| File name: | geek.exe |
| Full analysis: | https://app.any.run/tasks/d5517c53-906b-4556-b006-d8a875ee33e2 |
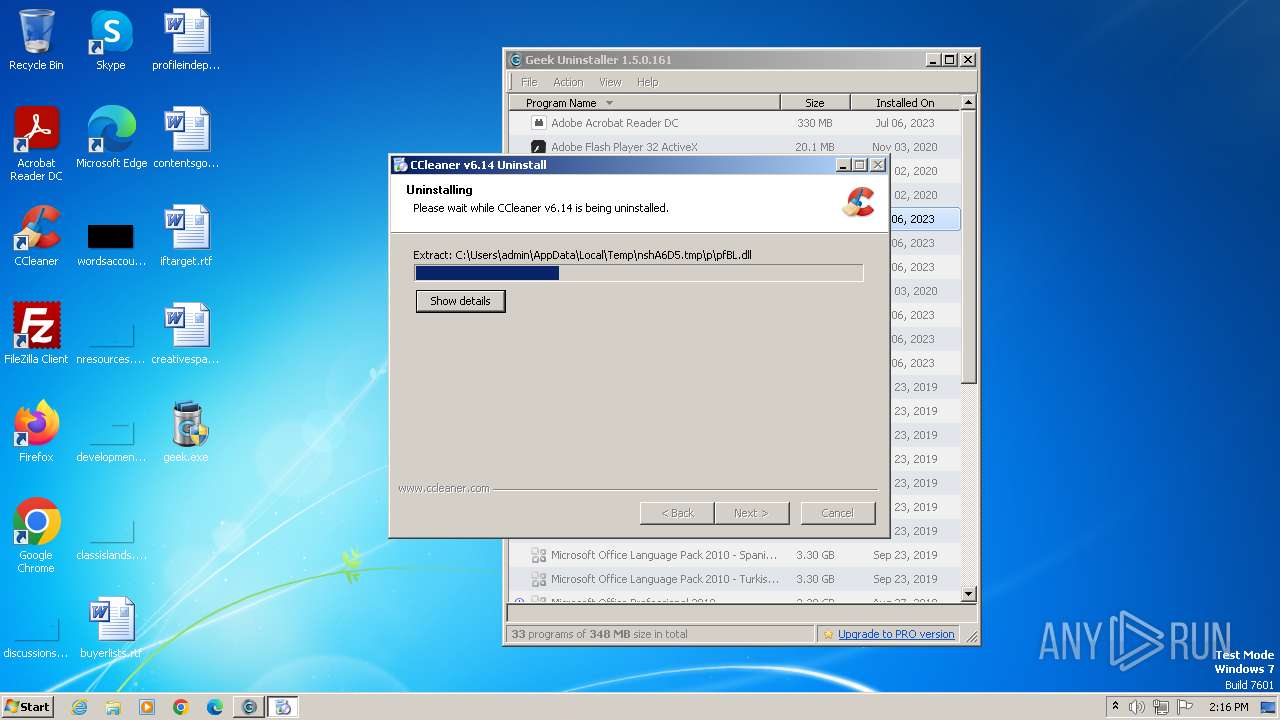
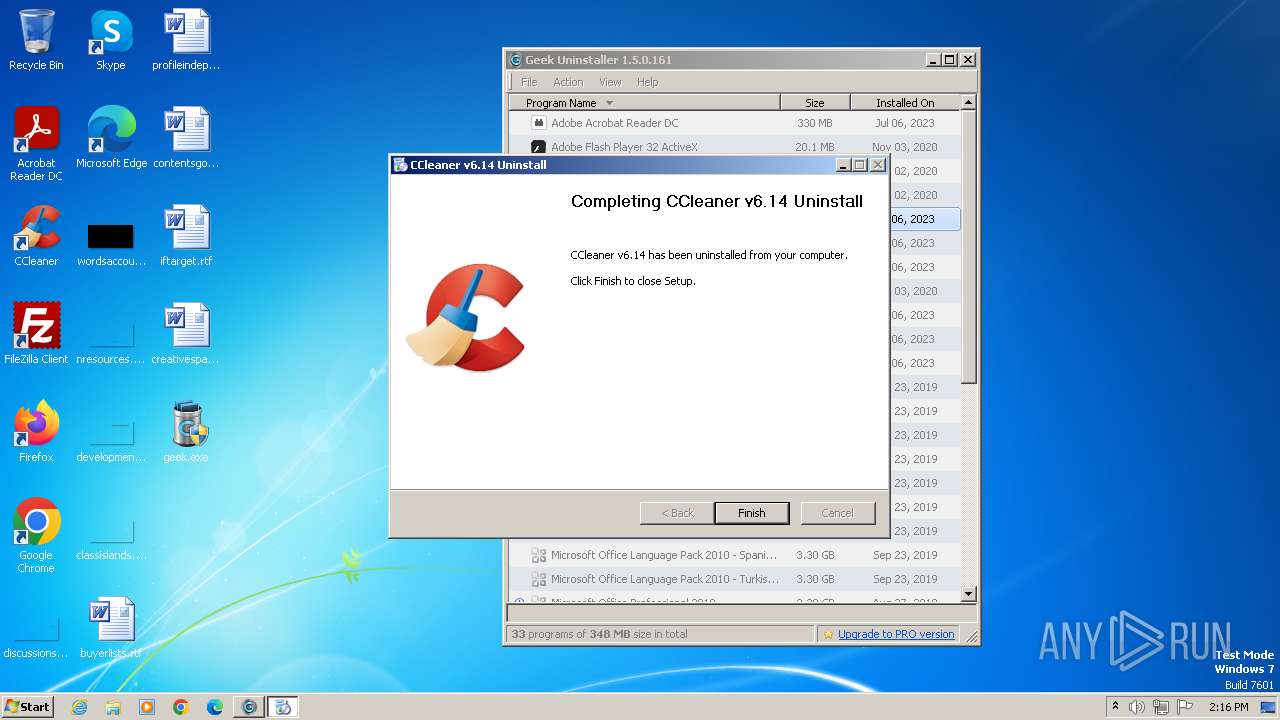
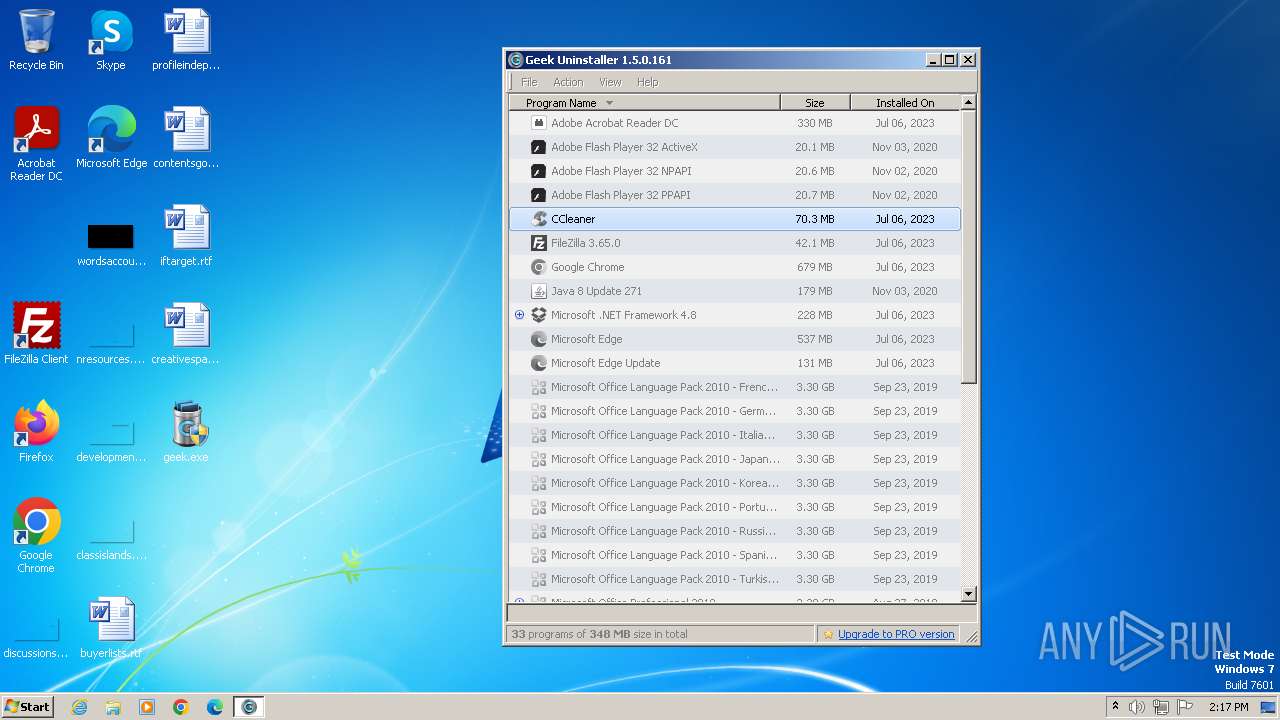
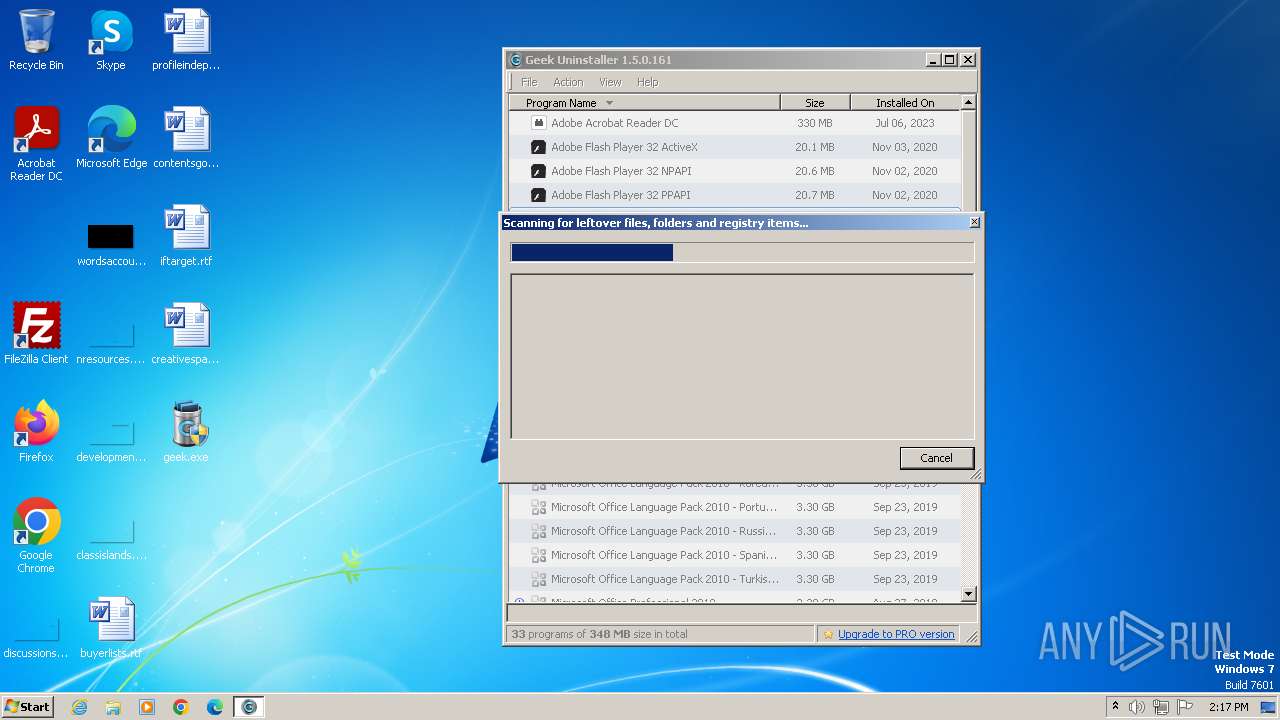
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2023, 14:16:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B2E0F4A508DFA44CE14A3421F316DFF5 |
| SHA1: | 37F2E769AB591654CFA801C37E84626EE04BD05E |
| SHA256: | 07FFE1C557809D2D87E3B33823737FEF1715FB2839D0FB8C5C7DCABF58376C8F |
| SSDEEP: | 98304:NAKO0ffMKh1uW1RXjm9++V28CokBEXIKUWyW+kmqMkUTM+wWssnuxEVW4PH9zU4K:DK |
MALICIOUS
Drops the executable file immediately after the start
- Un_A.exe (PID: 4060)
- uninst.exe (PID: 2668)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3684)
- cmd.exe (PID: 2536)
- nsBF8F.tmp (PID: 3384)
- nsC09A.tmp (PID: 3052)
SUSPICIOUS
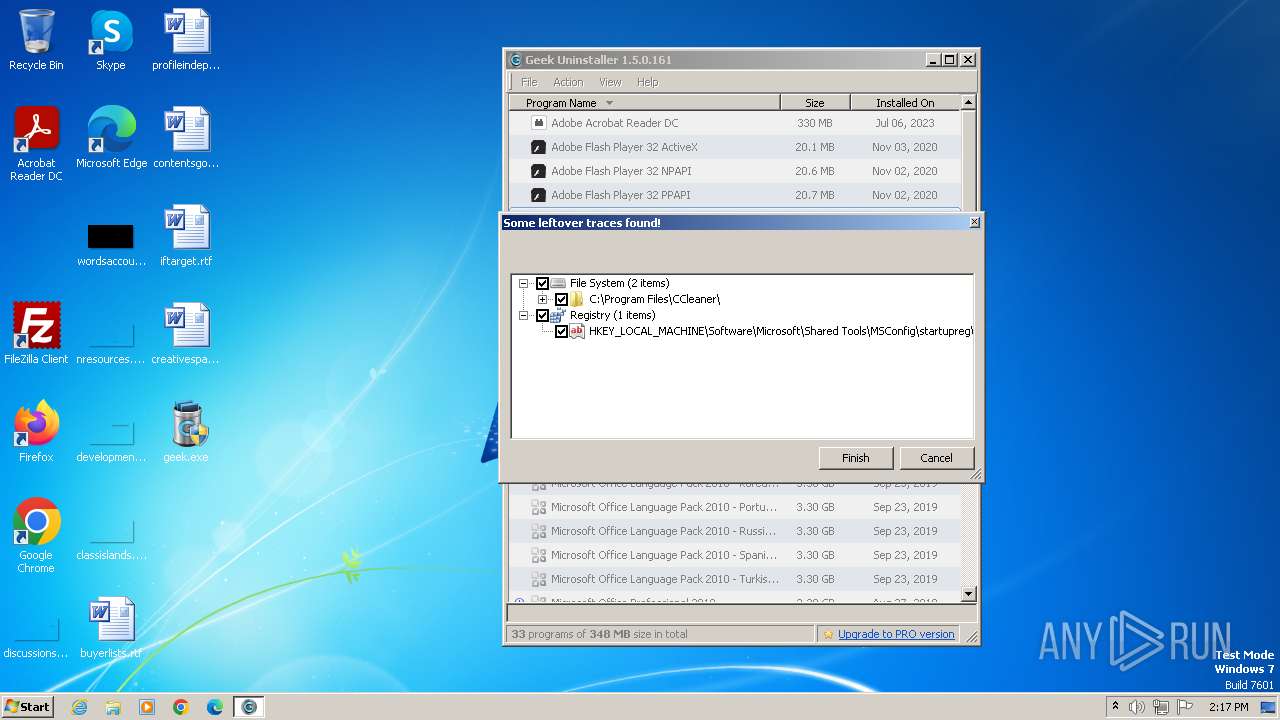
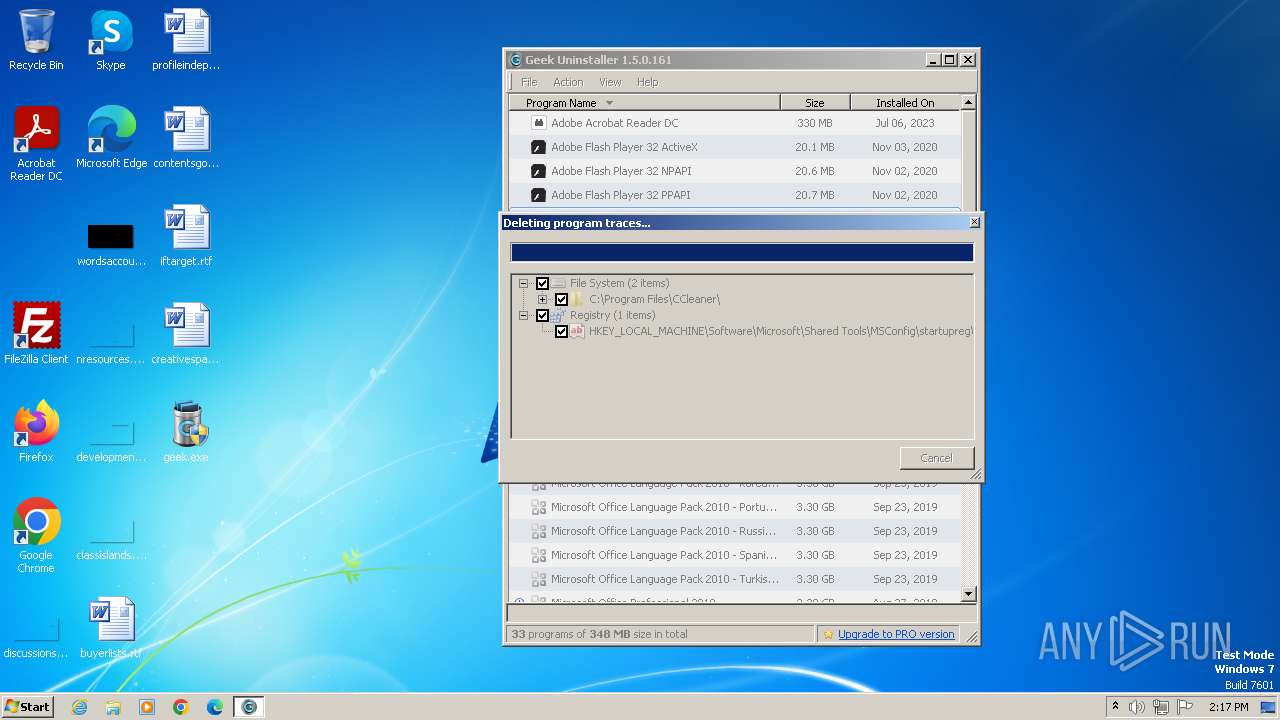
Starts itself from another location
- uninst.exe (PID: 2668)
Starts application with an unusual extension
- Un_A.exe (PID: 4060)
Malware-specific behavior (creating "System.dll" in Temp)
- Un_A.exe (PID: 4060)
Application launched itself
- cmd.exe (PID: 2536)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2536)
- nsBCEE.tmp (PID: 3436)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3684)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 2868)
- wmpnscfg.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:08:11 14:40:21+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 1860608 |
| InitializedDataSize: | 4738560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17b694 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
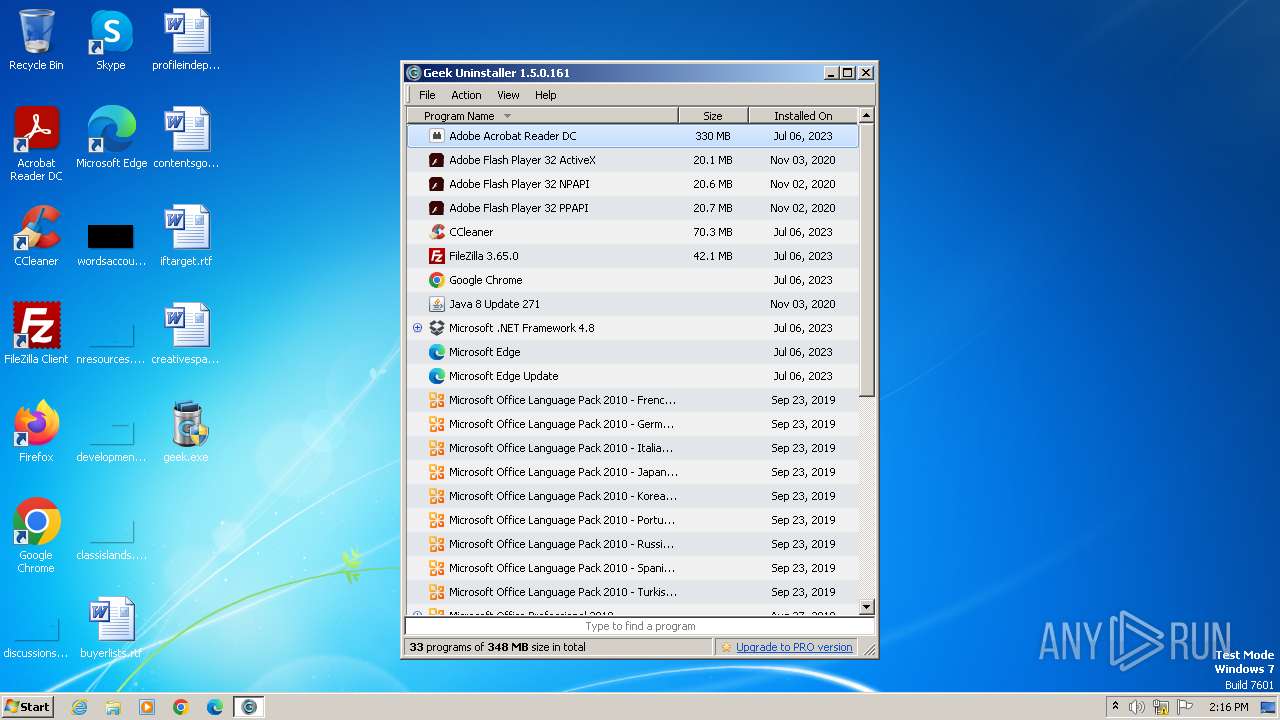
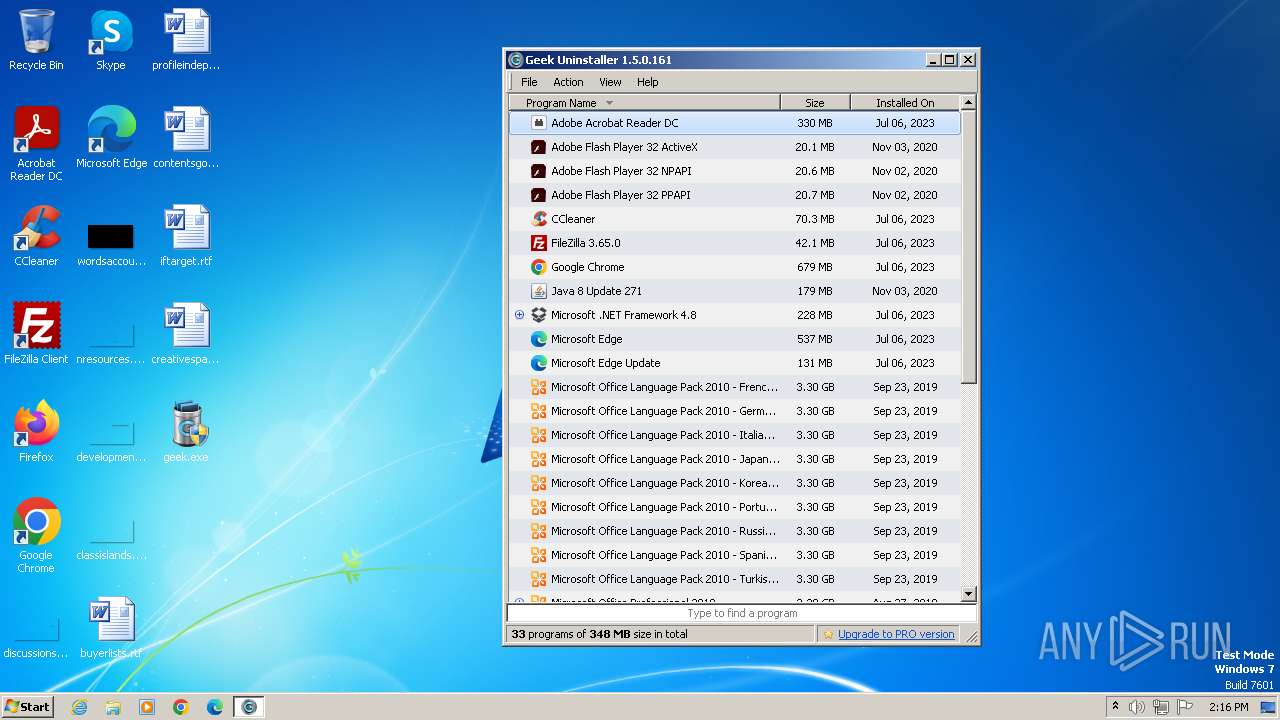
| FileVersionNumber: | 1.5.0.161 |
| ProductVersionNumber: | 1.5.0.161 |
| FileFlagsMask: | 0x001f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Geek Uninstaller |
| Comments: | https://geekuninstaller.com |
| FileDescription: | Geek Uninstaller |
| FileVersion: | 1.5.0.161 |
| InternalName: | Geek Uninstaller |
| LegalCopyright: | Copyright (C) 2012-2022 Geek Uninstaller |
| OriginalFileName: | geek.exe |
| ProductName: | Geek-Uninstaller |
| ProductVersion: | 1.5.0.161 |
Total processes
62
Monitored processes
17
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
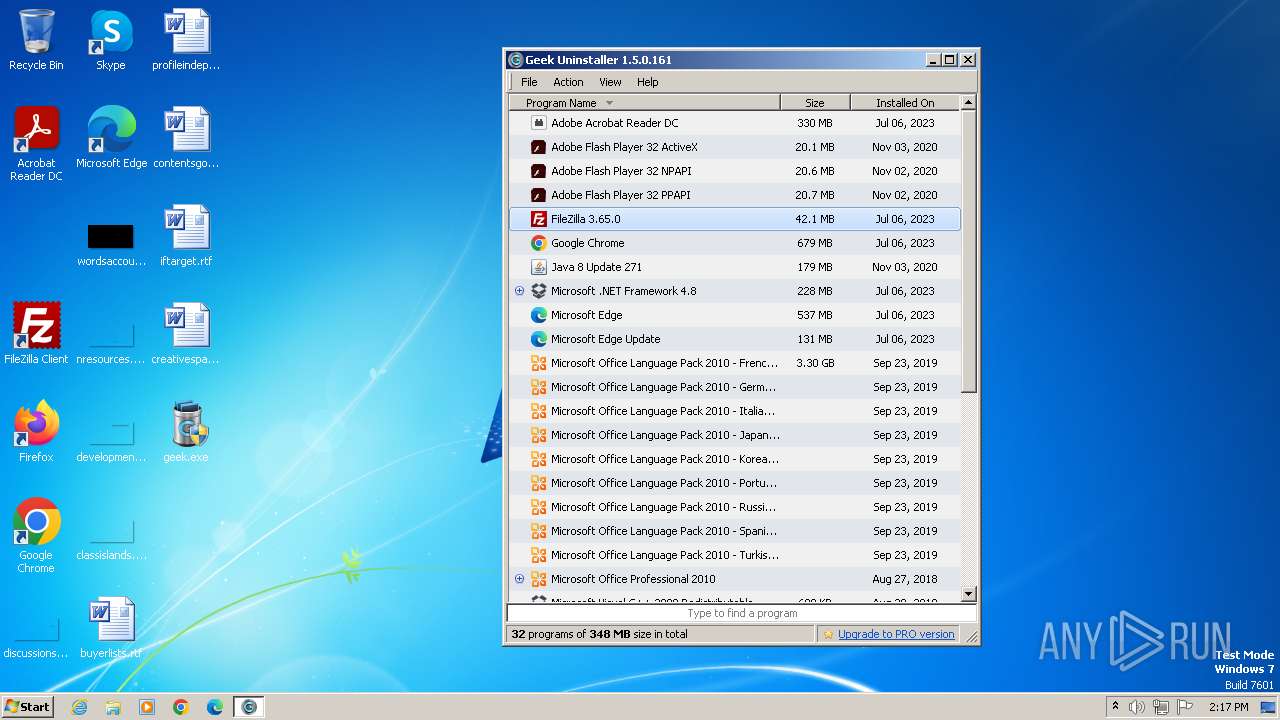
| 2524 | "C:\Users\admin\Desktop\geek.exe" | C:\Users\admin\Desktop\geek.exe | explorer.exe | ||||||||||||
User: admin Company: Geek Uninstaller Integrity Level: HIGH Description: Geek Uninstaller Exit code: 0 Version: 1.5.0.161 Modules
| |||||||||||||||
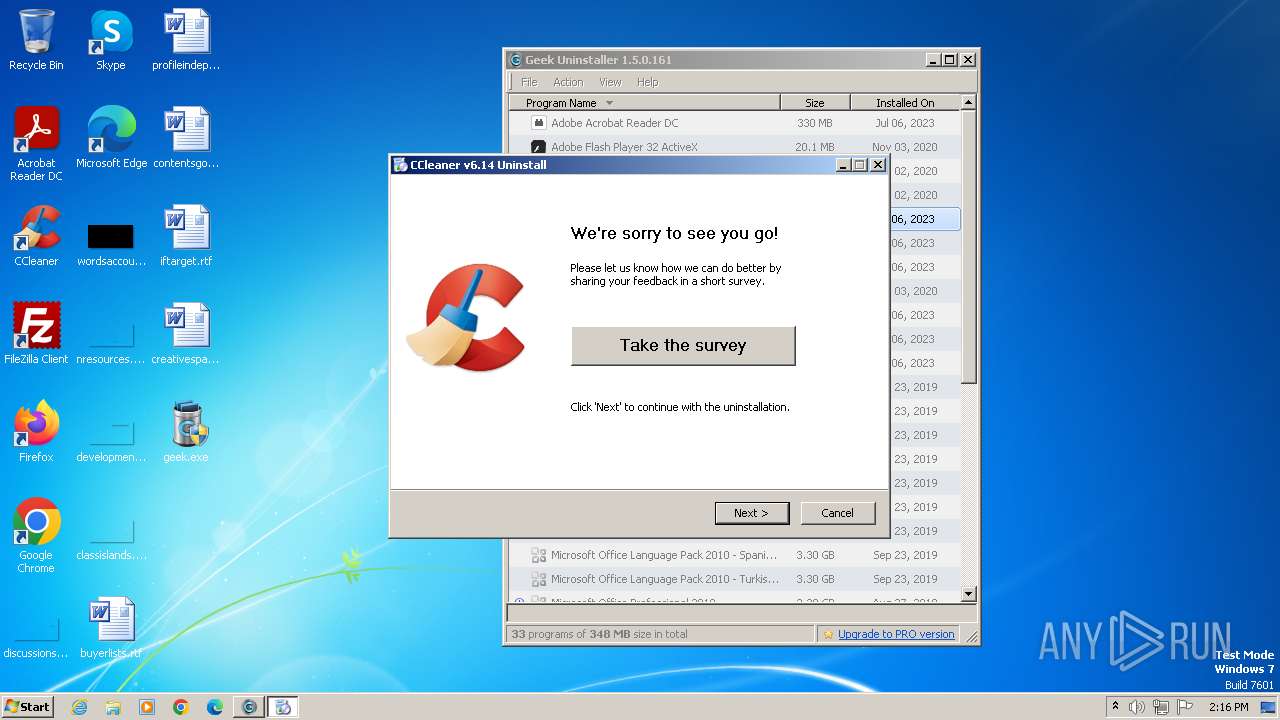
| 2536 | cmd /c for /f "usebackq tokens=1* delims=\" %# in (`C:\Windows\system32\schtasks /query /fo list ^| findstr /i CCleanerSkipUAC`) do C:\Windows\system32\schtasks /delete /tn "%f7f81a39-5f63-5b42-9efd-1f13b5431005quot; /f | C:\Windows\System32\cmd.exe | — | nsBCEE.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
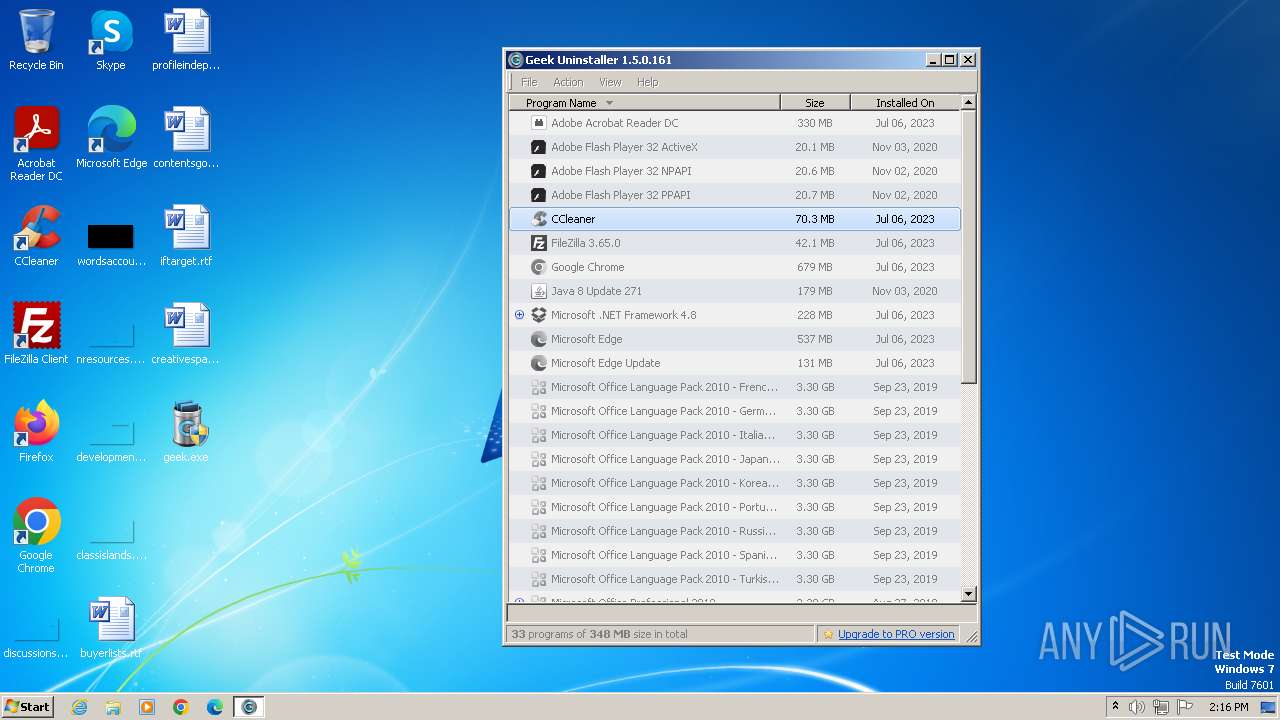
| 2668 | "C:\Program Files\CCleaner\uninst.exe" | C:\Program Files\CCleaner\uninst.exe | — | geek.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Installer Exit code: 0 Version: 6.14.0.10584 | |||||||||||||||
| 2696 | C:\Windows\system32\schtasks /delete /tn "CCleanerSkipUAC - admin" /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2868 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2968 | C:\Windows\system32\schtasks /delete /tn CCleanerCrashReporting /f | C:\Windows\System32\schtasks.exe | — | nsBF8F.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 3016 | C:\Windows\system32\schtasks /query /fo list | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 3052 | "C:\Users\admin\AppData\Local\Temp\nshA6D5.tmp\nsC09A.tmp" C:\Windows\system32\schtasks /delete /tn CCleanerClean /f | C:\Users\admin\AppData\Local\Temp\nshA6D5.tmp\nsC09A.tmp | — | Un_A.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 | |||||||||||||||
| 3060 | "C:\Users\admin\Desktop\geek.exe" | C:\Users\admin\Desktop\geek.exe | — | explorer.exe | |||||||||||
User: admin Company: Geek Uninstaller Integrity Level: MEDIUM Description: Geek Uninstaller Exit code: 3221226540 Version: 1.5.0.161 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
6 867
Read events
6 843
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2524) geek.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
12
Suspicious files
15
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:F341670D980C019EAC6B5C54F323DE61 | SHA256:3134589A533CF8AFCD0A2ABBB8EE81F8B00874CDE43FE0D91A3801C2F0B6450E | |||
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:F9A331D0F4A740A712D2723BBA9A94DC | SHA256:5EA5371119C8BAA481C2245706838A5C0A4FF899589B375CA60F78D22513263D | |||
| 2524 | geek.exe | C:\Users\admin\AppData\Local\Temp\Tar8E89.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2524 | geek.exe | C:\Users\admin\AppData\Local\Temp\Cab8E88.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\66EEEA81AAF56AAC071822D4FD0246FE | binary | |
MD5:1262BCCDE23C087DAAFD6461FA99B533 | SHA256:FBDF71CDC27BD62B7B8EED2E9959795343EB9500B8CD177E2642E7CDD46FC237 | |||
| 2524 | geek.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\update[1].txt | text | |
MD5:83838B4289E8C584CFD2A53EF414D33D | SHA256:72727B107B79962C08A14D80FFA925387E83CD9ACACFBAB7C7F5DA679B5BDD91 | |||
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:997E450CACA3F473A9346BB1D436A184 | SHA256:A2F05F595A5D37AADA1047667D63213B99ECADBC6DD40985E8DB9CCA698FACBE | |||
| 2524 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2668 | uninst.exe | C:\Users\admin\AppData\Local\Temp\nsbA5CA.tmp | binary | |
MD5:B6FB099CCFF23691507754D21E8456A7 | SHA256:05D51691C0C3E9D1AFB1419E105F9E40B0916BEC94B42560E63E181345F021D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e2a4e3862fadcd99 | unknown | compressed | 4.66 Kb | unknown |
— | — | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7cad2552c2a07960 | unknown | compressed | 65.2 Kb | unknown |
— | — | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
— | — | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQloXxw7SRy%2BF2phayuh6Pleg%3D%3D | unknown | binary | 503 b | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
— | — | 173.230.144.164:443 | geekuninstaller.com | Linode, LLC | US | unknown |
— | — | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
— | — | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
— | — | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
— | — | 192.168.100.255:138 | — | — | — | unknown |
— | — | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
— | — | 34.117.223.223:443 | analytics.ff.avast.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
— | — | 23.215.23.231:443 | service.piriform.com | Akamai International B.V. | US | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geekuninstaller.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
armmf.adobe.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
service.piriform.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
license.piriform.com |
| whitelisted |