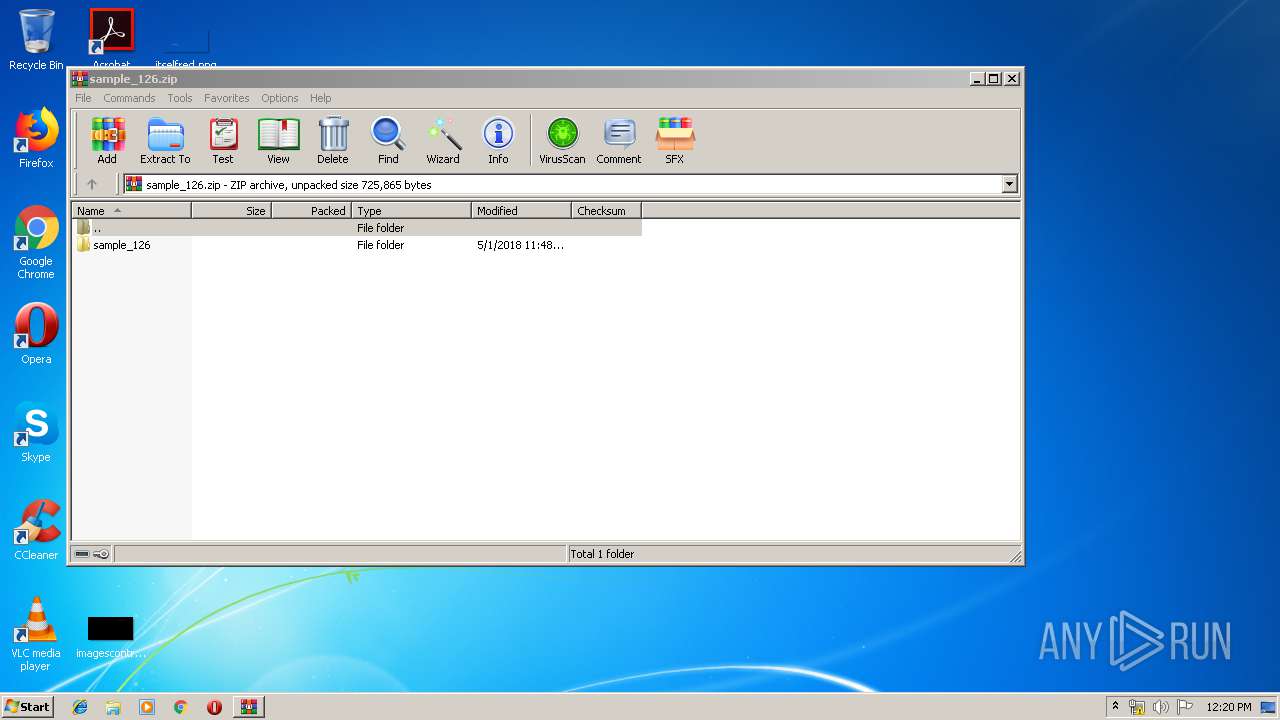
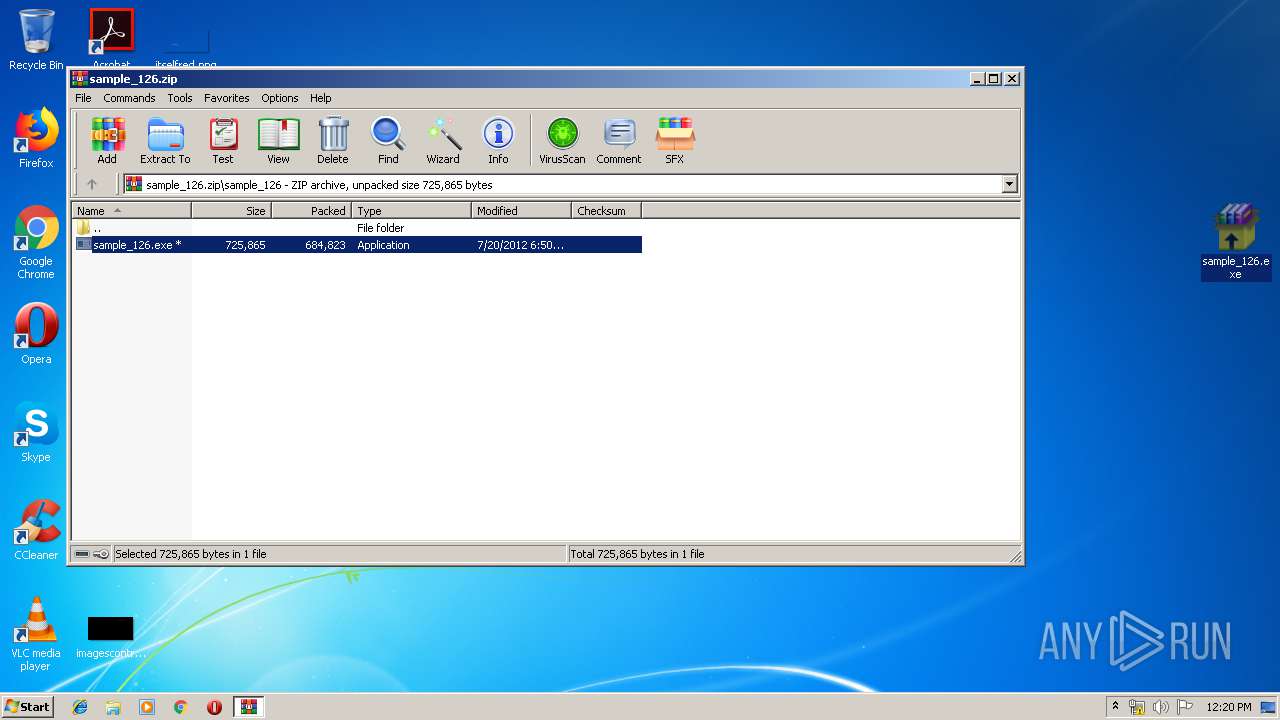
| File name: | sample_126.zip |
| Full analysis: | https://app.any.run/tasks/51986585-d825-46c9-adda-71085ae9965b |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:20:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4B5EDB3C9D6FD125C1641707489BE5A5 |
| SHA1: | 3F3A61C82AFD2F1CA7CE6CABBC65511D8D829ED5 |
| SHA256: | 0835382BA5F66511C4521D2670F462E6D41DA8F64AFF1E7C8BD4BC6DA2D7D1C0 |
| SSDEEP: | 12288:+XhY+Iyrru/6lKZ77PWGM6C5UN25ApsIT8fCrdZdQgmSZ4LmGL7cXVhuPNzmu:uIyWUKN7HMH5il8AdZdBP4LmGL7Tcu |
MALICIOUS
Application was dropped or rewritten from another process
- sample_126.exe (PID: 2468)
- cstart.exe (PID: 2244)
- cmin.exe (PID: 1240)
- gmin.exe (PID: 3236)
SUSPICIOUS
Creates files in the user directory
- sample_126.exe (PID: 2468)
- cmin.exe (PID: 1240)
Executable content was dropped or overwritten
- sample_126.exe (PID: 2468)
INFO
Manual execution by user
- sample_126.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_126/ |
Total processes
38
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1240 | C:\Users\admin\AppData\Roaming\cmin.exe -o http://coinobot.2:1234@us.ozco.in:8332 -g no | C:\Users\admin\AppData\Roaming\cmin.exe | cstart.exe | ||||||||||||
User: admin Company: Ufasoft Integrity Level: MEDIUM Description: bitcoin-miner Exit code: 0 Version: 7.0.2239.0 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\AppData\Roaming\cstart.exe" | C:\Users\admin\AppData\Roaming\cstart.exe | — | sample_126.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\Desktop\sample_126.exe" | C:\Users\admin\Desktop\sample_126.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3236 | C:\Users\admin\AppData\Roaming\gmin.exe -o http://us.ozco.in:8332 -u coinobot.2 -p 1234 -T | C:\Users\admin\AppData\Roaming\gmin.exe | — | cstart.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
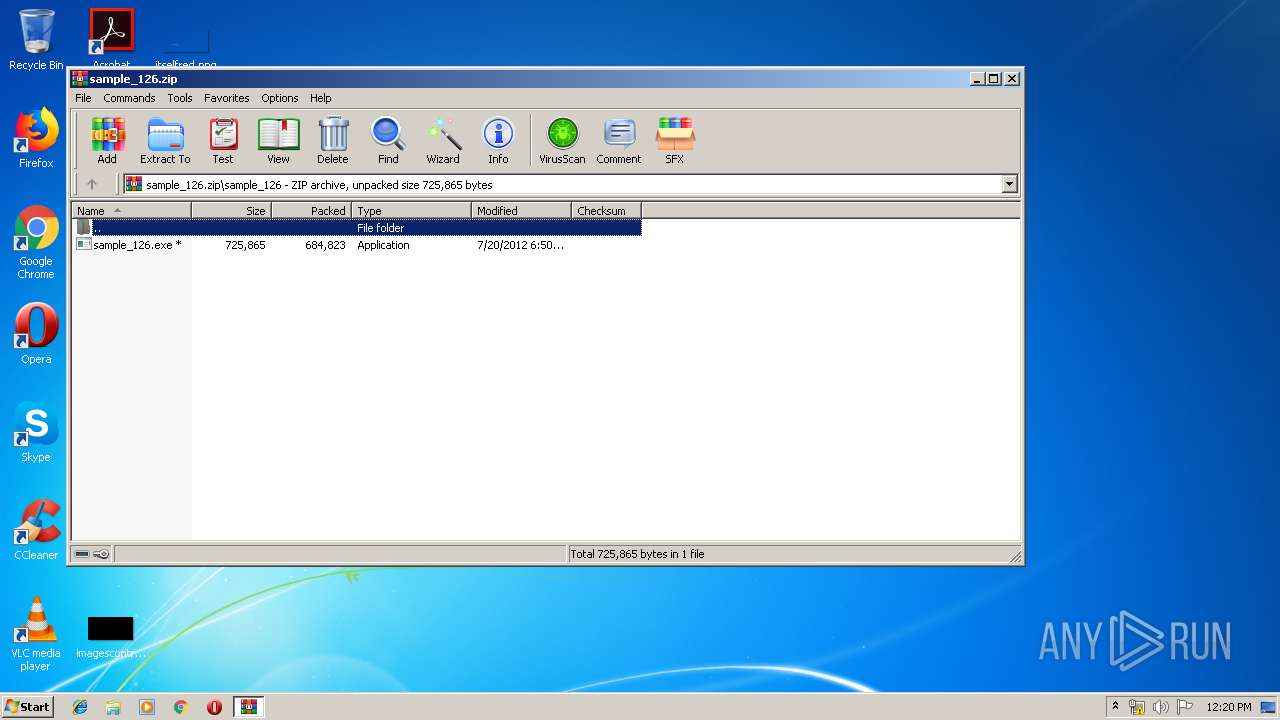
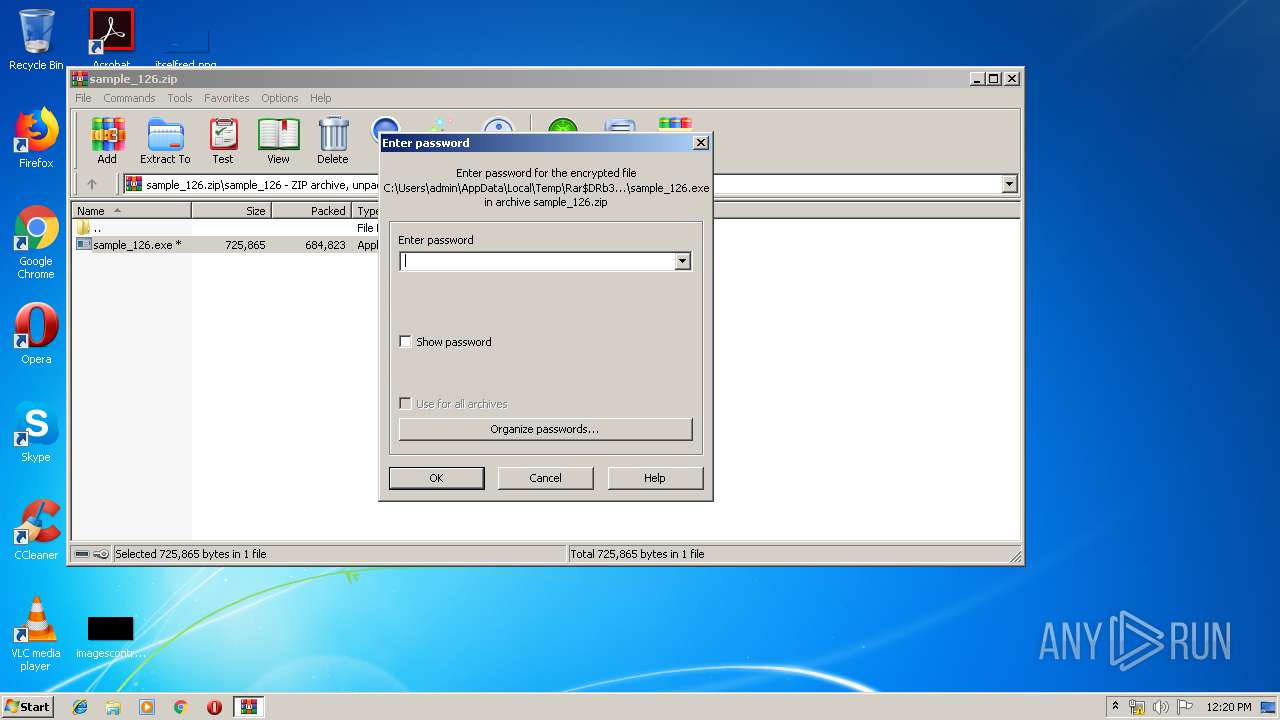
| 3612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_126.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
823
Read events
791
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_126.zip | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2468) sample_126.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Roaming |
Value: C:\Users\admin\AppData\Roaming | |||
Executable files
7
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3612.44175\sample_126\sample_126.exe | — | |
MD5:— | SHA256:— | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\gmin.exe | executable | |
MD5:01AA8F9282D12692A24FFD7D0DBB82CD | SHA256:C5CC8B958A2A2943561F1D9800B0D86EA7D0B7CC40EA78557257D551ABF3F650 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\poclbm120327.cl | text | |
MD5:0470182A132F73E9FEAACAB82F8274FE | SHA256:55851C4FC6457F7D83E15202CB2E0A894B363B3F15F505AB72991ED83F639BC3 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\diablo120328.cl | text | |
MD5:8BA9AB1F34BA302D7770BBE2F81560DB | SHA256:5A133391C497C15B581DAD364D30784B7E0C5A9C98DC4859A8BAE14D6E7B1A15 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\phatk120223.cl | text | |
MD5:8B3C553D0FBA4474261DD07D1FE57EAB | SHA256:B170C5AEBB94156FA7D84F67D3003611039BED163DB00B95A94C5FB6ED4B8C1C | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\pthreadGC2.dll | executable | |
MD5:8BC13C002F91CFF22A17F5A5191C1292 | SHA256:97C1A2CABFE69B987732A1502DAC6CCE9C6E31F6F7E9142FC4BC8D92077F2DA3 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\libcurl-4.dll | executable | |
MD5:7FEF219621CD9717A1D7FCC537DC9FBE | SHA256:F23D2ABF2C96813054DF51212F74FABBBB2D707A6B477CB2CF1D52D316A26302 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\libpdcurses.dll | executable | |
MD5:1B364EC27B6F4F8879DABADB096A4F64 | SHA256:94995B0560D2CCDA7951252397EB152B499454746B75D03479BBFA551DEF41E4 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\diakgcn120427.cl | text | |
MD5:961444A36167A43CBA15DC65587F31A9 | SHA256:D393CD16ABF3CE58533DF73A7155EE74F3E7DCDEEFB5CAF16426FBD67E0D1507 | |||
| 2468 | sample_126.exe | C:\Users\admin\AppData\Roaming\libusb-1.0.dll | executable | |
MD5:7F2523DEC5FA92C70F3AB13765D799FF | SHA256:7CEB91390AC581B78BE8A18A6EEBF7F9124A2460C4F9849EE4C75EC303412062 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1240 | cmin.exe | 185.53.178.9:8332 | us.ozco.in | Team Internet AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
us.ozco.in |
| malicious |