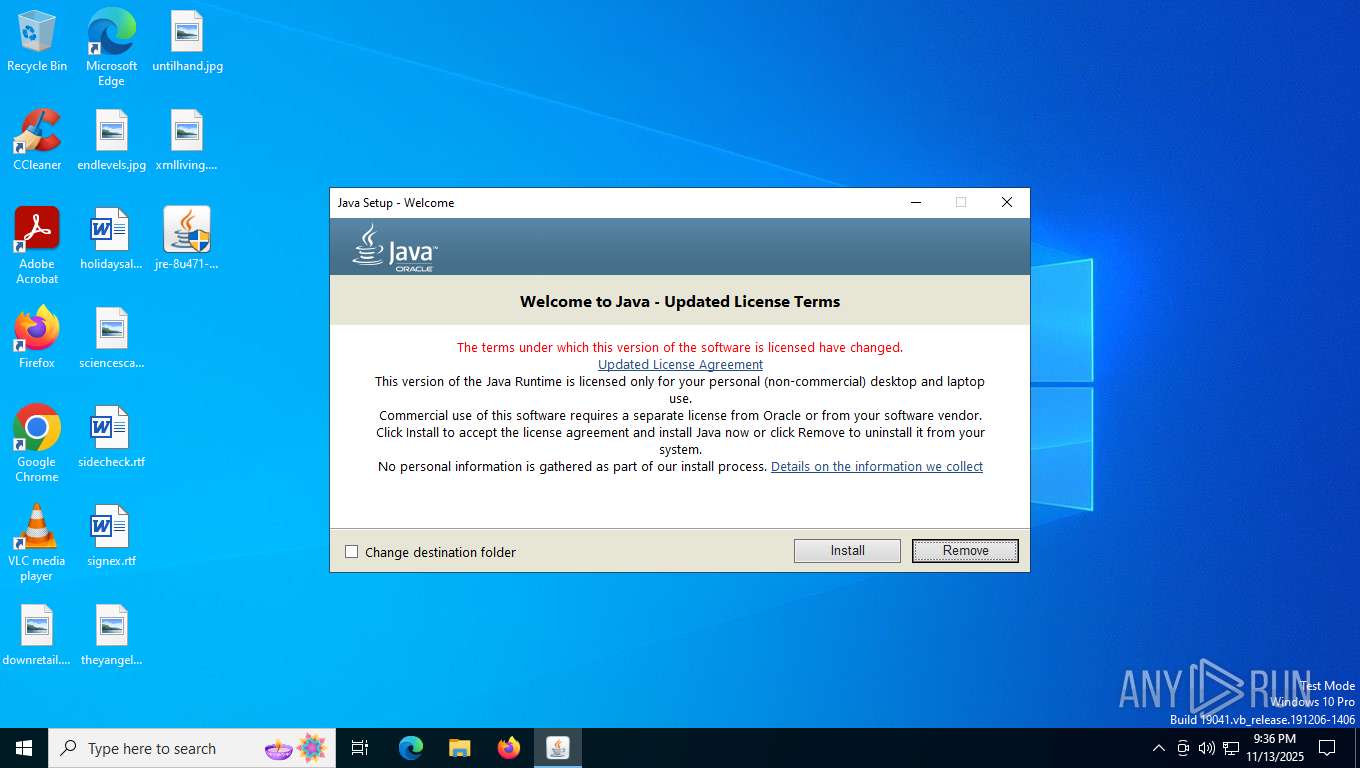
| File name: | jre-8u471-windows-x64.exe |
| Full analysis: | https://app.any.run/tasks/3b60137c-7cd3-4147-bafd-8be18c9ca032 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2025, 21:36:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | ADFFFCE8CA8D0FD2B718D9BE05ACC062 |
| SHA1: | 5F8F9FAAB8E819587D07603460F8B0DD6AE95BC4 |
| SHA256: | 083FDA16F0D2FB4A3ABBCA11E135FD916042921FAC3F5153289EBA6AE6ECD641 |
| SSDEEP: | 393216:MUj83O2MECTeeKYs3bW+TCITb97T391DV:MY8RVg5s3bWSC8t1J |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for Java to be installed
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6456)
- msiexec.exe (PID: 6124)
- installer.exe (PID: 2612)
- ssvagent.exe (PID: 6548)
- jp2launcher.exe (PID: 3392)
- jp2launcher.exe (PID: 6492)
- msiexec.exe (PID: 3388)
- javaw.exe (PID: 3132)
Reads Internet Explorer settings
- jre-8u471-windows-x64.exe (PID: 2060)
Reads security settings of Internet Explorer
- jre-8u471-windows-x64.exe (PID: 2060)
- installer.exe (PID: 2612)
- jp2launcher.exe (PID: 3392)
- jp2launcher.exe (PID: 6492)
Application launched itself
- msiexec.exe (PID: 6124)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6124)
Reads Mozilla Firefox installation path
- MSI4DC4.tmp (PID: 5652)
- installer.exe (PID: 2612)
There is functionality for taking screenshot (YARA)
- jre-8u471-windows-x64.exe (PID: 2060)
Executable content was dropped or overwritten
- installer.exe (PID: 2612)
Creates/Modifies COM task schedule object
- installer.exe (PID: 2612)
- ssvagent.exe (PID: 6548)
Process drops legitimate windows executable
- msiexec.exe (PID: 6124)
The process drops C-runtime libraries
- msiexec.exe (PID: 6124)
INFO
Java executable
- jre-8u471-windows-x64.exe (PID: 2164)
- jre-8u471-windows-x64.exe (PID: 4528)
- jre-8u471-windows-x64.exe (PID: 2060)
- MSI4DC4.tmp (PID: 5652)
- installer.exe (PID: 2612)
The sample compiled with english language support
- jre-8u471-windows-x64.exe (PID: 4528)
- msiexec.exe (PID: 6124)
- installer.exe (PID: 2612)
Reads the computer name
- jre-8u471-windows-x64.exe (PID: 4528)
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6124)
- msiexec.exe (PID: 6456)
- MSI4DC4.tmp (PID: 5652)
- installer.exe (PID: 2612)
- javaws.exe (PID: 3984)
- jp2launcher.exe (PID: 3392)
- javaws.exe (PID: 1568)
- jp2launcher.exe (PID: 6492)
- msiexec.exe (PID: 7144)
- javaw.exe (PID: 3132)
- javaw.exe (PID: 1568)
- msiexec.exe (PID: 3388)
Reads Environment values
- jre-8u471-windows-x64.exe (PID: 2060)
Checks supported languages
- jre-8u471-windows-x64.exe (PID: 4528)
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6124)
- msiexec.exe (PID: 6456)
- MSI4DC4.tmp (PID: 5652)
- installer.exe (PID: 2612)
- javaw.exe (PID: 3988)
- ssvagent.exe (PID: 6548)
- jaureg.exe (PID: 5268)
- javaws.exe (PID: 3984)
- jp2launcher.exe (PID: 3392)
- javaws.exe (PID: 1568)
- jp2launcher.exe (PID: 6492)
- msiexec.exe (PID: 7144)
- javaw.exe (PID: 3132)
- javaw.exe (PID: 1568)
- msiexec.exe (PID: 3388)
Create files in a temporary directory
- jre-8u471-windows-x64.exe (PID: 4528)
- MSI4DC4.tmp (PID: 5652)
- javaw.exe (PID: 3988)
- jp2launcher.exe (PID: 3392)
- jp2launcher.exe (PID: 6492)
Reads the machine GUID from the registry
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6124)
Reads the software policy settings
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6124)
- slui.exe (PID: 5652)
Checks proxy server information
- jre-8u471-windows-x64.exe (PID: 2060)
- jp2launcher.exe (PID: 3392)
- jp2launcher.exe (PID: 6492)
- slui.exe (PID: 5652)
Creates files or folders in the user directory
- jre-8u471-windows-x64.exe (PID: 2060)
- msiexec.exe (PID: 6124)
Starts application with an unusual extension
- msiexec.exe (PID: 6124)
Reads CPU info
- msiexec.exe (PID: 6124)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6124)
Creates a software uninstall entry
- msiexec.exe (PID: 6124)
Creates files in the program directory
- installer.exe (PID: 2612)
- javaw.exe (PID: 3988)
JAVA mutex has been found
- jp2launcher.exe (PID: 3392)
- jp2launcher.exe (PID: 6492)
- msiexec.exe (PID: 7144)
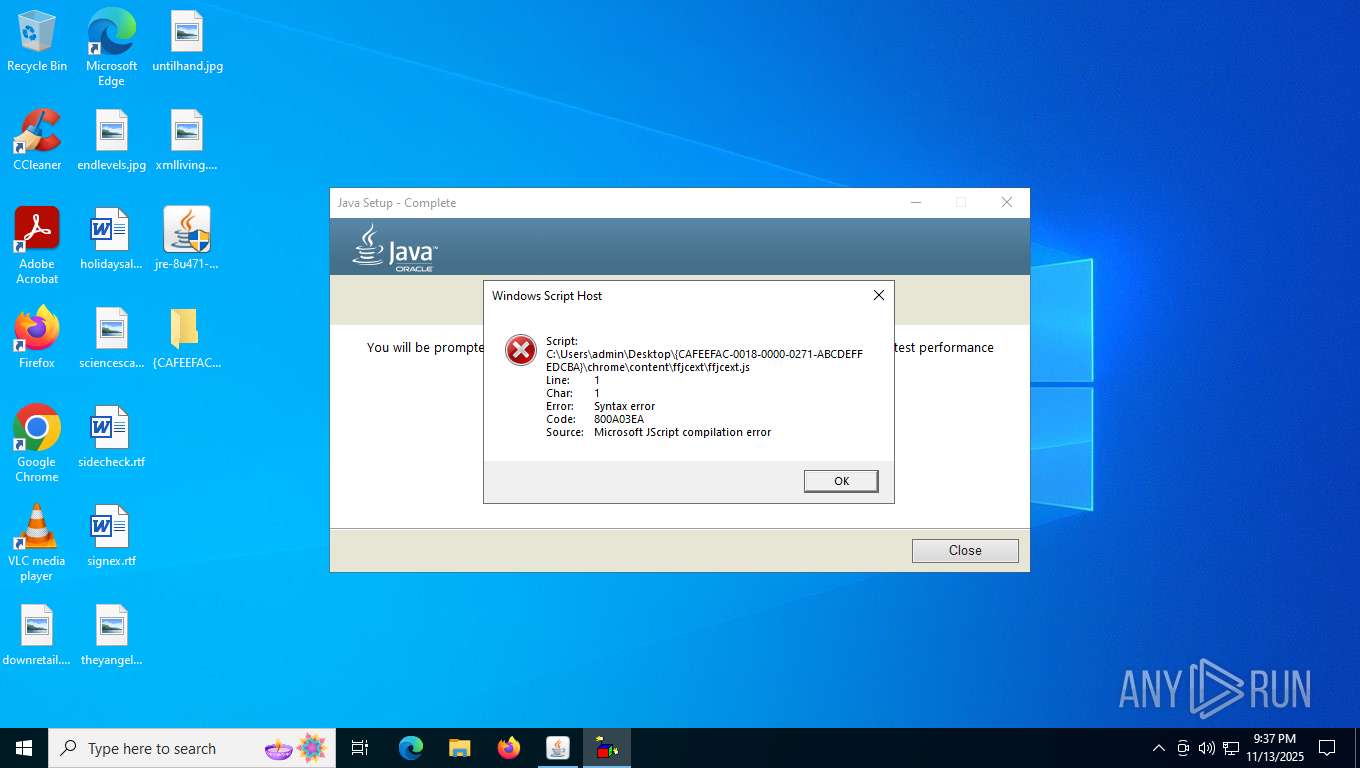
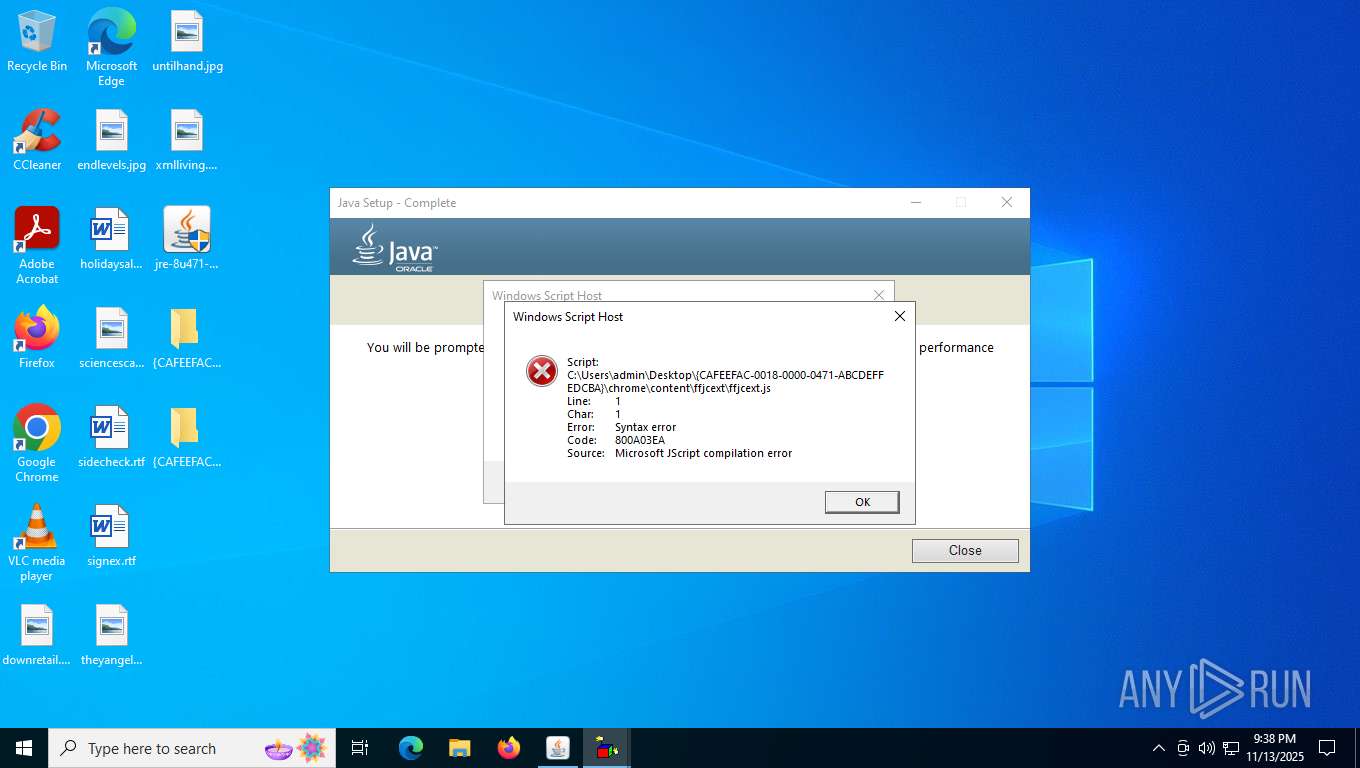
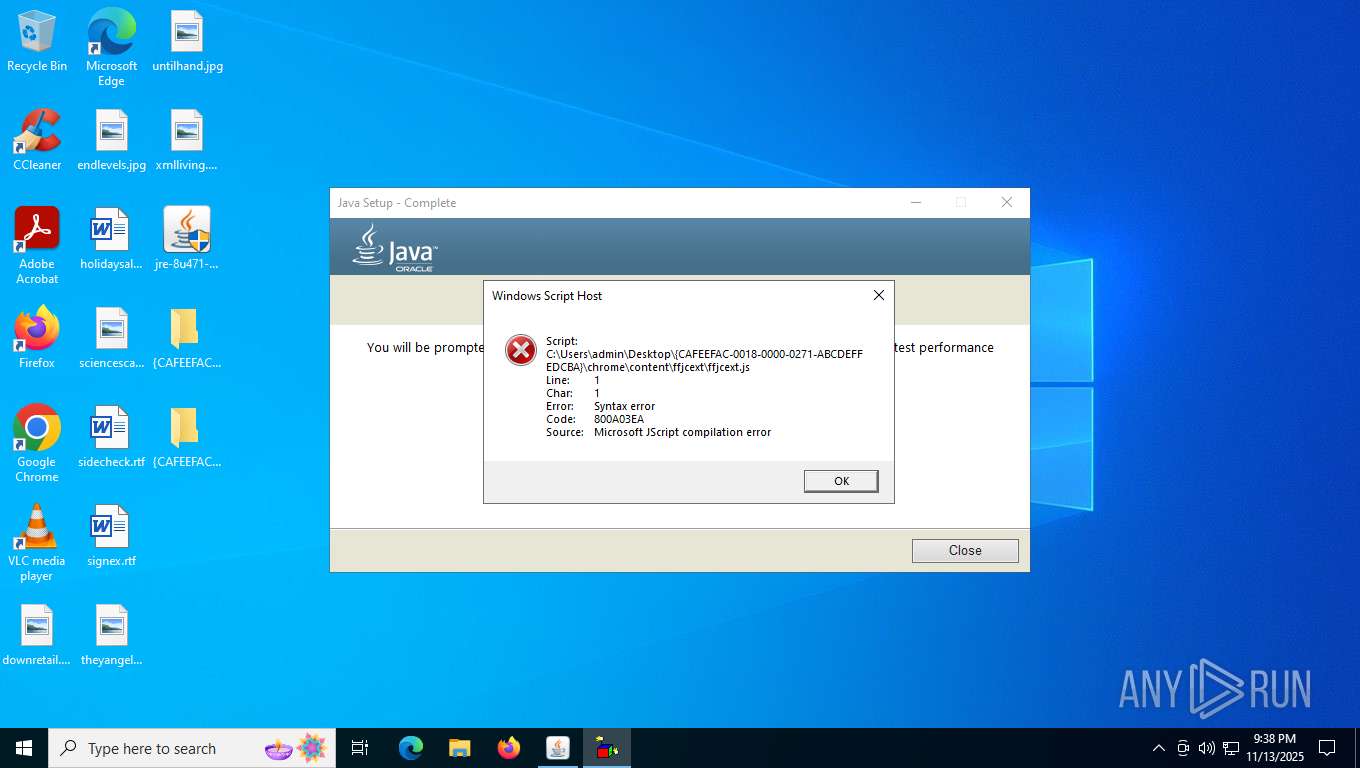
Manual execution by a user
- wscript.exe (PID: 5412)
- wscript.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (53.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (35.5) |
| .exe | | | Win32 Executable (generic) (5.8) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:09:26 05:45:46+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.36 |
| CodeSize: | 262656 |
| InitializedDataSize: | 40084992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19564 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.4710.9 |
| ProductVersionNumber: | 8.0.4710.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Oracle Corporation |
| FileDescription: | Java Platform SE binary |
| FileVersion: | 8.0.4710.9 |
| FullVersion: | 1.8.0_471-b09 |
| InternalName: | Setup Launcher |
| LegalCopyright: | Copyright © 2025 |
| OriginalFileName: | wrapper_jre_offline.exe |
| ProductName: | Java Platform SE 8 U471 |
| ProductVersion: | 8.0.4710.9 |
Total processes
166
Monitored processes
23
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\{CAFEEFAC-0018-0000-0471-ABCDEFFEDCBA}/chrome/content/ffjcext/ffjcext.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Java\jre1.8.0_471\bin\javaws.exe" -wait -fix -shortcut -silent | C:\Program Files\Java\jre1.8.0_471\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.471.0.09 Modules
| |||||||||||||||
| 1568 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_471\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -getUserPreviousDecisionsExist 30 | C:\Program Files\Java\jre1.8.0_471\bin\javaw.exe | — | jre-8u471-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4710.9 Modules
| |||||||||||||||
| 2060 | "C:\Users\admin\AppData\Local\Temp\jds1453828.tmp\jre-8u471-windows-x64.exe" | C:\Users\admin\AppData\Local\Temp\jds1453828.tmp\jre-8u471-windows-x64.exe | jre-8u471-windows-x64.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Version: 8.0.4710.9 Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\Desktop\jre-8u471-windows-x64.exe" | C:\Users\admin\Desktop\jre-8u471-windows-x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Platform SE binary Exit code: 3221226540 Version: 8.0.4710.9 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Java\jre1.8.0_471\installer.exe" /s INSTALLDIR="C:\Program Files\Java\jre1.8.0_471\\" INSTALL_SILENT=1 AUTO_UPDATE=0 SPONSORS=0 REPAIRMODE=0 ProductCode={77924AE4-039E-4CA4-87B4-2F64180471F0} | C:\Program Files\Java\jre1.8.0_471\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.4710.9 Modules
| |||||||||||||||
| 3132 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_471\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -getUserWebJavaStatus | C:\Program Files\Java\jre1.8.0_471\bin\javaw.exe | — | jre-8u471-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.4710.9 Modules
| |||||||||||||||
| 3388 | C:\Windows\System32\MsiExec.exe -Embedding 48C31806EECFD5277C1A20946F8CA65F E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Java\jre1.8.0_471\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_471" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80NzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDcxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDcxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtcGVybWlzc2lvbnMALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_471\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.471.0.09 Modules
| |||||||||||||||
Total events
46 177
Read events
17 796
Write events
13 321
Delete events
15 060
Modification events
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Country |
Value: GB | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | PostStatusUrl |
Value: https://sjremetrics.java.com/b/ss//6 | |||
| (PID) Process: | (2060) jre-8u471-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Method |
Value: joff | |||
| (PID) Process: | (6124) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: EC170000292DCA94E554DC01 | |||
Executable files
333
Suspicious files
88
Text files
196
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4528 | jre-8u471-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\jds1453828.tmp\jds1453828.tmp | — | |
MD5:— | SHA256:— | |||
| 4528 | jre-8u471-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\jds1453828.tmp\jre-8u471-windows-x64.exe | — | |
MD5:— | SHA256:— | |||
| 2060 | jre-8u471-windows-x64.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_471_x64\jre1.8.0_47164.msi | — | |
MD5:— | SHA256:— | |||
| 6124 | msiexec.exe | C:\Windows\Installer\164105.msi | — | |
MD5:— | SHA256:— | |||
| 6124 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:2A99B994B5F4A865435C516B905F2FD4 | SHA256:C783B092636A3D913D166B487CBCB3DC677C9A95F6C330F85658AF5B7590CE67 | |||
| 2060 | jre-8u471-windows-x64.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_471_x64\Java3BillDevices.png | image | |
MD5:8E52EFC6798ED074072F527309A1BA25 | SHA256:12491EBC4EB99BF014D3BC44F770114BDE013E84CBEC2633303559A8C6E5F991 | |||
| 6124 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:308091177D986A8FA4299879DC1612A3 | SHA256:7354B349E3525E63B2301E581FA3F9D419E14D8C12D6533852884FFEC91837B8 | |||
| 6124 | msiexec.exe | C:\Windows\Installer\MSI45C1.tmp | executable | |
MD5:64826B878EDCDB638B3511413D3CE65E | SHA256:CB334C89A254D0B0F2D11CFCF6B730E5D9DA23B45C66D0CAE0E7E5FF3278723C | |||
| 6124 | msiexec.exe | C:\Windows\Installer\MSI4582.tmp | executable | |
MD5:64826B878EDCDB638B3511413D3CE65E | SHA256:CB334C89A254D0B0F2D11CFCF6B730E5D9DA23B45C66D0CAE0E7E5FF3278723C | |||
| 6124 | msiexec.exe | C:\Windows\Installer\MSI4552.tmp | executable | |
MD5:64826B878EDCDB638B3511413D3CE65E | SHA256:CB334C89A254D0B0F2D11CFCF6B730E5D9DA23B45C66D0CAE0E7E5FF3278723C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
23
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6752 | svchost.exe | GET | 200 | 2.16.168.199:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.199:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
— | — | GET | 200 | 104.102.53.139:443 | https://javadl-esd-secure.oracle.com/update/1.8.0/99a6cb9582554a09bd4ac60f73f9b8e6/1.8.0_471-b09.xml | NL | — | — | unknown |
— | — | HEAD | 200 | 104.102.53.139:443 | https://rps-svcs.oracle.com/services/countrylookup | NL | — | — | unknown |
6124 | msiexec.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | binary | 727 b | whitelisted |
6124 | msiexec.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | binary | 471 b | whitelisted |
— | — | POST | 500 | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | — | — | unknown |
6124 | msiexec.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAqhj2P5bxF3HLsLQ%2BTWkLg%3D | unknown | binary | 727 b | whitelisted |
— | — | POST | 204 | 92.123.104.19:443 | https://www.bing.com/web/xlsc.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
— | — | POST | 500 | 4.154.185.43:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6752 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3292 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6752 | svchost.exe | 2.16.168.199:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.168.199:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5524 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2060 | jre-8u471-windows-x64.exe | 23.222.55.83:443 | javadl-esd-secure.oracle.com | AKAMAI-AS | NL | whitelisted |
2060 | jre-8u471-windows-x64.exe | 104.102.53.139:443 | rps-svcs.oracle.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
rps-svcs.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.java.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |