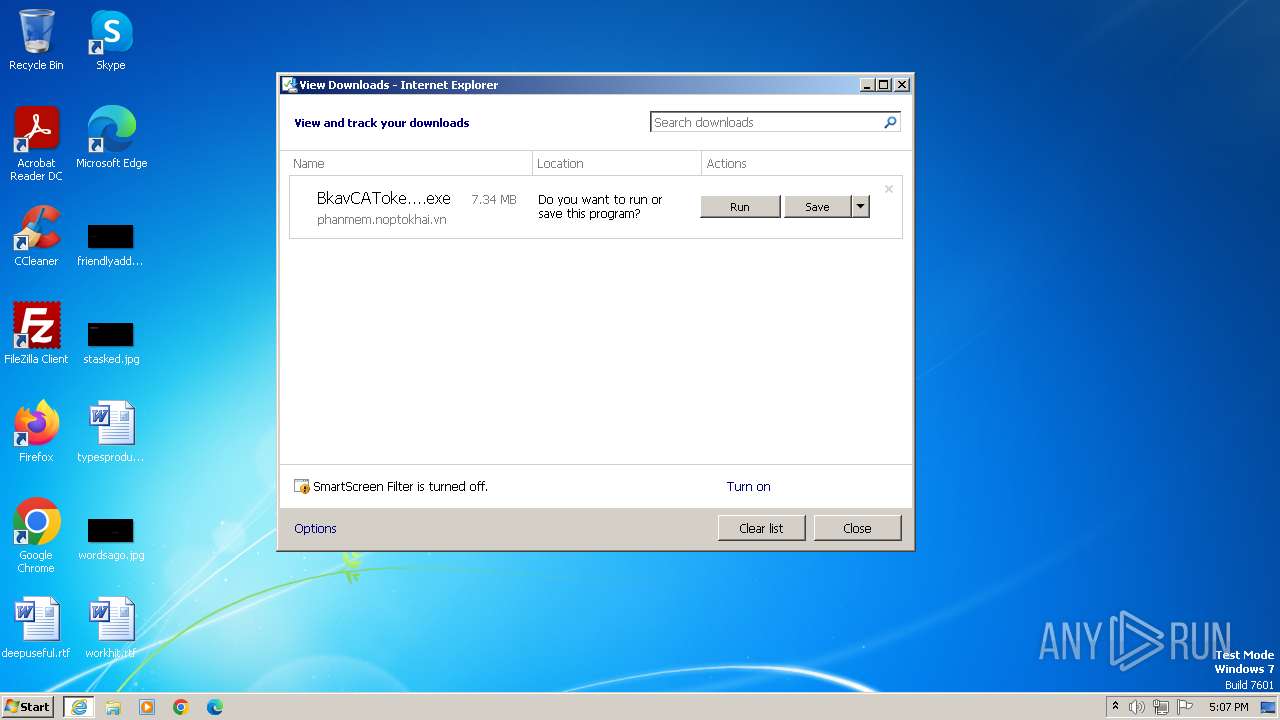
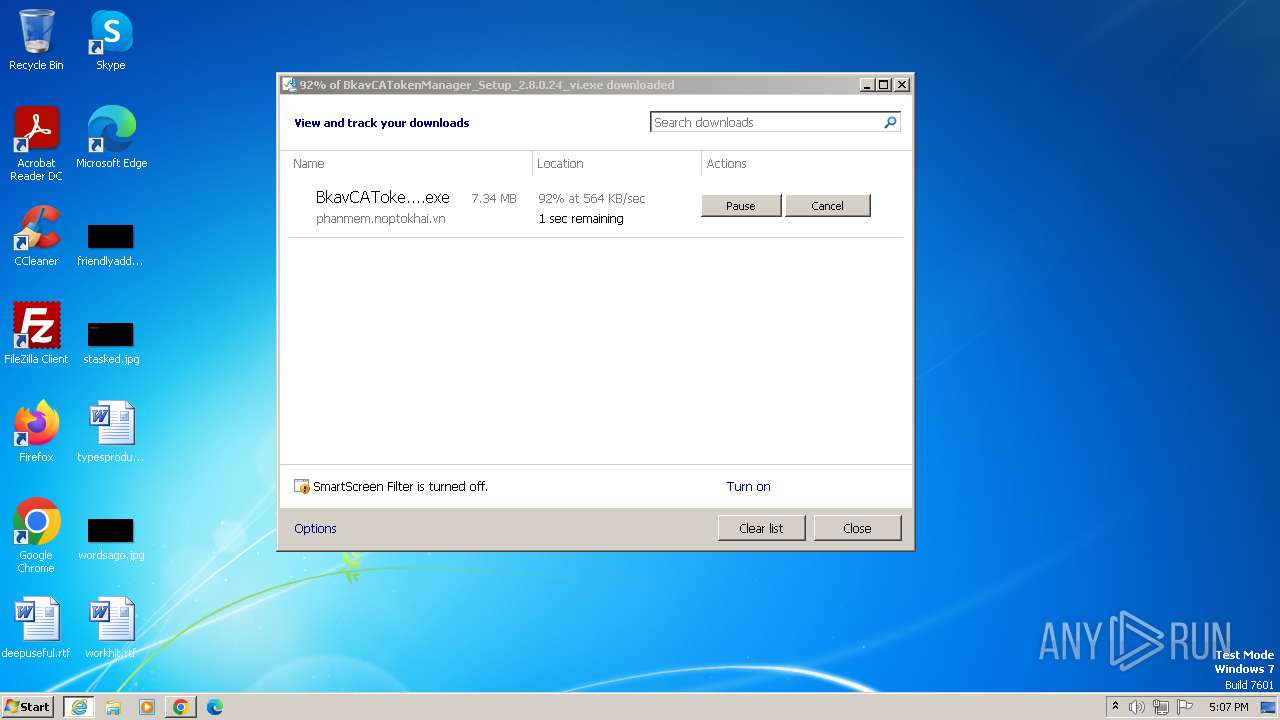
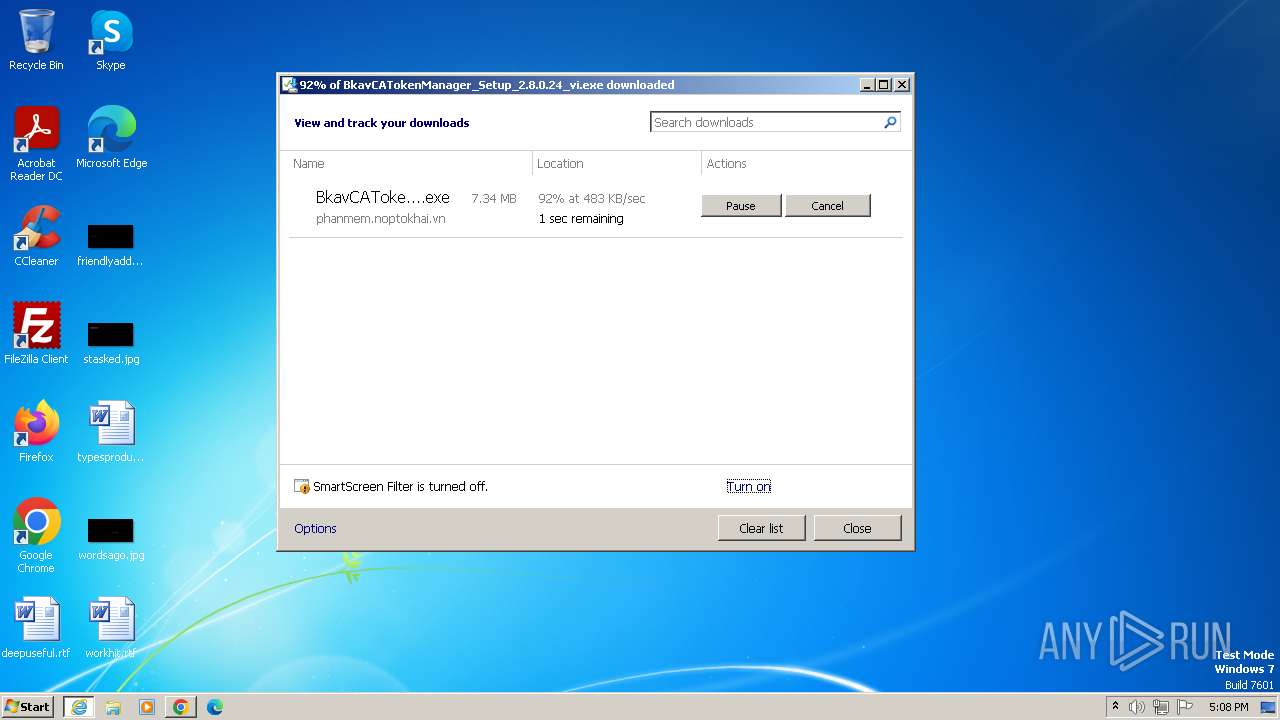
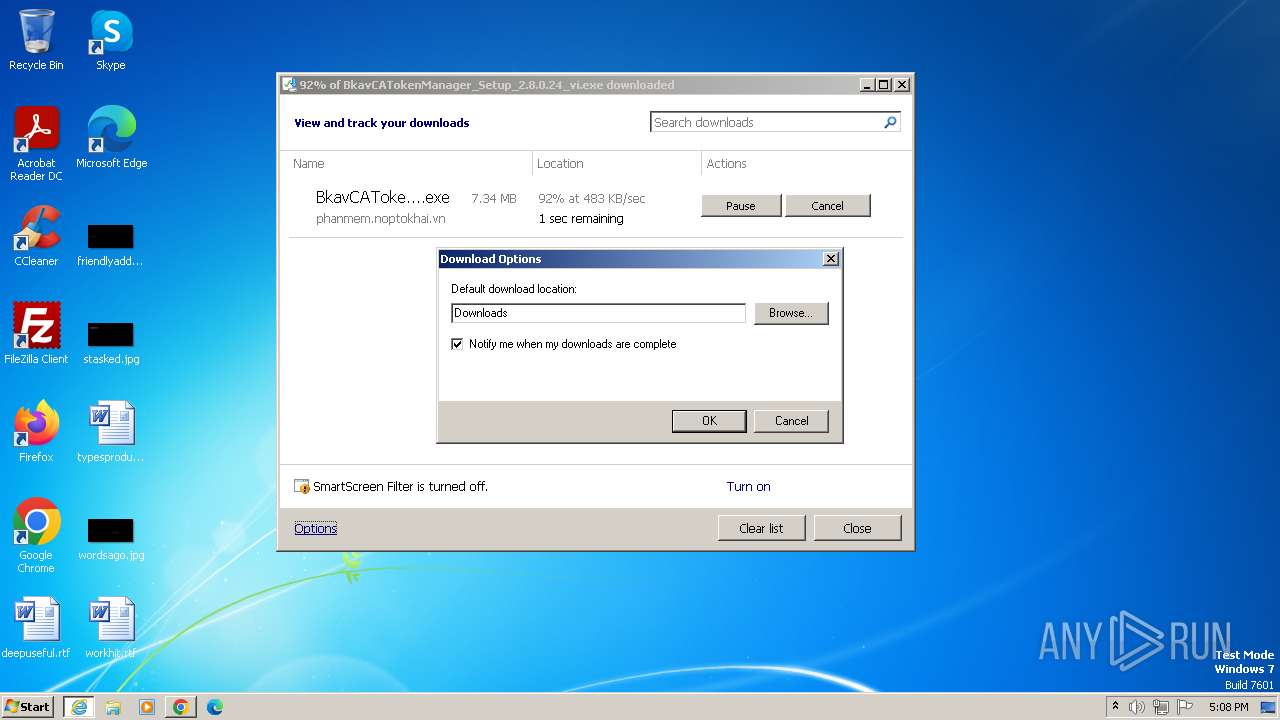
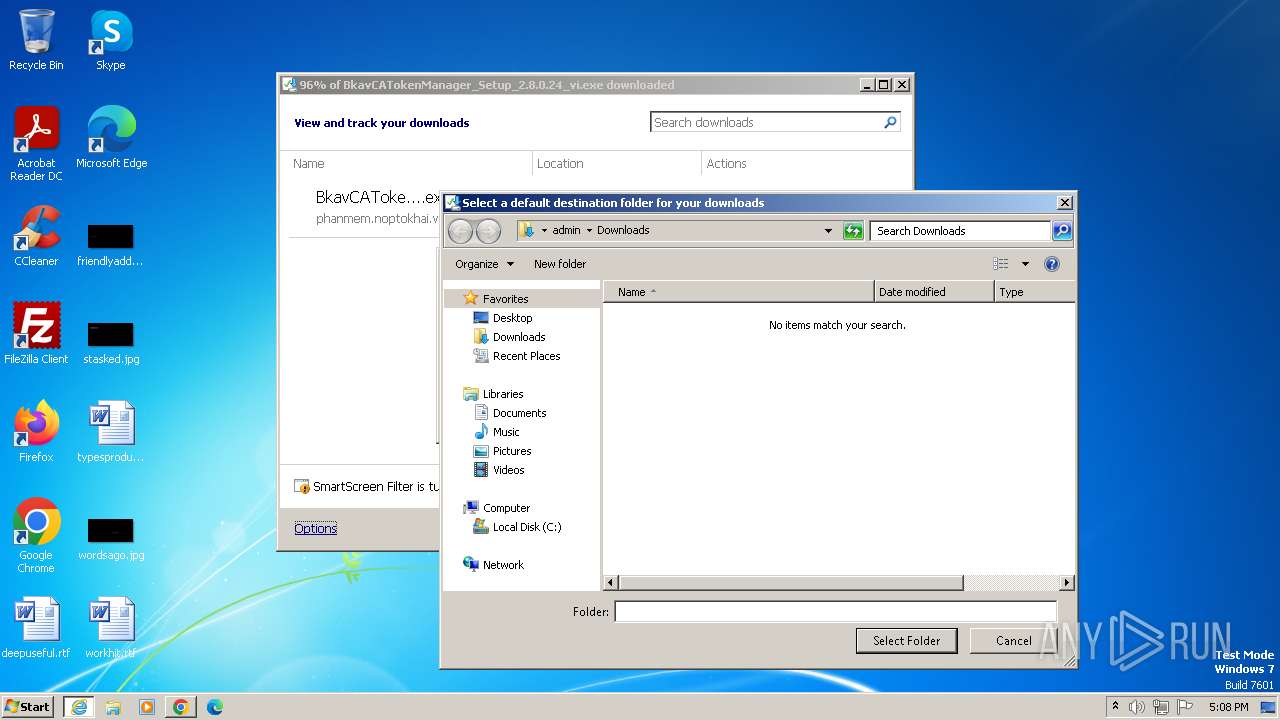
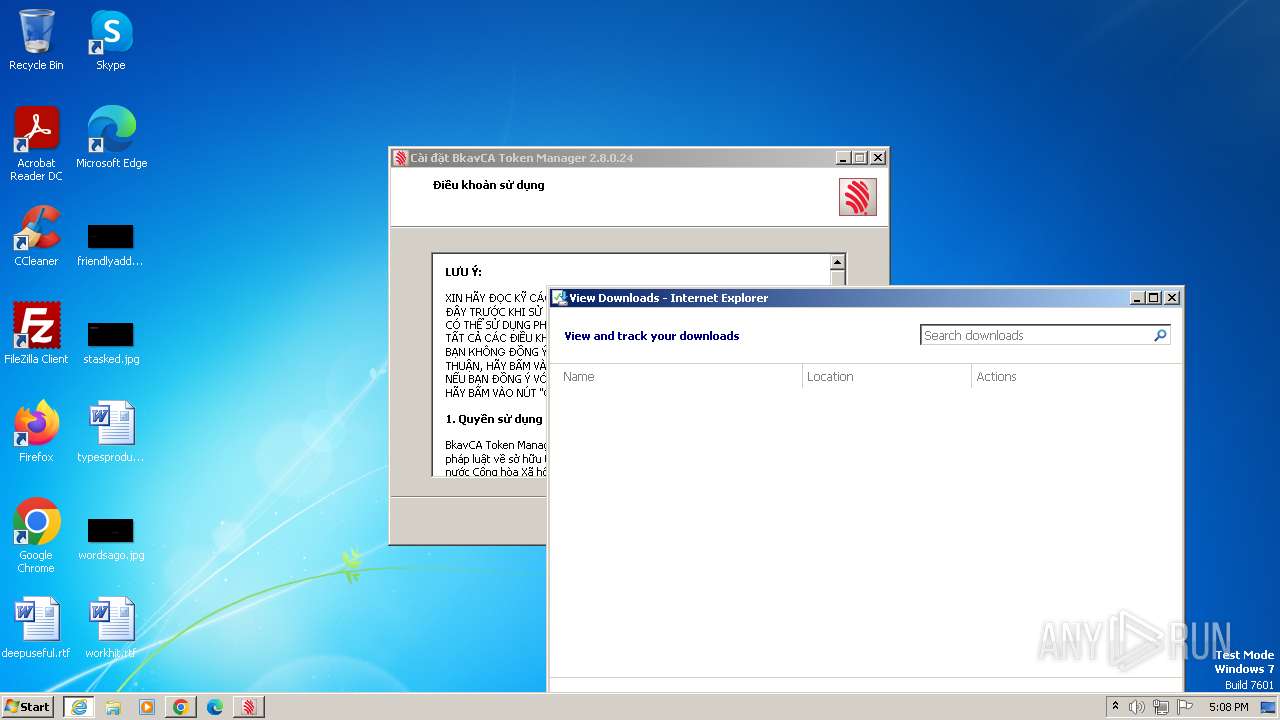
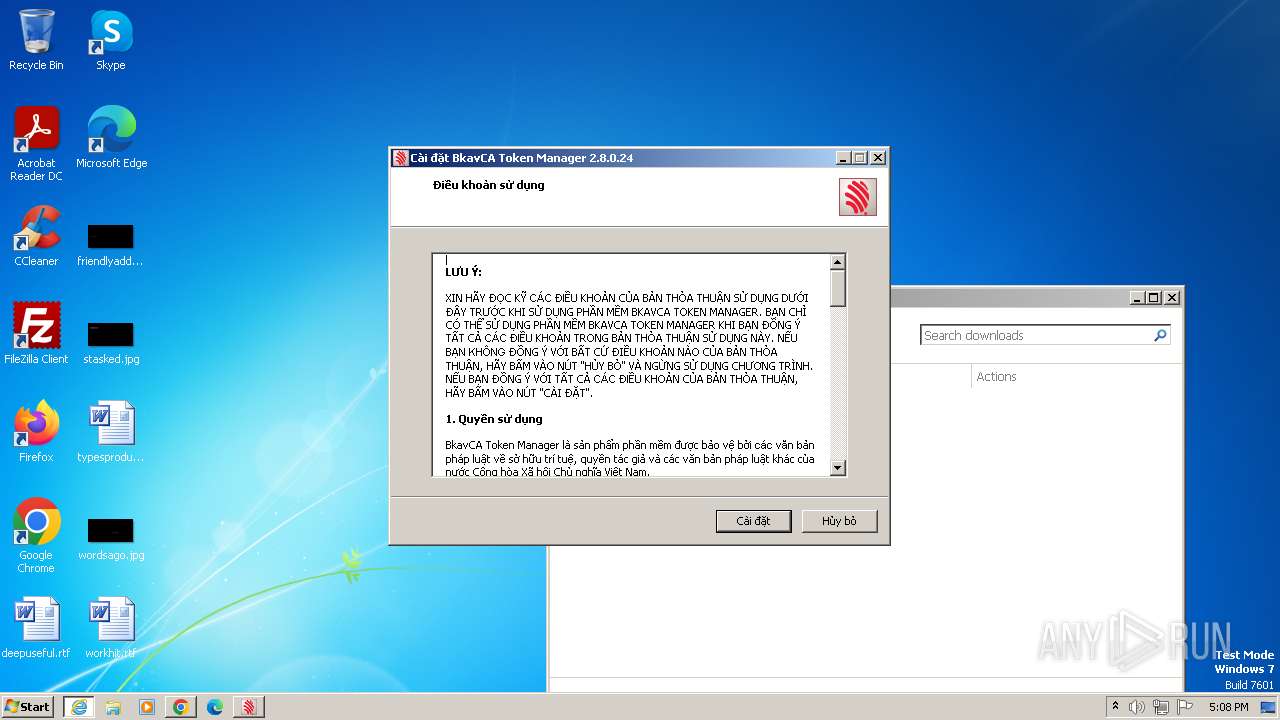
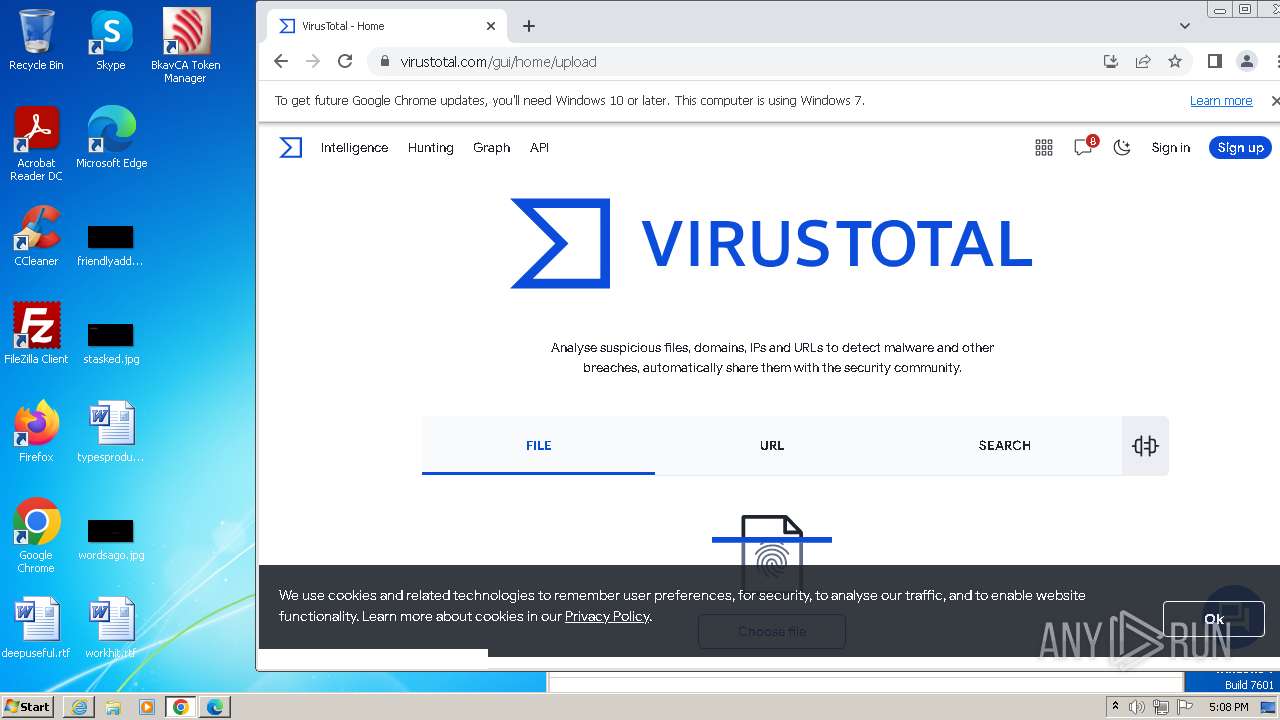
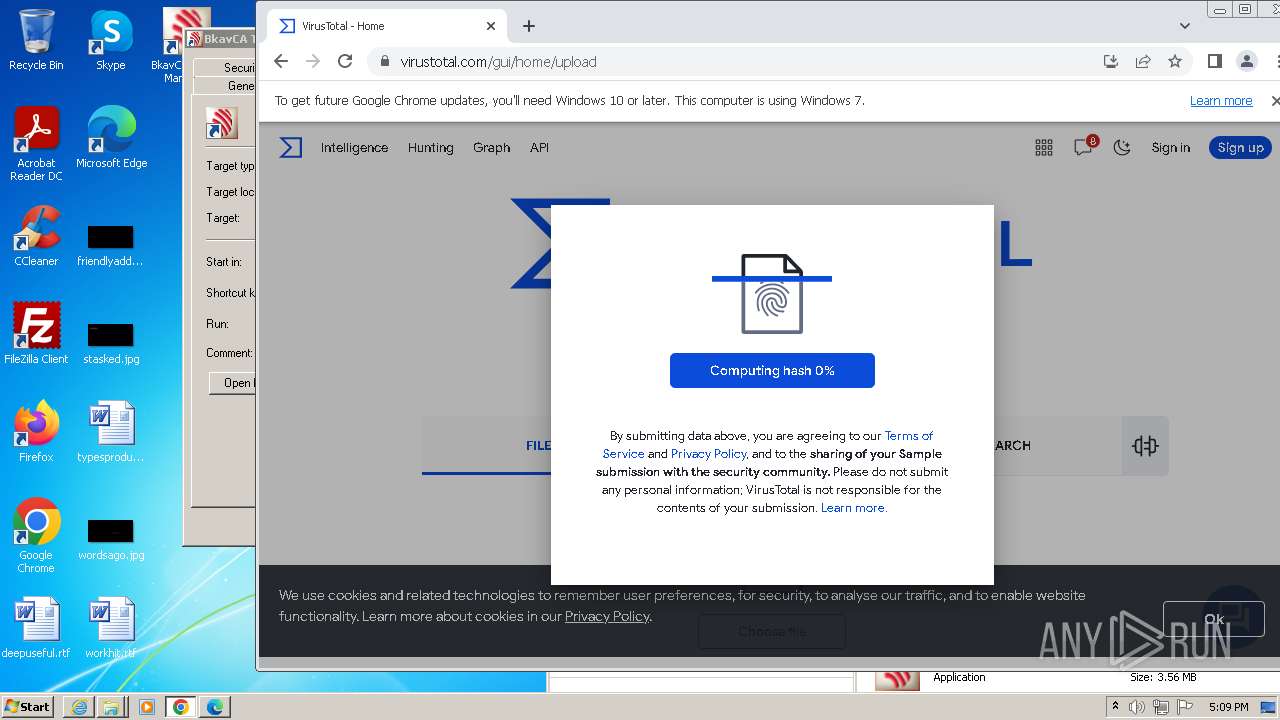
| URL: | phanmem.noptokhai.vn/BkavCATokenManager_Setup_2.8.0.24_vi.exe |
| Full analysis: | https://app.any.run/tasks/2ca13dff-5bd6-4f85-bc03-bc5ec7b6e0ff |
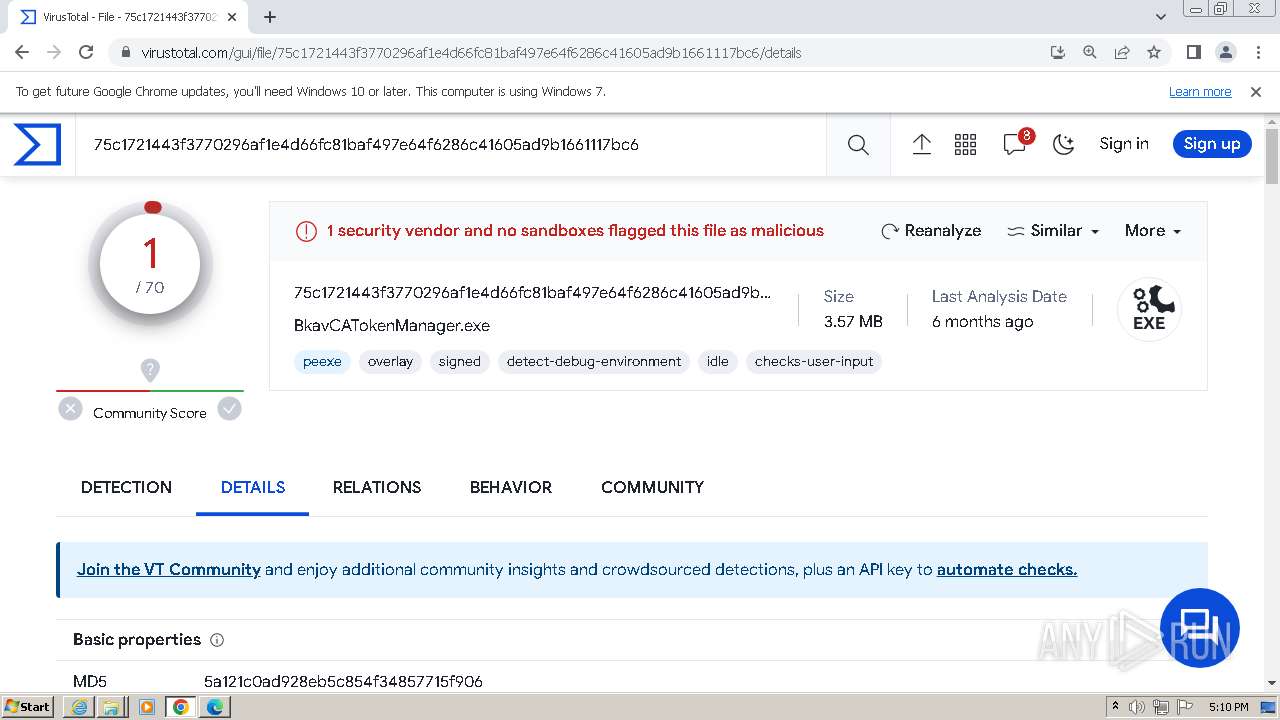
| Verdict: | Malicious activity |
| Analysis date: | November 01, 2023, 17:07:25 |
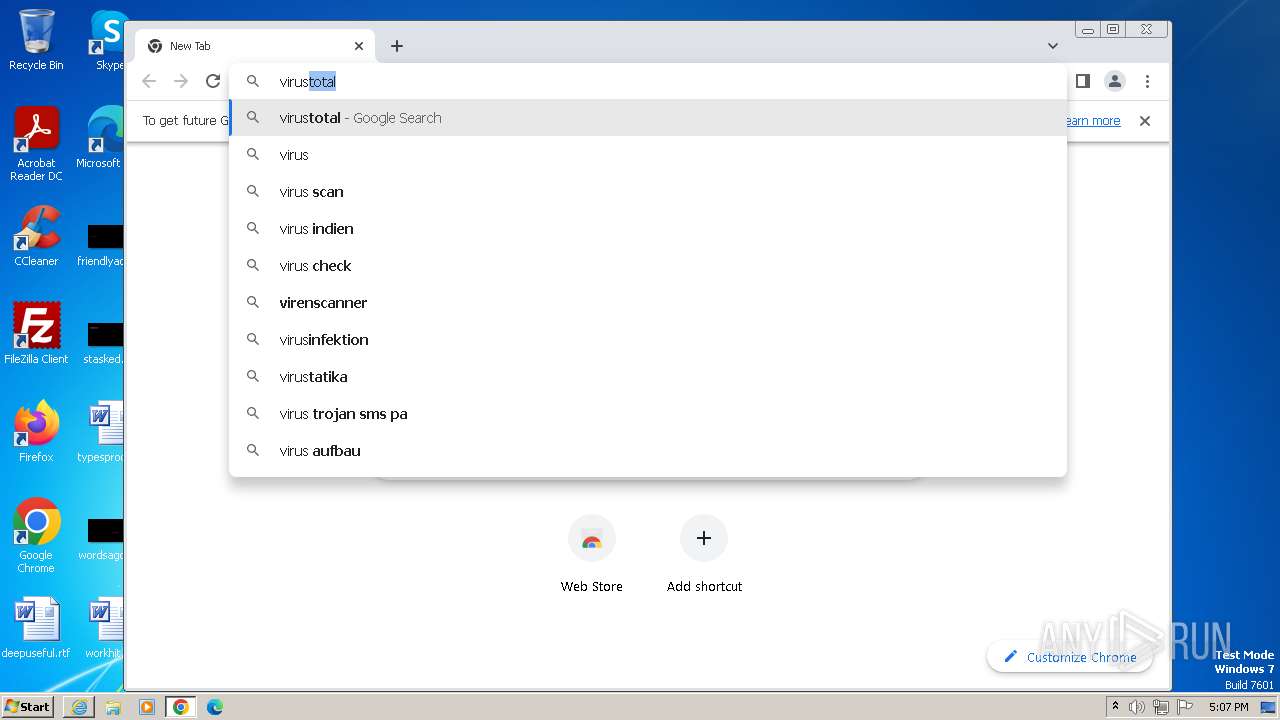
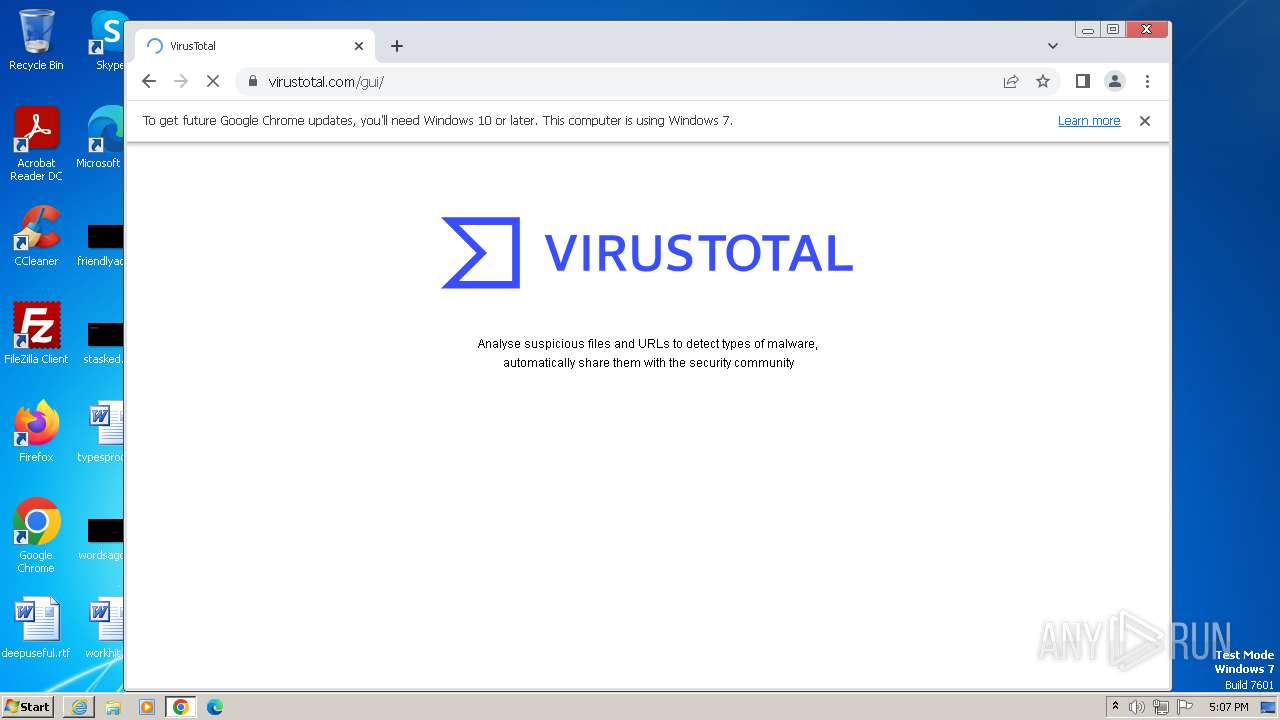
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
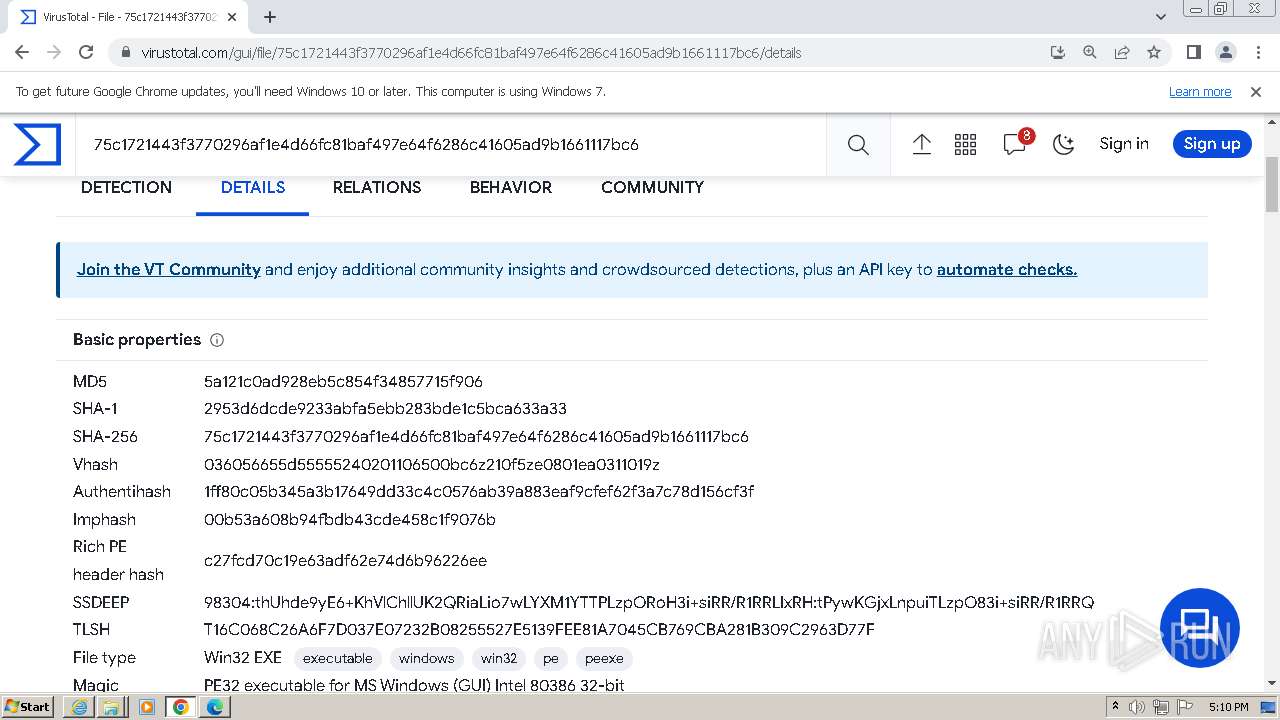
| SHA1: | CCF7188116B481577EF954F50AE688C6B2BEAE6B |
| SHA256: | 07E3366173FEAC58C1C6B6DF6315E45CE87BD405FC96604CB7865DBC4F858010 |
| SSDEEP: | 3:i5KOWKHKTELEORBdB94A:i5BguYA |
MALICIOUS
Drops the executable file immediately after the start
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3396)
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3296)
- Bkav_Limited.exe (PID: 3664)
- Bkav_Limited.exe (PID: 188)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- dpinst.exe (PID: 3568)
- drvinst.exe (PID: 372)
Creates a writable file the system directory
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- drvinst.exe (PID: 372)
Uses Task Scheduler to autorun other applications
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- cmd.exe (PID: 2312)
SUSPICIOUS
Reads the Windows owner or organization settings
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
The process drops C-runtime libraries
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
The process creates files with name similar to system file names
- Bkav_Limited.exe (PID: 3664)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- Bkav_Limited.exe (PID: 188)
Malware-specific behavior (creating "System.dll" in Temp)
- Bkav_Limited.exe (PID: 3664)
- Bkav_Limited.exe (PID: 188)
Process drops legitimate windows executable (CertUtil.exe)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
Process drops legitimate windows executable
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- dpinst.exe (PID: 3568)
- drvinst.exe (PID: 372)
Drops a system driver (possible attempt to evade defenses)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- dpinst.exe (PID: 3568)
- drvinst.exe (PID: 372)
Uses TASKKILL.EXE to kill process
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
Starts CMD.EXE for commands execution
- TokenManagerAgent.exe (PID: 2820)
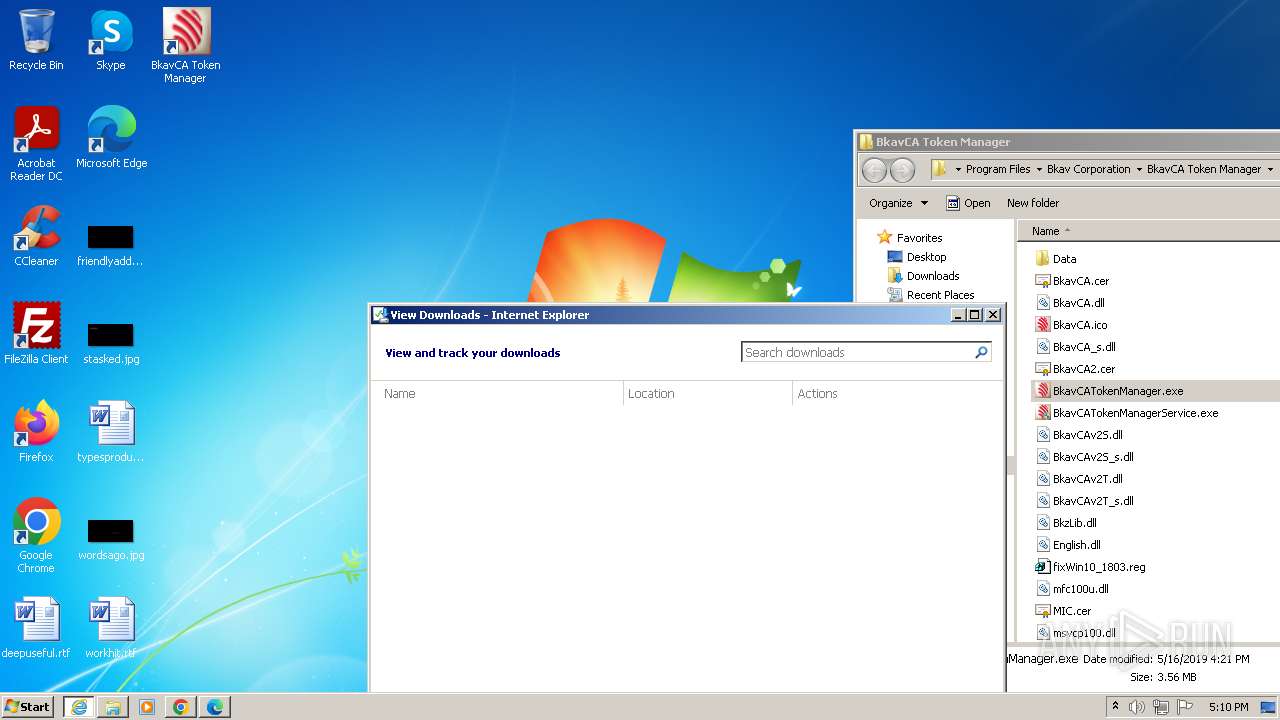
Creates files in the driver directory
- drvinst.exe (PID: 372)
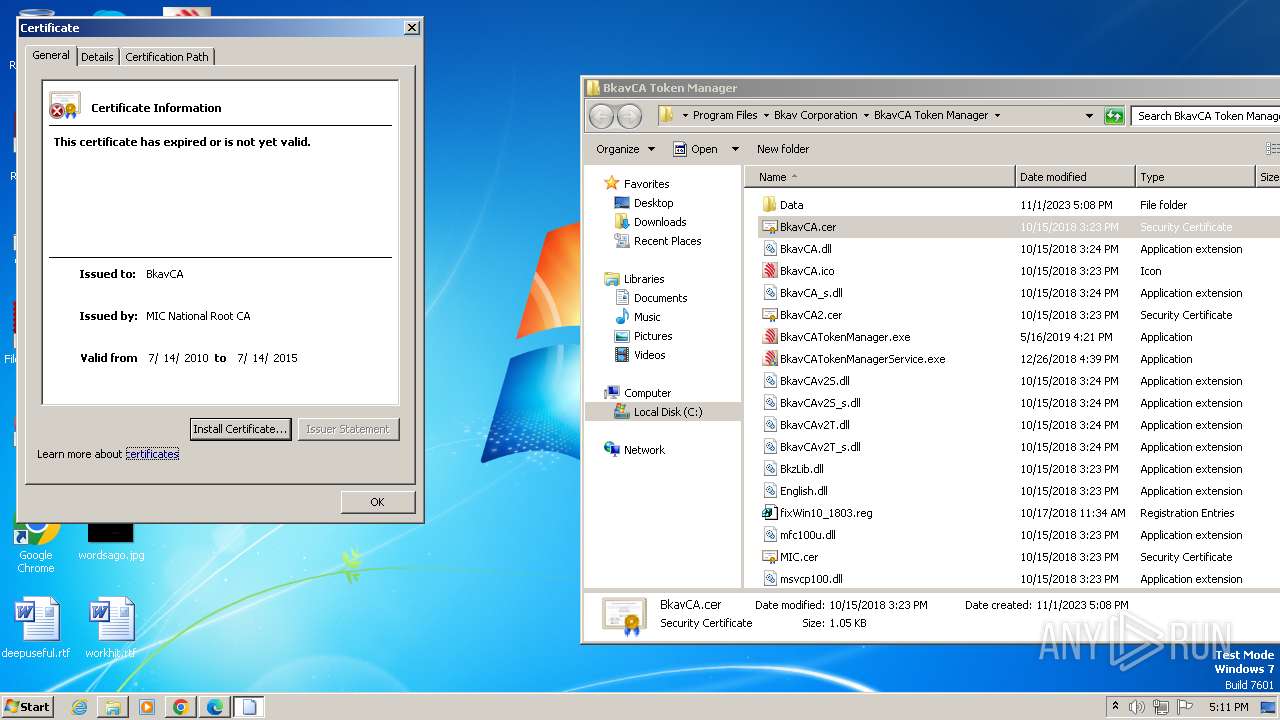
Checks Windows Trust Settings
- drvinst.exe (PID: 372)
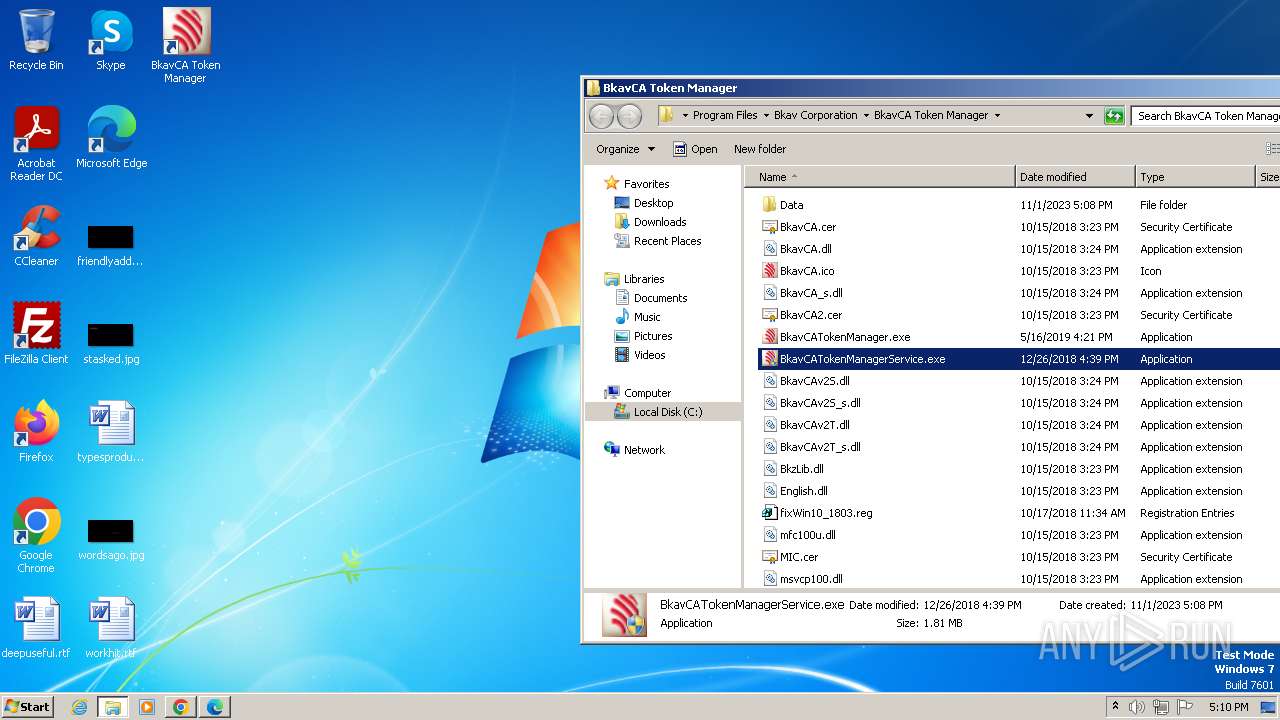
Executes as Windows Service
- rundll32.exe (PID: 3652)
- BkavCATokenManagerService.exe (PID: 2828)
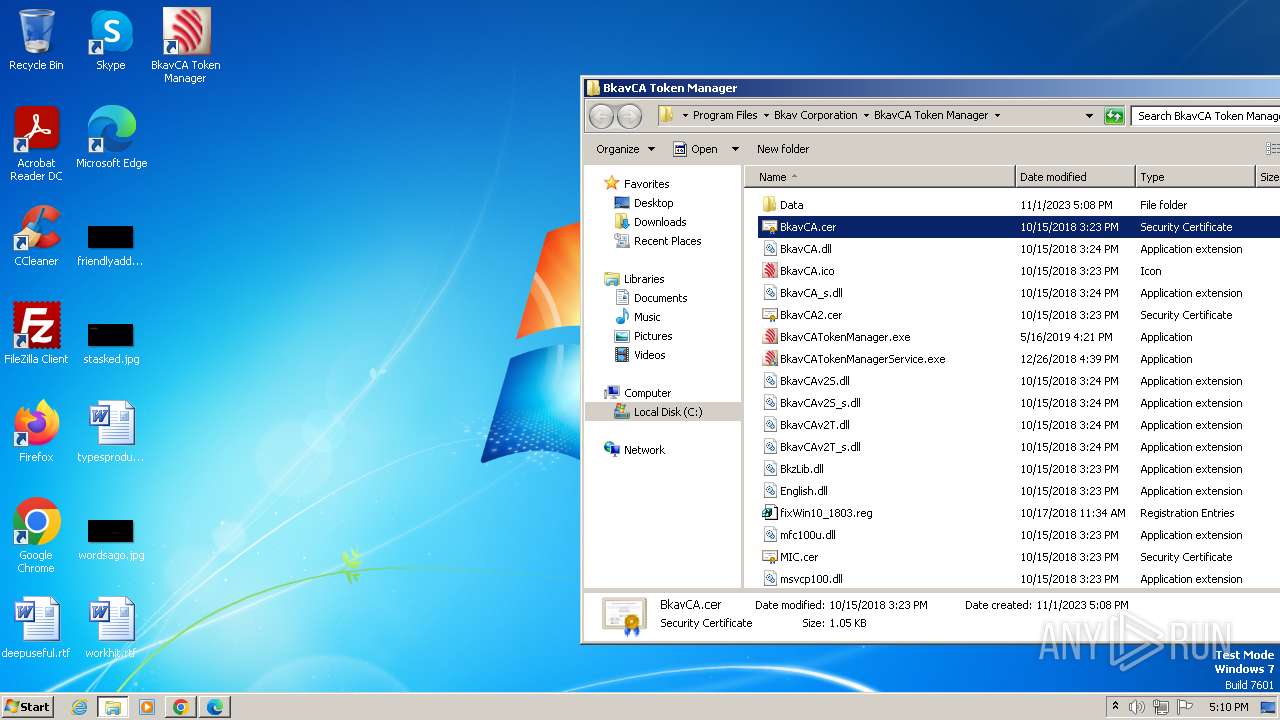
Reads settings of System Certificates
- BkavCATokenManager.exe (PID: 280)
- rundll32.exe (PID: 3764)
Adds/modifies Windows certificates
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
Searches for installed software
- BkavCATokenManager.exe (PID: 280)
Reads the Internet Settings
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
INFO
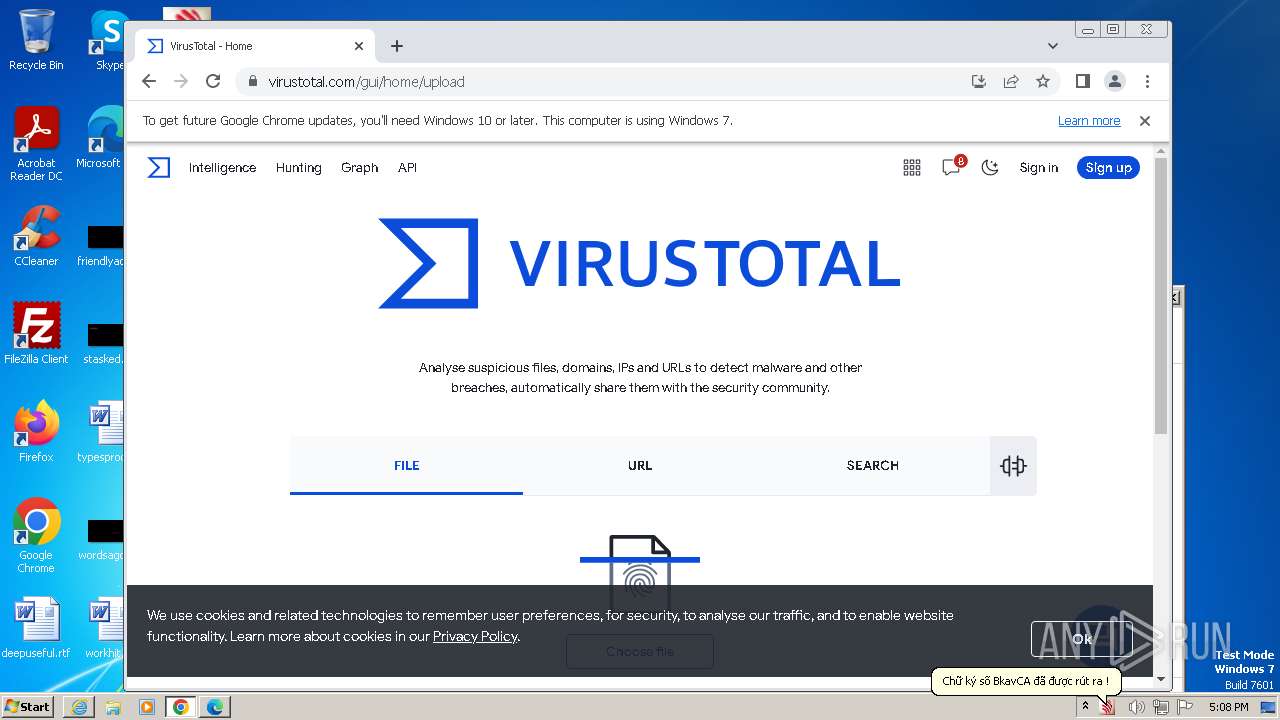
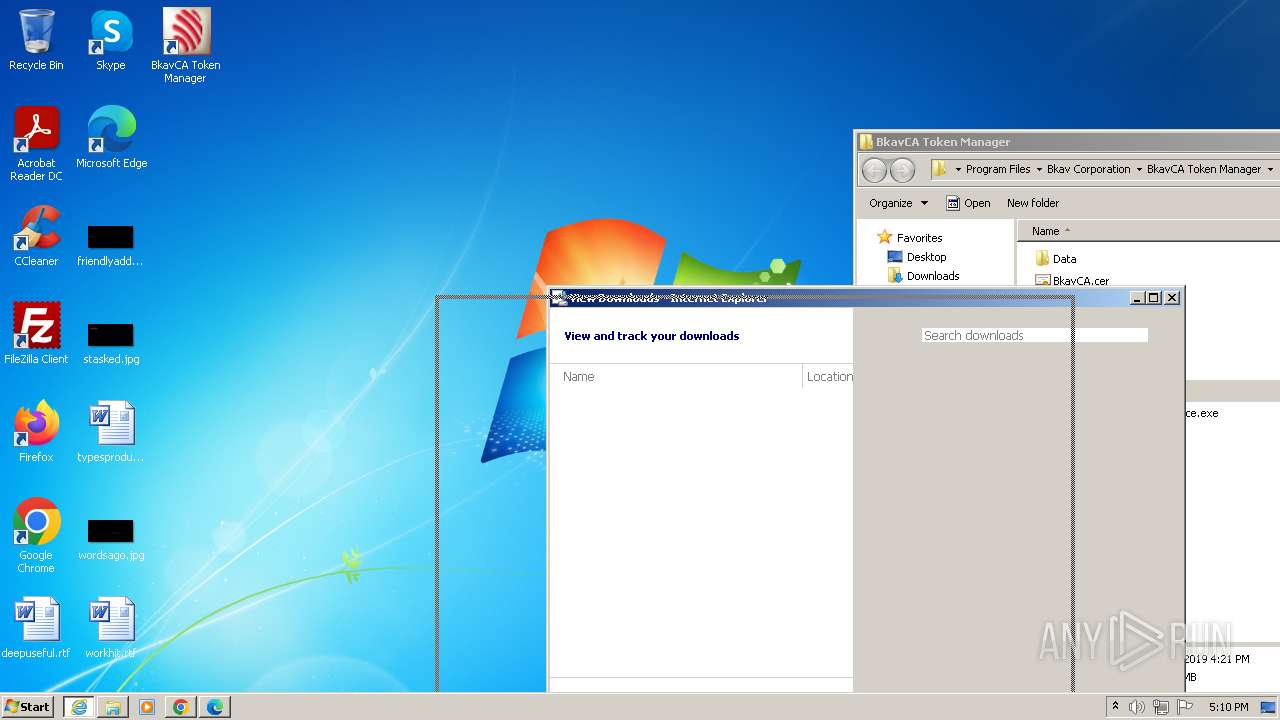
The process uses the downloaded file
- chrome.exe (PID: 280)
- chrome.exe (PID: 1952)
- iexplore.exe (PID: 3552)
- chrome.exe (PID: 2692)
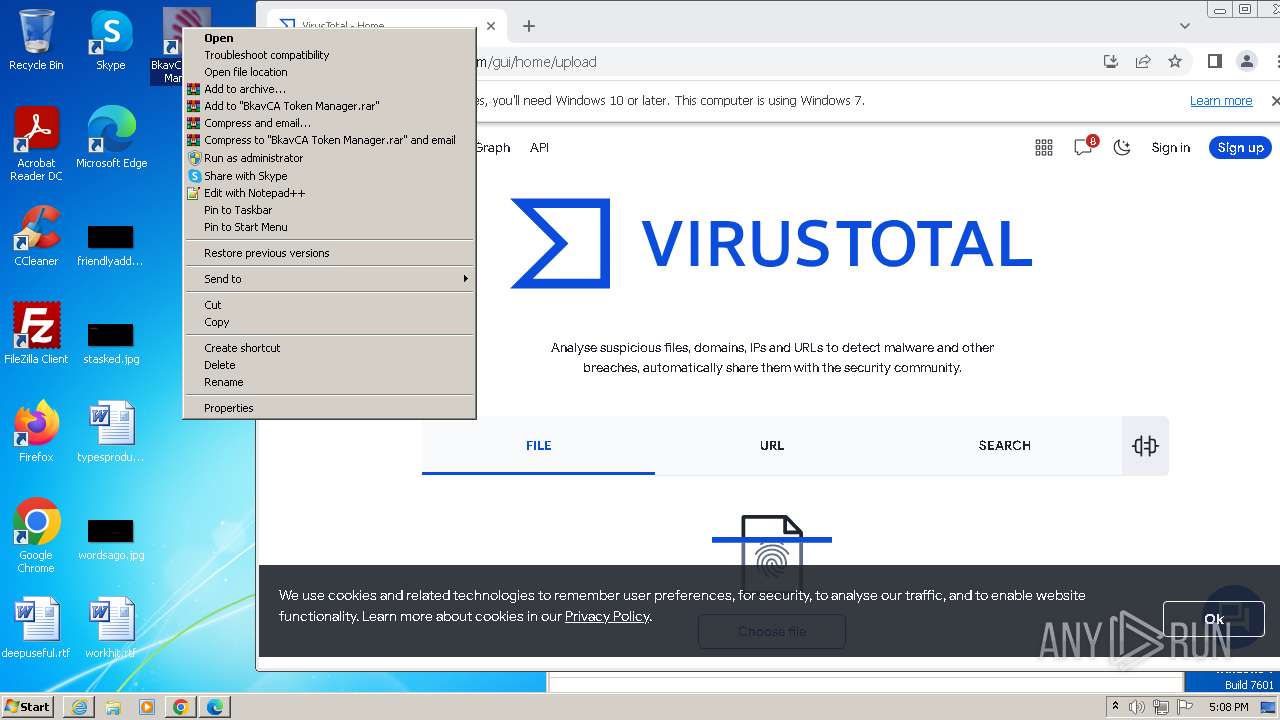
Manual execution by a user
- chrome.exe (PID: 584)
- BkavCATokenManager.exe (PID: 460)
- BkavCATokenManager.exe (PID: 3580)
- BkavCATokenManagerService.exe (PID: 3216)
- BkavCATokenManagerService.exe (PID: 1412)
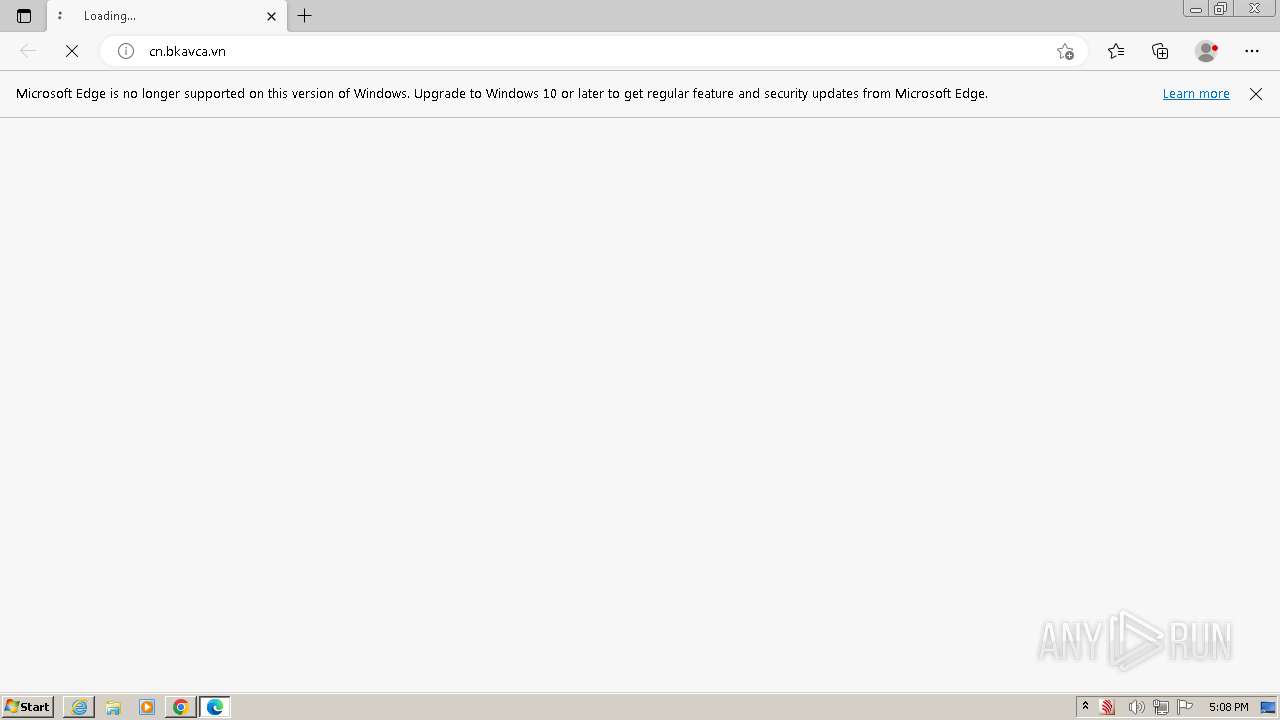
- msedge.exe (PID: 3924)
- rundll32.exe (PID: 3764)
Drops the executable file immediately after the start
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 3552)
Application launched itself
- chrome.exe (PID: 584)
- iexplore.exe (PID: 3552)
- msedge.exe (PID: 3924)
- msedge.exe (PID: 3680)
Checks supported languages
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3396)
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3296)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2500)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- Bkav_Limited.exe (PID: 3664)
- certutil.exe (PID: 792)
- dpinst.exe (PID: 3568)
- Bkav_Limited.exe (PID: 188)
- BkavCATokenManager.exe (PID: 280)
- TokenManagerAgent.exe (PID: 2820)
- BkavCATokenManagerService.exe (PID: 2680)
- BkavCATokenManagerService.exe (PID: 2828)
- drvinst.exe (PID: 372)
- BkavCATokenManager.exe (PID: 460)
- BkavCATokenManager.exe (PID: 3580)
- BkavCATokenManagerService.exe (PID: 1412)
Create files in a temporary directory
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3396)
- BkavCATokenManager_Setup_2.8.0.24_vi.exe (PID: 3296)
- Bkav_Limited.exe (PID: 3664)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- Bkav_Limited.exe (PID: 188)
- dpinst.exe (PID: 3568)
Reads the computer name
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2500)
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- Bkav_Limited.exe (PID: 3664)
- certutil.exe (PID: 792)
- Bkav_Limited.exe (PID: 188)
- BkavCATokenManager.exe (PID: 280)
- BkavCATokenManagerService.exe (PID: 2680)
- dpinst.exe (PID: 3568)
- drvinst.exe (PID: 372)
- BkavCATokenManagerService.exe (PID: 2828)
- BkavCATokenManagerService.exe (PID: 1412)
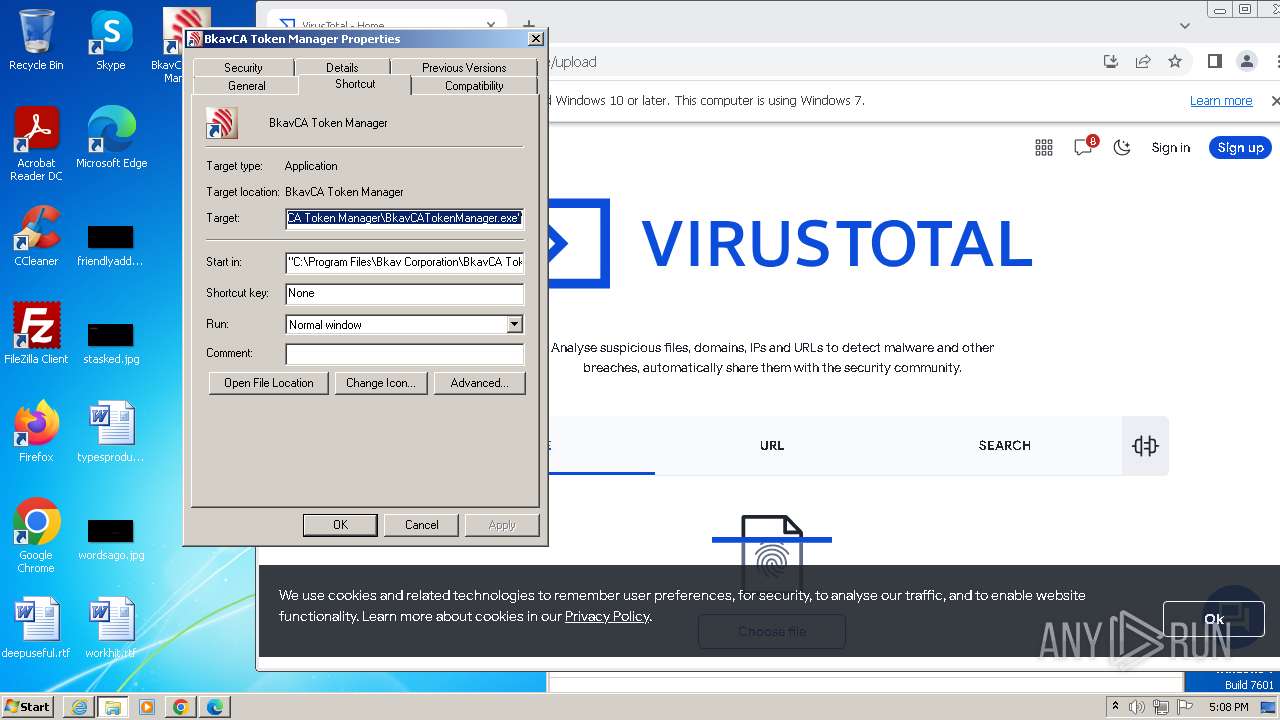
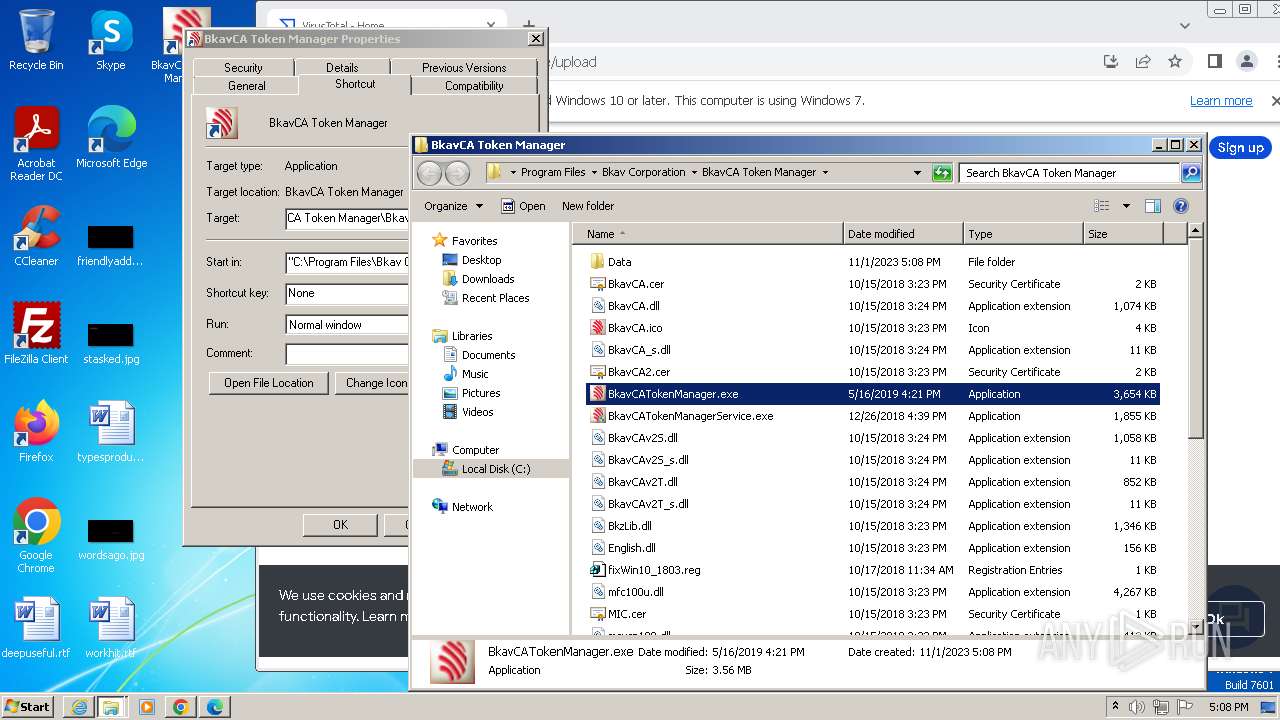
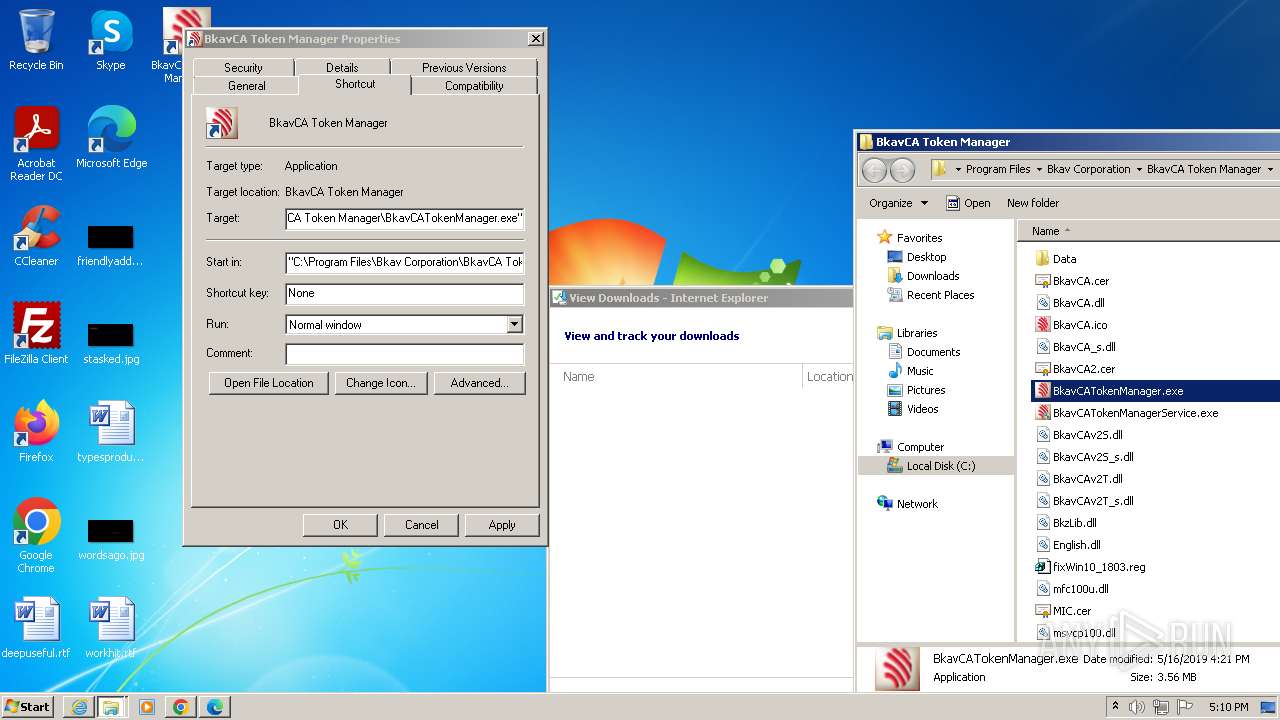
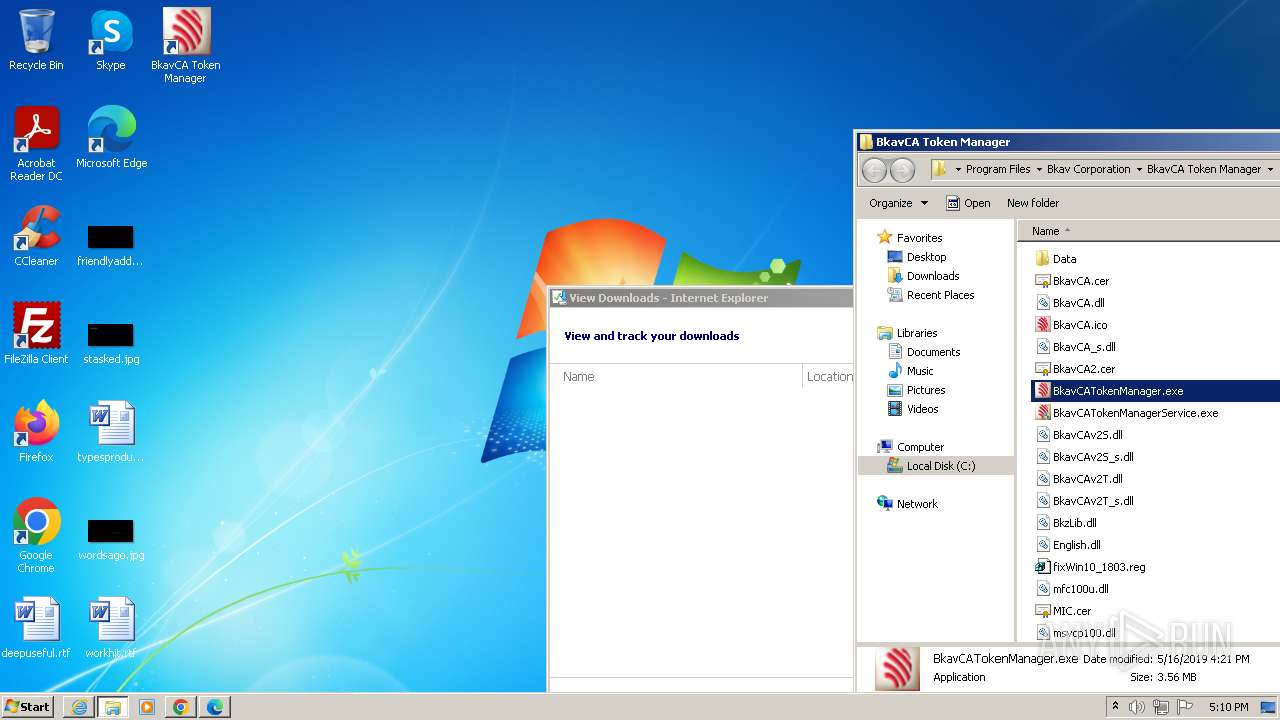
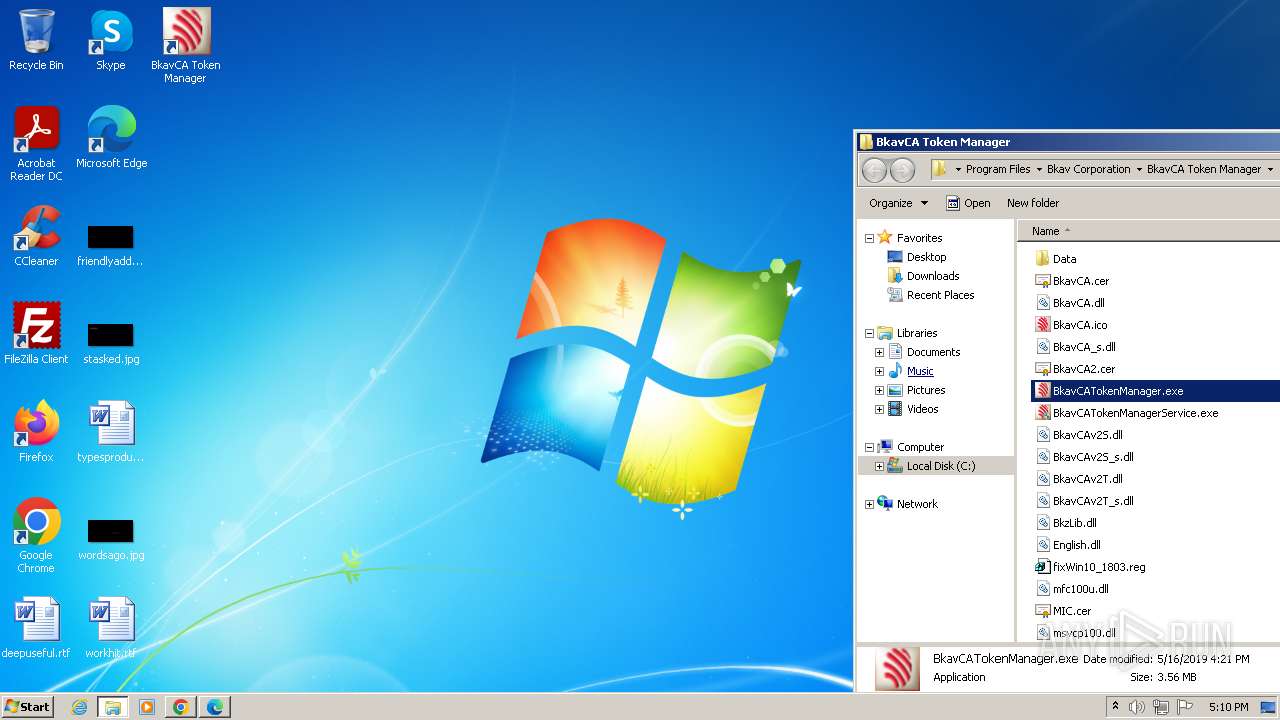
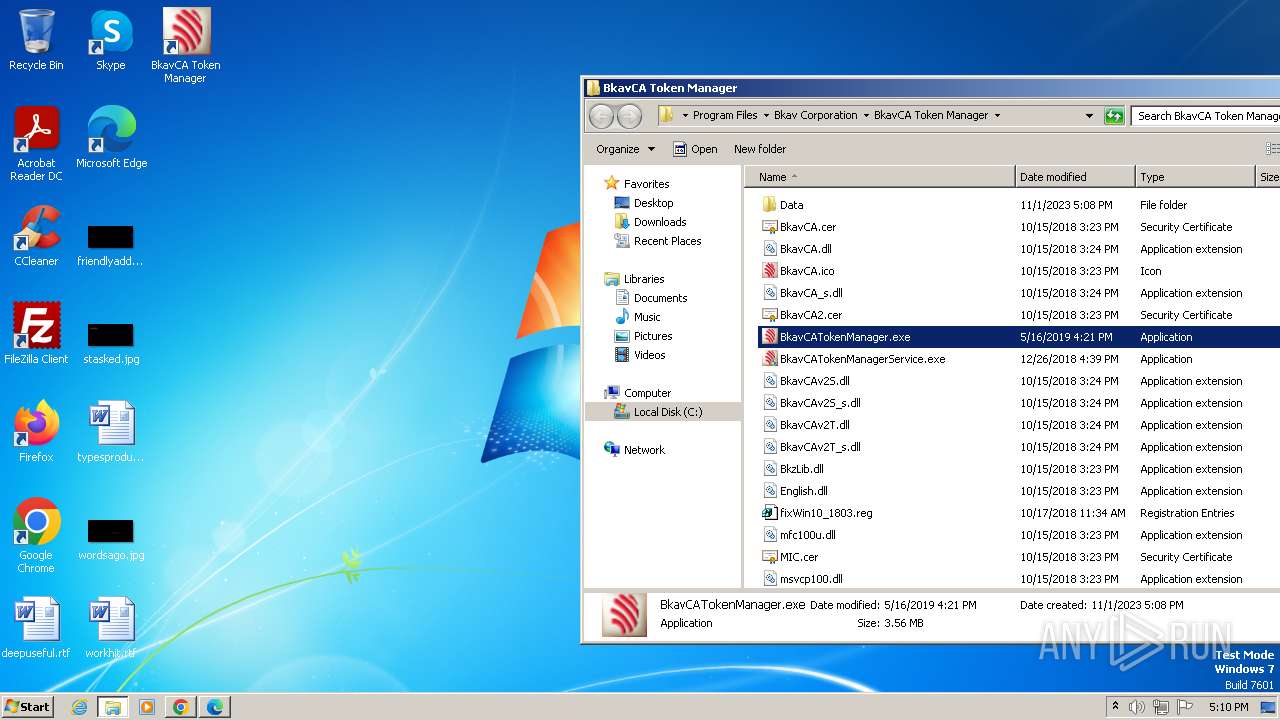
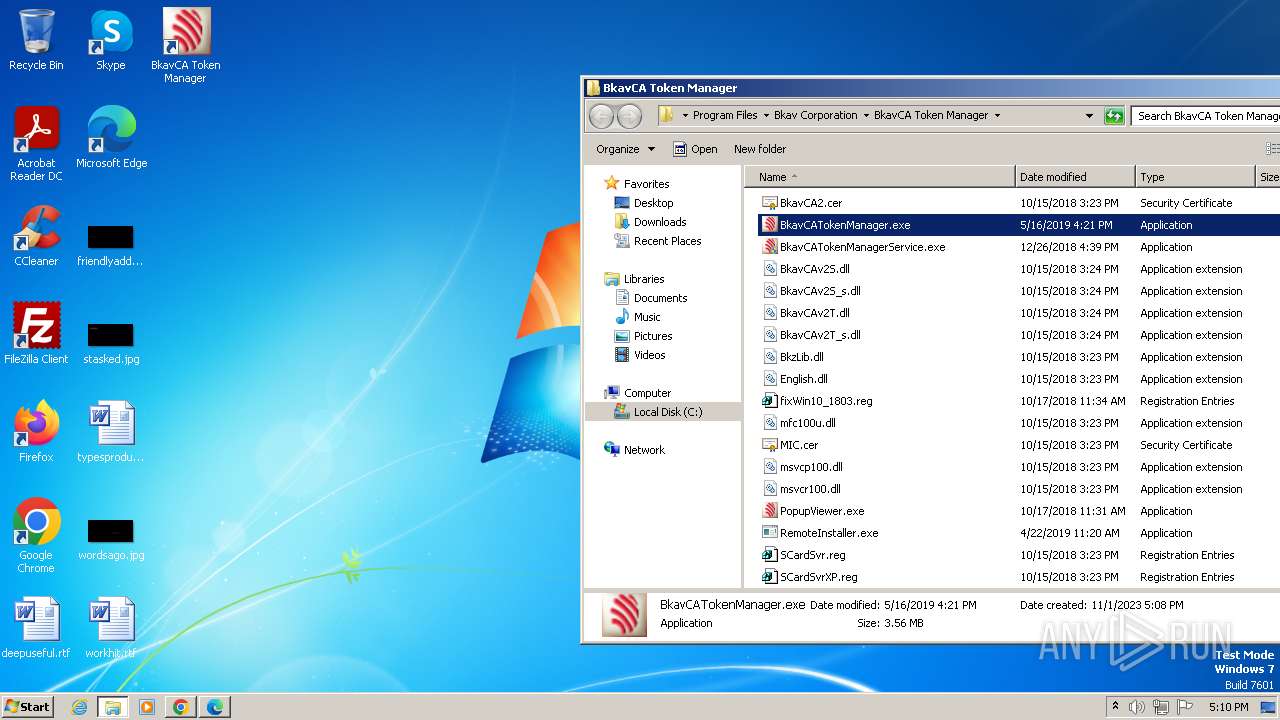
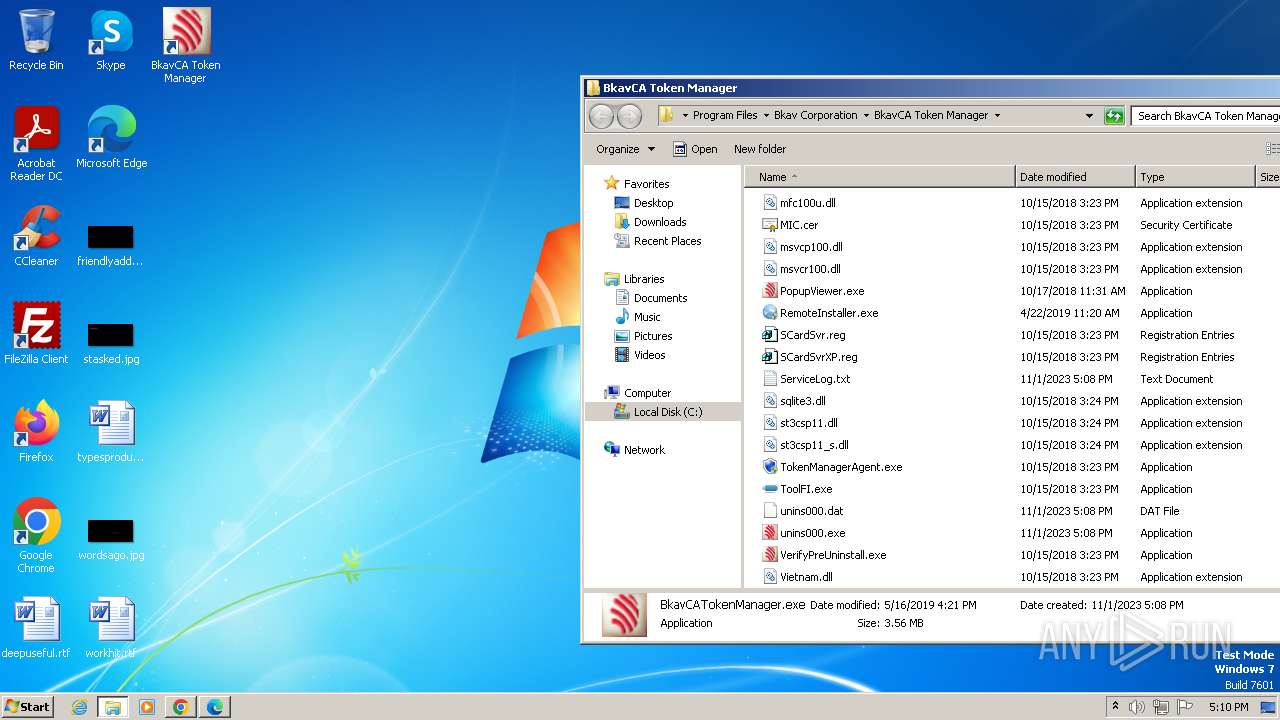
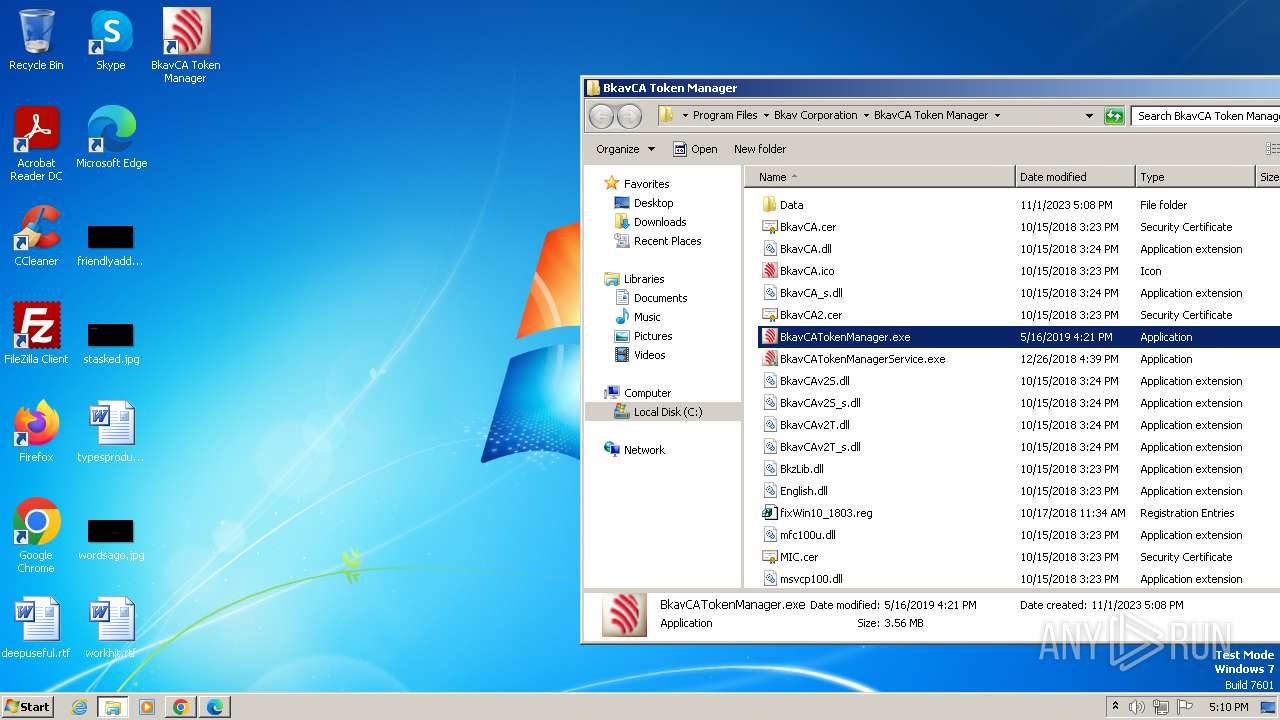
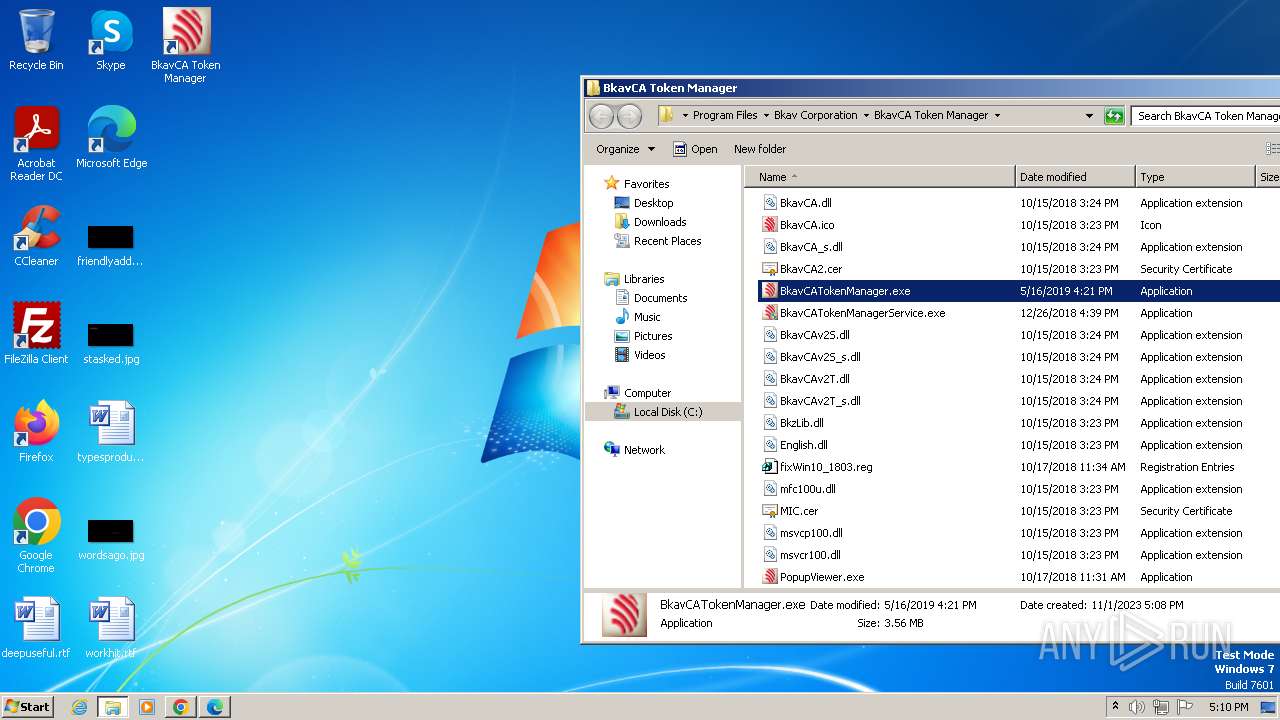
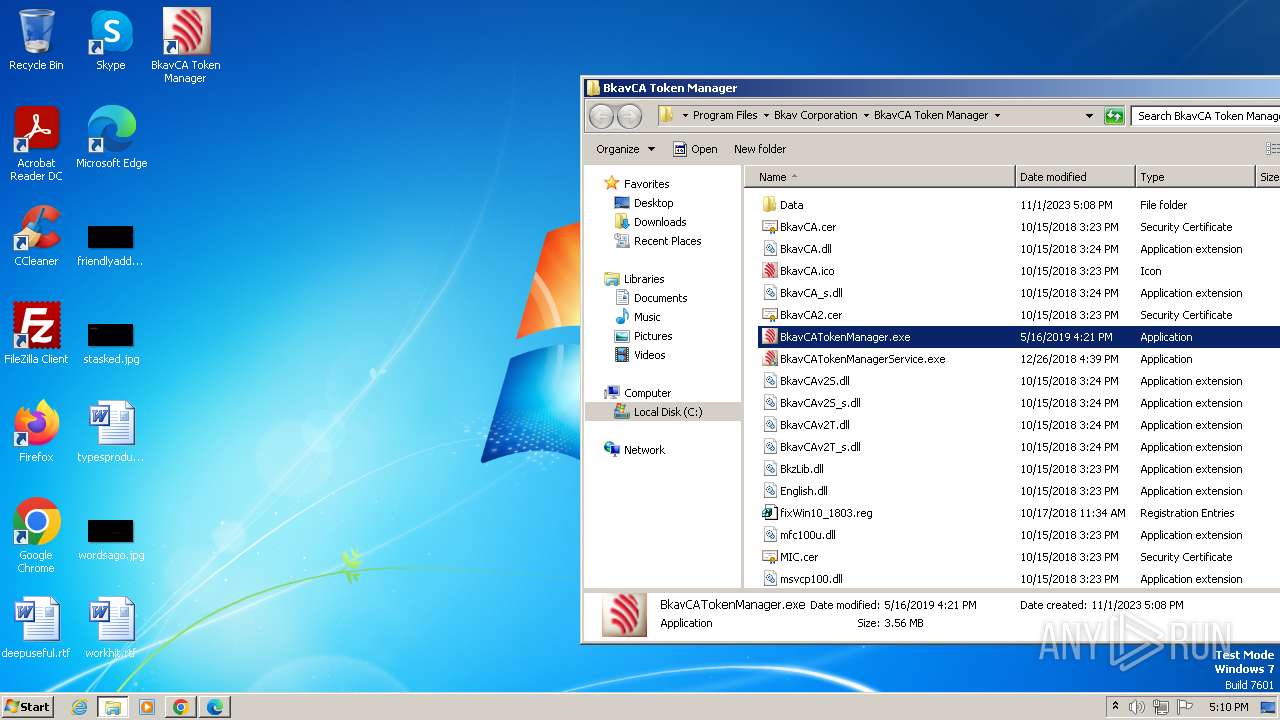
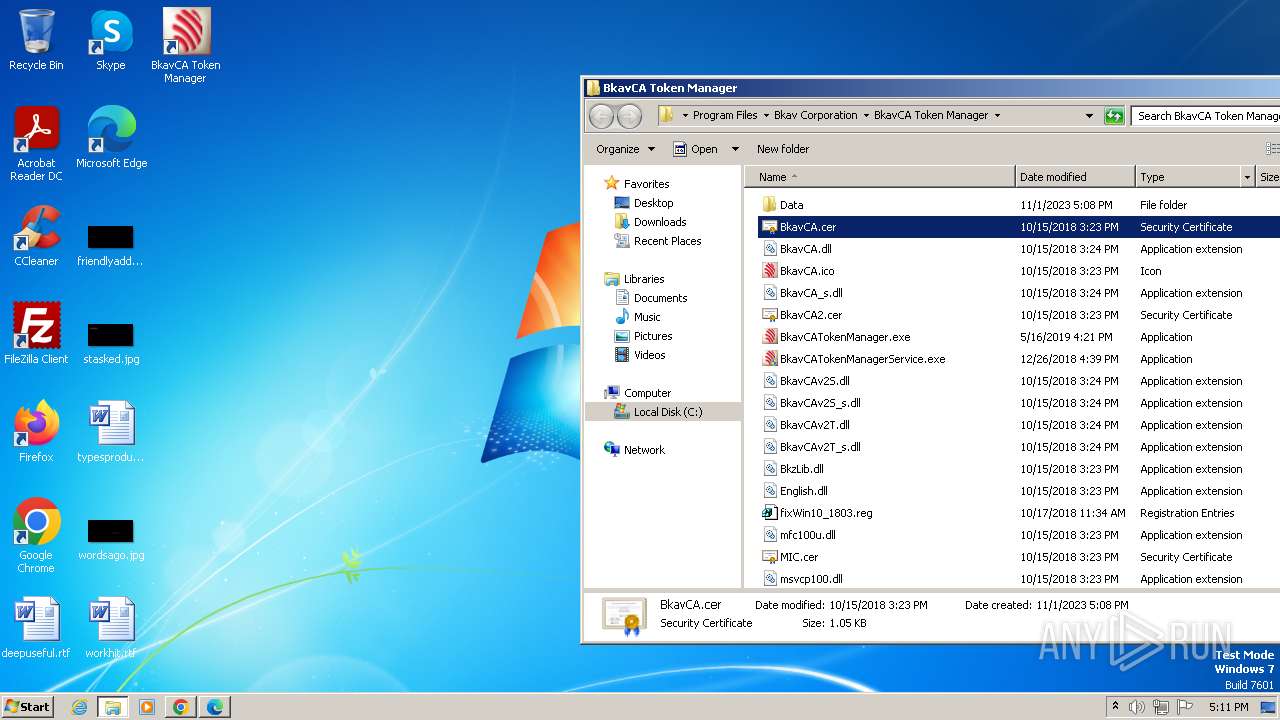
Creates files in the program directory
- BkavCATokenManager_Setup_2.8.0.24_vi.tmp (PID: 2356)
- BkavCATokenManagerService.exe (PID: 2828)
- BkavCATokenManager.exe (PID: 280)
Reads the machine GUID from the registry
- certutil.exe (PID: 792)
- dpinst.exe (PID: 3568)
- drvinst.exe (PID: 372)
- BkavCATokenManager.exe (PID: 280)
Reads product name
- TokenManagerAgent.exe (PID: 2820)
- BkavCATokenManager.exe (PID: 280)
Reads Environment values
- TokenManagerAgent.exe (PID: 2820)
- BkavCATokenManager.exe (PID: 280)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
136
Monitored processes
76
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x68a3f598,0x68a3f5a8,0x68a3f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 188 | "C:\Users\admin\AppData\Local\Temp\is-T41S5.tmp\Bkav_Limited.exe" | C:\Users\admin\AppData\Local\Temp\is-T41S5.tmp\Bkav_Limited.exe | — | BkavCATokenManager_Setup_2.8.0.24_vi.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3752 --field-trial-handle=1308,i,11134090893503030578,5319463823449757265,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4172 --field-trial-handle=1160,i,13673433140850262483,9679815088356064295,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
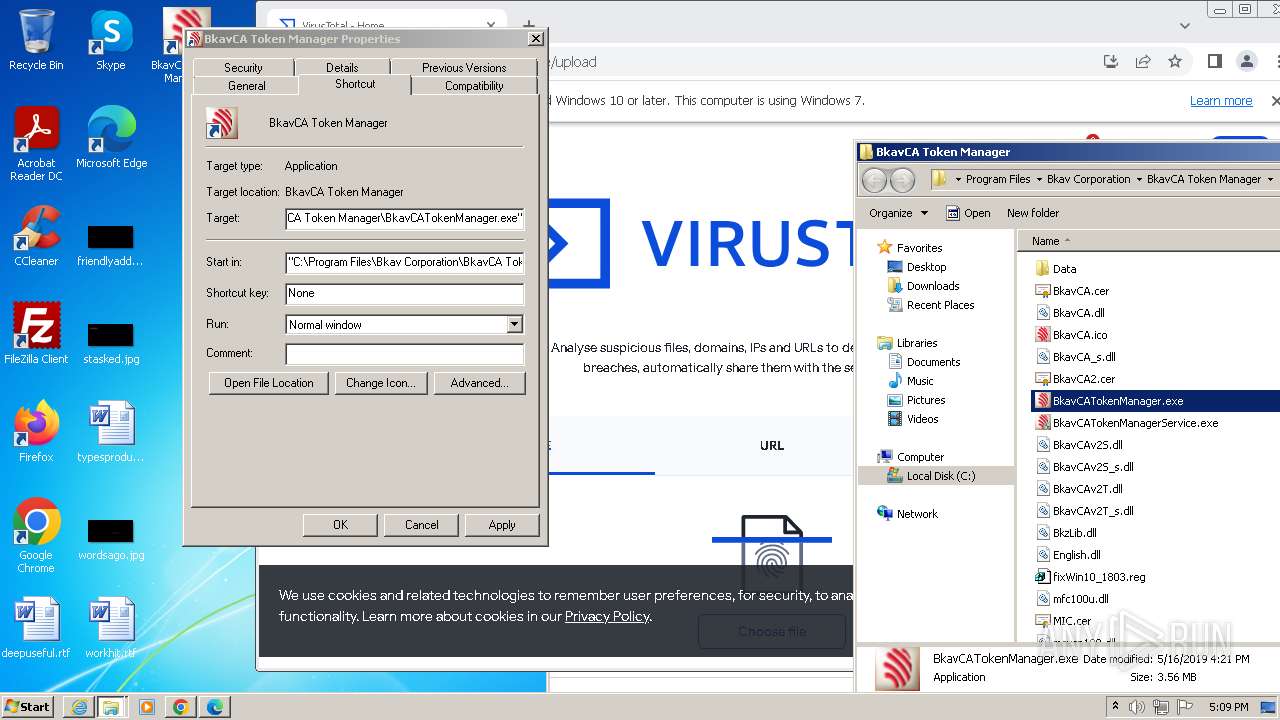
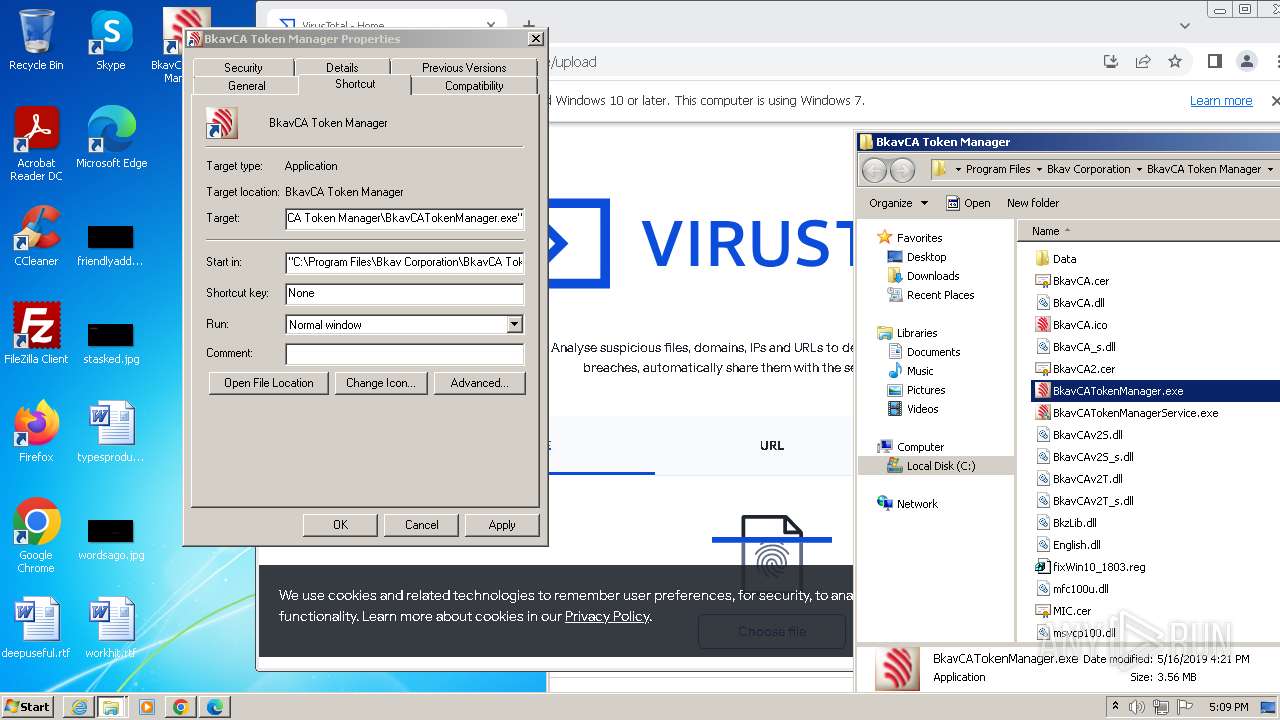
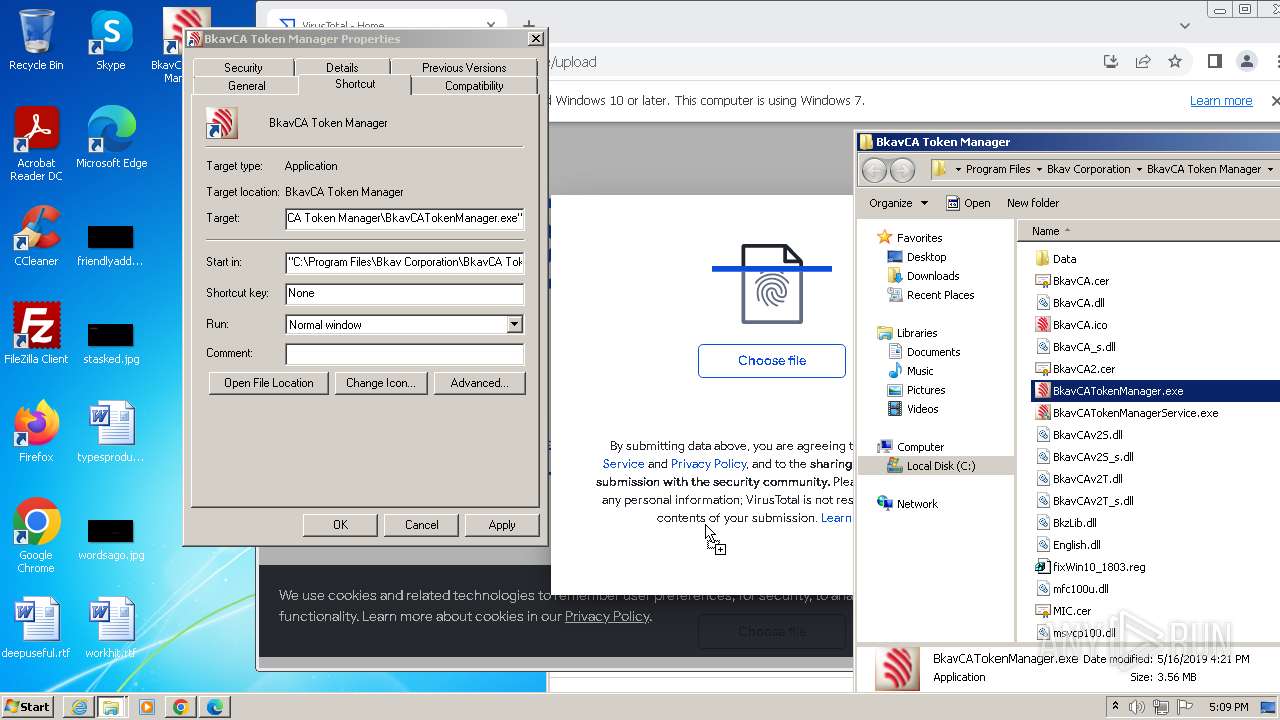
| 280 | "C:\Program Files\Bkav Corporation\BkavCA Token Manager\BkavCATokenManager.exe" | C:\Program Files\Bkav Corporation\BkavCA Token Manager\BkavCATokenManager.exe | BkavCATokenManager_Setup_2.8.0.24_vi.tmp | ||||||||||||
User: admin Company: Bkav Corporation Integrity Level: HIGH Description: BkavCA Token Manager Exit code: 0 Version: 2.8.0.24 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1488 --field-trial-handle=1296,i,1080547023372965159,4714154965775901677,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 372 | DrvInst.exe "4" "8" "C:\Users\admin\AppData\Local\Temp\{6851bea0-c6c0-1ec6-b79d-d6018514e625}\usbccid.inf" "0" "660eee203" "000003B4" "WinSta0\Default" "000005C8" "208" "c:\users\admin\appdata\local\temp\is-t41s5.tmp" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1500 --field-trial-handle=1308,i,11134090893503030578,5319463823449757265,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Bkav Corporation\BkavCA Token Manager\BkavCATokenManager.exe" | C:\Program Files\Bkav Corporation\BkavCA Token Manager\BkavCATokenManager.exe | — | explorer.exe | |||||||||||
User: admin Company: Bkav Corporation Integrity Level: MEDIUM Description: BkavCA Token Manager Exit code: 0 Version: 2.8.0.24 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4104 --field-trial-handle=1160,i,13673433140850262483,9679815088356064295,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
38 837
Read events
38 530
Write events
294
Delete events
13
Modification events
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
100
Suspicious files
314
Text files
112
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF27a819.TMP | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF27aa7a.TMP | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF27a7fa.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:B806171F9E7C87423595645872D869B0 | SHA256:851A8D533BEBF6A69C5518375396E97463302C1E2031D04F8EB5851C5C82CEB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
115
DNS requests
121
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
3552 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?68eaf9d0aba9cb5a | unknown | compressed | 4.66 Kb | unknown |
444 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | unknown | binary | 1.38 Kb | unknown |
3552 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3ebfdaea1830f9bc | unknown | compressed | 4.66 Kb | unknown |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3552 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aa68ceb9da32b9c2 | unknown | compressed | 4.66 Kb | unknown |
444 | msedge.exe | GET | 301 | 103.63.111.84:80 | http://cn.bkavca.vn/ | unknown | html | 166 b | unknown |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
444 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | binary | 1.52 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
584 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2084 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2084 | chrome.exe | 142.250.186.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
2084 | chrome.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
2084 | chrome.exe | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
584 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
www.recaptcha.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4000 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |