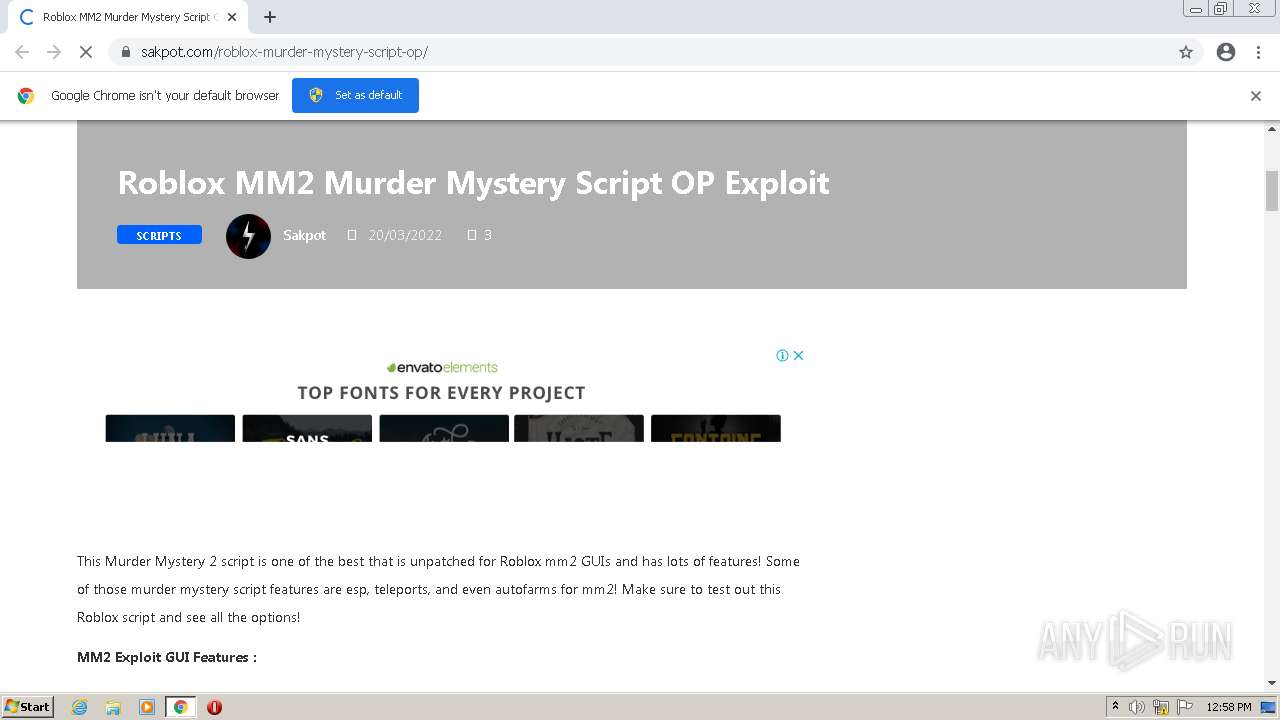
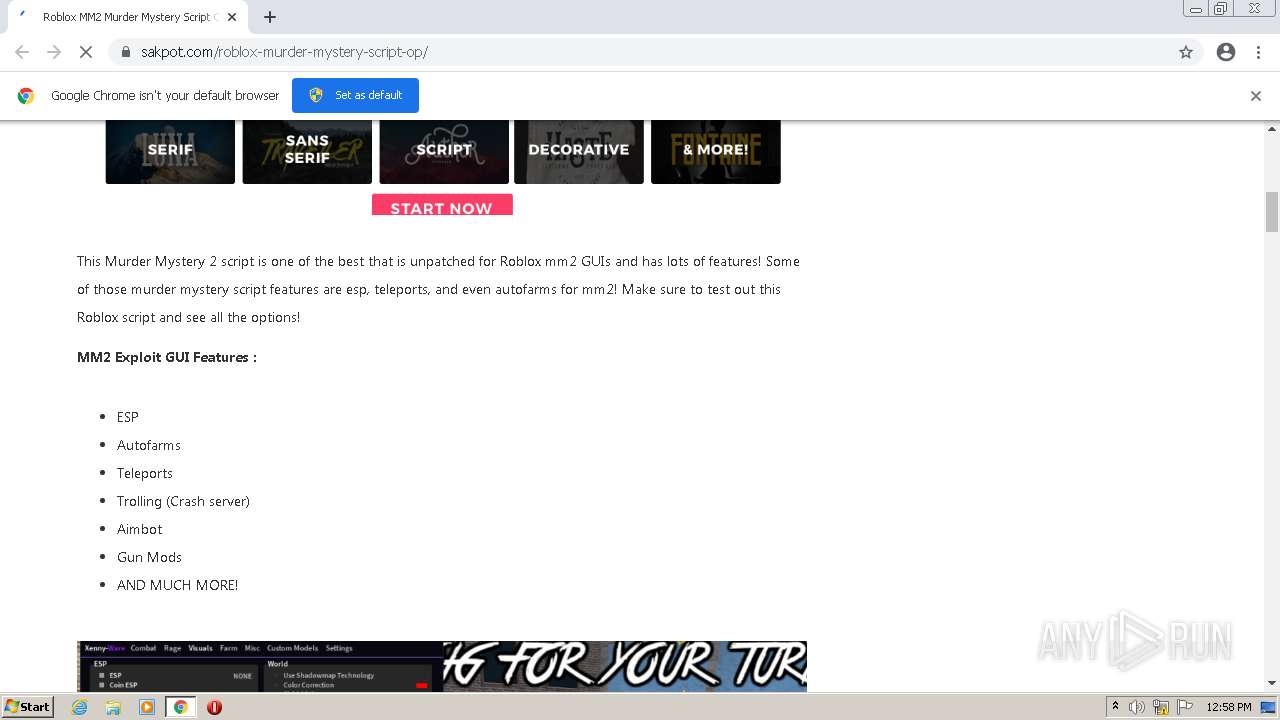
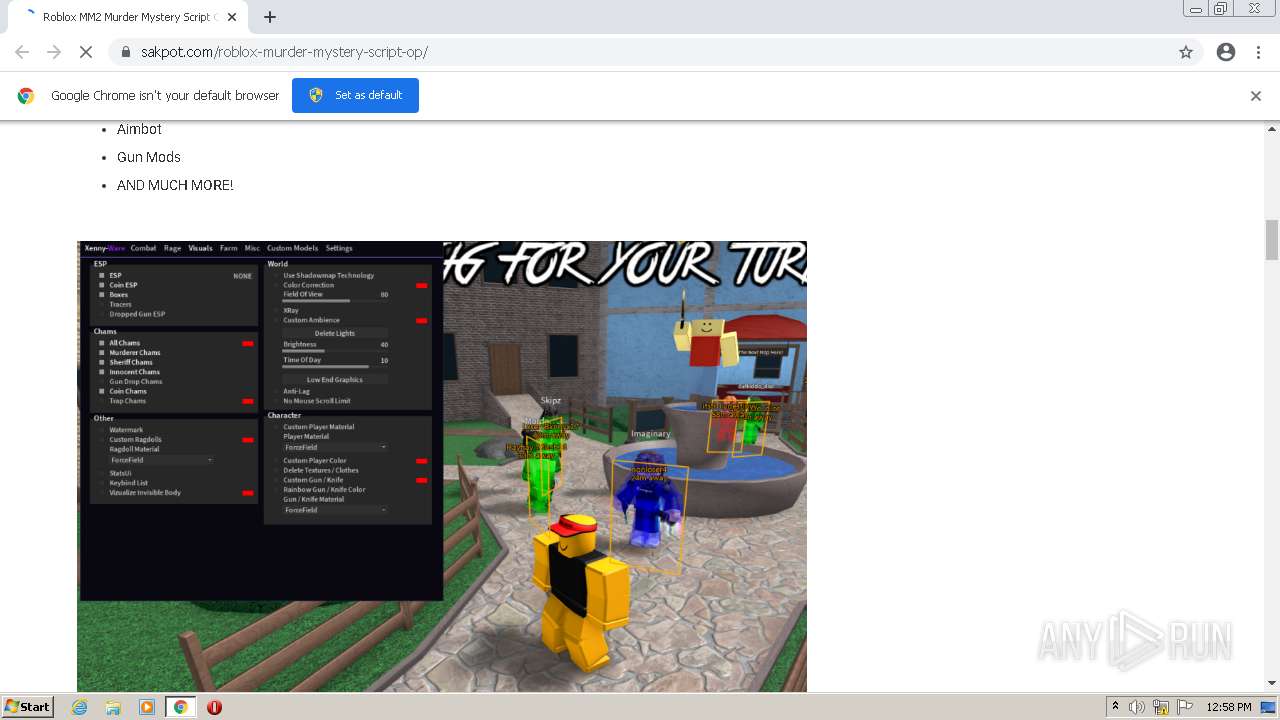
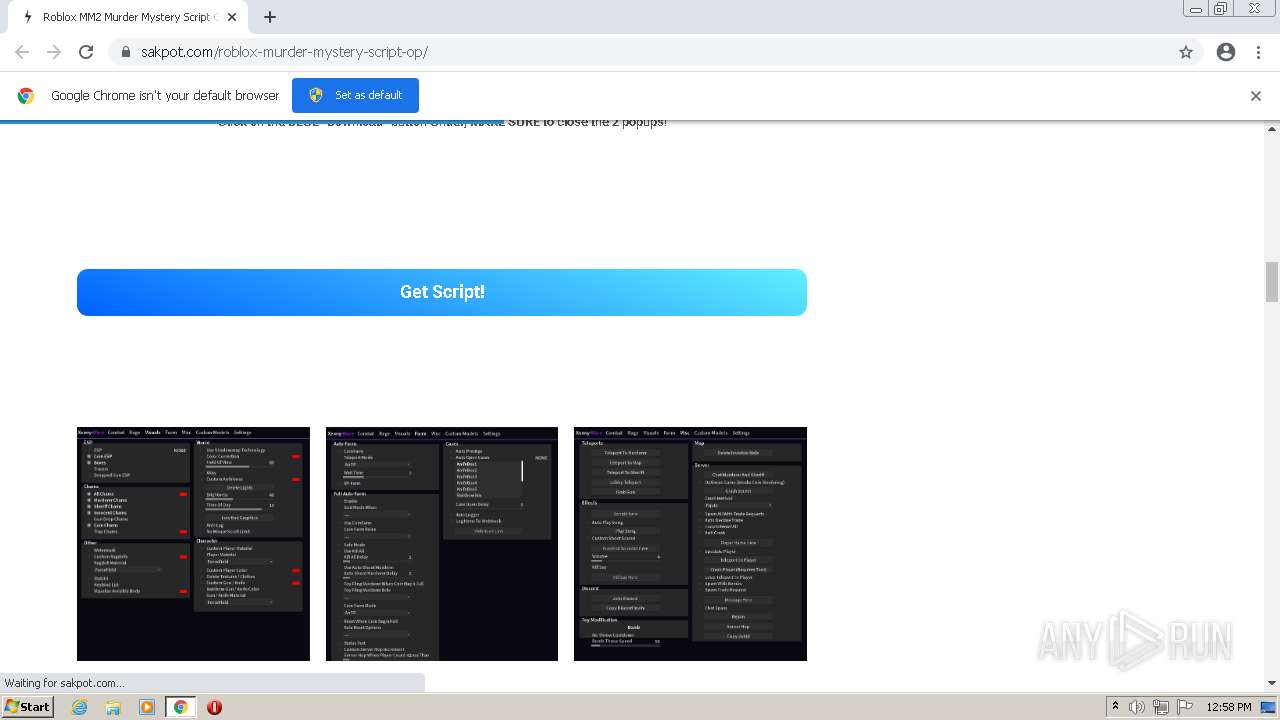
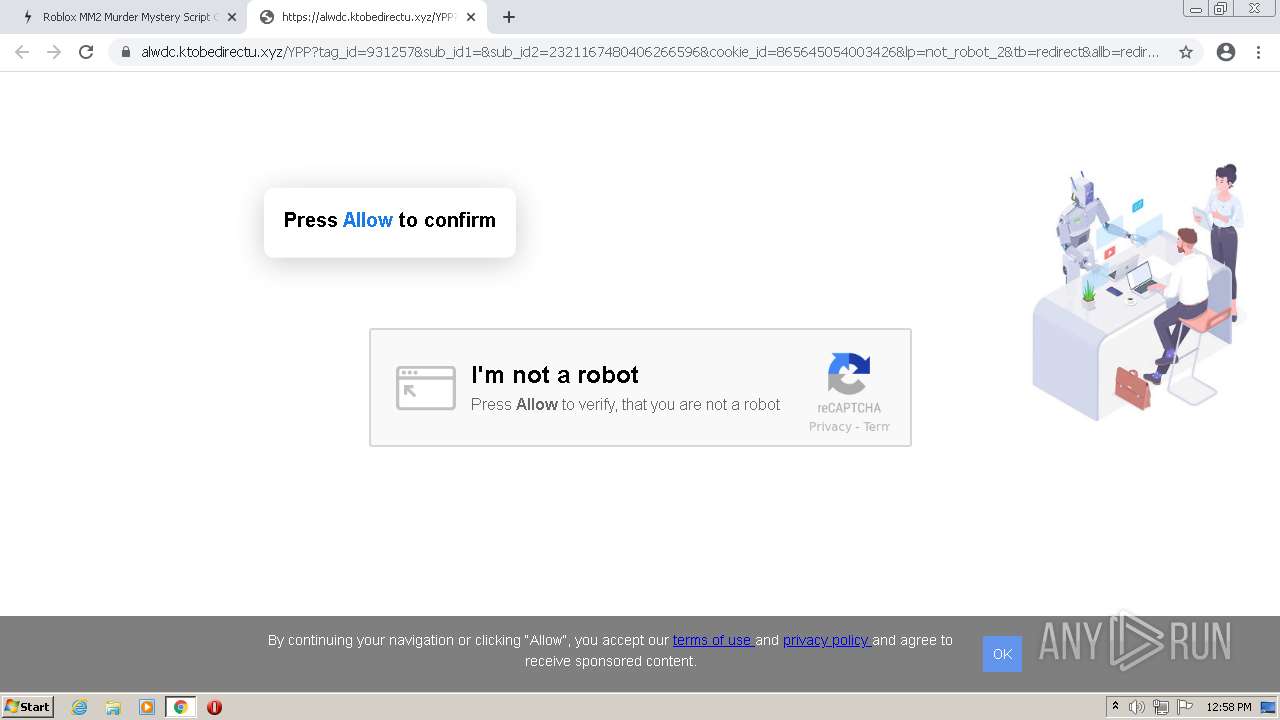
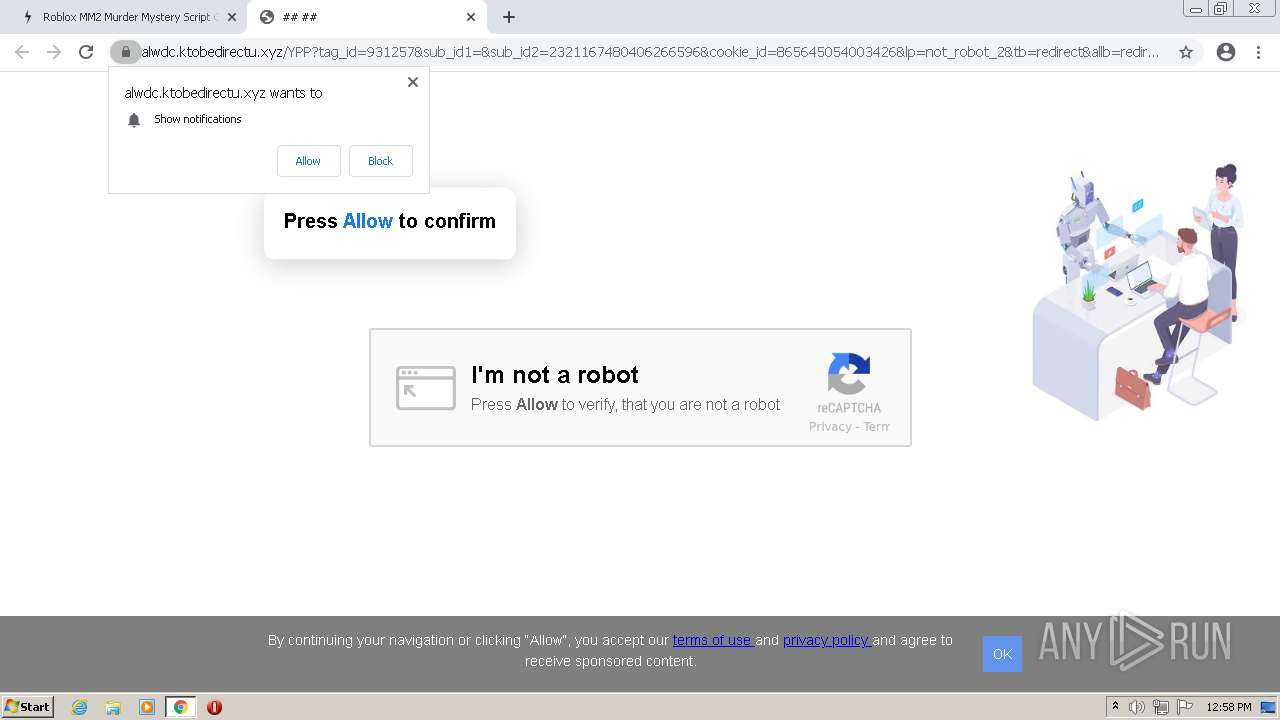
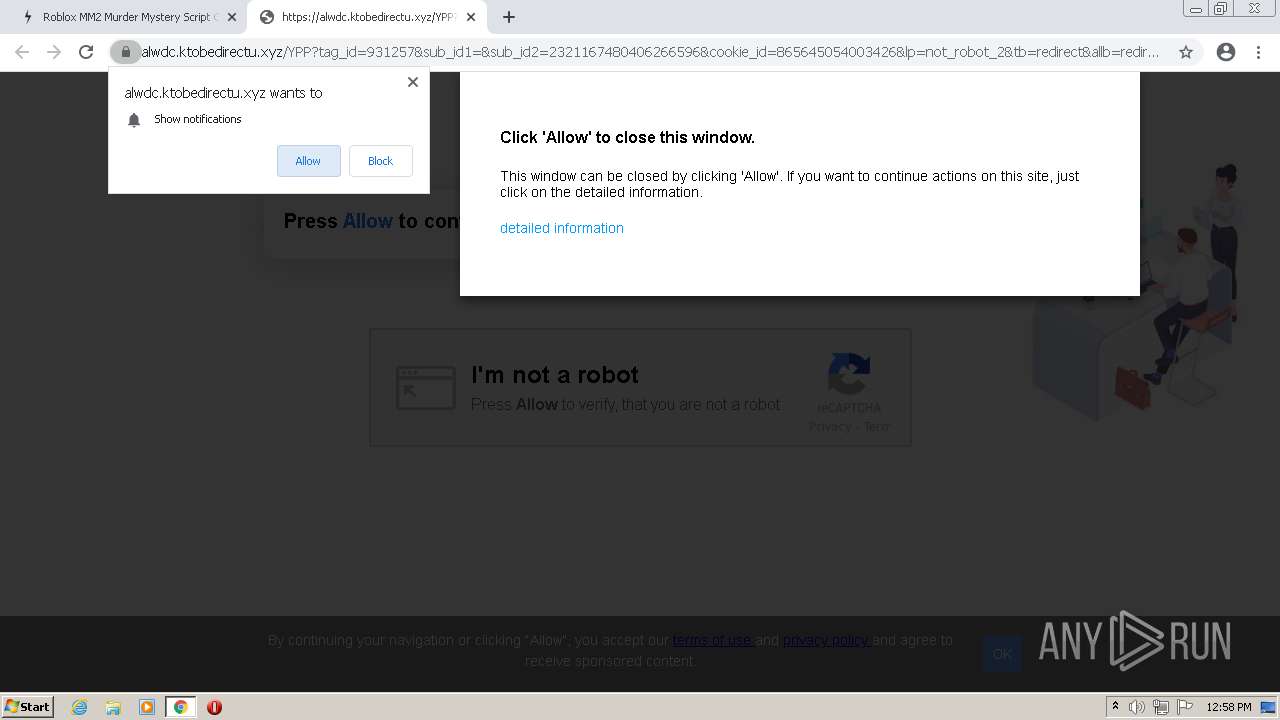
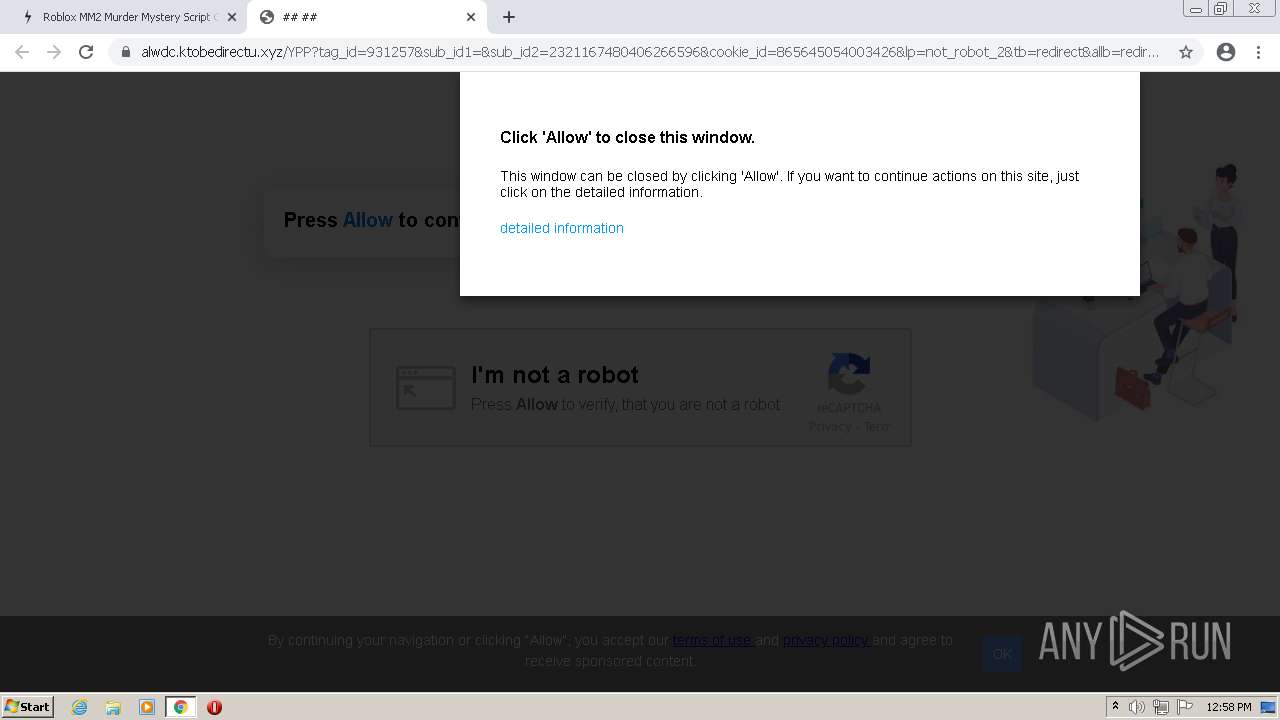
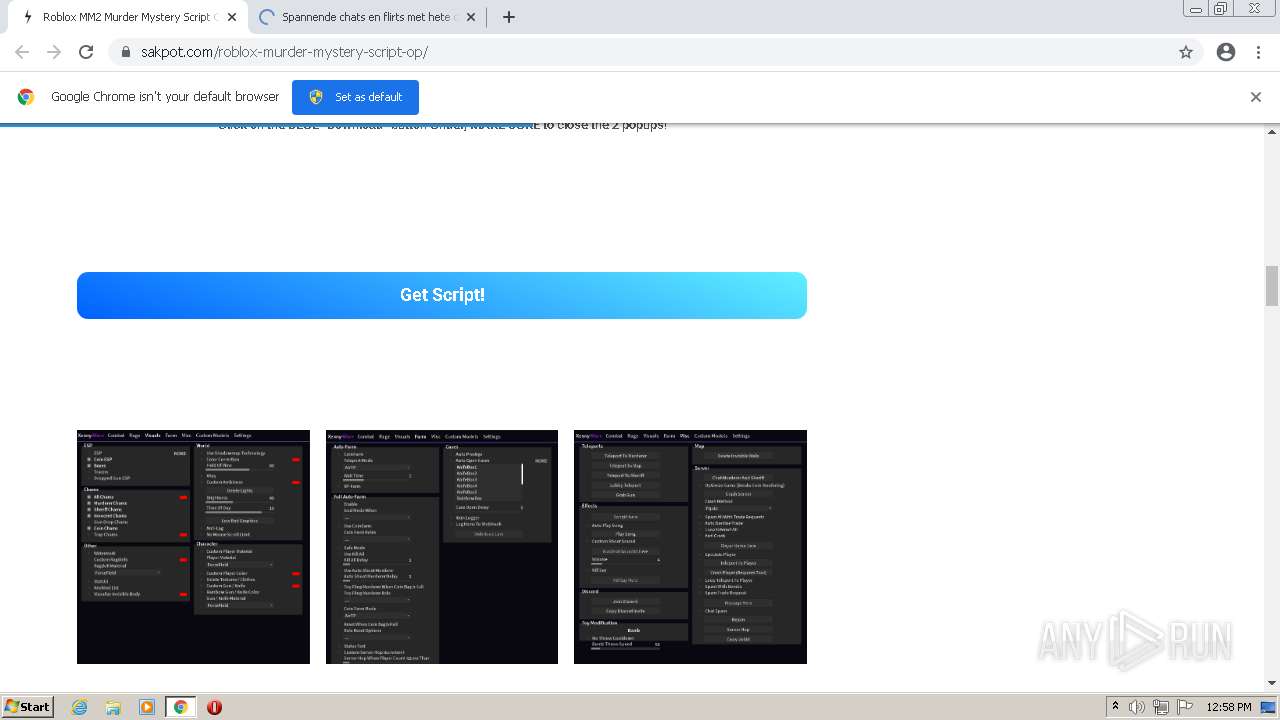
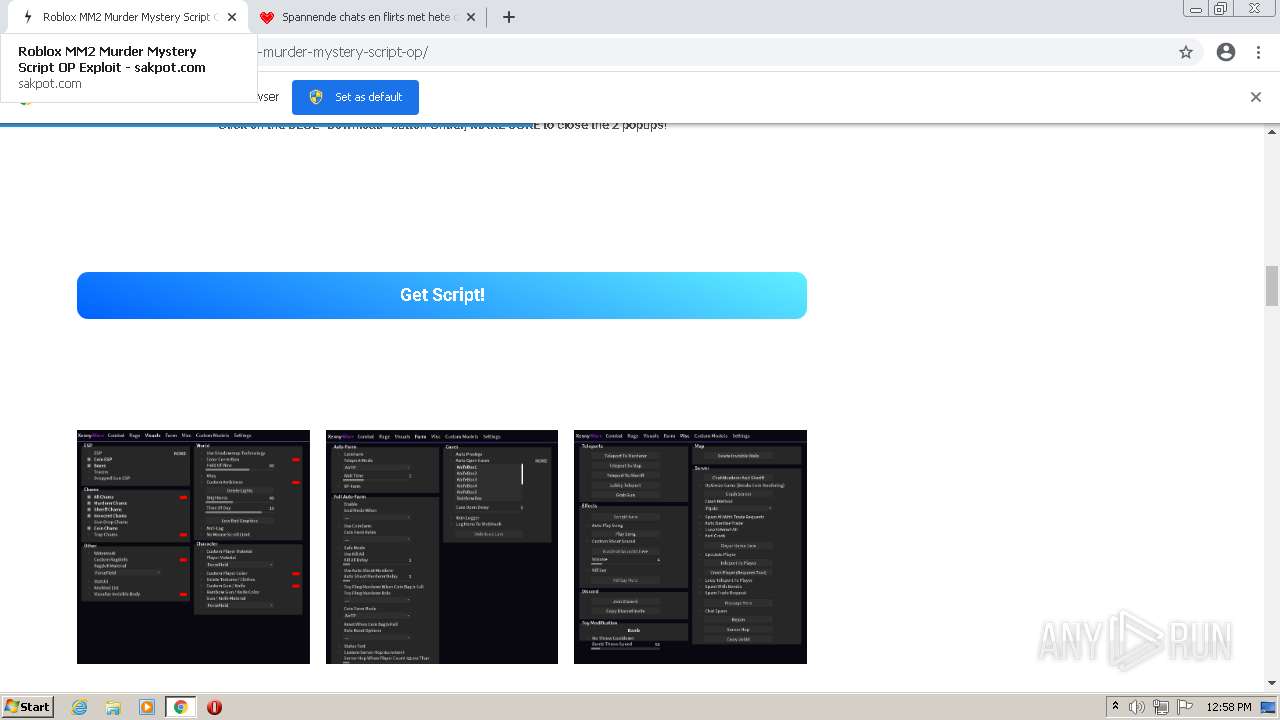
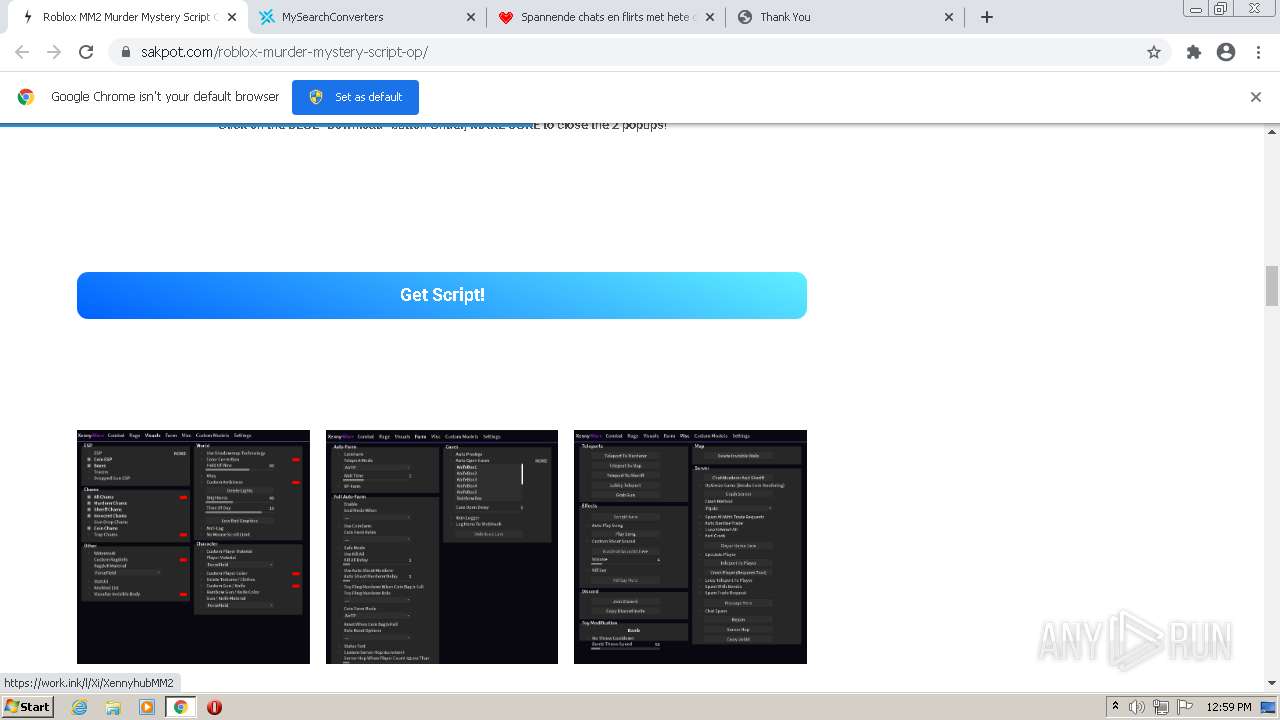
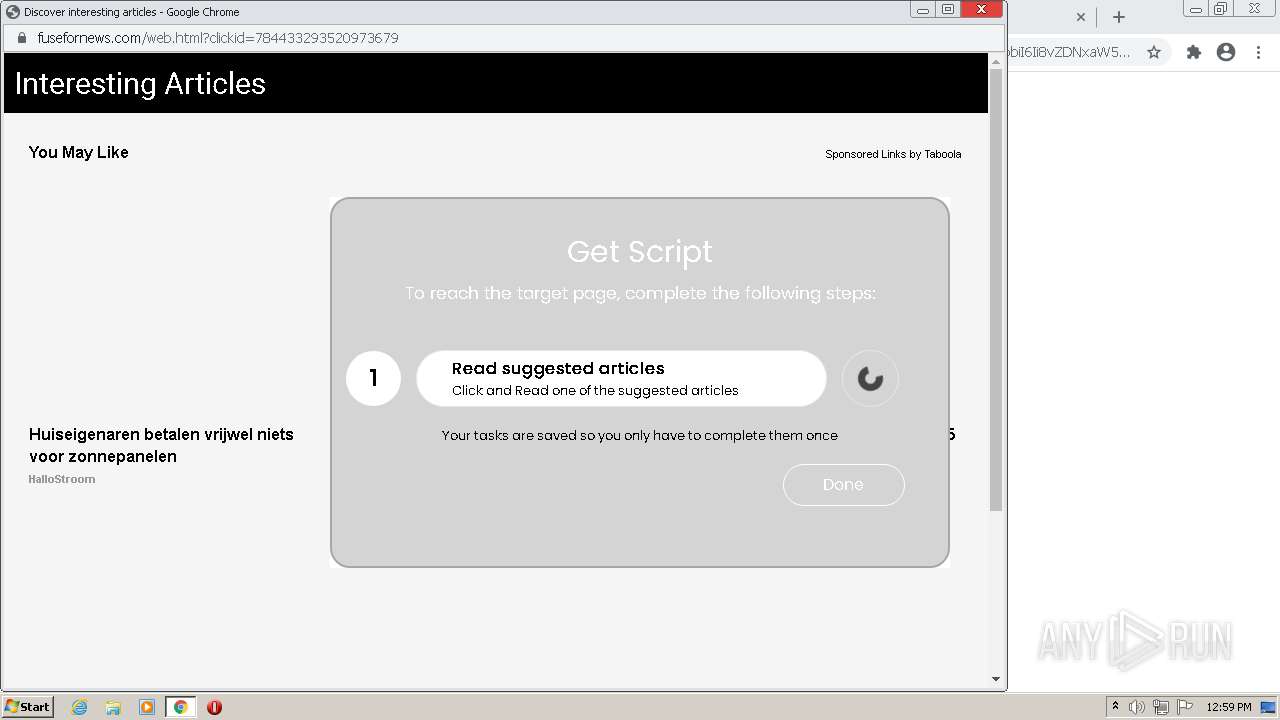
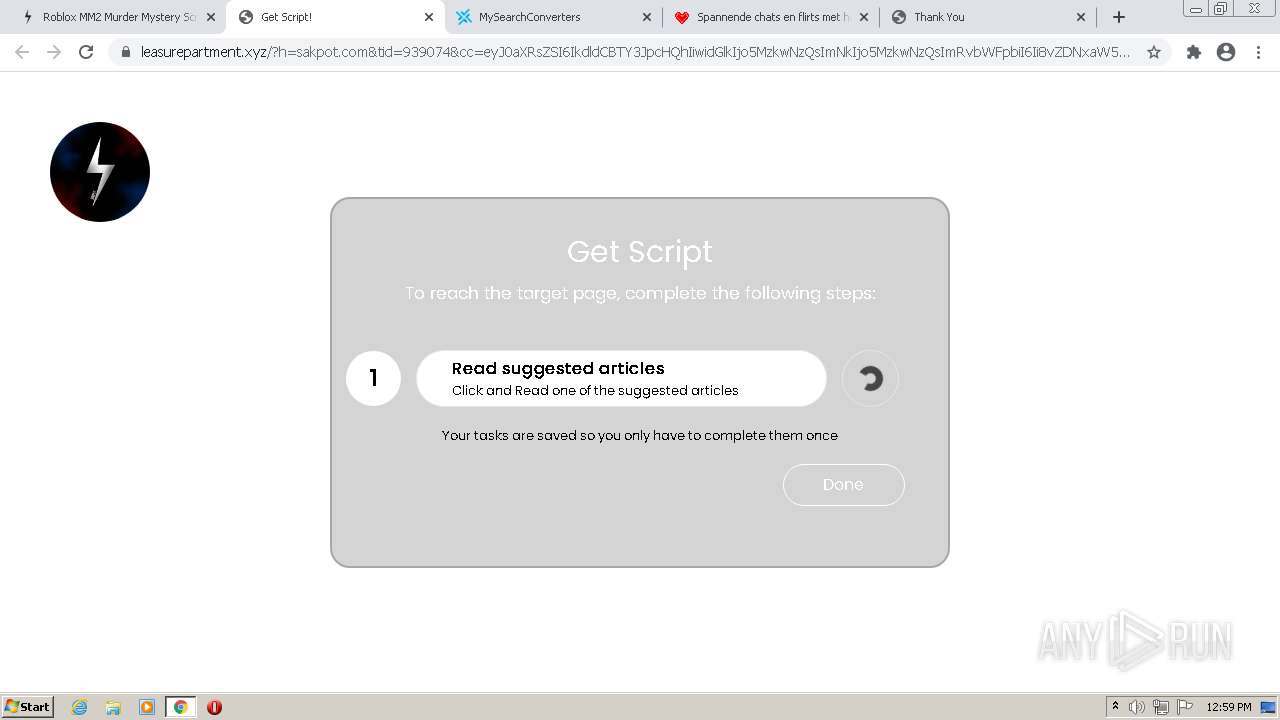
| URL: | https://sakpot.com/roblox-murder-mystery-script-op/ |
| Full analysis: | https://app.any.run/tasks/7f479c15-0223-44d5-9f5b-202df1f2b077 |
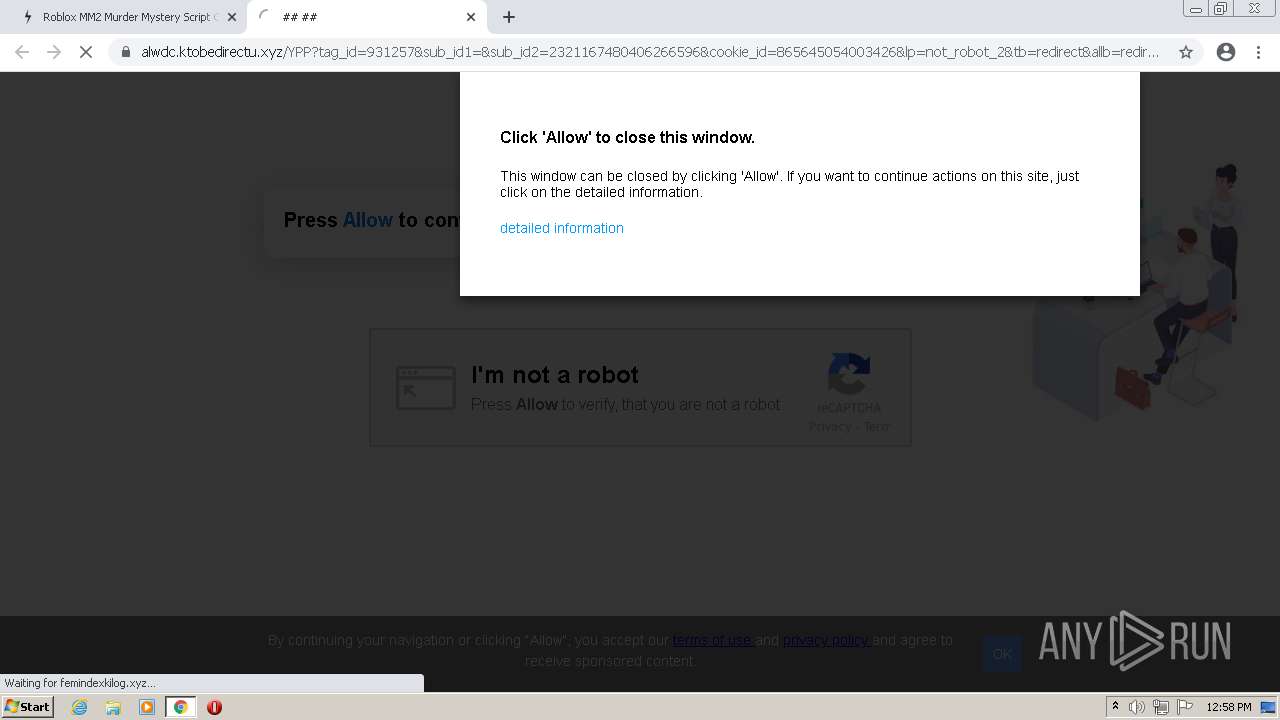
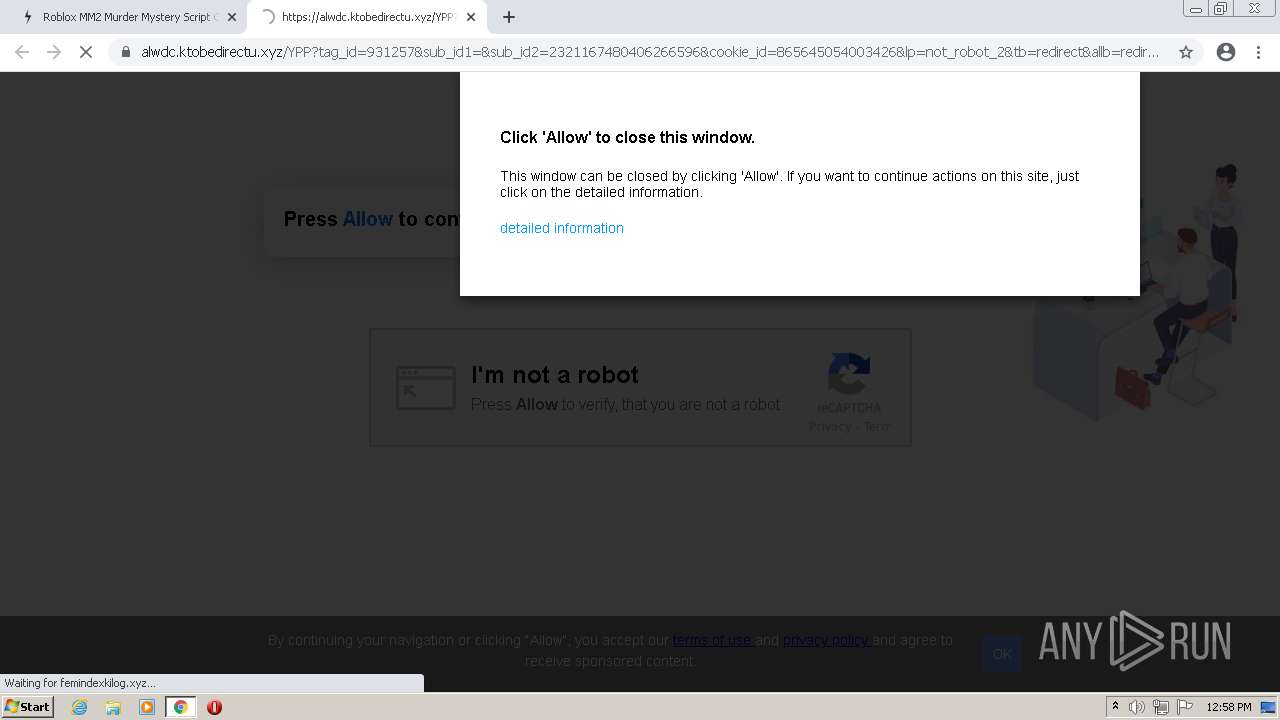
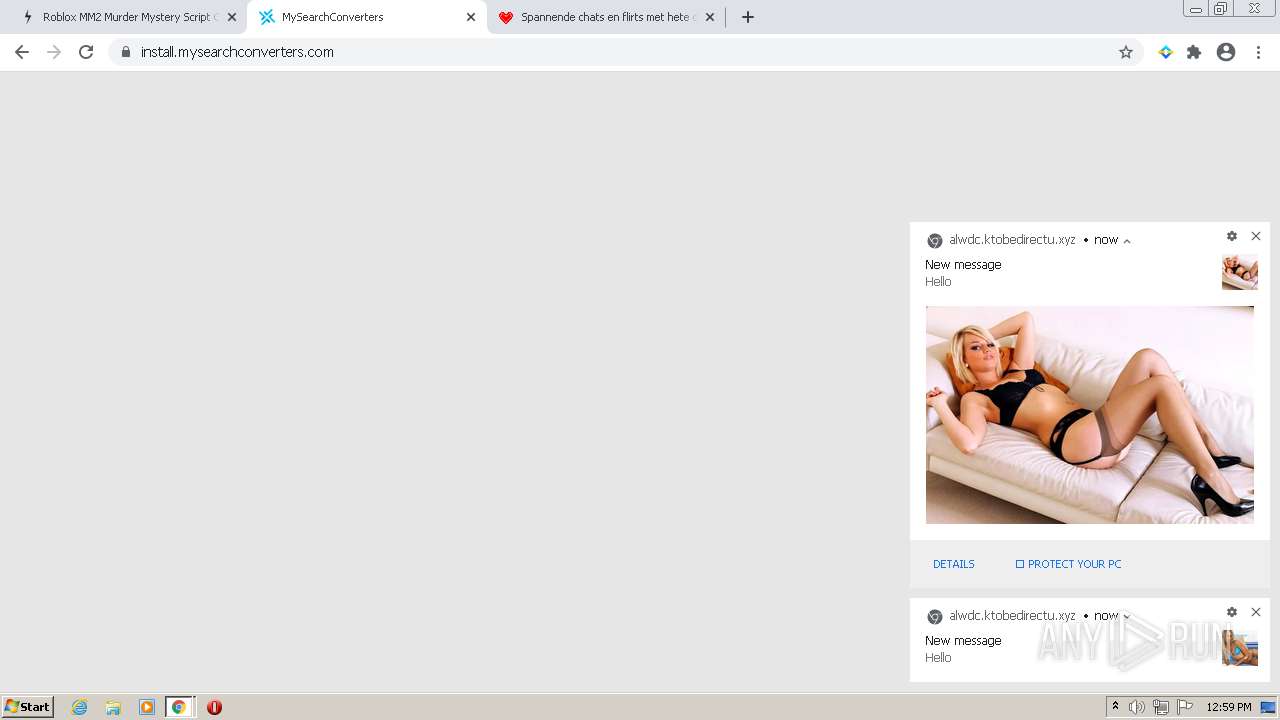
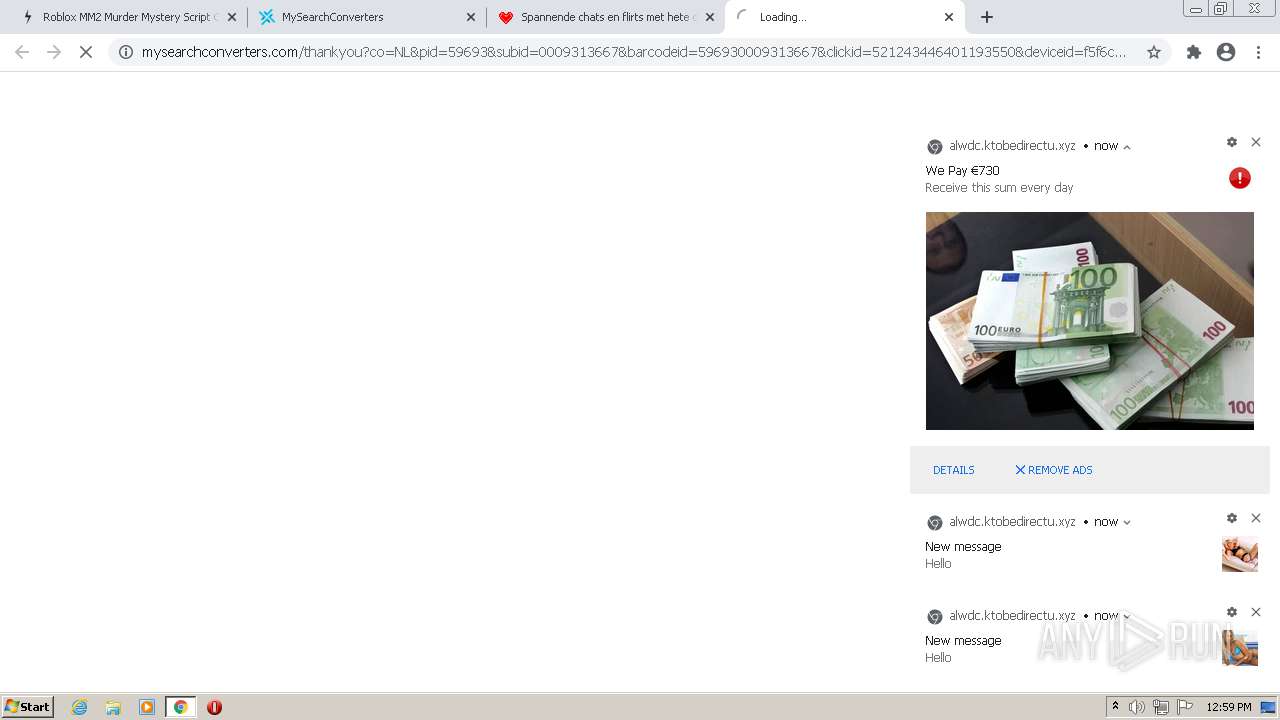
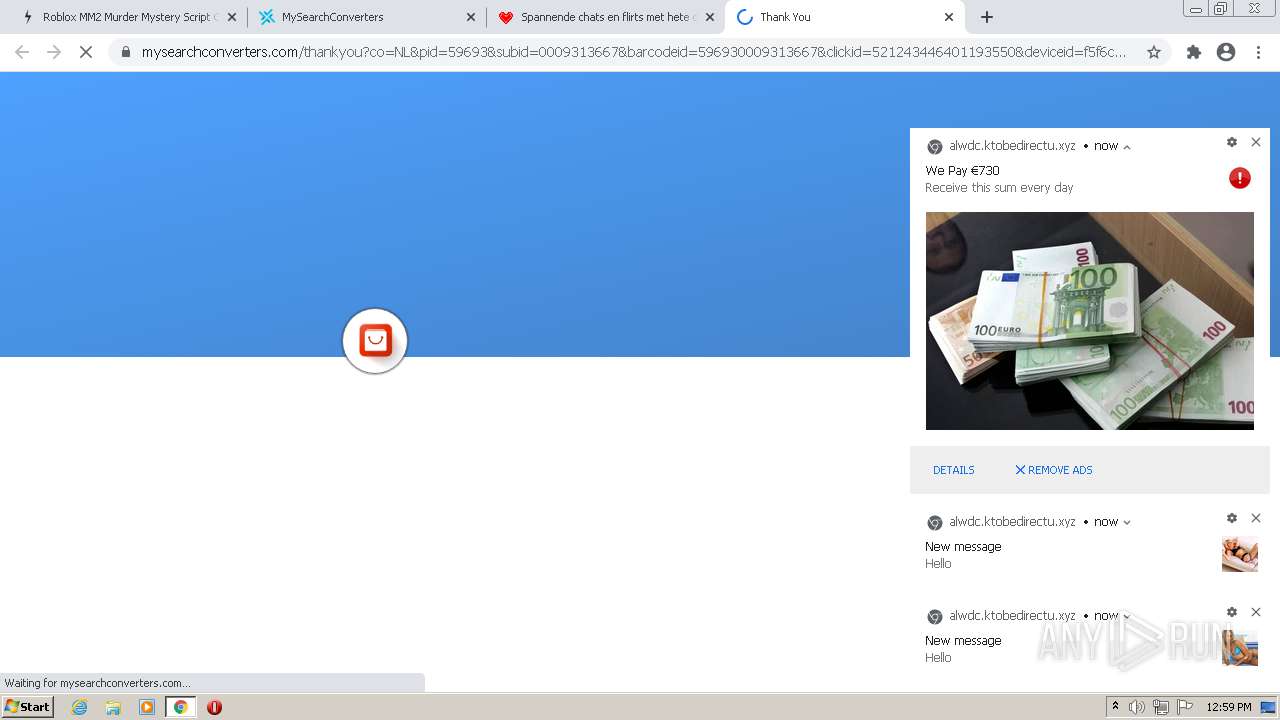
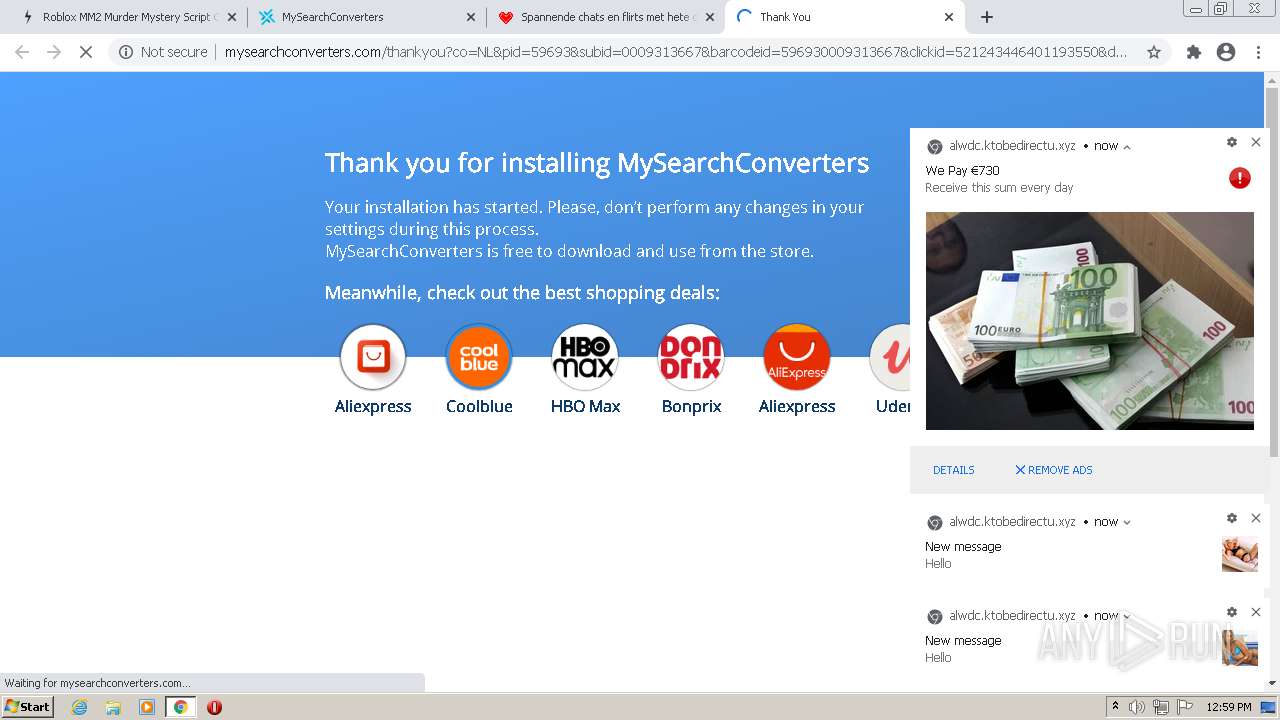
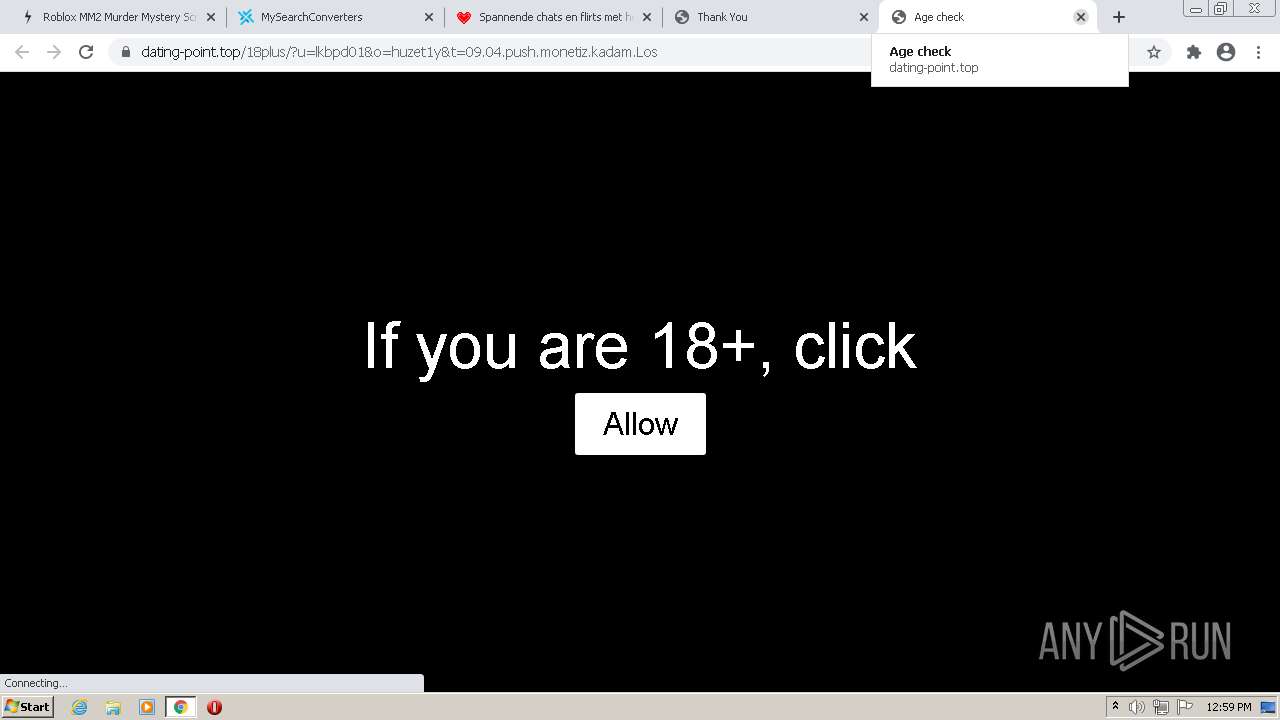
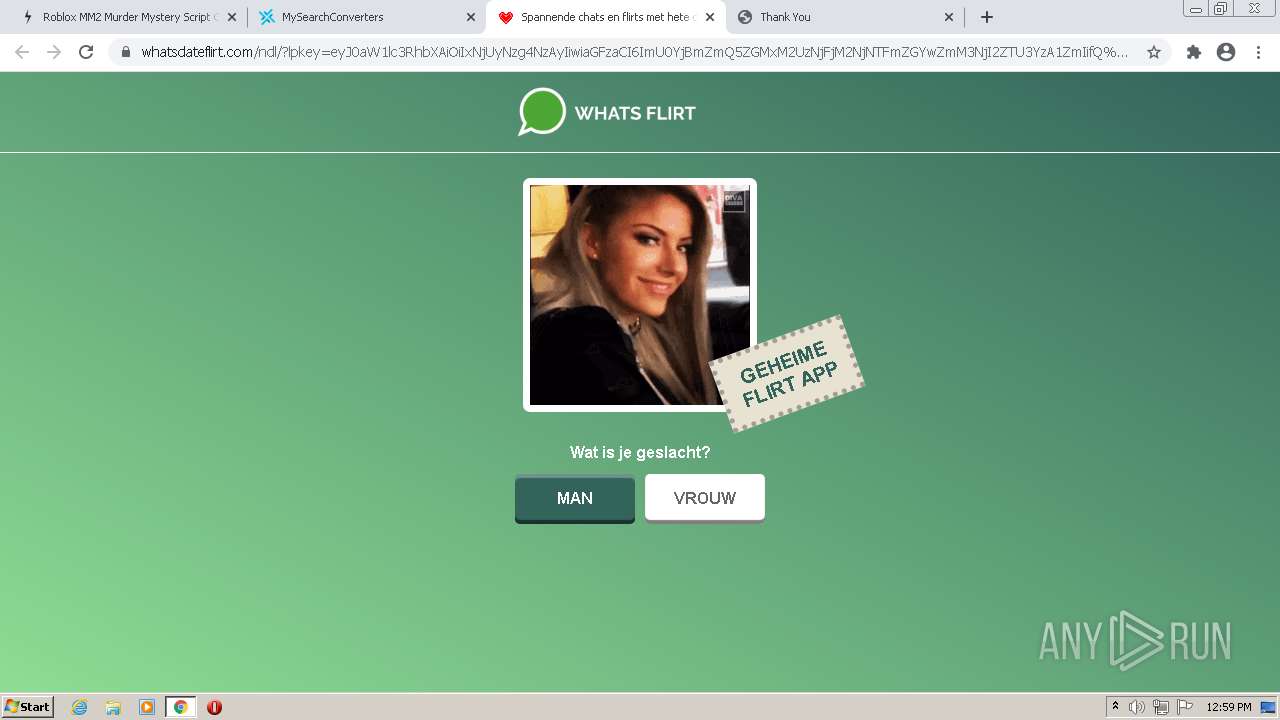
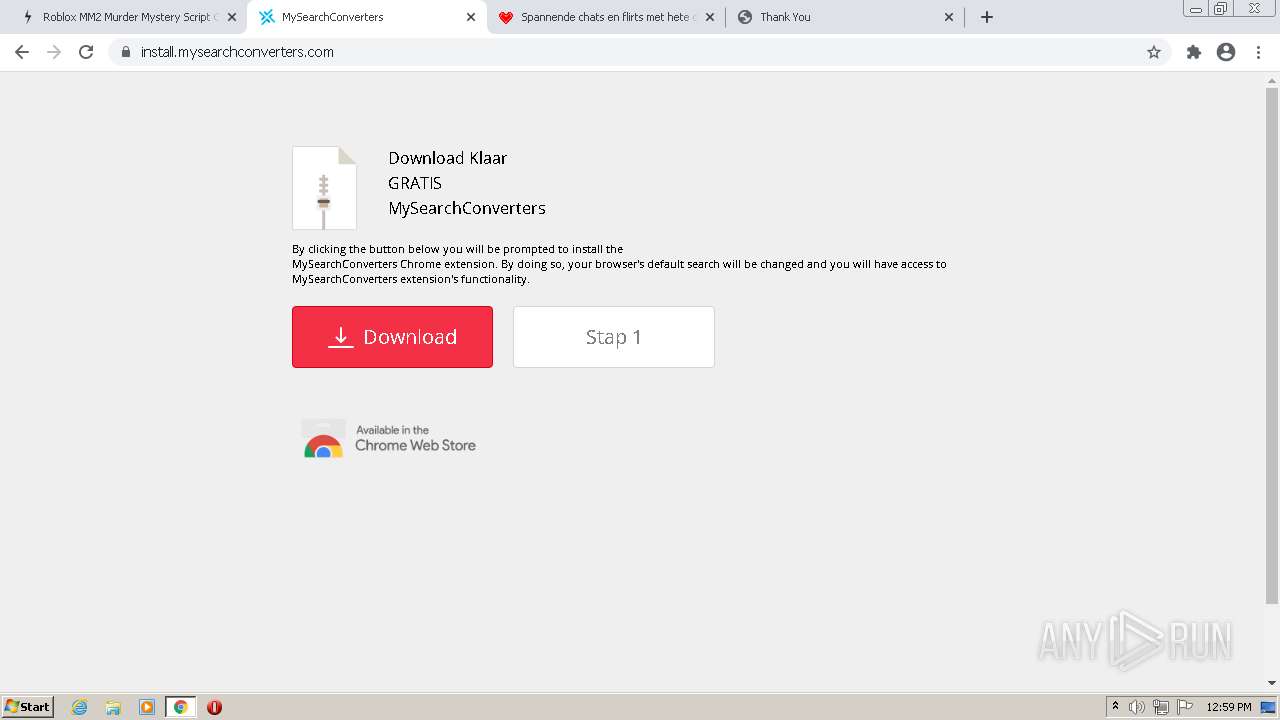
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2022, 11:57:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3752EFF1A3813D9E56C1286DEFACF809 |
| SHA1: | 3EB970A4519A874BF0B10DBE1C2EF076DA389D13 |
| SHA256: | 07CA9A40FA4D73BF09B6A204239572AFFC7E5EDDB14A633B9FF2321ACB2134CA |
| SSDEEP: | 3:N8J6QdIQdag1cWmXAhK:2wQKQdTmXAc |
MALICIOUS
No malicious indicators.SUSPICIOUS
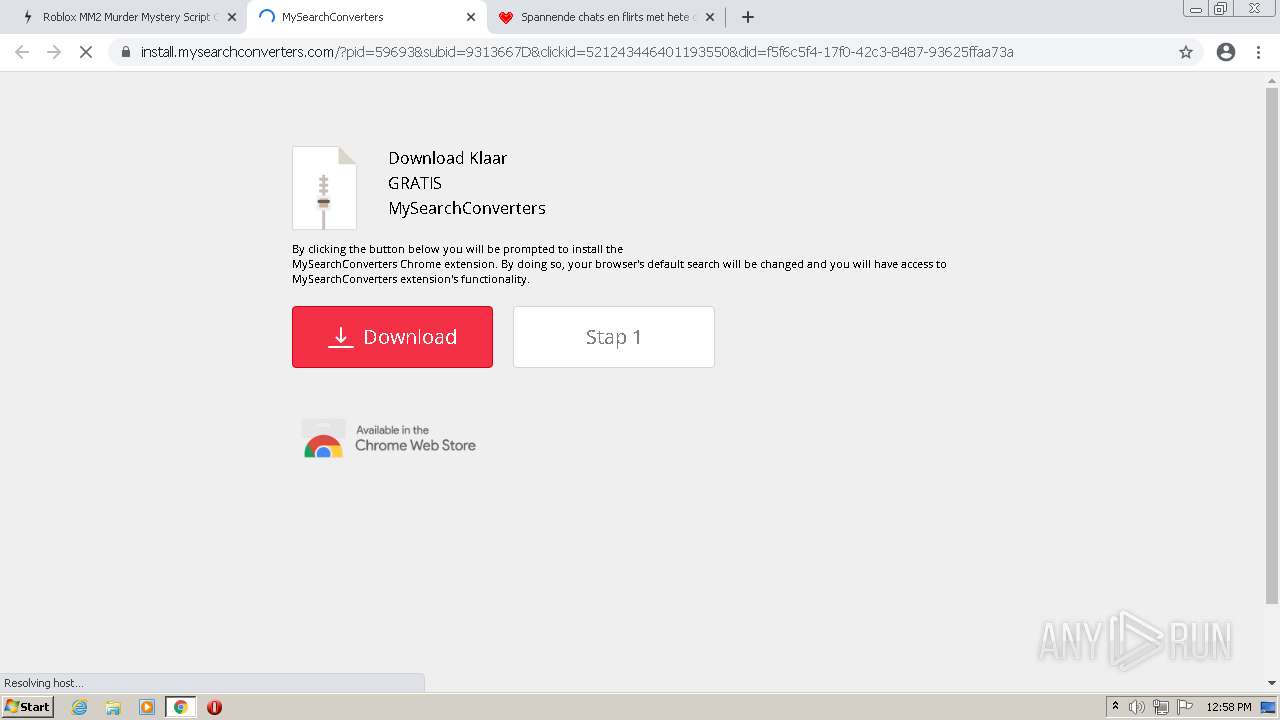
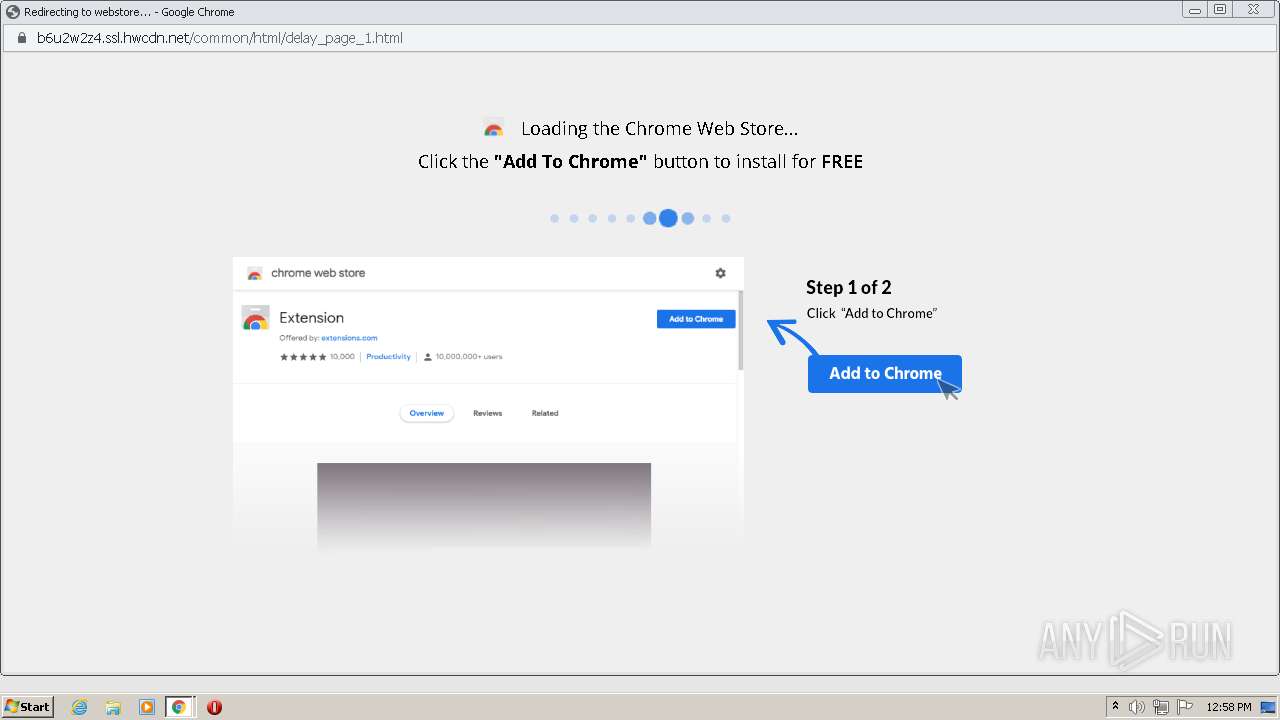
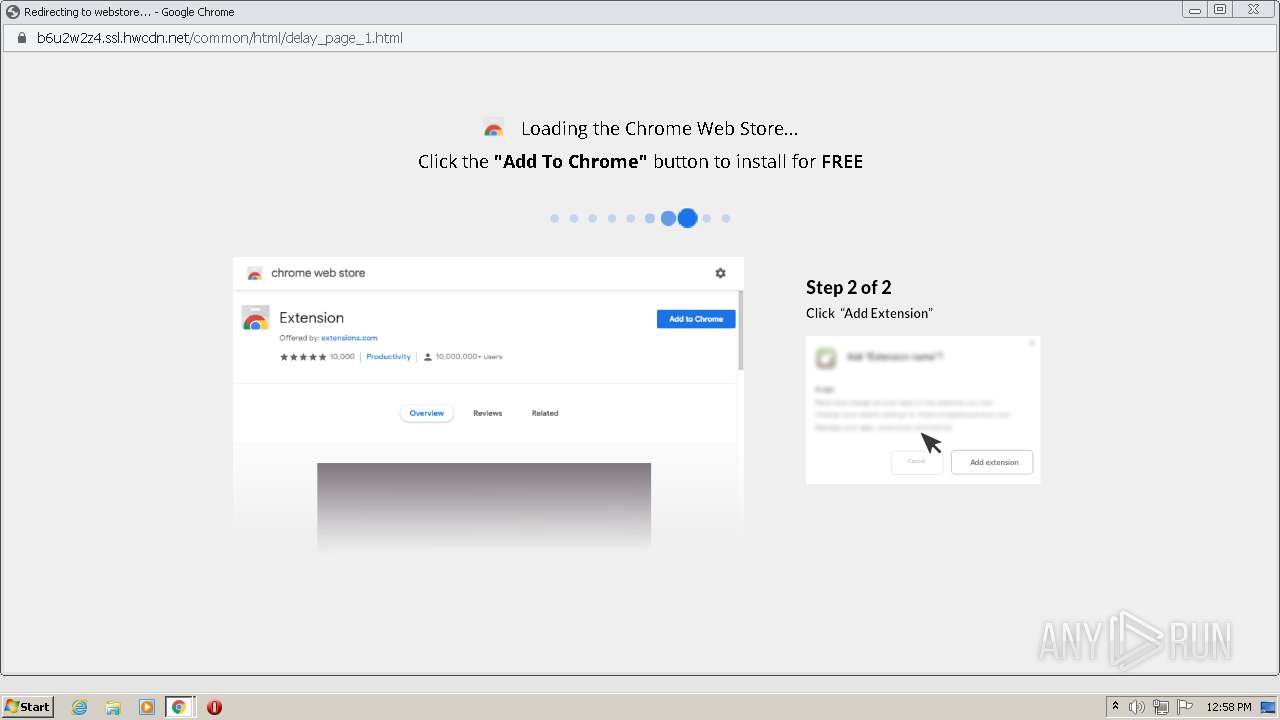
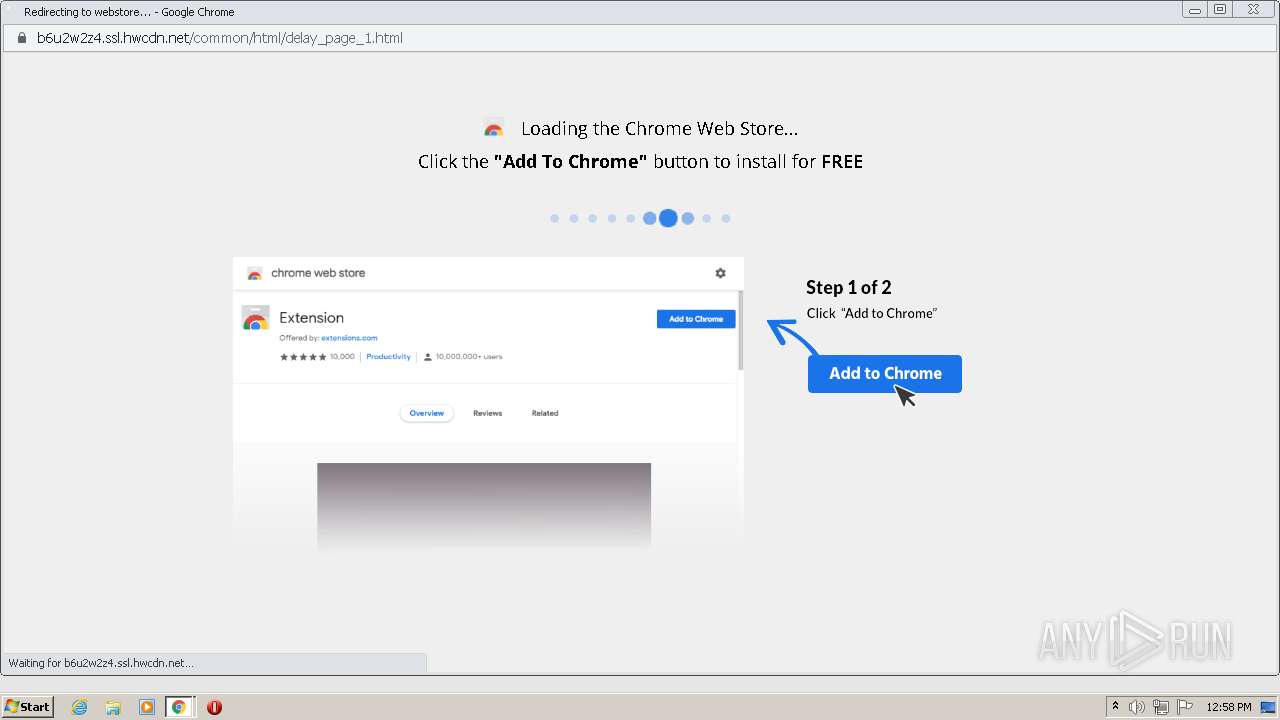
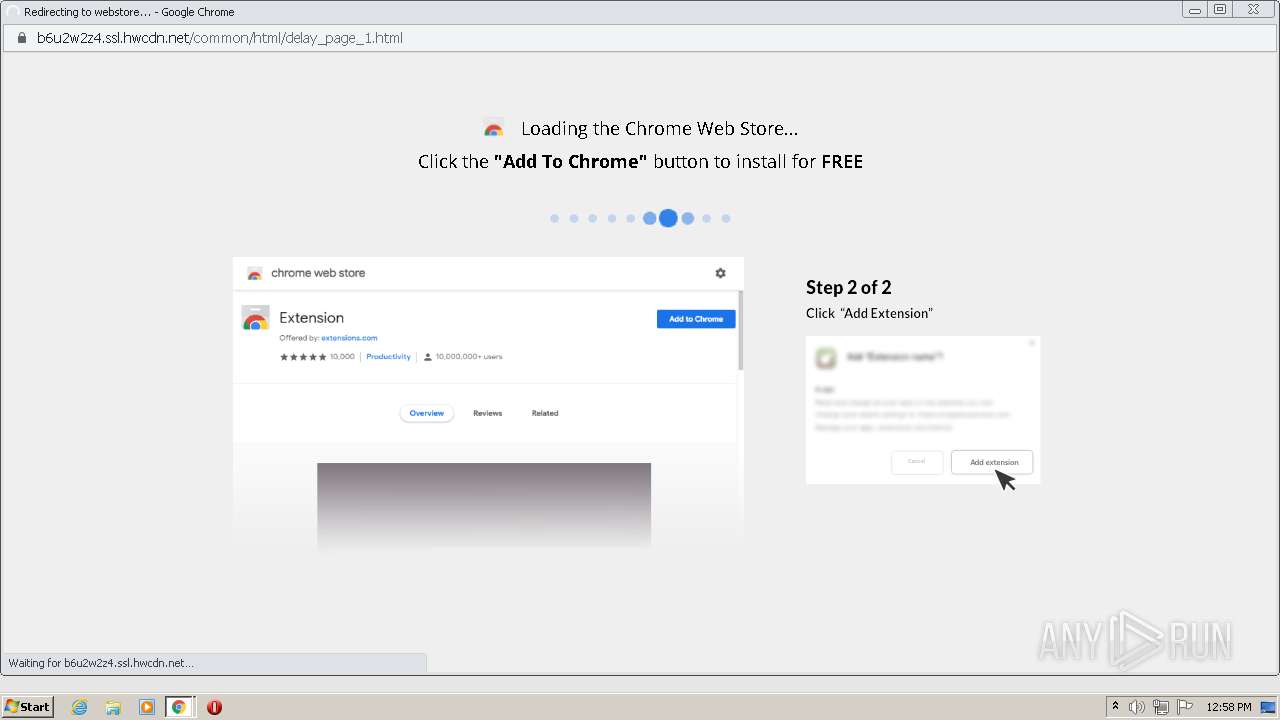
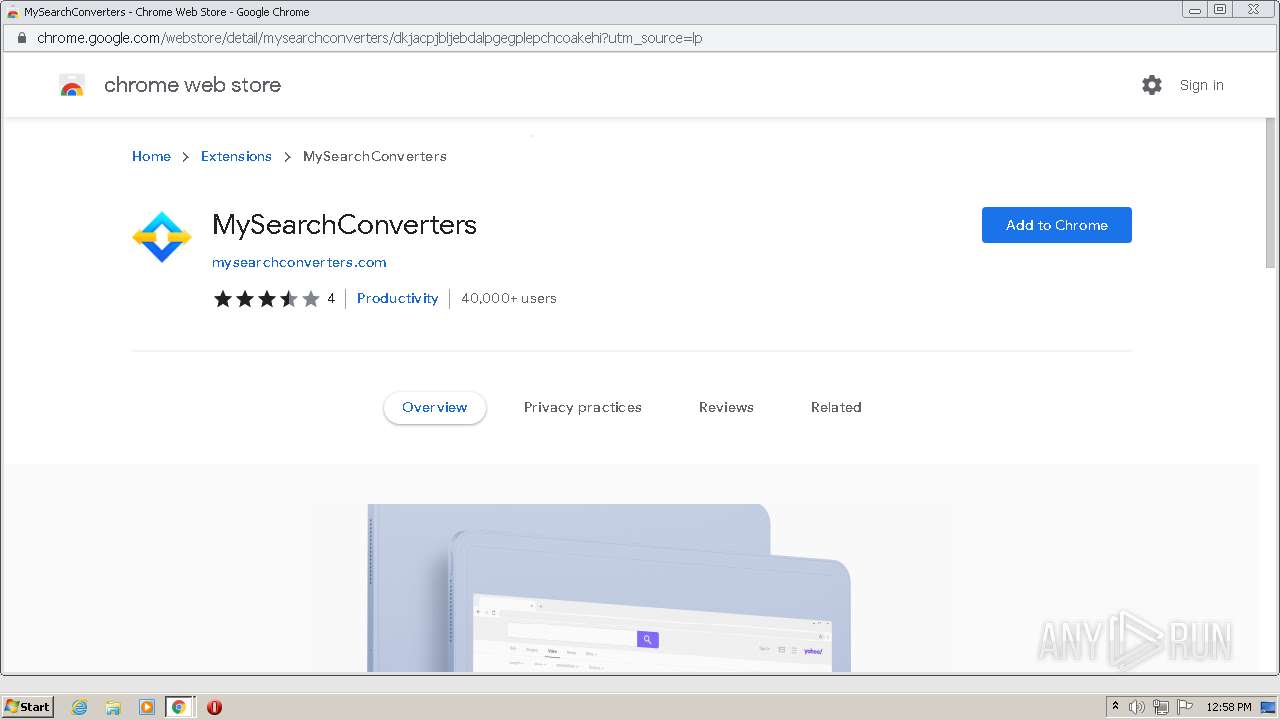
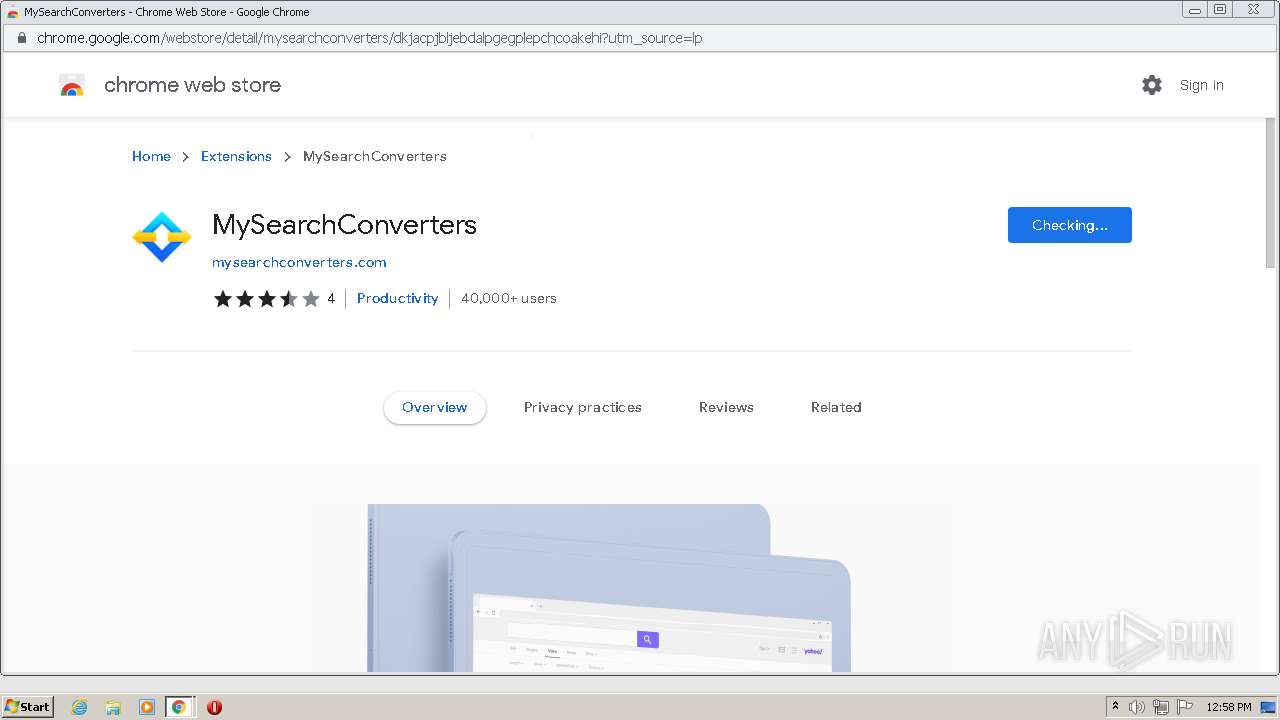
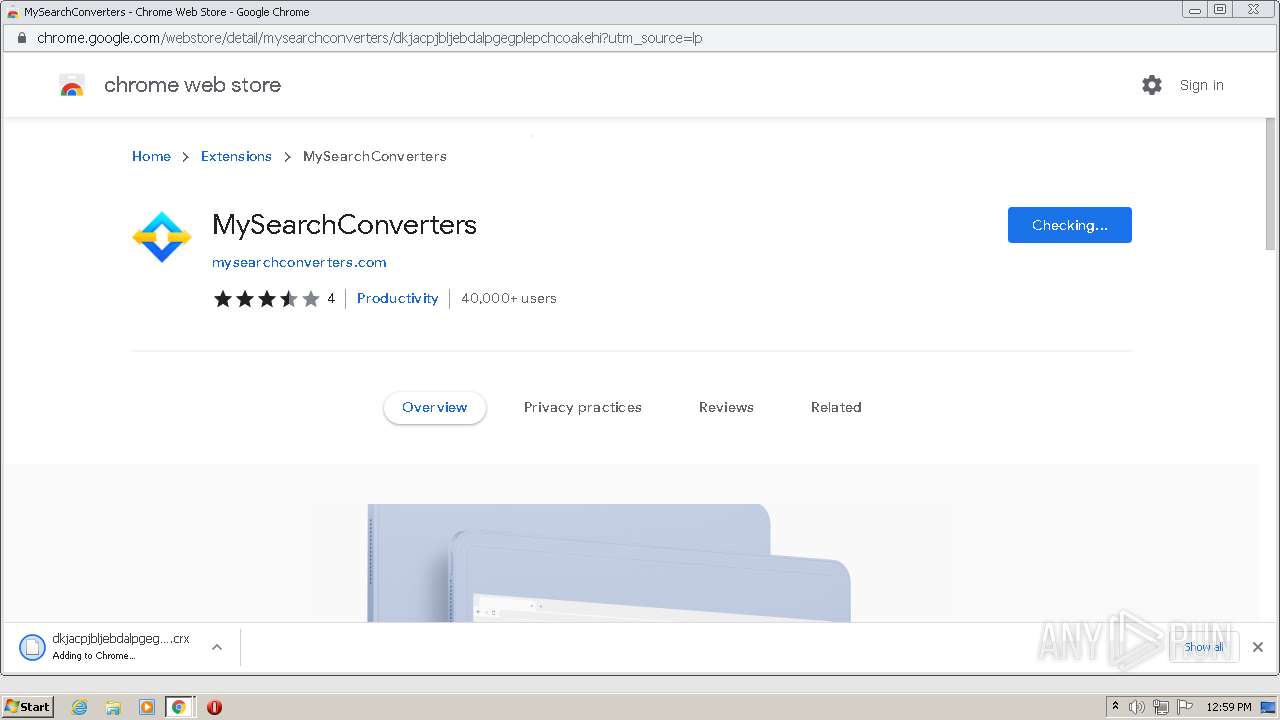
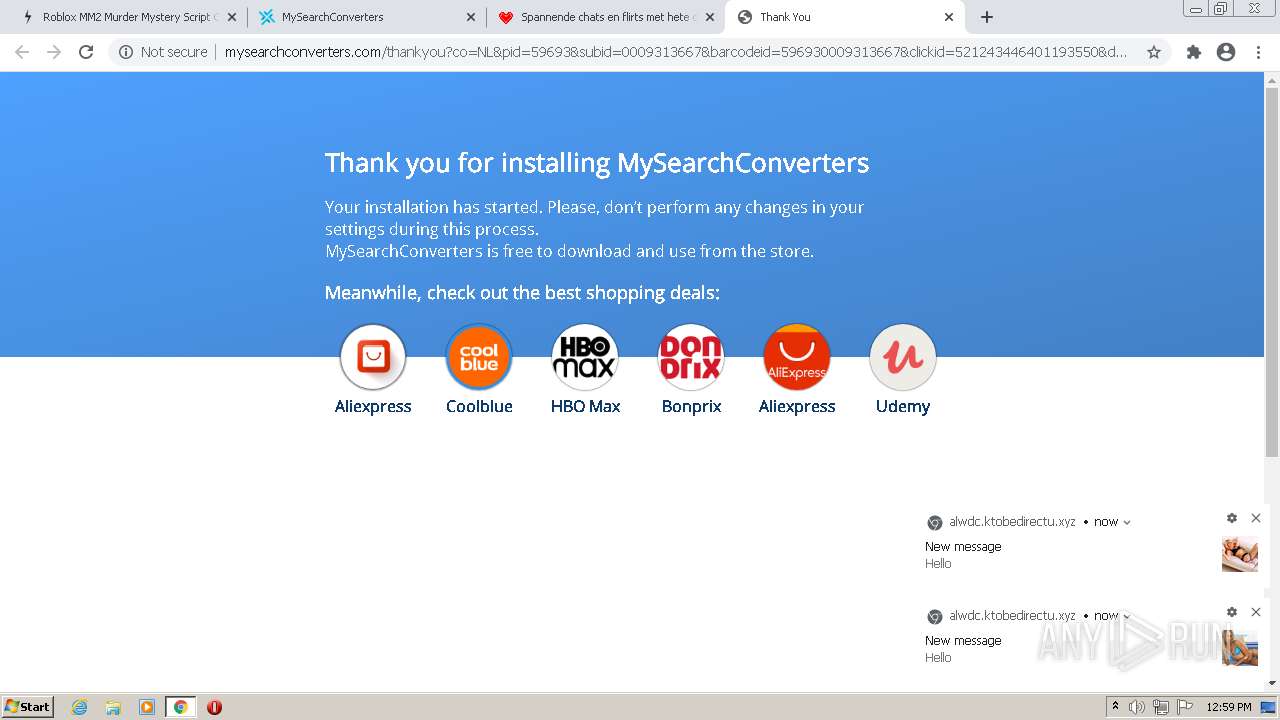
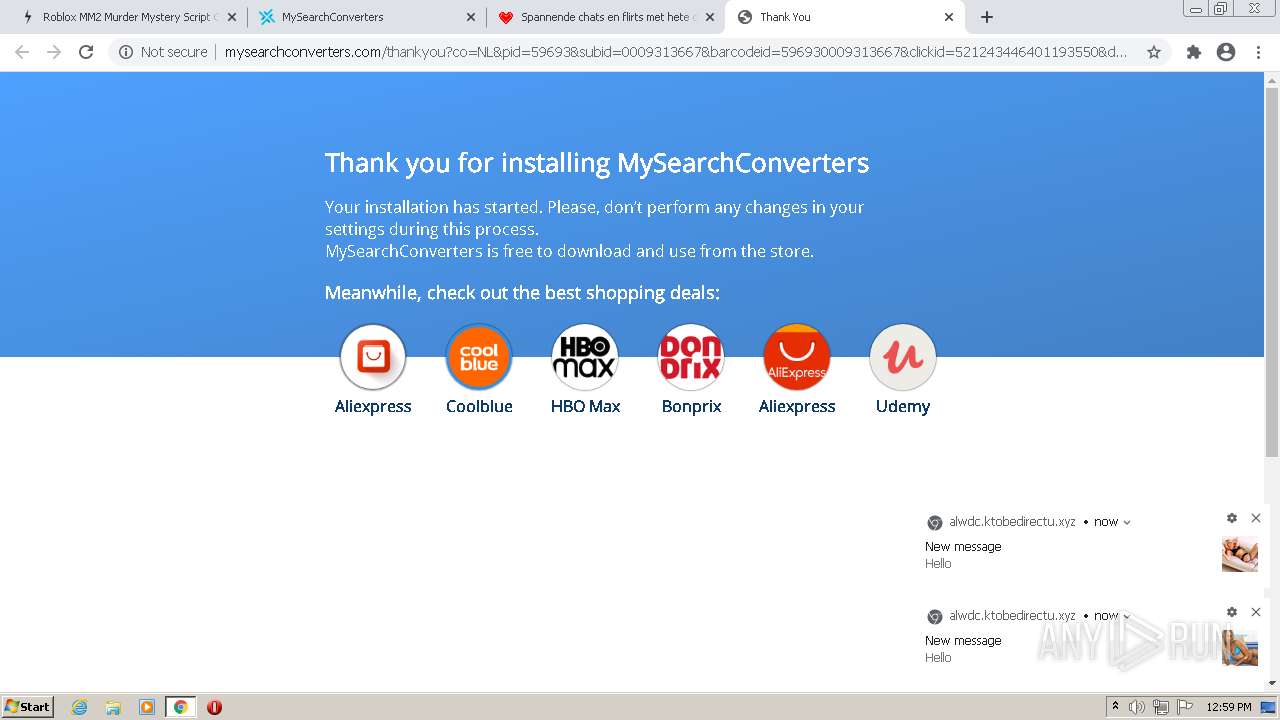
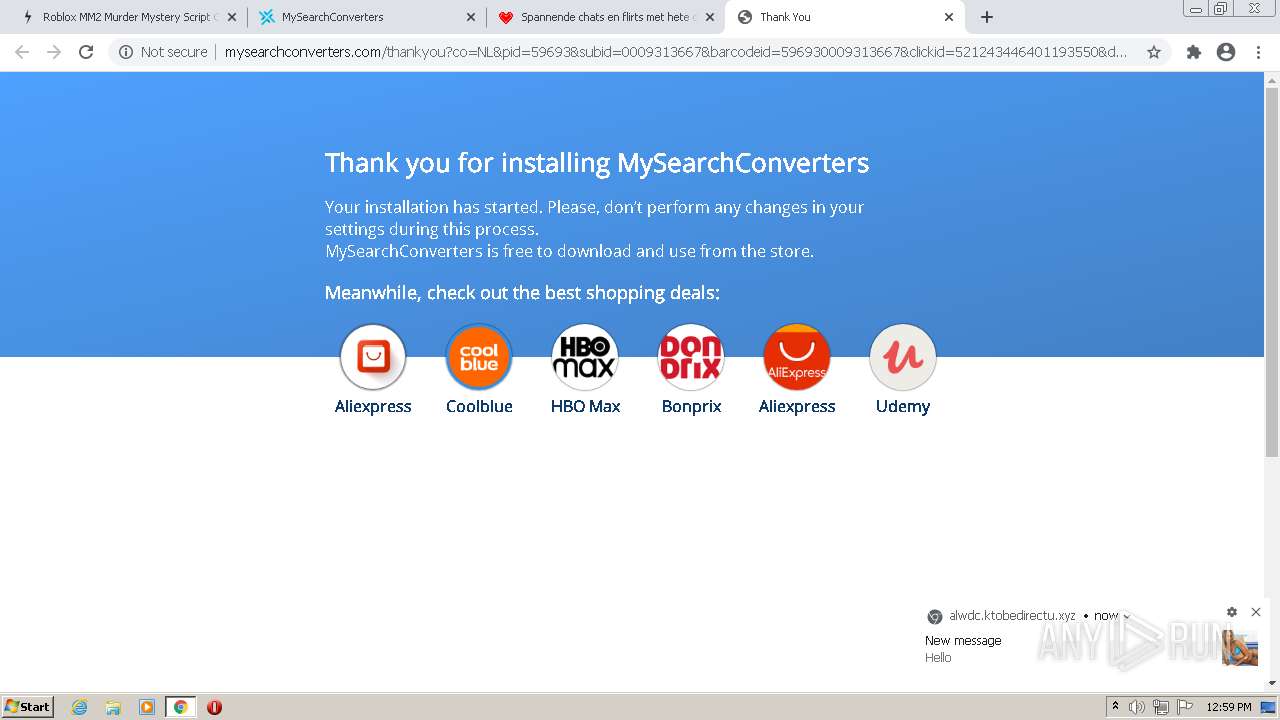
Modifies files in Chrome extension folder
- chrome.exe (PID: 696)
INFO
Reads the hosts file
- chrome.exe (PID: 2932)
- chrome.exe (PID: 696)
Checks supported languages
- chrome.exe (PID: 696)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 928)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 920)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 120)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1568)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 1432)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 304)
- chrome.exe (PID: 1464)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 1432)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 3000)
Reads the computer name
- chrome.exe (PID: 2932)
- chrome.exe (PID: 696)
- chrome.exe (PID: 928)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 120)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3748)
Reads settings of System Certificates
- chrome.exe (PID: 2932)
Application launched itself
- chrome.exe (PID: 696)
Reads the date of Windows installation
- chrome.exe (PID: 1664)
Checks Windows Trust Settings
- chrome.exe (PID: 696)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://sakpot.com/roblox-murder-mystery-script-op/" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
17 688
Read events
17 509
Write events
173
Delete events
6
Modification events
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
55
Text files
144
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62838DC0-2B8.pma | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5c53942f-627e-4b91-9f80-780cf5670e16.tmp | text | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf9755.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFf986e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf9745.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFf9958.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
186
DNS requests
95
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
— | — | HEAD | 200 | 209.85.226.103:80 | http://r2---sn-5hne6ns6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=45.128.199.18&mm=28&mn=sn-5hne6ns6&ms=nvh&mt=1652788585&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r5---sn-5hne6nsr.gvt1.com | US | — | — | whitelisted |
2932 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=d95fbcd25837d7028fc877c6688665d61817fe679e1e33de1aa6c935bf9b0174d1aca0b0bd387c51d4957f757577a62345c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d4c13c1e79bc2d95b&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fc27bb95ba7e6b3f8919e674a8f6c928ac3892fa8b2a5f01be7826d91aaf82394a4b4227e5f232ee36a3321bf2114229cb2fb5857ae8a1a8ffe9bacd8bf3f362beb8838c7c4520777aa0cb38246898f55e1ff5c9d09d0021de8e1f3d2f5fe21819a586f38f72b0daee307c3d28962303a45328cf5d85b75c71aacf30113441b41f0cf57a0b46eef528a904c80ca9c1dbf7db56b25cf33e2a251753b990ce32097442b3d76ea0255704a166ab4f0f66ca7&ccd=nl&stc=nb&cin=heistraat&mcd=0&cic=224093&kw=qldummy | US | — | — | suspicious |
2932 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=d95fbcd25837d7028fc877c6688665d61817fe679e1e33de1aa6c935bf9b0174d1aca0b0bd387c5114a4fbe71a3cbaf945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d890eb96b04bcceae&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f933abe7250a311611e598f7260ed2210e039a47617b0514c2a8032a35233ebc7ce3228fd9b401e98884c035a9958d9e0f8f822ac69b701ba245d4eeea1c2c5ad703d419ee8a36c42c57f754e09a6b3fc85d5d7e574ad69179a90b38746d9dc6bb1587f53b08d0069a284239e4417e1b15054acb0dfab4b9e234b7f90910aa986a25f8901d85e22904689915f106675dc5cbaafd3b6a3b0820fb8d6e3c9907667defd74827010009c9fd0eda8a67fe41d&ccd=nl&stc=nb&cin=heistraat&mcd=0&cic=224093&kw=qldummy | US | — | — | suspicious |
2932 | chrome.exe | GET | 302 | 173.239.53.32:80 | http://clkv4.extyoneplus-3.com/click?i=rf-7lKE5ujI_0 | US | — | — | suspicious |
2932 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=d95fbcd25837d7028fc877c6688665d61817fe679e1e33de1aa6c935bf9b0174d1aca0b0bd387c51c11a4539c265514945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3dcf92fb028347f0f8&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f93f57dd28a6cc2fcedc768425e9bd2e4095d76a4f1565fd72a8032a35233ebc7ce3228fd9b401e98884c035a9958d9e0f8f822ac69b701ba46291d0f3ef92c00d23f8e46553d6335c57f754e09a6b3fc85d5d7e574ad69179a90b38746d9dc6bb1587f53b08d0069a284239e4417e1b15054acb0dfab4b9e234b7f90910aa986a25f8901d85e22904689915f106675dc5cbaafd3b6a3b0827fa33e2992c5ad81defd74827010009ce683b5c1874e9ca7&ccd=nl&stc=nb&cin=heistraat&mcd=0&cic=224093&kw=qldummy | US | — | — | suspicious |
— | — | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 559 b | whitelisted |
— | — | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 559 b | whitelisted |
2932 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=d95fbcd25837d7028fc877c6688665d61817fe679e1e33de1aa6c935bf9b0174d1aca0b0bd387c515ca71983e786eab145c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d5cf09c947124740c&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f8c533da835c60c6e8311056b1df739f11f3d18282caf7c592a8032a35233ebc7ce3228fd9b401e98884c035a9958d9e0f8f822ac69b701ba002fab415868bff5ad94079e0f681acdc57f754e09a6b3fc85d5d7e574ad69179a90b38746d9dc6bb1587f53b08d0069a284239e4417e1b15054acb0dfab4b9e234b7f90910aa986a25f8901d85e22904689915f106675dc5cbaafd3b6a3b0827fa33e2992c5ad81defd74827010009c9fd0eda8a67fe41d&ccd=nl&stc=nb&cin=heistraat&mcd=0&cic=224093&kw=qldummy | US | — | — | suspicious |
2932 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2ebac95b411e2aed | US | compressed | 60.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 145.239.192.146:443 | sakpot.com | OVH SAS | FR | suspicious |
2932 | chrome.exe | 142.251.36.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | chrome.exe | 188.114.96.10:443 | cheatsquad.gg | Cloudflare Inc | US | malicious |
2932 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2932 | chrome.exe | 104.21.45.207:443 | freychang.fun | Cloudflare Inc | US | suspicious |
2932 | chrome.exe | 54.230.111.13:443 | improvided.xyz | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
sakpot.com |
| malicious |
accounts.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cheatsquad.gg |
| malicious |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
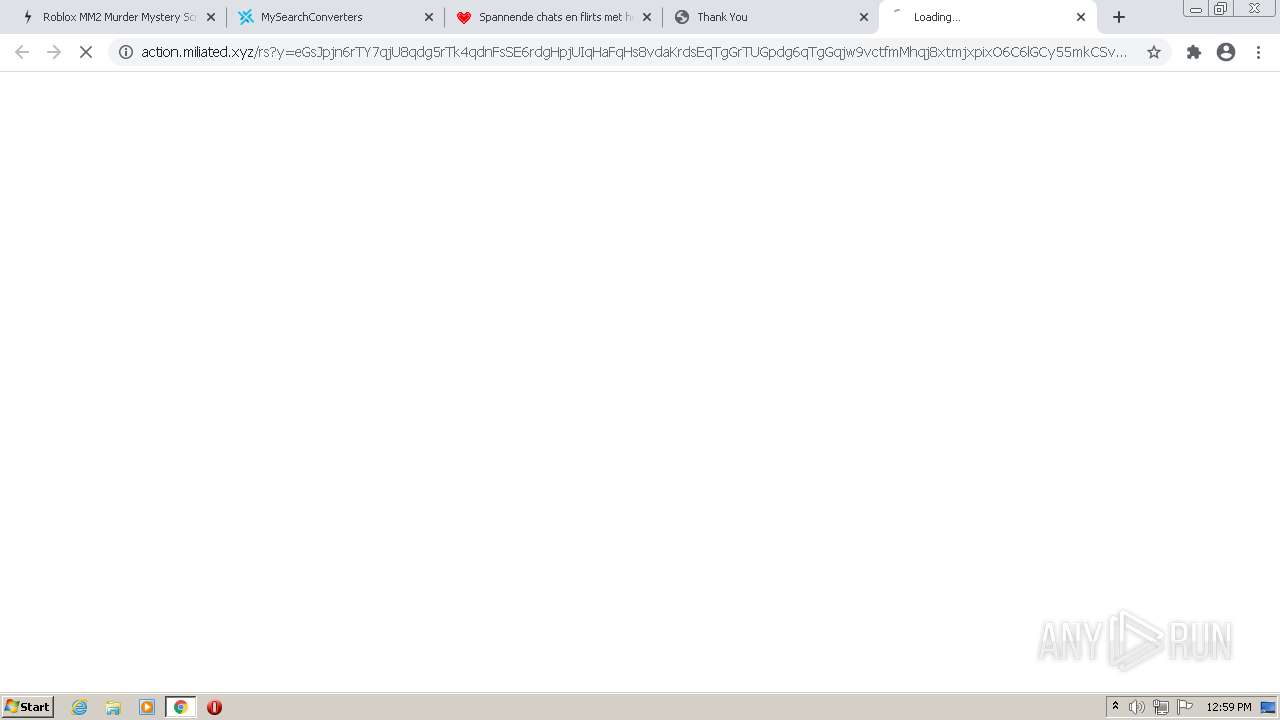
2932 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2932 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2932 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1 ETPRO signatures available at the full report