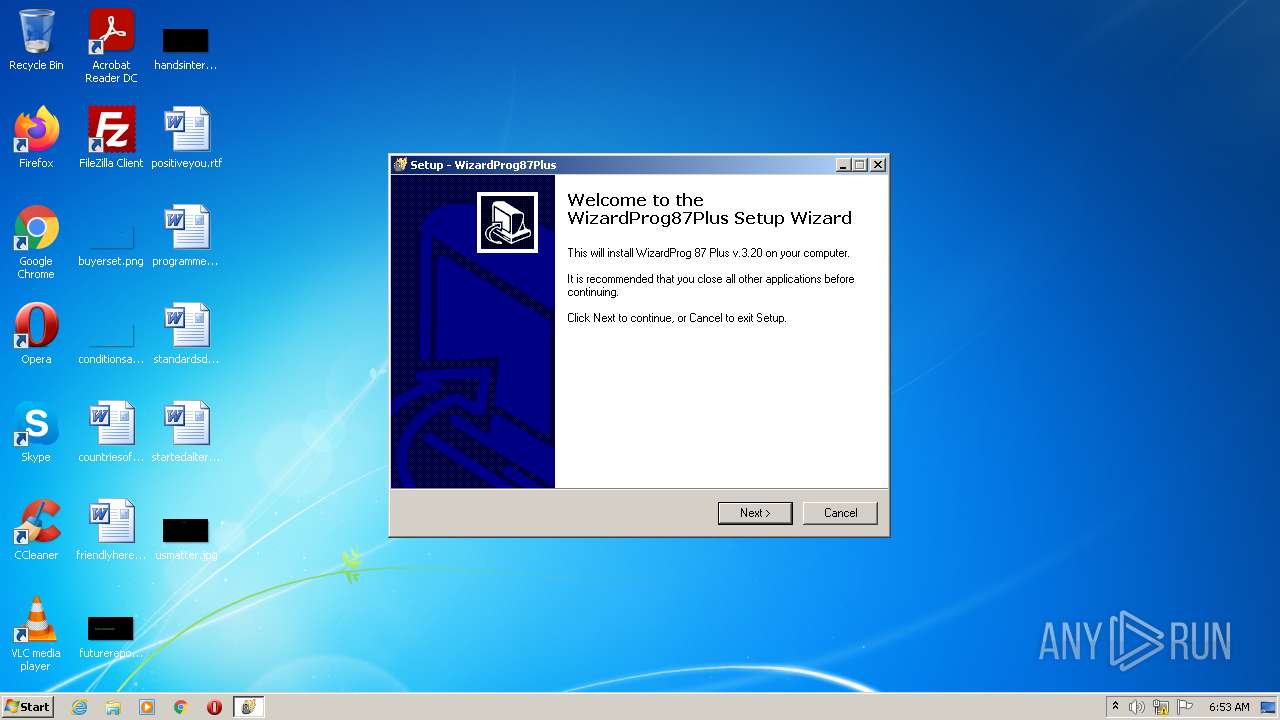
| File name: | setup87plusV320.exe |
| Full analysis: | https://app.any.run/tasks/385411d5-00cd-4c79-9ea3-a0301087812b |
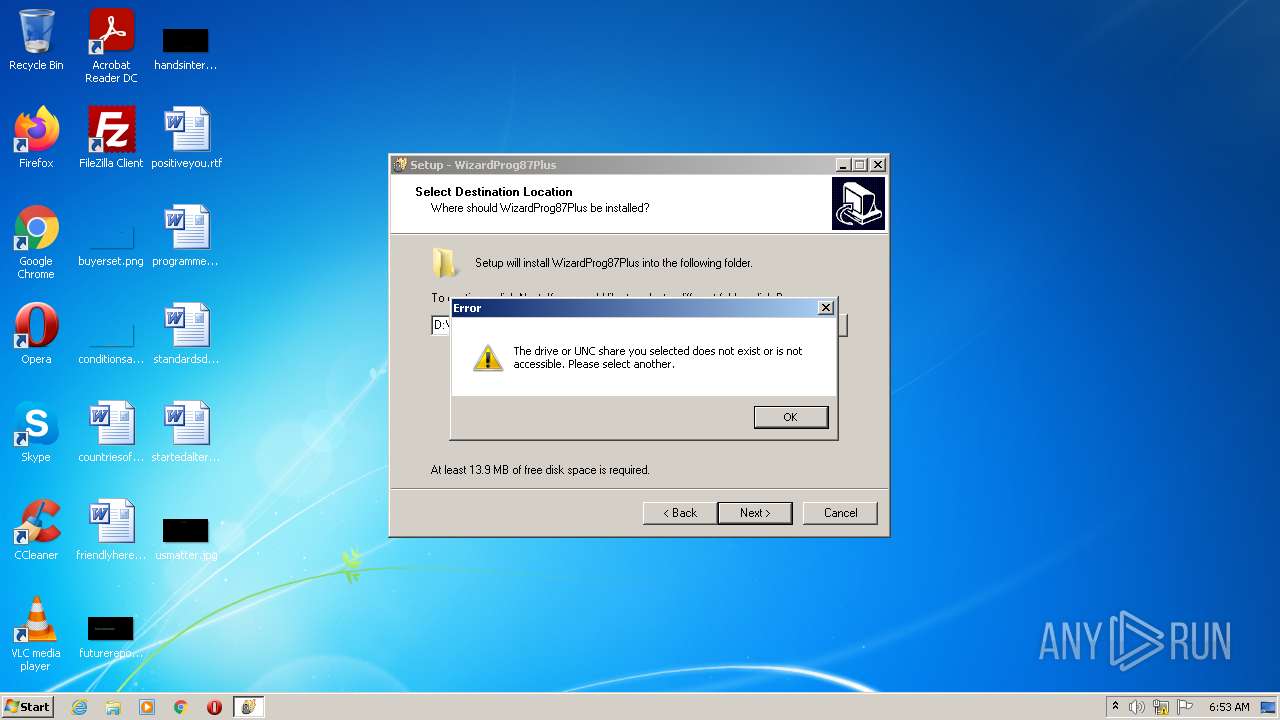
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 05:53:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B646E229AE8DF5B6D797EEAD2BAD3013 |
| SHA1: | 87FA32E2ADC0ED4E88C22500CEA98A263E155F97 |
| SHA256: | 083AC02735389430A665383B716137115D0B7DB57D35AA99B7EBDDA806F13287 |
| SSDEEP: | 196608:V7GhcFsBTV0aiQZOJ0AsxOTHZmy1cO99rtD8iDZ7Mx7fYT3f0paKVvBCkWeZQZBN:xGhusc9QkQC5WE9fDi12sPHC58Cyf6 |
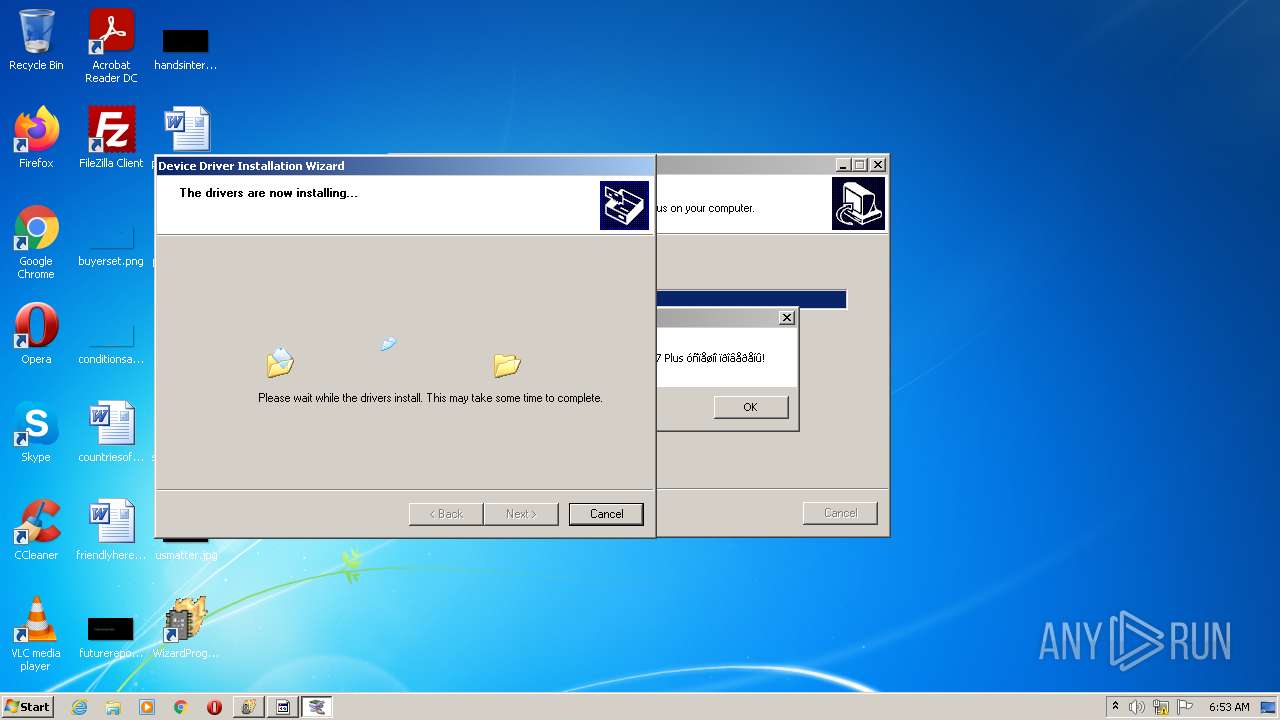
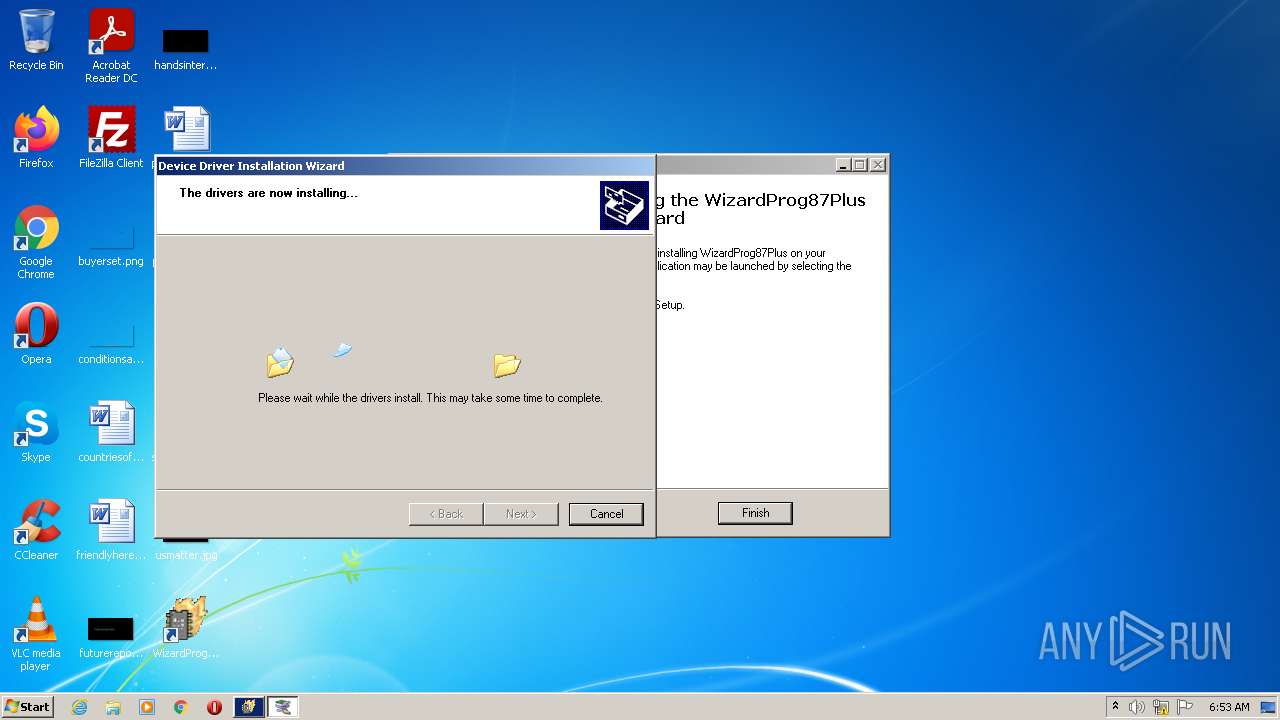
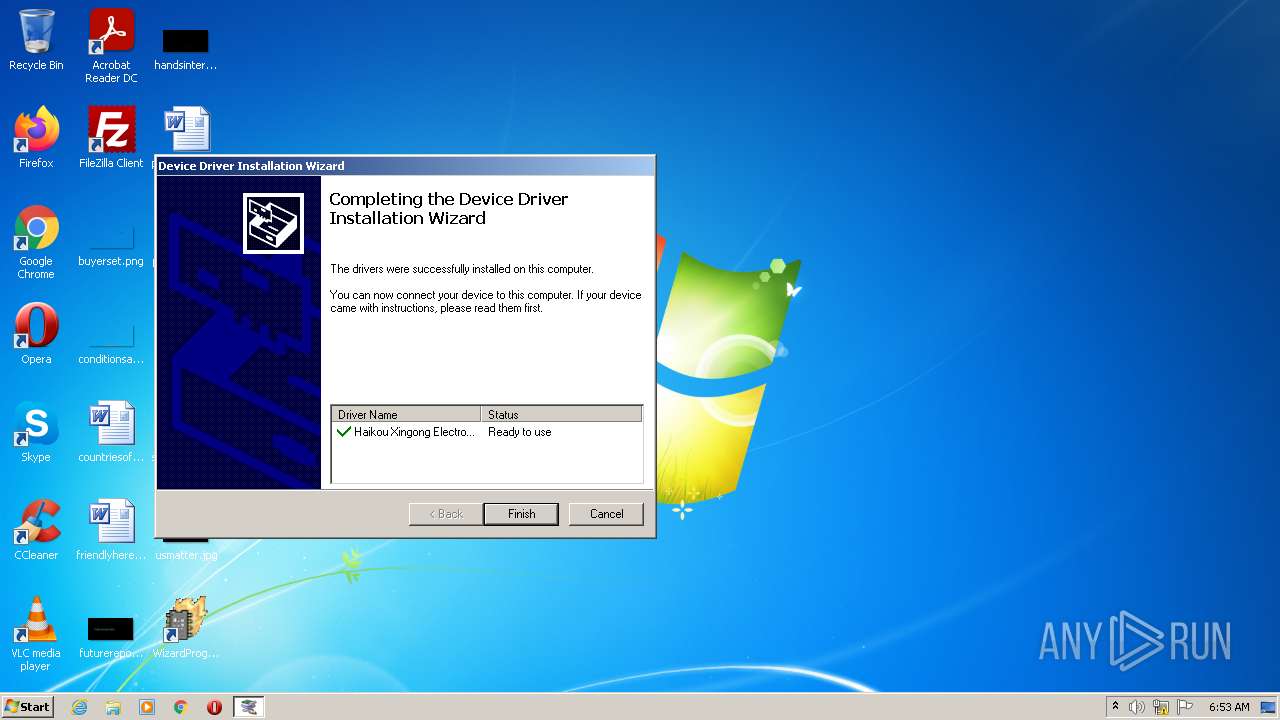
MALICIOUS
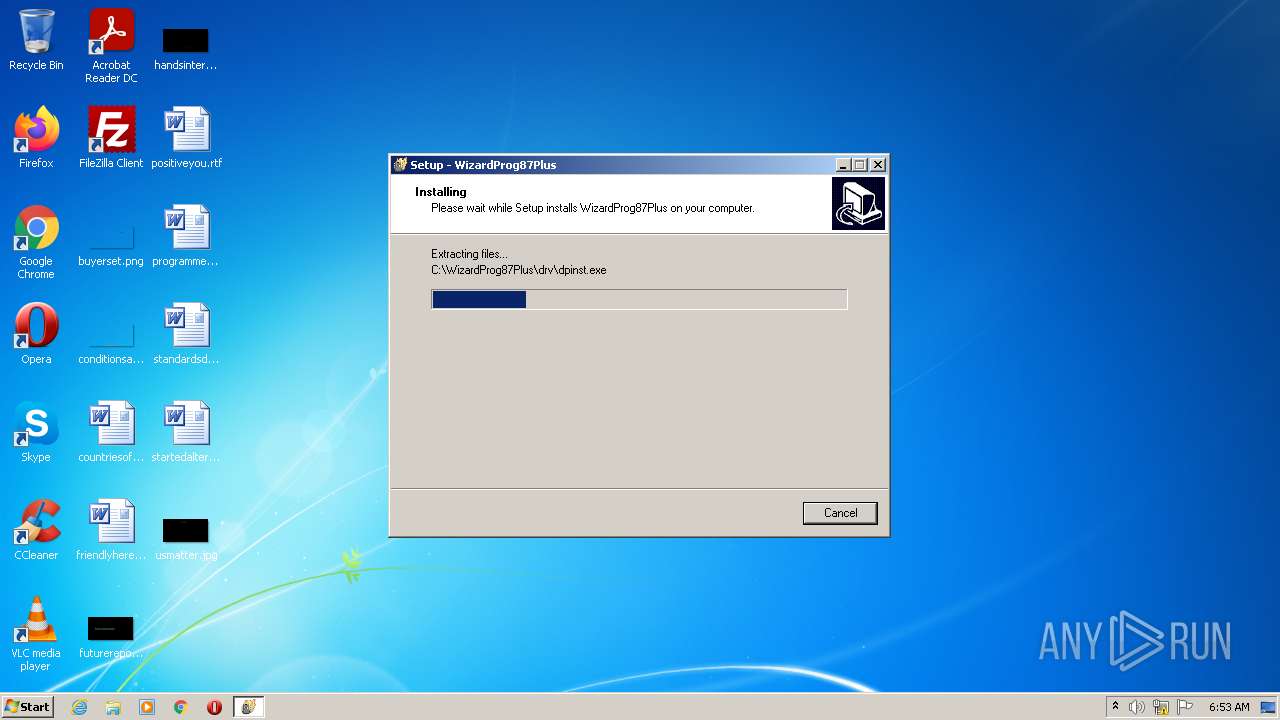
Drops executable file immediately after starts
- setup87plusV320.exe (PID: 3876)
- setup87plusV320.exe (PID: 3872)
- setup87plusV320.tmp (PID: 3564)
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
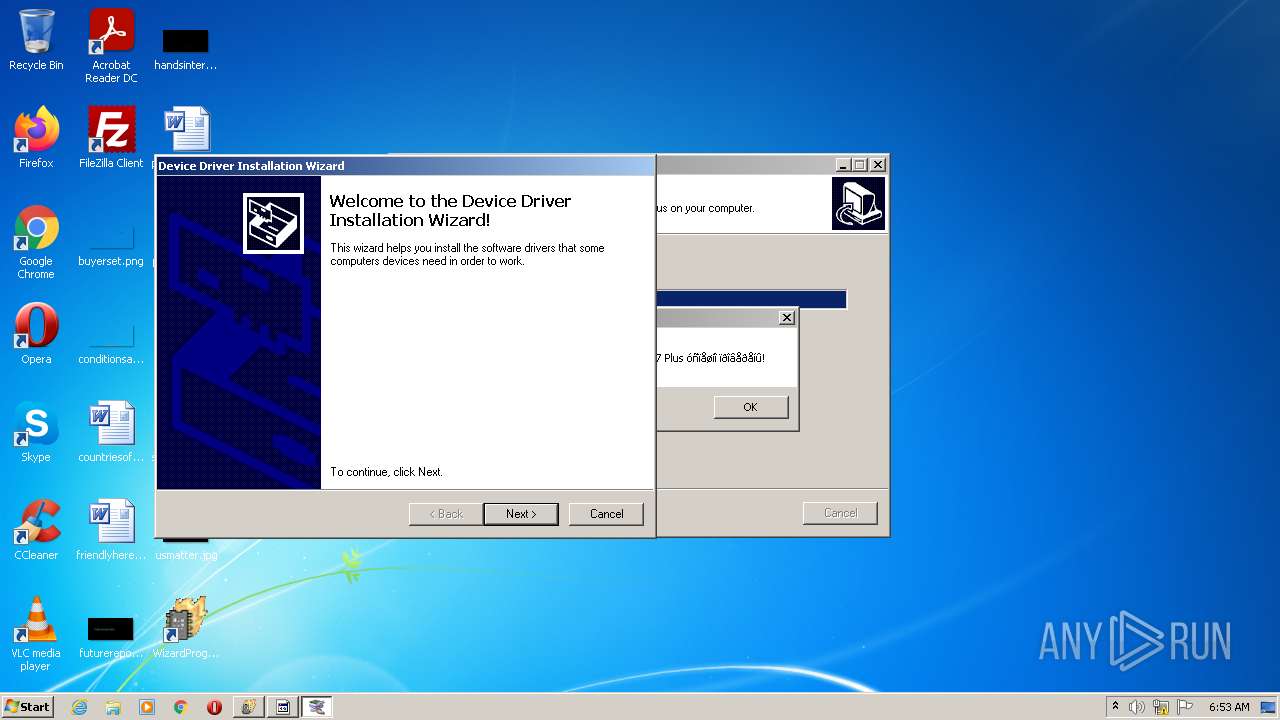
Application was dropped or rewritten from another process
- dpinst.exe (PID: 2176)
- usbinst.exe (PID: 1860)
- wp87plus.exe (PID: 3056)
Loads dropped or rewritten executable
- wp87plus.exe (PID: 3056)
SUSPICIOUS
Checks supported languages
- setup87plusV320.exe (PID: 3876)
- setup87plusV320.tmp (PID: 3364)
- setup87plusV320.exe (PID: 3872)
- setup87plusV320.tmp (PID: 3564)
- usbinst.exe (PID: 1860)
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
- wp87plus.exe (PID: 3056)
Drops a file with a compile date too recent
- setup87plusV320.exe (PID: 3876)
- setup87plusV320.exe (PID: 3872)
- setup87plusV320.tmp (PID: 3564)
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
Executable content was dropped or overwritten
- setup87plusV320.exe (PID: 3876)
- setup87plusV320.exe (PID: 3872)
- setup87plusV320.tmp (PID: 3564)
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
Reads the computer name
- setup87plusV320.tmp (PID: 3364)
- setup87plusV320.tmp (PID: 3564)
- usbinst.exe (PID: 1860)
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
- wp87plus.exe (PID: 3056)
Reads Windows owner or organization settings
- setup87plusV320.tmp (PID: 3564)
Reads the Windows organization settings
- setup87plusV320.tmp (PID: 3564)
Creates files in the Windows directory
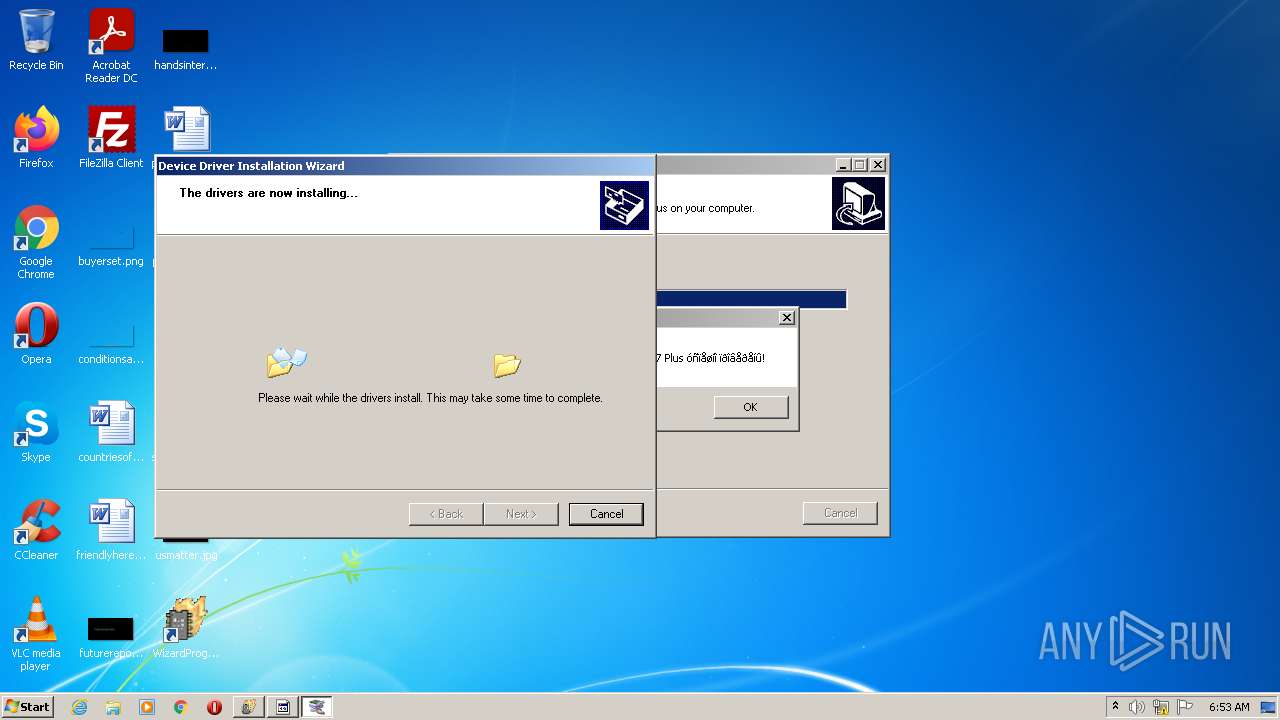
- dpinst.exe (PID: 2176)
- DrvInst.exe (PID: 1820)
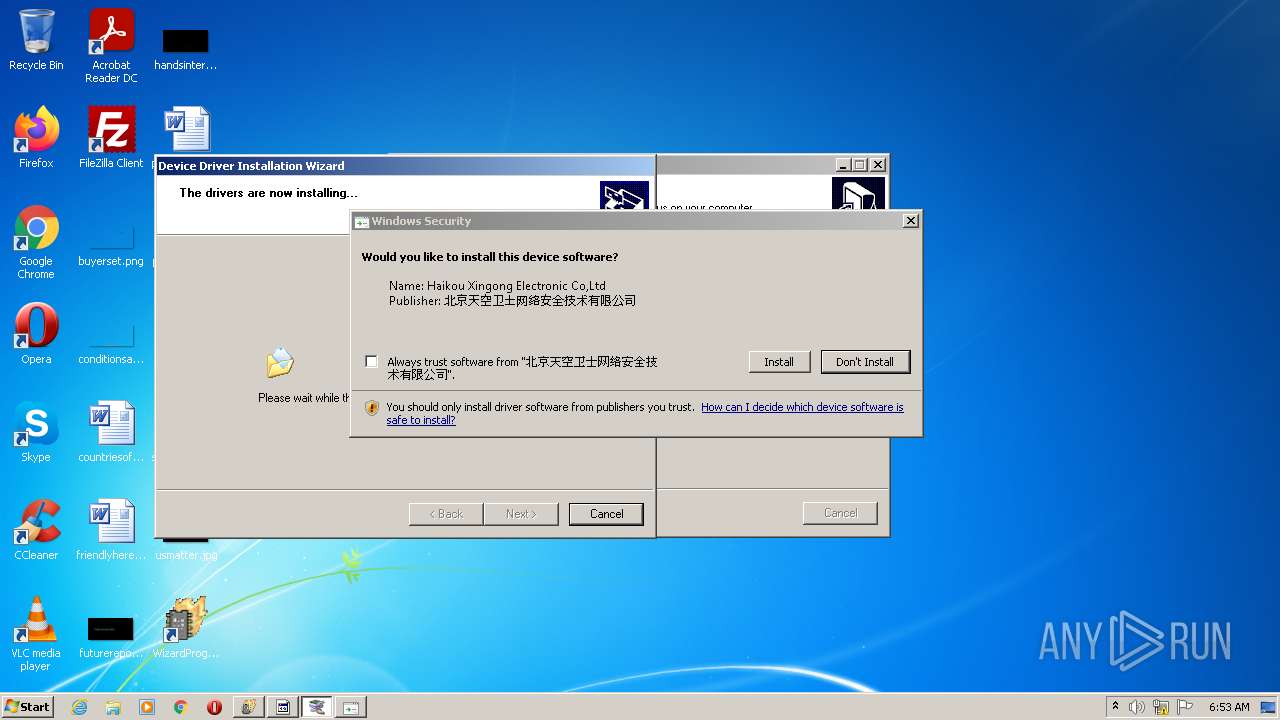
Executed via COM
- DrvInst.exe (PID: 1820)
Creates files in the driver directory
- DrvInst.exe (PID: 1820)
Removes files from Windows directory
- DrvInst.exe (PID: 1820)
Executed as Windows Service
- vssvc.exe (PID: 3352)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 1820)
Reads Environment values
- vssvc.exe (PID: 3352)
Creates a software uninstall entry
- dpinst.exe (PID: 2176)
INFO
Loads dropped or rewritten executable
- setup87plusV320.tmp (PID: 3564)
Application was dropped or rewritten from another process
- setup87plusV320.tmp (PID: 3364)
- setup87plusV320.tmp (PID: 3564)
Checks Windows Trust Settings
- DrvInst.exe (PID: 1820)
- rundll32.exe (PID: 2964)
Reads the computer name
- rundll32.exe (PID: 2964)
- vssvc.exe (PID: 3352)
Checks supported languages
- rundll32.exe (PID: 2964)
- vssvc.exe (PID: 3352)
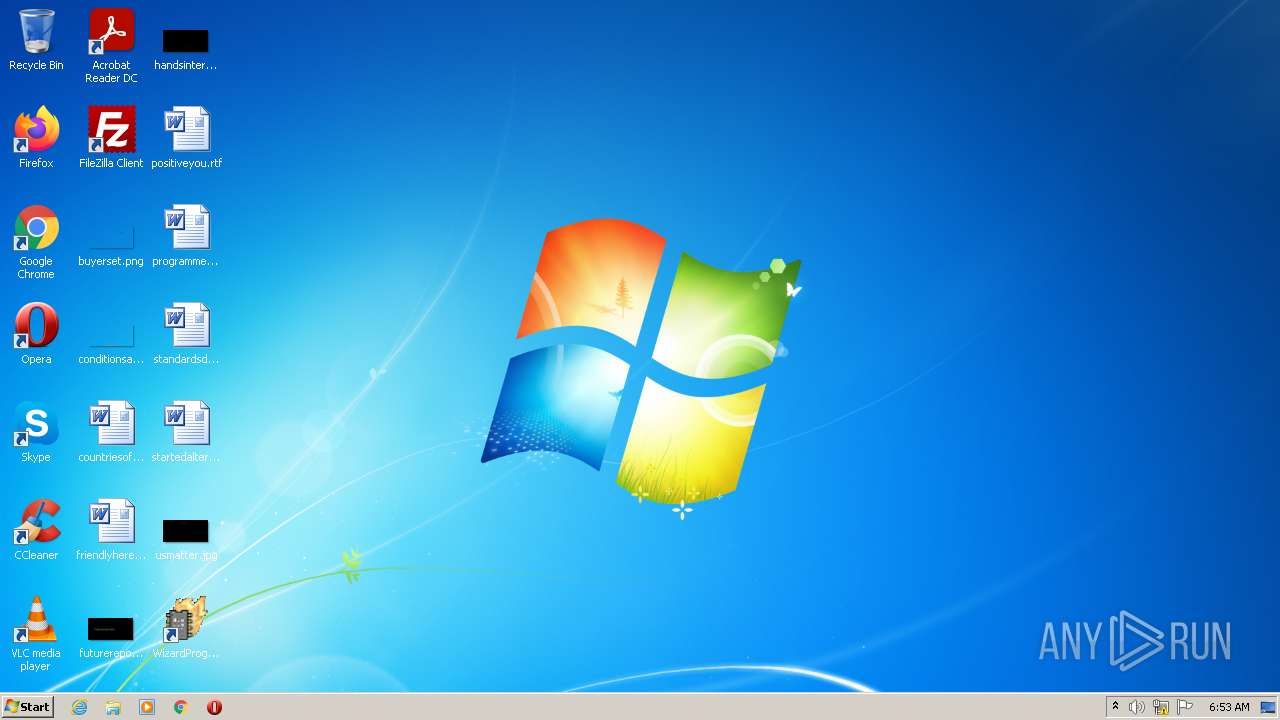
Manual execution by user
- wp87plus.exe (PID: 3056)
Reads settings of System Certificates
- rundll32.exe (PID: 2964)
- DrvInst.exe (PID: 1820)
Searches for installed software
- DrvInst.exe (PID: 1820)
Creates files in the program directory
- setup87plusV320.tmp (PID: 3564)
Creates a software uninstall entry
- setup87plusV320.tmp (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| ProductVersion: | |
|---|---|
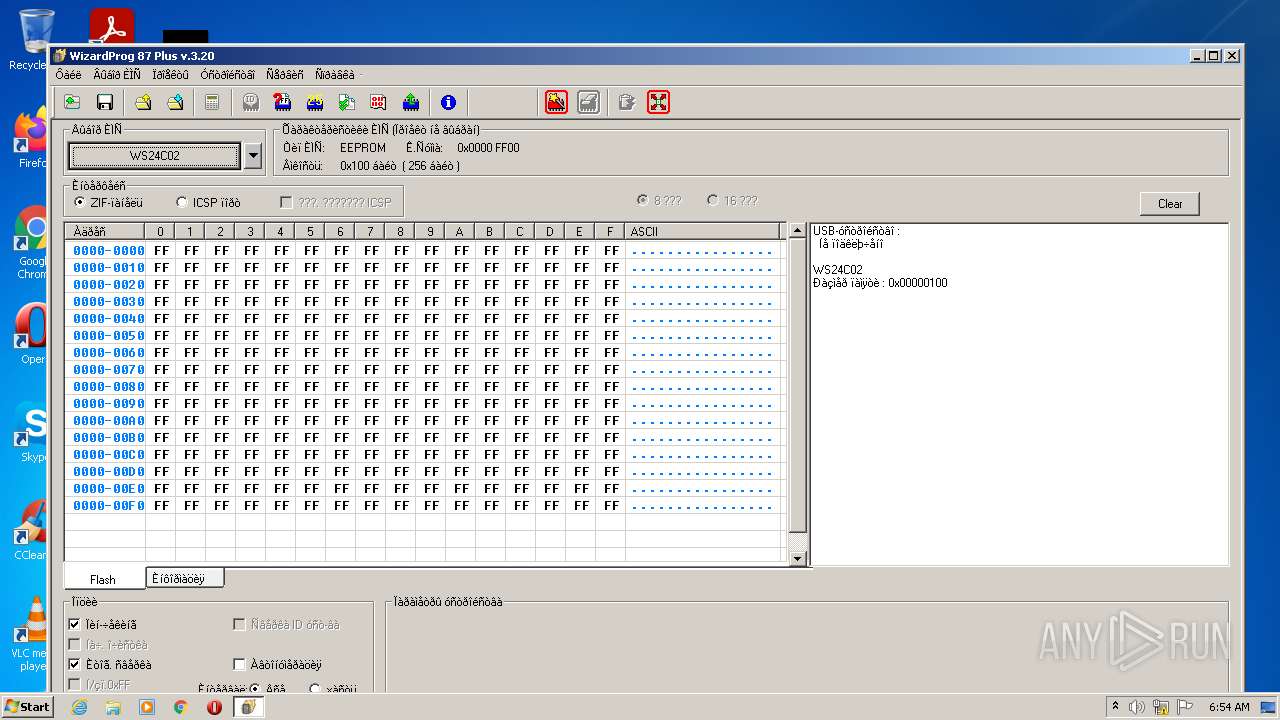
| ProductName: | WizardProg87Plus |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | WizardProg87Plus Setup |
| CompanyName: | WizardProg |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0x9a58 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 109056 |
| CodeSize: | 37376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | WizardProg |
| FileDescription: | WizardProg87Plus Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | WizardProg87Plus |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009174 | 0x00009200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56625 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73508 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00019834 | 0x00019A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.74917 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94378 | 1150 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.73459 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.78467 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.71584 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
47
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1820 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{49b1433e-f8ac-0ab3-3ee5-7c378719896f}\xgprowinusb.inf" "0" "68c15fea7" "000005C4" "WinSta0\Default" "0000058C" "208" "c:\wizardprog87plus\drv" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "C:\WizardProg87Plus\usbinst.exe" | C:\WizardProg87Plus\usbinst.exe | — | setup87plusV320.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2176 | "C:\WizardProg87Plus\drv\dpinst.exe" /LM /P | C:\WizardProg87Plus\drv\dpinst.exe | usbinst.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 256 Version: 2.1.1 Modules
| |||||||||||||||
| 2964 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{1cd27e98-4cec-6c27-0e58-1d569ee51a30} Global\{3602fde6-0298-3939-8ee9-0112ad242e6c} C:\Windows\System32\DriverStore\Temp\{79089764-a9c8-3381-ac0f-e260058d881c}\xgprowinusb.inf C:\Windows\System32\DriverStore\Temp\{79089764-a9c8-3381-ac0f-e260058d881c}\XgprowinusbX86.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
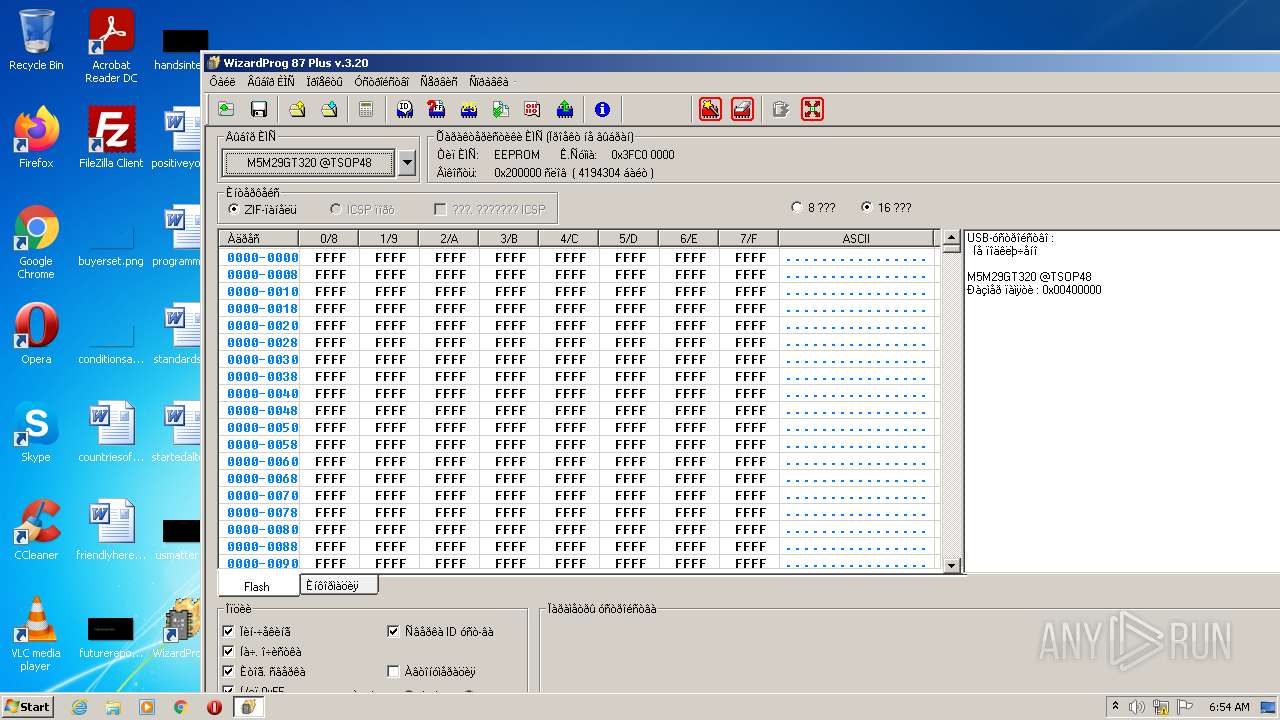
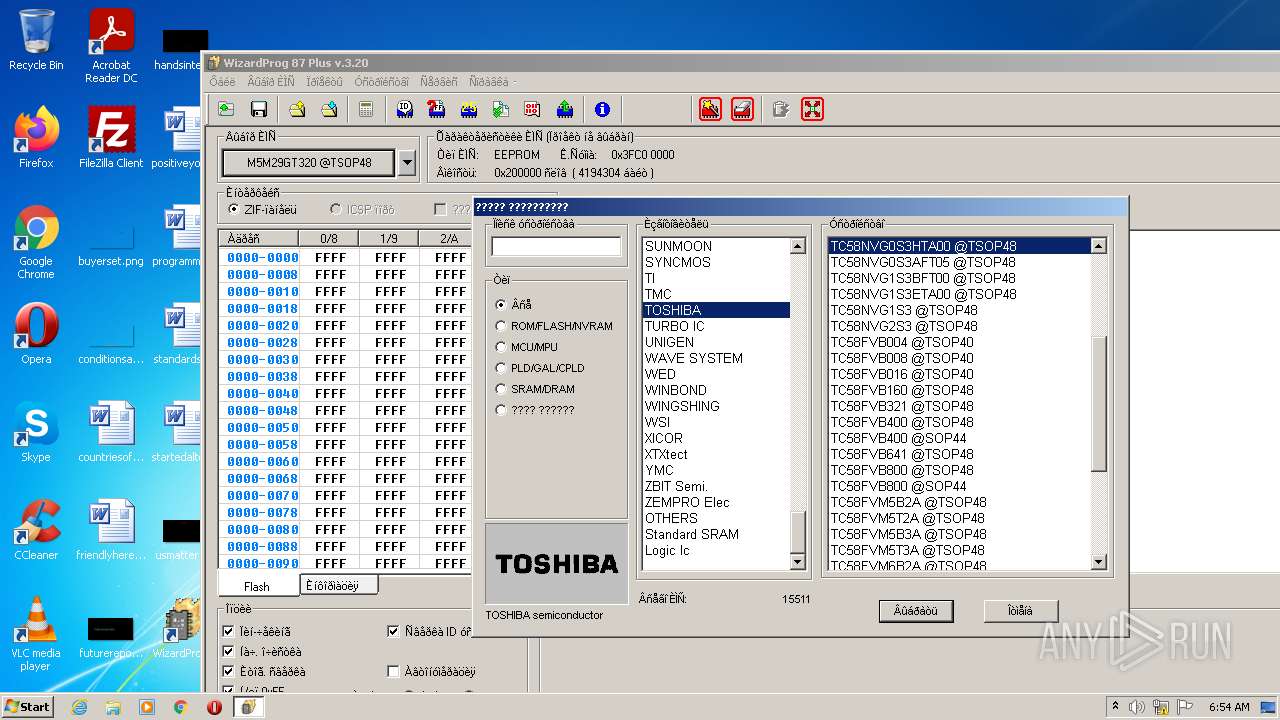
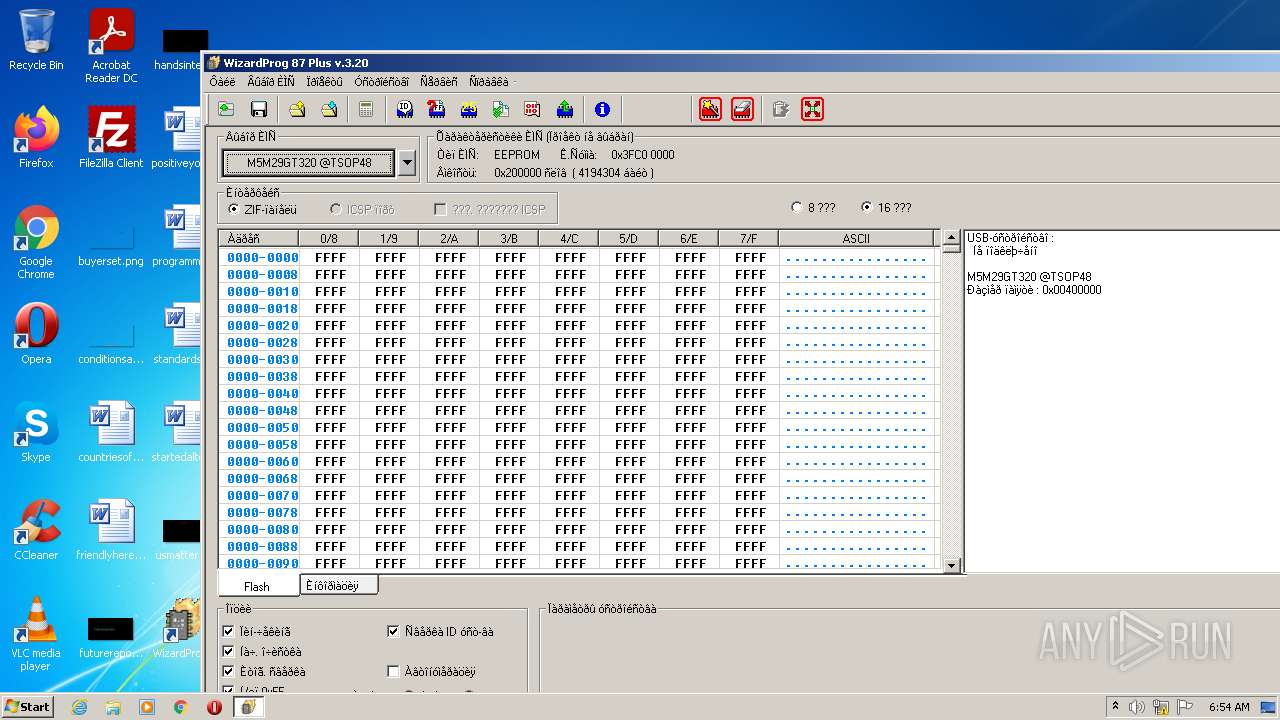
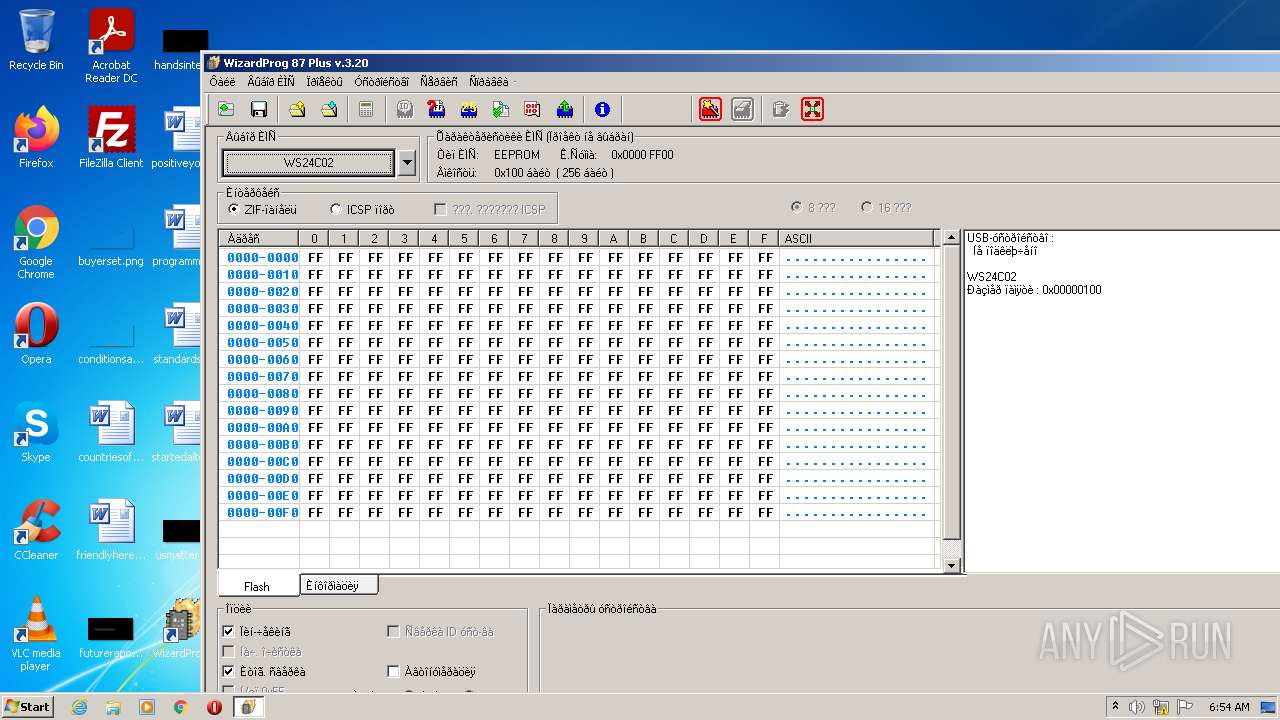
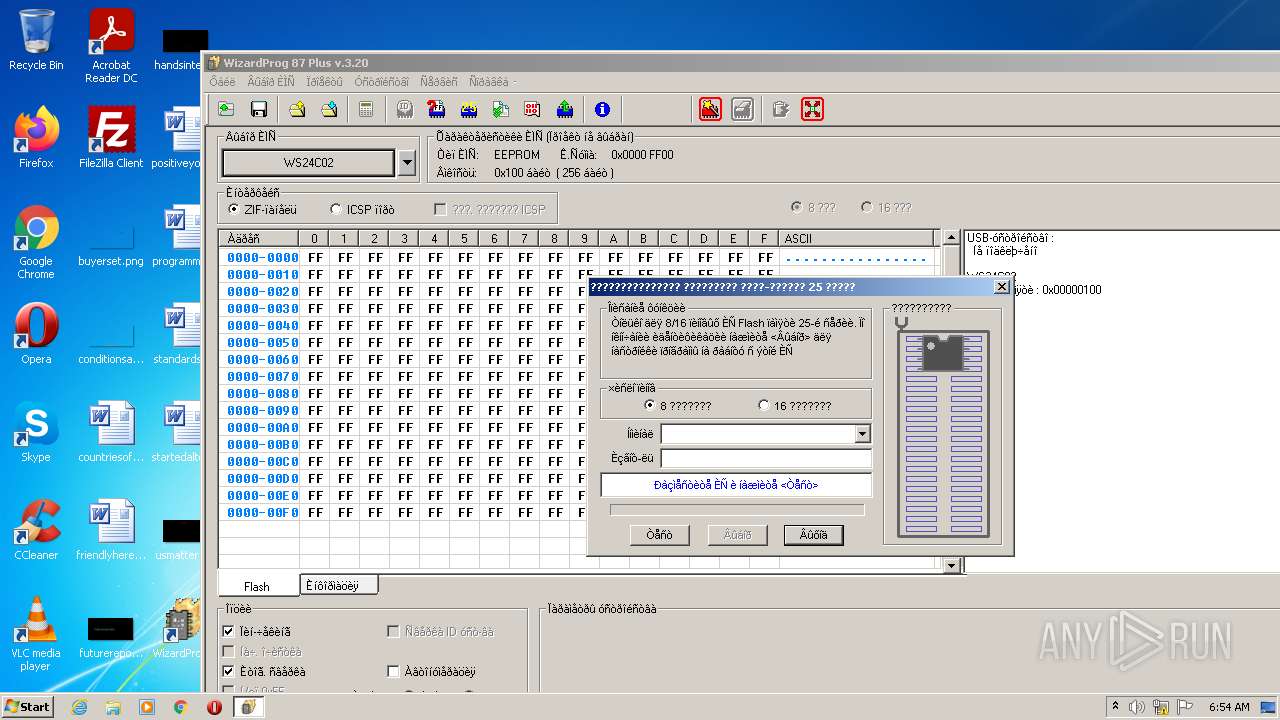
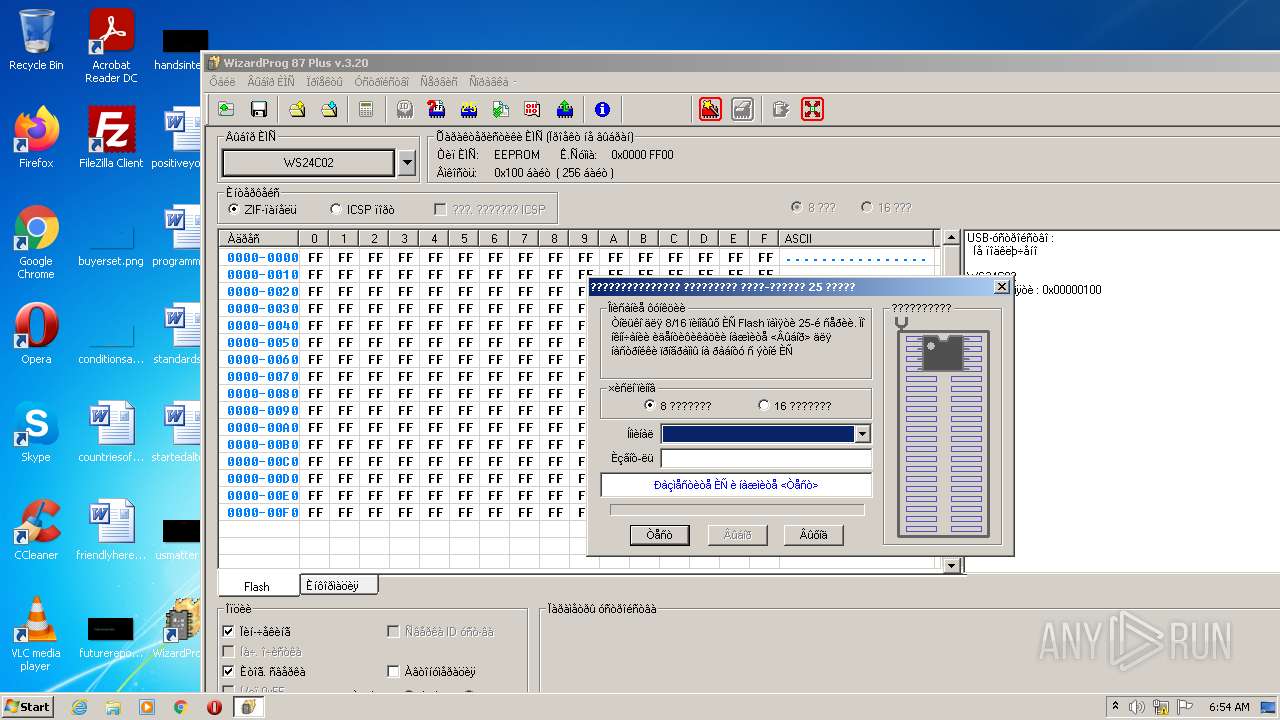
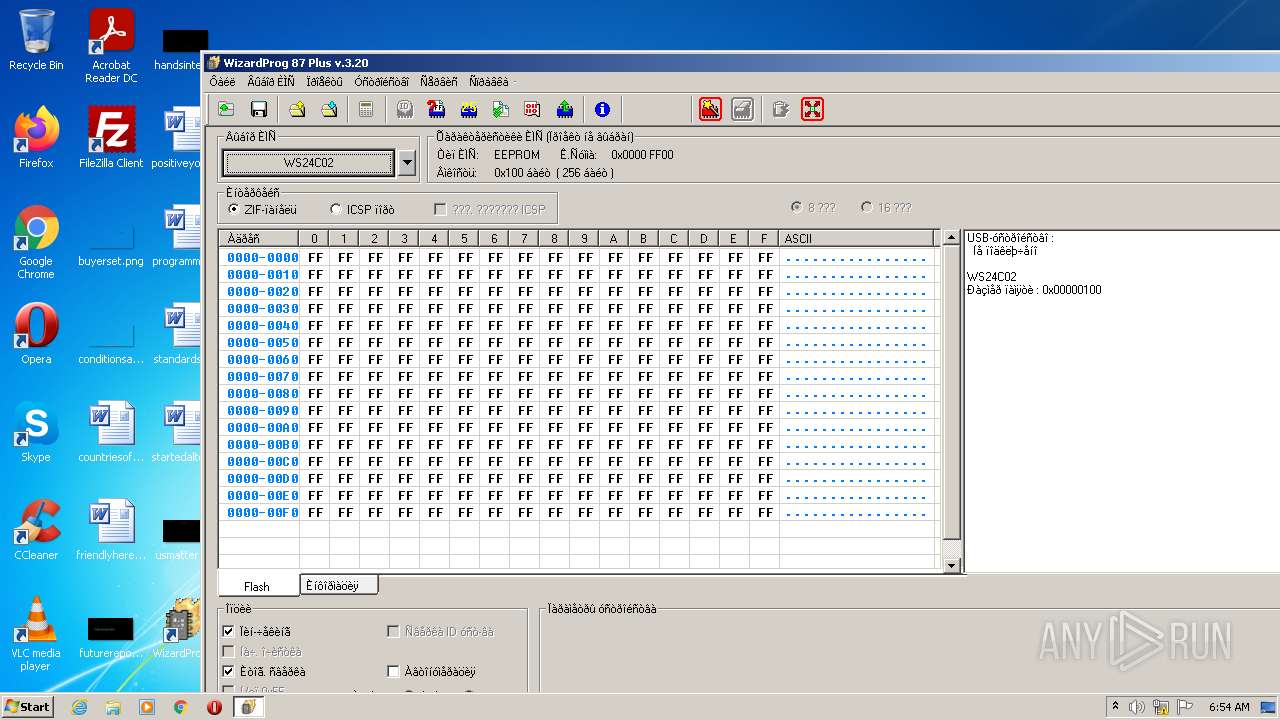
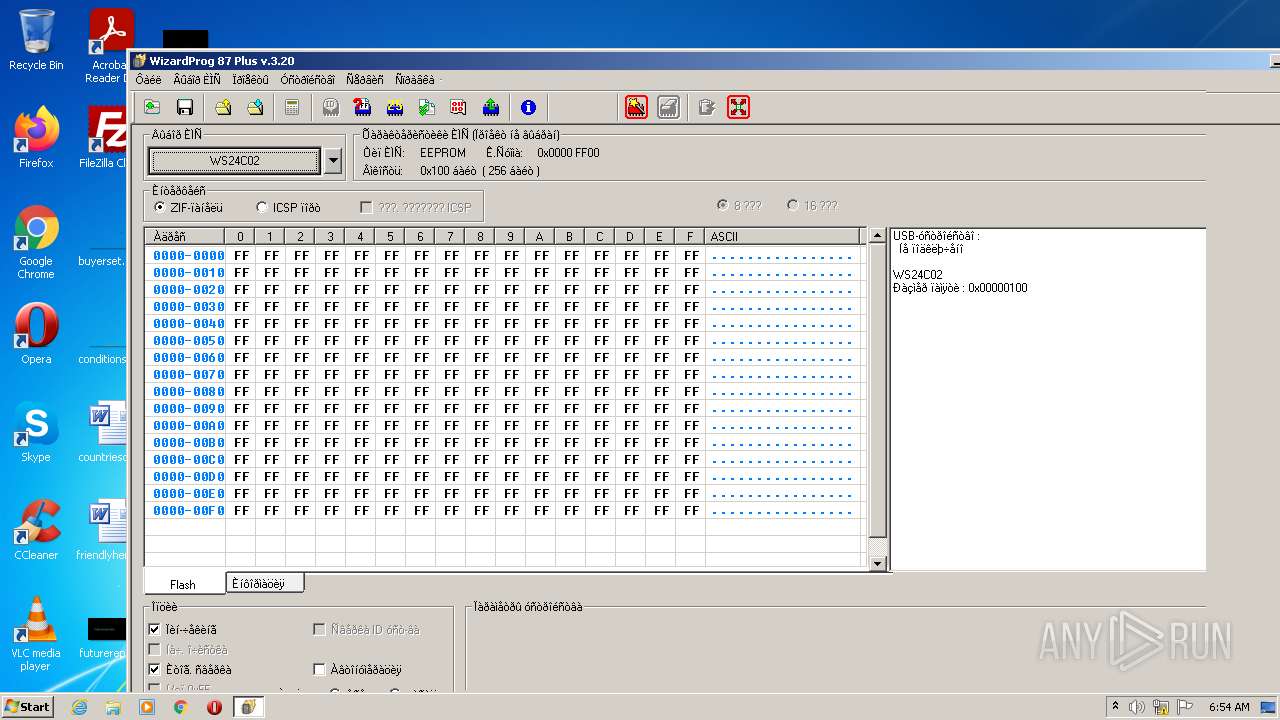
| 3056 | "C:\WizardProg87Plus\wp87plus.exe" | C:\WizardProg87Plus\wp87plus.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: WizardProg 87 Plus Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3352 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\Temp\is-MDFO5.tmp\setup87plusV320.tmp" /SL5="$20138,12905990,147456,C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe" | C:\Users\admin\AppData\Local\Temp\is-MDFO5.tmp\setup87plusV320.tmp | — | setup87plusV320.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\AppData\Local\Temp\is-K85FP.tmp\setup87plusV320.tmp" /SL5="$30130,12905990,147456,C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe" /SPAWNWND=$20134 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-K85FP.tmp\setup87plusV320.tmp | setup87plusV320.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe" /SPAWNWND=$20134 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe | setup87plusV320.tmp | ||||||||||||
User: admin Company: WizardProg Integrity Level: HIGH Description: WizardProg87Plus Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3876 | "C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe" | C:\Users\admin\AppData\Local\Temp\setup87plusV320.exe | Explorer.EXE | ||||||||||||
User: admin Company: WizardProg Integrity Level: MEDIUM Description: WizardProg87Plus Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
9 388
Read events
9 171
Write events
217
Delete events
0
Modification events
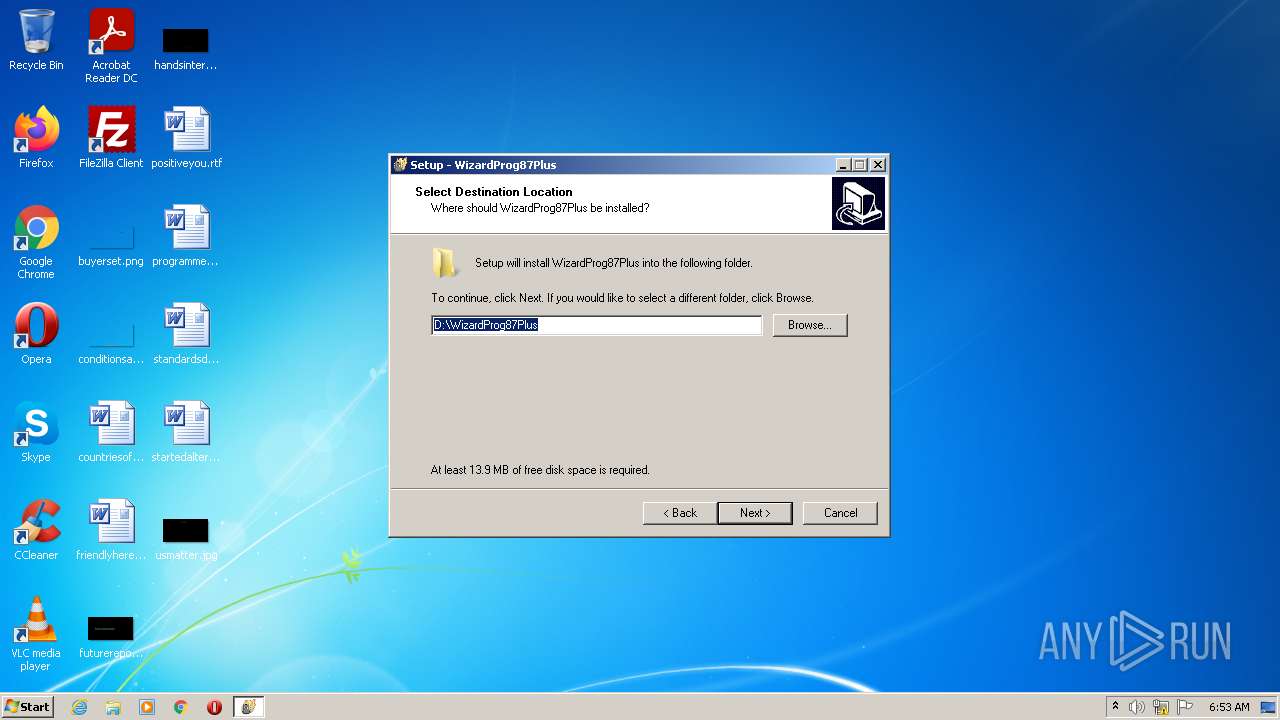
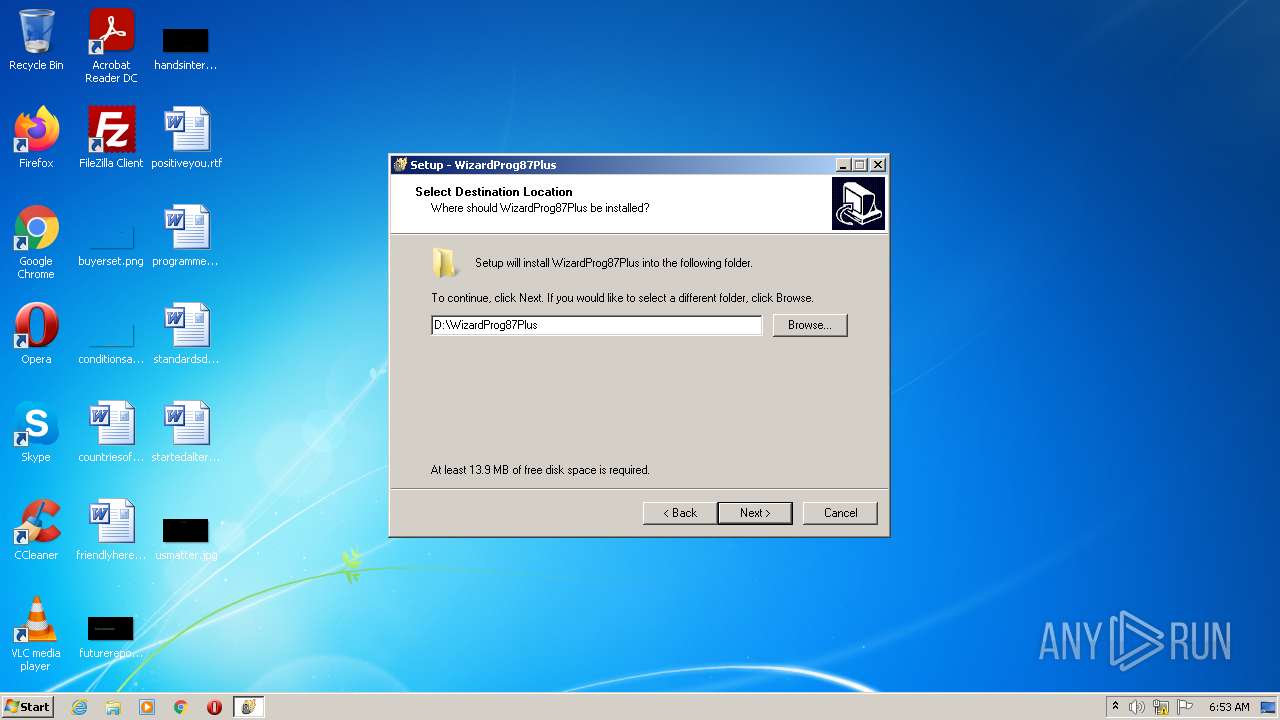
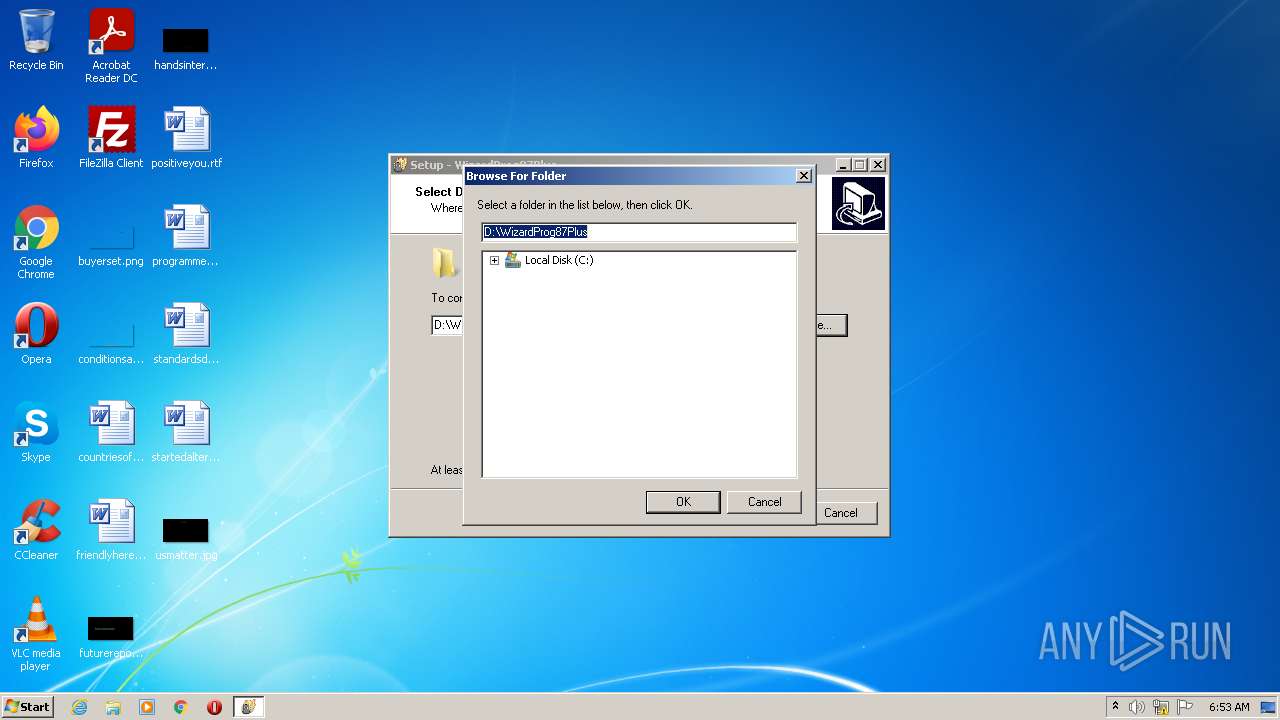
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.3 | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
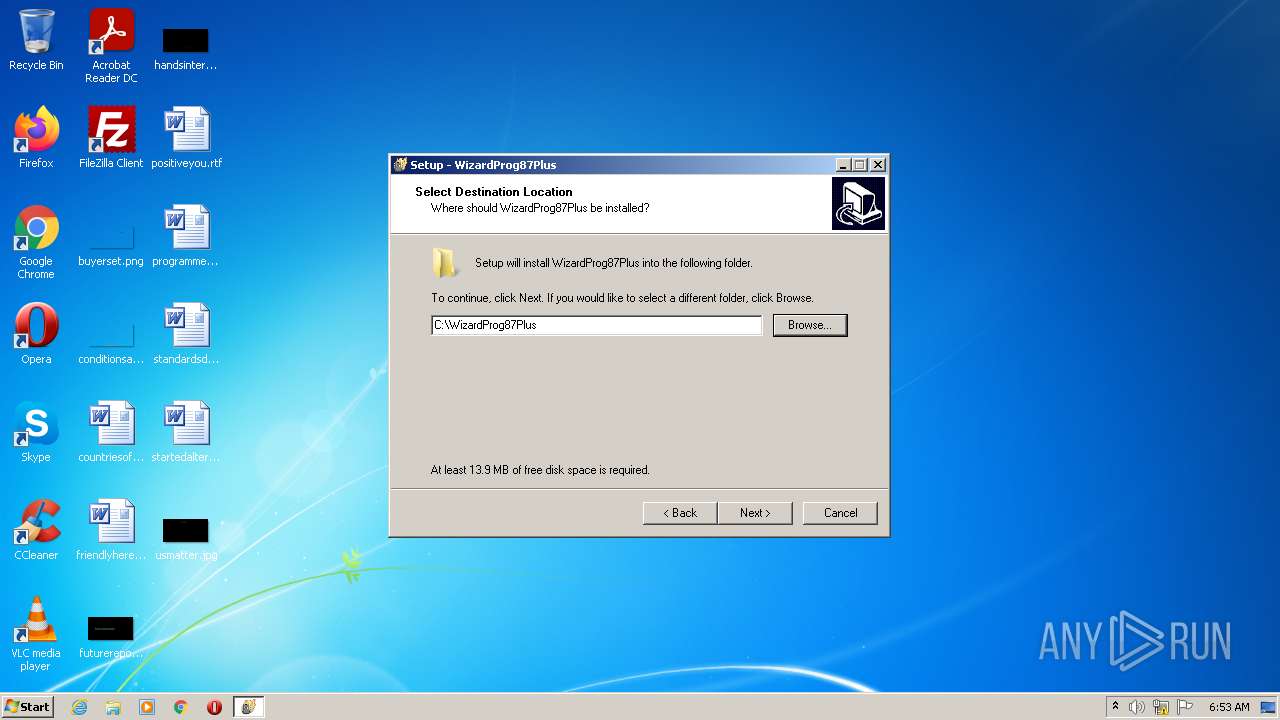
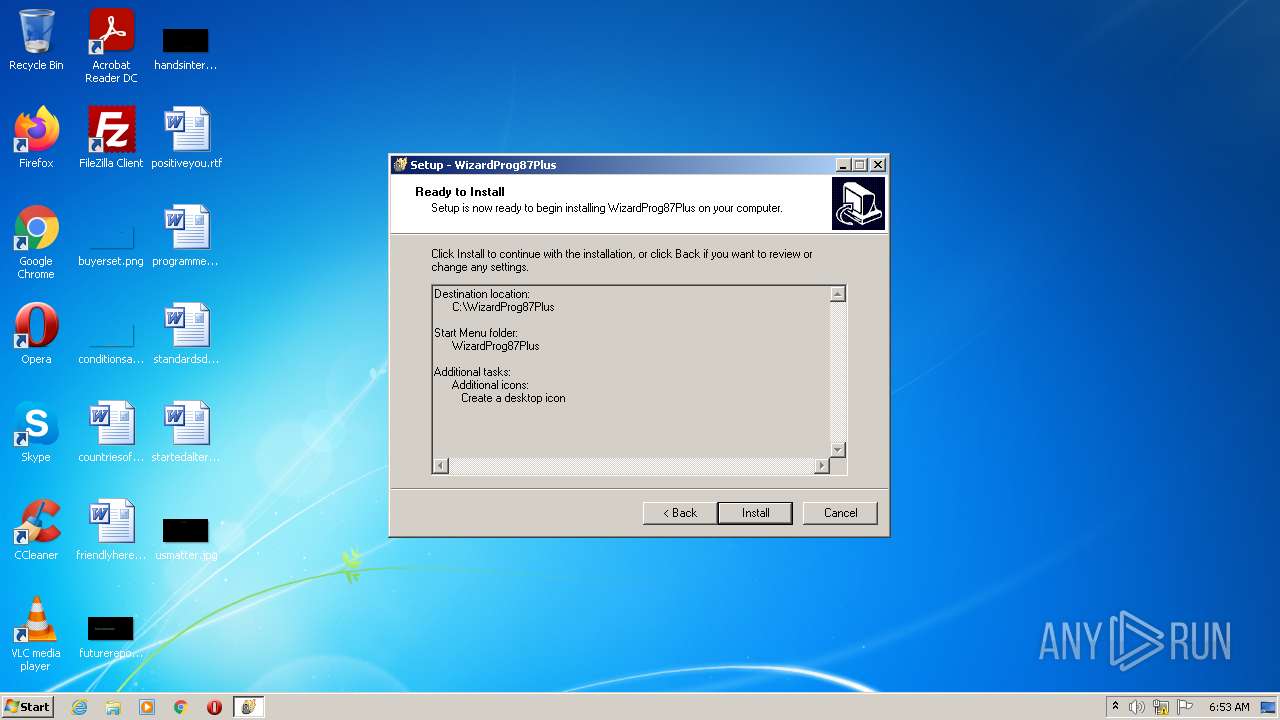
Value: C:\WizardProg87Plus | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\WizardProg87Plus\ | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: WizardProg87Plus | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: quicklaunchicon | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | DisplayName |
Value: WizardProg 87 Plus v.3.20 | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\WizardProg87Plus\unins000.exe" | |||
| (PID) Process: | (3564) setup87plusV320.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7C6BFC4A-69EF-4917-99E1-ADEDF3F74F72}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\WizardProg87Plus\unins000.exe" /SILENT | |||
Executable files
33
Suspicious files
26
Text files
62
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3876 | setup87plusV320.exe | C:\Users\admin\AppData\Local\Temp\is-MDFO5.tmp\setup87plusV320.tmp | executable | |
MD5:— | SHA256:— | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\is-7DOEO.tmp | executable | |
MD5:— | SHA256:— | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\wp87plus.exe | executable | |
MD5:— | SHA256:— | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\img\Adapter001.jpg | image | |
MD5:— | SHA256:— | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\drv\is-LAN0B.tmp | binary | |
MD5:BA82C7C8ECAAE5936D9A4B37F43A27CD | SHA256:3C4036915FA480D3BDEB9F365BE9D12451983AE496B7767E7EA8703AE0D7C980 | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\drv\Xgprowinusb.inf | binary | |
MD5:BA82C7C8ECAAE5936D9A4B37F43A27CD | SHA256:3C4036915FA480D3BDEB9F365BE9D12451983AE496B7767E7EA8703AE0D7C980 | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\drv\i386\is-RFNA7.tmp | executable | |
MD5:8E7B9F81E8823FEE2D82F7DE3A44300B | SHA256:EBE3B7708DD974EE87EFED3113028D266AF87CA8DBAE77C47C6F7612824D3D6C | |||
| 3564 | setup87plusV320.tmp | C:\Users\admin\AppData\Local\Temp\is-JGHNK.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3564 | setup87plusV320.tmp | C:\WizardProg87Plus\drv\is-T2QN3.tmp | cat | |
MD5:AF81015319DDBF1BD7DBA1F7952F630E | SHA256:5B2C98F0714589DC8EE0BDC9F0CBED1DD3429D9BFC50E26B40B86C9A98D22639 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report