| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/1f73cff2-1087-4da3-88d7-2e747f867ac5 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 06:24:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0E97B7EA2DA5AAD0ADFA11BE30B7F14C |
| SHA1: | 3C5798030EE399588FDE8FE5660499762BD11305 |
| SHA256: | 0810F09E46C9E8C309E902A0835165EE9DAF21FBDB318C642BF1984BFC486C87 |
| SSDEEP: | 49152:WcsQ6Q1JfTQ5XLtuEL4UEKnCiuBRJxdKigPuEy9gmjn:W1QTf0Xo3zjdKigPLylT |
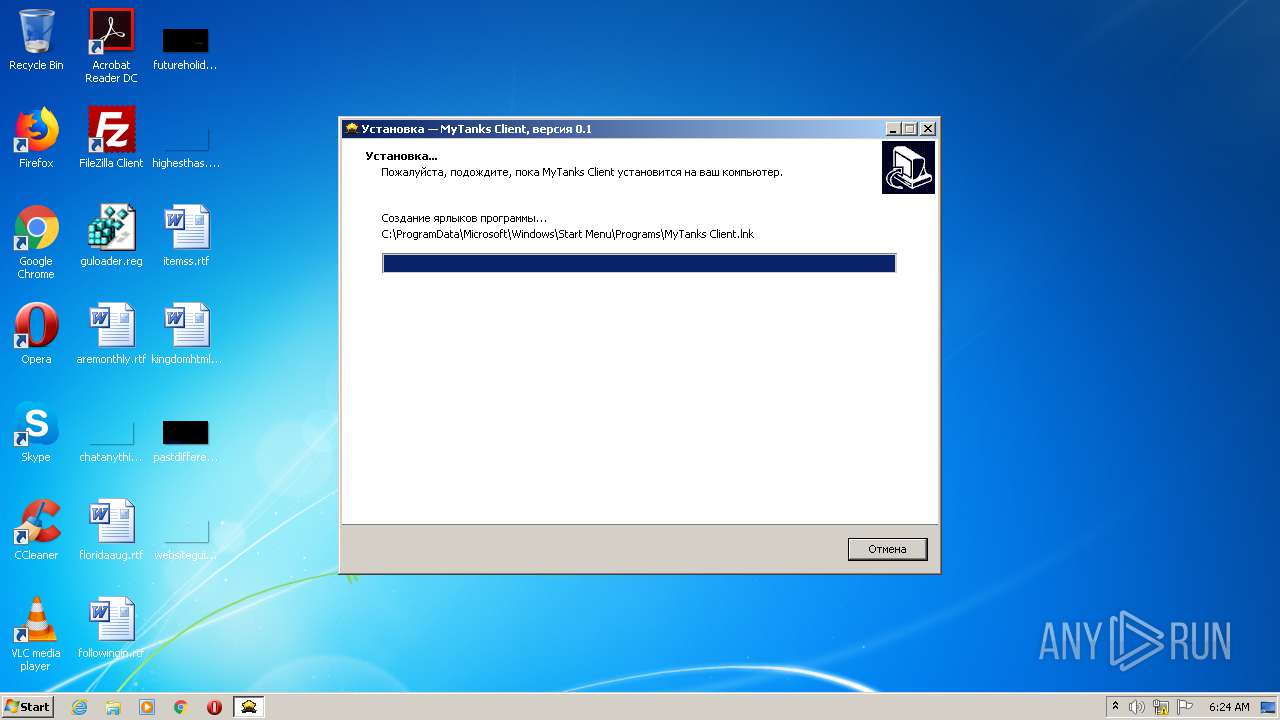
MALICIOUS
Drops executable file immediately after starts
- setup.exe (PID: 1680)
Application was dropped or rewritten from another process
- MyTanks.exe (PID: 2688)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 1680)
- setup.exe (PID: 2392)
- setup.tmp (PID: 2260)
- MyTanks.exe (PID: 2688)
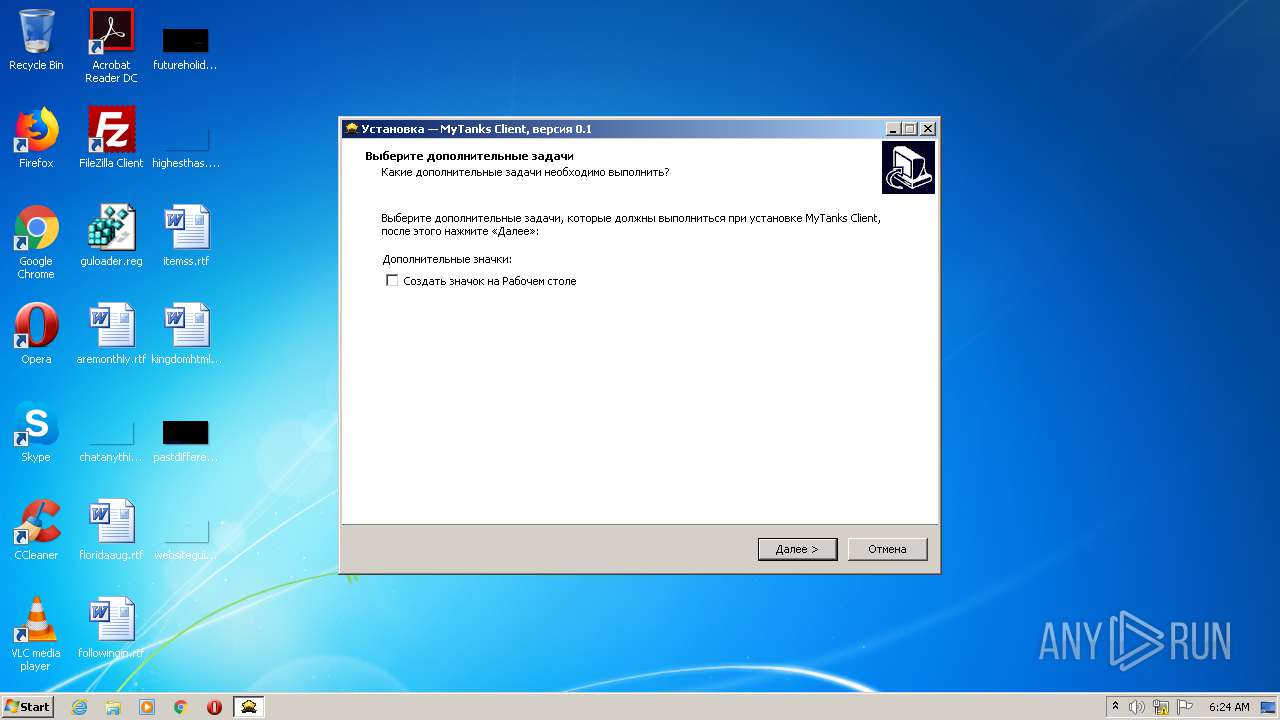
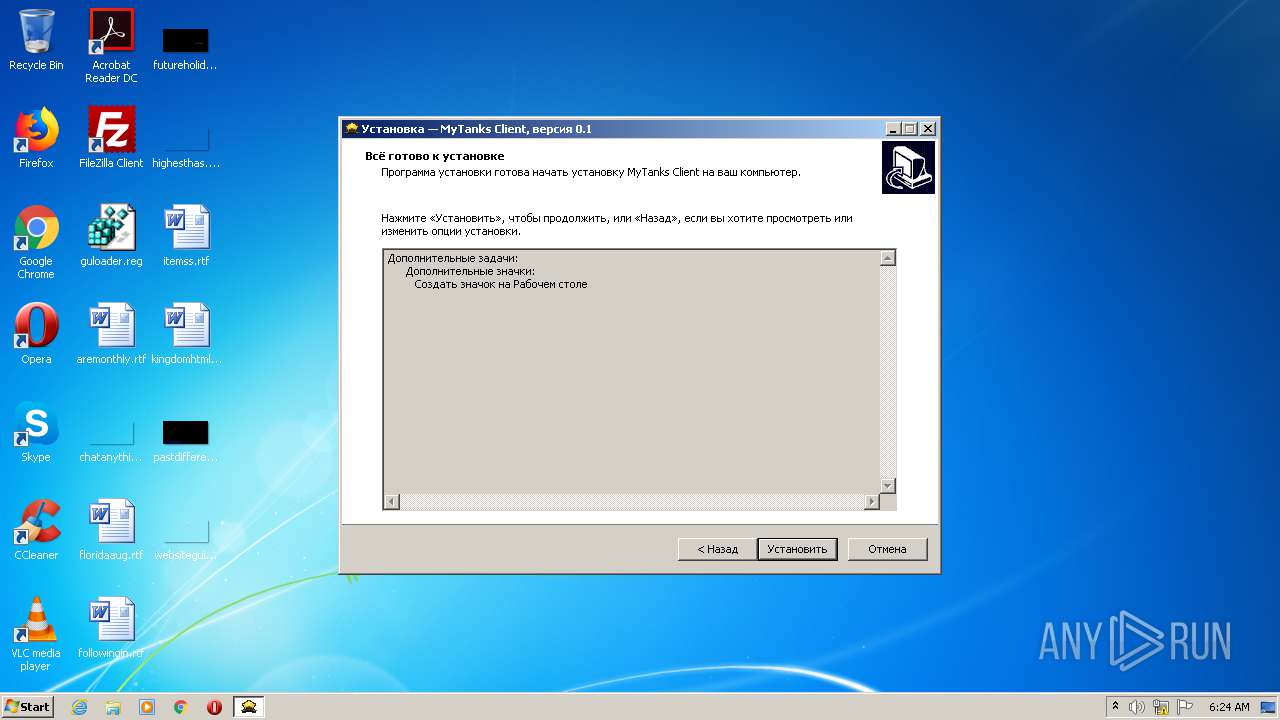
Creates files in the user directory
- setup.tmp (PID: 2260)
- MyTanks.exe (PID: 2688)
Reads the Windows organization settings
- setup.tmp (PID: 2260)
Reads Windows owner or organization settings
- setup.tmp (PID: 2260)
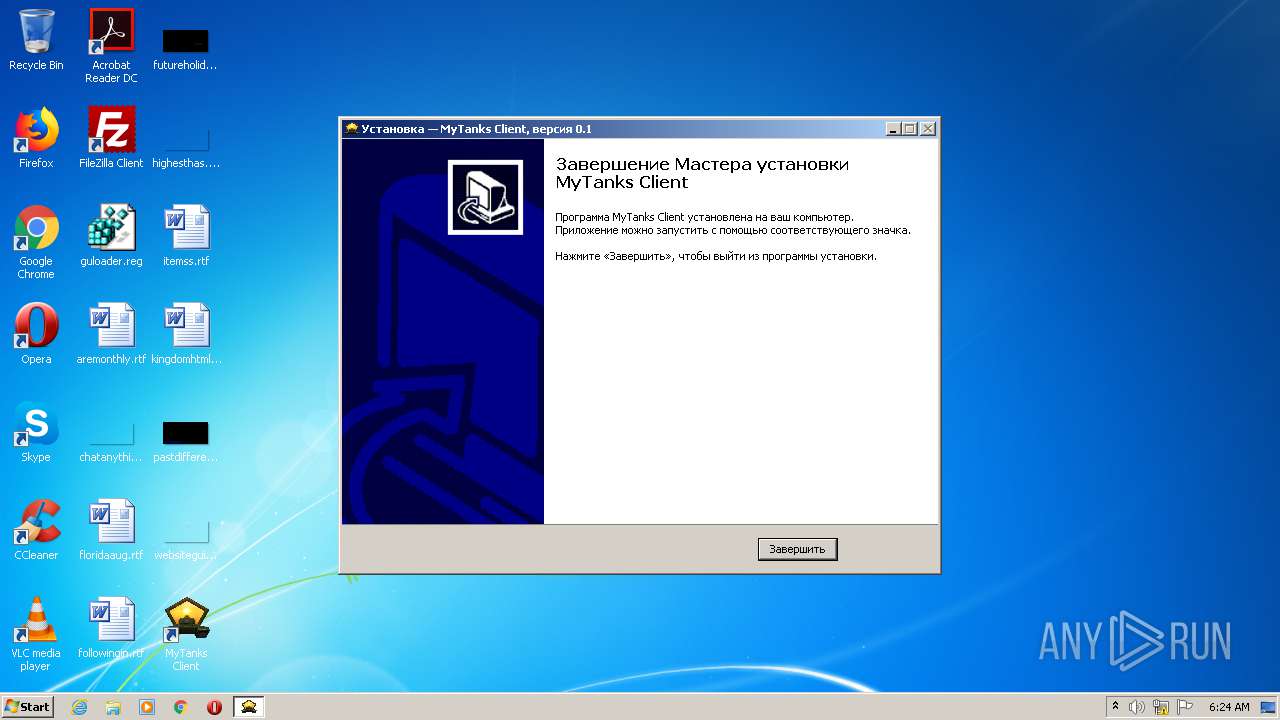
Creates a directory in Program Files
- setup.tmp (PID: 2260)
Drops a file with too old compile date
- setup.tmp (PID: 2260)
Drops a file that was compiled in debug mode
- setup.tmp (PID: 2260)
- MyTanks.exe (PID: 2688)
Reads Environment values
- MyTanks.exe (PID: 2688)
INFO
Application was dropped or rewritten from another process
- setup.tmp (PID: 3020)
- setup.tmp (PID: 2260)
Creates files in the program directory
- setup.tmp (PID: 2260)
Creates a software uninstall entry
- setup.tmp (PID: 2260)
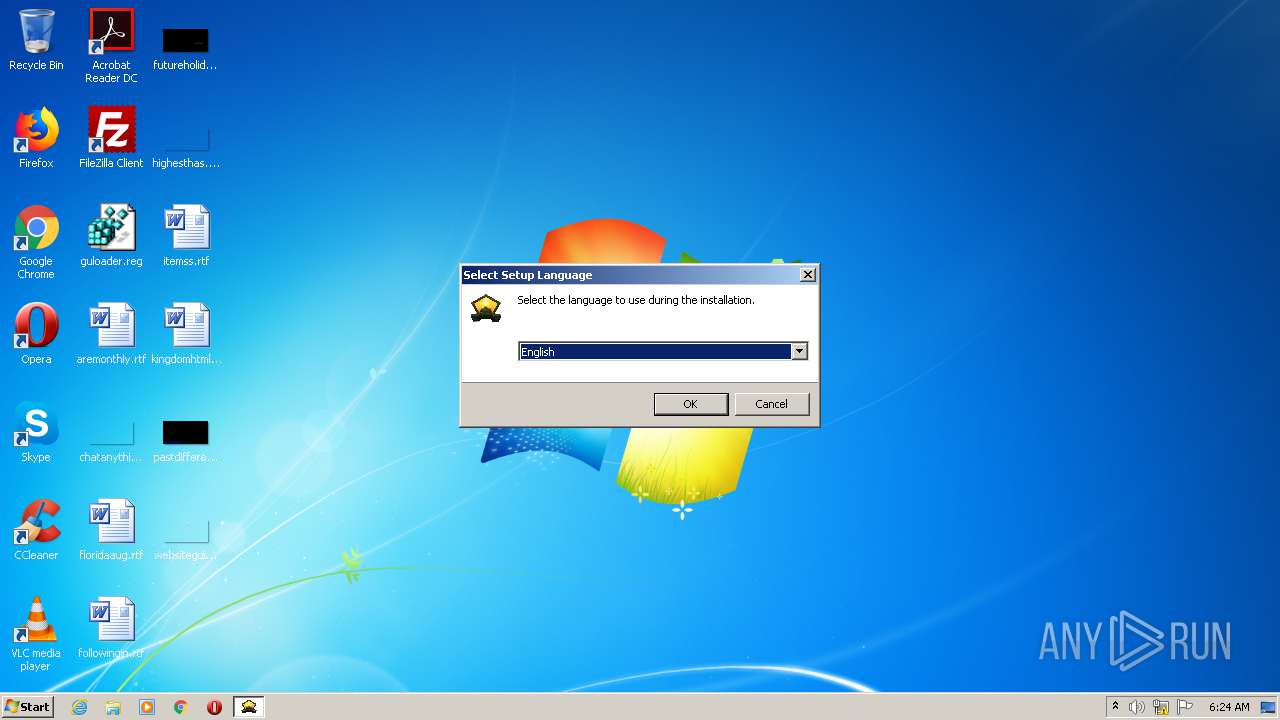
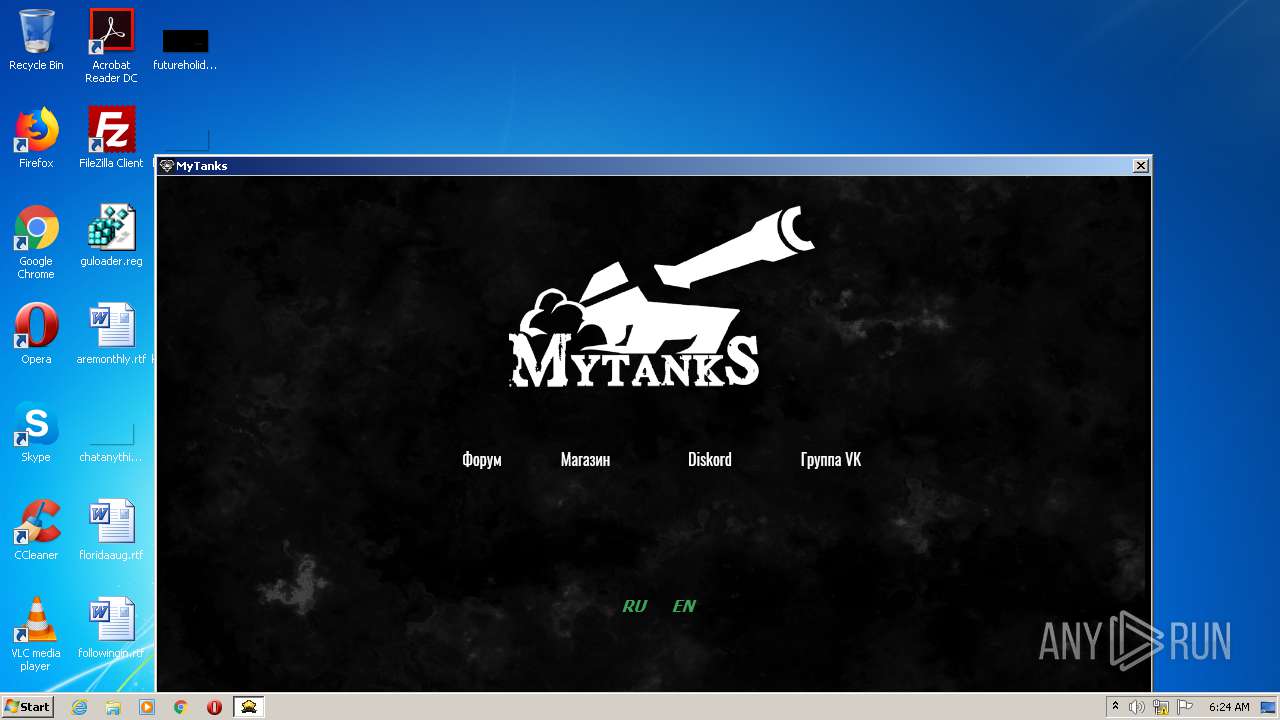
Manual execution by user
- MyTanks.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 13:15:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 99328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | MyTanks |
| FileDescription: | MyTanks Client Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | MyTanks Client |
| ProductVersion: | 0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Oct-2019 11:15:57 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | MyTanks |
| FileDescription: | MyTanks Client Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | MyTanks Client |
| ProductVersion: | 0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 12-Oct-2019 11:15:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E8 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36928 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95181 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.03517 |
.bss | 0x000AD000 | 0x00006778 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37999 |
.rsrc | 0x000B9000 | 0x00013574 | 0x00013600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.69673 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.15425 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.31895 | 884 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.28786 | 920 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053AC0 |
Total processes
45
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1680 | "C:\Users\admin\AppData\Local\Temp\setup.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\setup.exe | setup.tmp | ||||||||||||
User: admin Company: MyTanks Integrity Level: HIGH Description: MyTanks Client Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Temp\is-D8FE7.tmp\setup.tmp" /SL5="$3013A,1794419,782848,C:\Users\admin\AppData\Local\Temp\setup.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-D8FE7.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: MyTanks Integrity Level: MEDIUM Description: MyTanks Client Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Roaming\MyTanks Client\MyTanks.exe" | C:\Users\admin\AppData\Roaming\MyTanks Client\MyTanks.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: MyTanks Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\is-374RM.tmp\setup.tmp" /SL5="$20138,1794419,782848,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-374RM.tmp\setup.tmp | — | setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
788
Read events
740
Write events
42
Delete events
6
Modification events
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D40800001872F36FE1C6D601 | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 120786E8B73089A8D08D8C3F3694D5E30221A8627663392AFE3C098A86C41BA7 | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Roaming\MyTanks Client\MyTanks.exe | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: A305C4D1604A00CC16535CCC5EF539234E320BB50D3ABD0B7E0EE917B35C1A0D | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{B4609337-C93C-48D0-BB51-B39A5227F4E3}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.3 (u) | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{B4609337-C93C-48D0-BB51-B39A5227F4E3}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\MyTanks Client | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{B4609337-C93C-48D0-BB51-B39A5227F4E3}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\MyTanks Client\ | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{B4609337-C93C-48D0-BB51-B39A5227F4E3}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (2260) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{B4609337-C93C-48D0-BB51-B39A5227F4E3}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
5
Suspicious files
1
Text files
12
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2260 | setup.tmp | C:\Program Files\MyTanks Client\is-QN39Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2260 | setup.tmp | C:\Users\admin\AppData\Roaming\MyTanks Client\is-RC4RV.tmp | — | |
MD5:— | SHA256:— | |||
| 2260 | setup.tmp | C:\Users\admin\AppData\Roaming\MyTanks Client\is-632B2.tmp | — | |
MD5:— | SHA256:— | |||
| 2688 | MyTanks.exe | C:\Users\admin\AppData\Roaming\mytanks.client.Standlone\Local Store\cache\client.zip | — | |
MD5:— | SHA256:— | |||
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-374RM.tmp\setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 2260 | setup.tmp | C:\Users\admin\AppData\Roaming\MyTanks Client\MyTanks.exe | executable | |
MD5:— | SHA256:— | |||
| 1680 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-D8FE7.tmp\setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 2688 | MyTanks.exe | C:\Users\admin\AppData\Roaming\MyTanks Client\battles.swf | — | |
MD5:— | SHA256:— | |||
| 2260 | setup.tmp | C:\Program Files\MyTanks Client\unins000.dat | dat | |
MD5:— | SHA256:— | |||
| 2688 | MyTanks.exe | C:\Users\admin\AppData\Roaming\mytanks.client.Standlone\Local Store\cache\version.txt_web | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2688 | MyTanks.exe | GET | — | 45.87.3.232:80 | http://mytanksupdate.org/update/resources.zip | unknown | — | — | suspicious |
2688 | MyTanks.exe | GET | 200 | 45.87.3.232:80 | http://mytanksupdate.org/update/client.zip | unknown | compressed | 6.80 Mb | suspicious |
2688 | MyTanks.exe | GET | 200 | 45.87.3.232:80 | http://mytanksupdate.org/update/version.txt | unknown | text | 3 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | MyTanks.exe | 45.87.3.232:80 | mytanksupdate.org | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mytanksupdate.org |
| suspicious |
Threats
1 ETPRO signatures available at the full report