| File name: | CertTree.exe |
| Full analysis: | https://app.any.run/tasks/91a5ce70-e867-4433-9abe-61564b99658b |
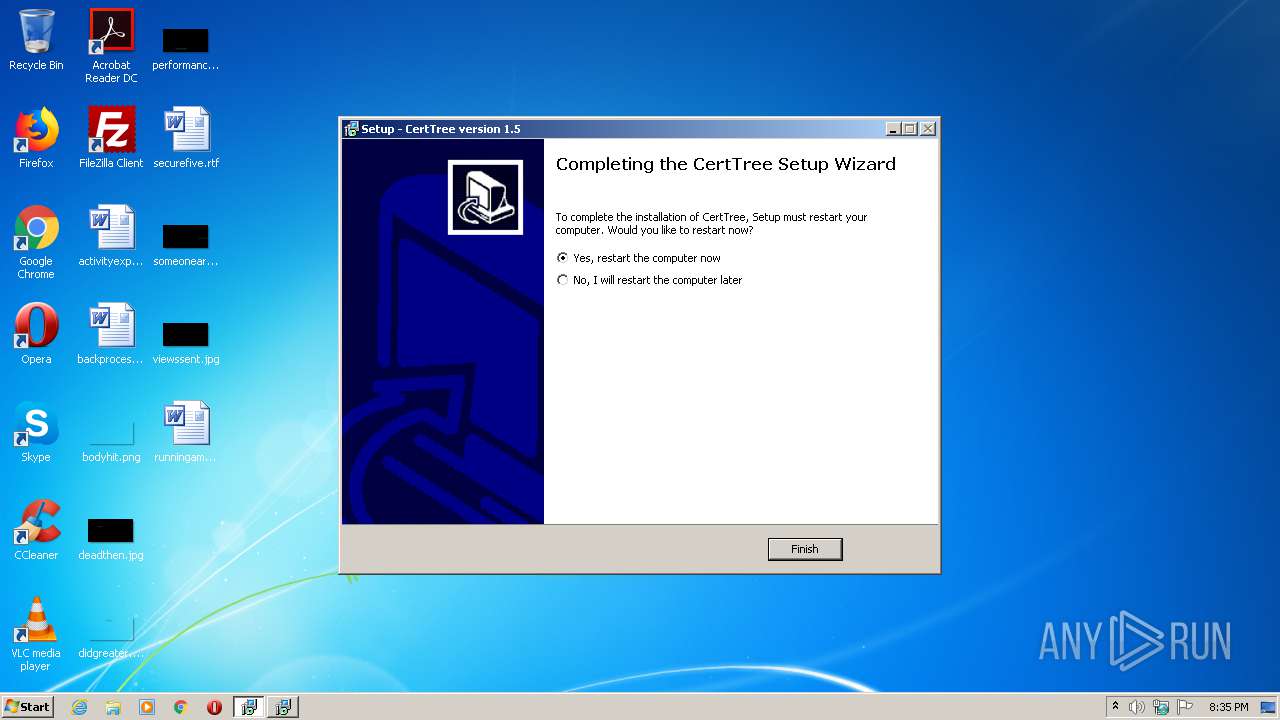
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2021, 20:35:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3B1CECCAC43B333022E36B97FB628755 |
| SHA1: | 922DF1B734CE482BBE163AE04F1F4B255CABE74A |
| SHA256: | 07DBDA10943335241DB3F610ED24207C2F6051564E569F557DD1ED8C8389F5E4 |
| SSDEEP: | 49152:8qeNVO+V/BUBGJ0YF1I8P7Jop40jpv6gWq:JEE+5yXYo8C4EsgL |
MALICIOUS
Drops executable file immediately after starts
- CertTree.exe (PID: 2776)
- CertTree.exe (PID: 4032)
- unins000.exe (PID: 2452)
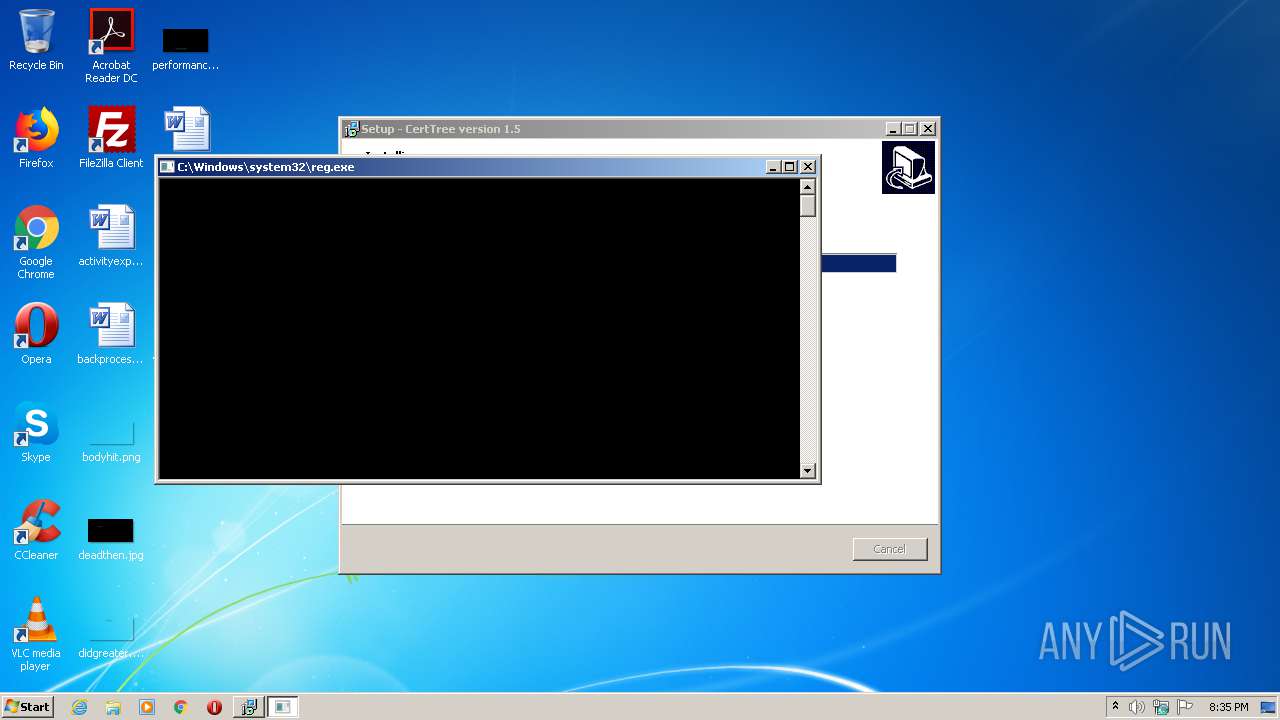
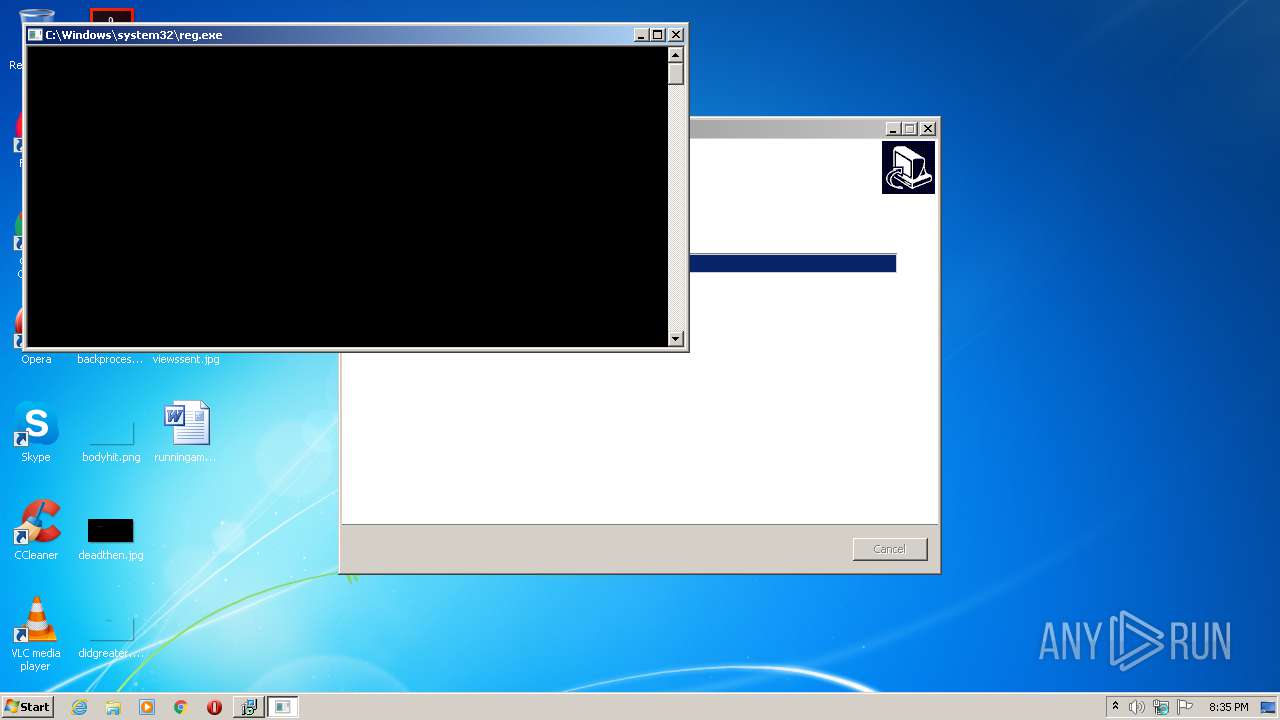
Changes settings of System certificates
- reg.exe (PID: 1448)
- reg.exe (PID: 3580)
Application was dropped or rewritten from another process
- unins000.exe (PID: 2452)
- _iu14D2N.tmp (PID: 3188)
SUSPICIOUS
Reads Windows owner or organization settings
- CertTree.tmp (PID: 848)
Executable content was dropped or overwritten
- CertTree.exe (PID: 2776)
- CertTree.exe (PID: 4032)
- CertTree.tmp (PID: 848)
- unins000.exe (PID: 2452)
Reads the Windows organization settings
- CertTree.tmp (PID: 848)
Uses REG.EXE to modify Windows registry
- CertTree.tmp (PID: 848)
Adds / modifies Windows certificates
- reg.exe (PID: 3580)
- reg.exe (PID: 1448)
Starts itself from another location
- unins000.exe (PID: 2452)
Starts application with an unusual extension
- unins000.exe (PID: 2452)
INFO
Application was dropped or rewritten from another process
- CertTree.tmp (PID: 848)
- CertTree.tmp (PID: 1540)
Creates a software uninstall entry
- CertTree.tmp (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:21 07:56:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Tulpep |
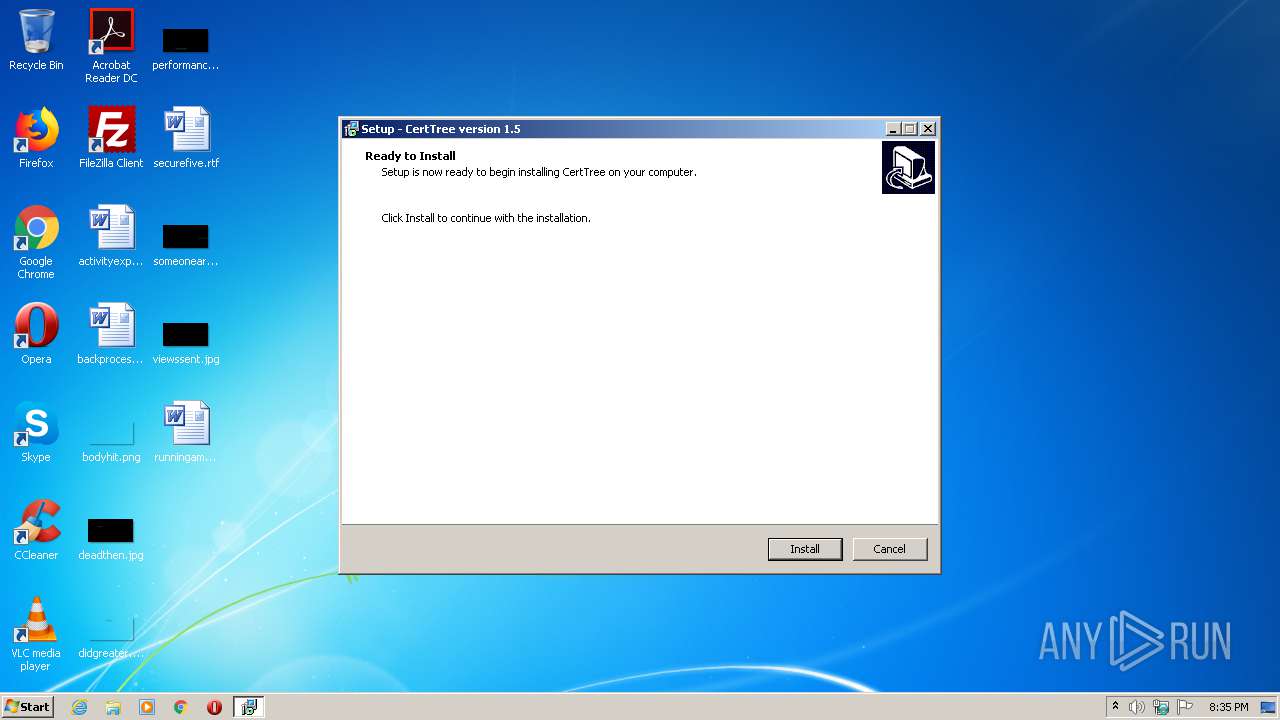
| FileDescription: | CertTree Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | CertTree |
| ProductVersion: | 1.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-May-2020 05:56:23 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Tulpep |
| FileDescription: | CertTree Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | CertTree |
| ProductVersion: | 1.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 21-May-2020 05:56:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B3604 | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35433 |
.itext | 0x000B5000 | 0x00001684 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9709 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04216 |
.bss | 0x000BB000 | 0x00006DA0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00004800 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41914 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4086 | 3.16547 | 864 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | UNKNOWN | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054058 |
Total processes
53
Monitored processes
9
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Users\admin\AppData\Local\Temp\is-5DHJ4.tmp\CertTree.tmp" /SL5="$50138,1072192,780800,C:\Users\admin\AppData\Local\Temp\CertTree.exe" /SPAWNWND=$40132 /NOTIFYWND=$30156 | C:\Users\admin\AppData\Local\Temp\is-5DHJ4.tmp\CertTree.tmp | CertTree.exe | ||||||||||||
User: admin Company: Tulpep Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 964 | "Timeout" 10 >nul | C:\Windows\system32\Timeout.exe | — | CertTree.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1448 | "C:\Windows\system32\reg.exe" import C:\temp\CertTree\Certtree.reg | C:\Windows\system32\reg.exe | — | CertTree.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\Temp\is-1D0I4.tmp\CertTree.tmp" /SL5="$30156,1072192,780800,C:\Users\admin\AppData\Local\Temp\CertTree.exe" | C:\Users\admin\AppData\Local\Temp\is-1D0I4.tmp\CertTree.tmp | — | CertTree.exe | |||||||||||
User: admin Company: Tulpep Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2452 | "C:\temp\Certtree\unins000.exe" /silent | C:\temp\Certtree\unins000.exe | CertTree.tmp | ||||||||||||
User: admin Company: Tulpep Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\CertTree.exe" | C:\Users\admin\AppData\Local\Temp\CertTree.exe | explorer.exe | ||||||||||||
User: admin Company: Tulpep Integrity Level: MEDIUM Description: CertTree Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\temp\Certtree\unins000.exe" /FIRSTPHASEWND=$101B0 /silent | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | — | unins000.exe | |||||||||||
User: admin Company: Tulpep Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3580 | "C:\Windows\system32\reg.exe" import C:\temp\CertTree\Certtree.reg | C:\Windows\system32\reg.exe | — | CertTree.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\AppData\Local\Temp\CertTree.exe" /SPAWNWND=$40132 /NOTIFYWND=$30156 | C:\Users\admin\AppData\Local\Temp\CertTree.exe | CertTree.tmp | ||||||||||||
User: admin Company: Tulpep Integrity Level: HIGH Description: CertTree Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
948
Read events
375
Write events
566
Delete events
7
Modification events
| (PID) Process: | (848) CertTree.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 50030000DEB370EAEC15D701 | |||
| (PID) Process: | (848) CertTree.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: DA8D751A9266515532A258B8EE8FDA477800960E6888C1C1132A28904C90557C | |||
| (PID) Process: | (848) CertTree.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AAD Token Issuer\Certificates\60BC88FA3B97CC73CDE7B2BBFFB29BD21AF6C06F |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000060BC88FA3B97CC73CDE7B2BBFFB29BD21AF6C06F200000000100000049030000308203453082022DA00302010202103E9493BCB37DD38B4745CD55D15ED6BB300D06092A864886F70D01010B0500304D314B304906035504031E42004D0053002D004F007200670061006E0069007A006100740069006F006E002D005000320050002D0041006300630065007300730020005B0032003000320030005D301E170D3230303330393030303030305A170D3231303330393030303030305A304D314B304906035504031E42004D0053002D004F007200670061006E0069007A006100740069006F006E002D005000320050002D0041006300630065007300730020005B0032003000320030005D30820122300D06092A864886F70D01010105000382010F003082010A0282010100BD2D36511122398F035828D12574490B5D8693A2CD35A3B9224044C2E0908D50F0BDFAD713B1944D5910FF695149A59CA8E22BFB2ED3F111D1EAD1139E9ED2C9D88A593992E91BCA4E0B52BC429691A8D3E75EAC8B80DC835DE21208016C7086667BB6452405C20988F7872469E2B46D50FD24BD3A733D3C2280DCB5798834904A39BAD004F78EED1D212B922AB1D12F76ADB51F5E6D99BFF5D239E47E61EA76E45C42389FEF7022A3F33B6044DB74B85AAF71A2B1E64B94C9C2B466C13E94B0EB5515FE1C9602DD9C0ED22EF6A0F99F5A4186EBE5EE58E5858C93C469A51015B03D42F1466FEEEC3F7E06CA1AA2A219CBB27265261BDE4F9E579A20A11AEE930203010001A321301F301D0603551D0E04160414D92A6D7DB4CB521F9C8F44CA8FA7A5123960A13E300D06092A864886F70D01010B05000382010100625C3E61E35281A4B10AD499A8C72023CA6C59512E9989FD2353B926C341F720EE9D0F7F3D69B45D28070F37F2E67B3528E16429BF9D73ADC1DFF68C06AC13130F9E9AC0E71857B13139F0BA7D3E54915FFD2460D3A8D9CA63C7D11E1818A457A47C9CFB834651F989A4D54907B223169531889B1A61120D51332B35B227490FC707A37DF7D58AE696ECD31BD5E52F34FFED9A47097E500BC1517E8989CCB10CB2B5B42266F84766EC49A0D06A25FCD27794888157AD0A283EE9B751366F290D6934EC965304D1765ECE941D79049273031BCD096DE9D8912660DD5692AB6992364AF52CB5E428DF657AA96860473421820DD87082EEA834DB7891656254D0DE | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | DisallowedCertLastSyncTime |
Value: C7C5E3B889EBD601 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | PinRulesLastSyncTime |
Value: E0DDE55B8BEBD601 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | HpkpEncodedCtl |
Value: 3081D906092A864886F70D010702A081CB3081C802010131003081BE06092B0601040182370A01A081B03081AD300C060A2B0601040182370A033C020801D66792A808C448170D3230303733313233333130335A300E060A2B0601040182370A03220500A07430723070060A2B0601040182370A033D0101FF045F305D06092A864886F70D010702A050304E0201013100304506092B0601040182370A01A0383036300C060A2B0601040182370A033D020801D66792A808C448170D3230303733313233333130335A300D0609608648016503040201050031003100 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | LastSyncTime |
Value: 096E1DB989EBD601 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | PinRulesLastError |
Value: E72E000000000000779753B7CCD6D601 | |||
| (PID) Process: | (1448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\02FAF3E291435468607857694DF5E45B68851868 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800000B00000001000000260000005300650063007400690067006F00200028004100640064005400720075007300740029000000090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F000000010000001400000009B9105C5BBA24343CA7F341C624E183F6EE7C1B620000000100000020000000687FA451382278FFF0C8B11F8D43D576671C6EB2BCEAB413FB83D965D06D2FF2140000000100000014000000ADBD987A34B426F7FAC42654EF03BDE024CB541A1D000000010000001000000006F9583C00A763C23FB9E065A3366D5503000000010000001400000002FAF3E291435468607857694DF5E45B6885186819000000010000001000000045ED9BBC5E43D3B9ECD63C060DB78E5C53000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00400000001000000100000001D3554048578B03F42424DBF20730A3F20000000010000003A040000308204363082031EA003020102020101300D06092A864886F70D0101050500306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74301E170D3030303533303130343833385A170D3230303533303130343833385A306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F7430820122300D06092A864886F70D01010105000382010F003082010A0282010100B7F71A33E6F200042D39E04E5BED1FBC6C0FCDB5FA23B6CEDE9B113397A4294C7D939FBD4ABC93ED031AE38FCFE56D505AD69729945A80B0497ADB2E95FDB8CABF37382D1E3E9141AD7056C7F04F3FE8329E74CAC89054E9C65F0F789D9A403C0EAC61AA5E148F9E87A16A50DCD79A4EAF05B3A671949C71B350600AC7139D38078602A8E9A869261890AB4CB04F23AB3A4F84D8DFCE9FE1696FBBD742D76B44E4C7ADEE6D415F725A710837B37965A459A09437F7002F0DC29272DAD03872DB14A845C45D2A7DB7B4D6C4EEACCD1344B7C92BDD430025FA61B9696A582311B7A7338F567559F5CD29D746B70A2B65B6D3426F15B2B87BFBEFE95D53D5345A270203010001A381DC3081D9301D0603551D0E04160414ADBD987A34B426F7FAC42654EF03BDE024CB541A300B0603551D0F040403020106300F0603551D130101FF040530030101FF3081990603551D2304819130818E8014ADBD987A34B426F7FAC42654EF03BDE024CB541AA173A471306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74820101300D06092A864886F70D01010505000382010100B09BE08525C2D623E20F9606929D41989CD9847981D91E5B14072336658FB0D877BBAC416C47608351B0F9323DE7FCF62613C78016A5BF5AFC87CF787989219AE24C070A8635BCF2DE51C4D296B7DC7E4EEE70FD1C39EB0C0251142D8EBD16E0C1DF4675E724ADECF442B48593701067BA9D06354A18D32B7ACC5142A17A63D1E6BBA1C52BC236BE130DE6BD637E797BA7090D40AB6ADD8F8AC3F6F68C1A420551D445F59FA76221681520433C99E77CBD24D8A9911773883F561B313818B4710F9ACDC80E9E8E2E1BE18C9883CB1F31F1444CC604734976600FC7F8BD17806B2EE9CC4C0E5A9A790F200A2ED59E63261E559294D882175A7BD0BCC78F4E8604 | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 848 | CertTree.tmp | C:\Temp\CertTree\is-O1BM3.tmp | — | |
MD5:— | SHA256:— | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\is-0VLVR.tmp | — | |
MD5:— | SHA256:— | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\is-MSBUS.tmp | — | |
MD5:— | SHA256:— | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\is-6RE19.tmp | — | |
MD5:— | SHA256:— | |||
| 3188 | _iu14D2N.tmp | C:\temp\Certtree\unins000.dat | — | |
MD5:— | SHA256:— | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\Certtree.bat | text | |
MD5:822B021D399078FB9870FF72C44613E2 | SHA256:C44009CB3B7586424F3D1E17785F50773735D89ABC3240846C69593E91EF70C6 | |||
| 2776 | CertTree.exe | C:\Users\admin\AppData\Local\Temp\is-1D0I4.tmp\CertTree.tmp | executable | |
MD5:4C4AB71E8C28BA865E6A01DDA40FCA7E | SHA256:CDF66385C6FF89C3B48AFDA7641E1818AD3A2F306BFA40DE09AC7A11C417245F | |||
| 2452 | unins000.exe | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | executable | |
MD5:960B9936F7780D8E43895ABCF986AC3F | SHA256:5EA8D503AE924CEDCEA6BB85EA12933987ACA56751E157670B403C5ED12407C0 | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\unins000.exe | executable | |
MD5:960B9936F7780D8E43895ABCF986AC3F | SHA256:5EA8D503AE924CEDCEA6BB85EA12933987ACA56751E157670B403C5ED12407C0 | |||
| 848 | CertTree.tmp | C:\Temp\CertTree\unins000.dat | dat | |
MD5:F26E2041471F7BE452BBBE276CA1B05A | SHA256:2FC023EB5C40A46B6228CFBE7519C537CF0E94EFE54B876D9799D9F7465CA3CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report