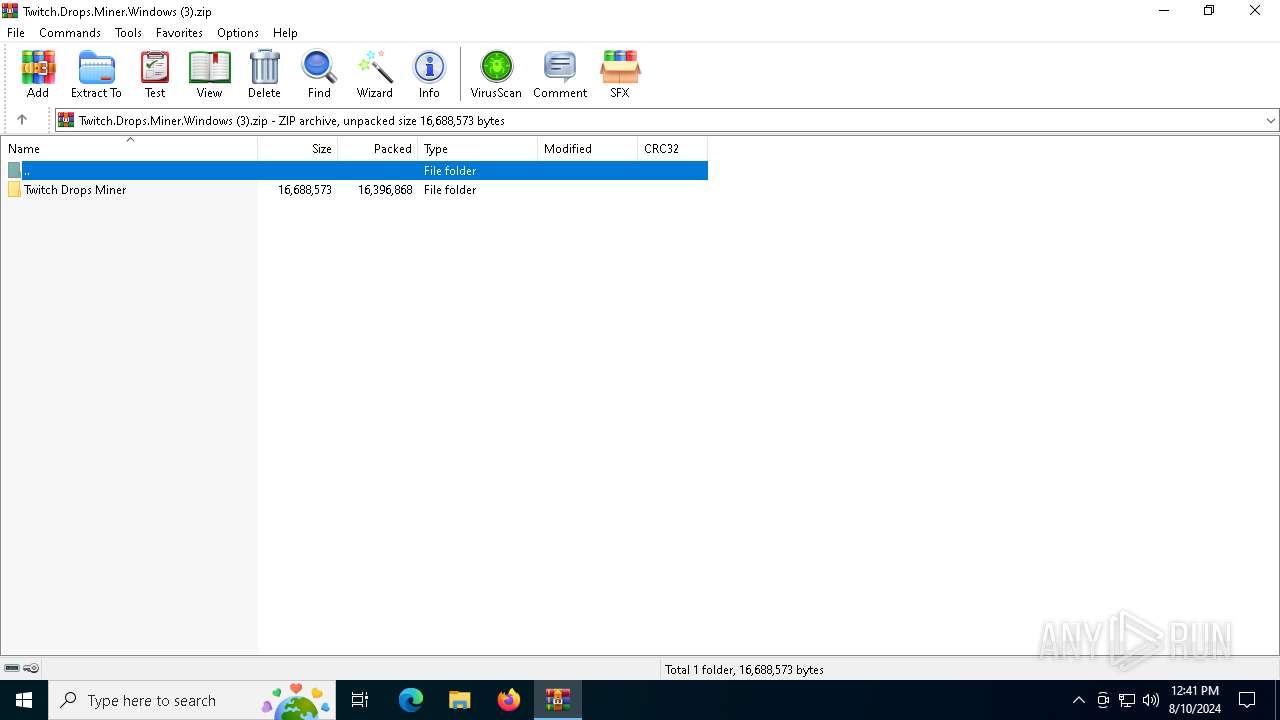
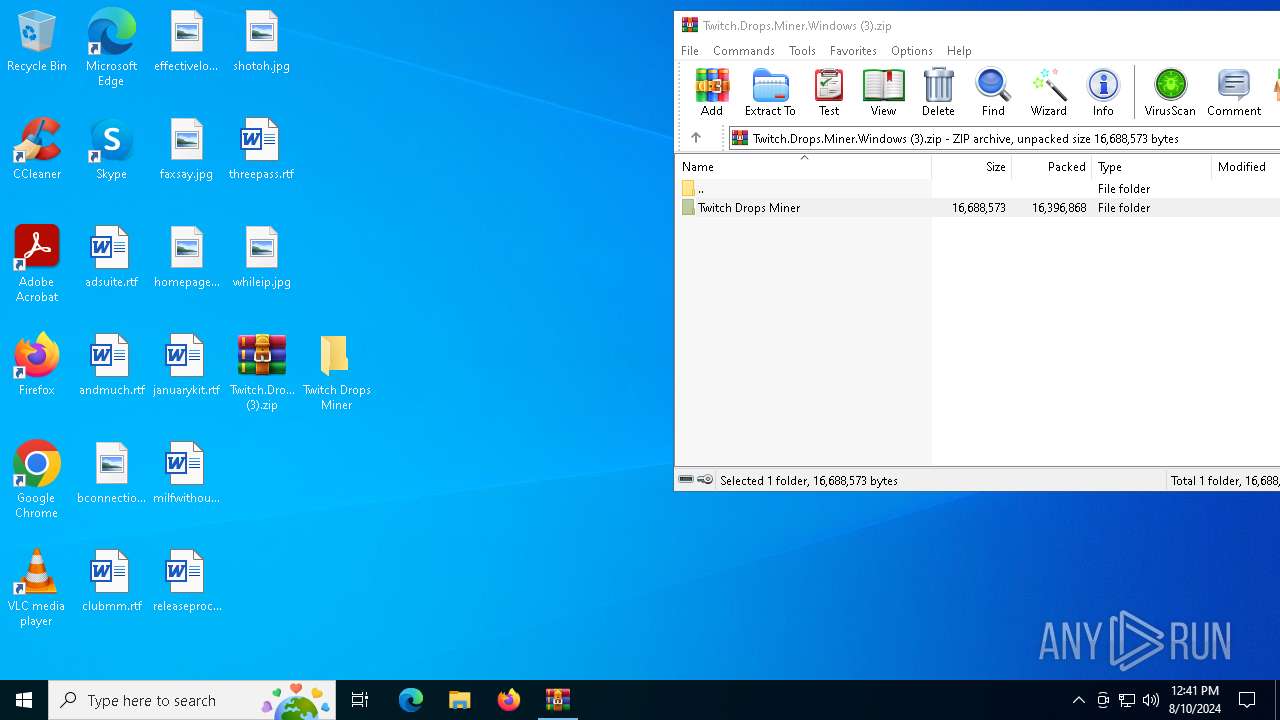
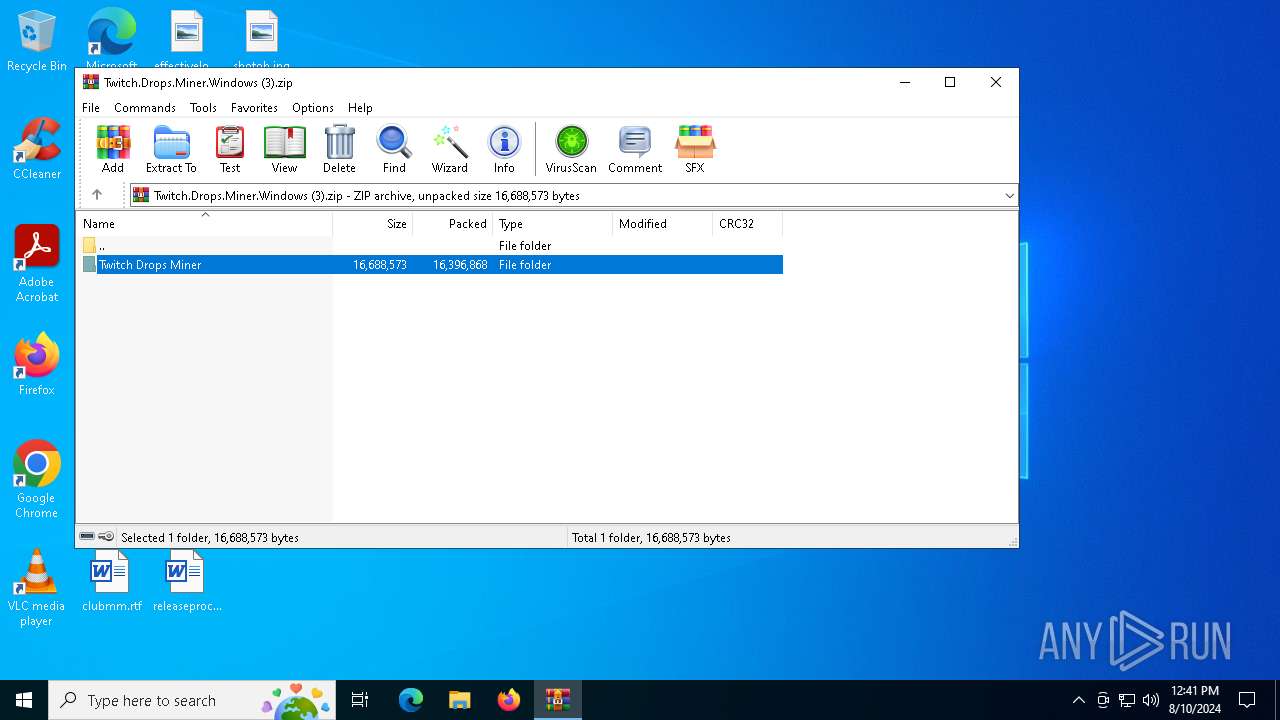
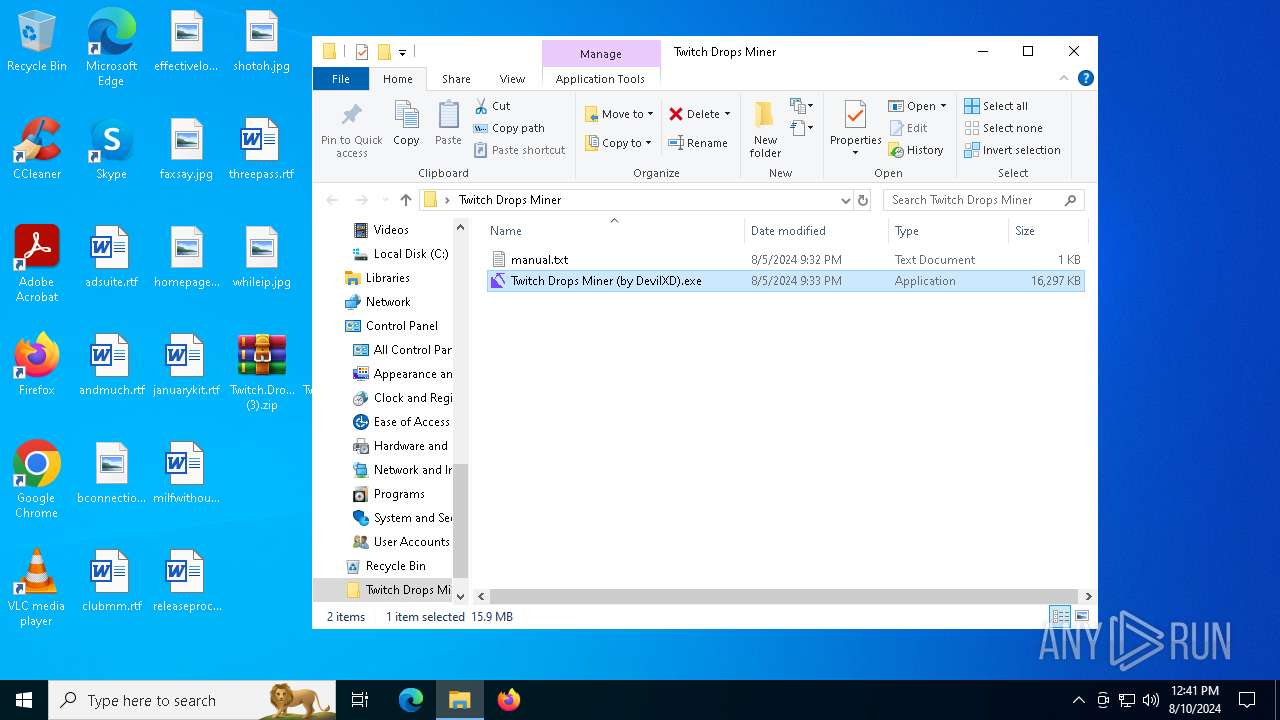
| File name: | Twitch.Drops.Miner.Windows (3).zip |
| Full analysis: | https://app.any.run/tasks/a340a7ff-9f1a-417a-85cd-80fa7ccbba9e |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2024, 12:41:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 4FE451C38EE129914E779011B404920B |
| SHA1: | 5775EFFF3A251DE16DCD09F427AA216F21FC9E91 |
| SHA256: | 07CE567873D3E27BF0B5747D4C60C22C9F09687BB520ADB3217DD66ED83C7594 |
| SSDEEP: | 98304:9ZU/d3QA4/J20UoAM/zW+VfBFrsL1uICylSCzGySNBe6VeDMRn7Q0yc1nAdN2l/l:oGdlYBLHH3yKTVwv6Pxc |
MALICIOUS
No malicious indicators.SUSPICIOUS
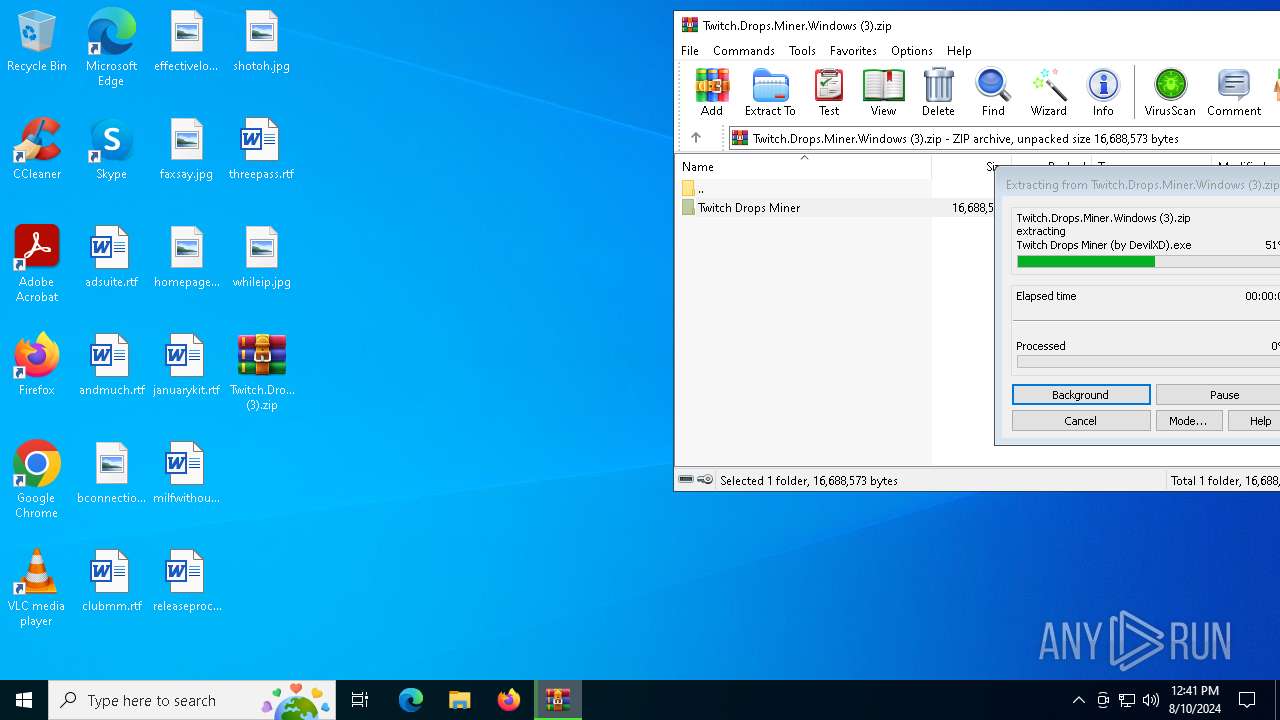
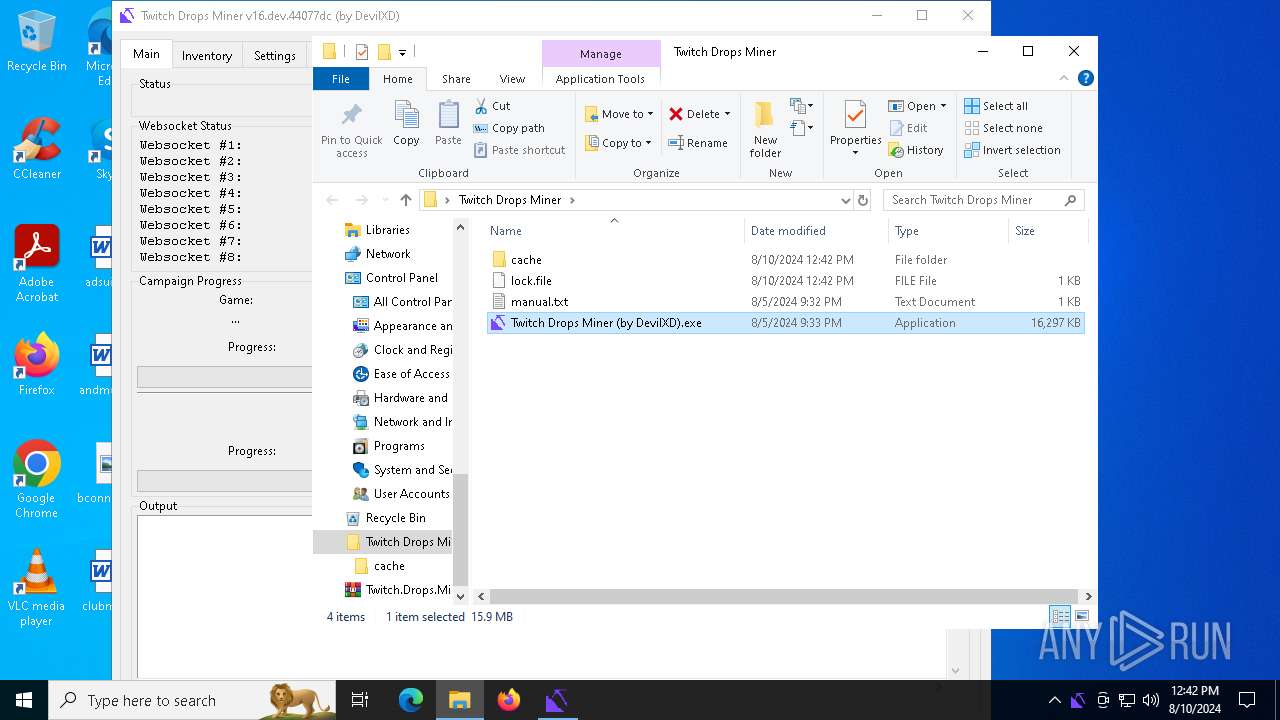
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6608)
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Process drops legitimate windows executable
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
The process drops C-runtime libraries
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Executable content was dropped or overwritten
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Process drops python dynamic module
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Application launched itself
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
Starts CMD.EXE for commands execution
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Loads Python modules
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
INFO
Create files in a temporary directory
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6608)
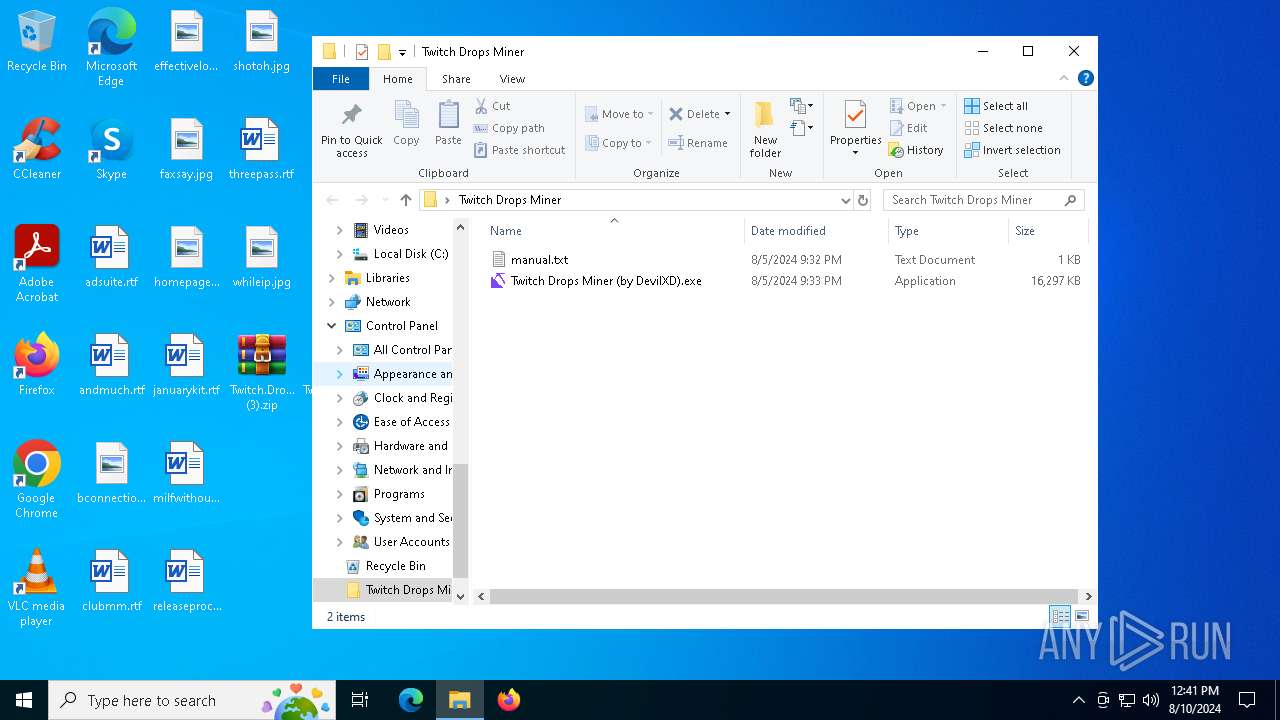
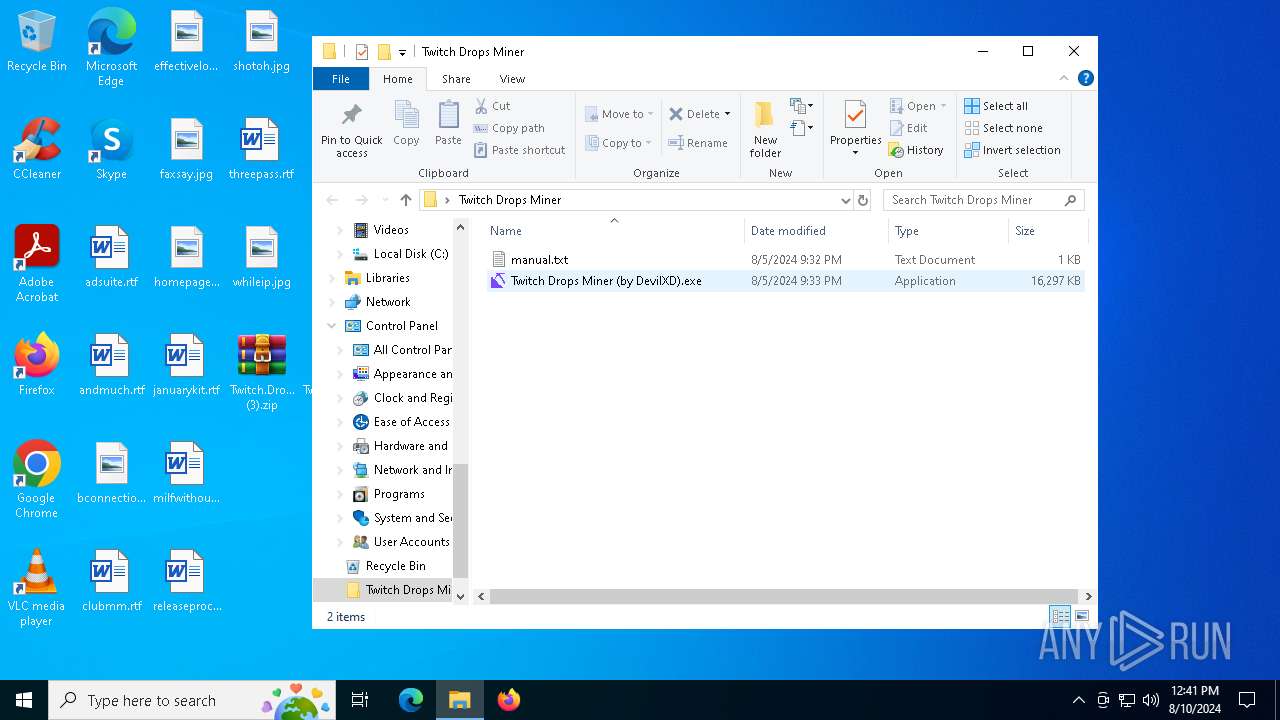
Manual execution by a user
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Reads the computer name
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Checks supported languages
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
PyInstaller has been detected (YARA)
- Twitch Drops Miner (by DevilXD).exe (PID: 6980)
- Twitch Drops Miner (by DevilXD).exe (PID: 3324)
Reads the machine GUID from the registry
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Checks operating system version
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Reads the software policy settings
- Twitch Drops Miner (by DevilXD).exe (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:08:05 21:32:50 |
| ZipCRC: | 0x537e2165 |
| ZipCompressedSize: | 498 |
| ZipUncompressedSize: | 991 |
| ZipFileName: | Twitch Drops Miner/manual.txt |
Total processes
134
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3324 | "C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe" | C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4088 | "C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe" | C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe | Twitch Drops Miner (by DevilXD).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4280 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | Twitch Drops Miner (by DevilXD).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
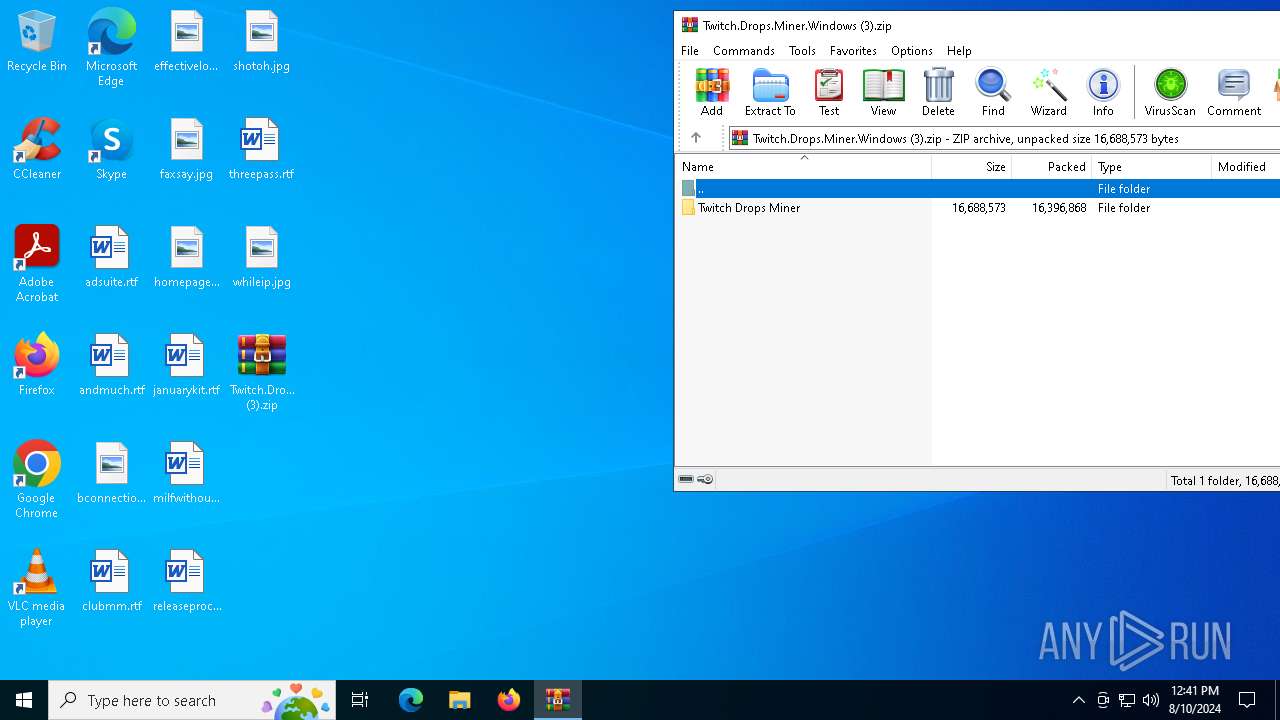
| 6608 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Twitch.Drops.Miner.Windows (3).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6940 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6980 | "C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe" | C:\Users\admin\Desktop\Twitch Drops Miner\Twitch Drops Miner (by DevilXD).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
10 001
Read events
9 982
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Twitch.Drops.Miner.Windows (3).zip | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF4300000043000000030400002C020000 | |||
| (PID) Process: | (6608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
162
Suspicious files
22
Text files
1 743
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_multiprocessing.pyd | executable | |
MD5:A77D9DD8AECE1F211E2949D54D299DD4 | SHA256:07B82738C674E58FEE4B11F259360C062D1DF22220A397434CF3A3771E52729E | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_overlapped.pyd | executable | |
MD5:F491399E85FF21AA74FF571F751C9ACE | SHA256:403B0567609CB2AA5D8FF8C992E10FAE9E3B86D7AA86CA4ACC6044821A49E36B | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_hashlib.pyd | executable | |
MD5:659A5EFA39A45C204ADA71E1660A7226 | SHA256:B16C0CC3BAA67246D8F44138C6105D66538E54D0AFB999F446CAE58AC83EF078 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_asyncio.pyd | executable | |
MD5:4679FB6C4927612A1F13FA3883533F47 | SHA256:A2EA28CA2BE4326A113DA539A081C8A889D55C13AABED755AD27C1738A1D10C1 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\PIL\_webp.cp310-win_amd64.pyd | executable | |
MD5:E96703F62275BA5F281A19F18EEB0A0D | SHA256:DEA85389547C6DFB9787A26F32DF93F9422A741B07AAEFDA750266D1E04A8429 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\VCRUNTIME140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\VCRUNTIME140_1.dll | executable | |
MD5:135359D350F72AD4BF716B764D39E749 | SHA256:34048ABAA070ECC13B318CEA31425F4CA3EDD133D350318AC65259E6058C8B32 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_bz2.pyd | executable | |
MD5:FBA120A94A072459011133DA3A989DB2 | SHA256:055A93C8B127DC840AC40CA70D4B0246AC88C9CDE1EF99267BBE904086E0B7D3 | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_decimal.pyd | executable | |
MD5:7CDC590AC9B4FFA52C8223823B648E5C | SHA256:F281BD8219B4B0655E9C3A5516FE0B36E44C28B0AC9170028DD052CA234C357C | |||
| 6980 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI69802\_lzma.pyd | executable | |
MD5:864B22495372FA4D8B18E1C535962AE2 | SHA256:FC57BD20B6B128AFA5FAAAC1FD0CE783031FAAF39F71B58C9CACF87A16F3325F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
40
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7028 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7104 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5924 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1984 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1116 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1984 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5924 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |