| File name: | cpuz_x64.exe |
| Full analysis: | https://app.any.run/tasks/0210ae8c-1354-4f1e-b493-e6d603372e32 |
| Verdict: | Malicious activity |
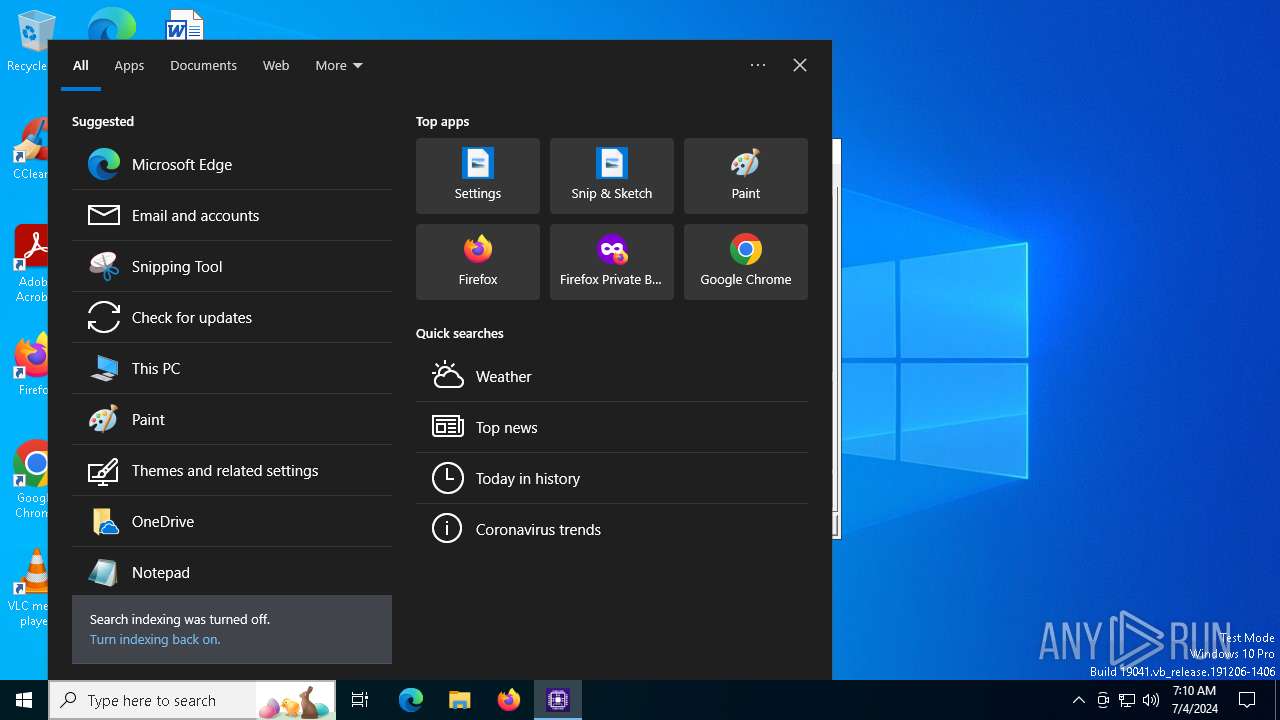
| Analysis date: | July 04, 2024, 07:09:45 |
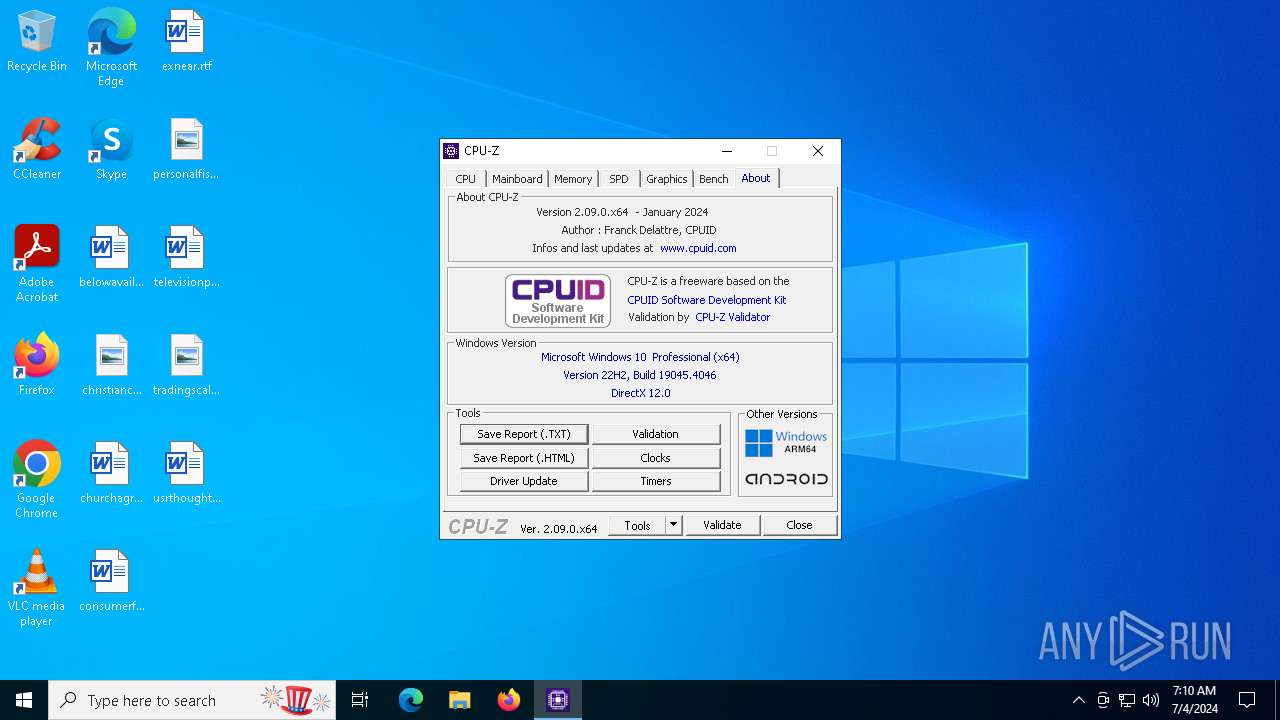
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 28D0F05B4AA1C04D1D20687287696876 |
| SHA1: | B0C3CCFDCA6A2BE57386A39FBE0627C03BF2FEF1 |
| SHA256: | 07EE15632C25D9519F0E045A091F67C79E432EE01F07F2C0064D0B739840CFC8 |
| SSDEEP: | 98304:0w9QWPSJQI5Ommi5XpmgJlVT904xgFx0ZaWWR1qH:0nDB904g0ZF |
MALICIOUS
Drops the executable file immediately after the start
- cpuz_x64.exe (PID: 6332)
SUSPICIOUS
Executable content was dropped or overwritten
- cpuz_x64.exe (PID: 6332)
Reads security settings of Internet Explorer
- cpuz_x64.exe (PID: 6332)
Drops a system driver (possible attempt to evade defenses)
- cpuz_x64.exe (PID: 6332)
Checks Windows Trust Settings
- cpuz_x64.exe (PID: 6332)
There is functionality for VM detection (VirtualBox)
- cpuz_x64.exe (PID: 6332)
INFO
Checks supported languages
- cpuz_x64.exe (PID: 6332)
Reads the computer name
- cpuz_x64.exe (PID: 6332)
Checks proxy server information
- cpuz_x64.exe (PID: 6332)
Reads the machine GUID from the registry
- cpuz_x64.exe (PID: 6332)
Reads the software policy settings
- cpuz_x64.exe (PID: 6332)
Reads Environment values
- cpuz_x64.exe (PID: 6332)
Creates files or folders in the user directory
- cpuz_x64.exe (PID: 6332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
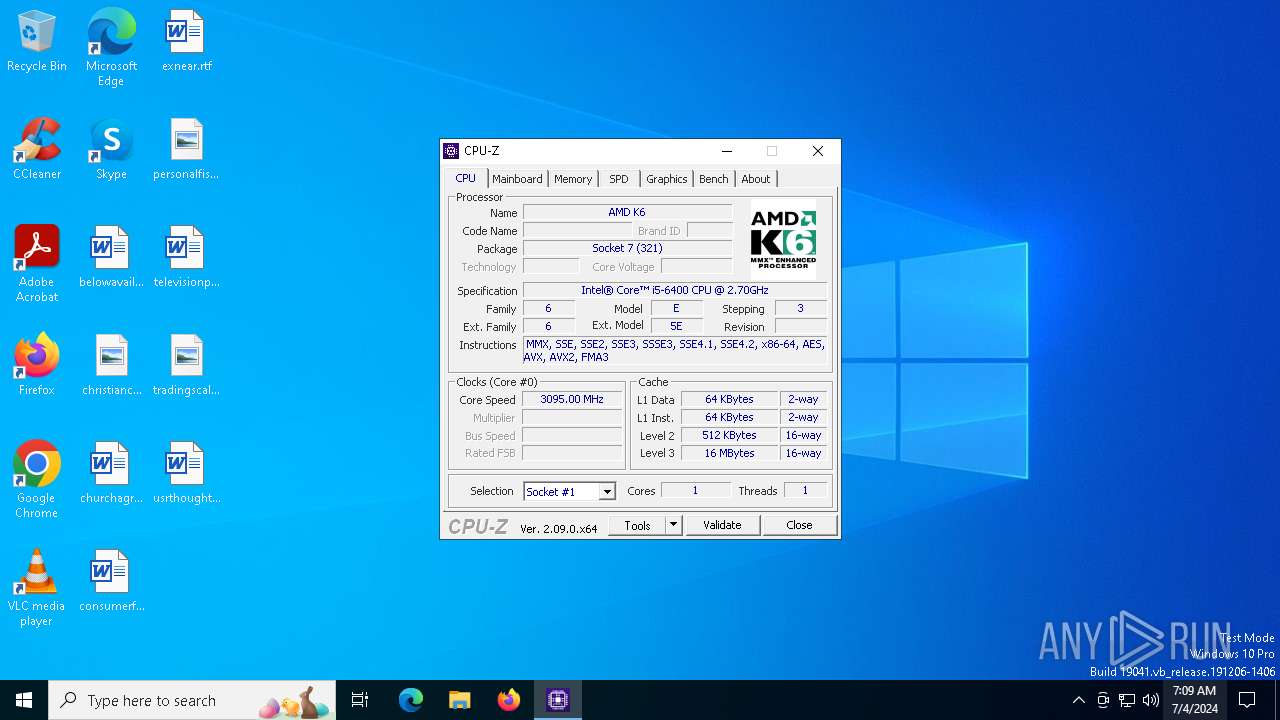
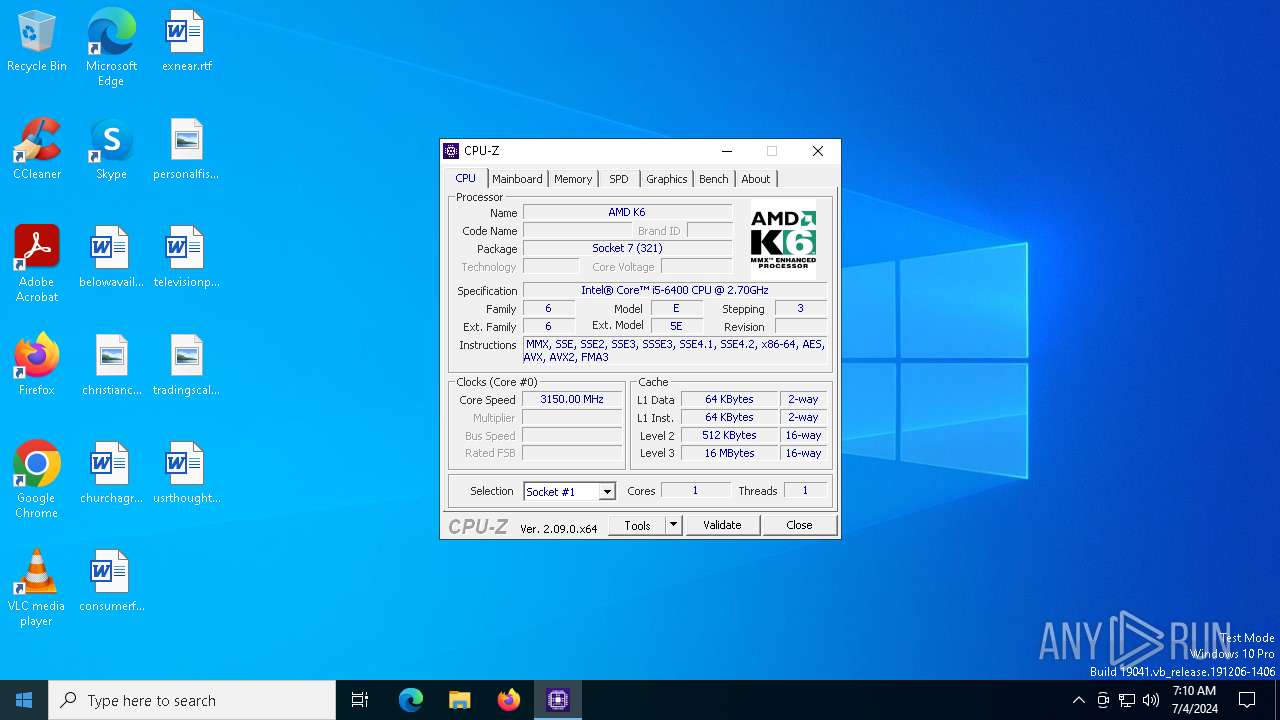
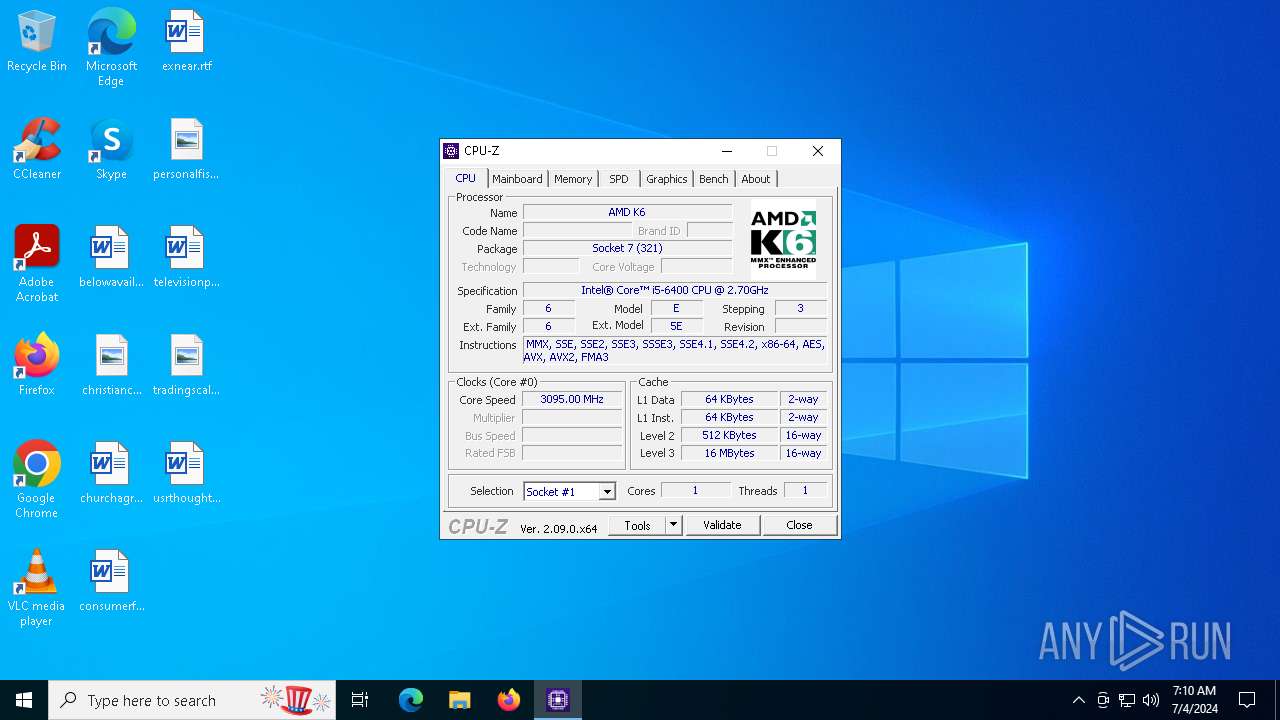
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:01:22 15:26:12+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 9 |
| CodeSize: | 1871360 |
| InitializedDataSize: | 2951680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x156fa4 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.9.0 |
| ProductVersionNumber: | 2.0.9.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | CPUID |
| FileDescription: | CPU-Z Application |
| FileVersion: | 2, 0, 9, 0 |
| InternalName: | cpuz.exe |
| LegalCopyright: | Copyright (C) 2004-2024 |
| OriginalFileName: | cpuz.exe |
| ProductName: | CPU-Z Application |
| ProductVersion: | 2, 0, 9, 0 |
Total processes
136
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6284 | "C:\Users\admin\AppData\Local\Temp\cpuz_x64.exe" | C:\Users\admin\AppData\Local\Temp\cpuz_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 2, 0, 9, 0 Modules
| |||||||||||||||
| 6332 | "C:\Users\admin\AppData\Local\Temp\cpuz_x64.exe" | C:\Users\admin\AppData\Local\Temp\cpuz_x64.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Version: 2, 0, 9, 0 Modules
| |||||||||||||||
Total events
1 134
Read events
1 123
Write events
11
Delete events
0
Modification events
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6332) cpuz_x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | cpuz_x64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\cpuid[1].ver | text | |
MD5:43D52D86AEE86D1B018044B93345E312 | SHA256:AAD2420F5099E69DE15F51B7A1285356093273ADE6C5751B476E869B9F863825 | |||
| 6332 | cpuz_x64.exe | C:\WINDOWS\temp\cpuz_driver_6332.log | text | |
MD5:F984605BE6B69FF678CAAE40B1FE0E0A | SHA256:55F8D9530CB14690868D406B3078DE8625E22FF8F225CEFBD237B080B35AAB31 | |||
| 6332 | cpuz_x64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E3214E7AFC18DAD34C3995A792B3DEEF | der | |
MD5:A691F27D5FA9A71D43ABAE8188D853A7 | SHA256:993B20882CC6A28ED4C150531A379A43D65FFDA9873DA120E815E6A3A4E3F946 | |||
| 6332 | cpuz_x64.exe | C:\WINDOWS\temp\cpuz158\cpuz158_x64.sys | executable | |
MD5:2A5A72F76452C1DF305B868457324C9E | SHA256:B14C360AF8730CDE304650E925824190EB2D5147A2620F325A3BB5BBCEE2ED14 | |||
| 6332 | cpuz_x64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 6332 | cpuz_x64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E3214E7AFC18DAD34C3995A792B3DEEF | binary | |
MD5:CCC02790B81C499DC036C53128754E3A | SHA256:373AF31BC16BE1768F201451CCC876D92CEA68735FA4B515CBA8D2F92BD6F14D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
66
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6332 | cpuz_x64.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSqvAx8TddPgtxsmyqvWexsTg%3D%3D | unknown | — | — | unknown |
1972 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1972 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
3996 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
1768 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3032 | svchost.exe | GET | 304 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
1768 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1972 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2128 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2204 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6332 | cpuz_x64.exe | 195.154.81.43:443 | download.cpuid.com | Online S.a.s. | FR | unknown |
6332 | cpuz_x64.exe | 184.24.77.48:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
1972 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1972 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1972 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cpuid.com |
| whitelisted |
r3.o.lencr.org |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1768 | SIHClient.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED SYNACK resend with different ACK |
1768 | SIHClient.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED SYNACK resend with different ACK |
1768 | SIHClient.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED SYNACK resend with different ACK |
1768 | SIHClient.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED SYNACK resend with different ACK |