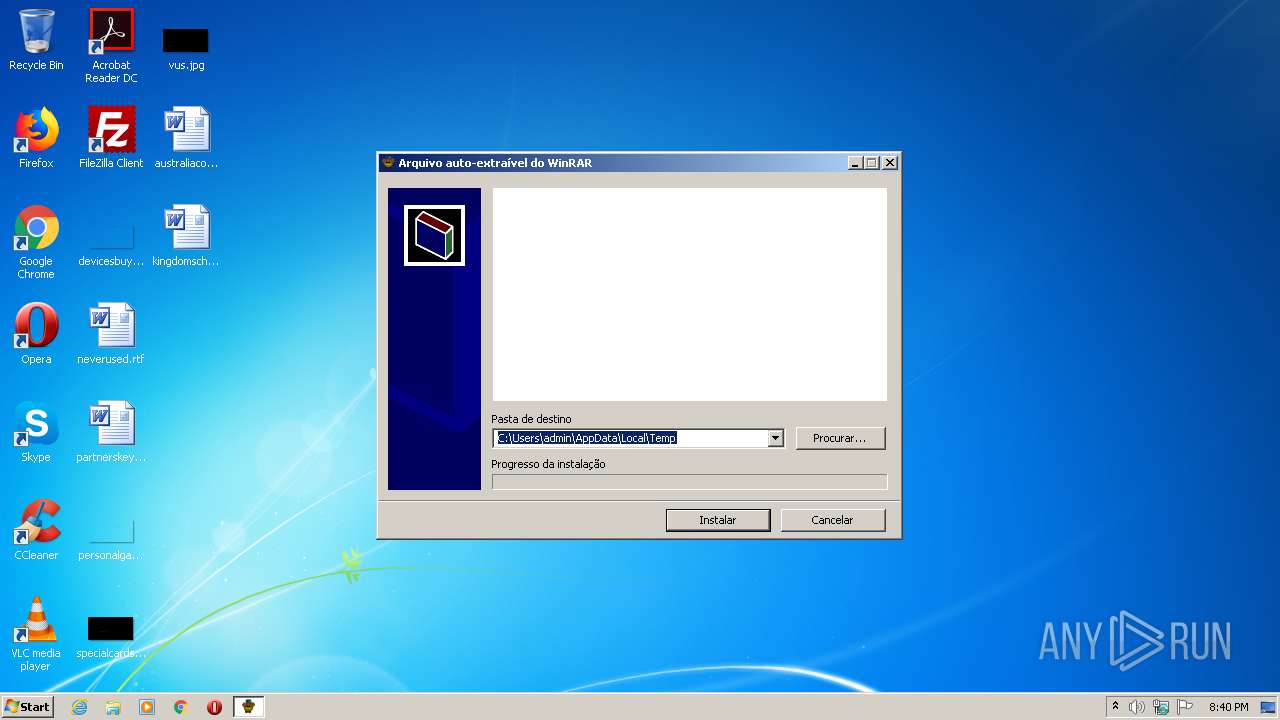
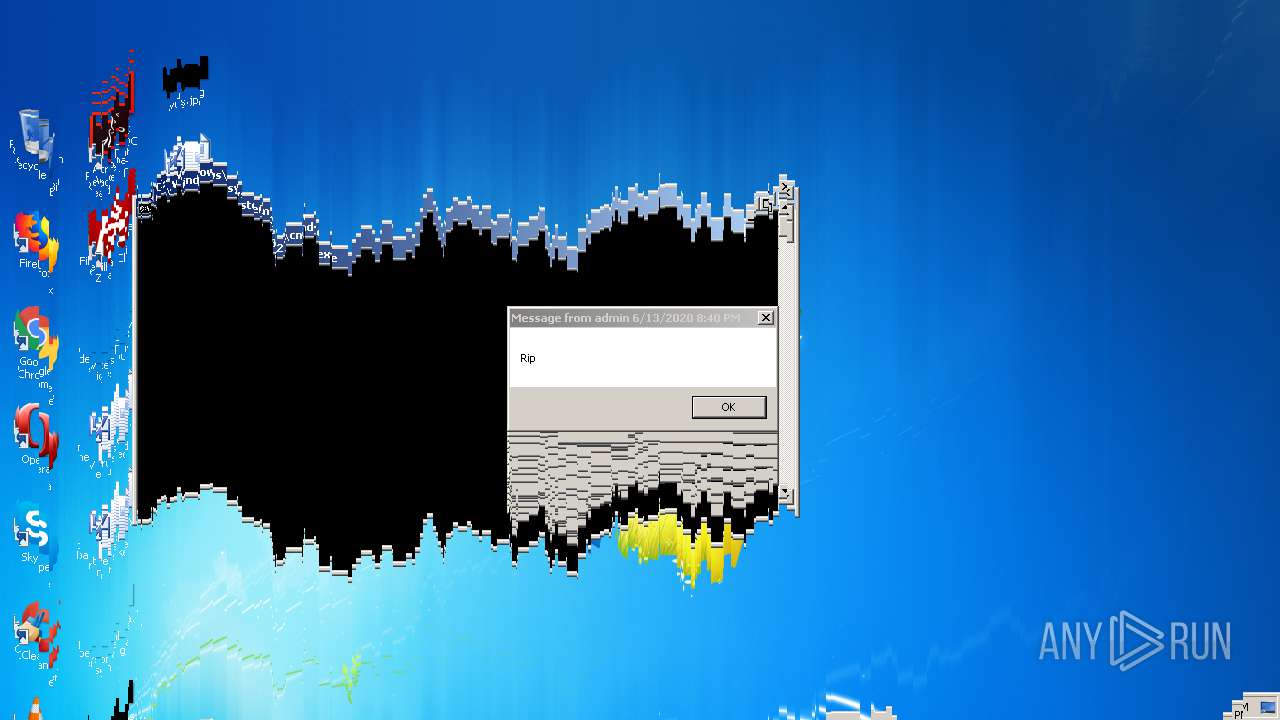
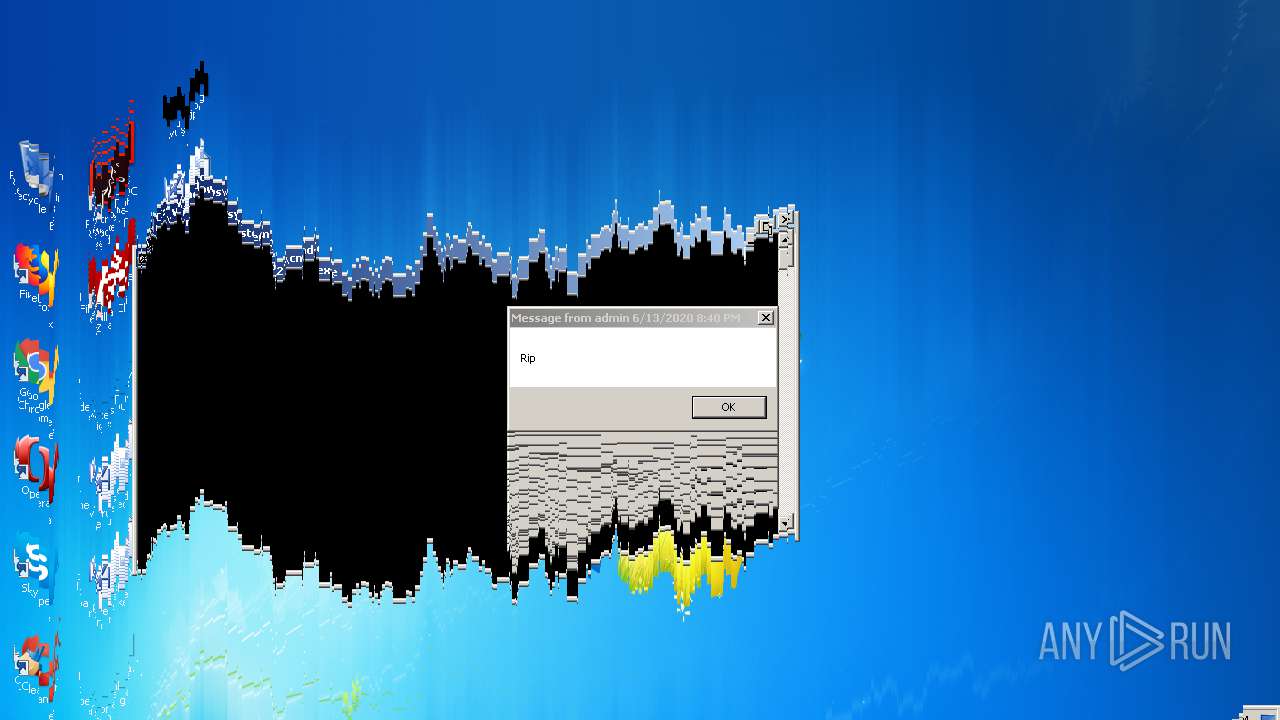
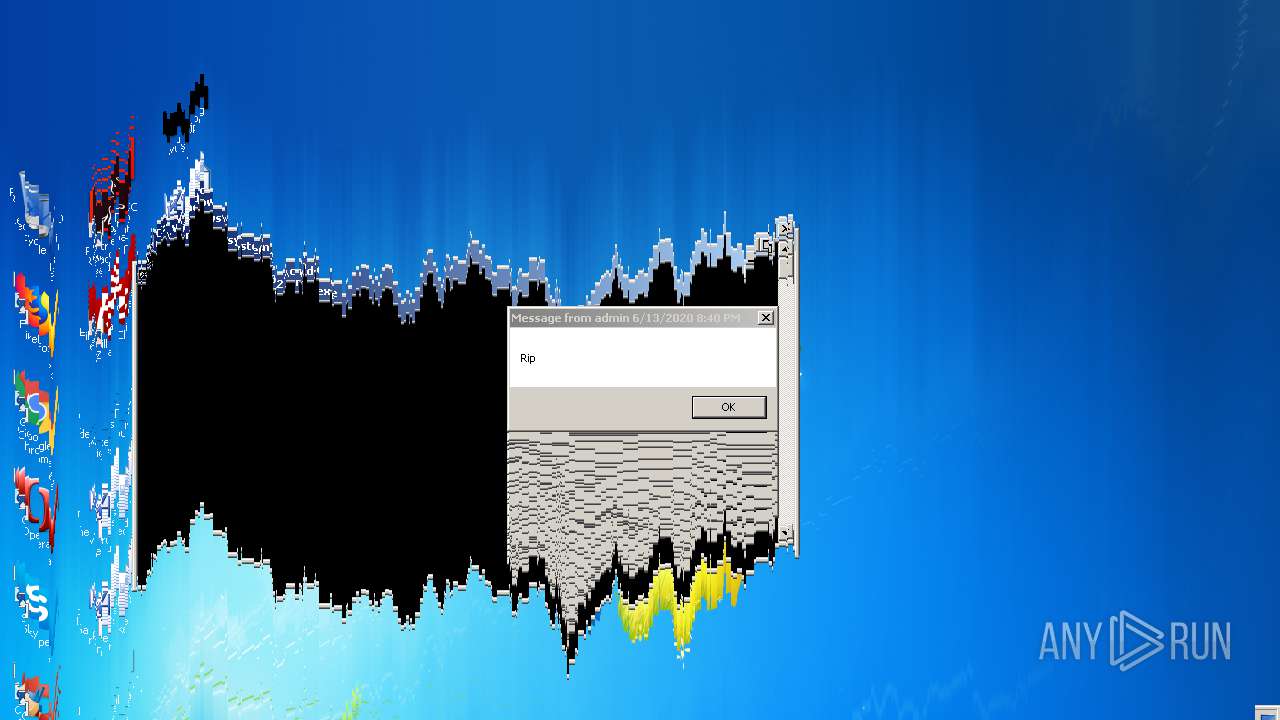
| File name: | Fnaf 1-4 JumpScare.exe |
| Full analysis: | https://app.any.run/tasks/c290e648-2453-458d-b24b-853e7a7c9dd1 |
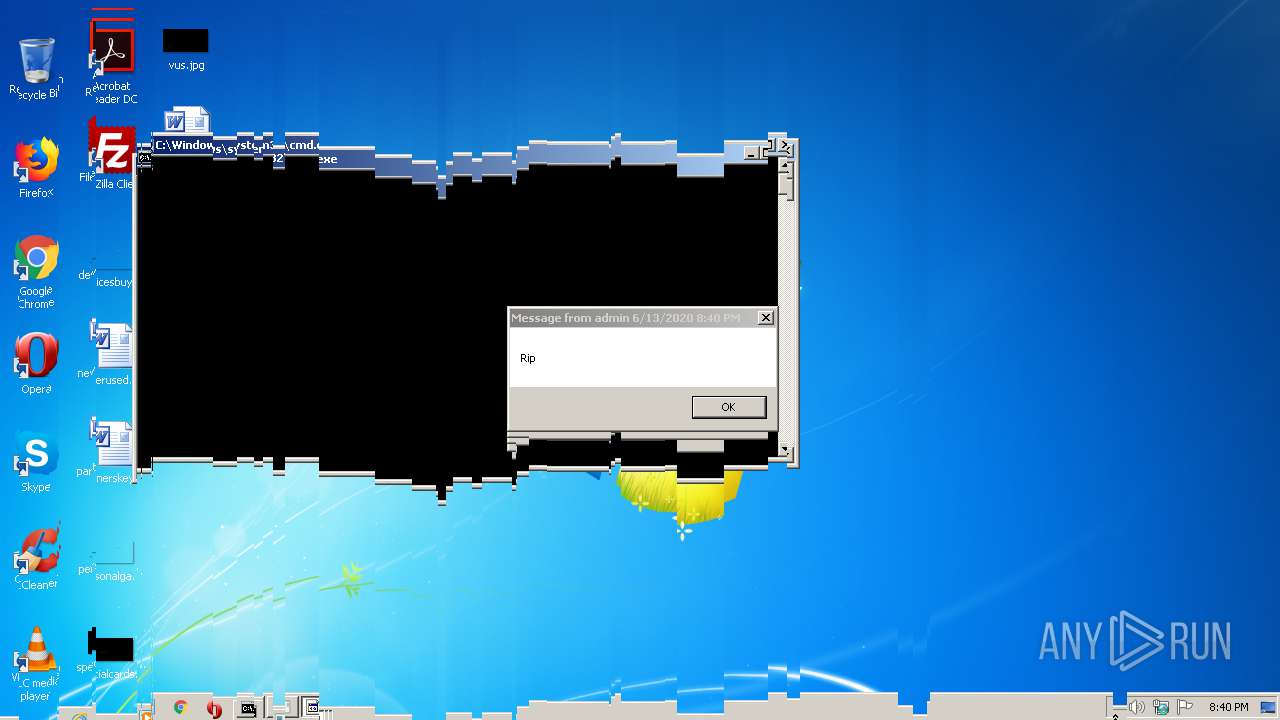
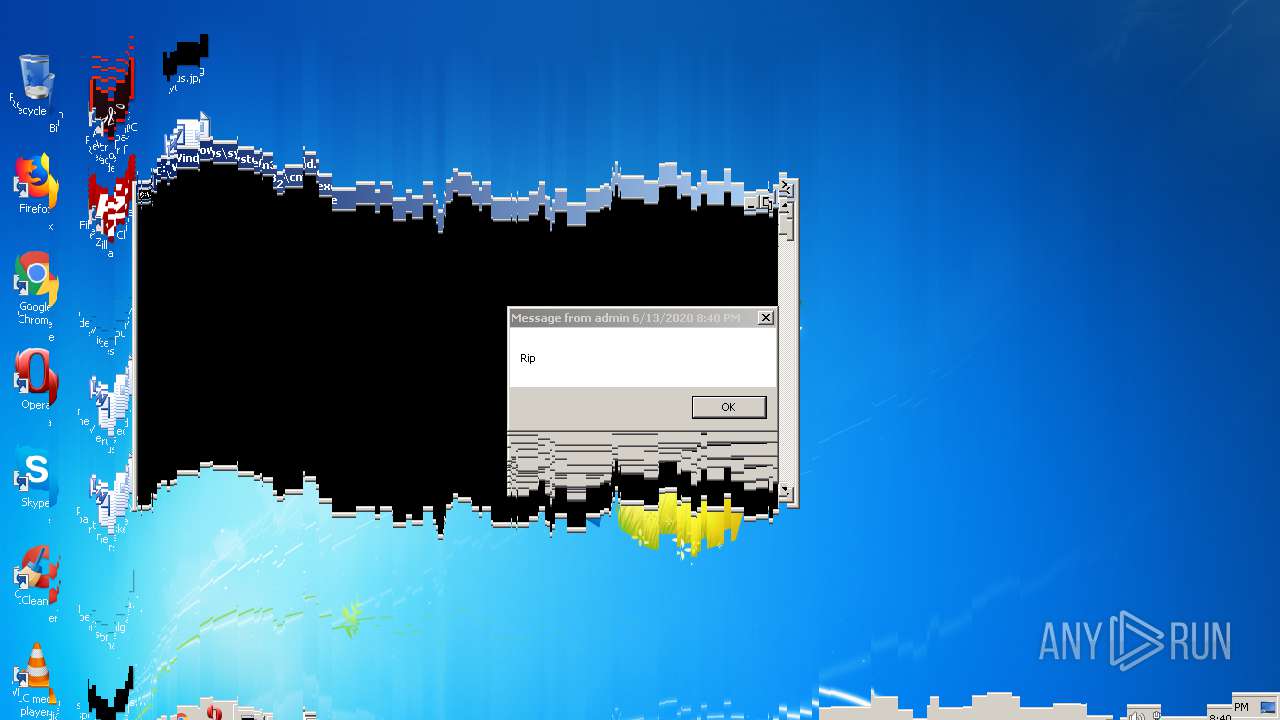
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2020, 19:40:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8ED5D7D98F10999A4CD45136FE462A8E |
| SHA1: | 139276A880FE262ADA73ECCE04844456CDA436F4 |
| SHA256: | 07D352B9F74CDD54AD567E5B54A9825FDCB747CC33D7EB1CDF8F2D920812D490 |
| SSDEEP: | 49152:bpzt0t2pm1jiA1te00w33+4x6w/jrCoY3a4ucS6wl/8L2EtvvKlKqAPofeFyozbY:b5Rm1jiKz0BE6oSuB6qY/VKJfevbY |
MALICIOUS
Application was dropped or rewritten from another process
- melter.exe (PID: 3416)
- melter.exe (PID: 3820)
- melter.exe (PID: 2040)
- melter.exe (PID: 2316)
SUSPICIOUS
Executable content was dropped or overwritten
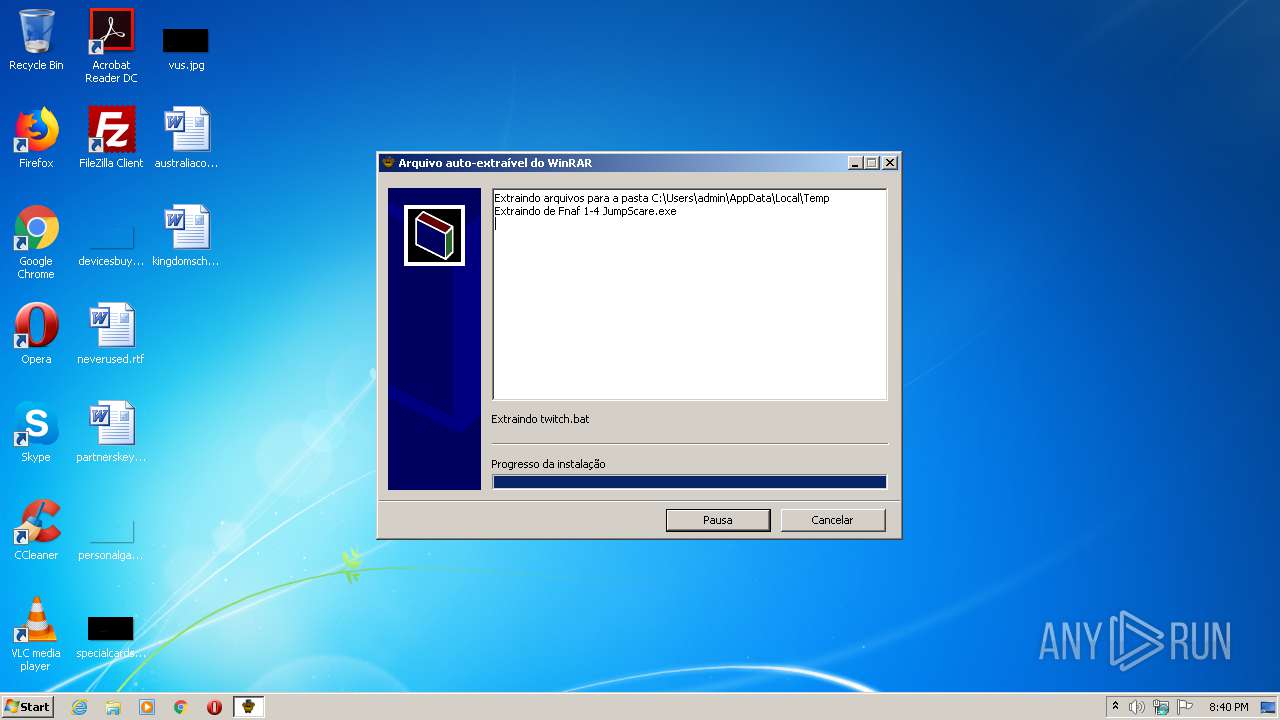
- Fnaf 1-4 JumpScare.exe (PID: 1488)
Reads internet explorer settings
- Fnaf 1-4 JumpScare.exe (PID: 1488)
Executes scripts
- cmd.exe (PID: 4024)
Reads Internet Cache Settings
- WScript.exe (PID: 2060)
- Fnaf 1-4 JumpScare.exe (PID: 1488)
Starts CMD.EXE for commands execution
- Fnaf 1-4 JumpScare.exe (PID: 1488)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4024)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:03 12:34:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 168960 |
| InitializedDataSize: | 72192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e35b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2016 11:34:21 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Jan-2016 11:34:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00029324 | 0x00029400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72276 |
.rdata | 0x0002B000 | 0x000054E3 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16456 |
.data | 0x00031000 | 0x000215E8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.578 |
.rsrc | 0x00053000 | 0x0000AA4C | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53148 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.45277 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.33455 | 488 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.06923 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.89852 | 3752 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 5.28997 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
60
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
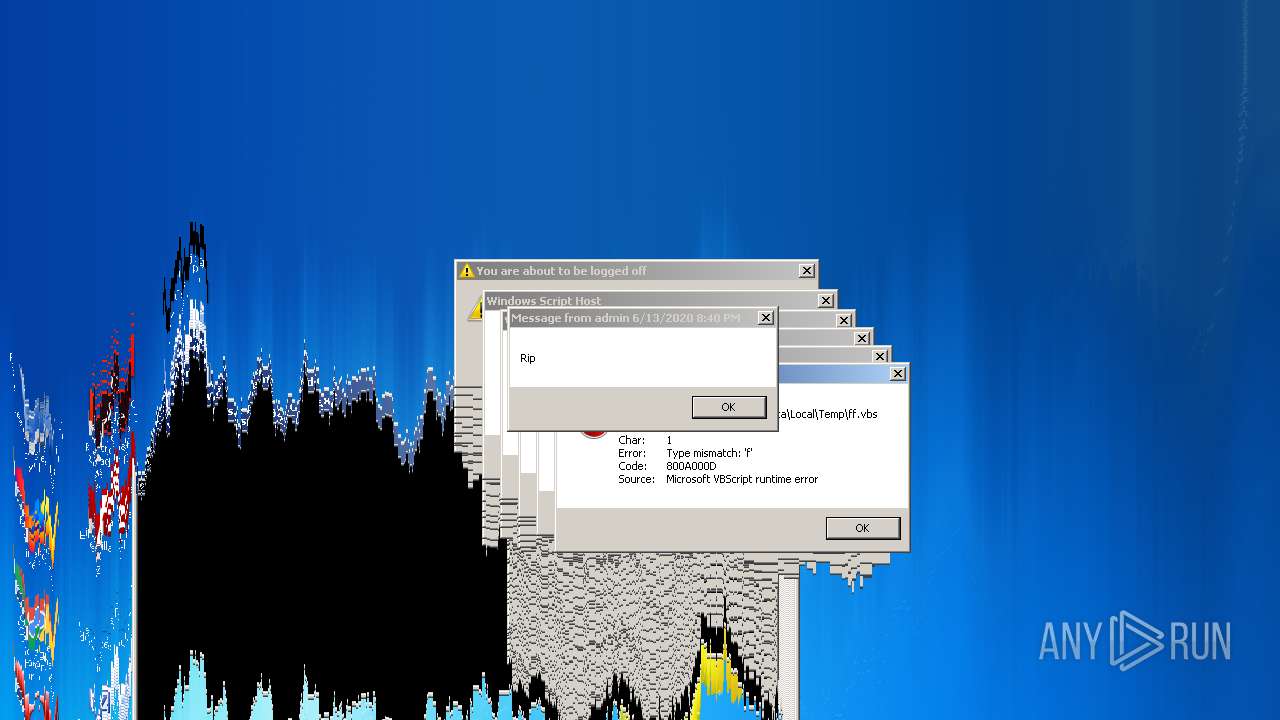
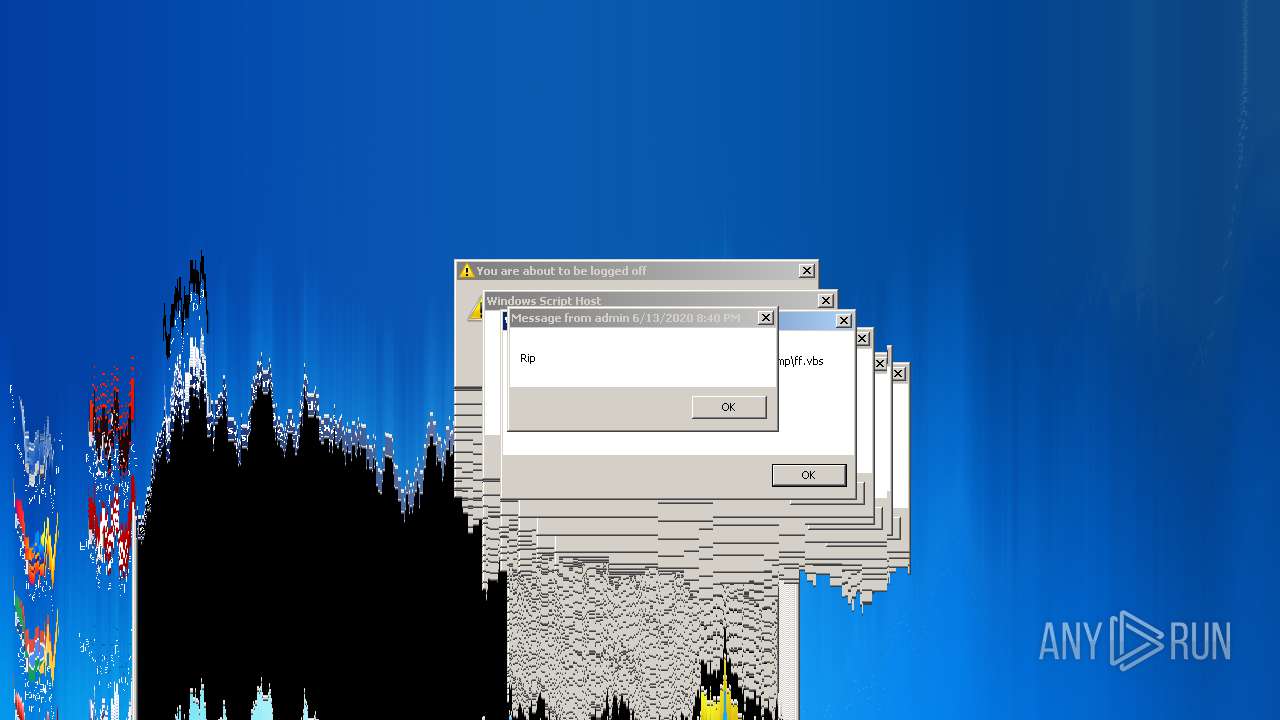
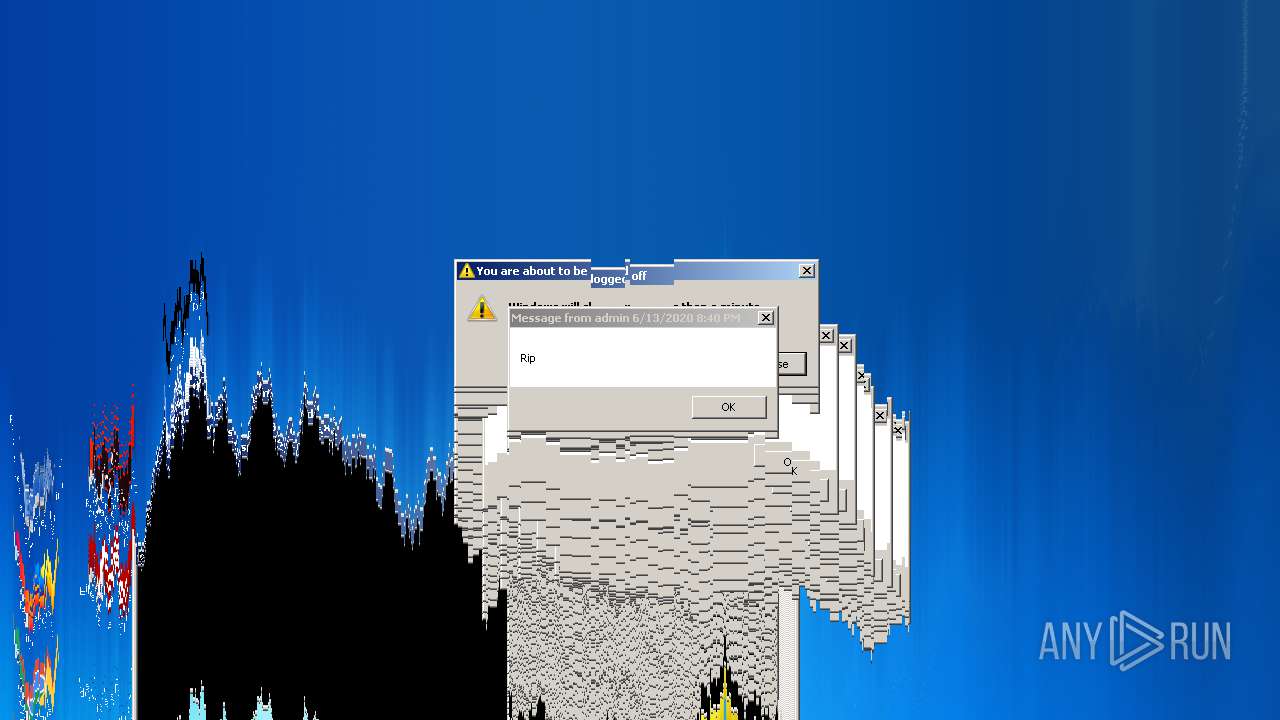
| 392 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\ff.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1232 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\AppData\Local\Temp\Fnaf 1-4 JumpScare.exe" | C:\Users\admin\AppData\Local\Temp\Fnaf 1-4 JumpScare.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1640 | shutdown -r -t 5 | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1780 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1992 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | melter.exe | C:\Users\admin\AppData\Local\Temp\melter.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2060 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\GG.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2096 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 3221225794 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | timeout /t 5 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 285
Read events
1 237
Write events
48
Delete events
0
Modification events
| (PID) Process: | (1488) Fnaf 1-4 JumpScare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1488) Fnaf 1-4 JumpScare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1488) Fnaf 1-4 JumpScare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1488) Fnaf 1-4 JumpScare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1488) Fnaf 1-4 JumpScare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4024) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4024) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2060) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {C120DE80-FDE4-49F5-A713-E902EF062B8A} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 01000000000000005D7C1787BA41D601 | |||
| (PID) Process: | (2060) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverSetThreadExecutionState |
Value: 2147483648 | |||
| (PID) Process: | (2060) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverState |
Value: 4 | |||
Executable files
1
Suspicious files
1
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | Fnaf 1-4 JumpScare.exe | C:\Users\admin\AppData\Local\Temp\ff.vbs | binary | |
MD5:8FA14CDD754F91CC6554C9E71929CCE7 | SHA256:252F10C83610EBCA1A059C0BAE8255EBA2F95BE4D1D7BCFA89D7248A82D9F111 | |||
| 1488 | Fnaf 1-4 JumpScare.exe | C:\Users\admin\AppData\Local\Temp\GG.vbs | text | |
MD5:846731532273AAFC53DB5807BDC63A0B | SHA256:50F1795E51960B5643D8CD01F1D1D38BDCF1B98CAB2872B2403850282A6A797C | |||
| 1488 | Fnaf 1-4 JumpScare.exe | C:\Users\admin\AppData\Local\Temp\twitch.bat | text | |
MD5:A1BD5600DB945C1555EBA336C6FBF4C9 | SHA256:11905942CDC817F6CEE251CE795CE589F24BAC69A301769230E5A7DE05469150 | |||
| 1488 | Fnaf 1-4 JumpScare.exe | C:\Users\admin\AppData\Local\Temp\earthquake.mp3 | mp3 | |
MD5:B0E8D9699DB13F95BDC8279AB8FA15C6 | SHA256:D9BF219A269C57D17FE7122FE2FB973D868A6E673ECE0484416A124A8ED4008F | |||
| 1488 | Fnaf 1-4 JumpScare.exe | C:\Users\admin\AppData\Local\Temp\melter.exe | executable | |
MD5:D9BAAC374CC96E41C9F86C669E53F61C | SHA256:A1D883577BCB6C4F9DE47B06FE97C370C09BDDFFB6569B6CF93576371BDBC412 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report