| File name: | sample1.bin |
| Full analysis: | https://app.any.run/tasks/91b2128f-4900-4778-b3f1-d3d4ad3f6458 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2022, 07:15:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DF8A2C219C032BEF70FE59D8D2EF393A |
| SHA1: | 2440B3EC995ACE60D31DCFBD9E4F011BAFFAD4FF |
| SHA256: | 07B8F25E7B536F5B6F686C12D04EDC37E11347C8ACD5C53F98A174723078C365 |
| SSDEEP: | 6144:TmcD66RRj05JGmrpQsK3RD2u270jupCJsCxCI:qcD663hZ2zkPaCxj |
MALICIOUS
Changes the autorun value in the registry
- sample1.bin.exe (PID: 2520)
Runs injected code in another process
- sample1.bin.exe (PID: 2520)
Application was injected by another process
- Explorer.EXE (PID: 528)
SUSPICIOUS
Checks supported languages
- sample1.bin.exe (PID: 2520)
- explorer.exe (PID: 352)
Executable content was dropped or overwritten
- sample1.bin.exe (PID: 2520)
Drops a file with too old compile date
- sample1.bin.exe (PID: 2520)
Creates files in the user directory
- sample1.bin.exe (PID: 2520)
Creates executable files which already exist in Windows
- sample1.bin.exe (PID: 2520)
Starts Internet Explorer
- sample1.bin.exe (PID: 2520)
Reads the computer name
- explorer.exe (PID: 352)
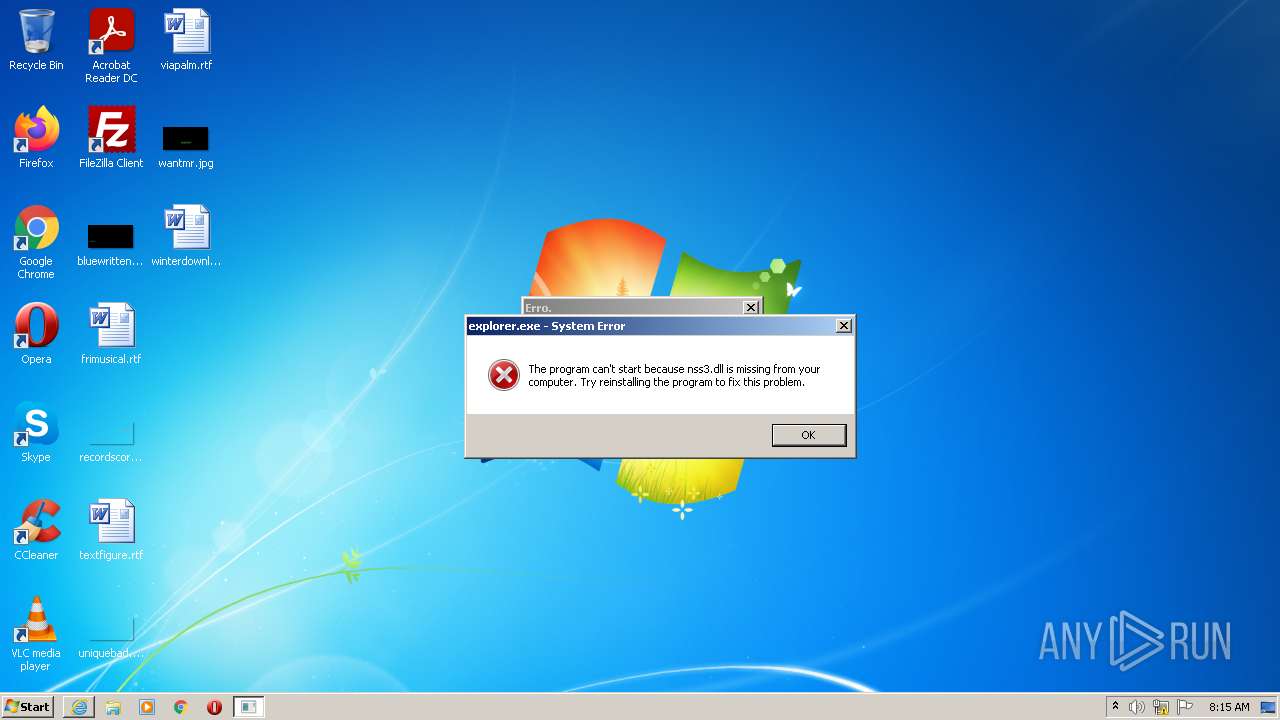
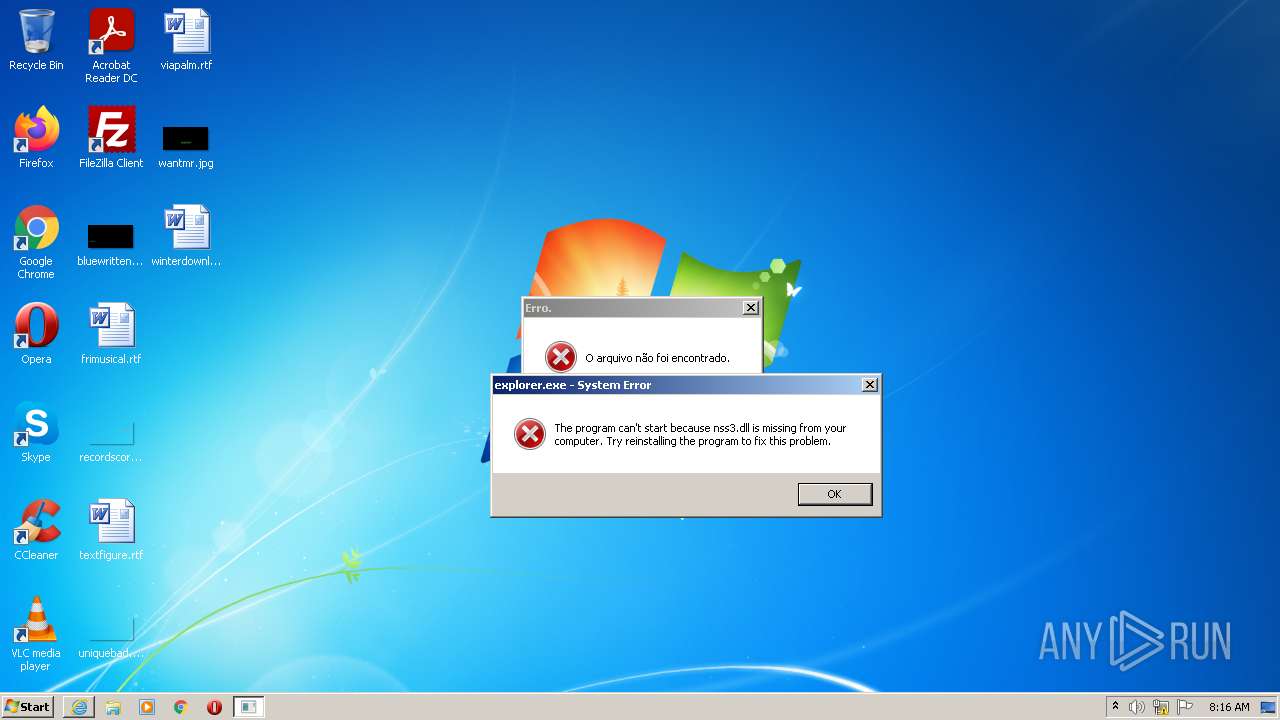
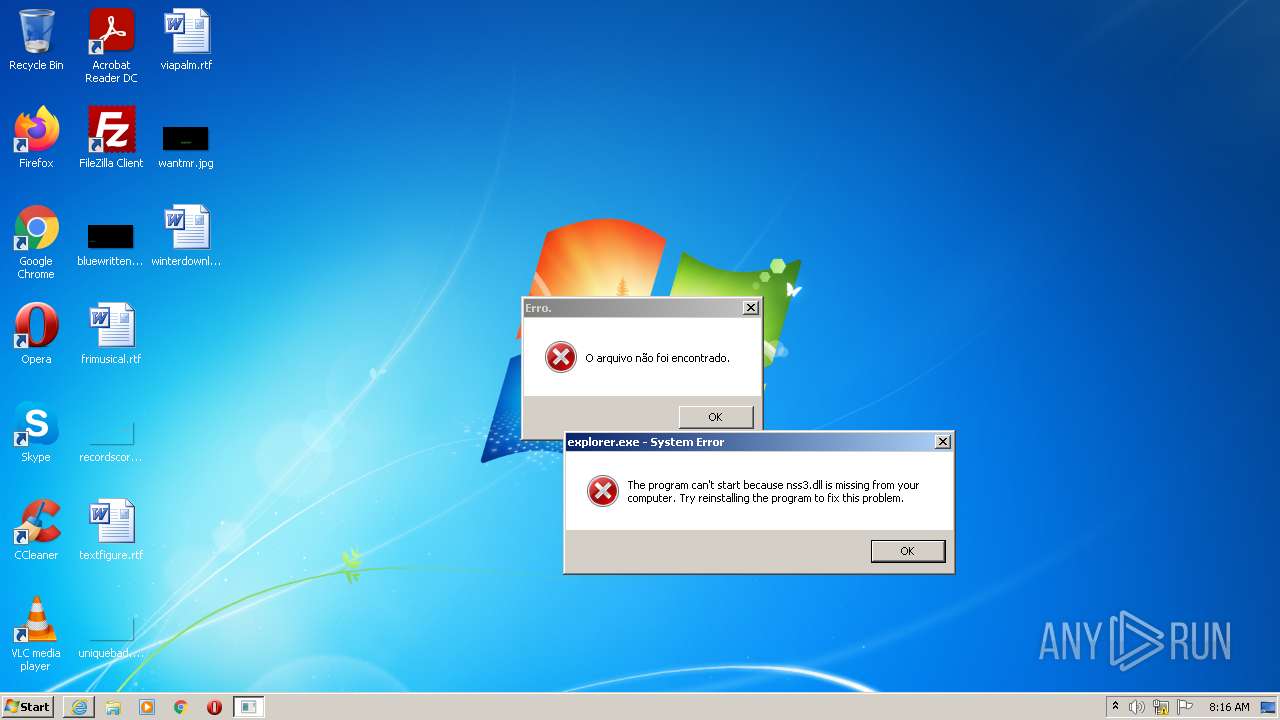
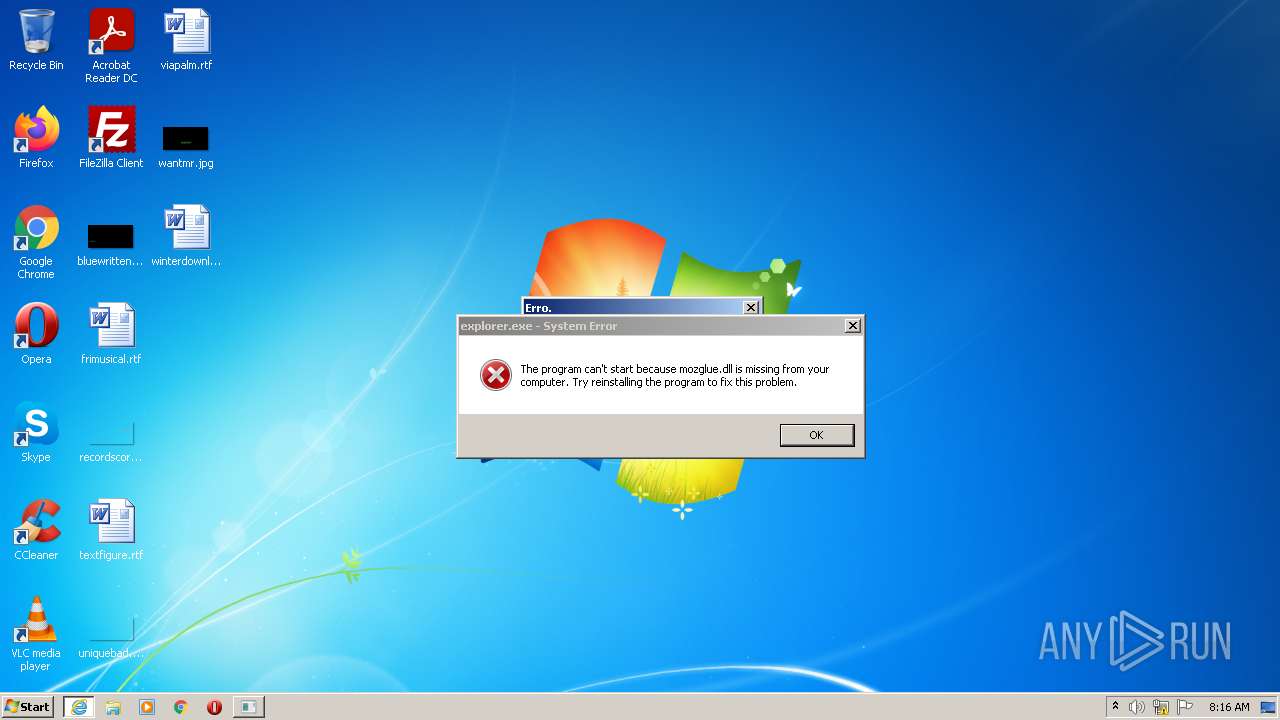
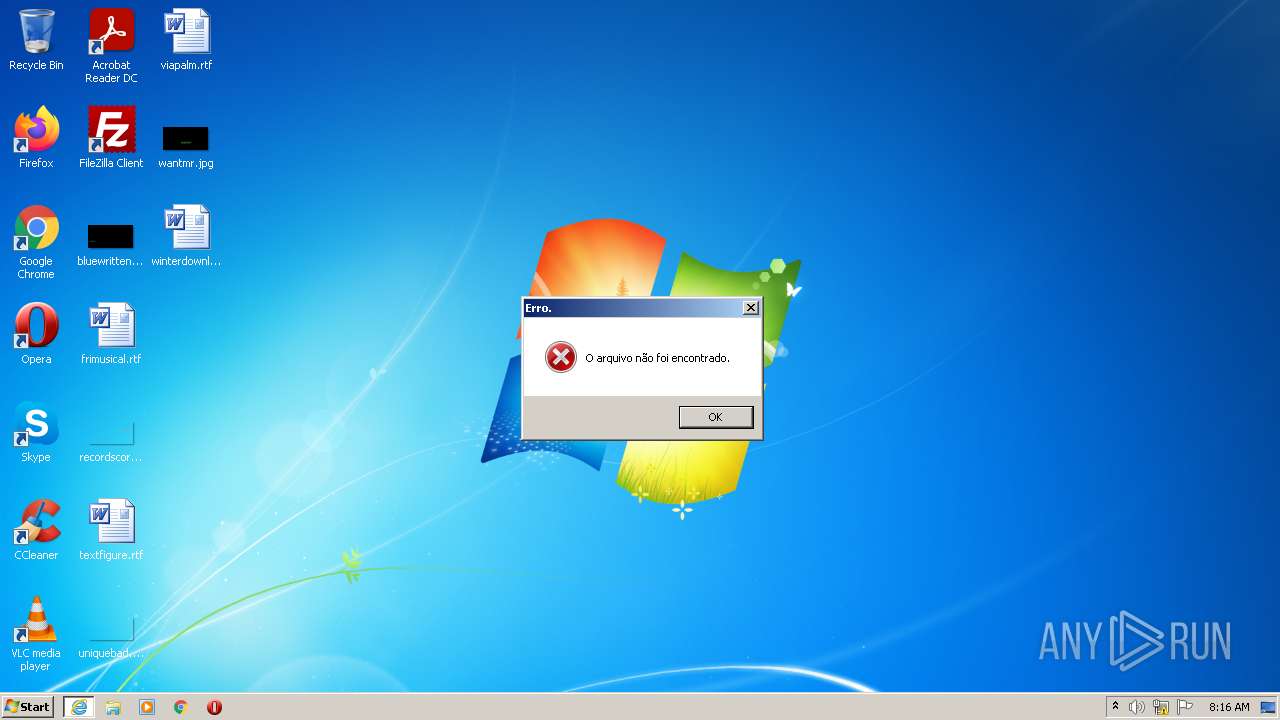
Loads DLL from Mozilla Firefox
- explorer.exe (PID: 352)
INFO
Reads the computer name
- iexplore.exe (PID: 2976)
Checks supported languages
- iexplore.exe (PID: 2976)
Creates files in the user directory
- iexplore.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 45568 |
| InitializedDataSize: | 243712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbbf4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000B1C8 | 0x0000B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41418 |
DATA | 0x0000D000 | 0x00000220 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.76426 |
BSS | 0x0000E000 | 0x000011F1 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00010000 | 0x00000BE4 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77096 |
.tls | 0x00011000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00012000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.205446 |
.reloc | 0x00013000 | 0x00000A60 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.2459 |
.rsrc | 0x00014000 | 0x000399D0 | 0x00039A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.96334 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.0948 | 388 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
XX-XX-XX-XX | 7.96319 | 235330 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
crypt32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
pstorec.dll |
rasapi32.dll |
shell32.dll |
user32.dll |
Total processes
35
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe" | C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 528 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\sample1.bin.exe" | C:\Users\admin\AppData\Local\Temp\sample1.bin.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | sample1.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 030
Read events
1 005
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2520) sample1.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft |
Value: C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe | |||
| (PID) Process: | (2520) sample1.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft |
Value: C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe | |||
| (PID) Process: | (2520) sample1.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{07PKOYYX-VOKQ-NVJ7-RHVV-8S8JJ1V306OG} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe Restart | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\vítima |
| Operation: | write | Name: | FirstExecution |
Value: 07/04/2022 -- 08:15 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\vítima |
| Operation: | write | Name: | NewIdentification |
Value: vítima | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (528) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.VagreargRkcybere.Qrsnhyg |
Value: 000000003F0000004B0000008E0F0D00000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF00FEAE759EB1D60100000000 | |||
Executable files
1
Suspicious files
1
Text files
141
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\XxX.xXx | text | |
MD5:— | SHA256:— | |||
| 2520 | sample1.bin.exe | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\UuU.uUu | text | |
MD5:— | SHA256:— | |||
| 2520 | sample1.bin.exe | C:\Users\admin\AppData\Roaming\Microsoft\explorer.exe | executable | |
MD5:DF8A2C219C032BEF70FE59D8D2EF393A | SHA256:07B8F25E7B536F5B6F686C12D04EDC37E11347C8ACD5C53F98A174723078C365 | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\Roaming\logs.dat | text | |
MD5:E21BD9604EFE8EE9B59DC7605B927A2A | SHA256:51A3FE220229AA3FDDDC909E20A4B107E7497320A00792A280A03389F2EACB46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
aliencz.ddns.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |