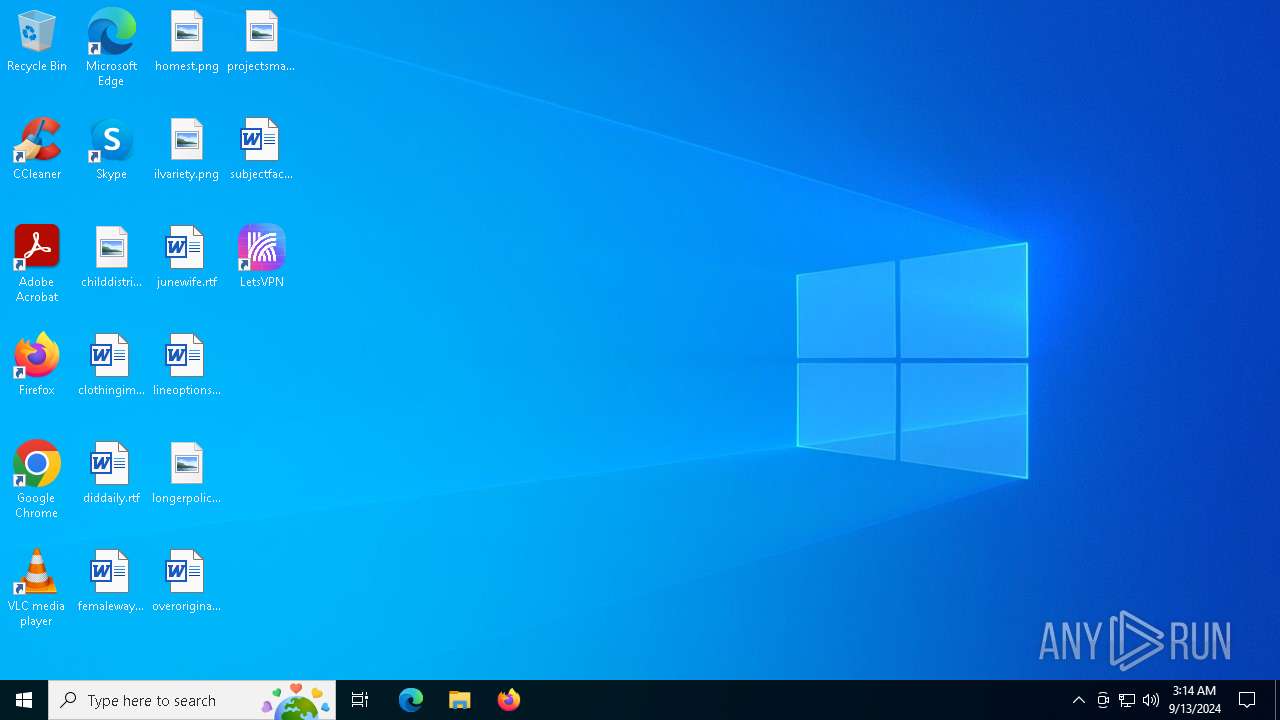
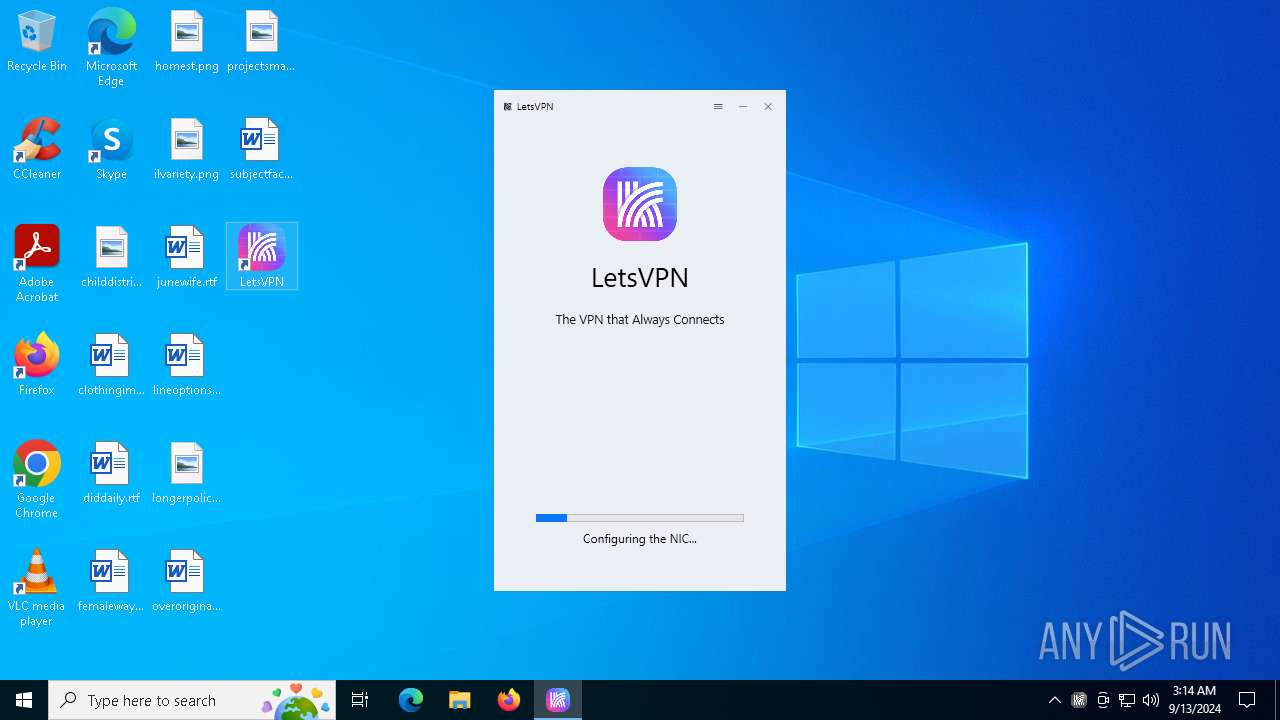
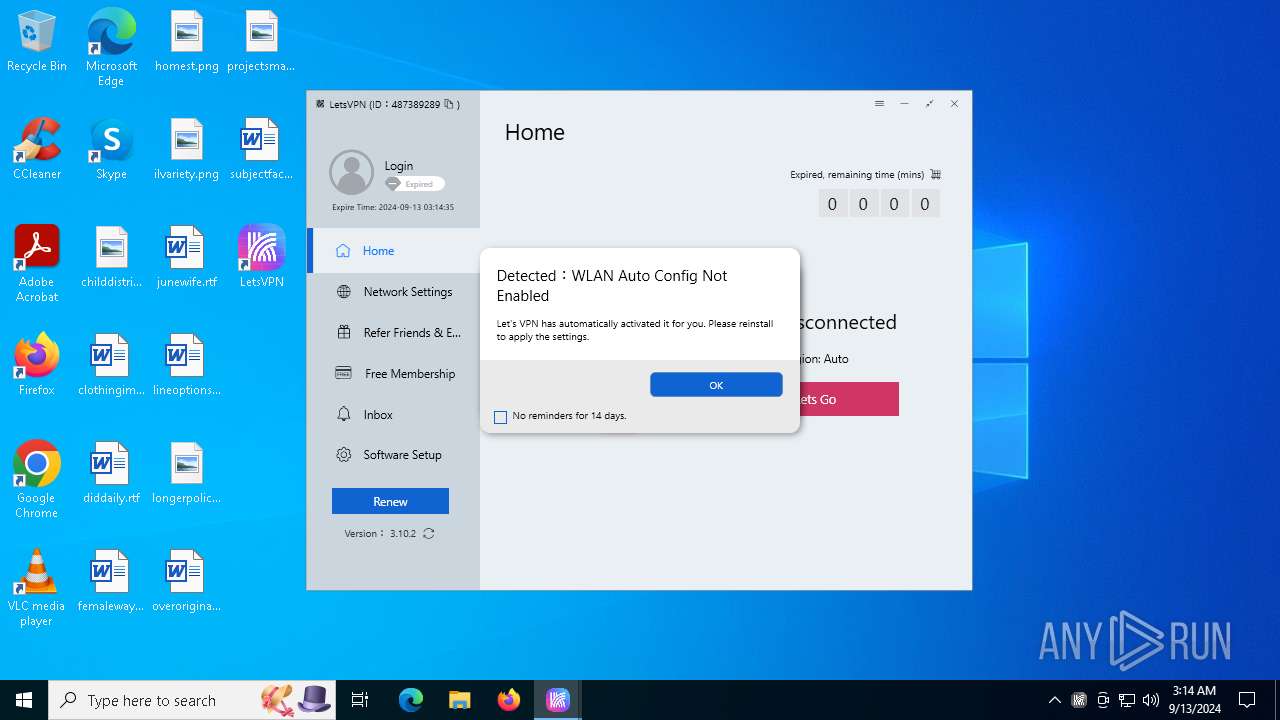
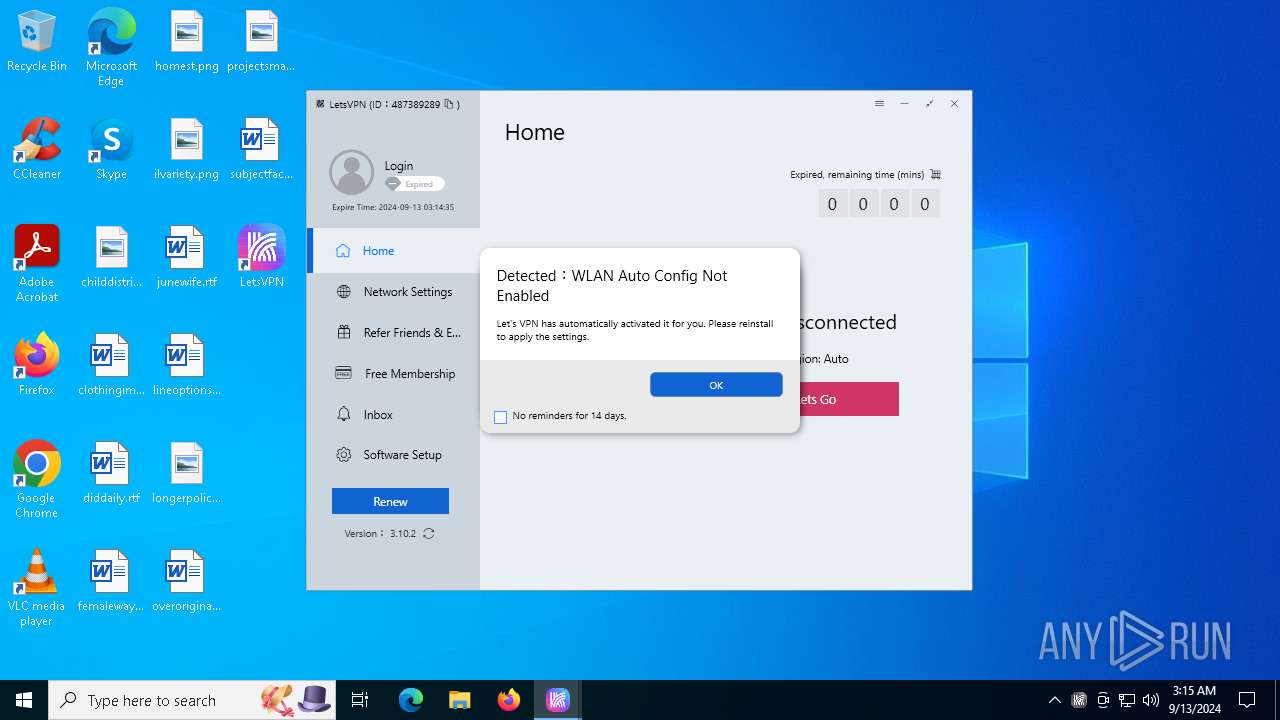
| File name: | letsvpn-latest.exe |
| Full analysis: | https://app.any.run/tasks/14e7dd59-cce1-4216-9836-91200809fe50 |
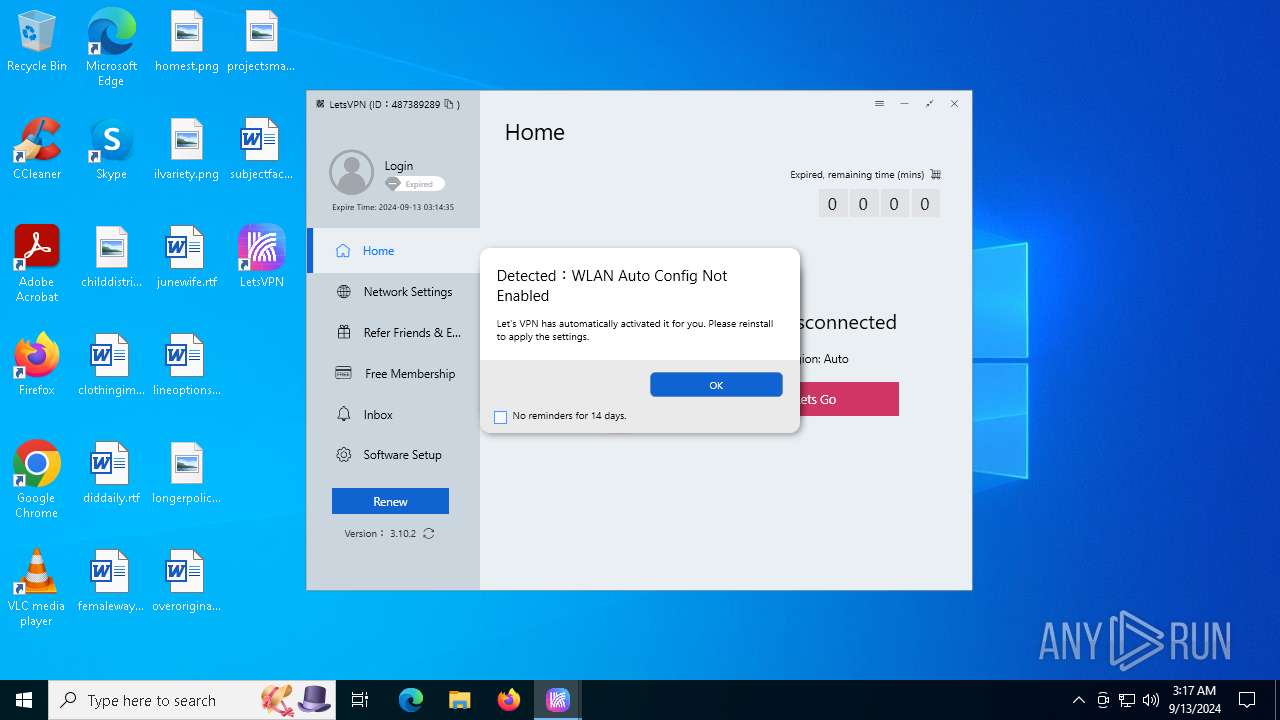
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2024, 03:13:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
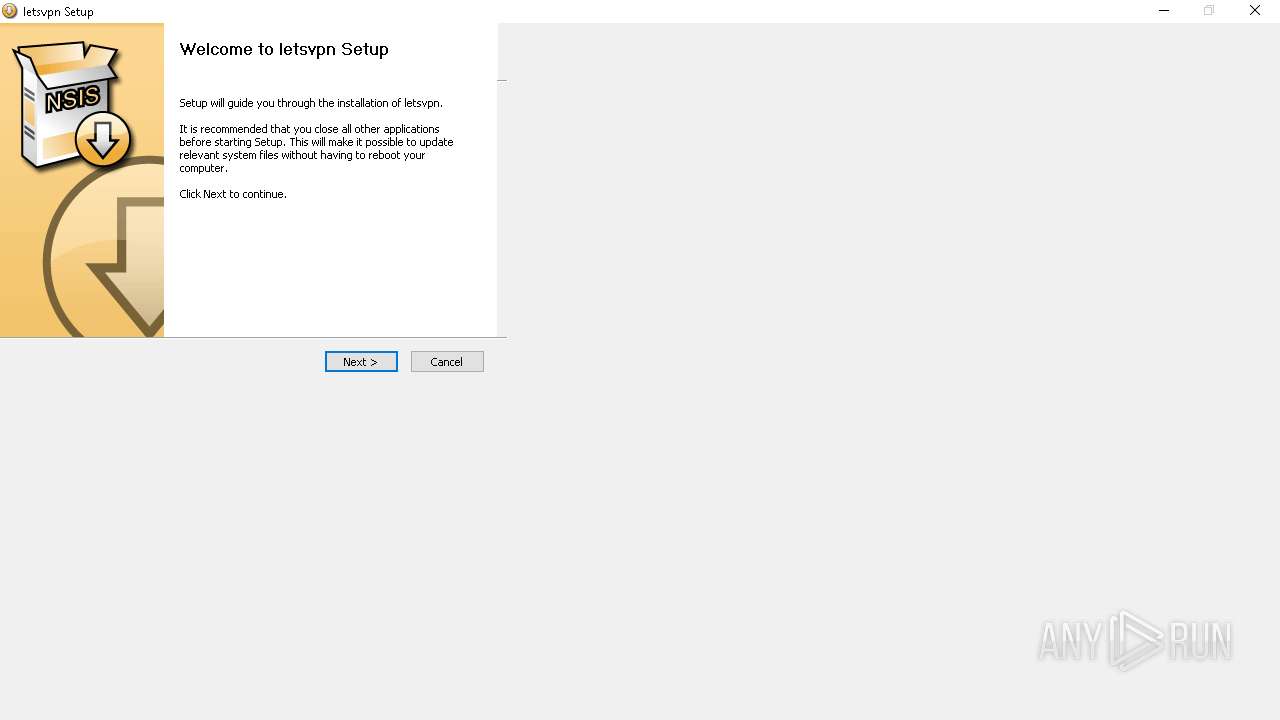
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 94F6BD702B7A2E17C45D16EAF7DA0D64 |
| SHA1: | 45F8C05851BCF16416E087253CE962B320E9DB8A |
| SHA256: | 07F44325EAB13B01D536A42E90A0247C6EFECF23CCD4586309828AA814F5C776 |
| SSDEEP: | 196608:KVRrUSWRLbOXpTQy3DJajGVYwDfMtuxfsC5abtpByzr:KVFjeLbYtQyUjGVYwD04psC4tpByn |
MALICIOUS
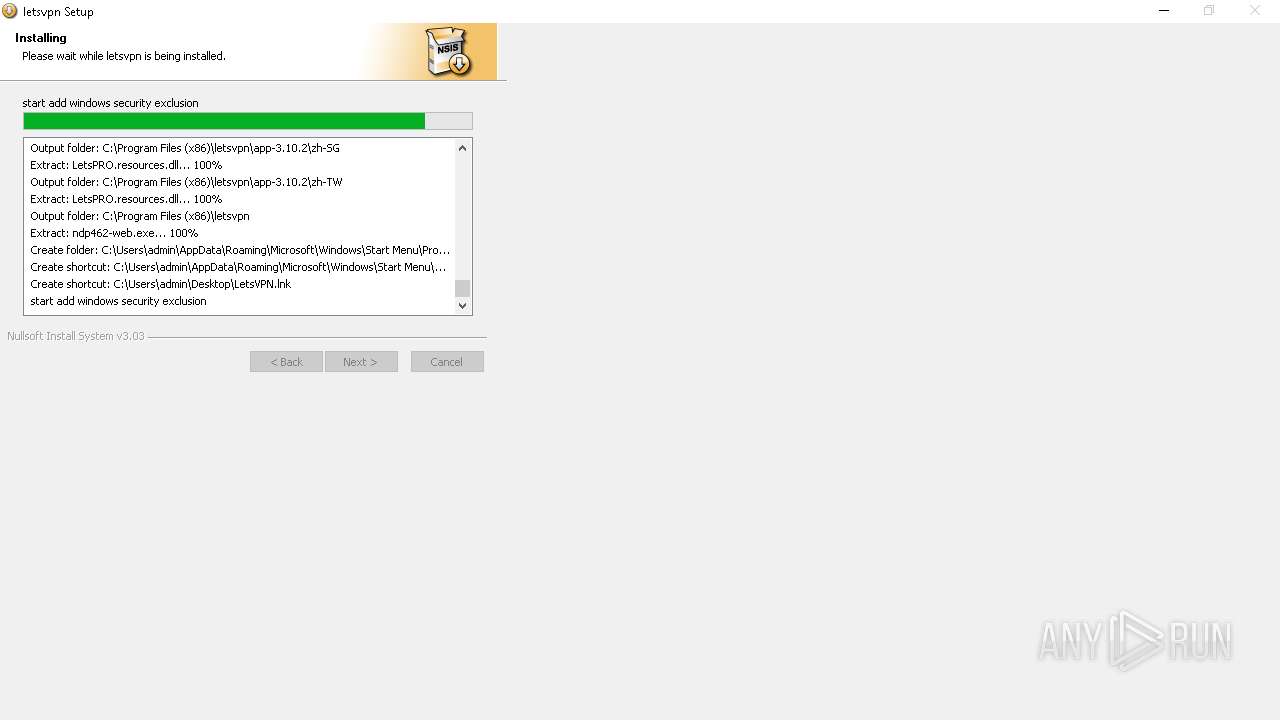
Bypass execution policy to execute commands
- powershell.exe (PID: 6016)
- powershell.exe (PID: 1292)
Changes powershell execution policy (Bypass)
- letsvpn-latest.exe (PID: 4704)
Changes the autorun value in the registry
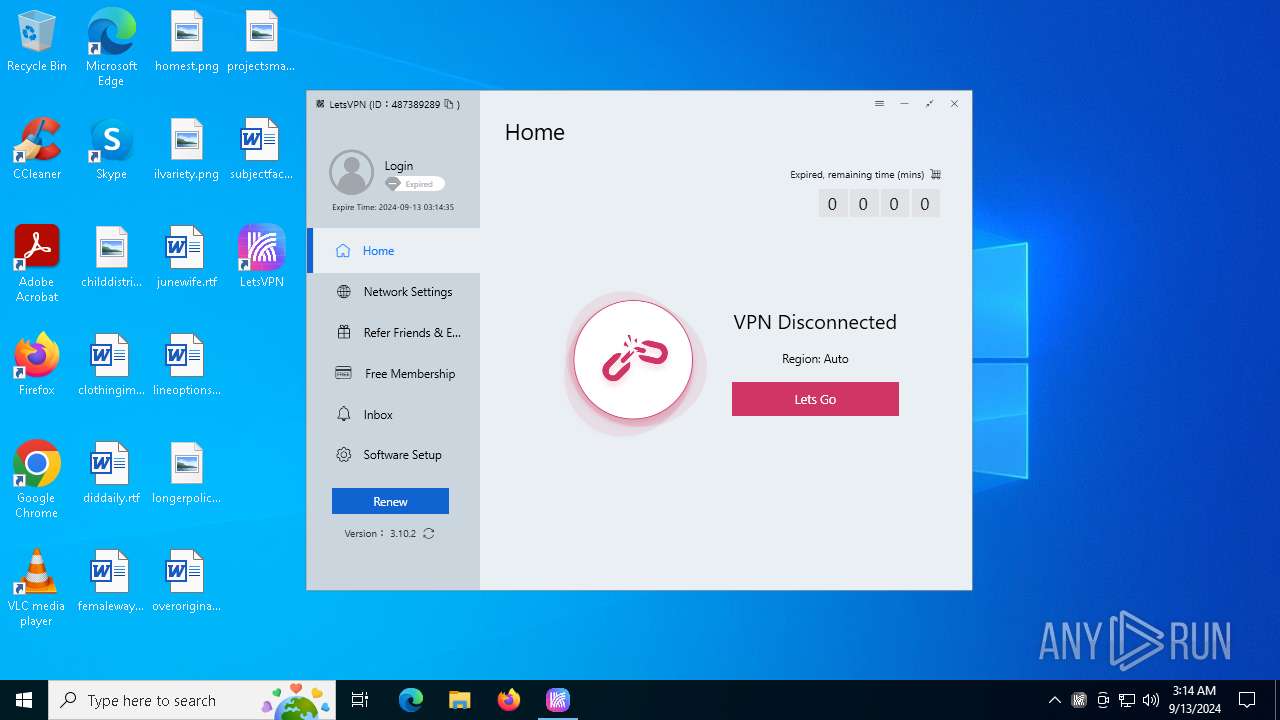
- LetsPRO.exe (PID: 6568)
SUSPICIOUS
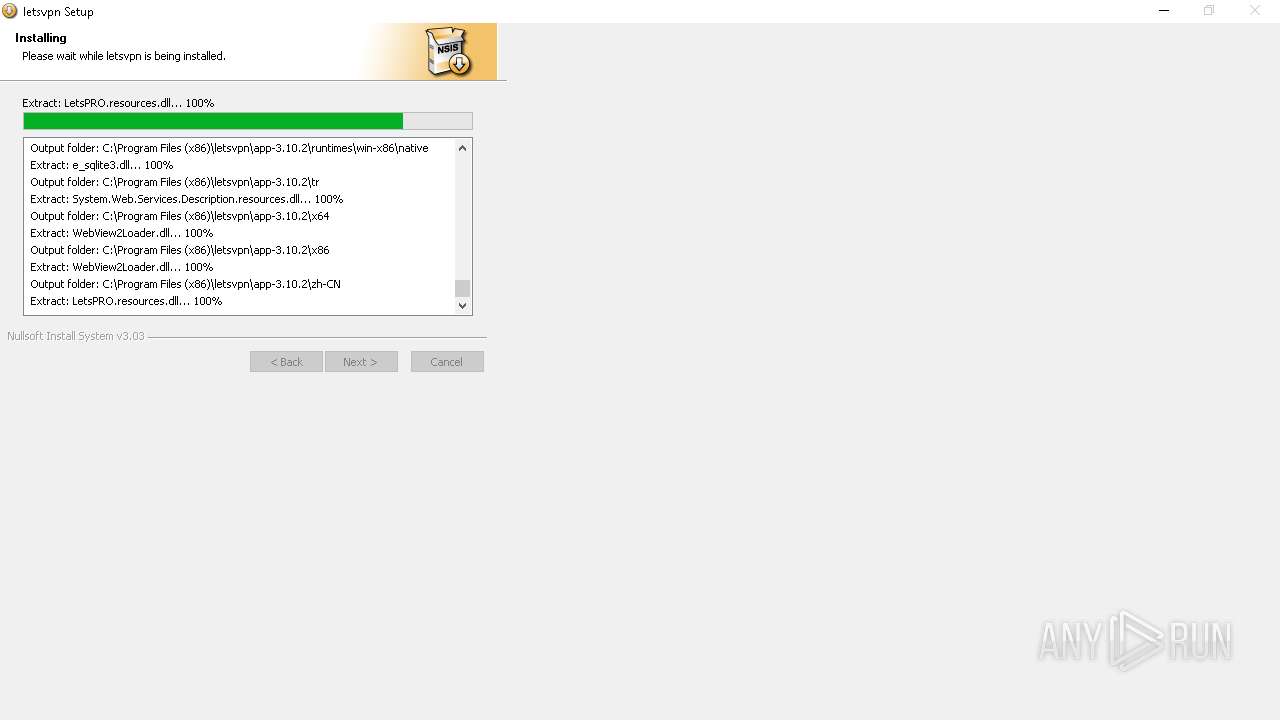
Malware-specific behavior (creating "System.dll" in Temp)
- letsvpn-latest.exe (PID: 4704)
Checks processor architecture
- powershell.exe (PID: 6016)
Process drops legitimate windows executable
- letsvpn-latest.exe (PID: 4704)
Starts POWERSHELL.EXE for commands execution
- letsvpn-latest.exe (PID: 4704)
Drops a system driver (possible attempt to evade defenses)
- letsvpn-latest.exe (PID: 4704)
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 6676)
The process creates files with name similar to system file names
- letsvpn-latest.exe (PID: 4704)
Executable content was dropped or overwritten
- letsvpn-latest.exe (PID: 4704)
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- drvinst.exe (PID: 6212)
Reads security settings of Internet Explorer
- tapinstall.exe (PID: 5720)
- LetsPRO.exe (PID: 6568)
Checks Windows Trust Settings
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- LetsPRO.exe (PID: 6568)
Creates files in the driver directory
- drvinst.exe (PID: 6676)
- drvinst.exe (PID: 6212)
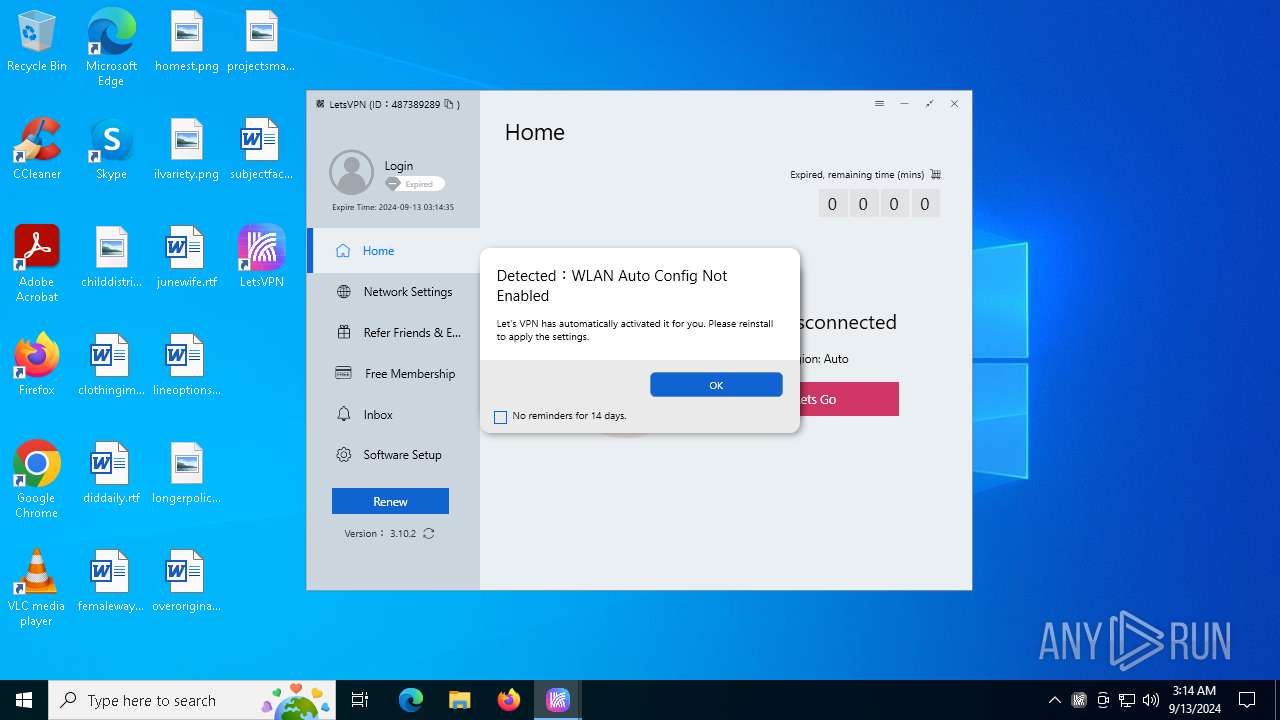
Creates or modifies Windows services
- drvinst.exe (PID: 6212)
Starts CMD.EXE for commands execution
- letsvpn-latest.exe (PID: 4704)
- LetsPRO.exe (PID: 6568)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6720)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 1124)
Creates a software uninstall entry
- letsvpn-latest.exe (PID: 4704)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 1060)
The process checks if it is being run in the virtual environment
- LetsPRO.exe (PID: 6568)
Executes as Windows Service
- WmiApSrv.exe (PID: 1608)
Suspicious use of NETSH.EXE
- LetsPRO.exe (PID: 6568)
Process uses ARP to discover network configuration
- cmd.exe (PID: 5160)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 2796)
The process executes Powershell scripts
- letsvpn-latest.exe (PID: 4704)
INFO
Checks supported languages
- letsvpn-latest.exe (PID: 4704)
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- drvinst.exe (PID: 6212)
- LetsPRO.exe (PID: 5044)
- LetsPRO.exe (PID: 6568)
- tapinstall.exe (PID: 5376)
- tapinstall.exe (PID: 2580)
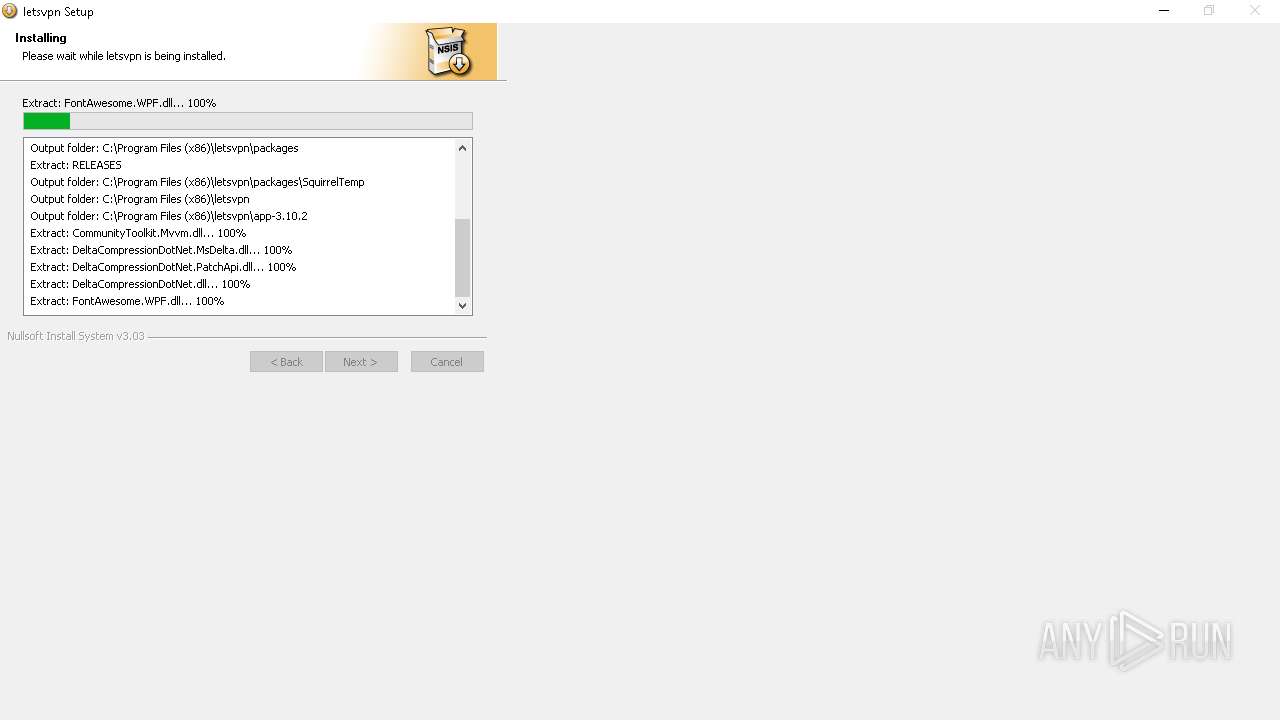
Create files in a temporary directory
- letsvpn-latest.exe (PID: 4704)
- tapinstall.exe (PID: 5720)
- LetsPRO.exe (PID: 6568)
Reads the computer name
- letsvpn-latest.exe (PID: 4704)
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- drvinst.exe (PID: 6212)
- LetsPRO.exe (PID: 6568)
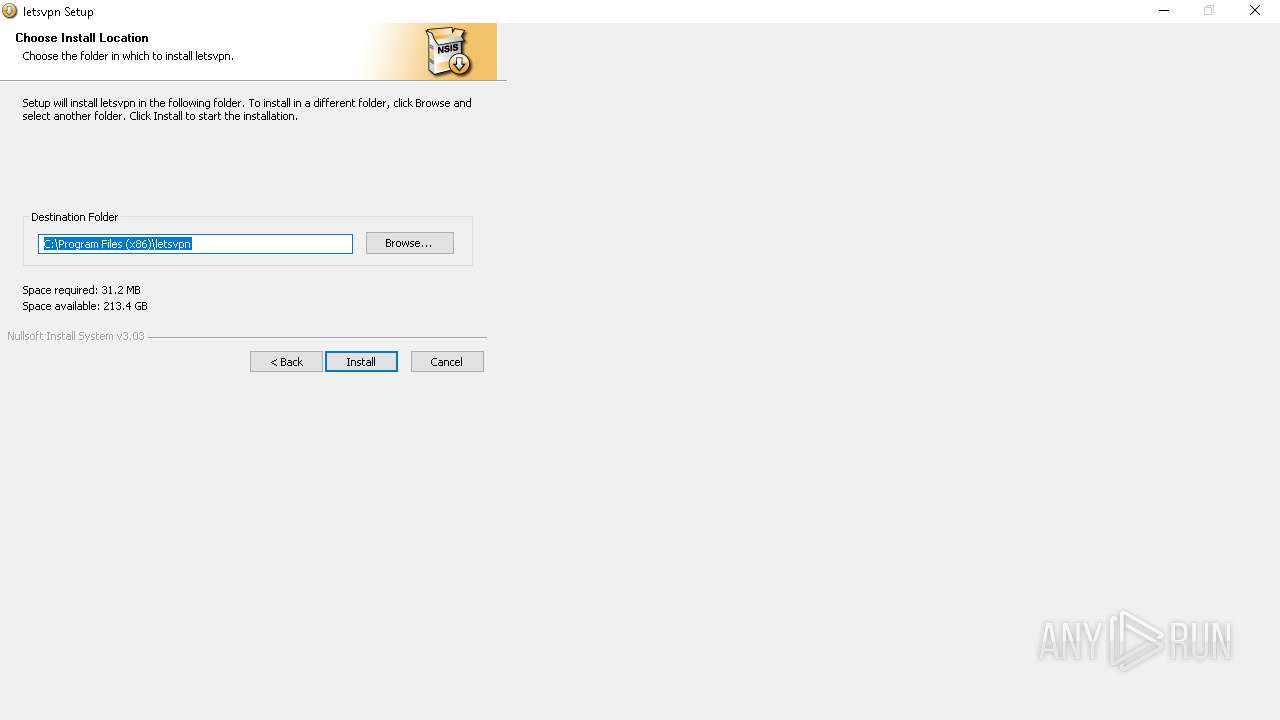
Creates files in the program directory
- letsvpn-latest.exe (PID: 4704)
- LetsPRO.exe (PID: 6568)
Creates files or folders in the user directory
- letsvpn-latest.exe (PID: 4704)
- LetsPRO.exe (PID: 6568)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1292)
- LetsPRO.exe (PID: 6568)
Reads the software policy settings
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- LetsPRO.exe (PID: 6568)
Reads the machine GUID from the registry
- tapinstall.exe (PID: 5720)
- drvinst.exe (PID: 6676)
- LetsPRO.exe (PID: 6568)
The process uses the downloaded file
- LetsPRO.exe (PID: 6568)
- powershell.exe (PID: 1292)
Reads Windows Product ID
- LetsPRO.exe (PID: 6568)
Reads CPU info
- LetsPRO.exe (PID: 6568)
Reads the time zone
- LetsPRO.exe (PID: 6568)
Checks proxy server information
- LetsPRO.exe (PID: 6568)
Disables trace logs
- LetsPRO.exe (PID: 6568)
- netsh.exe (PID: 6644)
Attempting to connect via WebSocket
- LetsPRO.exe (PID: 6568)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
167
Monitored processes
40
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | "cmd.exe" /C route print | C:\Windows\SysWOW64\cmd.exe | — | LetsPRO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1124 | cmd /c netsh advfirewall firewall Delete rule name=LetsPRO | C:\Windows\SysWOW64\cmd.exe | — | letsvpn-latest.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | powershell -inputformat none -ExecutionPolicy Bypass -File "C:\Program Files (x86)\letsvpn\AddWindowsSecurityExclusion.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | letsvpn-latest.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1608 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2248 | netsh advfirewall firewall Delete rule name=LetsPRO.exe | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Program Files (x86)\letsvpn\driver\tapinstall.exe" findall tap0901 | C:\Program Files (x86)\letsvpn\driver\tapinstall.exe | — | letsvpn-latest.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 2796 | "cmd.exe" /C ipconfig /all | C:\Windows\SysWOW64\cmd.exe | — | LetsPRO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 992
Read events
45 824
Write events
150
Delete events
18
Modification events
| (PID) Process: | (4704) letsvpn-latest.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Lets |
| Operation: | write | Name: | InstallTimeStamp |
Value: 20240913031413.737 | |||
| (PID) Process: | (4704) letsvpn-latest.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Lets |
| Operation: | write | Name: | InstallNewVersion |
Value: 3.10.2 | |||
| (PID) Process: | (5720) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\tap0901 |
| Operation: | write | Name: | Owners |
Value: oem1.inf | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\PnpLockdownFiles\%SystemRoot%/System32/drivers/tap0901.sys |
| Operation: | write | Name: | Owners |
Value: oem1.inf | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_662fd96dfdced4ae\Descriptors\tap0901 |
| Operation: | write | Name: | Configuration |
Value: tap0901.ndi | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_662fd96dfdced4ae\Descriptors\tap0901 |
| Operation: | write | Name: | Manufacturer |
Value: %provider% | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_662fd96dfdced4ae\Descriptors\tap0901 |
| Operation: | write | Name: | Description |
Value: %devicedescription% | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_662fd96dfdced4ae\Configurations\tap0901.ndi |
| Operation: | write | Name: | Service |
Value: tap0901 | |||
| (PID) Process: | (6212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_662fd96dfdced4ae\Configurations\tap0901.ndi |
| Operation: | write | Name: | ConfigScope |
Value: 5 | |||
Executable files
222
Suspicious files
28
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6016 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E1015863F57D4268A22DE74FB0604B1D | SHA256:8DCCDA0D44972E768EABCA75CF5319FFB2A8C3CF252B339068CF3167706AC01E | |||
| 4704 | letsvpn-latest.exe | C:\Users\admin\AppData\Local\Temp\nsrAA14.tmp\modern-header.bmp | image | |
MD5:5ACF495828FEAE7F85E006B7774AF497 | SHA256:6CFEBB59F0BA1B9F1E8D7AA6387F223A468EB2FF74A9ED3C3F4BB688C2B6455E | |||
| 4704 | letsvpn-latest.exe | C:\Users\admin\AppData\Local\Temp\nsrAA14.tmp\modern-wizard.bmp | image | |
MD5:7F8E1969B0874C8FB9AB44FC36575380 | SHA256:076221B4527FF13C3E1557ABBBD48B0CB8E5F7D724C6B9171C6AADADB80561DD | |||
| 6016 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nbgw15xr.1c5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\driver\tap0901.sys | executable | |
MD5:C10CCDEC5D7AF458E726A51BB3CDC732 | SHA256:589C5667B1602837205DA8EA8E92FE13F8C36048B293DF931C99B39641052253 | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\driver\OemVista.inf | binary | |
MD5:26009F092BA352C1A64322268B47E0E3 | SHA256:150EF8EB07532146F833DC020C02238161043260B8A565C3CFCB2365BAD980D9 | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\driver\tap0901.cat | binary | |
MD5:F73AC62E8DF97FAF3FC8D83E7F71BF3F | SHA256:CC74CDB88C198EB00AEF4CAA20BF1FDA9256917713A916E6B94435CD4DCB7F7B | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\app-3.10.2\CommunityToolkit.Mvvm.dll | executable | |
MD5:8BFA2E9DC7F4AC42D1FA58FC3FF37267 | SHA256:C5059BF1DD92DEB3C590D0EA8065DC62B89259F4266C0EA54F5C8D062056C76F | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\packages\RELEASES | text | |
MD5:88743D5BBFAE19E5A47718DFE70AA16D | SHA256:6665603C3313E2A1BB963AB2B9D3B48AC38A083B4C7060CF506EBA6837474B84 | |||
| 4704 | letsvpn-latest.exe | C:\Program Files (x86)\letsvpn\driver\tapinstall.exe | executable | |
MD5:1E3CF83B17891AEE98C3E30012F0B034 | SHA256:9F45A39015774EEAA2A6218793EDC8E6273EB9F764F3AEDEE5CF9E9CCACDB53F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
76
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6568 | LetsPRO.exe | GET | 101 | 52.74.183.227:80 | http://ws-ap1.pusher.com/app/4fc436ef36f4026102d7?protocol=5&client=pusher-dotnet-client&version=1.1.2 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
1480 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1480 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7072 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1944 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1944 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
7072 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.baidu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6568 | LetsPRO.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |