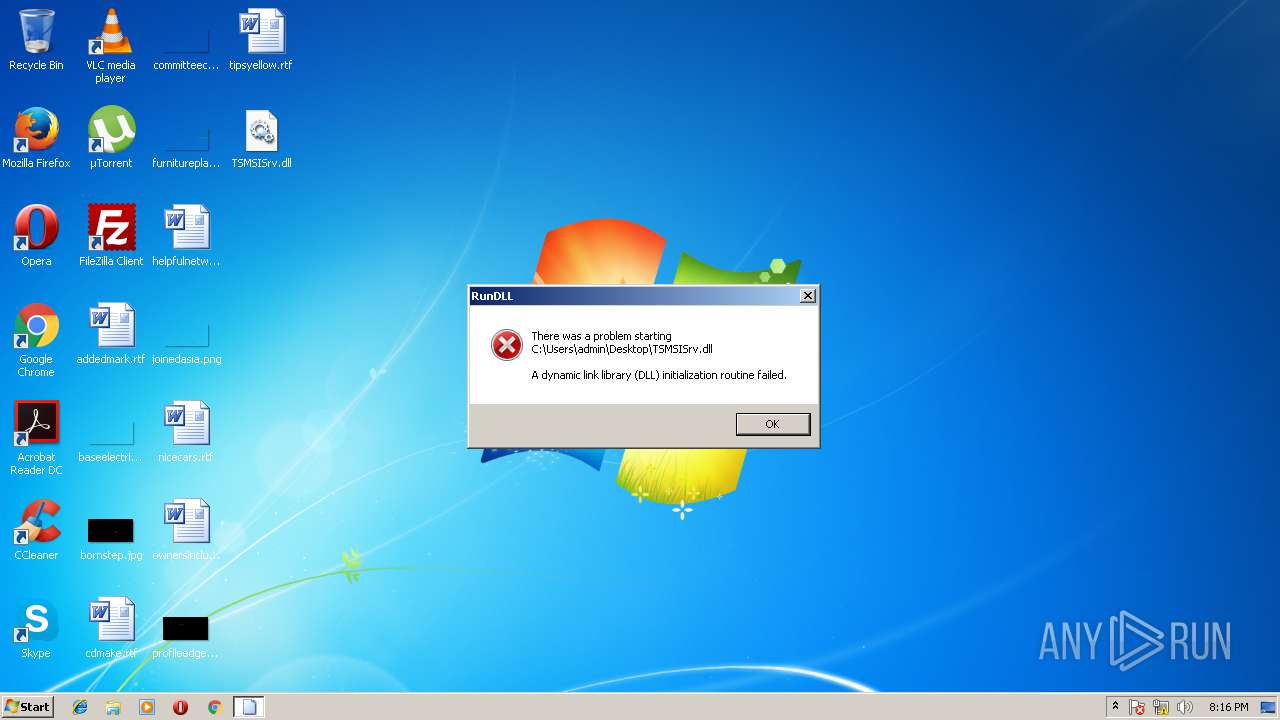
| File name: | TSMSISrv.dll |
| Full analysis: | https://app.any.run/tasks/af25f269-15d9-4dd5-b334-6f0777b1356c |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2018, 19:15:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | D6FD2DF91432CA21C79ECE2C6637D1C6 |
| SHA1: | 53C9EA5AC9B2EFC5E8E0B4E3A051FA1615CC09A9 |
| SHA256: | 07FB252D2E853A9B1B32F30EDE411F2EFBB9F01E4A7782DB5EACF3F55CF34902 |
| SSDEEP: | 3072:CBpvHaTURjKbH23R/oH+6xJ6RotJkhe+/SwUg4mPN3k117y:CrzUbqexpzNrCN3Su |
MALICIOUS
Application loaded dropped or rewritten executable
- explorer.exe (PID: 1640)
- SearchProtocolHost.exe (PID: 3616)
Runs app for hidden code execution
- explorer.exe (PID: 1640)
SUSPICIOUS
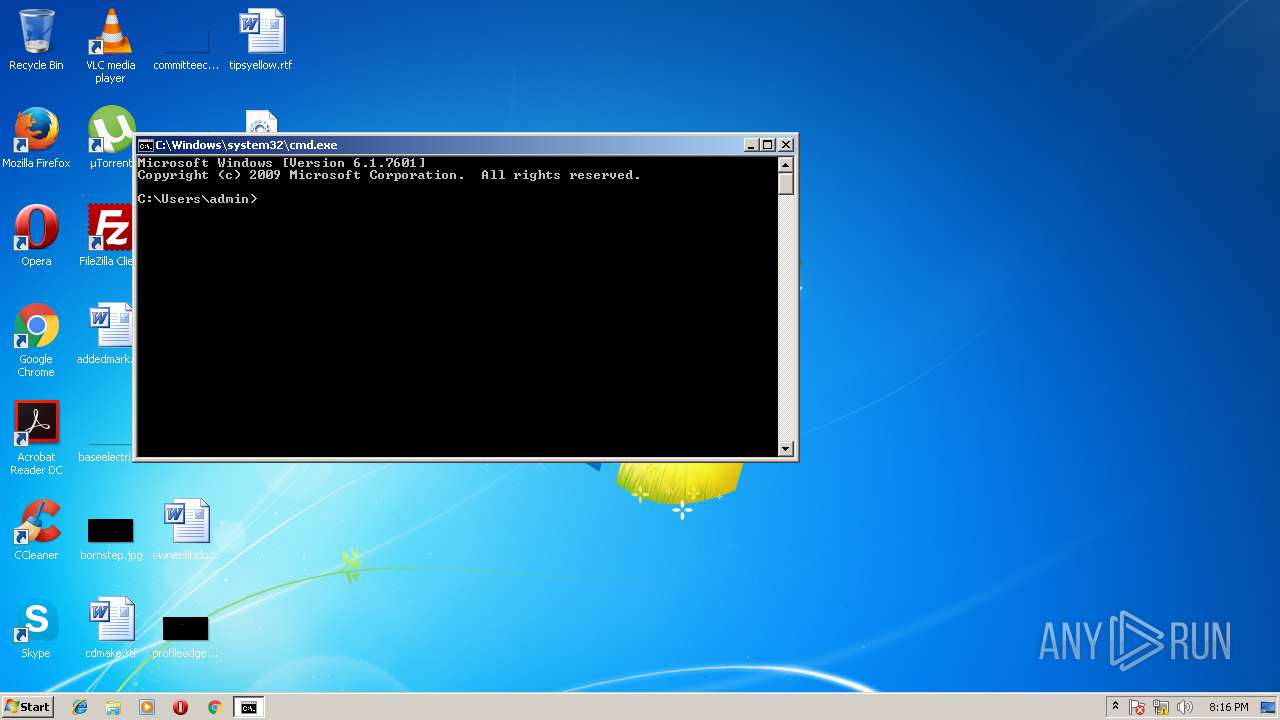
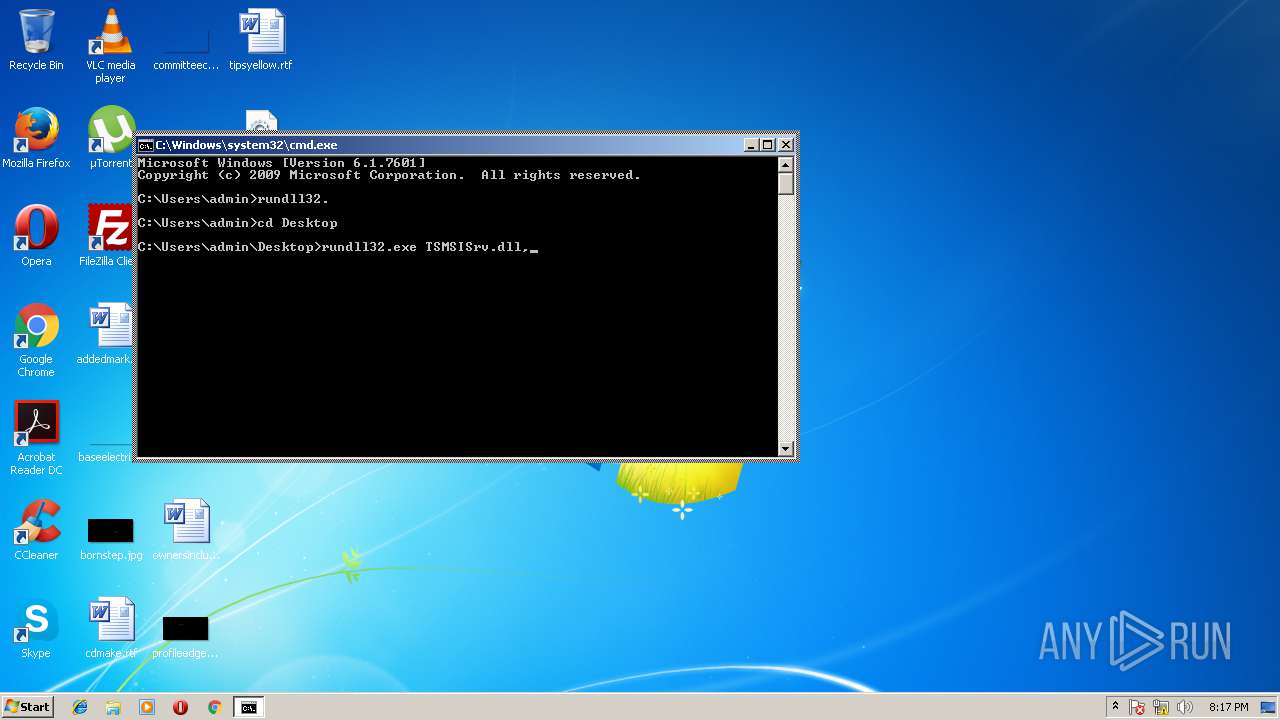
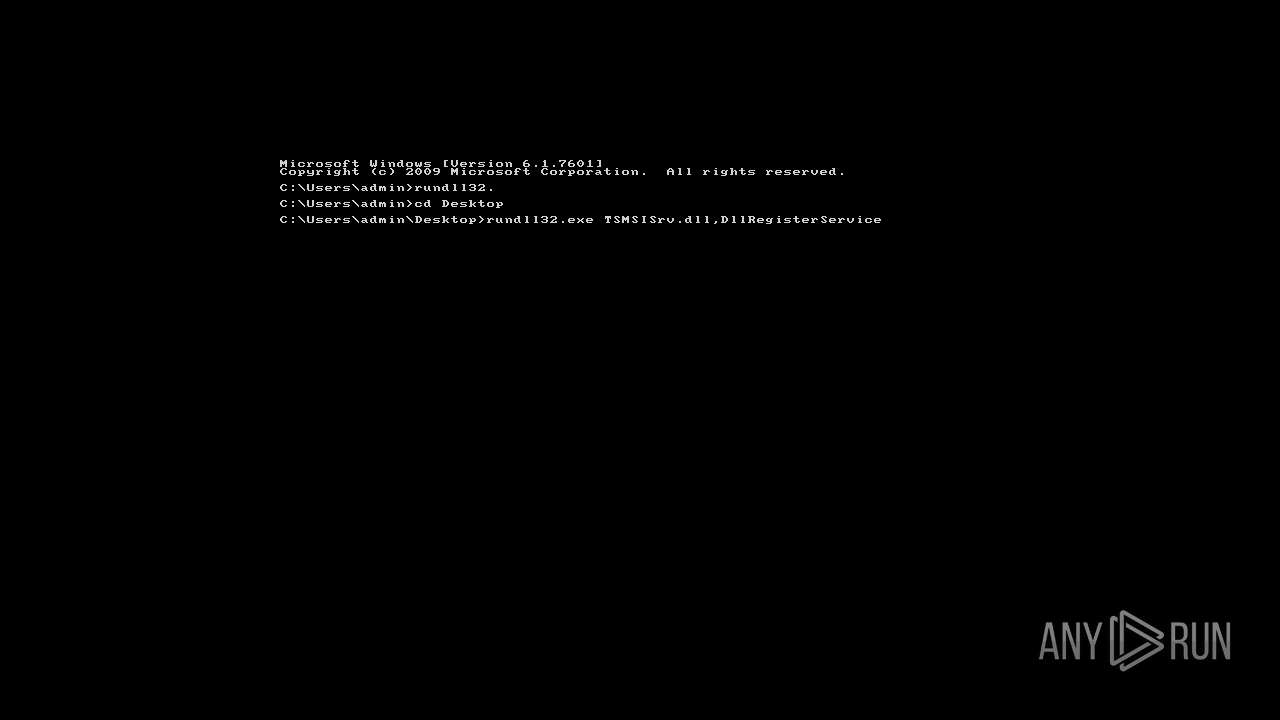
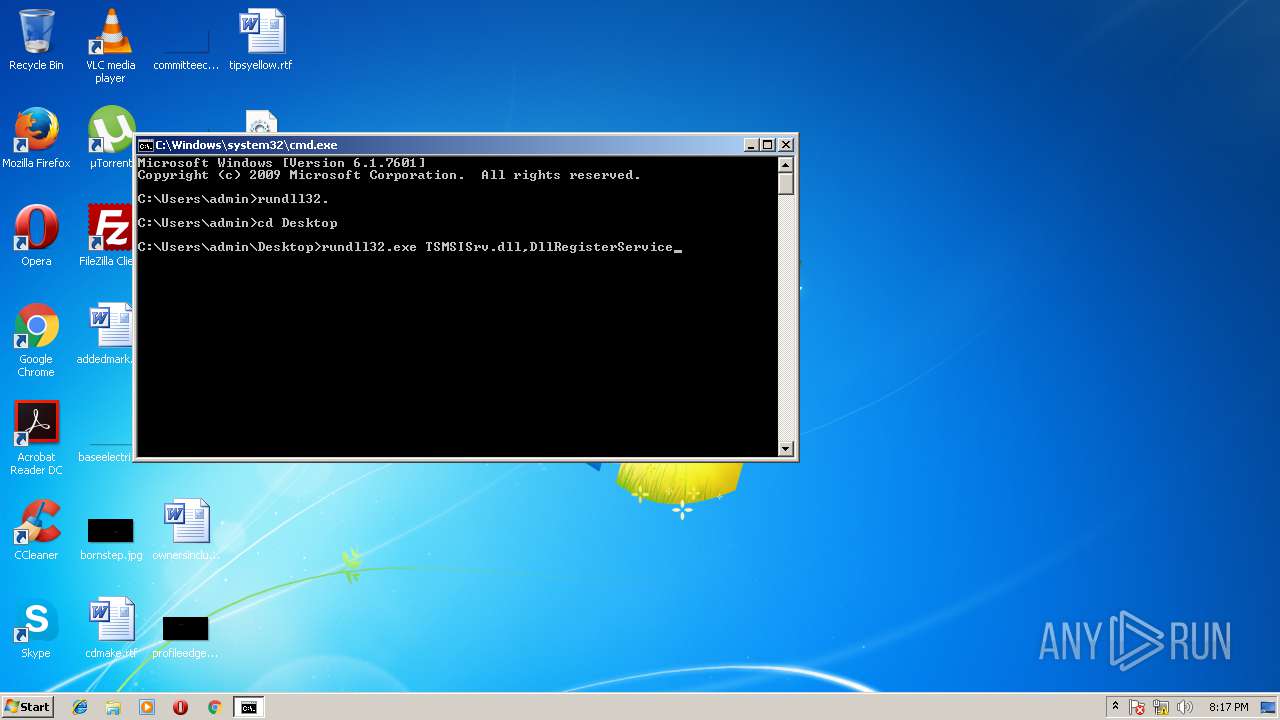
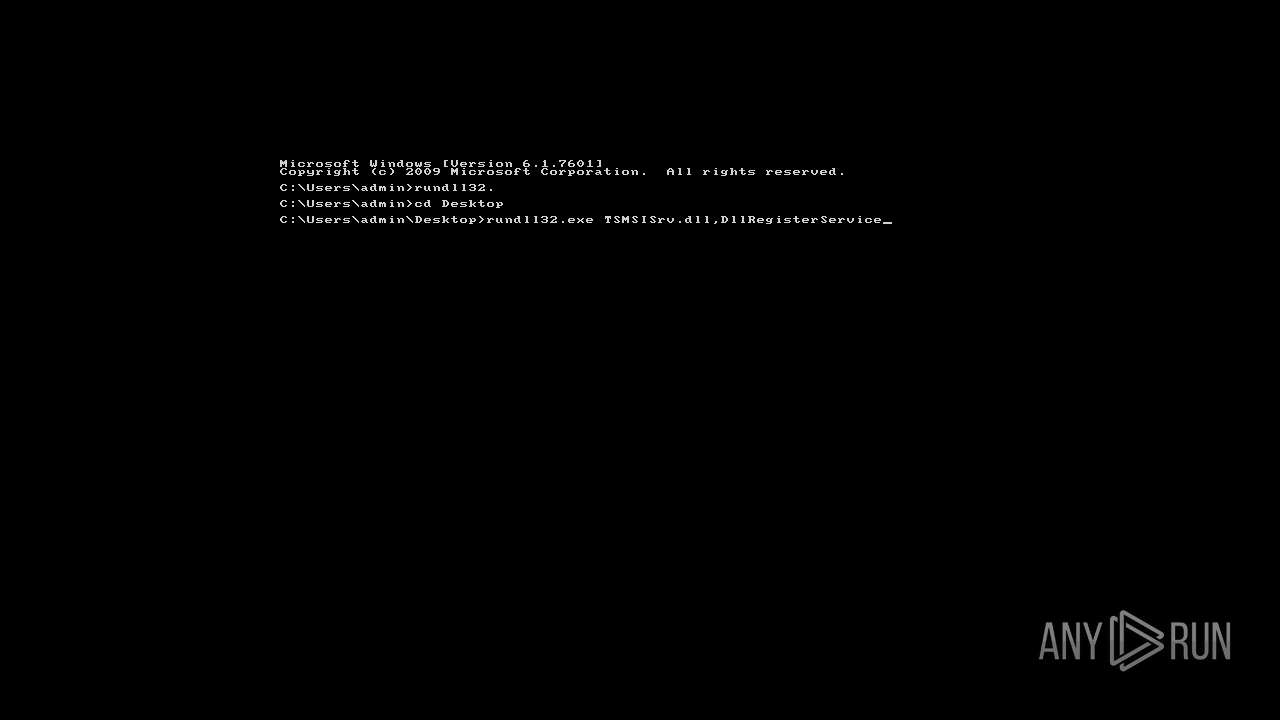
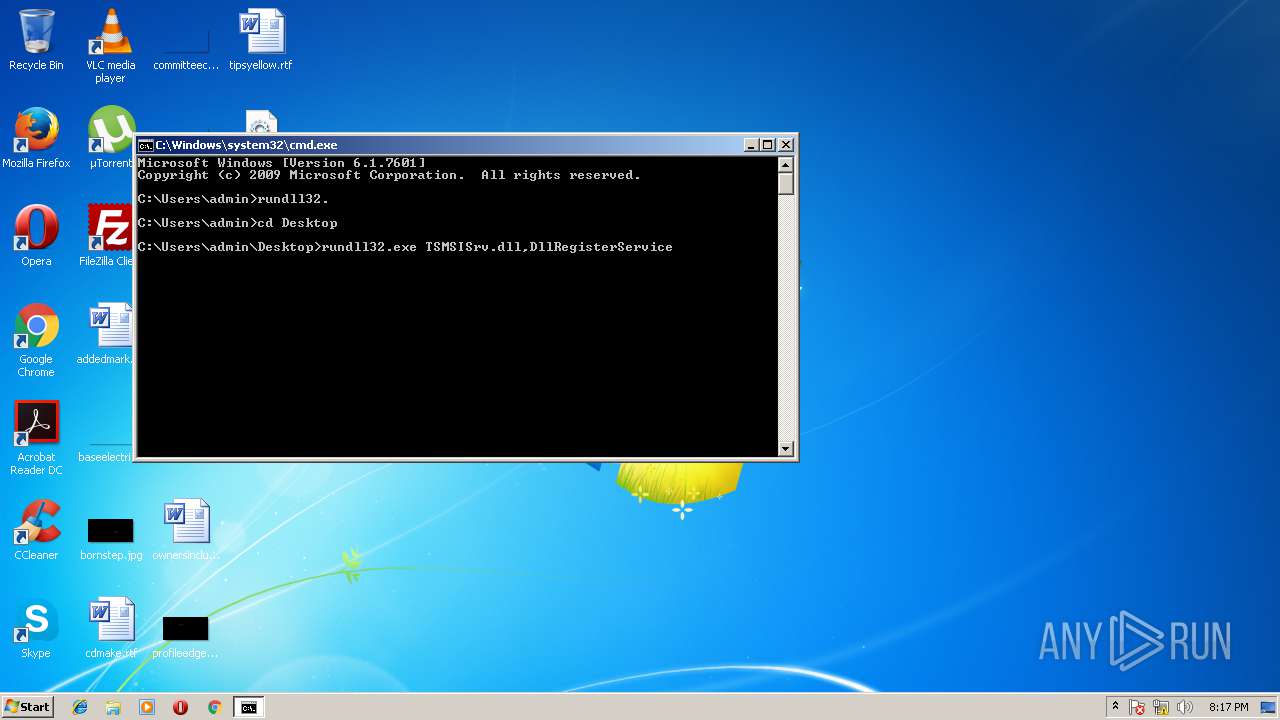
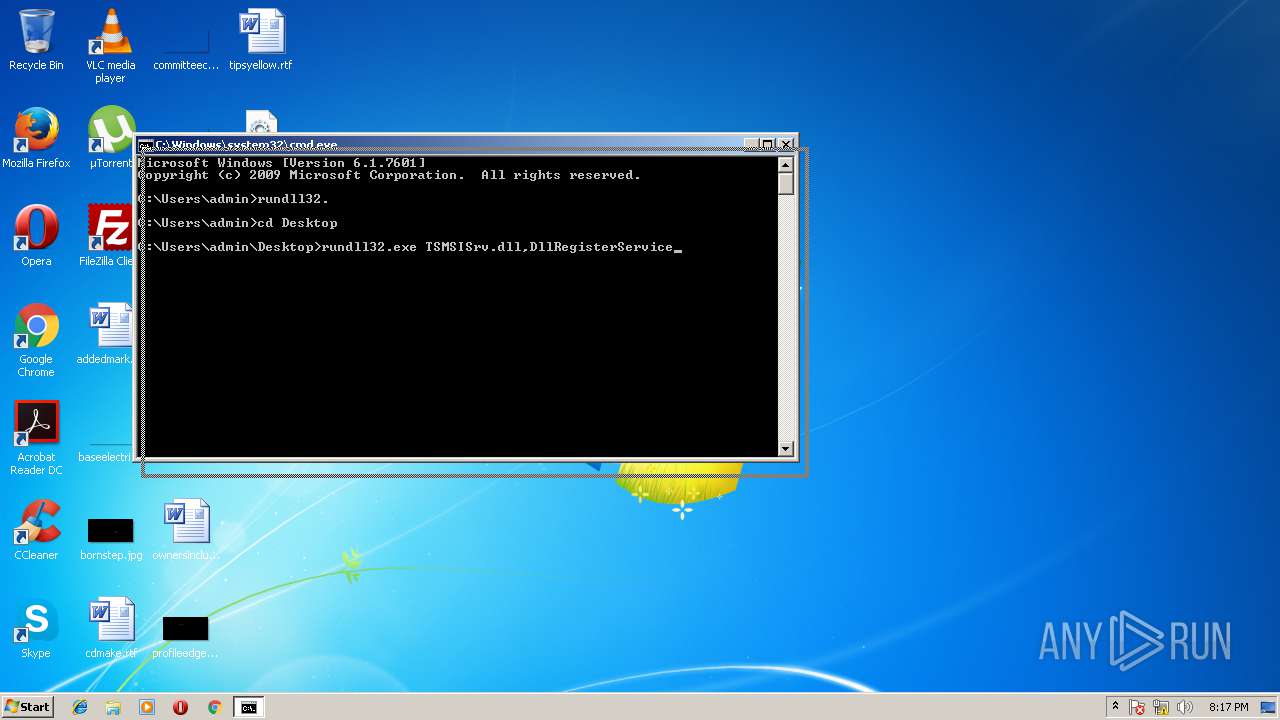
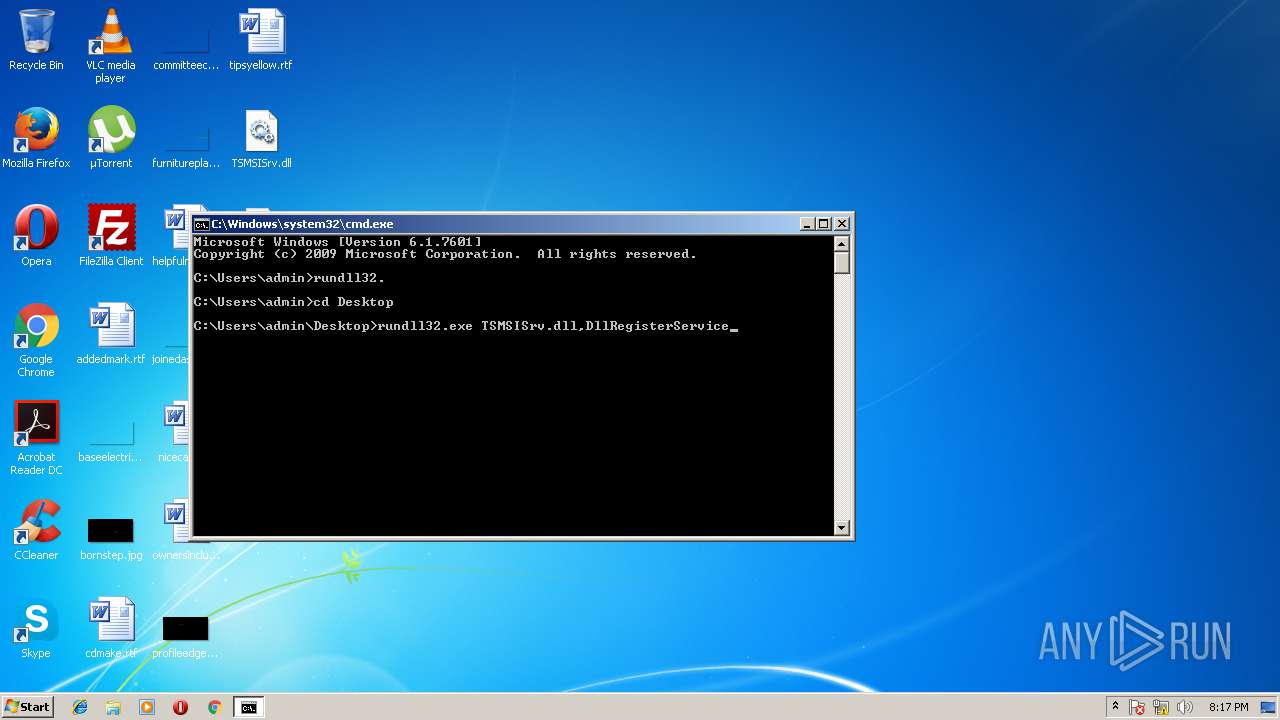
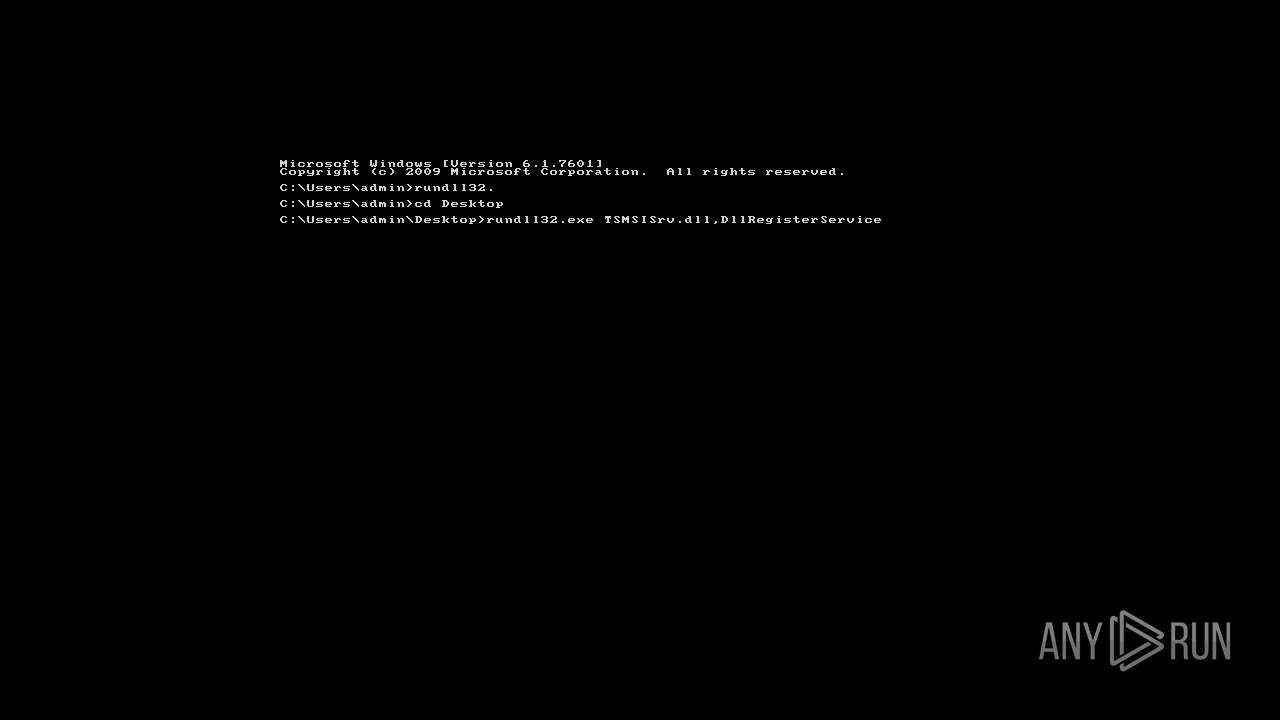
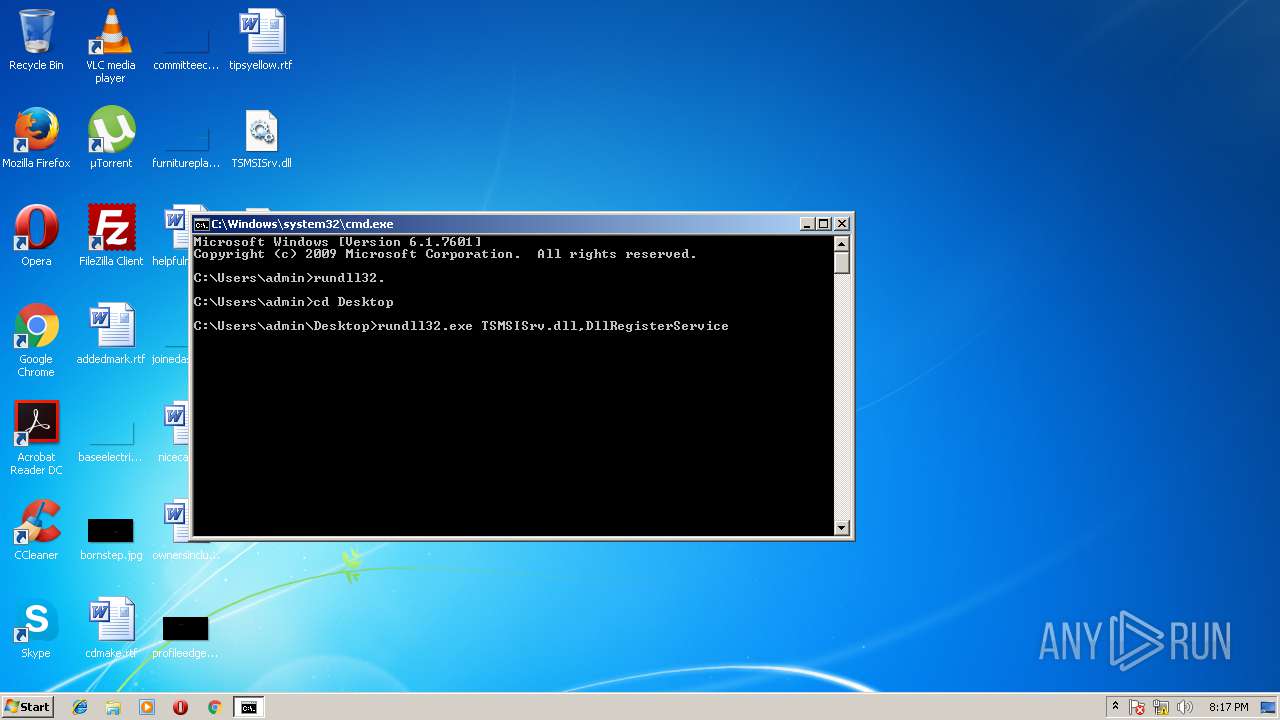
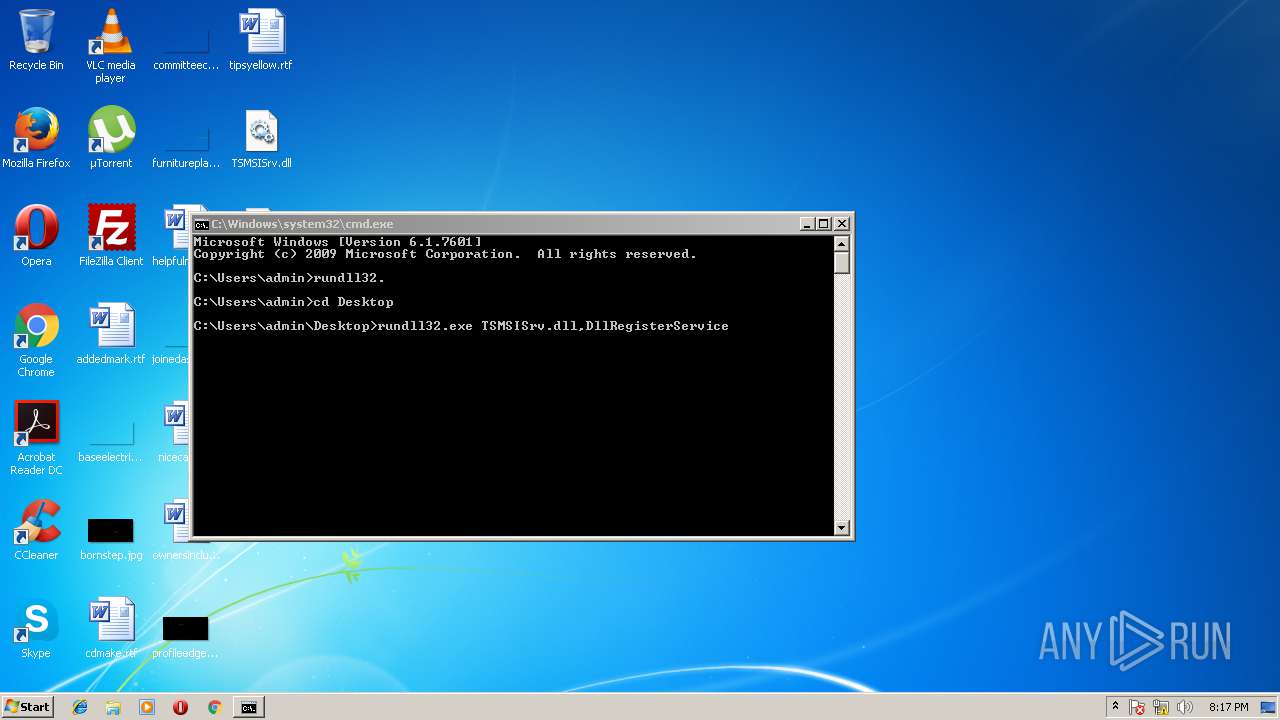
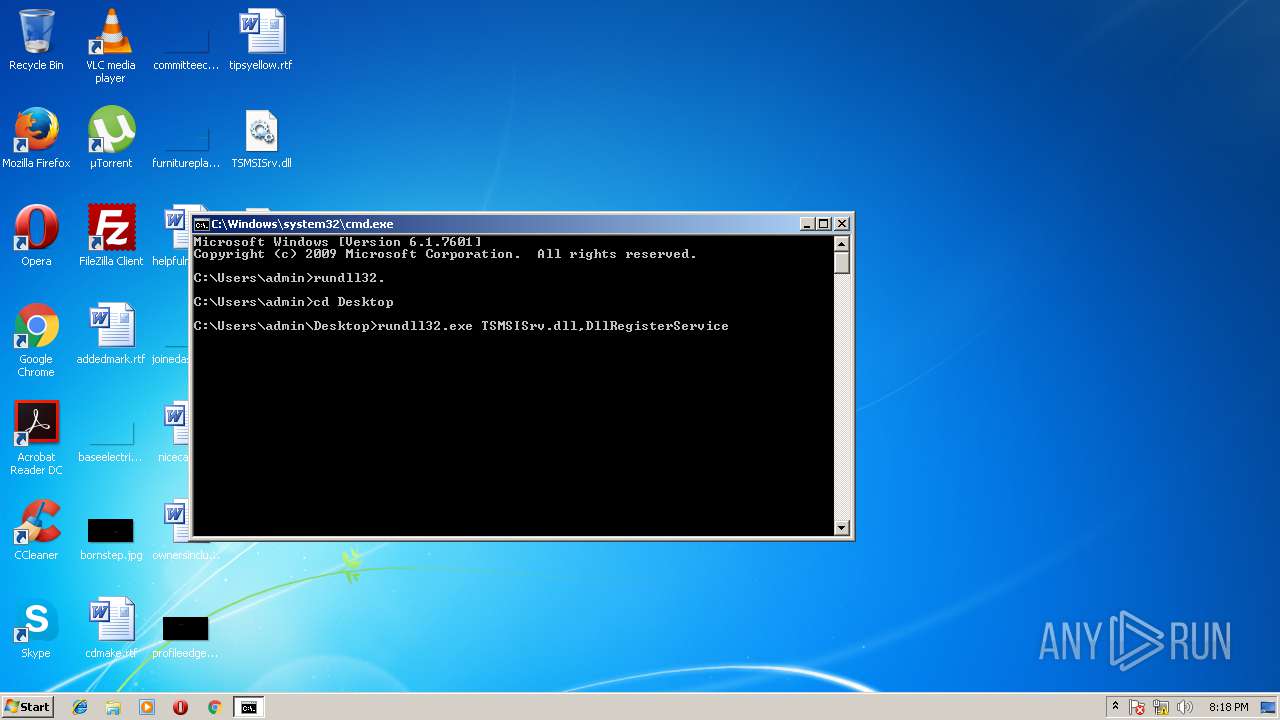
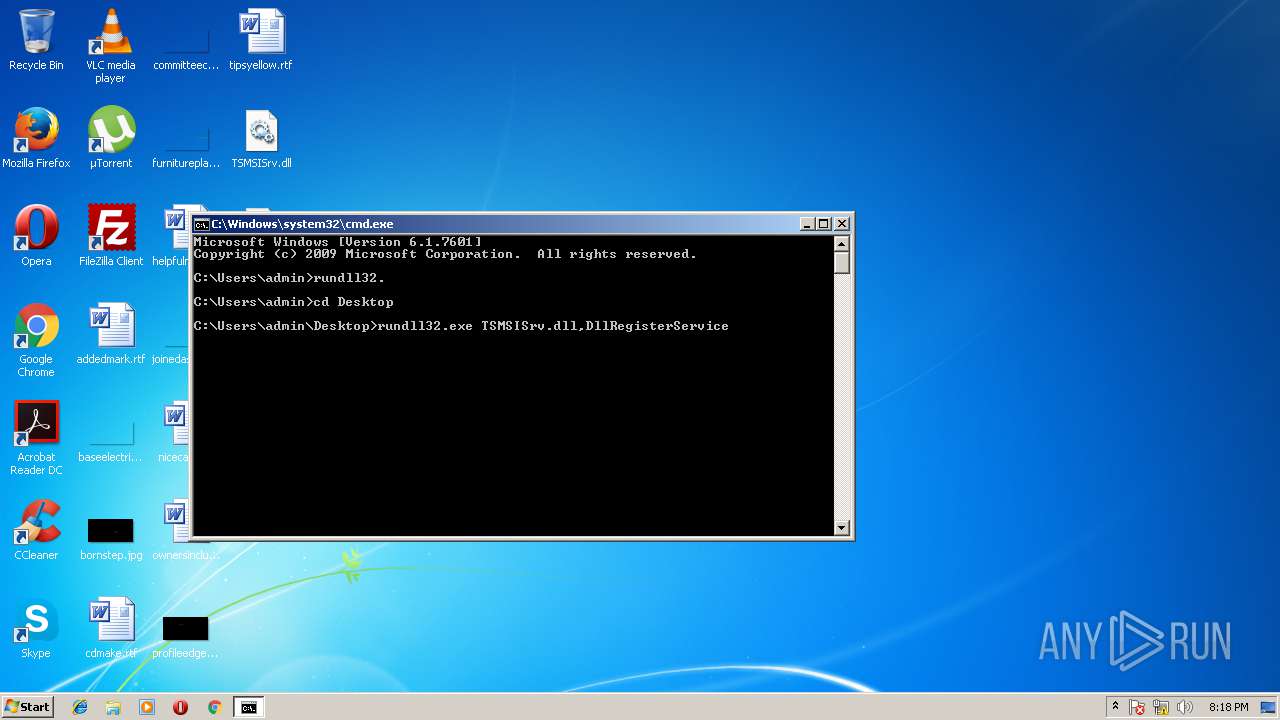
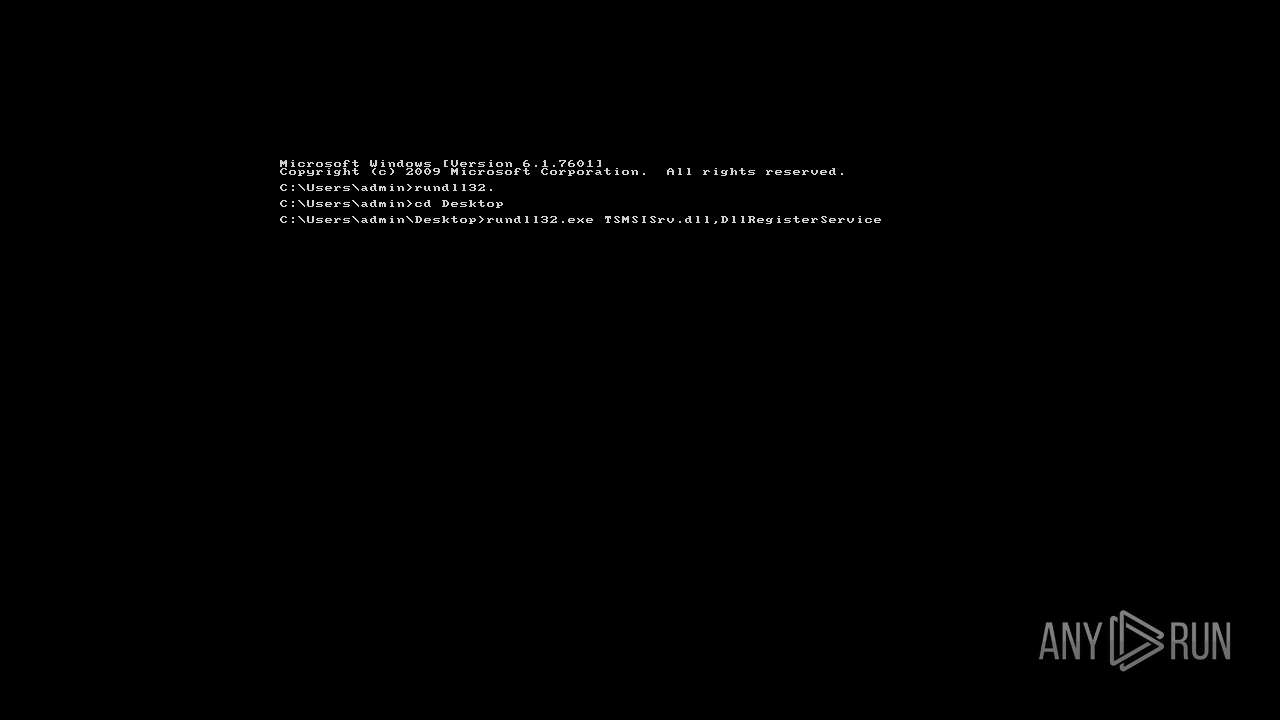
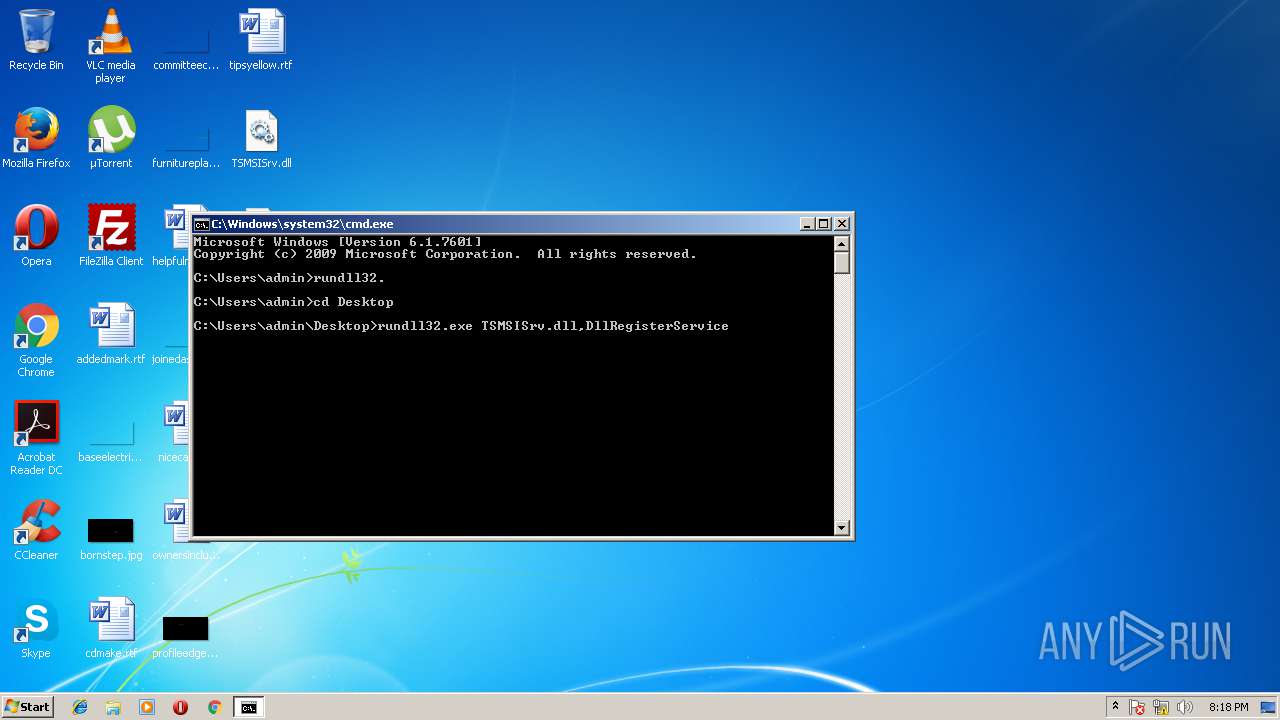
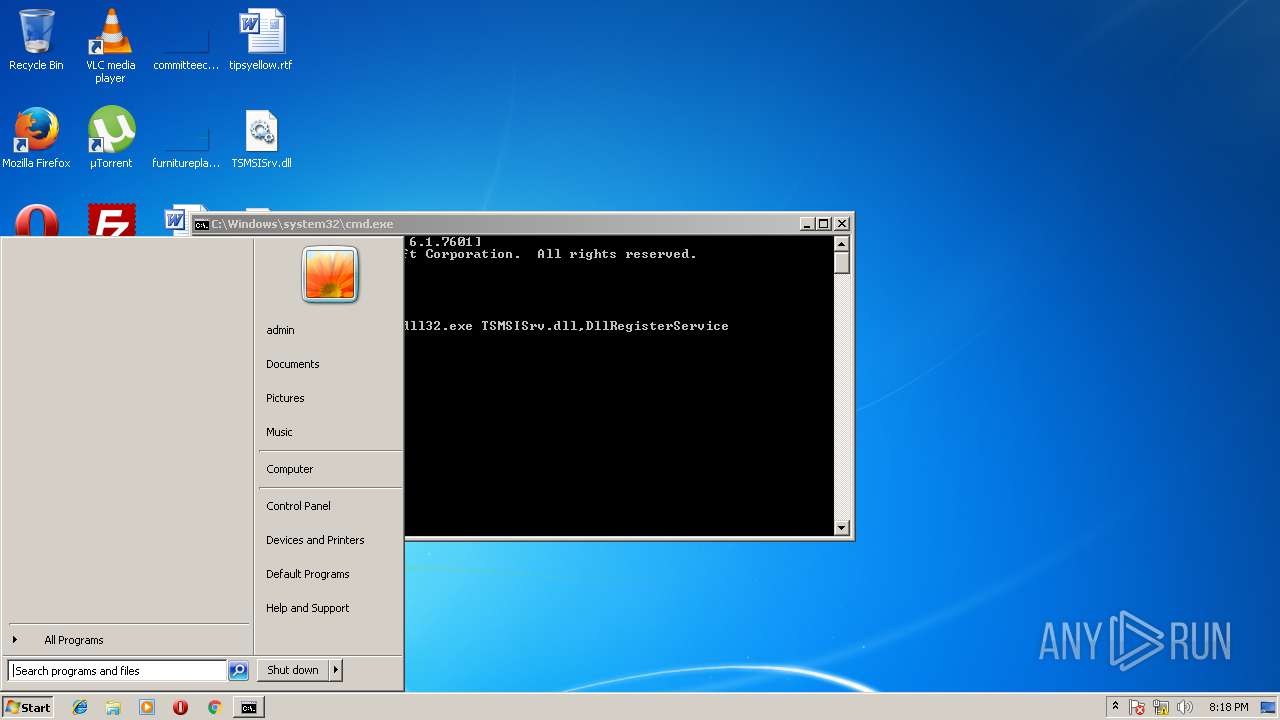
Starts CMD.EXE for commands execution
- explorer.exe (PID: 1640)
INFO
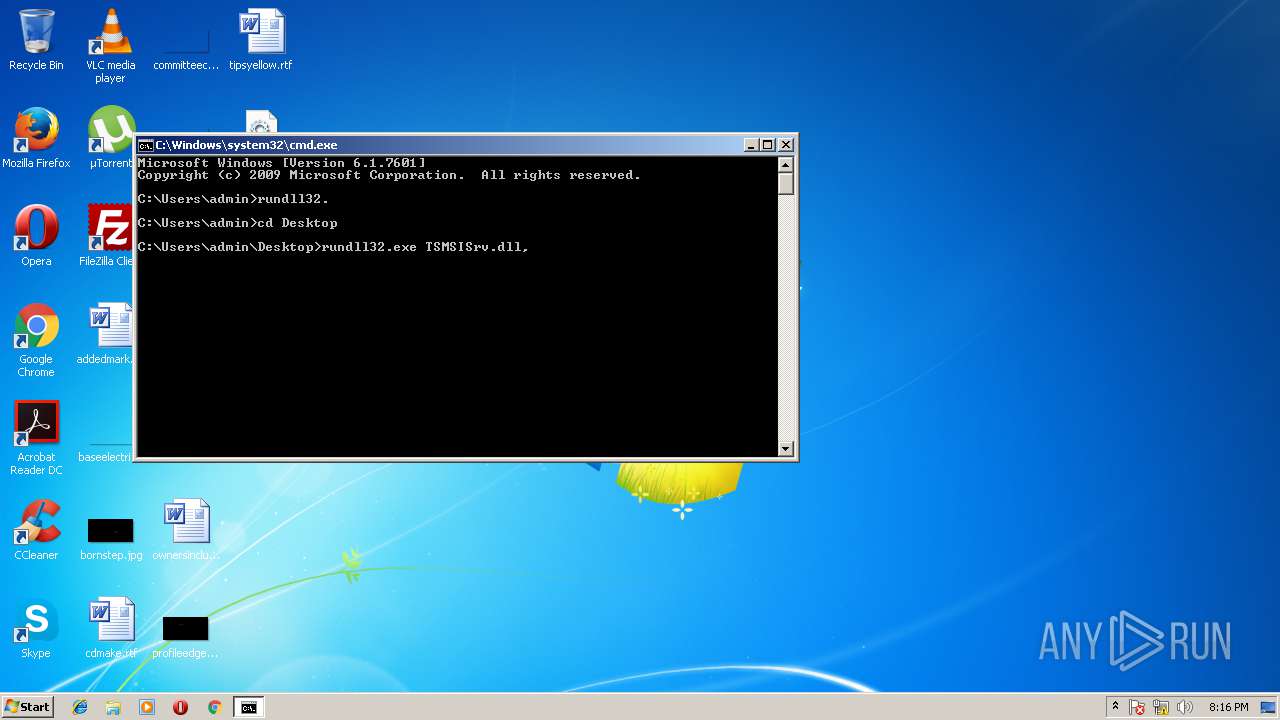
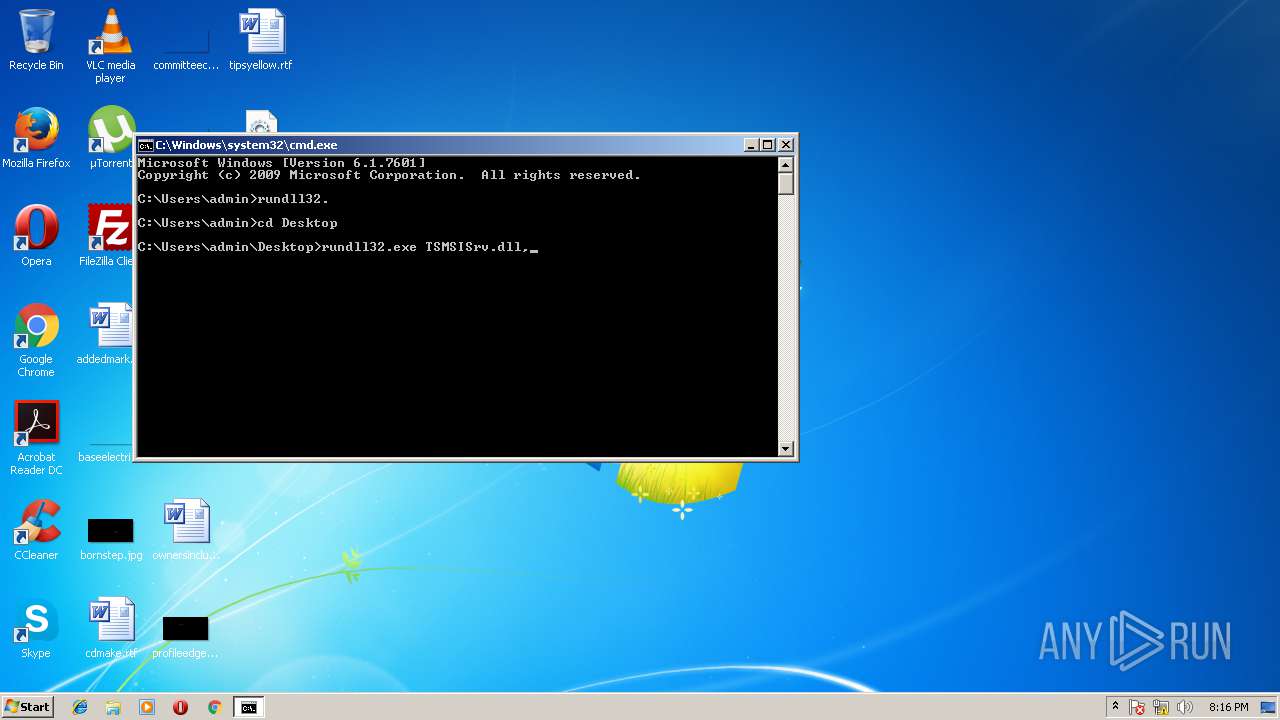
Application loaded main object executable
- rundll32.exe (PID: 1104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ocx | | | Windows ActiveX control (73.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (17.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:04:22 20:20:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 111616 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10a66 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.4.23 |
| ProductVersionNumber: | 2.0.4.23 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Corel Inc. |
| FileDescription: | VirtCDRDrv Module |
| FileVersion: | 2, 0, 4, 23 |
| InternalName: | VirtCDRDrv |
| LegalCopyright: | Copyright 2001-2011 Corel Inc. |
| OriginalFileName: | VirtCDRDrv.DLL |
| ProductName: | VirtCDRDrv Module |
| ProductVersion: | 2, 0, 4, 23 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Apr-2015 18:20:39 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Corel Inc. |
| FileDescription: | VirtCDRDrv Module |
| FileVersion: | 2, 0, 4, 23 |
| InternalName: | VirtCDRDrv |
| LegalCopyright: | Copyright 2001-2011 Corel Inc. |
| OriginalFilename: | VirtCDRDrv.DLL |
| ProductName: | VirtCDRDrv Module |
| ProductVersion: | 2, 0, 4, 23 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Apr-2015 18:20:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001B3BE | 0x0001B400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69466 |
.rdata | 0x0001D000 | 0x00009E3E | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98798 |
.data | 0x00027000 | 0x00003CA0 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.42897 |
.rsrc | 0x0002B000 | 0x00000E98 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.12164 |
.reloc | 0x0002C000 | 0x000021E0 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47921 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41406 | 764 | UNKNOWN | English - United States | RT_VERSION |
7 | 1.39929 | 52 | UNKNOWN | English - United States | RT_STRING |
101 | 5.26902 | 878 | UNKNOWN | English - United States | REGISTRY |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll |
WINMM.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
DllCanUnloadNow | 1 | 0x0000C57C |
DllGetClassObject | 2 | 0x0000C588 |
DllRegisterServer | 3 | 0x0000C5F4 |
DllUnregisterServer | 4 | 0x0000C603 |
Total processes
37
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1073807364 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1104 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\TSMSISrv.dll", DllCanUnloadNow | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1640 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 951
Read events
1 678
Write events
273
Delete events
0
Modification events
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\91\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF400981C149D7D30100000000 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000100000001000000B31202000100000000000000000000007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E006500780065000000000004010000E6D9190300000000CD8F647613000000B03152D6F1B25748A4CEA8E7C6EA7D2743003A005C00570069006E0064006F00770073005C00730079007300740065006D00330032005C0063006D0064002E00650078006500000000000000740000000000000002000000D8443B0378673100C468310068345403E8D8310000000000B4D9190300000000B4DB1903EDE07F774B720800FEFFFFFFE72F8377822E8377000031003A00000038414003000000000000000000000000000000000000000000000000000031004041400300000000000000000000FFFFAD010000000000000000000000000000103E40030100000038414003ACDA1903E82C83773A0000000000310068345403A9010000D4CF2204CCDA190333AB8377D43BE60AFA0B000010270000110000005D53020000DB1903F8AA83775D530200D4CF220420DB1903002DCA02A0DB190300000000A2010000240100001E000000100000000600000028DB1903DAE29B75E207000020DB1903E20704001200130010001E0024011E00400981C149D7D30150DB190357C167763CDB1903A0DB190362C16776E2070400030012000000000001000000B31202007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000F701EC0AF701A4E8A5015869207700000000D007F701C4E8A5010B8C1F770100000000000000537A1F775604010200200000000000000100000010E9A50136170D76560401021008F7010500000000000000FFFFFFFFD007F701000000000CE9A50138E9A50100000000000000000000000064E9A501703B3A000000000040913B77090080015CE9A50135590D7656040102A00641030500000044E9A501506A20771CC0247701000000EF7A1F77560401021D000000002000005CE9A50163590D7664E9A5010000000000000000560401024066377701000000C8E9A501A13697770000000000000000D82C3900C8E9A501B8369777E0929A770000000000003100A006410300000000C4E9A5010E000B007C0100000000000000000000CF679577280641030100000098064103D0E9A501E82C8377D82C3900CF679577ECEBA501110000001047340008473400000031000000000050EA0000C0C9441C00EAA5018291647650EAA50104EAA50127956476000000008C31CA022CEAA501CD9464768C31CA02D8EAA501002DCA02E194647600000000002DCA02D8EAA50134EAA5010000000001000000B31202007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000F701EC0AF701A4E8A5015869207700000000D007F701C4E8A5010B8C1F770100000000000000537A1F775604010200200000000000000100000010E9A50136170D76560401021008F7010500000000000000FFFFFFFFD007F701000000000CE9A50138E9A50100000000000000000000000064E9A501703B3A000000000040913B77090080015CE9A50135590D7656040102A00641030500000044E9A501506A20771CC0247701000000EF7A1F77560401021D000000002000005CE9A50163590D7664E9A5010000000000000000560401024066377701000000C8E9A501A13697770000000000000000D82C3900C8E9A501B8369777E0929A770000000000003100A006410300000000C4E9A5010E000B007C0100000000000000000000CF679577280641030100000098064103D0E9A501E82C8377D82C3900CF679577ECEBA501110000001047340008473400000031000000000050EA0000C0C9441C00EAA5018291647650EAA50104EAA50127956476000000008C31CA022CEAA501CD9464768C31CA02D8EAA501002DCA02E194647600000000002DCA02D8EAA50134EAA501 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 0000000001000000000000000F0F0100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF400981C149D7D30100000000 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000100000001000000C221030001000000000000000F0F01007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000008277306AD60028010000020003000000000022608874C34E9577514F95777D519577D0000200280100000200030000000000000000009E020000000000002801000020223A0300000000000000009C0002009C000200ECE8A501CA334D719C0002002801000002000300000000009C000200DA334D71F8E8A50103F68874F5F388740BF688745626431C00000000109E3703280100000000000001000000E8E8A50138519577D00002002801000002000300000000000000000030E9A501D1509577D00002002801000002000300E850957726C9441C28010000000000009097CD028896CD0224E9A5013DA9647600000000FBFFFF7F48E9A501987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000FA5CA072BA5CA070FA5CA07000000000000000000000000080000002E006C006E006B0000006E00640020001100000010473400084734002E006C00FCE90000BCC9441CACE9A50182916476FCE9A501B0E9A50127956476000000008C31CA02D8E9A501CD9464768C31CA0284EAA501002DCA02E194647600000000002DCA0284EAA501E0E9A5010000000001000000B31202007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000F701EC0AF701A4E8A5015869207700000000D007F701C4E8A5010B8C1F770100000000000000537A1F775604010200200000000000000100000010E9A50136170D76560401021008F7010500000000000000FFFFFFFFD007F701000000000CE9A50138E9A50100000000000000000000000064E9A501703B3A000000000040913B77090080015CE9A50135590D7656040102A00641030500000044E9A501506A20771CC0247701000000EF7A1F77560401021D000000002000005CE9A50163590D7664E9A5010000000000000000560401024066377701000000C8E9A501A13697770000000000000000D82C3900C8E9A501B8369777E0929A770000000000003100A006410300000000C4E9A5010E000B007C0100000000000000000000CF679577280641030100000098064103D0E9A501E82C8377D82C3900CF679577ECEBA501110000001047340008473400000031000000000050EA0000C0C9441C00EAA5018291647650EAA50104EAA50127956476000000008C31CA022CEAA501CD9464768C31CA02D8EAA501002DCA02E194647600000000002DCA02D8EAA50134EAA5010000000001000000B31202007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000F701EC0AF701A4E8A5015869207700000000D007F701C4E8A5010B8C1F770100000000000000537A1F775604010200200000000000000100000010E9A50136170D76560401021008F7010500000000000000FFFFFFFFD007F701000000000CE9A50138E9A50100000000000000000000000064E9A501703B3A000000000040913B77090080015CE9A50135590D7656040102A00641030500000044E9A501506A20771CC0247701000000EF7A1F77560401021D000000002000005CE9A50163590D7664E9A5010000000000000000560401024066377701000000C8E9A501A13697770000000000000000D82C3900C8E9A501B8369777E0929A770000000000003100A006410300000000C4E9A5010E000B007C0100000000000000000000CF679577280641030100000098064103D0E9A501E82C8377D82C3900CF679577ECEBA501110000001047340008473400000031000000000050EA0000C0C9441C00EAA5018291647650EAA50104EAA50127956476000000008C31CA022CEAA501CD9464768C31CA02D8EAA501002DCA02E194647600000000002DCA02D8EAA50134EAA501 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 0000000001000000010000000F0F0100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF400981C149D7D30100000000 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000100000002000000C221030001000000010000000F0F01007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000020003000000000022608874C34E9577514F95777D519577D0000200280100000200030000000000000000009E020000000000002801000020223A0300000000000000009C0002009C000200ECE8A501CA334D719C0002002801000002000300000000009C000200DA334D71F8E8A50103F68874F5F388740BF688745626431C00000000109E3703280100000000000001000000E8E8A50138519577D00002002801000002000300000000000000000030E9A501D1509577D00002002801000002000300E850957726C9441C28010000000000009097CD028896CD0224E9A5013DA9647600000000FBFFFF7F48E9A501987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000FA5CA072BA5CA070FA5CA07000000000000000000000000080000002E006C006E006B0000006E00640020001100000010473400084734002E006C00FCE90000BCC9441C00EA0000B4C9441CB4E9A5018291647600EAA501B8E9A50127956476000000008C31CA02E0E9A501CD9464768C31CA02002DCA0284EAA501E194647600000000002DCA0284EAA501E8E9A50101000000010000000F0F01007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000020003000000000022608874C34E9577514F95777D519577D0000200280100000200030000000000000000009E020000000000002801000020223A0300000000000000009C0002009C000200ECE8A501CA334D719C0002002801000002000300000000009C000200DA334D71F8E8A50103F68874F5F388740BF688745626431C00000000109E3703280100000000000001000000E8E8A50138519577D00002002801000002000300000000000000000030E9A501D1509577D00002002801000002000300E850957726C9441C28010000000000009097CD028896CD0224E9A5013DA9647600000000FBFFFF7F48E9A501987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000FA5CA072BA5CA070FA5CA07000000000000000000000000080000002E006C006E006B0000006E00640020001100000010473400084734002E006C00FCE90000BCC9441C00EA0000B4C9441CB4E9A5018291647600EAA501B8E9A50127956476000000008C31CA02E0E9A501CD9464768C31CA02002DCA0284EAA501E194647600000000002DCA0284EAA501E8E9A50101000000010000000F0F01007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000020003000000000022608874C34E9577514F95777D519577D0000200280100000200030000000000000000009E020000000000002801000020223A0300000000000000009C0002009C000200ECE8A501CA334D719C0002002801000002000300000000009C000200DA334D71F8E8A50103F68874F5F388740BF688745626431C00000000109E3703280100000000000001000000E8E8A50138519577D00002002801000002000300000000000000000030E9A501D1509577D00002002801000002000300E850957726C9441C28010000000000009097CD028896CD0224E9A5013DA9647600000000FBFFFF7F48E9A501987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000FA5CA072BA5CA070FA5CA07000000000000000000000000080000002E006C006E006B0000006E00640020001100000010473400084734002E006C00FCE90000BCC9441C00EA0000B4C9441CB4E9A5018291647600EAA501B8E9A50127956476000000008C31CA02E0E9A501CD9464768C31CA02002DCA0284EAA501E194647600000000002DCA0284EAA501E8E9A501 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 00000000010000000100000077150100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF400981C149D7D30100000000 | |||
| (PID) Process: | (1640) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000001000000020000002A2803000100000001000000771501007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D8EAA501D0EAA50100000000C0B6F7013C0000004AC8441CC0E8A501240122778CE8A5010000000000000000100000000000000000000000480BF7010500000000000000340CF701480BF70104591F770000000008B7F7010000000008B7F70100000000340CF7010000000000000000D80BF7010000000008EAA501480BF70158EAA50174FF9602000000000000000004E9A5013B57237750EAA50160EAA5010000000000000000480BF701D80BF70100000000340CF701000000000500000058EAA501000000000000000000000000F4E9A50194E9A501FA59227750EAA50160EAA501F4E9A50158E9A50174E9A50184E9A501480BF7010000000005000000D80BF70100000000340CF70108EAA50158EAA50100000000045A227708EAA5010500000005000000000000000000000000000000000000000000000000000000B505017D000000000000000011000000104734000847340000000000FCE90000BCC9441CACE9A50182916476FCE9A501B0E9A50127956476000000008C31CA02D8E9A501CD9464768C31CA0284EAA501002DCA02E194647600000000002DCA0284EAA501E0E9A5010100000001000000771501007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D8EAA501D0EAA50100000000C0B6F7013C0000004AC8441CC0E8A501240122778CE8A5010000000000000000100000000000000000000000480BF7010500000000000000340CF701480BF70104591F770000000008B7F7010000000008B7F70100000000340CF7010000000000000000D80BF7010000000008EAA501480BF70158EAA50174FF9602000000000000000004E9A5013B57237750EAA50160EAA5010000000000000000480BF701D80BF70100000000340CF701000000000500000058EAA501000000000000000000000000F4E9A50194E9A501FA59227750EAA50160EAA501F4E9A50158E9A50174E9A50184E9A501480BF7010000000005000000D80BF70100000000340CF70108EAA50158EAA50100000000045A227708EAA5010500000005000000000000000000000000000000000000000000000000000000B505017D000000000000000011000000104734000847340000000000FCE90000BCC9441CACE9A50182916476FCE9A501B0E9A50127956476000000008C31CA02D8E9A501CD9464768C31CA0284EAA501002DCA02E194647600000000002DCA0284EAA501E0E9A5010100000001000000771501007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D8EAA501D0EAA50100000000C0B6F7013C0000004AC8441CC0E8A501240122778CE8A5010000000000000000100000000000000000000000480BF7010500000000000000340CF701480BF70104591F770000000008B7F7010000000008B7F70100000000340CF7010000000000000000D80BF7010000000008EAA501480BF70158EAA50174FF9602000000000000000004E9A5013B57237750EAA50160EAA5010000000000000000480BF701D80BF70100000000340CF701000000000500000058EAA501000000000000000000000000F4E9A50194E9A501FA59227750EAA50160EAA501F4E9A50158E9A50174E9A50184E9A501480BF7010000000005000000D80BF70100000000340CF70108EAA50158EAA50100000000045A227708EAA5010500000005000000000000000000000000000000000000000000000000000000B505017D000000000000000011000000104734000847340000000000FCE90000BCC9441CACE9A50182916476FCE9A501B0E9A50127956476000000008C31CA02D8E9A501CD9464768C31CA0284EAA501002DCA02E194647600000000002DCA0284EAA501E0E9A501 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | explorer.exe | C:\Users\admin\AppData\Local\IconCache.db | binary | |
MD5:— | SHA256:— | |||
| 1640 | explorer.exe | C:\Users\admin\Desktop\TSMSISrv - Copy.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report