| URL: | http://espaciomarketing.com/cgi-bin/NpiLk-iE2k51g3RP6PYx9_YMibeEEWI-N5/ |
| Full analysis: | https://app.any.run/tasks/159fcf56-678b-420c-a9aa-64e9b80a60f7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 24, 2019, 03:07:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D835324938C6715A357EFC282EBEC100 |
| SHA1: | 82E1485CAE6E738A1D6AC36AC376B31D58F4E144 |
| SHA256: | 083E2EF57F7B82A3D4B87F74043AE41B27091ECC0659A139A7B4356DB6F0A81C |
| SSDEEP: | 3:N1KbSExBCyRCMIqnOLBVFT6cXoVOf:CDxVRjn4BVwcQOf |
MALICIOUS
Application was dropped or rewritten from another process
- 408.exe (PID: 1860)
- 408.exe (PID: 2080)
- soundser.exe (PID: 2140)
- soundser.exe (PID: 2684)
Downloads executable files from the Internet
- powershell.exe (PID: 3140)
Emotet process was detected
- soundser.exe (PID: 2684)
EMOTET was detected
- soundser.exe (PID: 2140)
Changes the autorun value in the registry
- soundser.exe (PID: 2140)
Connects to CnC server
- soundser.exe (PID: 2140)
SUSPICIOUS
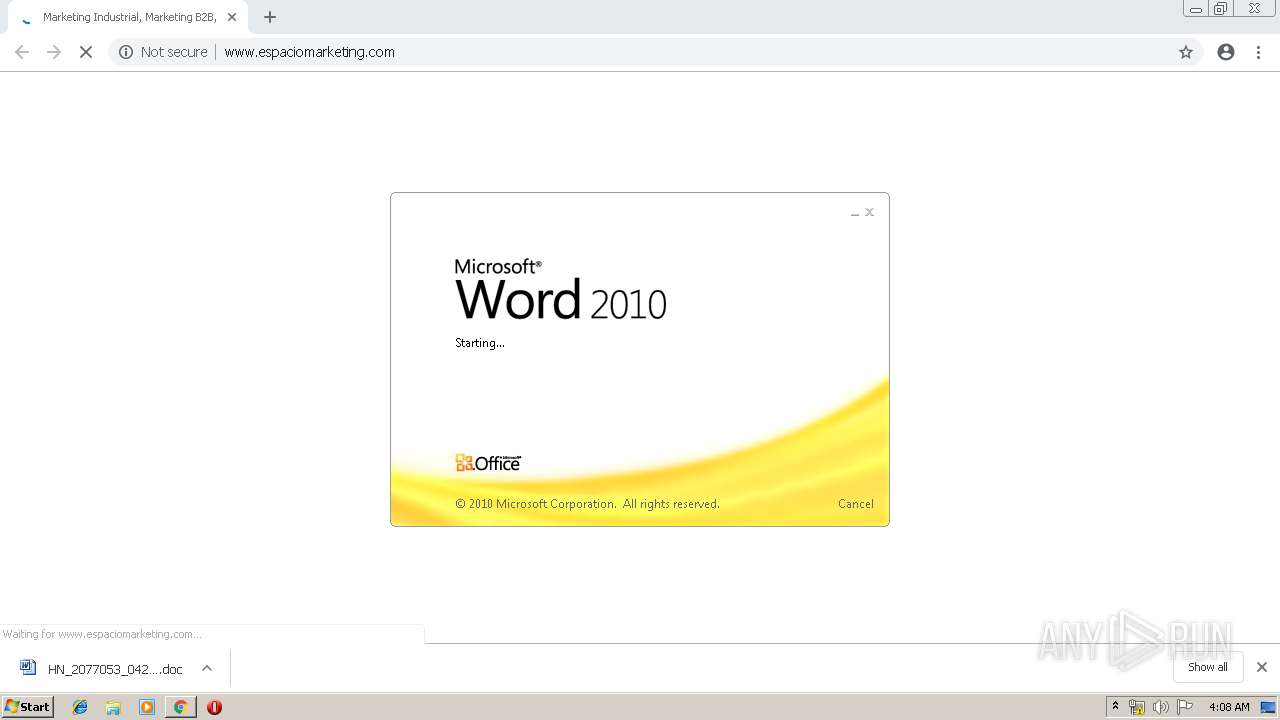
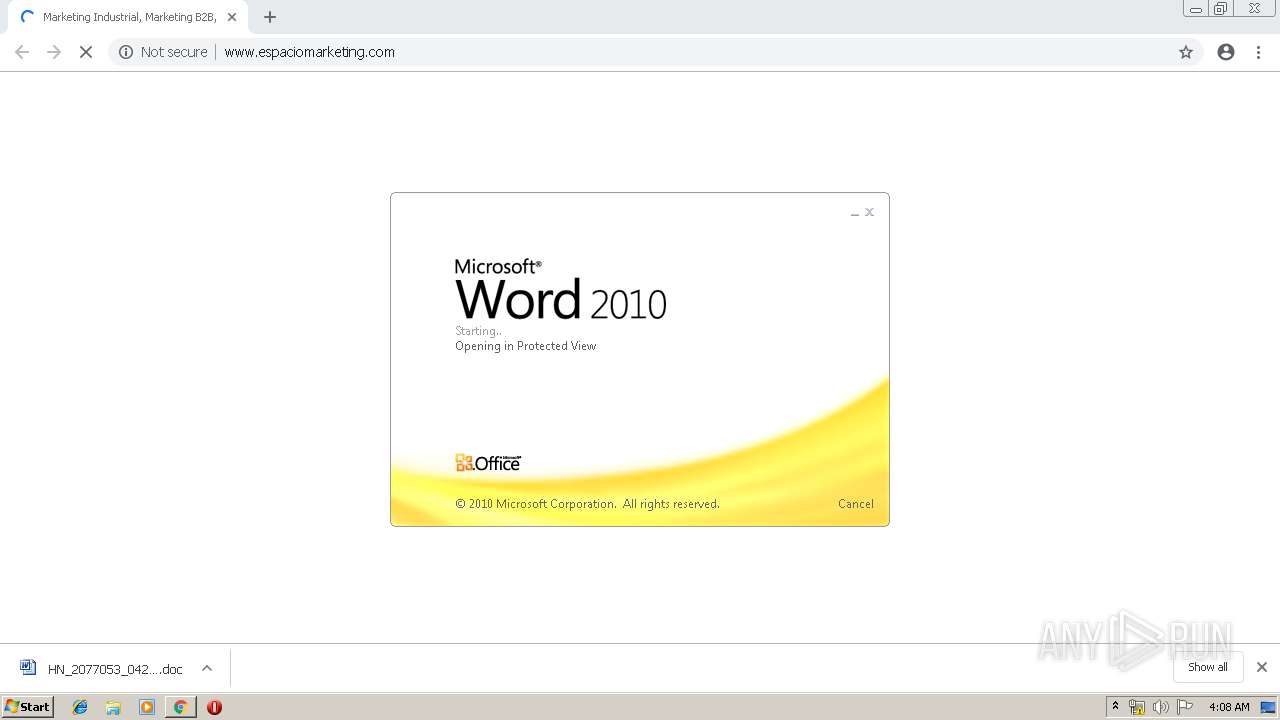
Starts Microsoft Office Application
- chrome.exe (PID: 2580)
- WINWORD.EXE (PID: 3896)
Application launched itself
- WINWORD.EXE (PID: 3896)
- 408.exe (PID: 1860)
- soundser.exe (PID: 2684)
Creates files in the user directory
- powershell.exe (PID: 3140)
Executable content was dropped or overwritten
- powershell.exe (PID: 3140)
- 408.exe (PID: 2080)
Starts itself from another location
- 408.exe (PID: 2080)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2580)
Connects to server without host name
- soundser.exe (PID: 2140)
INFO
Application launched itself
- chrome.exe (PID: 2580)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 936)
- WINWORD.EXE (PID: 3896)
Creates files in the user directory
- WINWORD.EXE (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
27
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4875916405648502688 --mojo-platform-channel-handle=4696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --service-pipe-token=11428837763857796402 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11428837763857796402 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15680146553497734587 --mojo-platform-channel-handle=4672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9696122652753453864 --mojo-platform-channel-handle=4788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13269575685544792114 --mojo-platform-channel-handle=4024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13381665692952316437 --mojo-platform-channel-handle=4748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\408.exe" | C:\Users\admin\408.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4936732723616853867 --mojo-platform-channel-handle=5208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2080 | --2178a1ba | C:\Users\admin\408.exe | 408.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 235
Read events
2 663
Write events
557
Delete events
15
Modification events
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2580-13200548874166250 |
Value: 259 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
35
Text files
216
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\93bb8d1e-5d8d-4e85-ad72-26e77f4bc6f4.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
39
DNS requests
33
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | chrome.exe | GET | 301 | 208.82.116.134:80 | http://espaciomarketing.com/ | US | — | — | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/css/layout.css | US | text | 57.8 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://espaciomarketing.com/cgi-bin/NpiLk-iE2k51g3RP6PYx9_YMibeEEWI-N5/ | US | document | 239 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/ | US | html | 89.1 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/style.css | US | html | 1.37 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/css/grid.css | US | text | 12.9 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/css/base.css | US | text | 13.2 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/css/shortcodes.css | US | text | 22.2 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 208.82.116.134:80 | http://www.espaciomarketing.com/wp-content/themes/espacio-marketing/css/slideshow.css | US | text | 13.1 Kb | suspicious |
2580 | chrome.exe | GET | 200 | 172.217.21.206:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | text | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 208.82.116.134:80 | espaciomarketing.com | Network Data Center Host, Inc. | US | suspicious |
2580 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.205.227:443 | www.google.pl | Google Inc. | US | whitelisted |
2580 | chrome.exe | 172.217.16.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 172.217.21.206:80 | translate.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
espaciomarketing.com |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.pl |
| whitelisted |
www.espaciomarketing.com |
| unknown |
s.w.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2580 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2580 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2580 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3140 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3140 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3140 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2140 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2 ETPRO signatures available at the full report