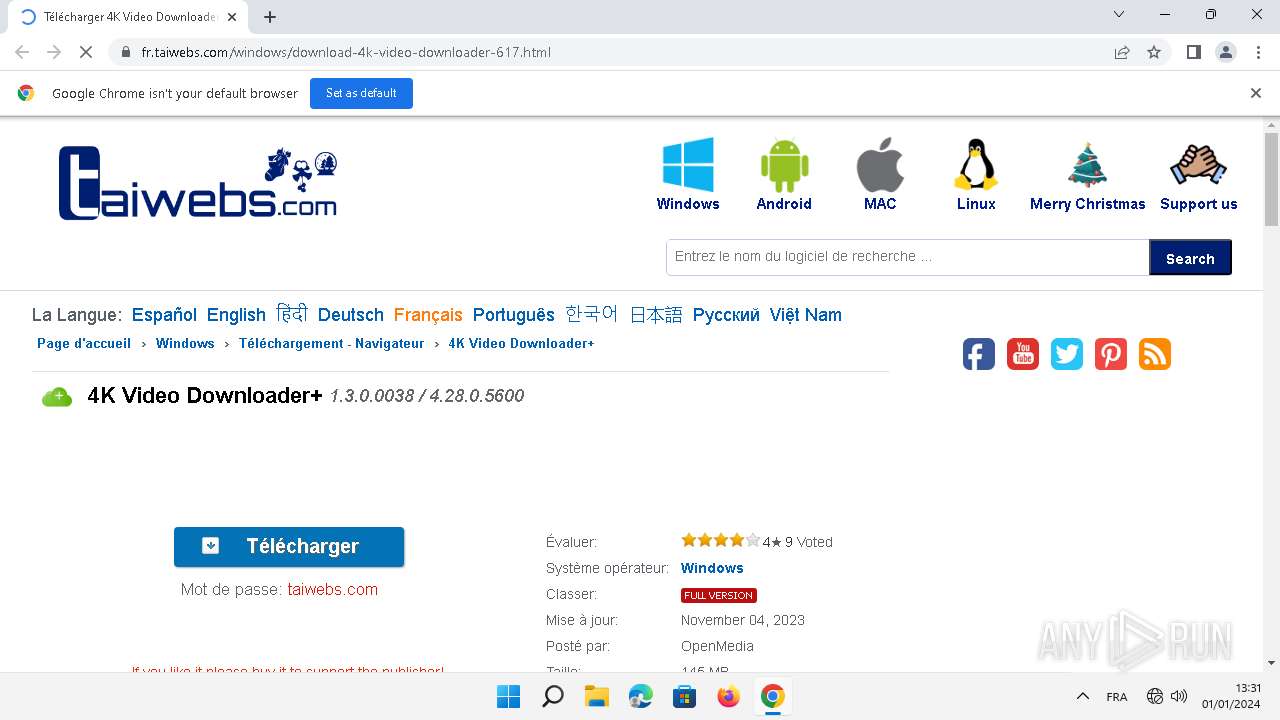
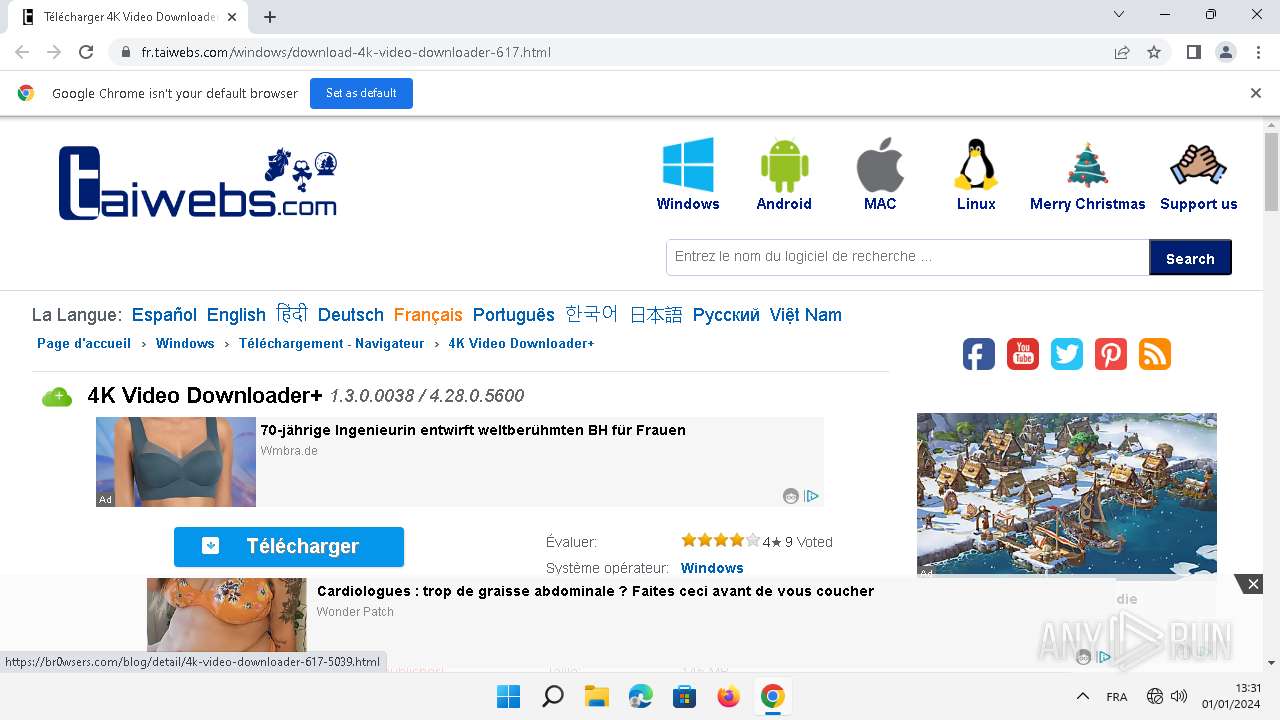
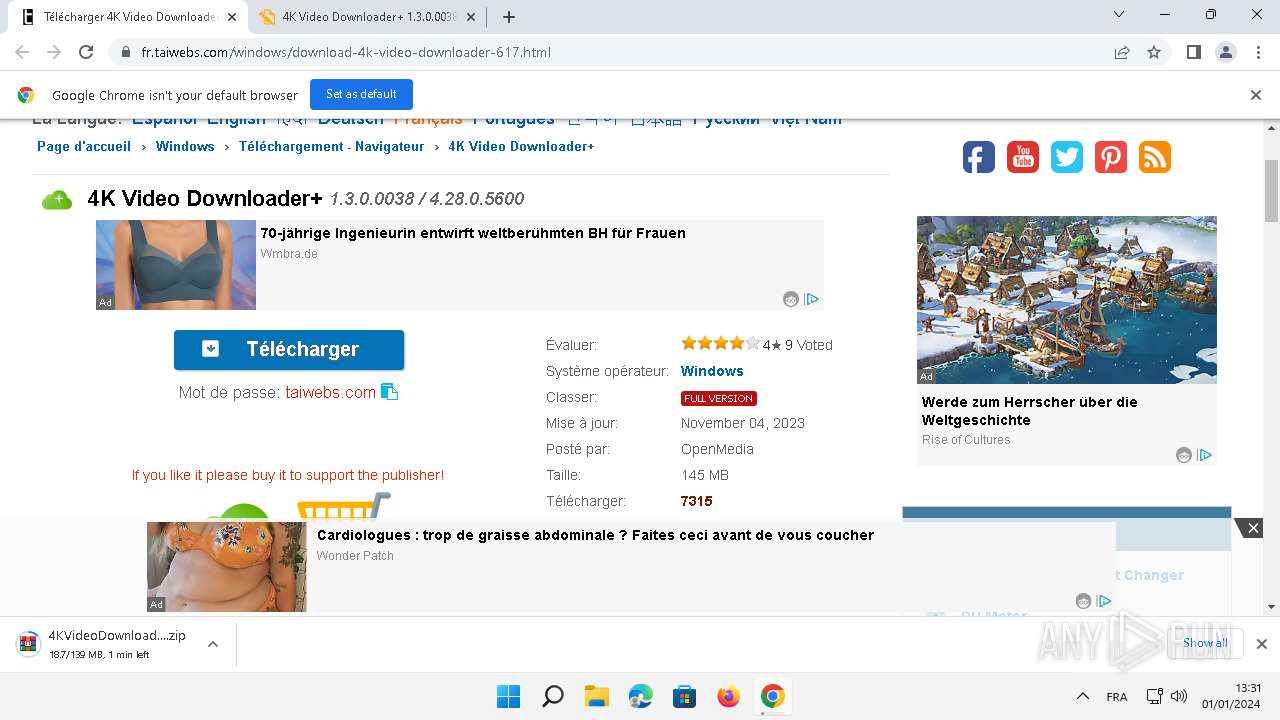
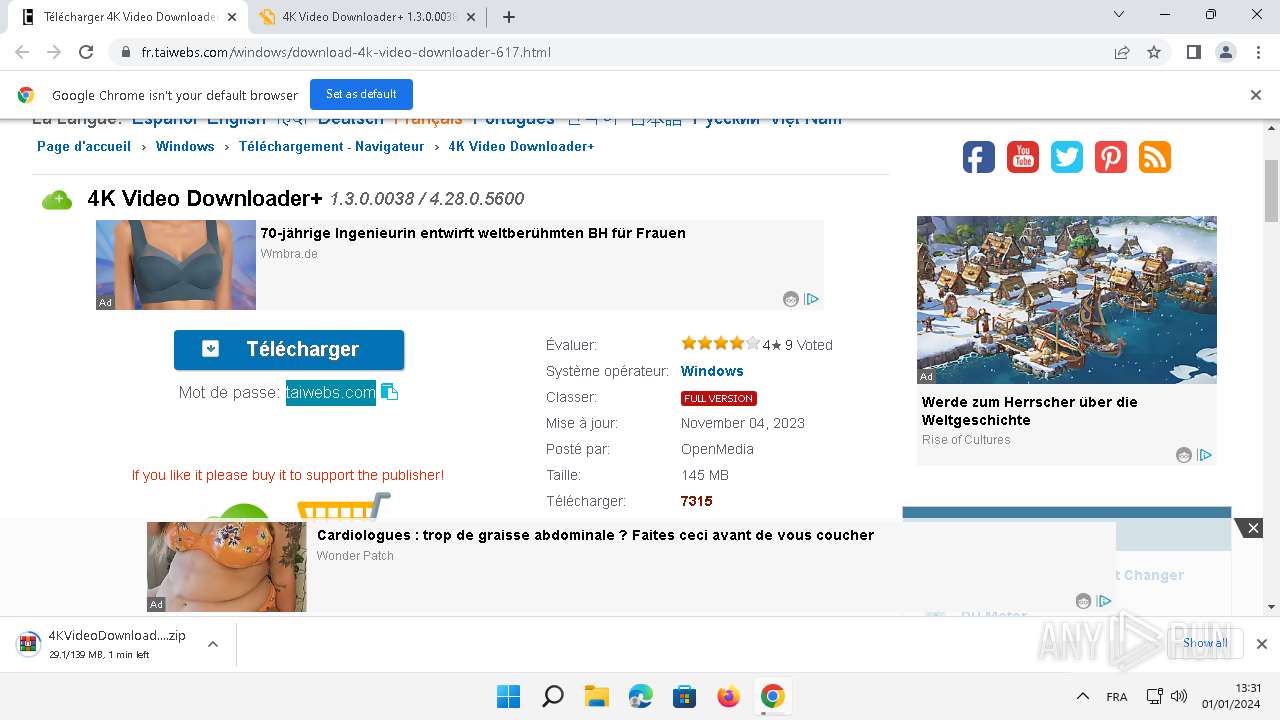
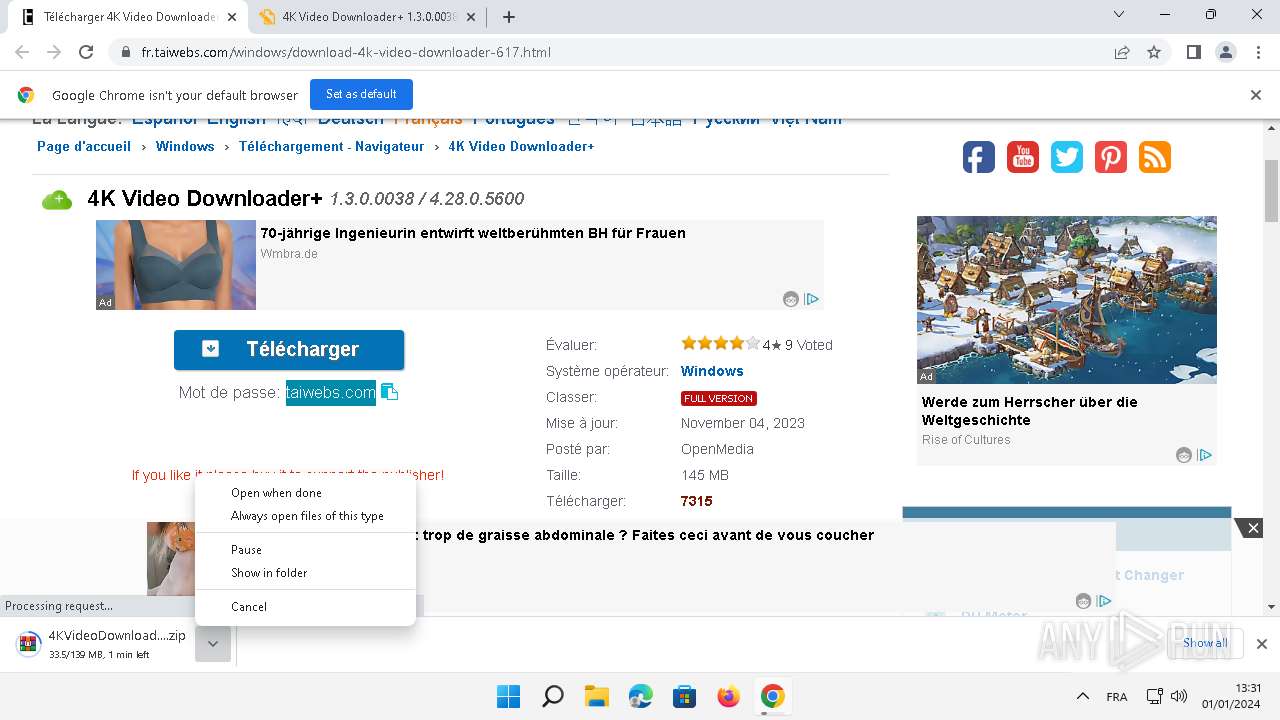
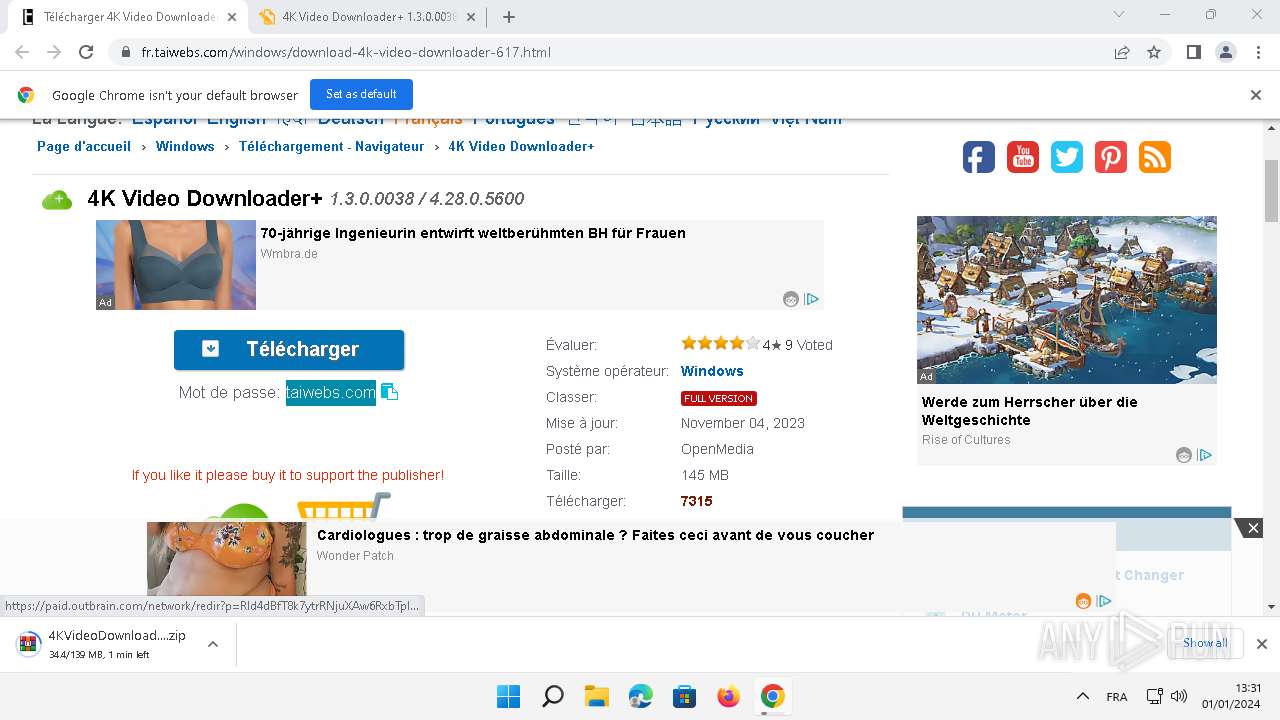
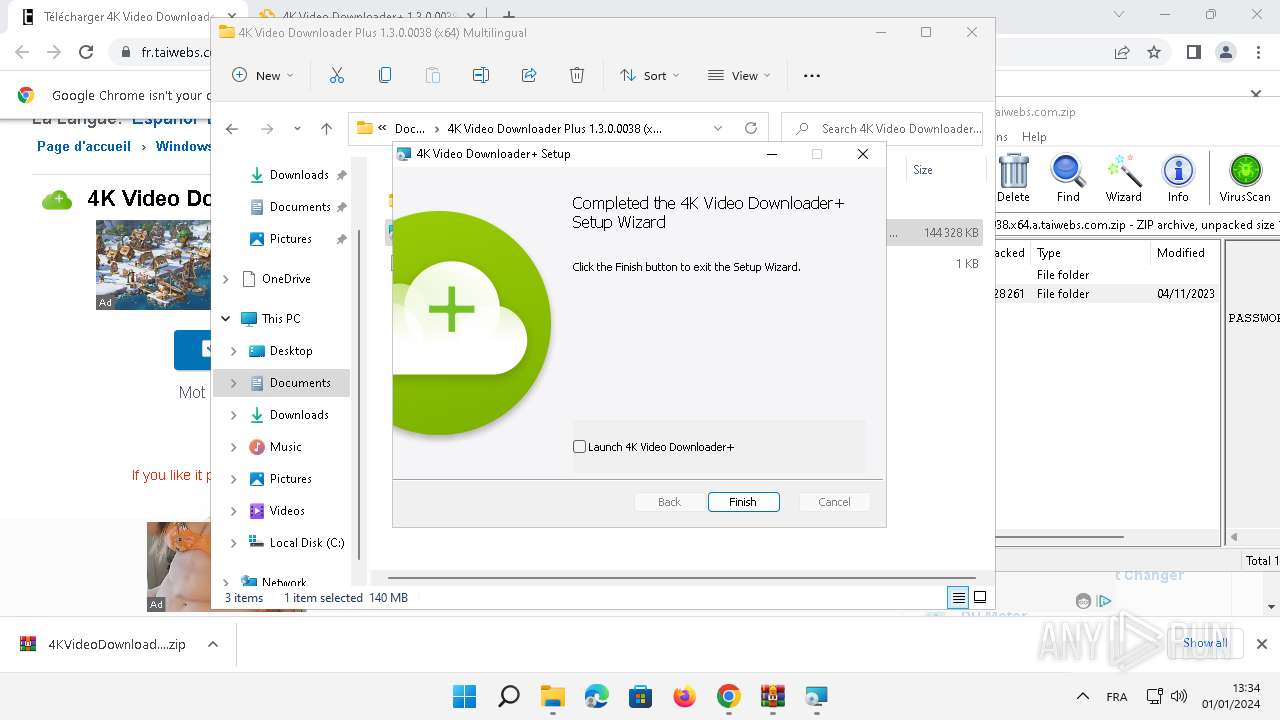
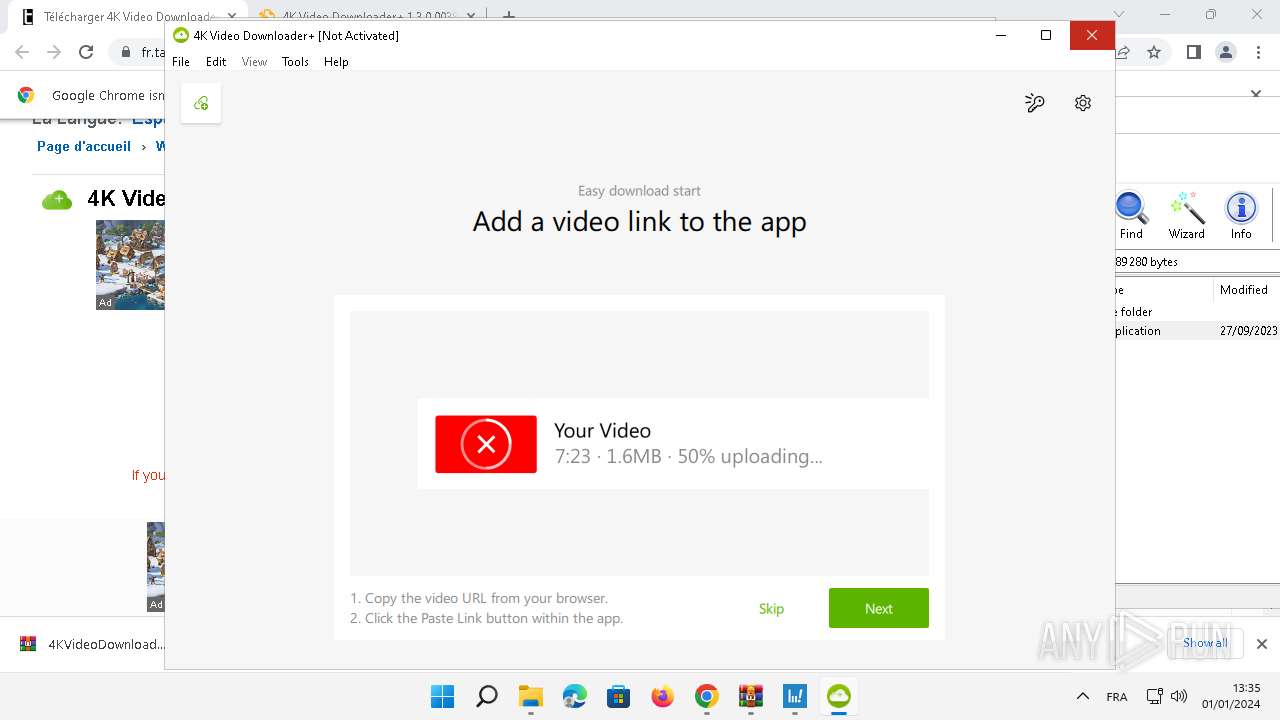
| URL: | https://fr.taiwebs.com/windows/download-4k-video-downloader-617.html |
| Full analysis: | https://app.any.run/tasks/f3238cda-33ce-4213-b7f3-aec3fb4ae021 |
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2024, 12:30:47 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MD5: | 0ECEA735591291E0B5ED3A5A55BA7545 |
| SHA1: | 6B0CAE1BF0116720CA3E73E4EC2D253831E4DC3B |
| SHA256: | 07BC923FFF8E29A4A68C12C1BF2DF066591B8552F6737A0E741B7CB5CF1DDBBD |
| SSDEEP: | 3:N8RiMSBGFMjKJROIXzuXsD0:2Rw0pPJD0 |
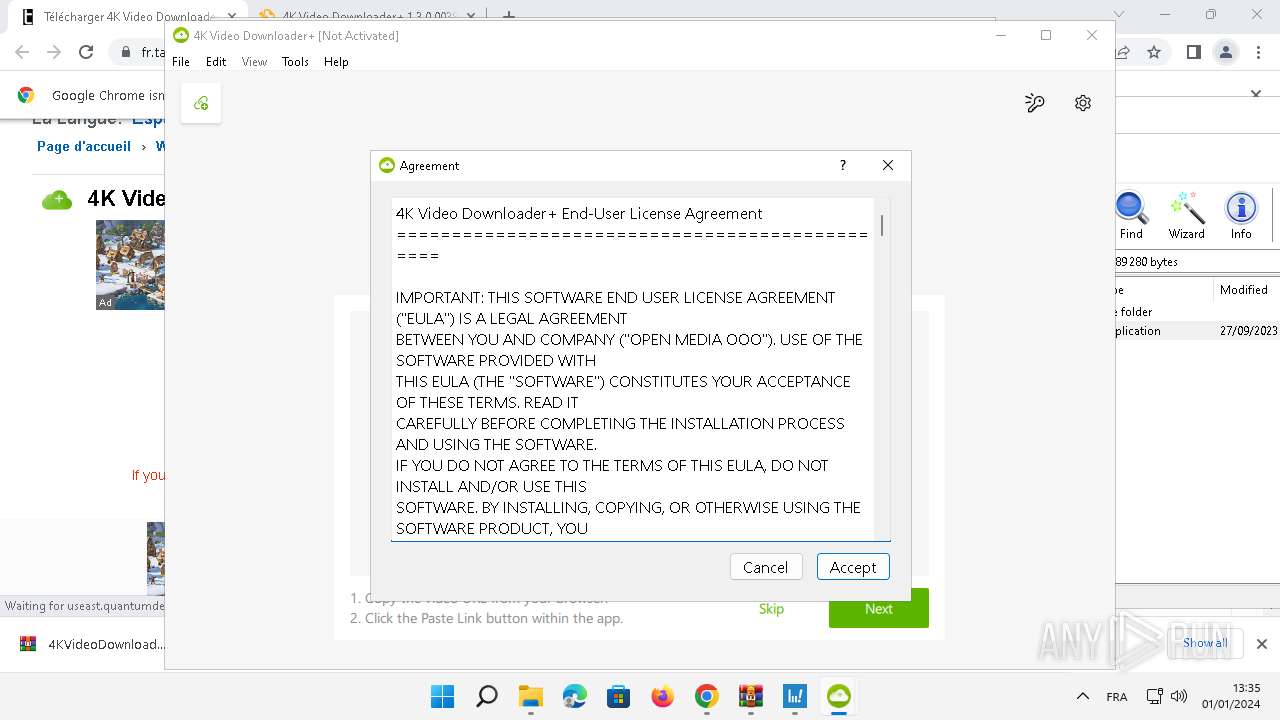
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- OpenWith.exe (PID: 8880)
- msiexec.exe (PID: 7640)
- 4kvideodownloaderplus.exe (PID: 4324)
Checks Windows Trust Settings
- msiexec.exe (PID: 7584)
Detected use of alternative data streams (AltDS)
- 4kvideodownloaderplus.exe (PID: 4324)
Reads settings of System Certificates
- 4kvideodownloaderplus.exe (PID: 4324)
INFO
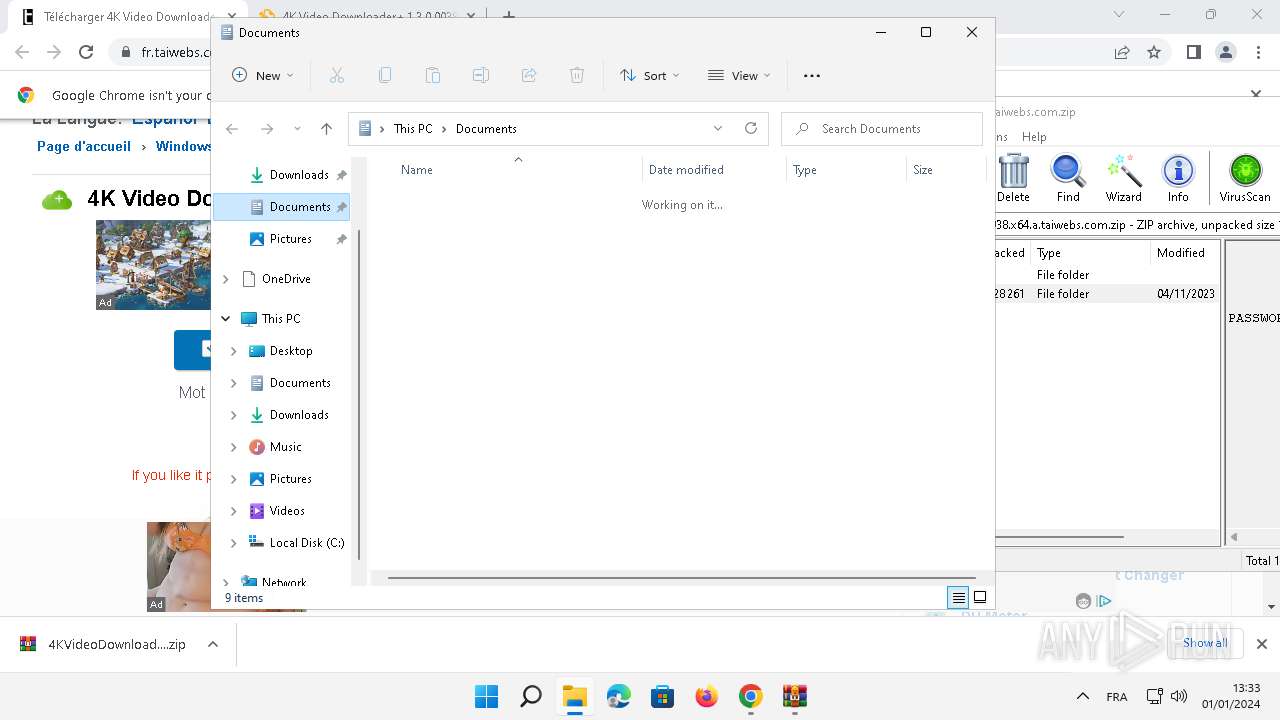
Drops the executable file immediately after the start
- chrome.exe (PID: 3780)
- msiexec.exe (PID: 7640)
- WinRAR.exe (PID: 1852)
- msiexec.exe (PID: 7584)
The process uses the downloaded file
- chrome.exe (PID: 8256)
- WinRAR.exe (PID: 8916)
- OpenWith.exe (PID: 8880)
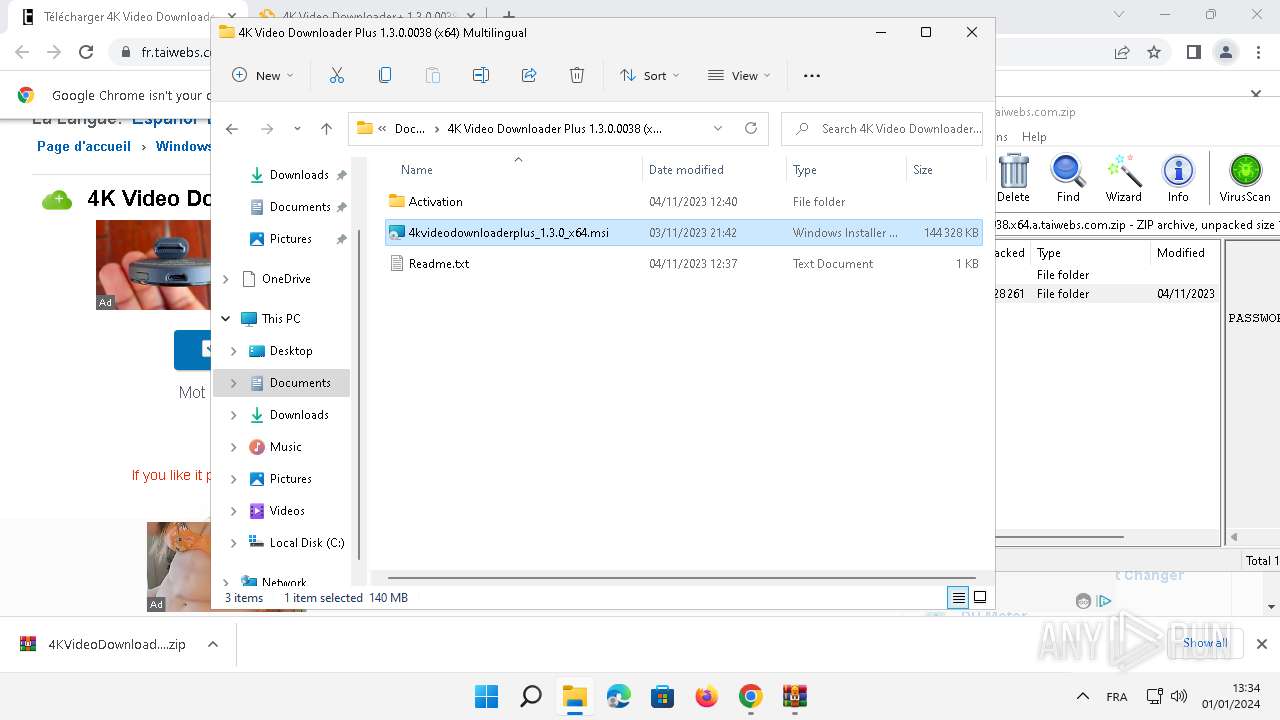
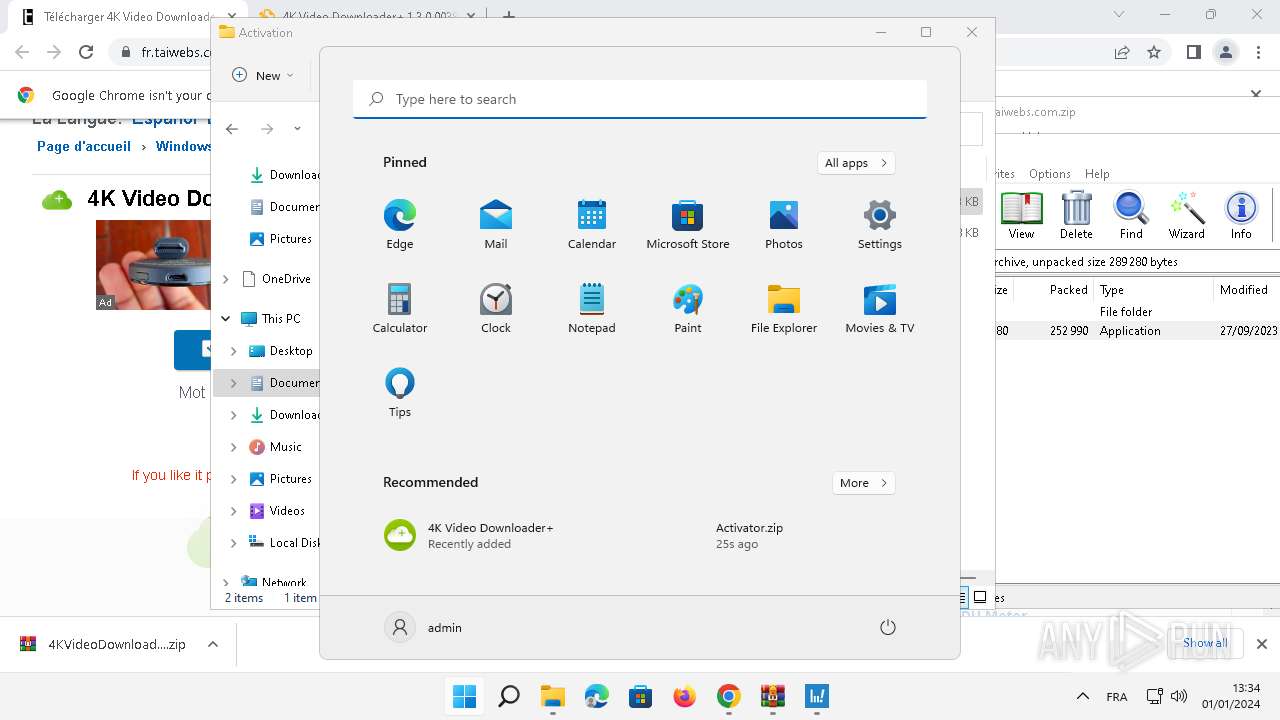
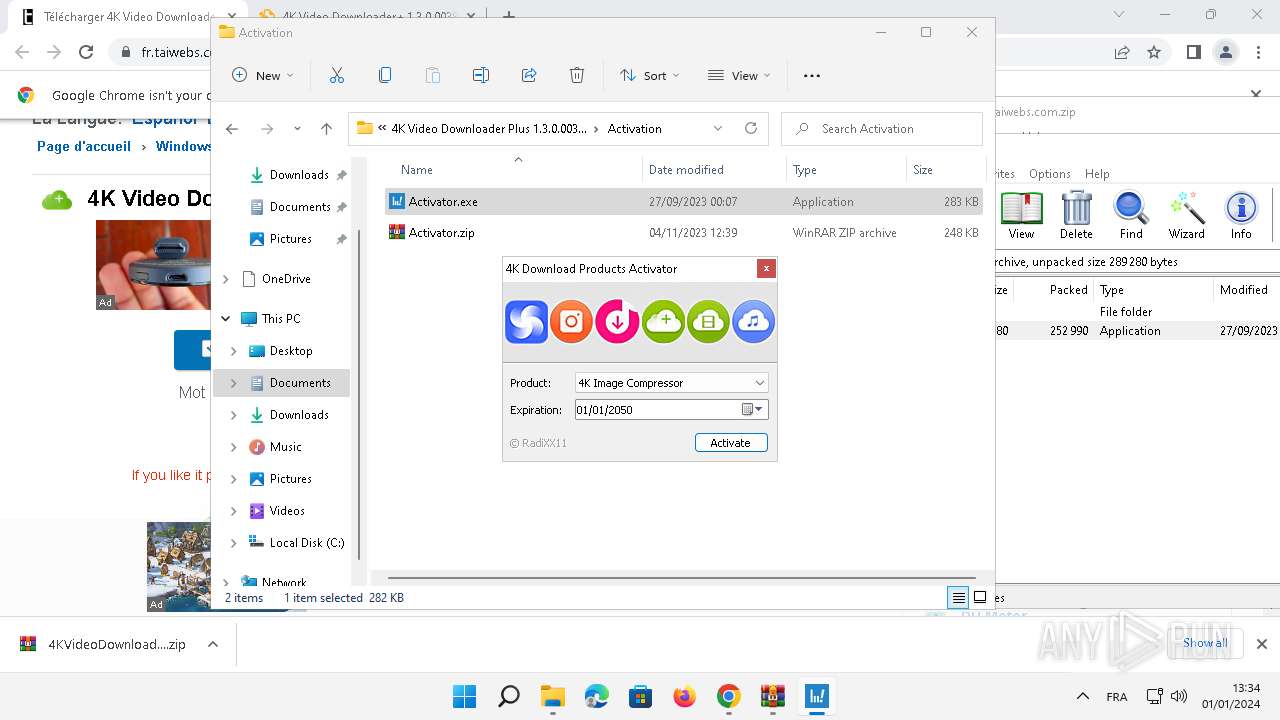
Manual execution by a user
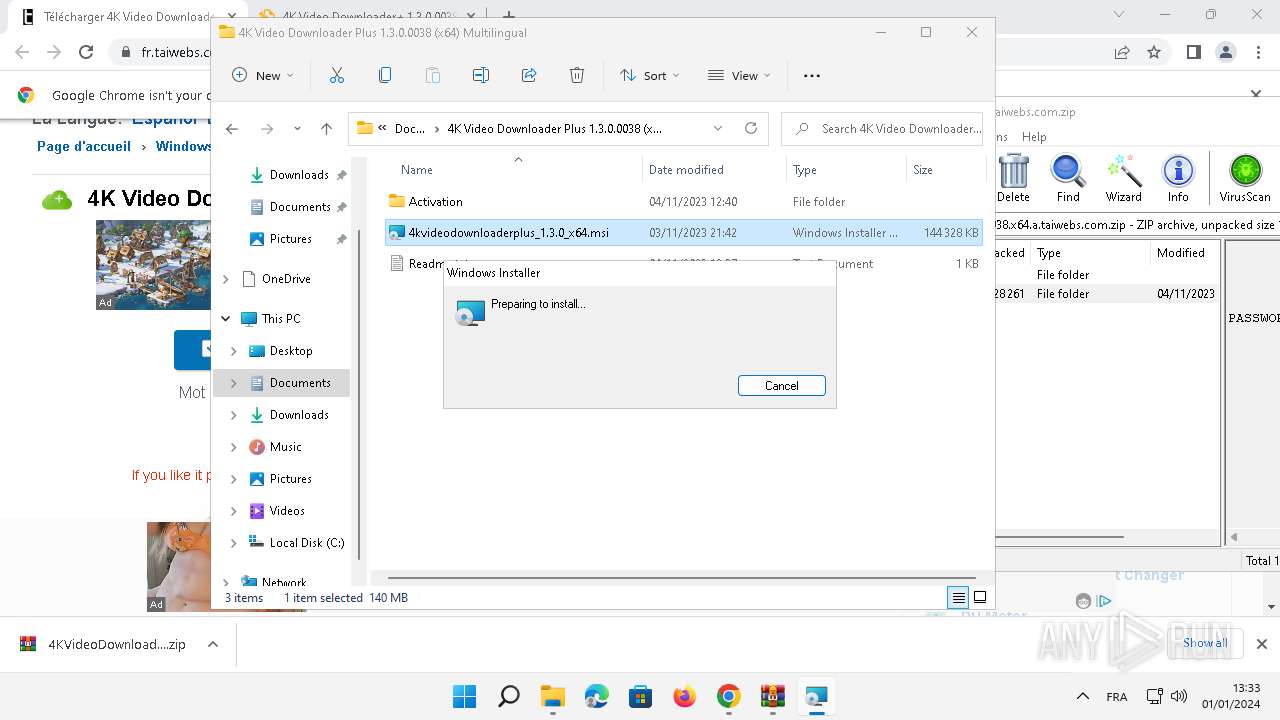
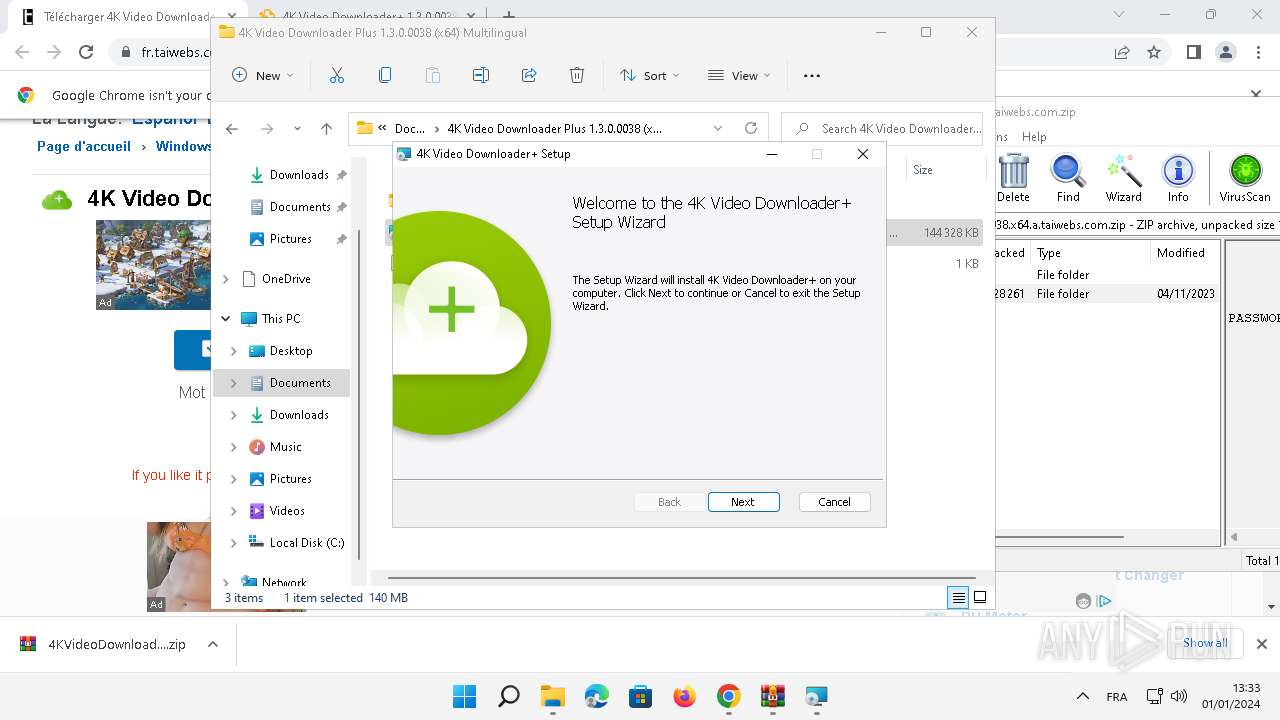
- msiexec.exe (PID: 7640)
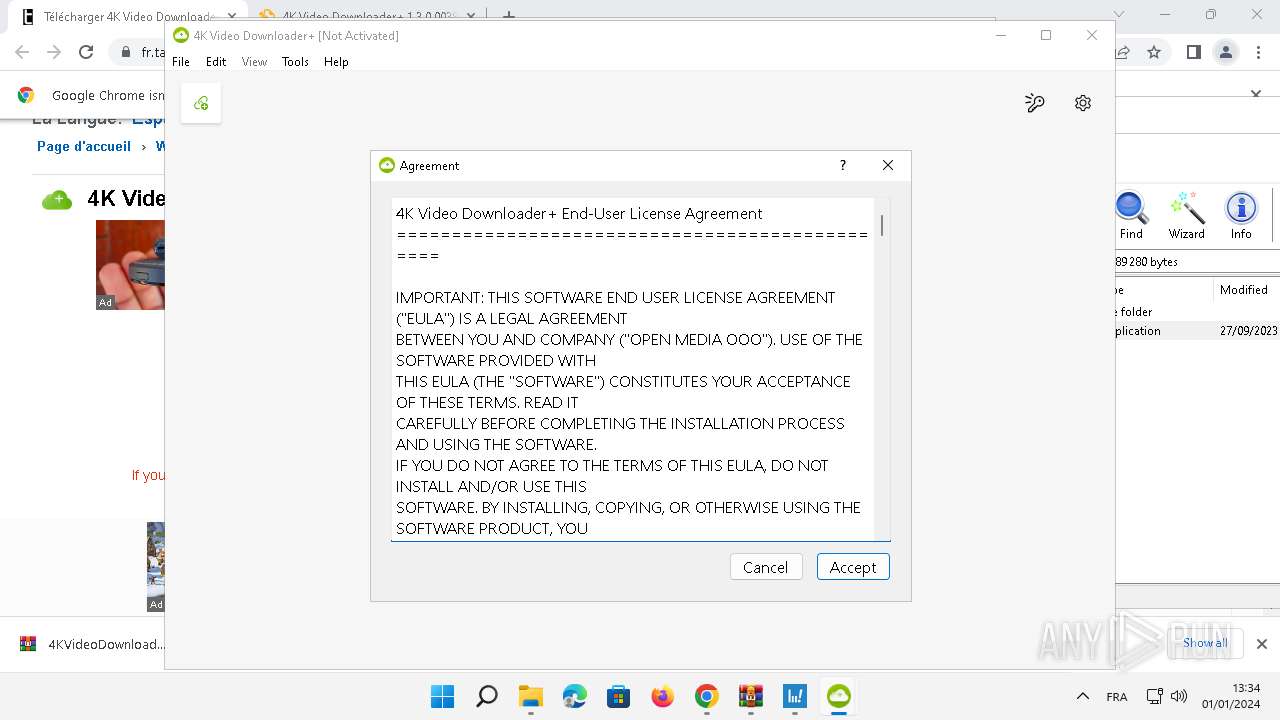
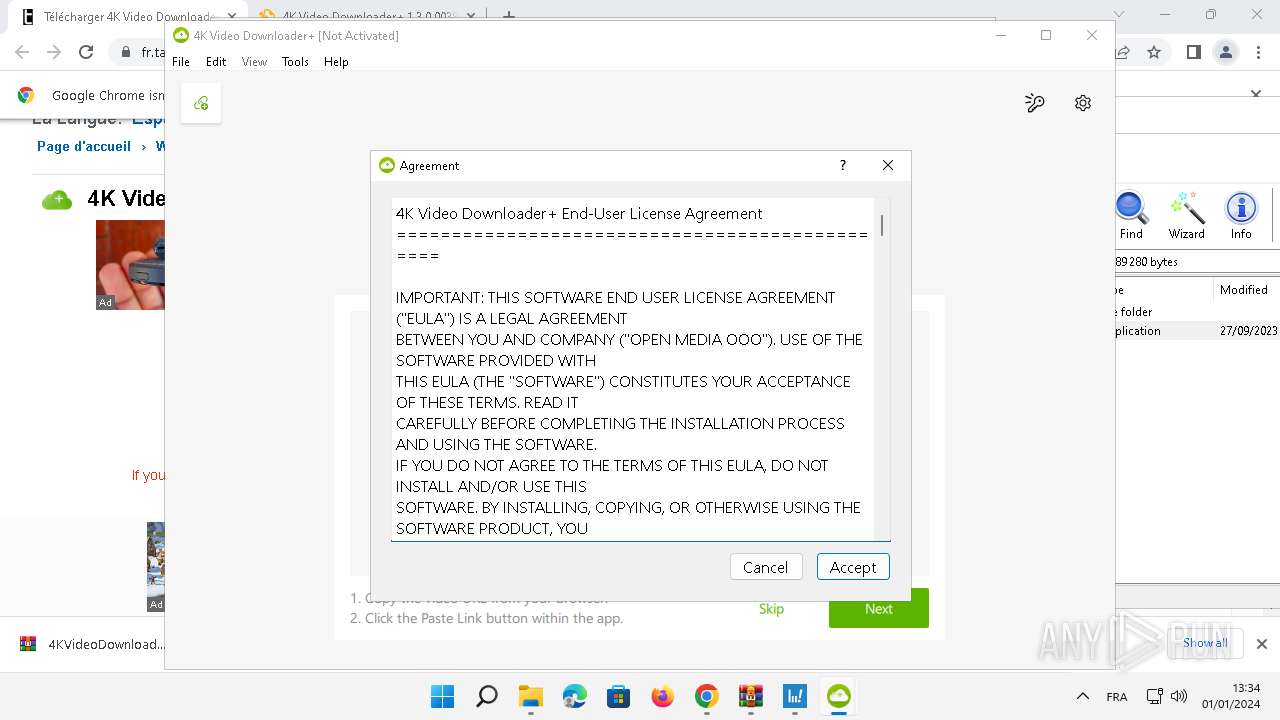
- 4kvideodownloaderplus.exe (PID: 4324)
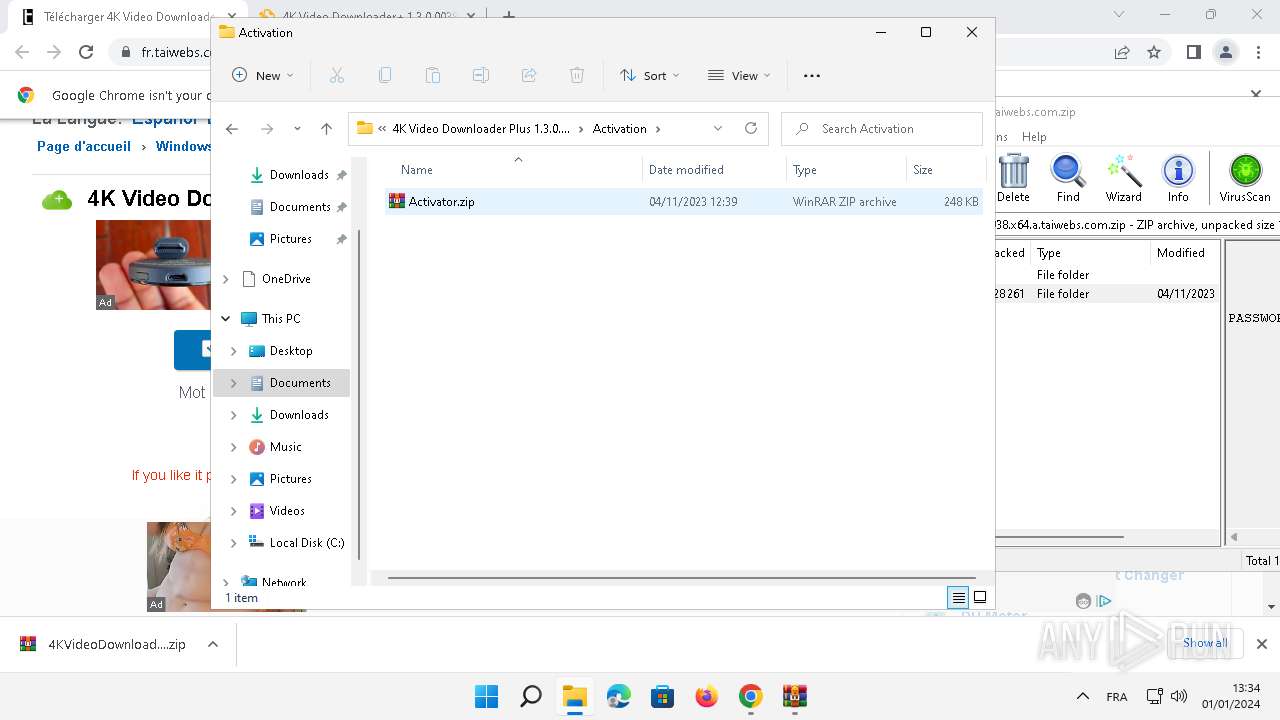
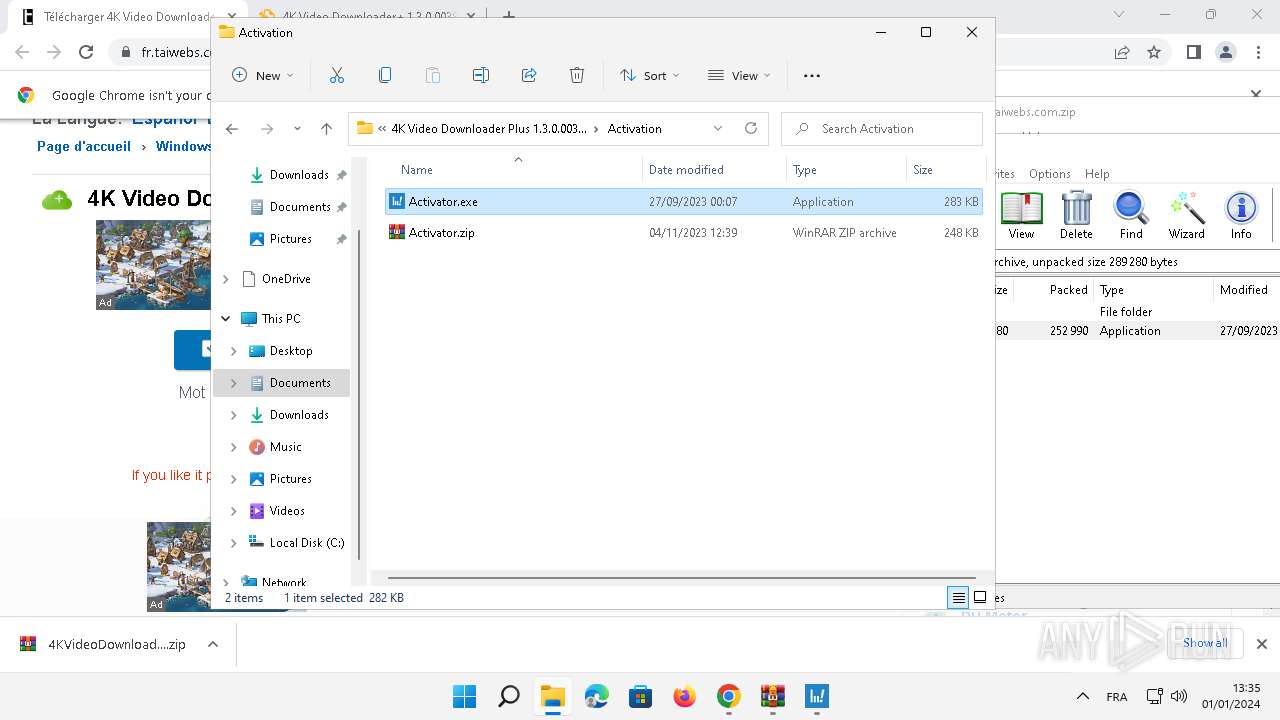
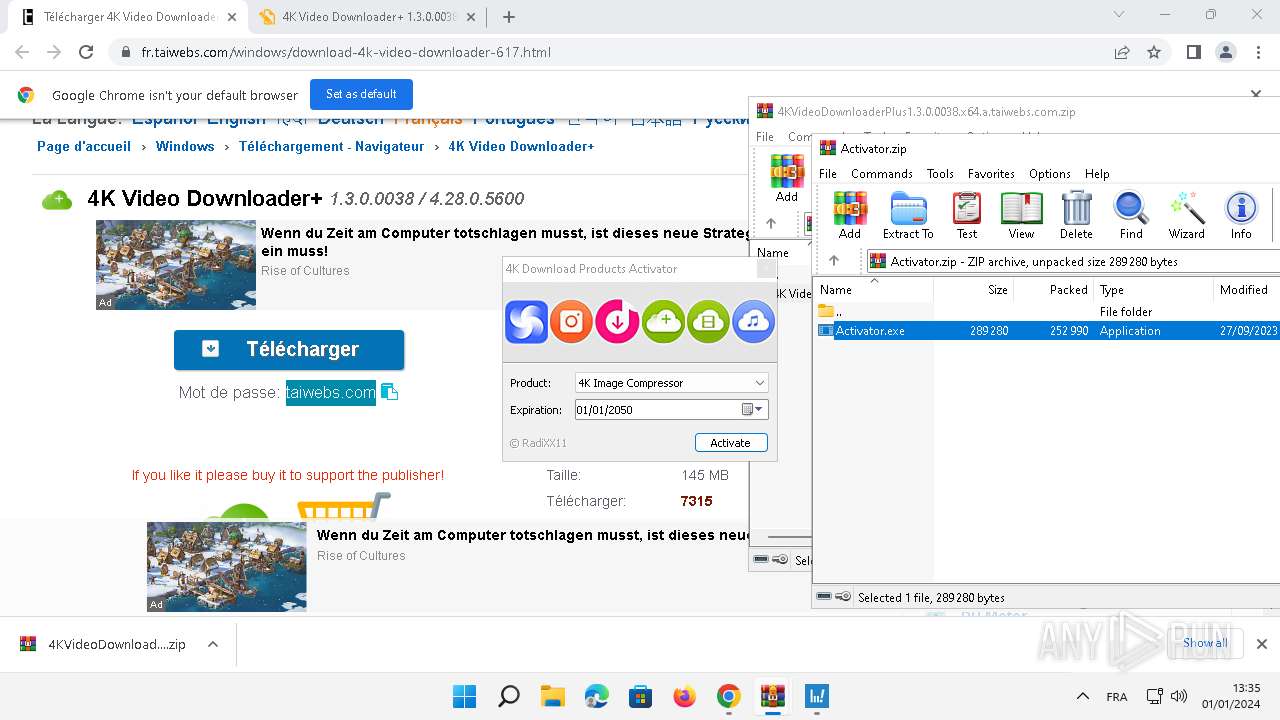
- WinRAR.exe (PID: 1852)
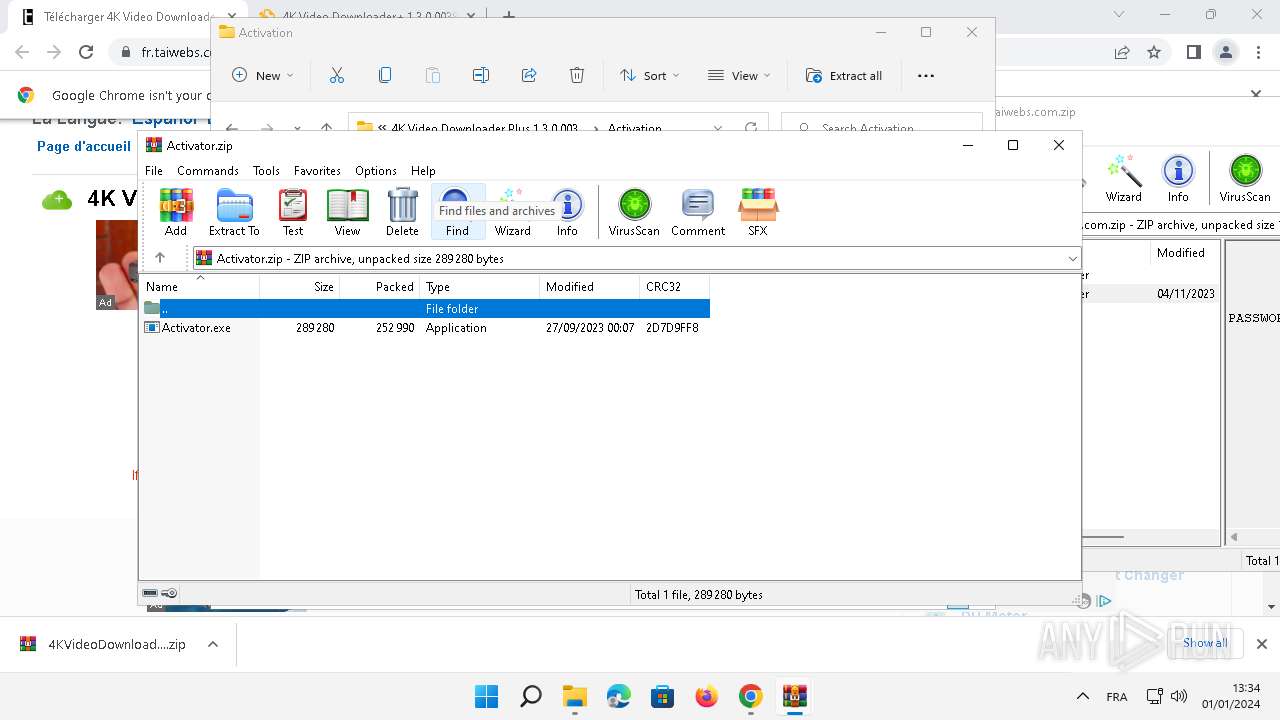
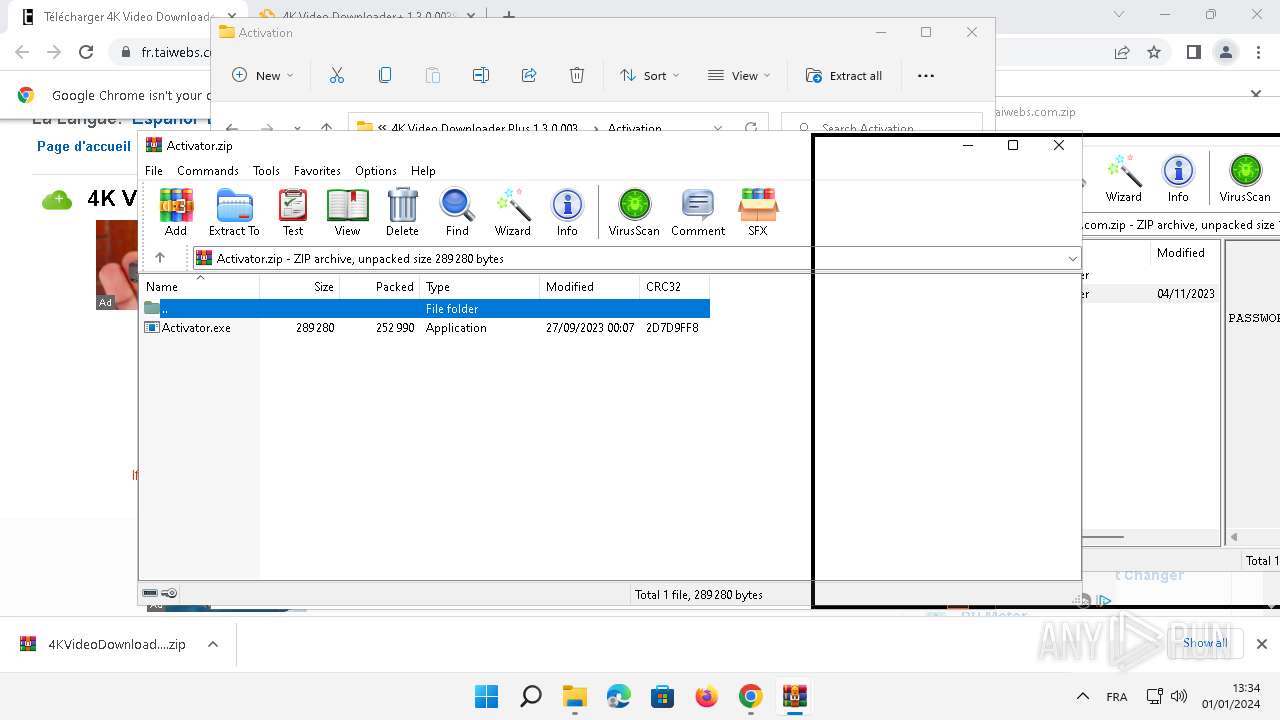
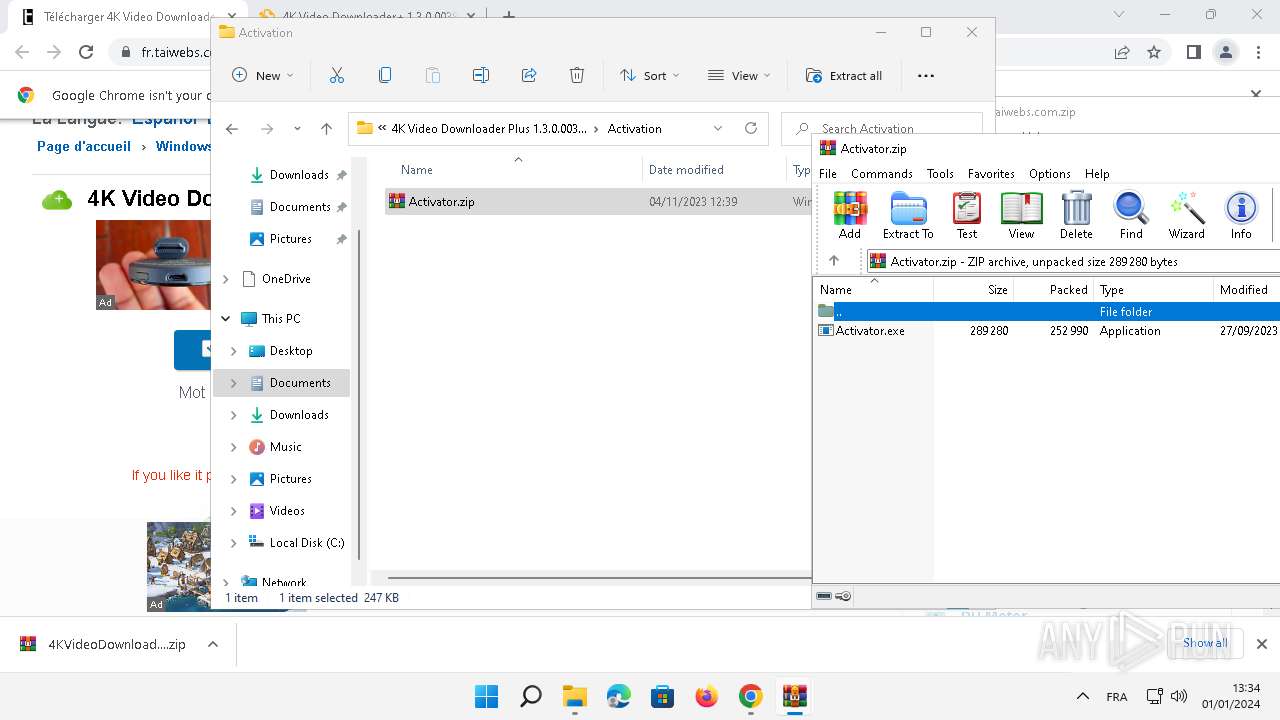
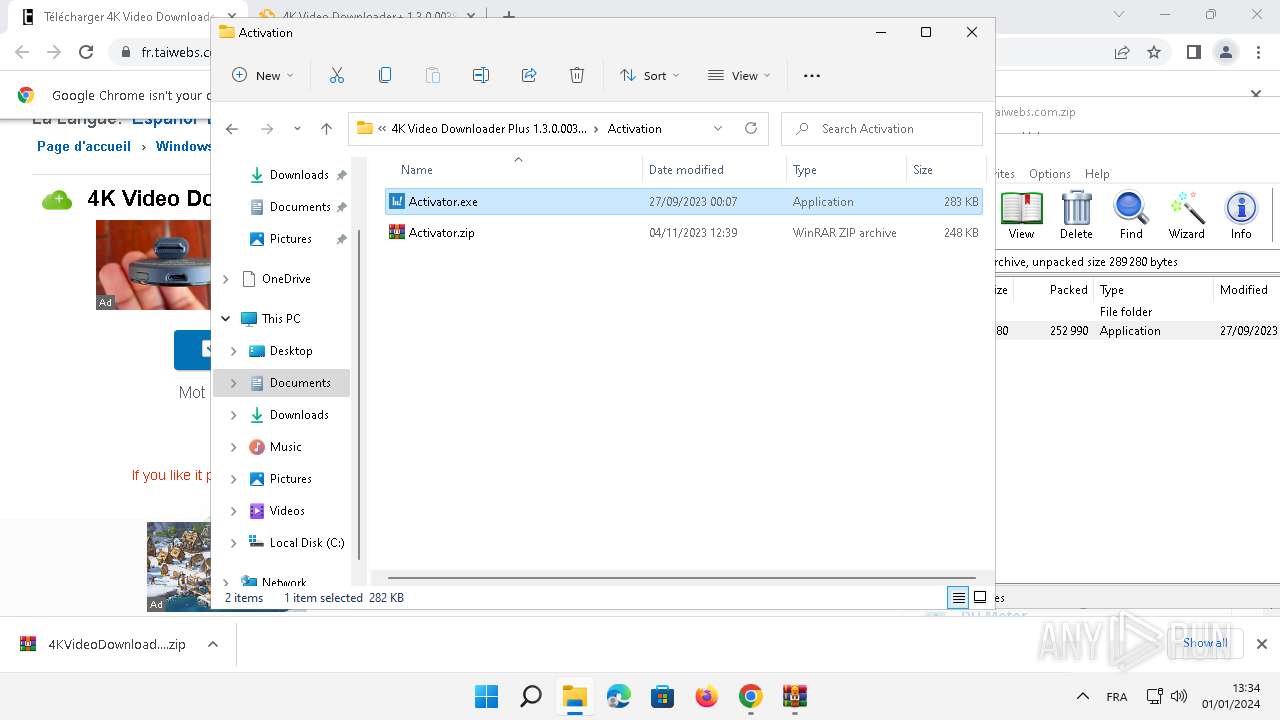
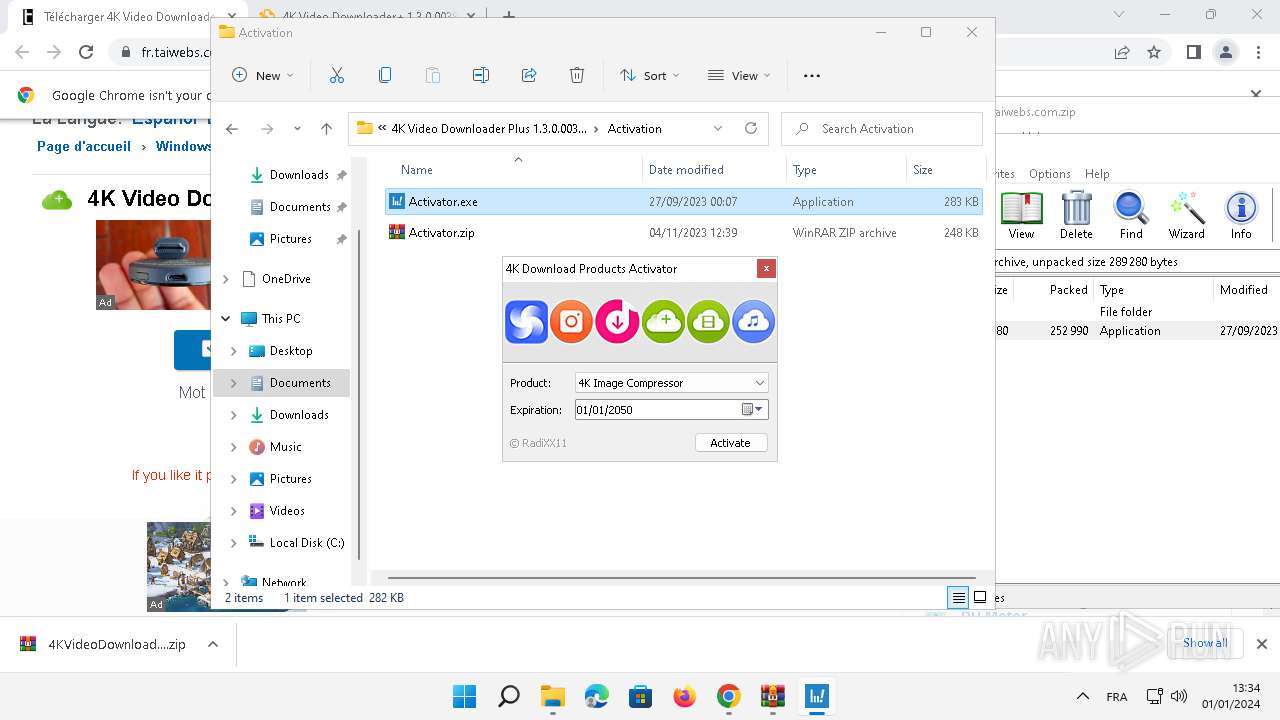
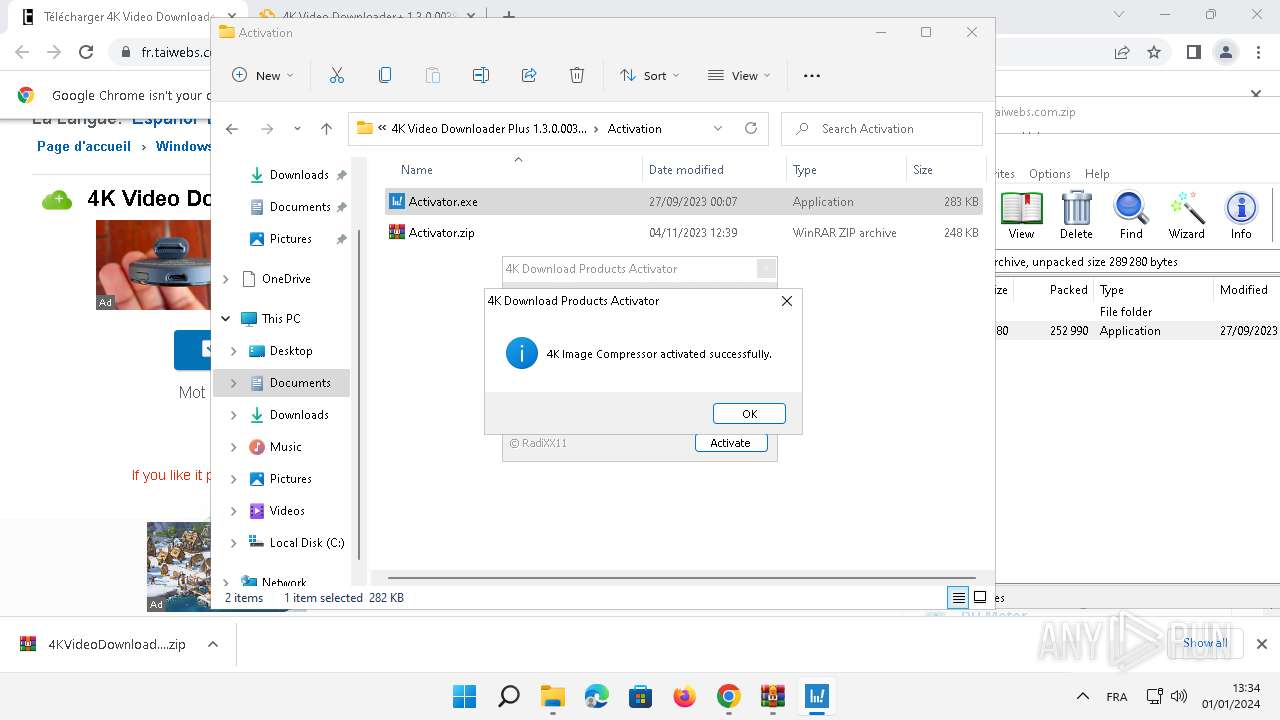
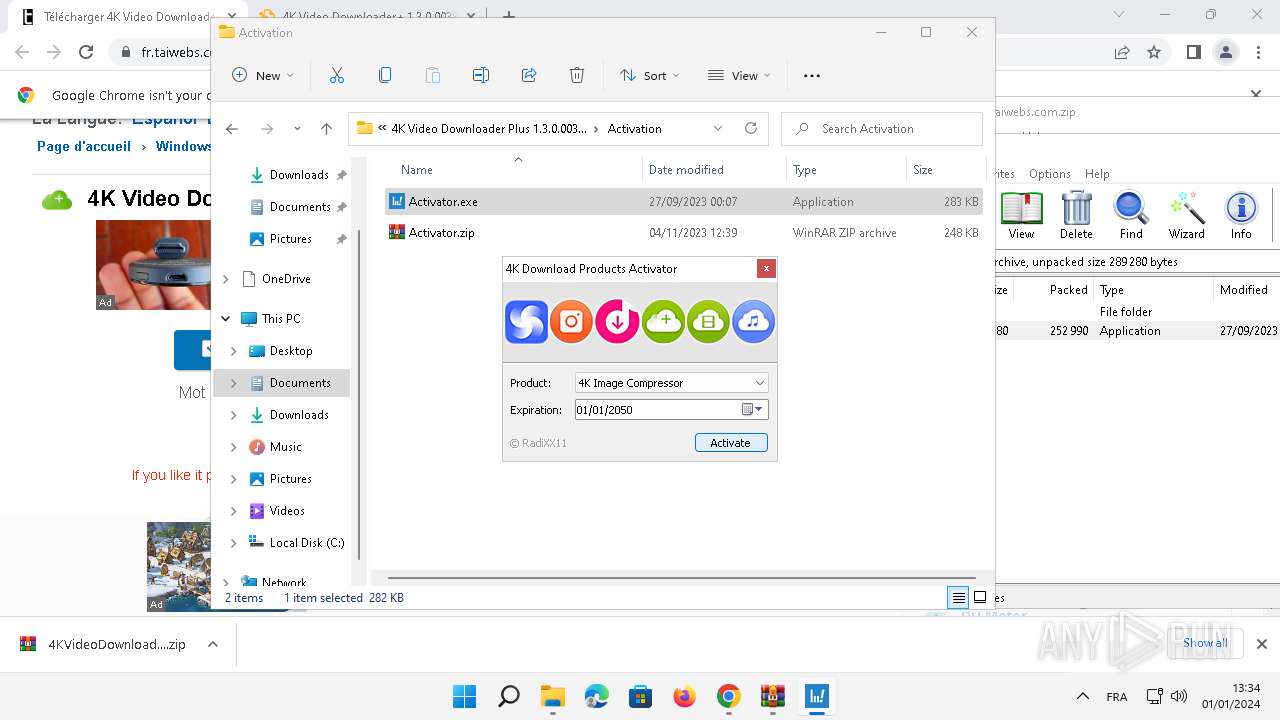
- Activator.exe (PID: 3948)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7640)
Checks proxy server information
- msiexec.exe (PID: 7640)
Reads the computer name
- msiexec.exe (PID: 7584)
- msiexec.exe (PID: 7296)
- msiexec.exe (PID: 1316)
- msiexec.exe (PID: 4128)
- msiexec.exe (PID: 4236)
- Activator.exe (PID: 3948)
- MiniSearchHost.exe (PID: 1640)
- 4kvideodownloaderplus.exe (PID: 4324)
- QtWebEngineProcess.exe (PID: 4344)
- QtWebEngineProcess.exe (PID: 6076)
- QtWebEngineProcess.exe (PID: 5060)
- identity_helper.exe (PID: 6324)
- identity_helper.exe (PID: 7476)
Application launched itself
- chrome.exe (PID: 3228)
- msiexec.exe (PID: 7584)
- msedge.exe (PID: 1836)
- msedge.exe (PID: 3484)
Creates files or folders in the user directory
- msiexec.exe (PID: 7640)
- 4kvideodownloaderplus.exe (PID: 4324)
Checks supported languages
- msiexec.exe (PID: 7296)
- msiexec.exe (PID: 7584)
- msiexec.exe (PID: 1316)
- msiexec.exe (PID: 4128)
- msiexec.exe (PID: 4236)
- Activator.exe (PID: 3948)
- MiniSearchHost.exe (PID: 1640)
- 4kvideodownloaderplus.exe (PID: 4324)
- crashpad_handler.exe (PID: 7044)
- QtWebEngineProcess.exe (PID: 6076)
- QtWebEngineProcess.exe (PID: 4344)
- QtWebEngineProcess.exe (PID: 5060)
- identity_helper.exe (PID: 6324)
- identity_helper.exe (PID: 7476)
Reads Environment values
- msiexec.exe (PID: 7296)
Executes as Windows Service
- VSSVC.exe (PID: 8104)
Process drops legitimate windows executable
- msiexec.exe (PID: 7584)
The process drops C-runtime libraries
- msiexec.exe (PID: 7584)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7584)
- 4kvideodownloaderplus.exe (PID: 4324)
Create files in a temporary directory
- 4kvideodownloaderplus.exe (PID: 4324)
Process checks computer location settings
- 4kvideodownloaderplus.exe (PID: 4324)
Connects to unusual port
- 4kvideodownloaderplus.exe (PID: 4324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
235
Monitored processes
124
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4028 --field-trial-handle=1924,i,9639054957954479458,8258623493041535895,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 112.0.5615.50 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=112.0.5615.50 --initial-client-data=0x114,0x118,0x11c,0xec,0x120,0x7ff890d6aa60,0x7ff890d6aa70,0x7ff890d6aa80 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 112.0.5615.50 Modules
| |||||||||||||||
| 1316 | C:\Windows\syswow64\MsiExec.exe -Embedding 0BC58DAAF20EE047E82AEB5AB96324EE C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3588 --field-trial-handle=2256,i,16784887849667588872,15887806456029246993,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=6628 --field-trial-handle=2056,i,6753292497500312080,4288588073118519799,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1640 | "C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\MiniSearchHost.exe" -ServerName:MiniSearchUI.AppXj3y73at8fy1htwztzxs68sxx1v7cksp7.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\MiniSearchHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 421.22500.3595.0 Modules
| |||||||||||||||
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2548 --field-trial-handle=2256,i,16784887849667588872,15887806456029246993,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1832 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3004 --field-trial-handle=1924,i,9639054957954479458,8258623493041535895,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 112.0.5615.50 Modules
| |||||||||||||||
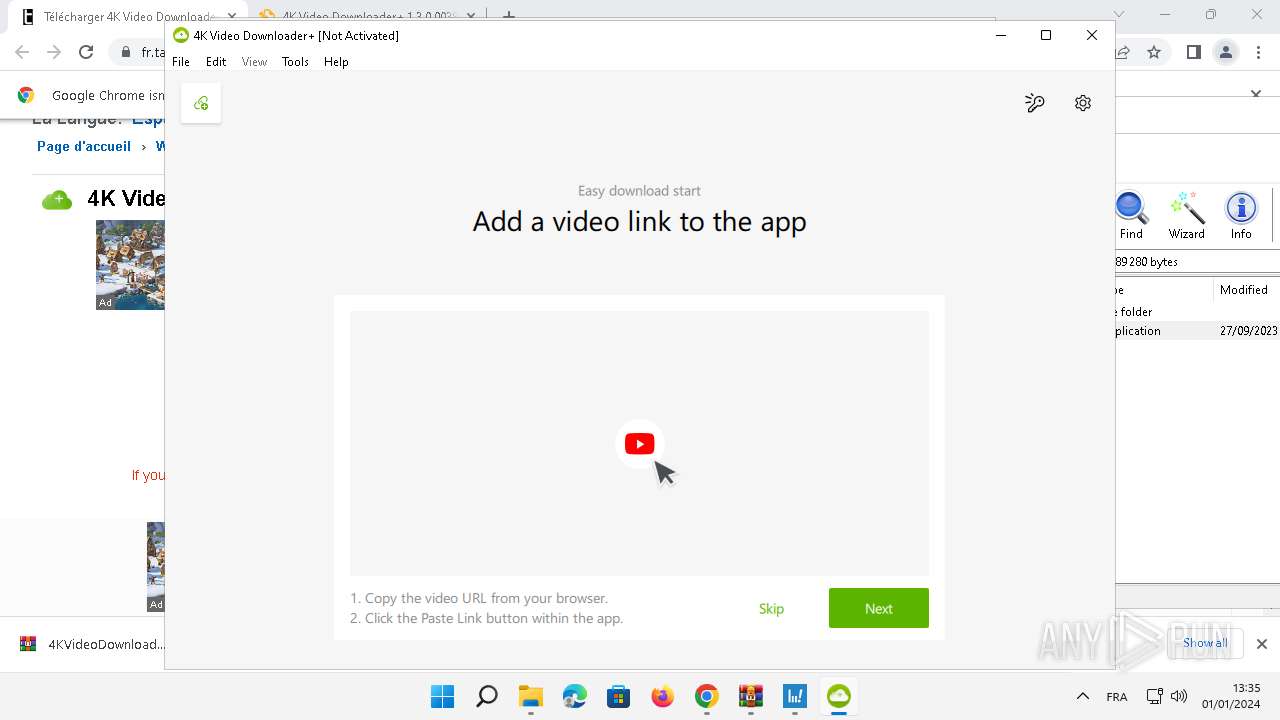
| 1836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.4kdownload.com/thanks-for-installing?source=videodownloaderplus&redirect-locale=fr&install=first | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | 4kvideodownloaderplus.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
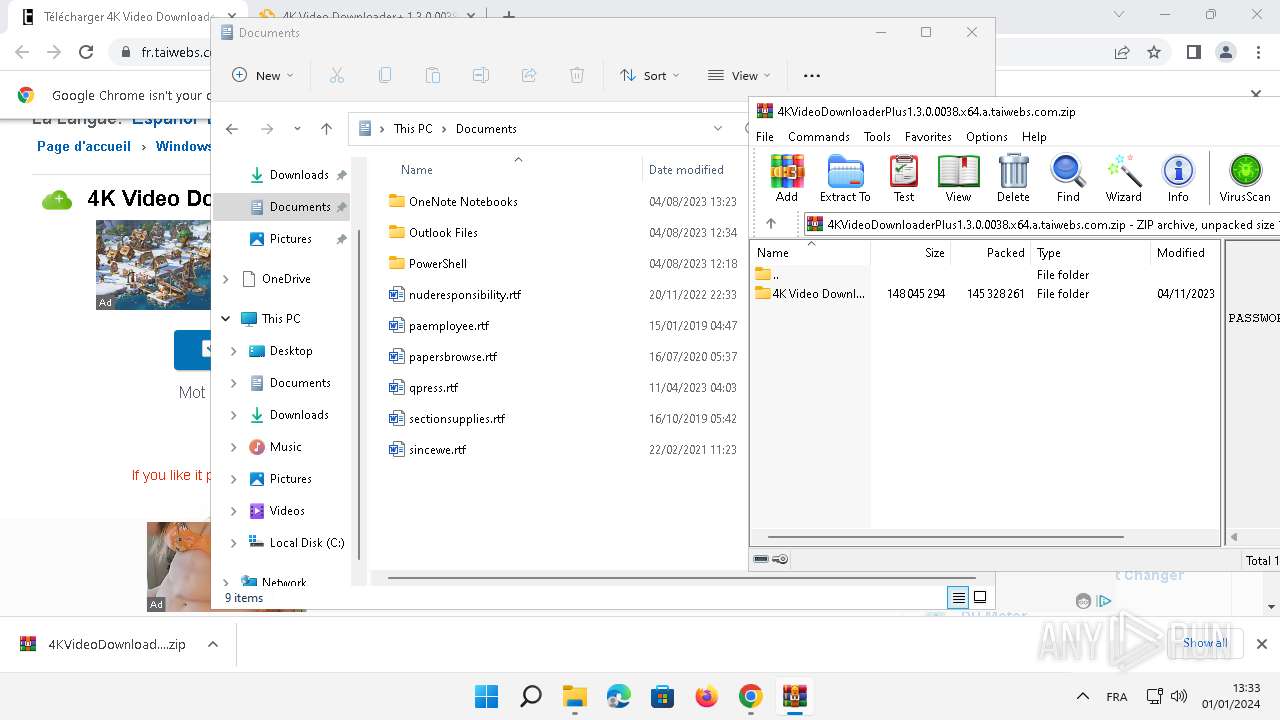
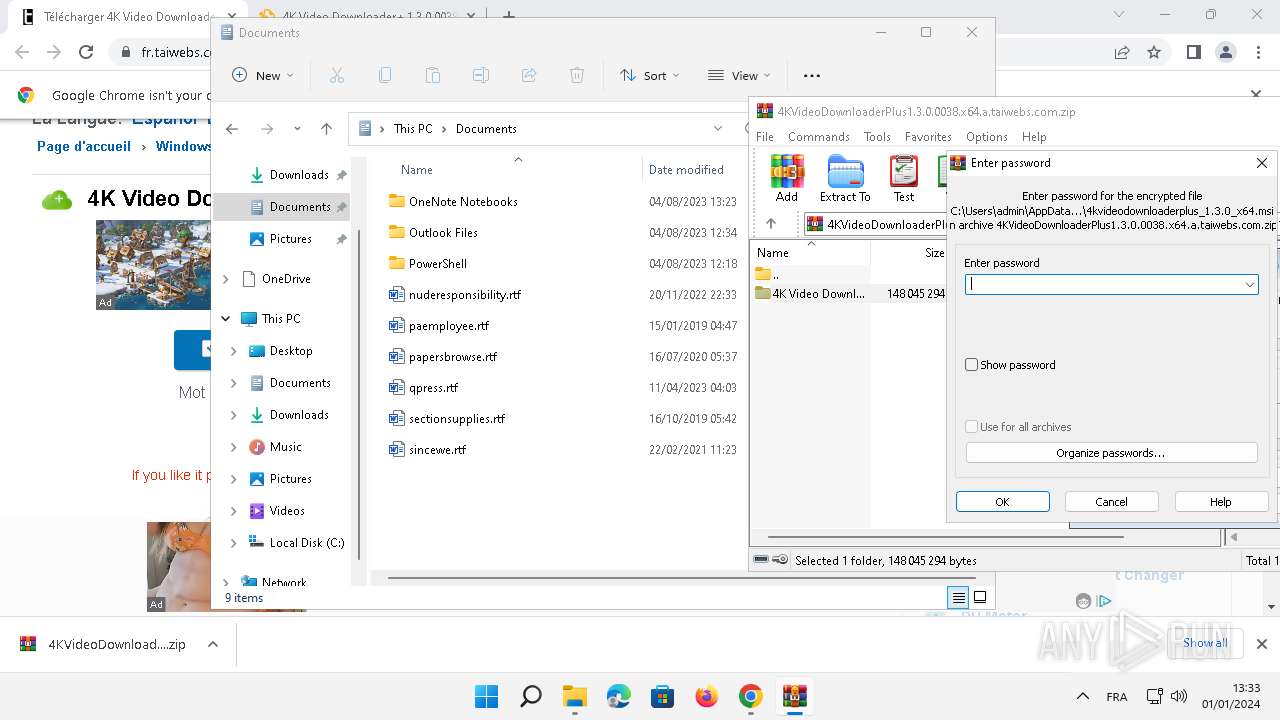
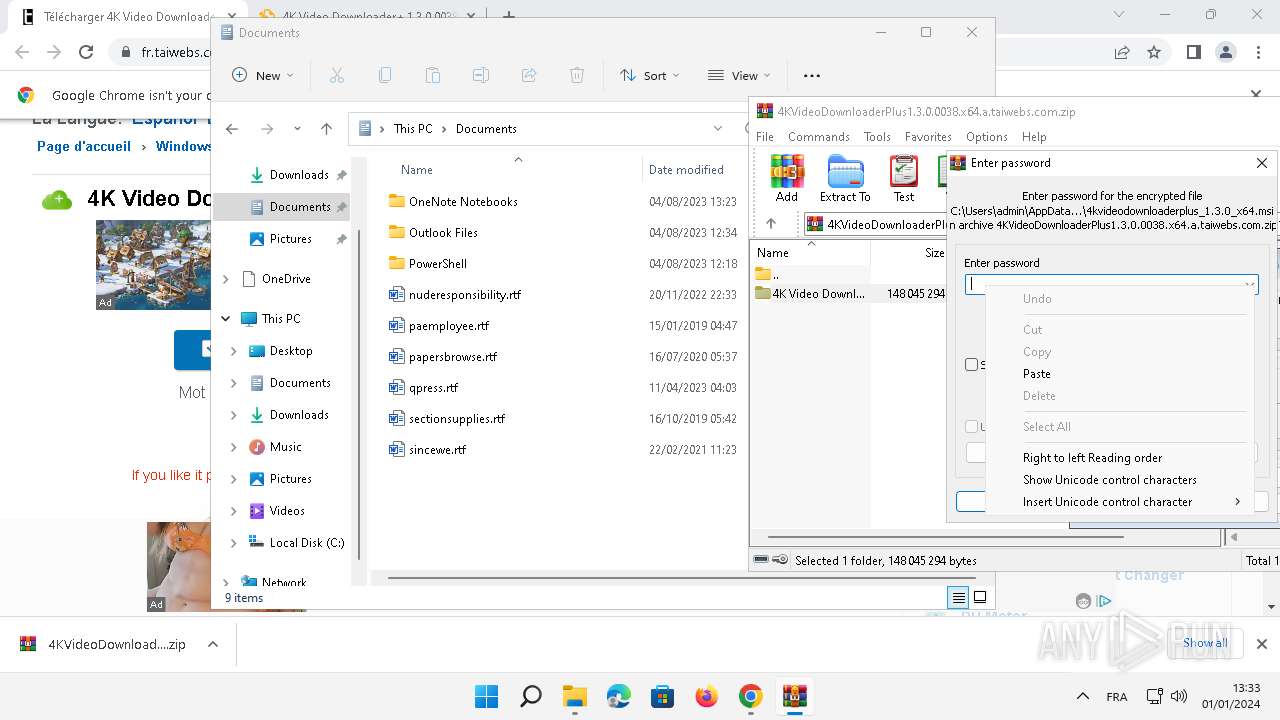
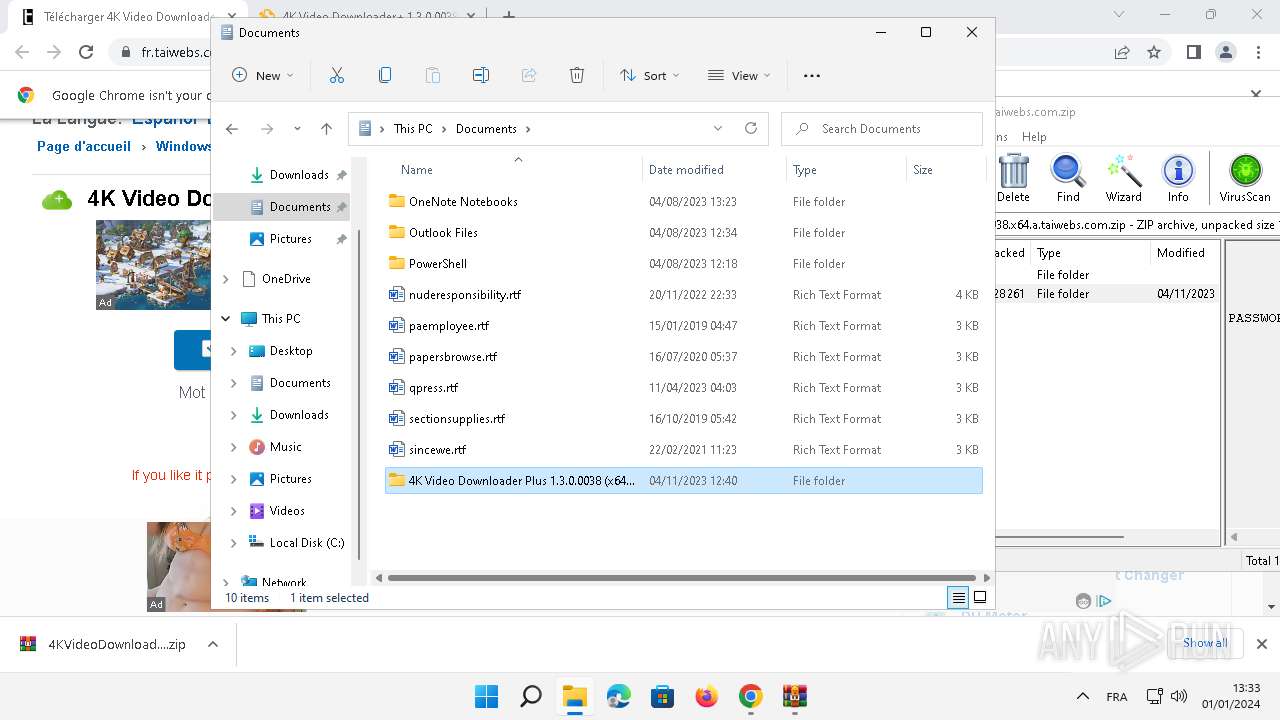
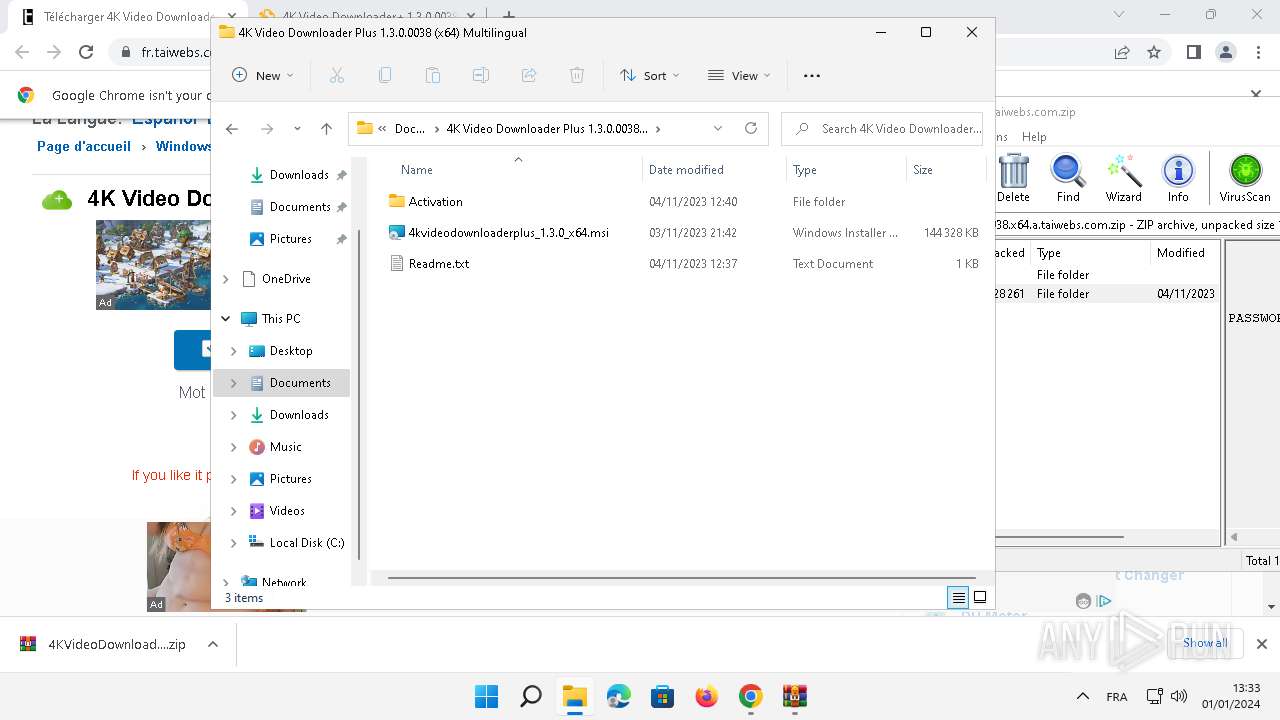
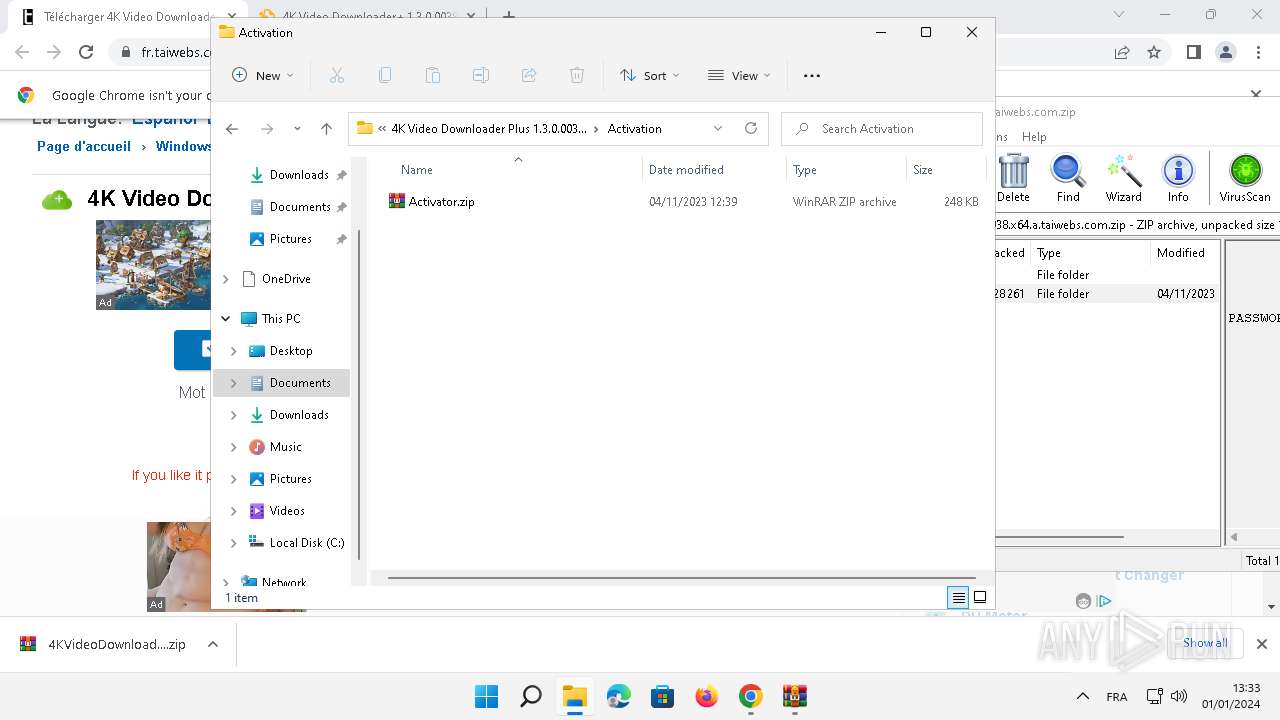
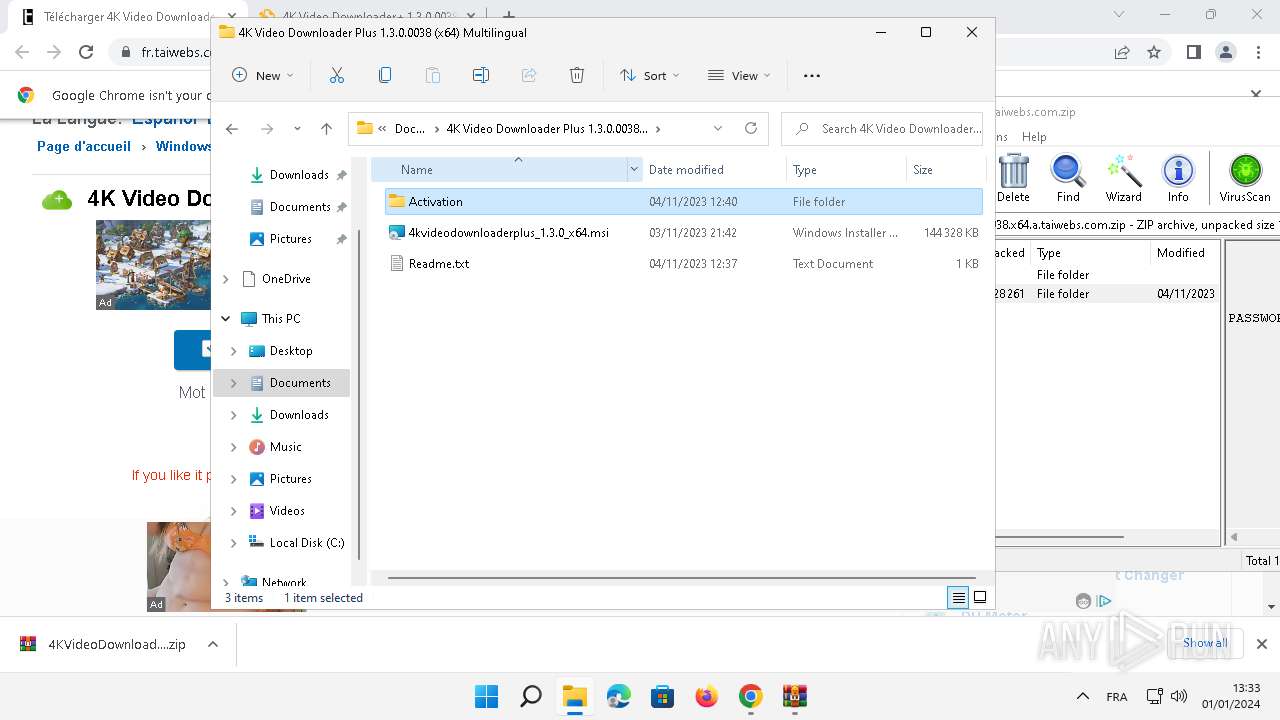
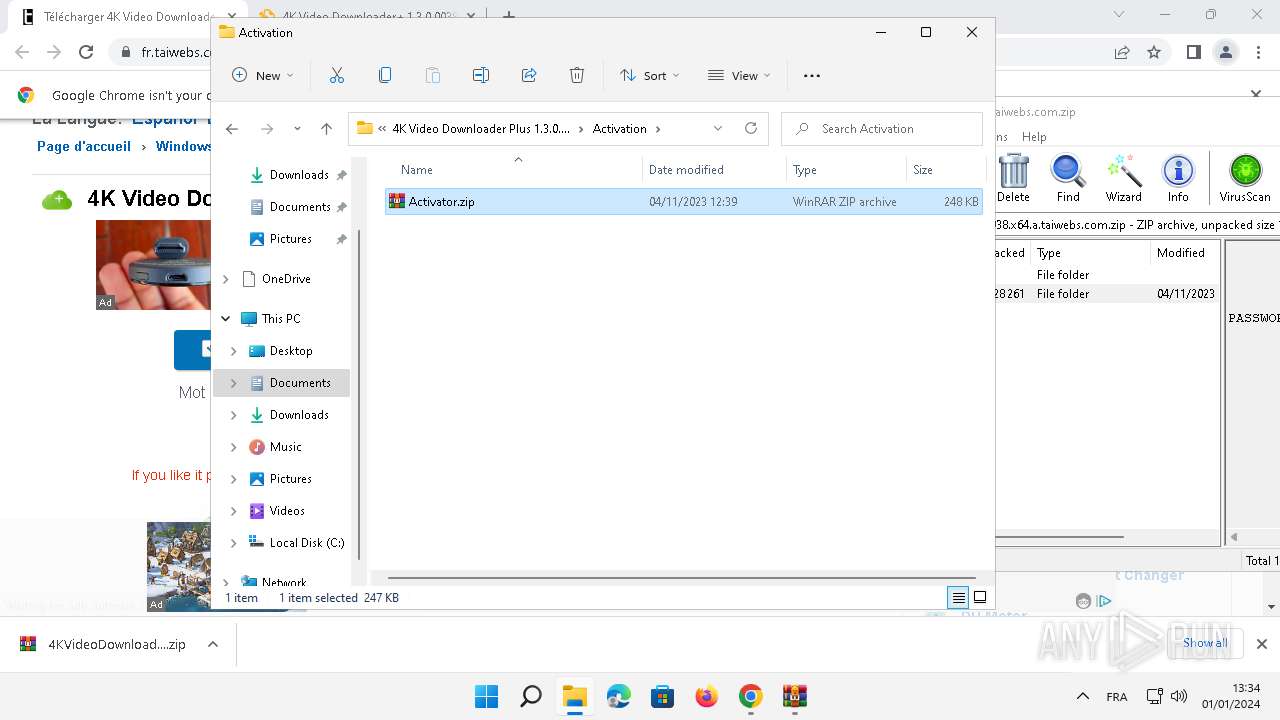
| 1852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Documents\4K Video Downloader Plus 1.3.0.0038 (x64) Multilingual\Activation\Activator.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
49 662
Read events
49 456
Write events
189
Delete events
17
Modification events
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
89
Suspicious files
883
Text files
414
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe2bbf.TMP | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:858B51004CDB48854BA078F75A43ECFB | SHA256:78A581395DB475C3703E4EEF3E3067BC30404B0B4685D10A768BBE1463883FE5 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe2e6e.TMP | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\USERS\ADMIN\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\VARIATIONS | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe2bce.TMP | text | |
MD5:9AFA158F26CE275667A102E80CCD037E | SHA256:21B0C15A516487434BD41AD685AAEF241667C45F343DBE7A92172B0FFAC4BEF9 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFe2c8a.TMP | text | |
MD5:A6053317AC622DE2C8BF659220909621 | SHA256:6428A9D5F65709FE30E8C0648E6C2D5762E3982D25EBD3BE3A8364A79B4183F1 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:BACC94C0F59D1DB67392A588F4ED3D17 | SHA256:46C118D73600F3AA46514EEAD09436163D7721F0F97663B02432EE1264420B18 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\01f462c5-a8e8-406a-b7f2-f886c0ca6bec.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
479
DNS requests
490
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4088 | smartscreen.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?44f112139d34e41c | unknown | compressed | 4.66 Kb | unknown |
4088 | smartscreen.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | binary | 471 b | unknown |
3752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1412 | svchost.exe | GET | 200 | 2.16.164.35:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | text | 22 b | unknown |
5944 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | — | — | unknown |
5944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 1.09 Kb | unknown |
4732 | chrome.exe | GET | 200 | 192.124.249.36:80 | http://certificates.godaddy.com/repository/gdig2.crt | unknown | binary | 1.21 Kb | unknown |
5944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 78 b | unknown |
5944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 5.38 Kb | unknown |
5944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 17.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4088 | smartscreen.exe | 20.105.95.163:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4088 | smartscreen.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
3228 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4088 | smartscreen.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4732 | chrome.exe | 172.67.222.18:443 | fr.taiwebs.com | CLOUDFLARENET | US | unknown |
4732 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4732 | chrome.exe | 104.18.11.207:443 | maxcdn.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
4732 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
4732 | chrome.exe | 104.22.58.199:443 | services.vlitag.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fr.taiwebs.com |
| unknown |
accounts.google.com |
| shared |
maxcdn.bootstrapcdn.com |
| whitelisted |
taiwebs.com |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |
services.vlitag.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4732 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1412 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
4732 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
4732 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7248 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
4kvideodownloaderplus.exe | QEventLoop: Cannot be used without QApplication
|