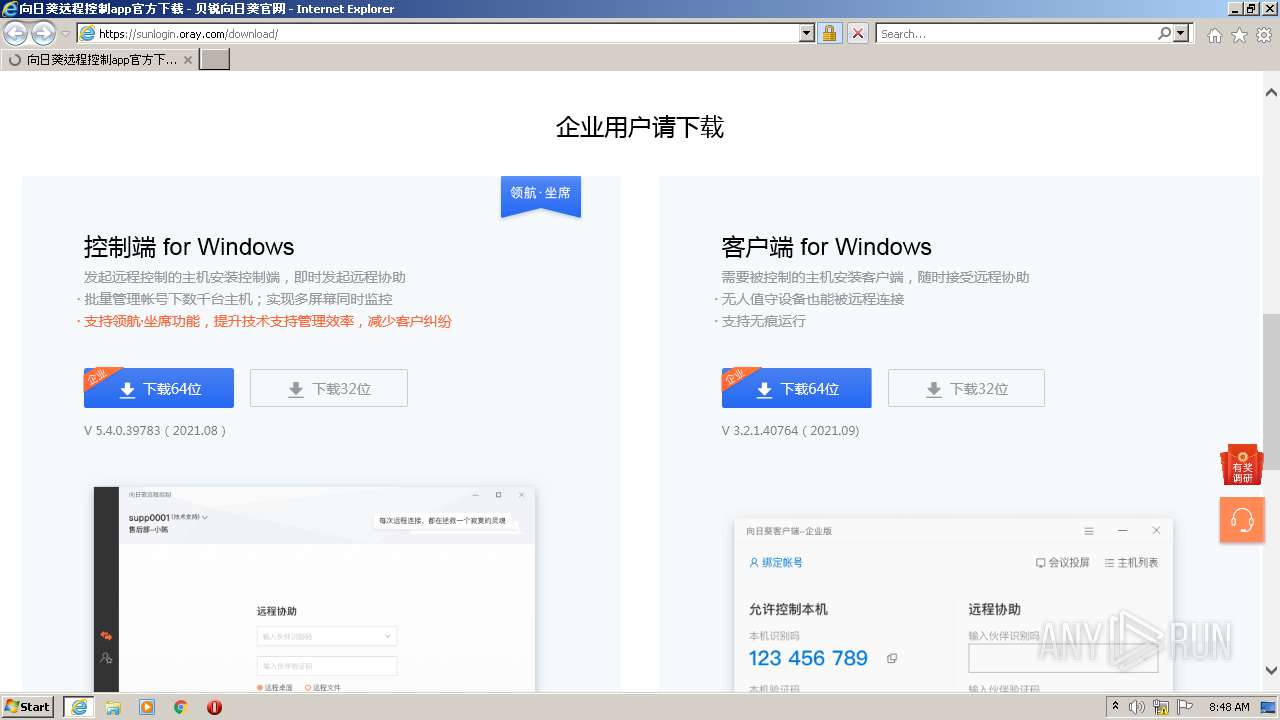
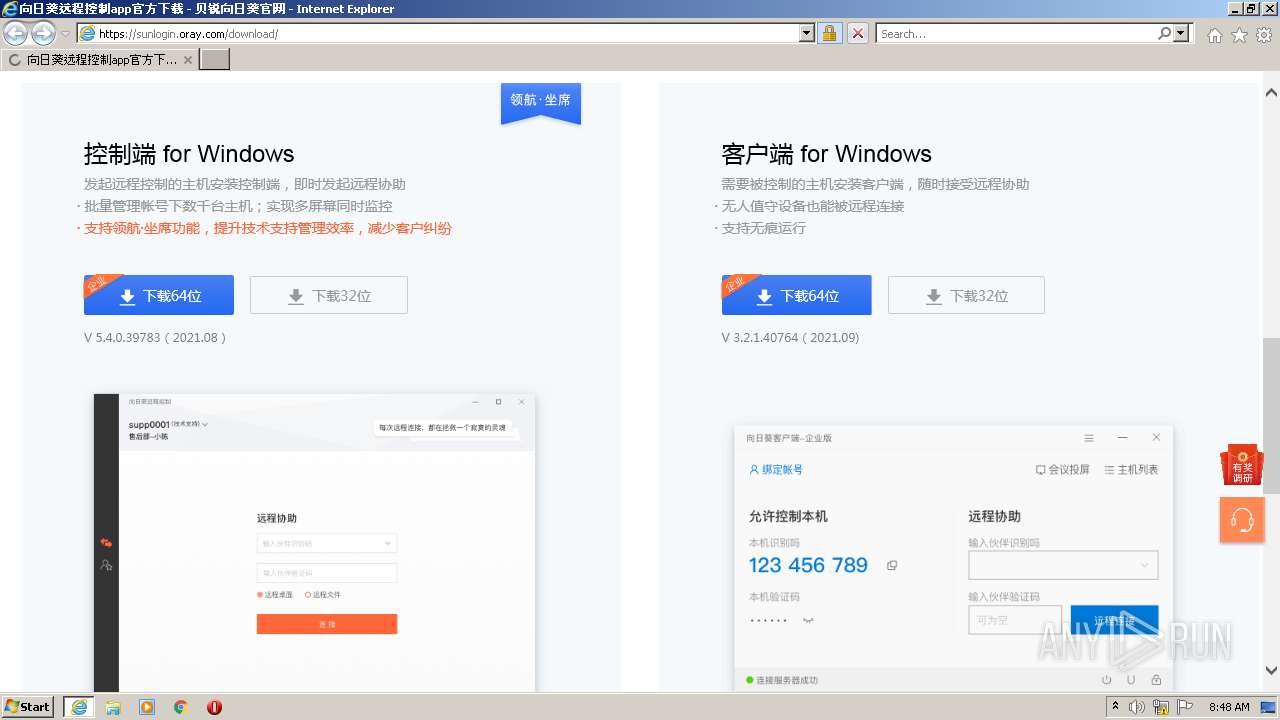
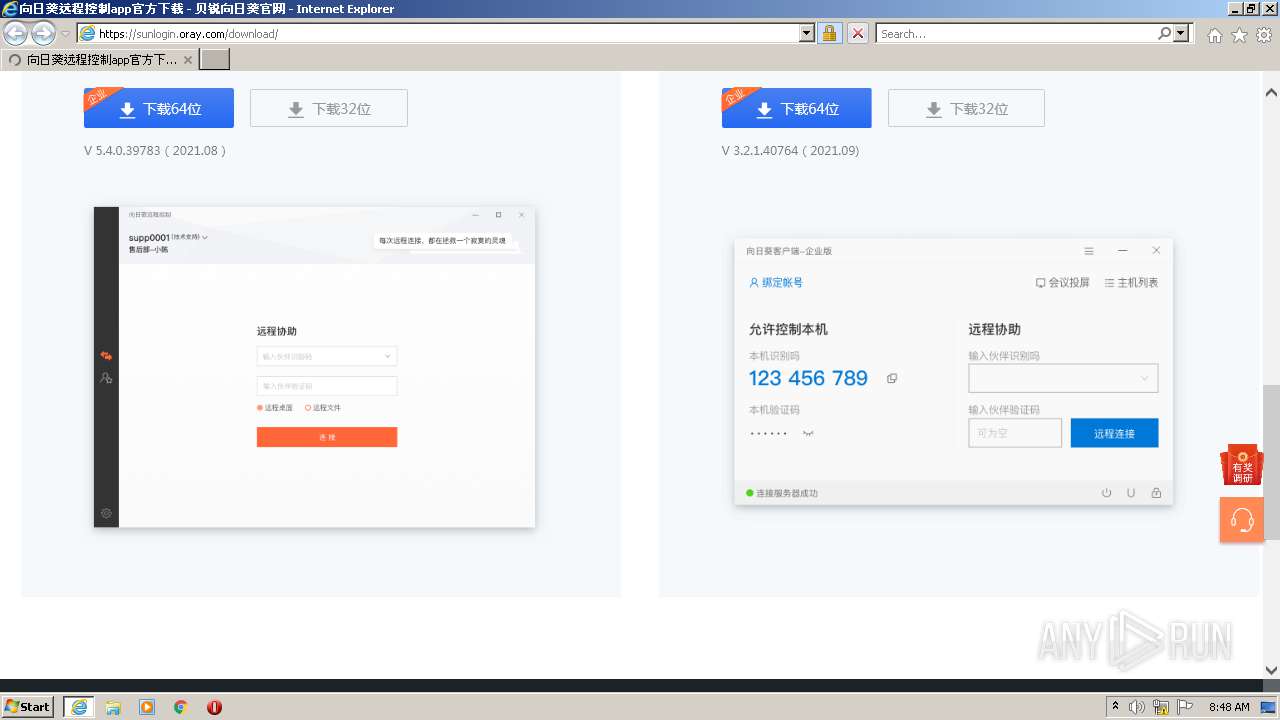
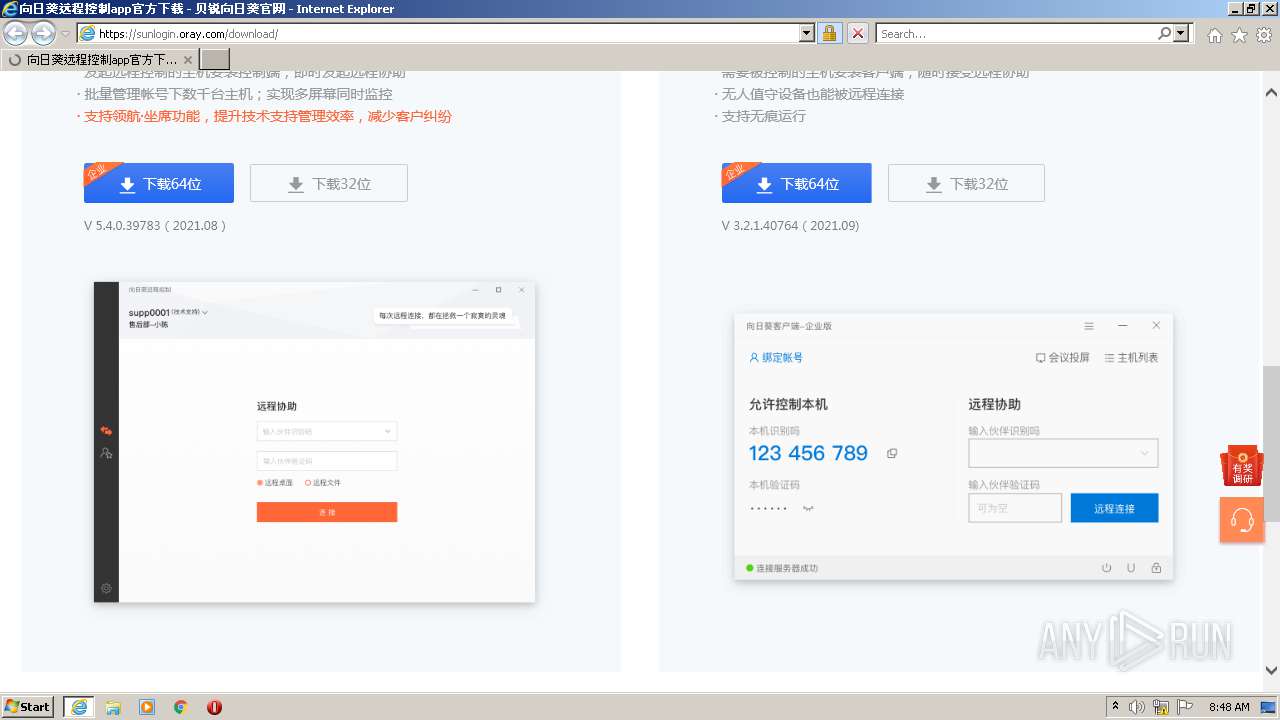
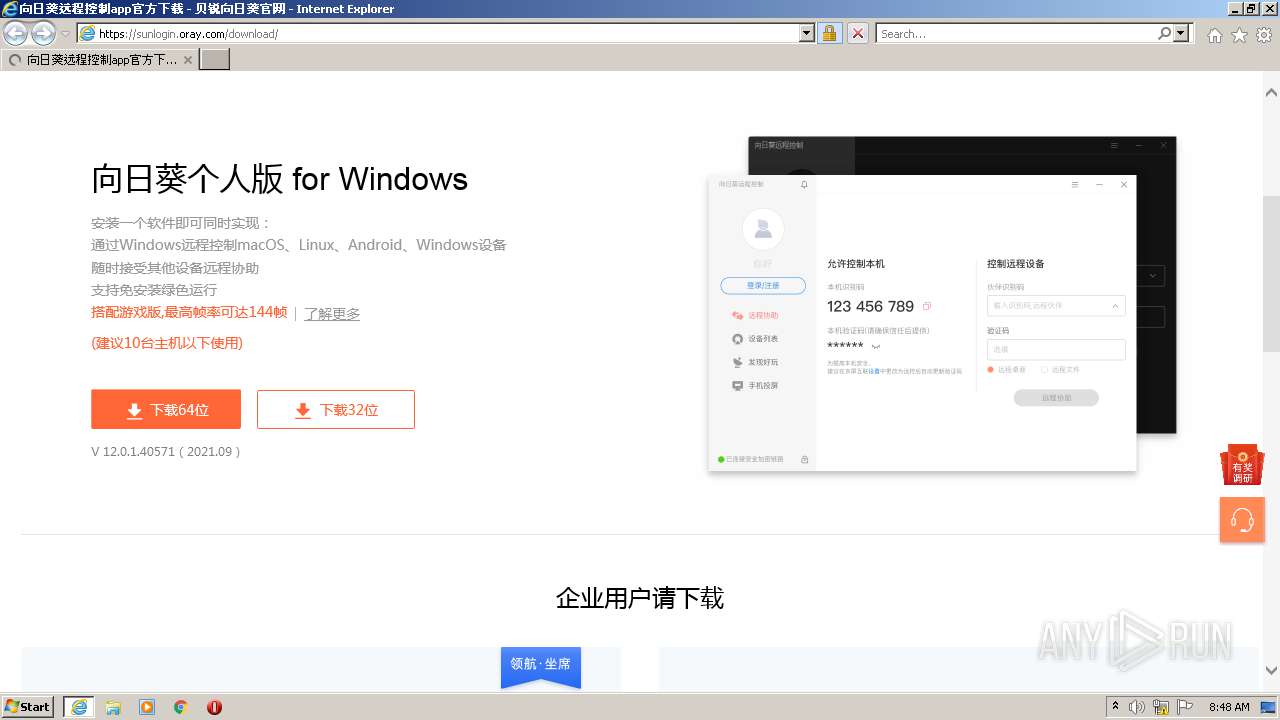
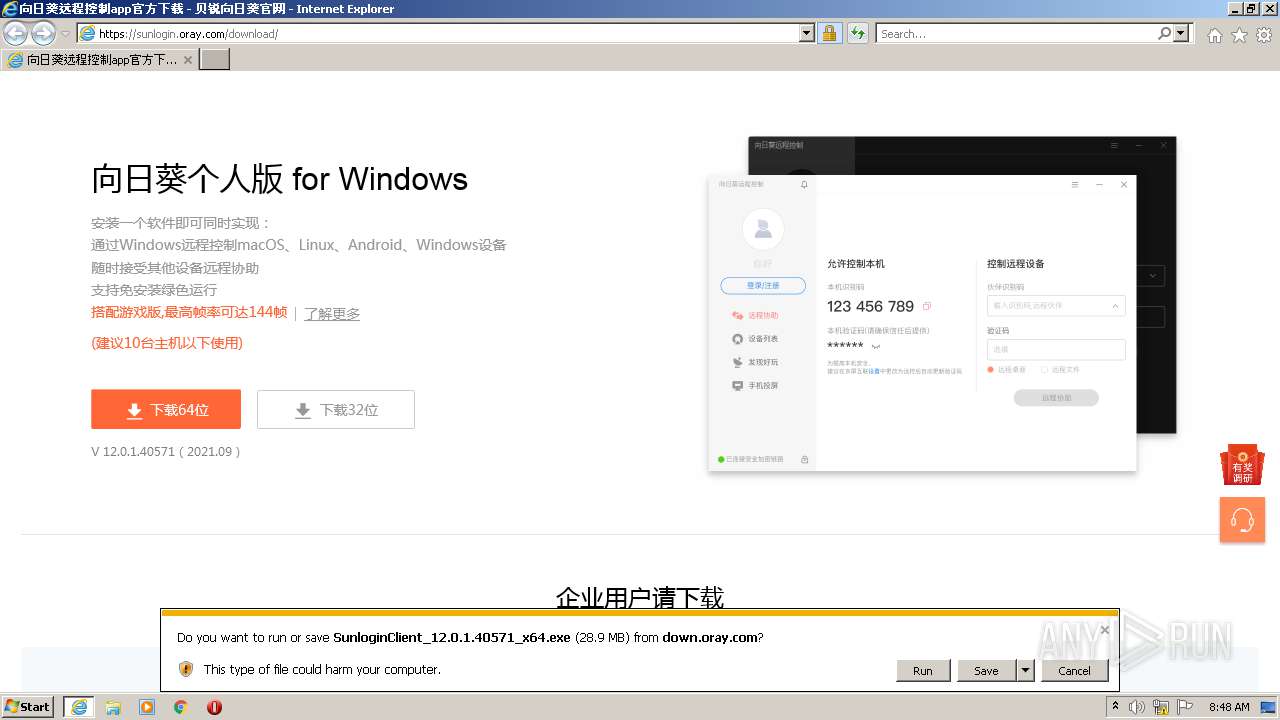
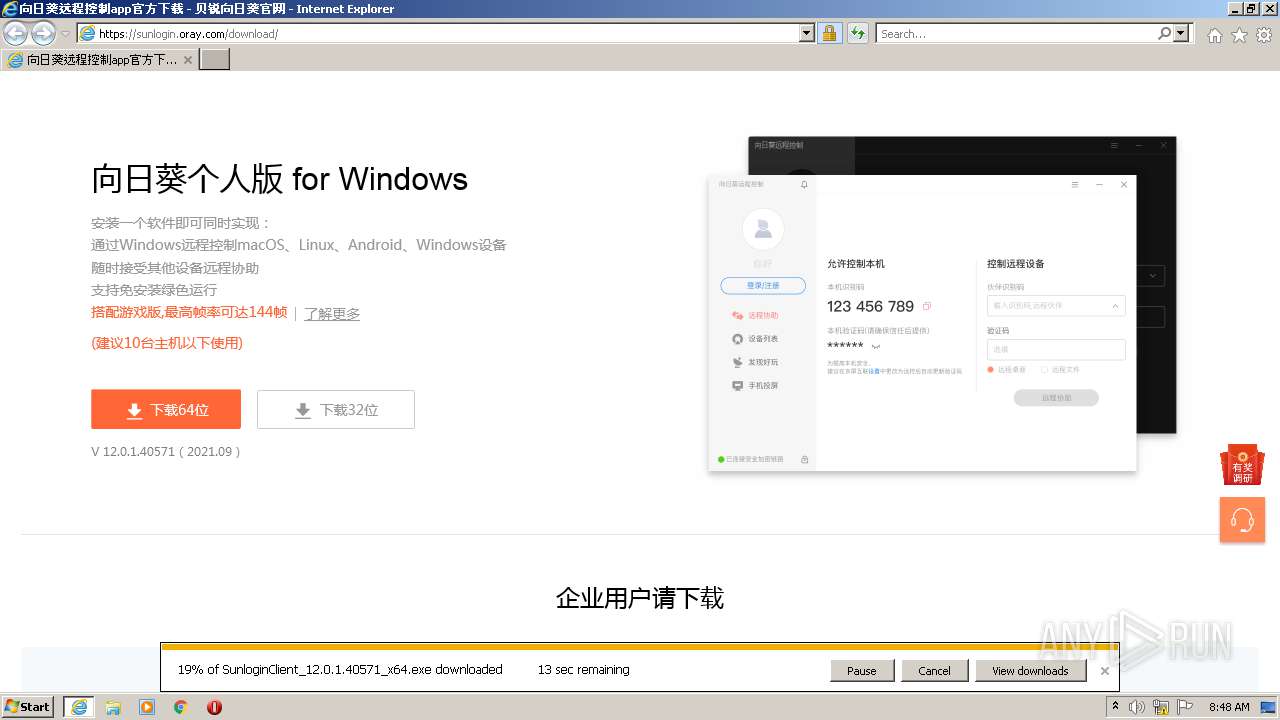
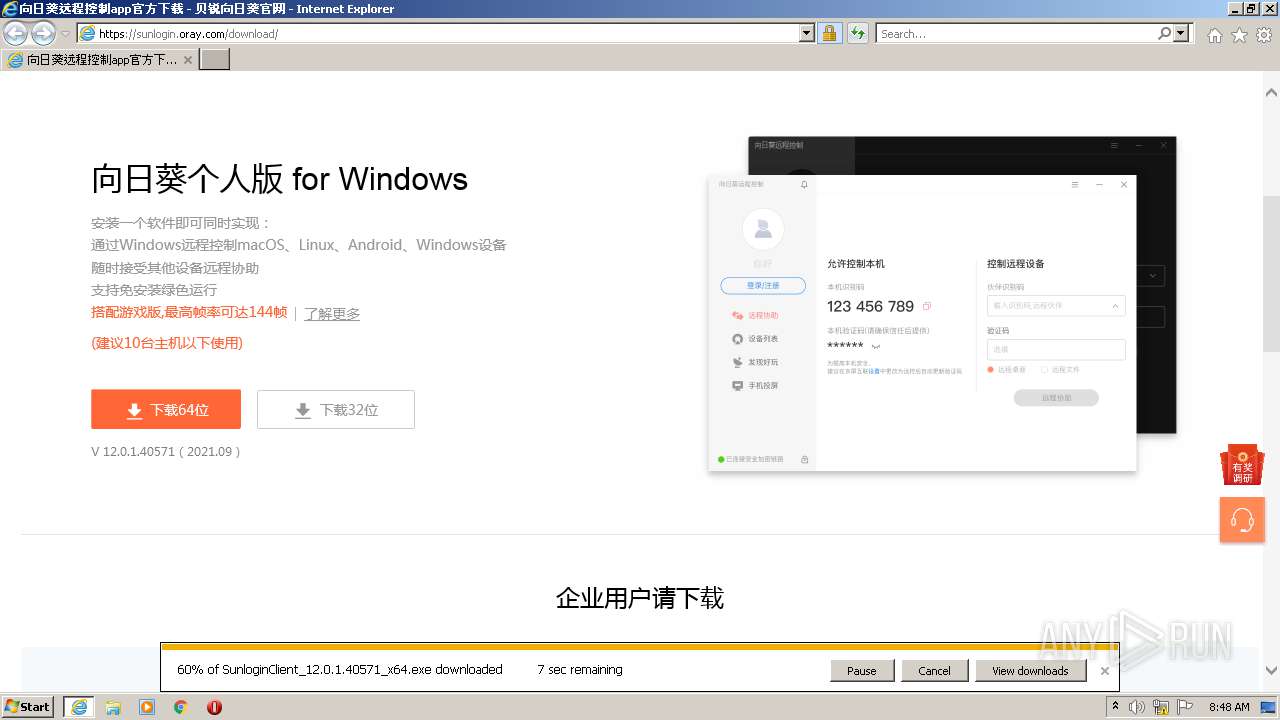
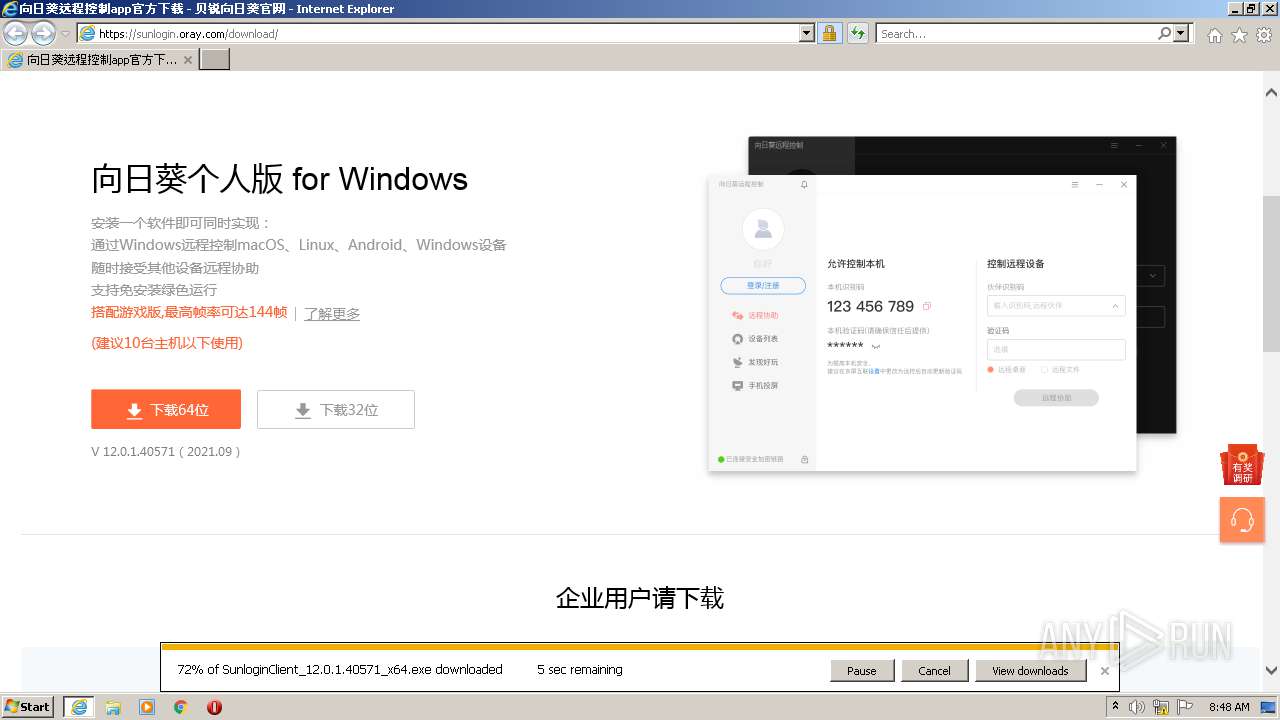
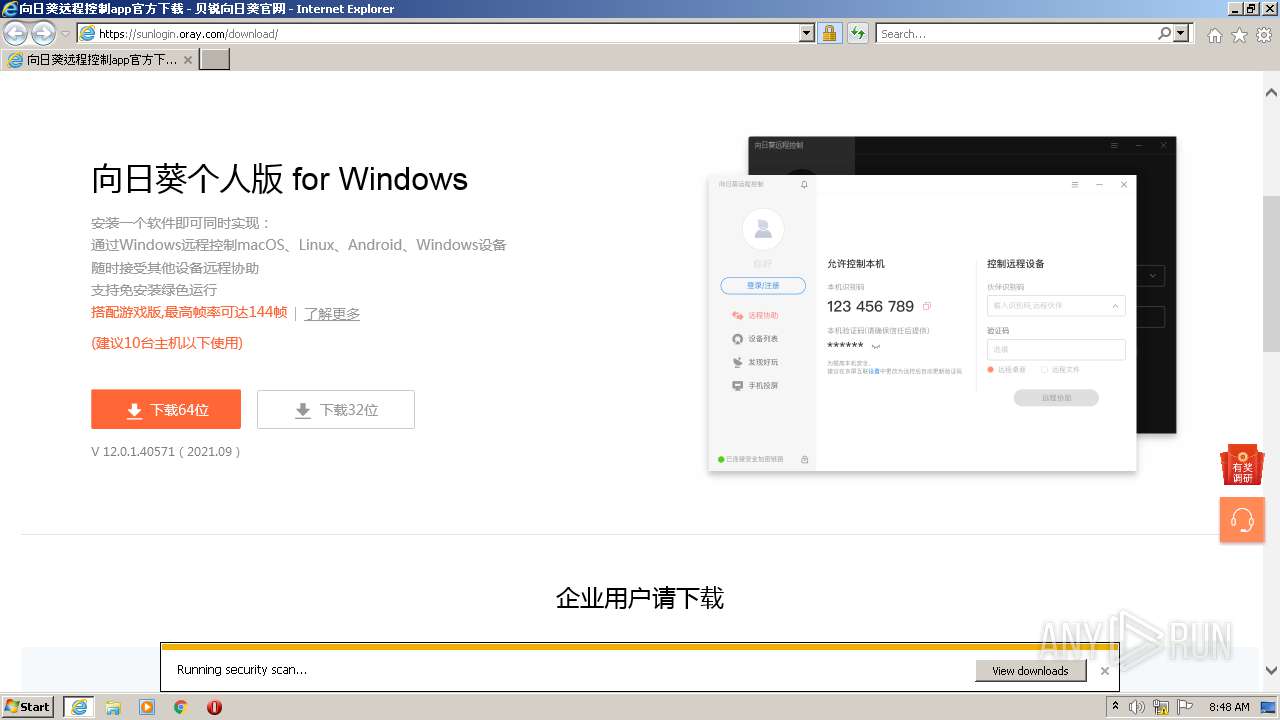
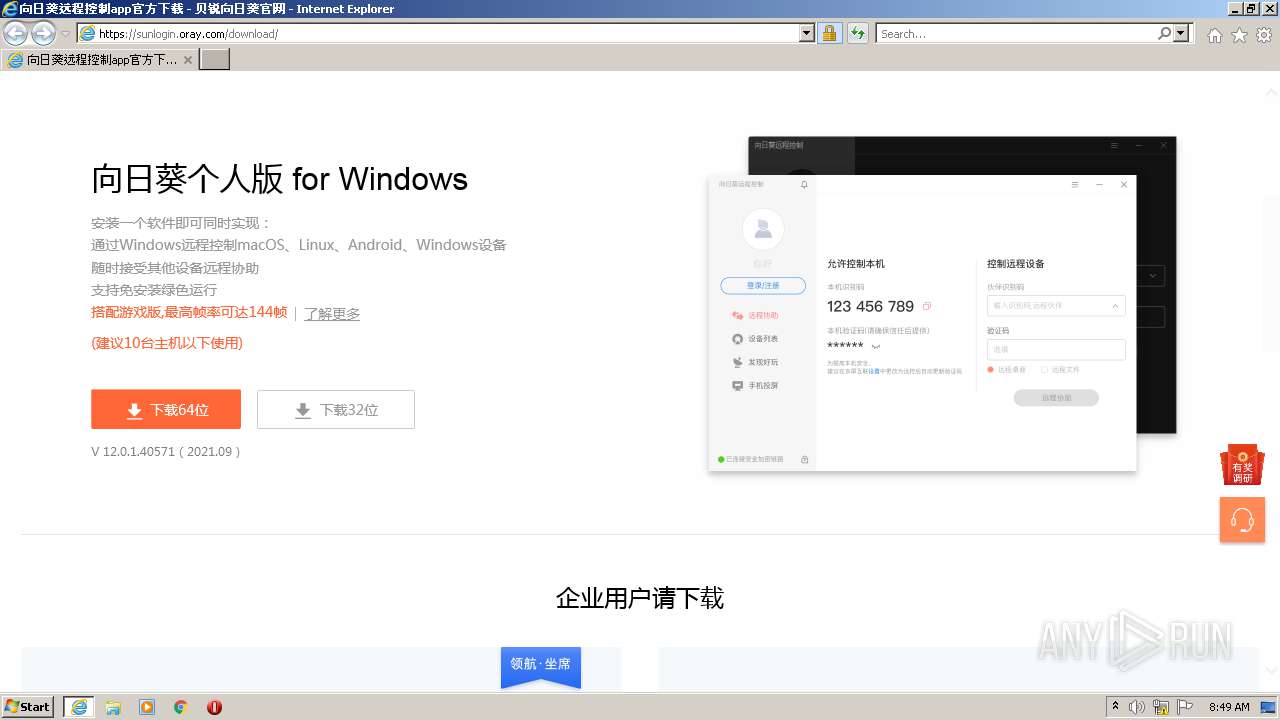
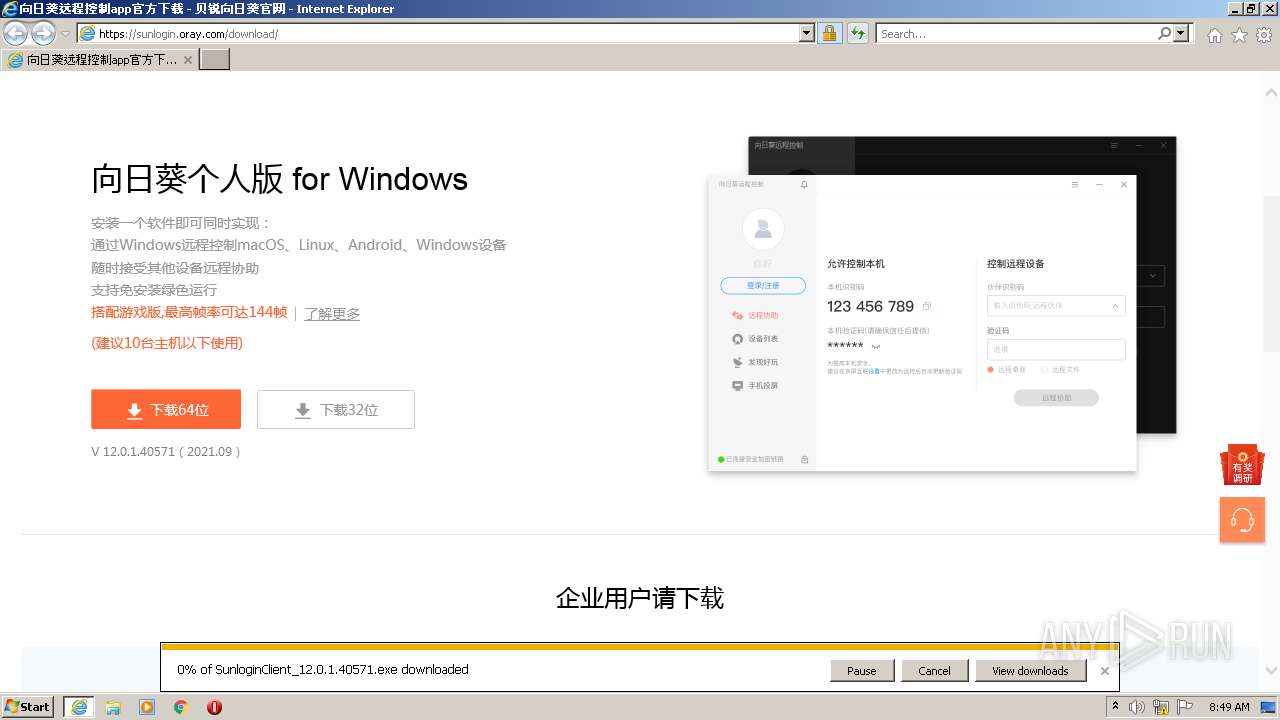
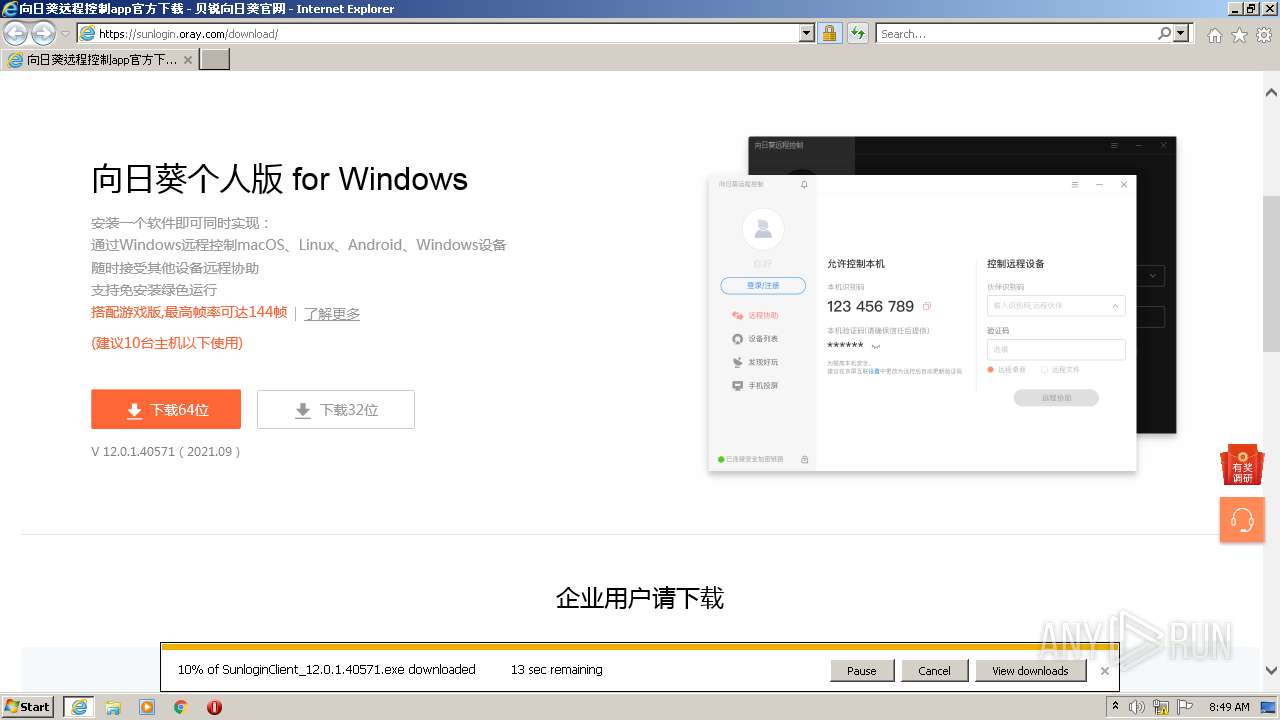
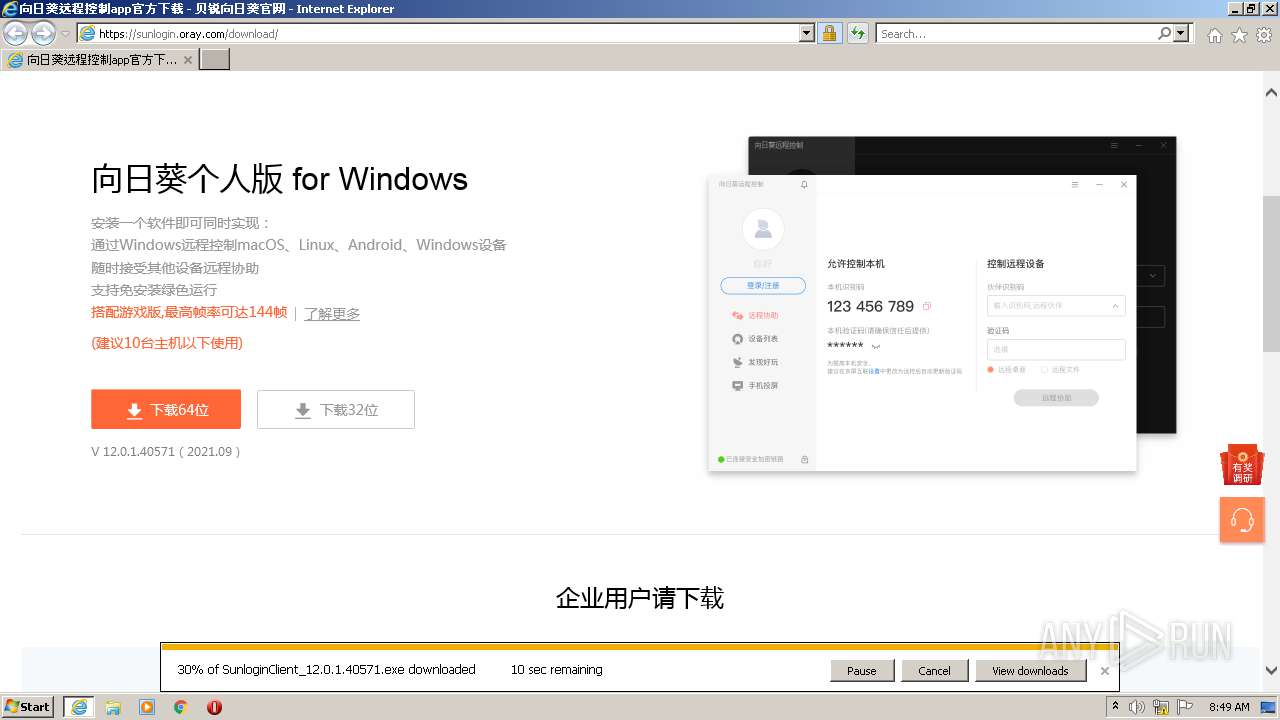
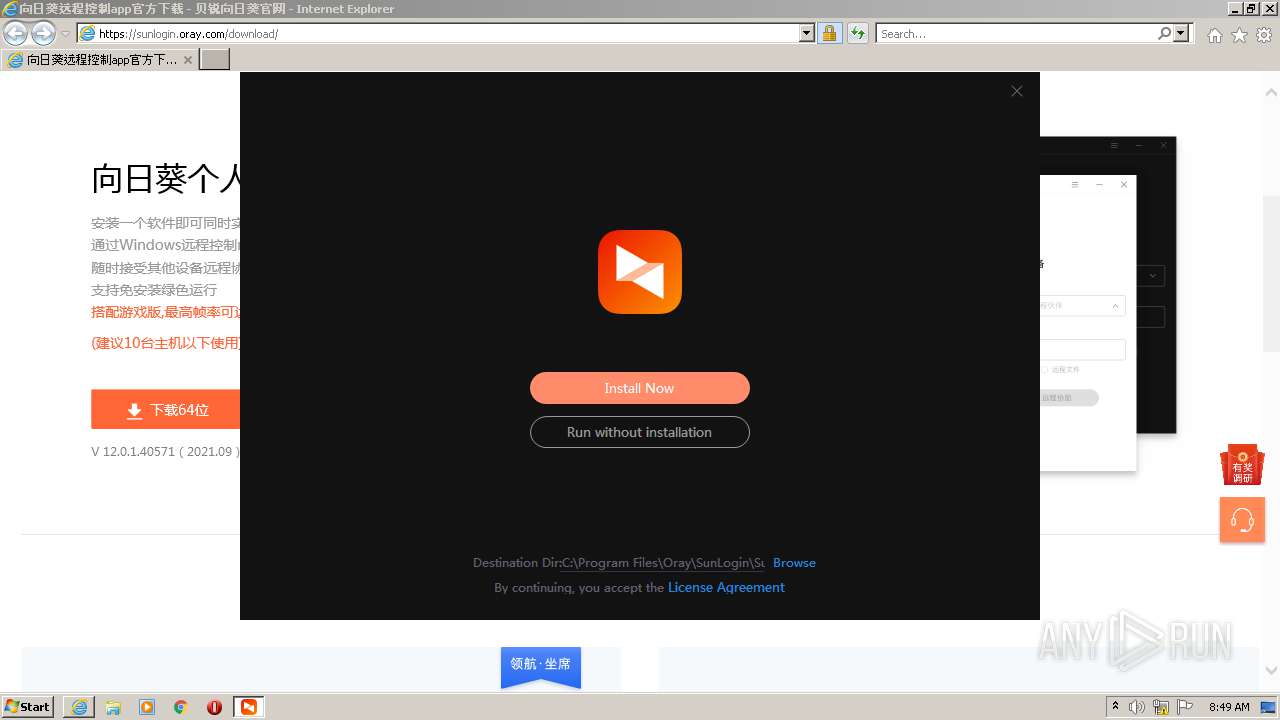
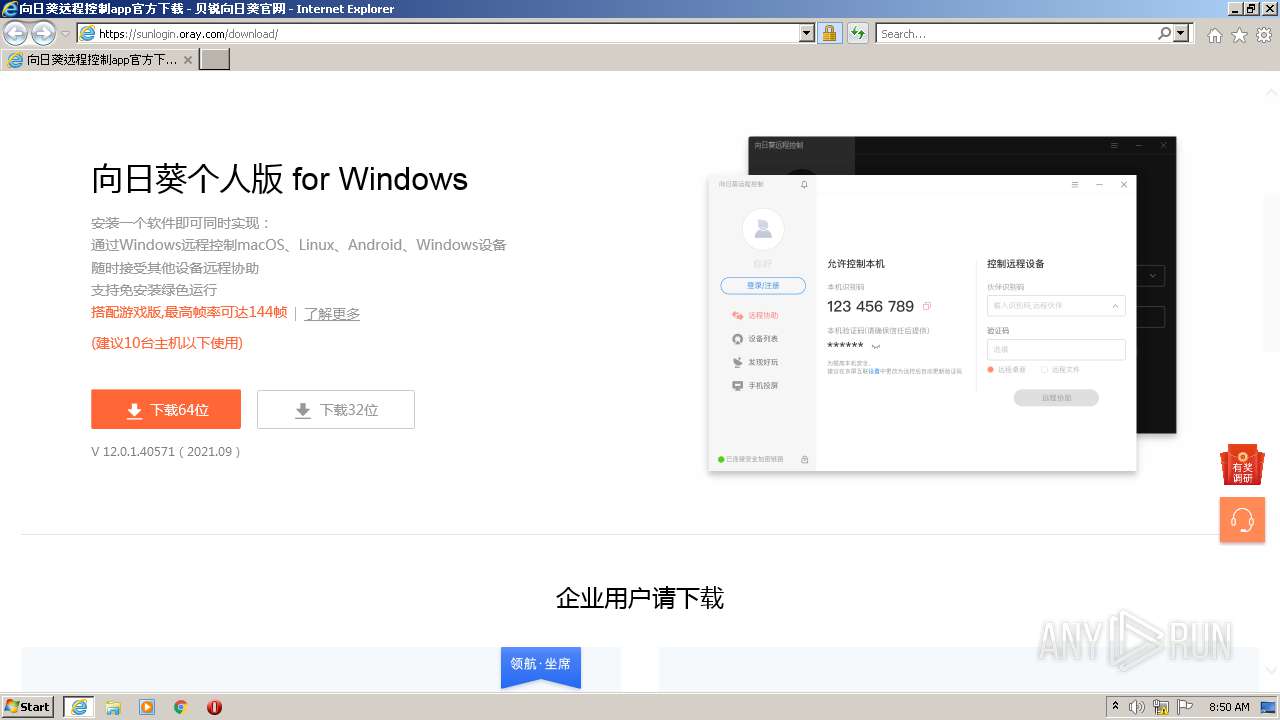
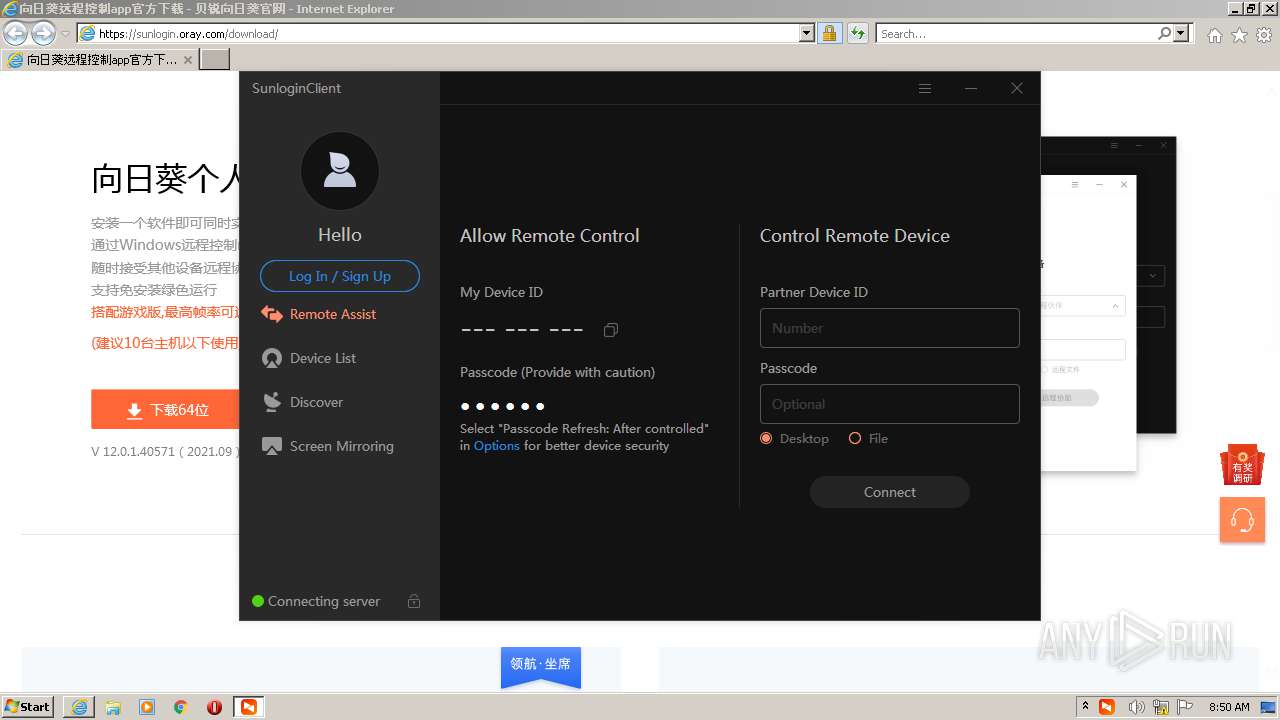
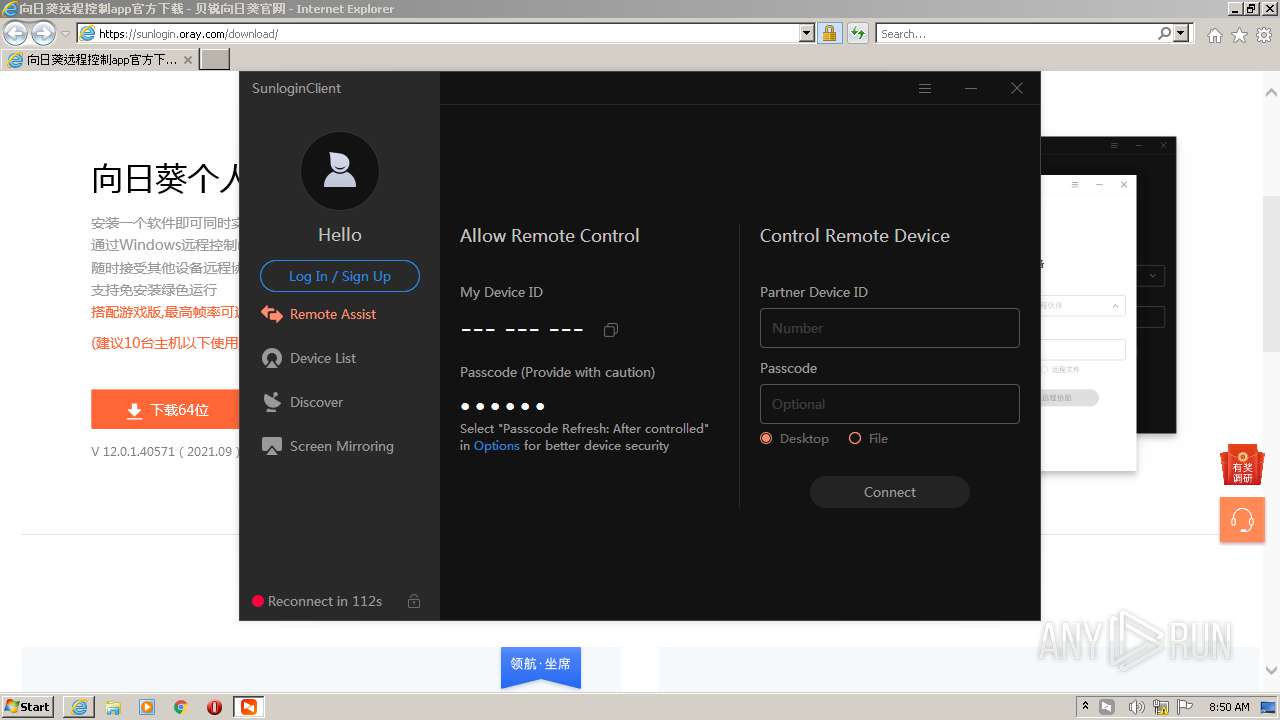
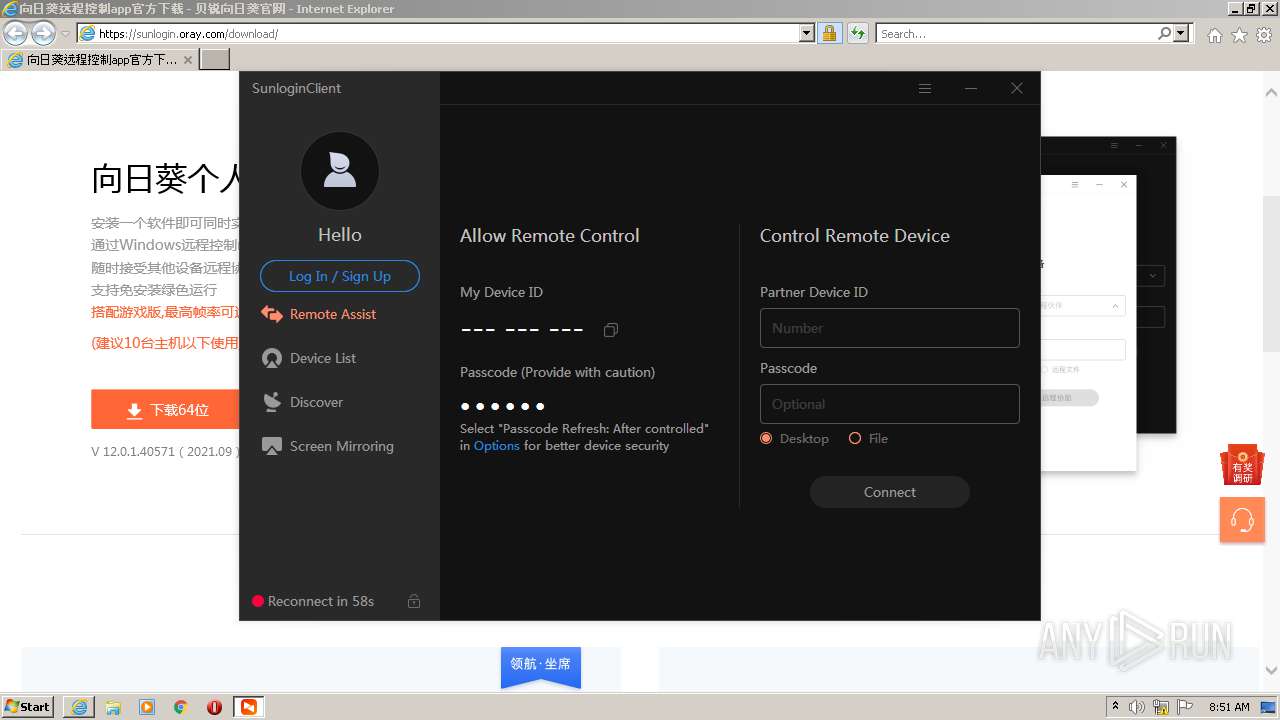
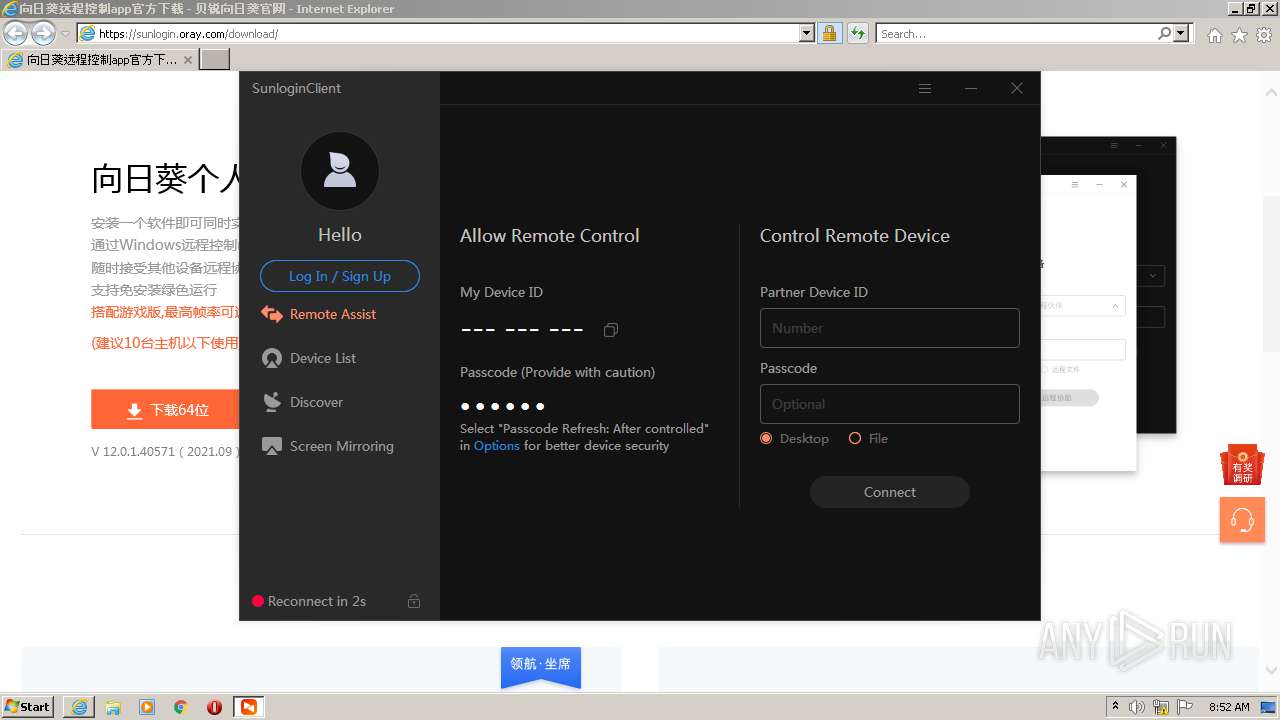
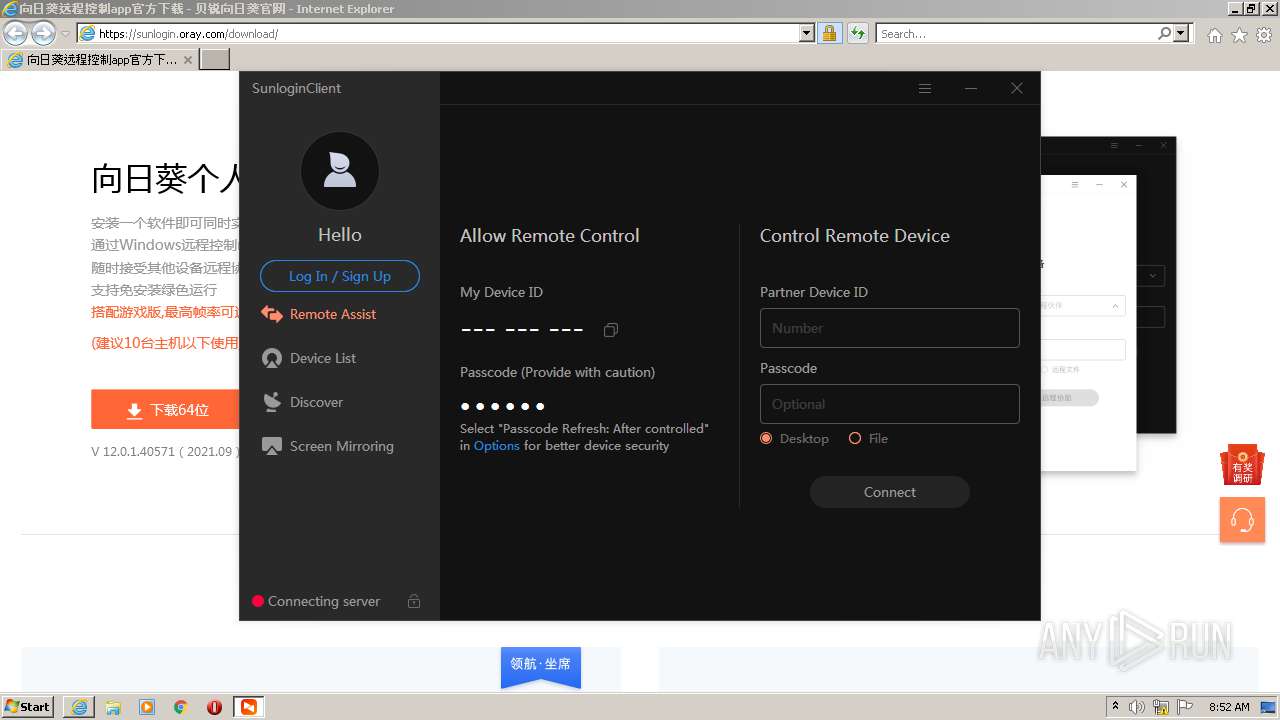
| URL: | https://sunlogin.oray.com/download/ |
| Full analysis: | https://app.any.run/tasks/4ef65d0f-21c1-4353-9625-bd08f3a93b94 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2021, 07:47:25 |
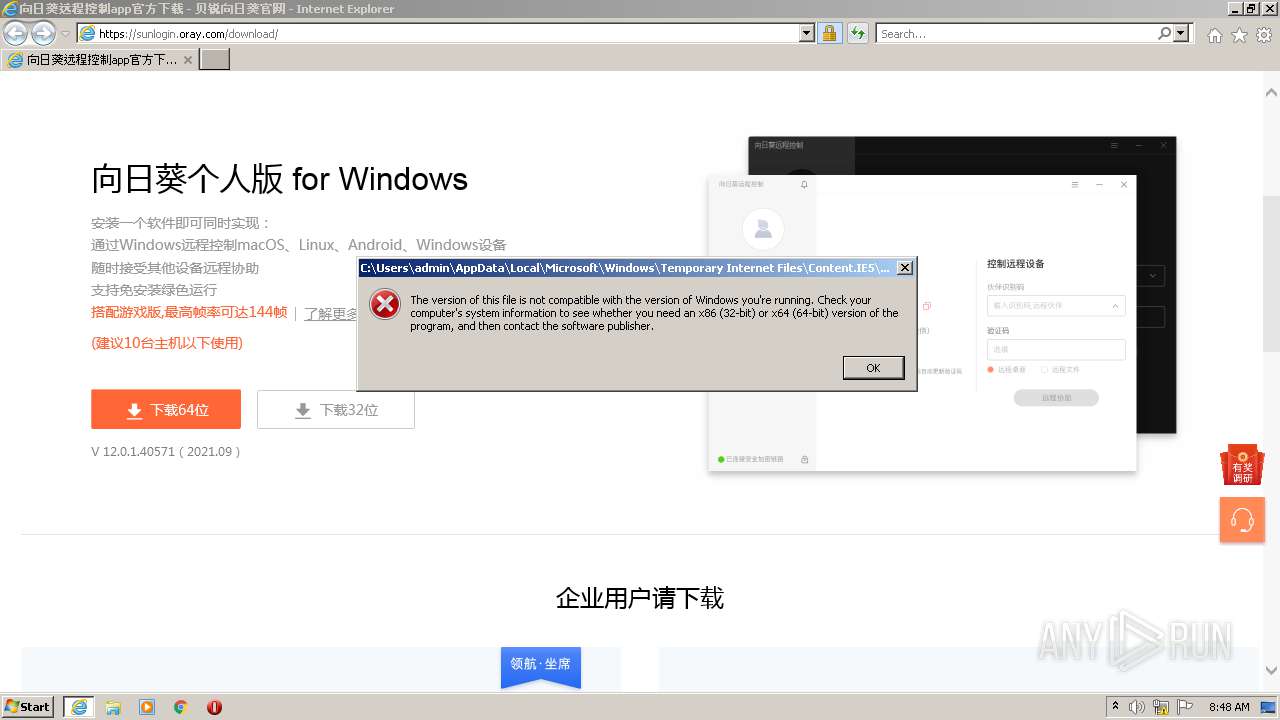
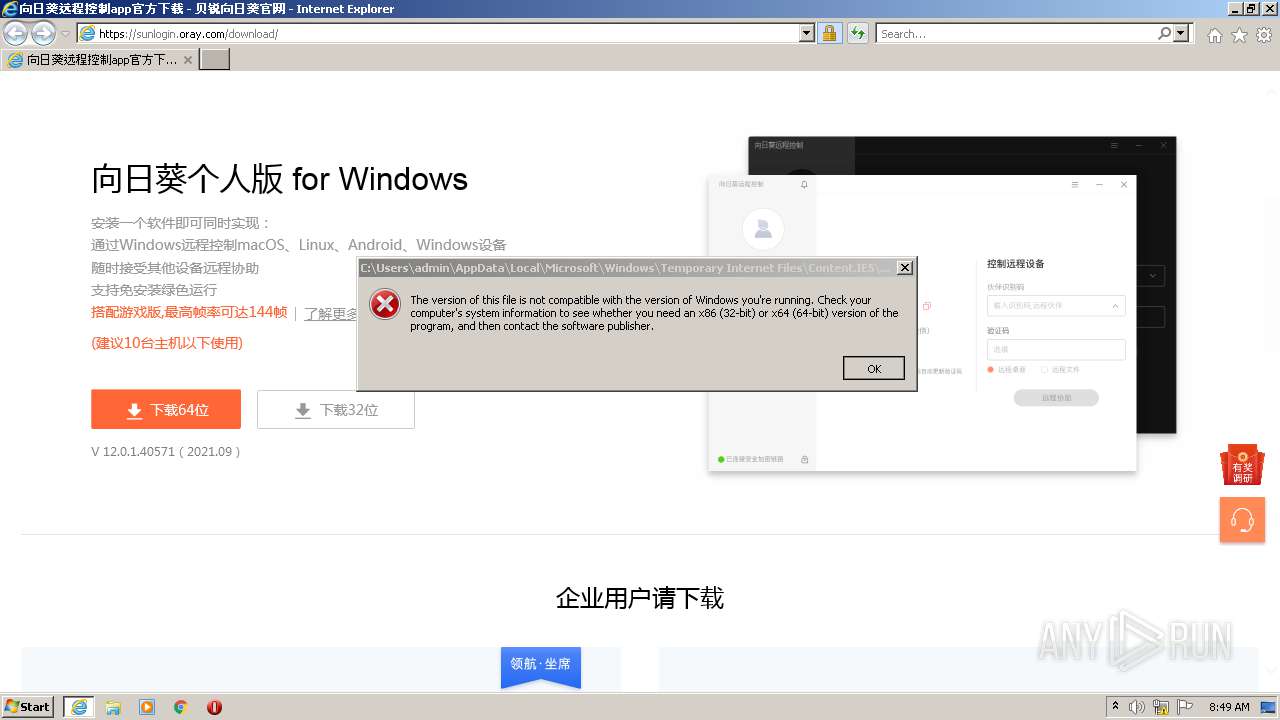
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CDEF57F20EB1273B5580CBACFE398ABD |
| SHA1: | E3F8A902DCC40A82C1355B47C022860E3EE87386 |
| SHA256: | 07F3D21B9162E4D138D21759C9248B8FDD95811C855182540D5F231026C81865 |
| SSDEEP: | 3:N8d9KMEcLGG8Ln:2qmLGNL |
MALICIOUS
Application was dropped or rewritten from another process
- SunloginClient_12.0.1.40571.exe (PID: 1740)
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient.exe (PID: 572)
- devcon.exe (PID: 708)
- SunloginClient.exe (PID: 3236)
- SunloginClient.exe (PID: 3668)
- SunloginClient.exe (PID: 824)
- SunloginClient.exe (PID: 3152)
- SunloginClient.exe (PID: 656)
Changes the autorun value in the registry
- SunloginClient_12.0.1.40571.exe (PID: 2380)
Drops executable file immediately after starts
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3028)
Executable content was dropped or overwritten
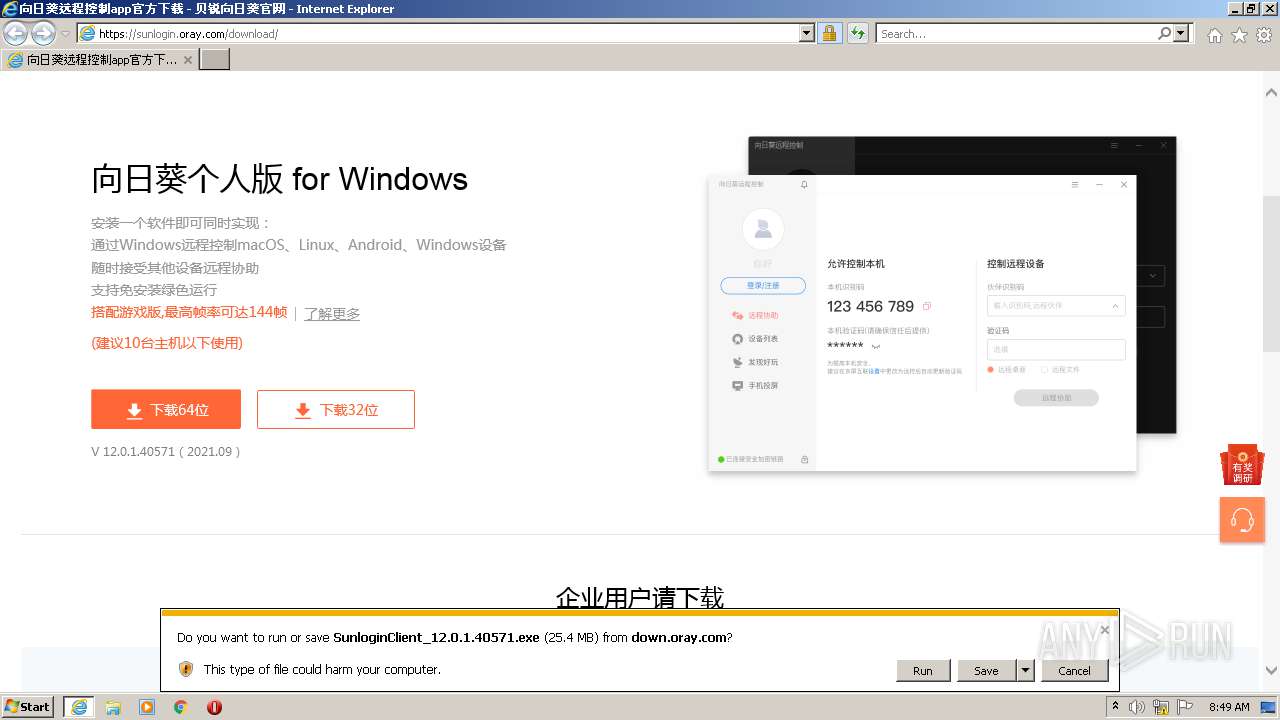
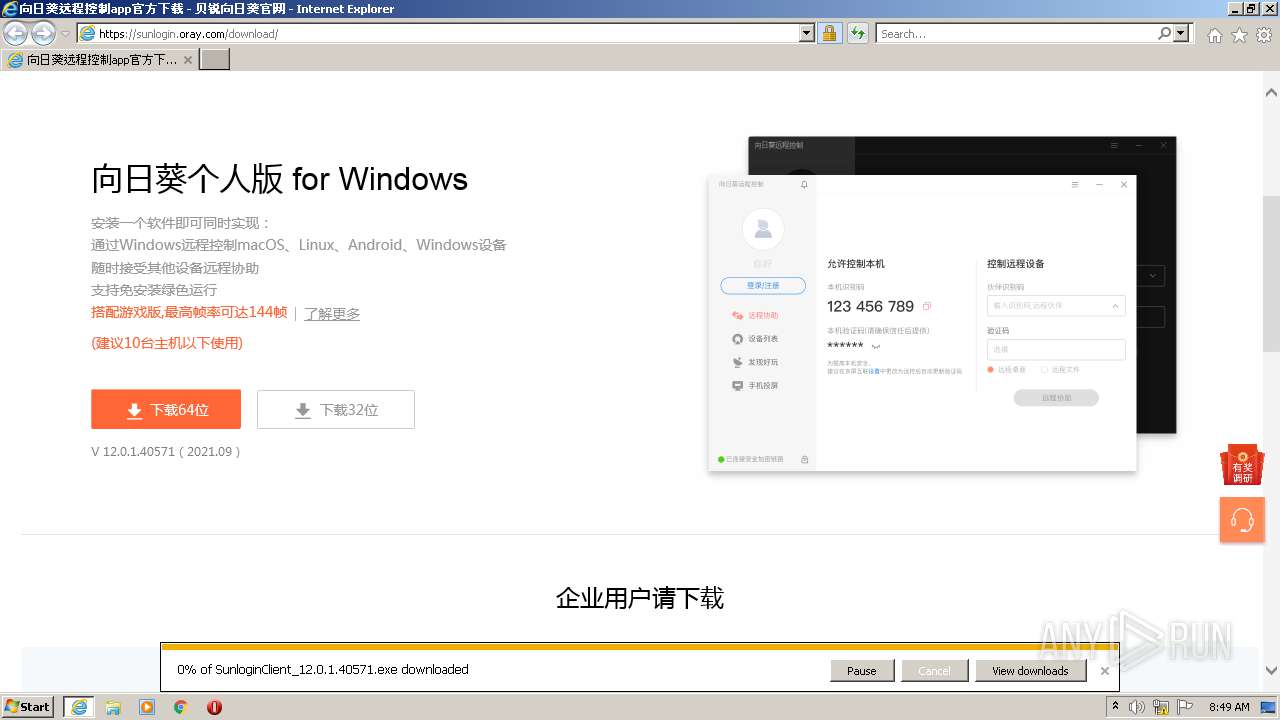
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2392)
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- devcon.exe (PID: 708)
- SunloginClient.exe (PID: 3236)
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2392)
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient.exe (PID: 3236)
Checks supported languages
- SunloginClient_12.0.1.40571.exe (PID: 1740)
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- cmd.exe (PID: 2628)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 3576)
- cmd.exe (PID: 1340)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 580)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 120)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2136)
- SunloginClient.exe (PID: 572)
- devcon.exe (PID: 708)
- SunloginClient.exe (PID: 3236)
- DrvInst.exe (PID: 2836)
- SunloginClient.exe (PID: 3668)
- SunloginClient.exe (PID: 824)
- SunloginClient.exe (PID: 3152)
- DrvInst.exe (PID: 3208)
- SunloginClient.exe (PID: 656)
Cleans NTFS data-stream (Zone Identifier)
- SunloginClient_12.0.1.40571.exe (PID: 1740)
Application launched itself
- SunloginClient_12.0.1.40571.exe (PID: 1740)
- cmd.exe (PID: 2628)
- SunloginClient.exe (PID: 3236)
- SunloginClient.exe (PID: 3152)
Reads the computer name
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient_12.0.1.40571.exe (PID: 1740)
- SunloginClient.exe (PID: 572)
- devcon.exe (PID: 708)
- SunloginClient.exe (PID: 3236)
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
- SunloginClient.exe (PID: 3668)
- SunloginClient.exe (PID: 824)
- SunloginClient.exe (PID: 3152)
- SunloginClient.exe (PID: 656)
Creates a directory in Program Files
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient.exe (PID: 3236)
Starts CMD.EXE for commands execution
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- cmd.exe (PID: 2628)
Drops a file with too old compile date
- SunloginClient_12.0.1.40571.exe (PID: 2380)
Creates files in the program directory
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient.exe (PID: 3236)
- SunloginClient.exe (PID: 3668)
- SunloginClient.exe (PID: 656)
Reads Environment values
- netsh.exe (PID: 2680)
- netsh.exe (PID: 3420)
- netsh.exe (PID: 4000)
- netsh.exe (PID: 3776)
- netsh.exe (PID: 1932)
- netsh.exe (PID: 2324)
- netsh.exe (PID: 1384)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 1892)
- netsh.exe (PID: 4004)
- netsh.exe (PID: 3376)
- netsh.exe (PID: 2636)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 120)
- SunloginClient.exe (PID: 3236)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2836)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 3576)
- cmd.exe (PID: 1340)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 120)
- cmd.exe (PID: 580)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 2744)
Starts itself from another location
- SunloginClient_12.0.1.40571.exe (PID: 2380)
Creates a software uninstall entry
- SunloginClient_12.0.1.40571.exe (PID: 2380)
Creates files in the Windows directory
- devcon.exe (PID: 708)
- DrvInst.exe (PID: 2836)
- SunloginClient.exe (PID: 3236)
- DrvInst.exe (PID: 3208)
Searches for installed software
- SunloginClient_12.0.1.40571.exe (PID: 2380)
- SunloginClient.exe (PID: 3236)
- SunloginClient.exe (PID: 3668)
- SunloginClient.exe (PID: 824)
- SunloginClient.exe (PID: 656)
Executed as Windows Service
- SunloginClient.exe (PID: 3236)
Drops a file that was compiled in debug mode
- devcon.exe (PID: 708)
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
- SunloginClient_12.0.1.40571.exe (PID: 2380)
Executed via COM
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
Removes files from Windows directory
- DrvInst.exe (PID: 2836)
- SunloginClient.exe (PID: 3236)
- DrvInst.exe (PID: 3208)
Creates files in the driver directory
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
Reads CPU info
- SunloginClient.exe (PID: 3236)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2392)
Creates files in the user directory
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2392)
Reads the computer name
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 3028)
- netsh.exe (PID: 2680)
- netsh.exe (PID: 4000)
- netsh.exe (PID: 3776)
- netsh.exe (PID: 1932)
- netsh.exe (PID: 2324)
- netsh.exe (PID: 1384)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 1892)
- netsh.exe (PID: 2636)
- netsh.exe (PID: 4004)
- netsh.exe (PID: 3376)
- netsh.exe (PID: 120)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 3420)
Checks supported languages
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 3028)
- netsh.exe (PID: 2680)
- netsh.exe (PID: 4000)
- netsh.exe (PID: 3420)
- netsh.exe (PID: 3776)
- netsh.exe (PID: 1932)
- netsh.exe (PID: 1384)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 1892)
- netsh.exe (PID: 2324)
- netsh.exe (PID: 4004)
- netsh.exe (PID: 3376)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 120)
- netsh.exe (PID: 2636)
Application launched itself
- iexplore.exe (PID: 2392)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2392)
Checks Windows Trust Settings
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2392)
- devcon.exe (PID: 708)
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
Changes settings of System certificates
- iexplore.exe (PID: 2392)
Reads settings of System Certificates
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2392)
- devcon.exe (PID: 708)
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3208)
Reads internet explorer settings
- iexplore.exe (PID: 3028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
43
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 120 | netsh advfirewall firewall add rule name="SunloginDesktopAgent" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\agent\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" --mod=install --cmd=driver_mirror | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe | SunloginClient_12.0.1.40571.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: HIGH Description: SunloginClient Exit code: 0 Version: 12.0.1.40571 Modules
| |||||||||||||||
| 580 | cmd /c netsh advfirewall firewall delete rule name="SunloginDesktopAgent" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 656 | "C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" --admin=1 | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe | SunloginClient.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: MEDIUM Description: SunloginClient Exit code: 0 Version: 12.0.1.40571 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Oray\SunLogin\SunloginClient\Driver\Mirror\devcon.exe" reinstall "C:\Program Files\Oray\SunLogin\SunloginClient\Driver\Mirror\OrayMir.inf" C50B00D7-AE62-4936-8BC8-20E0B9F0BEFB | C:\Program Files\Oray\SunLogin\SunloginClient\Driver\Mirror\devcon.exe | SunloginClient.exe | ||||||||||||
User: admin Company: Windows (R) Server 2003 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 5.2.3790.1830 built by: WinDDK Modules
| |||||||||||||||
| 824 | "C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" --mod=update --cmd=check | C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe | SunloginClient.exe | ||||||||||||
User: SYSTEM Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: SYSTEM Description: SunloginClient Exit code: 0 Version: 12.0.1.40571 Modules
| |||||||||||||||
| 1340 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=tcp enable=yes profile=domain | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1384 | netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\SunloginClient_12.0.1.40571.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\SunloginClient_12.0.1.40571.exe | — | iexplore.exe | |||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: MEDIUM Description: SunloginClient Exit code: 1 Version: 12.0.1.40571 Modules
| |||||||||||||||
Total events
34 072
Read events
33 109
Write events
959
Delete events
4
Modification events
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30913999 | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30913999 | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
44
Suspicious files
38
Text files
239
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:B555047FAF3A74C8F1BE66A02CD6B7FC | SHA256:31F959F9423D017DC692F8AD21D7FCF52FF973FEEB37F2444F3D72ED87209301 | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:66B8A421C419F87BB66FE602A2D88936 | SHA256:3D46B7D476177784865DD90E3F16694728CD781062076A3301B3AD3C7D7E6492 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | binary | |
MD5:066F1C317E4DD1E45B9544A9AD633D2B | SHA256:EBBEC78553D558E225F16688C461237FA084EED12F42260E2BEF9AE0F1797B87 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\773CFF2C7835D48C4E76FE153DBA9F81_40A8C54141774970FA2A3B2AC3918CCD | der | |
MD5:45745DF4CBF7083771F1E0DD685F826D | SHA256:FB1EBE2950C8DD0A74EF96E1E55F8E19FD7437FFDB292FED3AC0149C262ACEBF | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\773CFF2C7835D48C4E76FE153DBA9F81_DE868A117854FB5E13D53239776C372A | der | |
MD5:83877B481DD2899B7E56616C40380D18 | SHA256:9B96628761BA020A5D940F8D1FBD4A997A2FB38A3C358F5020071FBB05B0DF88 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\2113cf87ff2345b92864[1].css | text | |
MD5:4456043D61B29CEBFFC0B8F9A62DD9C4 | SHA256:AB549AED1A8A5506311246C1CFD00E8E66A090220FA58A9AB7E319B9721EAB08 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\773CFF2C7835D48C4E76FE153DBA9F81_DE868A117854FB5E13D53239776C372A | binary | |
MD5:C20AEA53F3D32FE2E5D353EAA543F3DE | SHA256:FCADDB767559A4F897B4C4B1837680817BB8EE35E567E569416FD353D4764F9C | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:92127EE7BB5472DBA28CAE8B531AB66C | SHA256:DA2A7A8541D3A3A0E6F41D44E16E3A6A585911627814171D43A5A95B6A306DC6 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download[1].htm | html | |
MD5:DD5AFD1E58C47626B29FF838B9730BCA | SHA256:DF8FC25489915334D6045626DAF96BB70F82E8471BABBF1BF9824E84BE5C1F1D | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | der | |
MD5:50557D44A0AEAB4950CA7F35FBF65B43 | SHA256:688F9E4BE2F5DCFBBDFA56D2C2F6339711785505A20E49EDFE8DD4CE22F0652F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
120
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7683192c9e028993 | US | compressed | 4.70 Kb | whitelisted |
3028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJiUKgT2m88fZ4nxc1Lu6M%2FjvkagQUDNtsgkkPSmcKuBTuesRIUojrVjgCEAsjf0QkQYAdL0CSeiItMII%3D | US | der | 471 b | shared |
3028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAsllCLO2YEqFaBOmVKKDvo%3D | US | der | 471 b | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6fb0e3af794058cb | US | compressed | 4.70 Kb | whitelisted |
3028 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDDPT5nWSERQN6vQXtA%3D%3D | US | der | 1.41 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2392 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1bd11a383a14b435 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | iexplore.exe | 47.110.217.173:443 | sunlogin.oray.com | — | CN | unknown |
2392 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2392 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2392 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3028 | iexplore.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
3028 | iexplore.exe | 110.242.68.204:443 | fxgate.baidu.com | CHINA UNICOM China169 Backbone | CN | unknown |
3028 | iexplore.exe | 79.133.177.225:443 | res.orayimg.com | SOT LINE Limited Company | RU | malicious |
3028 | iexplore.exe | 47.246.43.227:443 | res.orayimg.com | — | US | malicious |
3028 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3028 | iexplore.exe | 120.55.52.22:443 | sentry.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sunlogin.oray.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |
res.orayimg.com |
| malicious |
static.orayimg.com |
| malicious |
cdn.orayimg.com |
| malicious |
hm.baidu.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SunloginClient_12.0.1.40571.exe | [2104] 2021-09-30 08:49:40.924 - Info - [dpi] SetDPIAwareness isn't support.
|
SunloginClient_12.0.1.40571.exe | [2104] 2021-09-30 08:49:40.929 = Debug = [select_tracker] run ok
|
SunloginClient_12.0.1.40571.exe | [2104] 2021-09-30 08:49:40.999 = Debug = [select_tracker] run ok
|
SunloginClient_12.0.1.40571.exe | [3856] 2021-09-30 08:49:40.999 = Debug = [thread] set thread name Thread-3856 0458e1e0 / 3856
|
SunloginClient_12.0.1.40571.exe | [3856] 2021-09-30 08:49:41.000 * Error * [SensorsDatas::init_sensors_thread] [sensors] distinct_id is empty create now!
|
SunloginClient_12.0.1.40571.exe | [3856] 2021-09-30 08:49:41.001 - Info - [SensorsDatas::init_sensors_thread] [sensors] init with file: C:/ProgramData/OrayClient/sensors/datas
|
SunloginClient_12.0.1.40571.exe | [2104] 2021-09-30 08:49:41.014 * Error * [CSSLStream] Remove temp(C:\Users\admin\AppData\Local\Temp\u1u4.0) file ok
|
SunloginClient_12.0.1.40571.exe | [2104] 2021-09-30 08:49:41.015 = Debug = [select_tracker] run ok
|
SunloginClient_12.0.1.40571.exe | [3920] 2021-09-30 08:49:41.015 = Debug = [thread] set thread name Thread-3920 0458e0e0 / 3920
|
SunloginClient_12.0.1.40571.exe | [3856] 2021-09-30 08:49:43.782 - Info - [http::call3][1] new call:https://sl-tk.oray.com/track
|