.run/tasks/89399b1a-1f25-48f5-a234-f629ab0f6983 |
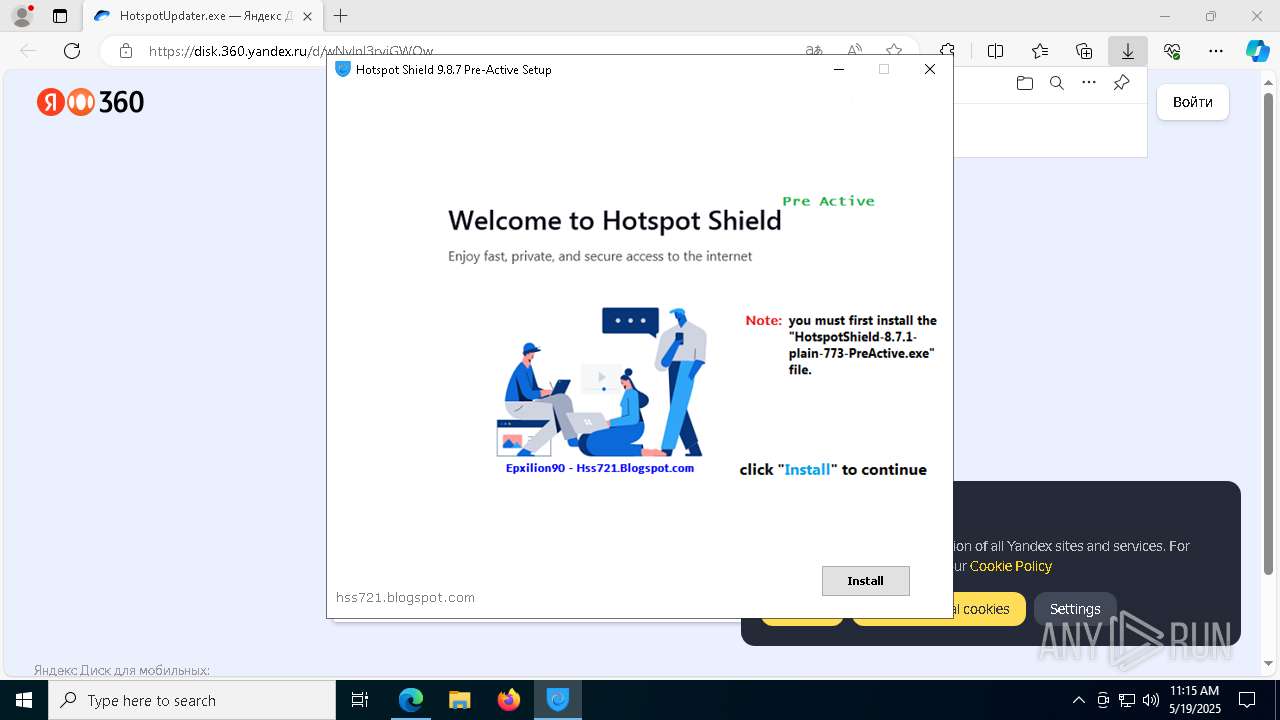
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 11:14:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 741CEC2247FAB456257954023416FAF0 |
| SHA1: | 69D72A338DFA9F76E2C71E472533427DDD4EEA86 |
| SHA256: | 085088C27DEB0F3D67DB8F5FFE63FEA9C38FF677E6B756968E57AD6742DED1C8 |
| SSDEEP: | 3:N8UsZZKDr4jWTRp:2UGZKDLTRp |
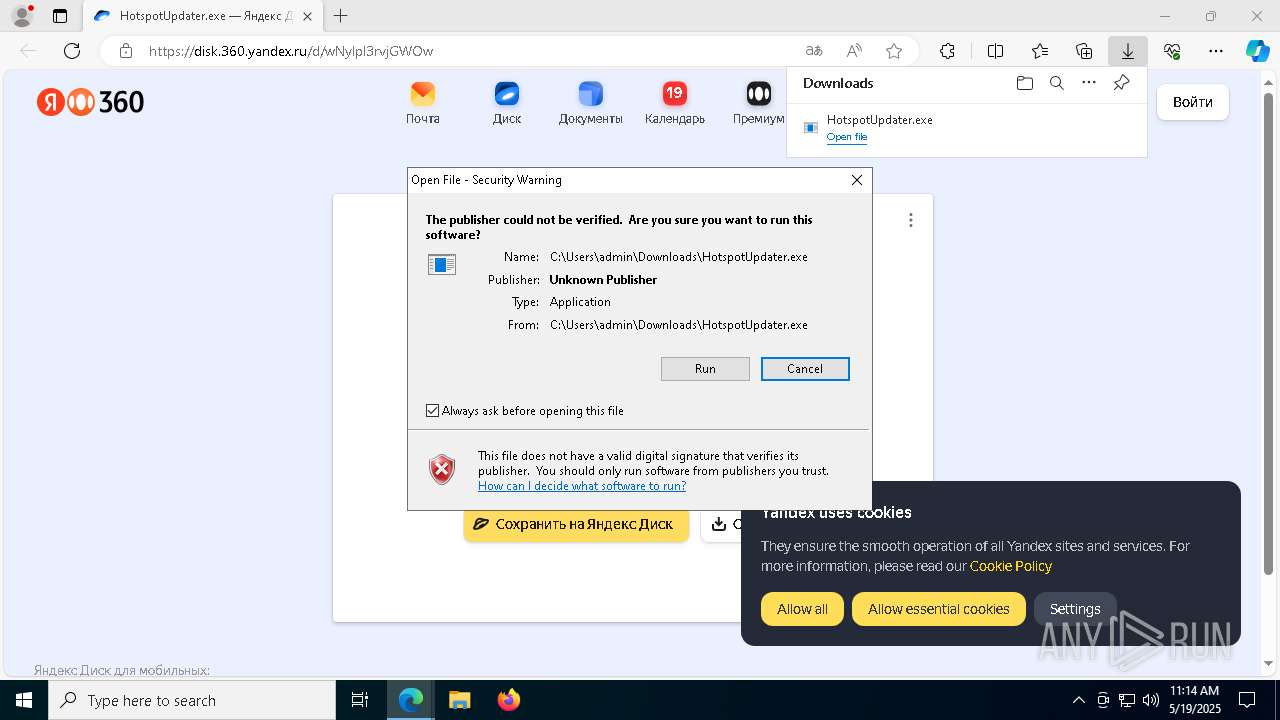
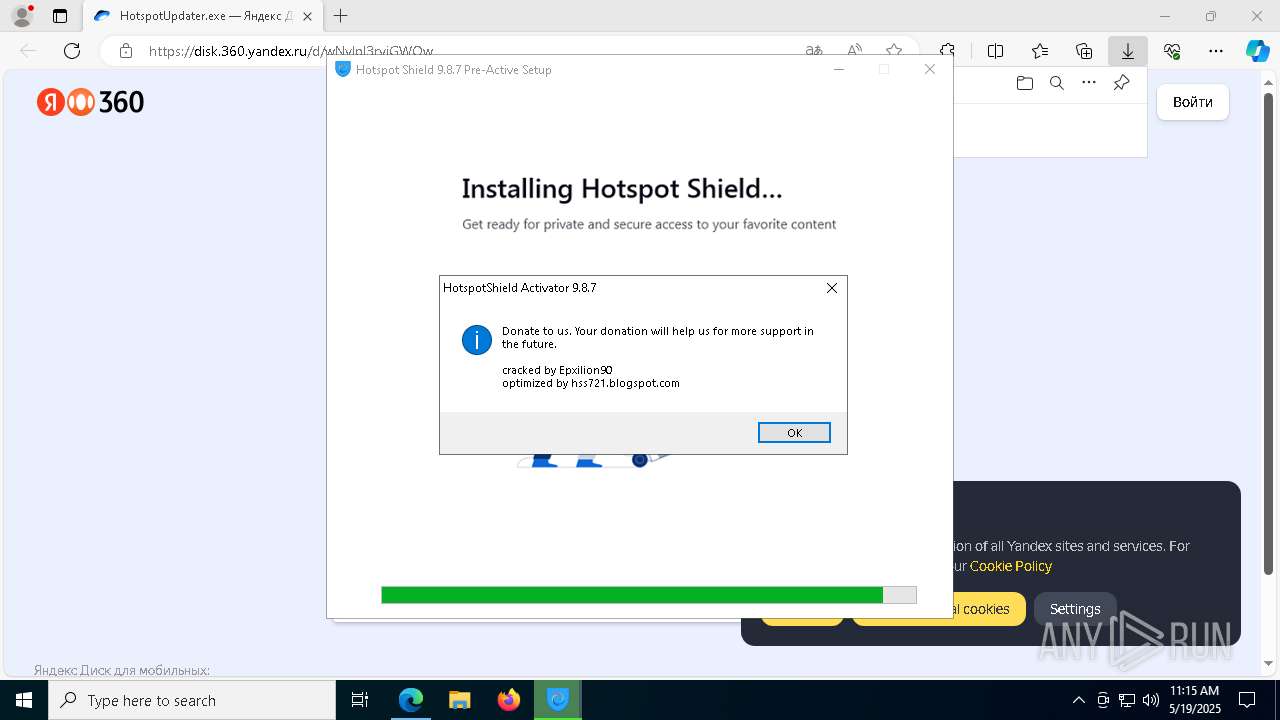
MALICIOUS
Executing a file with an untrusted certificate
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6424)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8104)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- cmw_srv.exe (PID: 8040)
- hsscp.exe (PID: 7888)
- hsscp.exe (PID: 5376)
- hsscp.exe (PID: 6108)
- hsscp.exe (PID: 5728)
Changes the autorun value in the registry
- reg.exe (PID: 6576)
XORed URL has been found (YARA)
- HotspotUpdater.exe (PID: 8060)
SUSPICIOUS
The process checks if it is being run in the virtual environment
- HotspotUpdater.exe (PID: 8060)
Reads security settings of Internet Explorer
- HotspotUpdater.exe (PID: 8060)
- msiexec.exe (PID: 5984)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tapinstall.exe (PID: 1240)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
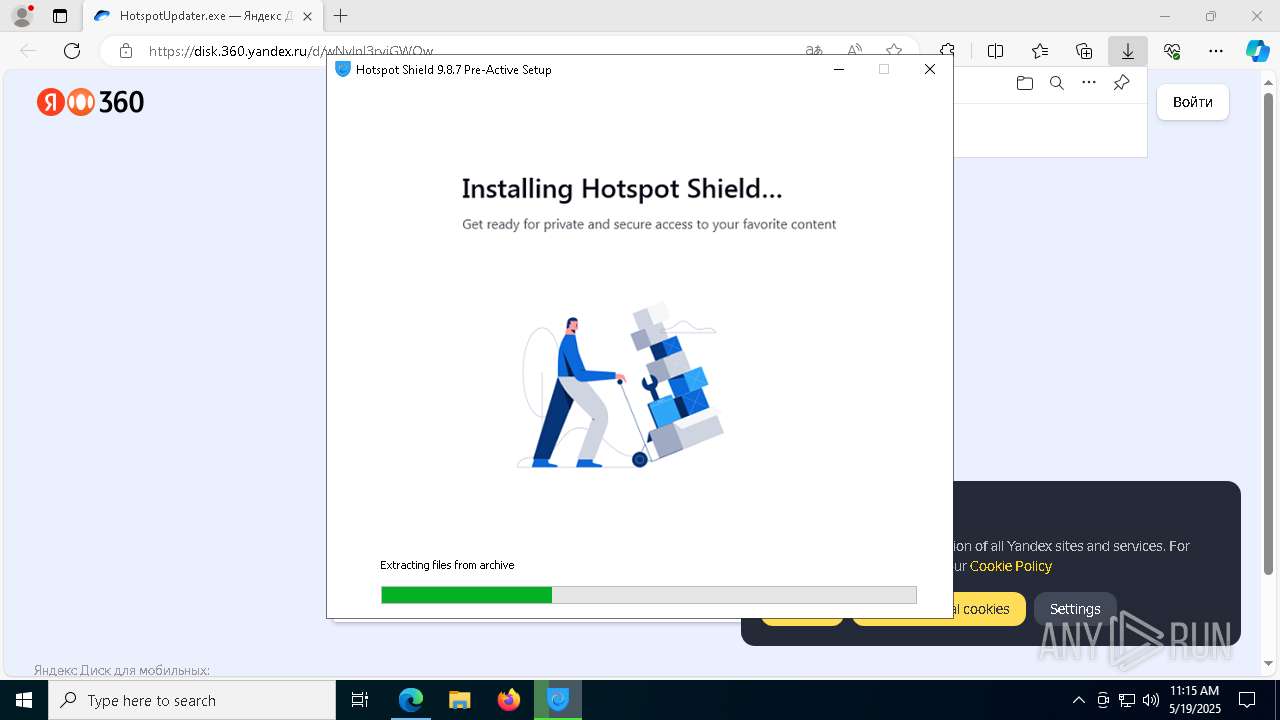
Executable content was dropped or overwritten
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tap-windows-9.21.2.exe (PID: 1012)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8104)
- drvinst.exe (PID: 6476)
- tapinstall.exe (PID: 1240)
- drvinst.exe (PID: 6760)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- tap-windows-9.21.2.EXE (PID: 8040)
- cmw_srv.exe (PID: 8040)
Starts CMD.EXE for commands execution
- ftp.exe (PID: 2268)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7848)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6752)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 1096)
ADVANCEDINSTALLER mutex has been found
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
Reads the Windows owner or organization settings
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msiexec.exe (PID: 7608)
Process drops legitimate windows executable
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msiexec.exe (PID: 7608)
The process creates files with name similar to system file names
- tap-windows-9.21.2.EXE (PID: 8040)
- msiexec.exe (PID: 7608)
Malware-specific behavior (creating "System.dll" in Temp)
- tap-windows-9.21.2.EXE (PID: 8040)
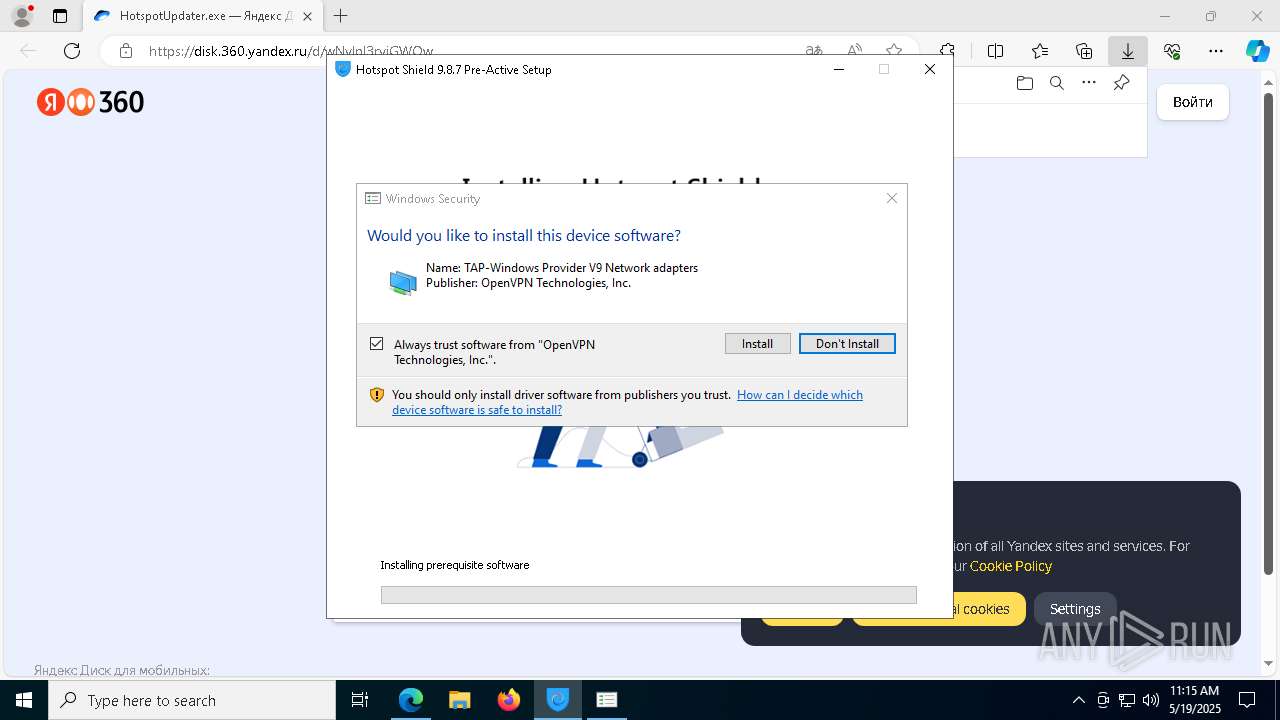
Drops a system driver (possible attempt to evade defenses)
- tap-windows-9.21.2.EXE (PID: 8040)
- tapinstall.exe (PID: 1240)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 6760)
- msiexec.exe (PID: 7608)
Creates files in the driver directory
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 6760)
Creates or modifies Windows services
- drvinst.exe (PID: 6760)
Creates a software uninstall entry
- tap-windows-9.21.2.EXE (PID: 8040)
There is functionality for taking screenshot (YARA)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
Detects AdvancedInstaller (YARA)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
Application launched itself
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7848)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7848)
Starts application with an unusual extension
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
Executing commands from a ".bat" file
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7848)
Uses NETSH.EXE to obtain data on the network
- cmw_srv.exe (PID: 8040)
Executes as Windows Service
- cmw_srv.exe (PID: 8040)
INFO
Checks supported languages
- identity_helper.exe (PID: 8180)
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- msiexec.exe (PID: 7608)
- msiexec.exe (PID: 5984)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8104)
- tap-windows-9.21.2.exe (PID: 1012)
- tapinstall.exe (PID: 1240)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 6760)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- tapinstall.exe (PID: 6828)
- tap-windows-9.21.2.EXE (PID: 8040)
- msiexec.exe (PID: 3240)
Executable content was dropped or overwritten
- msedge.exe (PID: 5680)
- msedge.exe (PID: 7900)
- msiexec.exe (PID: 7608)
Create files in a temporary directory
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tap-windows-9.21.2.EXE (PID: 8040)
- tapinstall.exe (PID: 1240)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- tap-windows-9.21.2.exe (PID: 1012)
Application launched itself
- msedge.exe (PID: 5680)
Reads the computer name
- identity_helper.exe (PID: 8180)
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- msiexec.exe (PID: 7608)
- msiexec.exe (PID: 5984)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 6760)
- tap-windows-9.21.2.exe (PID: 1012)
- tapinstall.exe (PID: 1240)
- msiexec.exe (PID: 3240)
Reads Environment values
- identity_helper.exe (PID: 8180)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- msiexec.exe (PID: 5984)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msiexec.exe (PID: 3240)
Checks proxy server information
- HotspotUpdater.exe (PID: 8060)
The sample compiled with english language support
- HotspotUpdater.exe (PID: 8060)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tap-windows-9.21.2.EXE (PID: 8040)
- tapinstall.exe (PID: 1240)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 6760)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msedge.exe (PID: 7900)
- msiexec.exe (PID: 7608)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5548)
- rundll32.exe (PID: 5124)
Reads the machine GUID from the registry
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tapinstall.exe (PID: 1240)
- drvinst.exe (PID: 6476)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msiexec.exe (PID: 7608)
Reads the software policy settings
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- tapinstall.exe (PID: 1240)
- rundll32.exe (PID: 5124)
- drvinst.exe (PID: 6476)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6724)
- msiexec.exe (PID: 7608)
Creates files or folders in the user directory
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8104)
Process checks computer location settings
- msiexec.exe (PID: 5984)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 5936)
Adds/modifies Windows certificates
- drvinst.exe (PID: 6476)
Creates files in the program directory
- tap-windows-9.21.2.EXE (PID: 8040)
Manual execution by a user
- hsscp.exe (PID: 6108)
- hsscp.exe (PID: 5728)
.NET Reactor protector has been detected
- hsscp.exe (PID: 5376)
- cmw_srv.exe (PID: 8040)
Themida protector has been detected
- cmw_srv.exe (PID: 8040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
254
Monitored processes
112
Malicious processes
11
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\cmd.exe /S /D /c" cls" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\WINDOWS\system32\cmd.exe /S /D /c" del "C:\Users\admin\AppData\Local\Temp\EXE7F25.bat" " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1568 --field-trial-handle=2300,i,3988697674439173271,1758524632172156931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6400 --field-trial-handle=2300,i,3988697674439173271,1758524632172156931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Roaming\hss721.blogspot.com\Hotspot Shield 9.8.7 Pre-Active\prerequisites\tap-windows-9.21.2.exe" | C:\Users\admin\AppData\Roaming\hss721.blogspot.com\Hotspot Shield 9.8.7 Pre-Active\prerequisites\tap-windows-9.21.2.exe | HotspotShield-9.8.7-plain-773-PreActive.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7560 --field-trial-handle=2300,i,3988697674439173271,1758524632172156931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4384 --field-trial-handle=2300,i,3988697674439173271,1758524632172156931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | C:\Windows\explorer.exe /root,C:\Users\admin\AppData\Local\Temp\HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Windows\explorer.exe | — | HotspotUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5264 --field-trial-handle=2300,i,3988697674439173271,1758524632172156931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Program Files\TAP-Windows\bin\tapinstall.exe | tap-windows-9.21.2.EXE | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
Total events
61 586
Read events
61 194
Write events
373
Delete events
19
Modification events
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 83AB178511942F00 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 61D11E8511942F00 | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {30D0D90F-AF02-484C-93FC-56F35C4426D5} | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4551D646-AEEB-4140-AF1C-03B35F7FD064} | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2D415AD8-B42D-481F-9C31-2CEA9E25CE4B} | |||
| (PID) Process: | (5680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82ACA0EB-6A9C-4750-818B-CB195A8369A5} | |||
Executable files
169
Suspicious files
490
Text files
140
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b72c.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
130
DNS requests
141
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8184 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4152 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747703930&P2=404&P3=2&P4=dp4iHQoJEkjnK2BHtr3xnleuJTtAaJrKyfpMT7S%2b1x3icZNN%2f0ZRyJFnxPL35Tgygx9UAolPES1y8ncPQXmxnA%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747703930&P2=404&P3=2&P4=dp4iHQoJEkjnK2BHtr3xnleuJTtAaJrKyfpMT7S%2b1x3icZNN%2f0ZRyJFnxPL35Tgygx9UAolPES1y8ncPQXmxnA%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747703931&P2=404&P3=2&P4=cxp8%2byyzllcU6j21%2b1KddkkT9ZxpuZPGQSMXwiog%2f%2beVkdpWZWzQDa%2fqoydlejhTKCGyvXPjS9naT6gBZ%2bK9nQ%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747703931&P2=404&P3=2&P4=cxp8%2byyzllcU6j21%2b1KddkkT9ZxpuZPGQSMXwiog%2f%2beVkdpWZWzQDa%2fqoydlejhTKCGyvXPjS9naT6gBZ%2bK9nQ%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747703930&P2=404&P3=2&P4=dp4iHQoJEkjnK2BHtr3xnleuJTtAaJrKyfpMT7S%2b1x3icZNN%2f0ZRyJFnxPL35Tgygx9UAolPES1y8ncPQXmxnA%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747703931&P2=404&P3=2&P4=cxp8%2byyzllcU6j21%2b1KddkkT9ZxpuZPGQSMXwiog%2f%2beVkdpWZWzQDa%2fqoydlejhTKCGyvXPjS9naT6gBZ%2bK9nQ%3d%3d | unknown | — | — | whitelisted |
4152 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747703931&P2=404&P3=2&P4=cxp8%2byyzllcU6j21%2b1KddkkT9ZxpuZPGQSMXwiog%2f%2beVkdpWZWzQDa%2fqoydlejhTKCGyvXPjS9naT6gBZ%2bK9nQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5680 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 52.123.243.217:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
disk.360.yandex.ru |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
yastatic.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO OpenDrive Cloud Storage Domain in DNS Lookup (od .lk) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO OpenDrive Cloud Storage Domain in DNS Lookup (od .lk) |