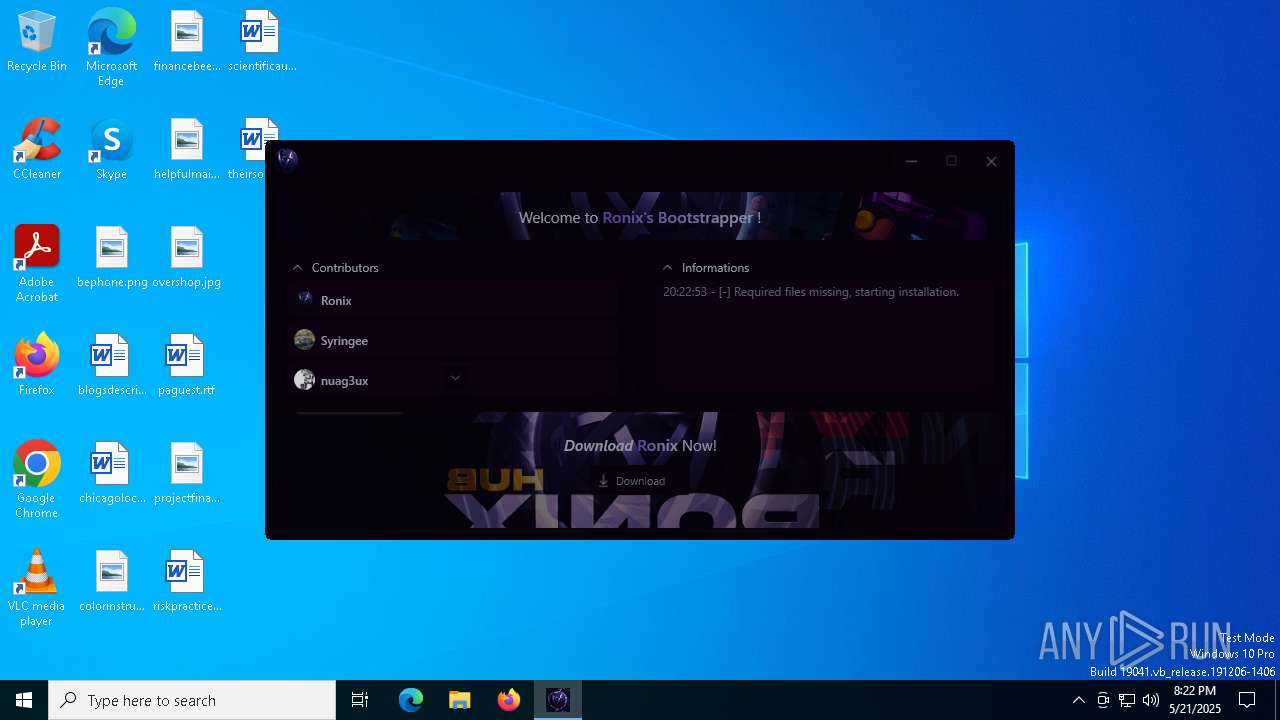
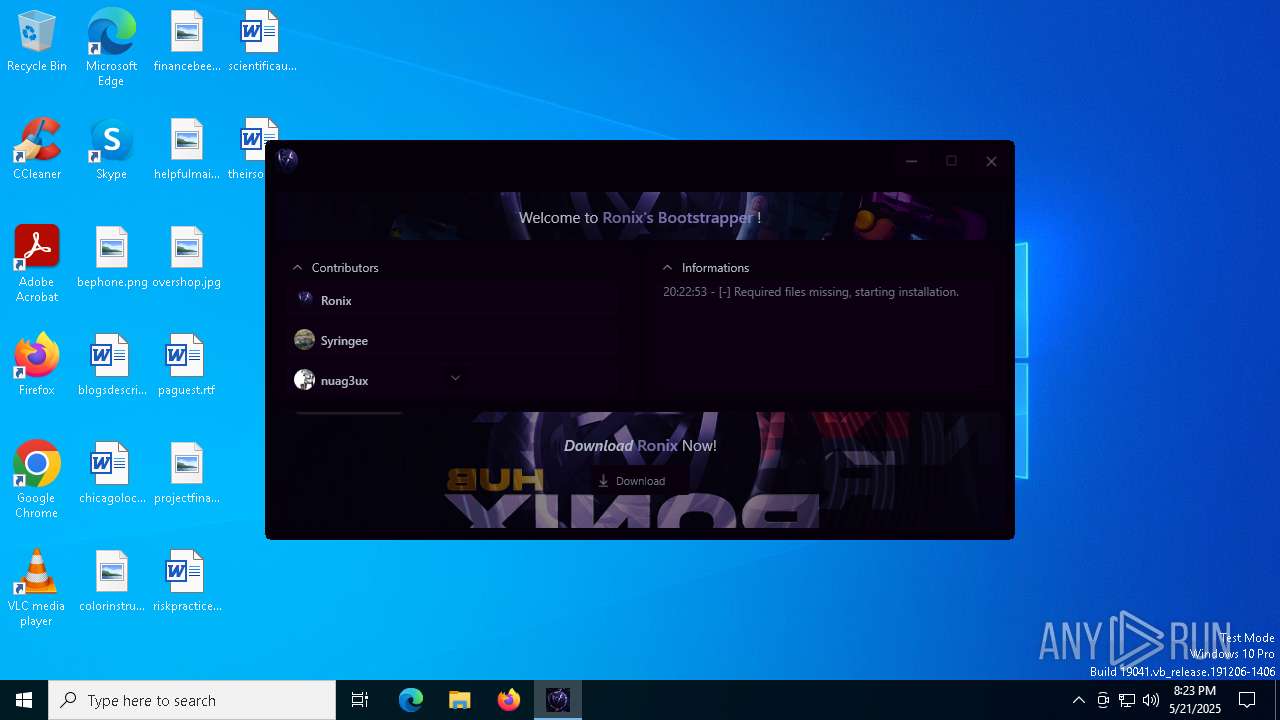
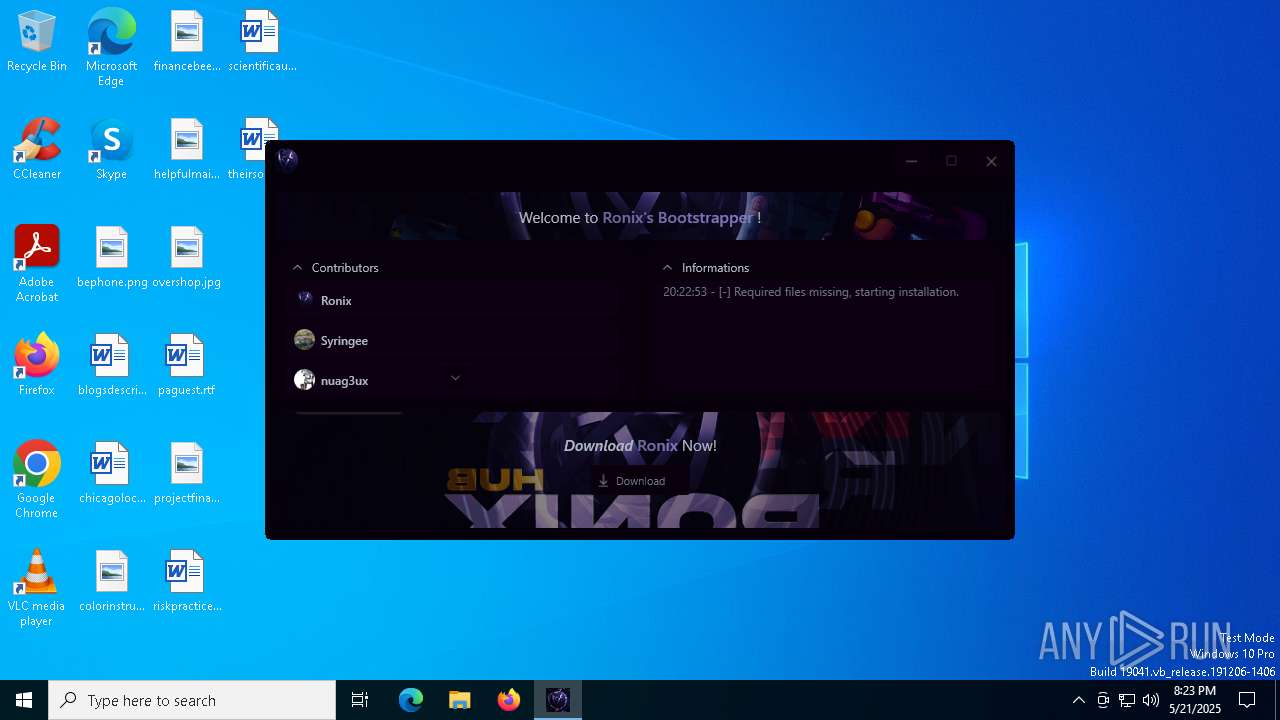
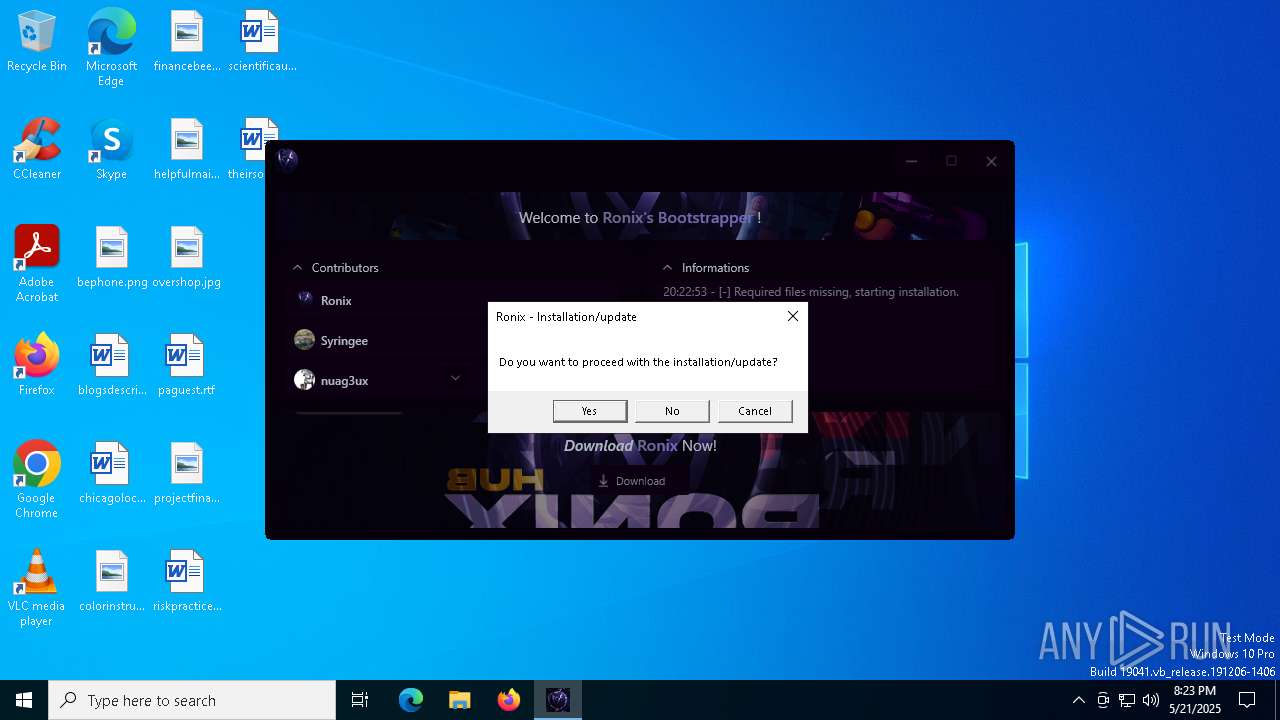
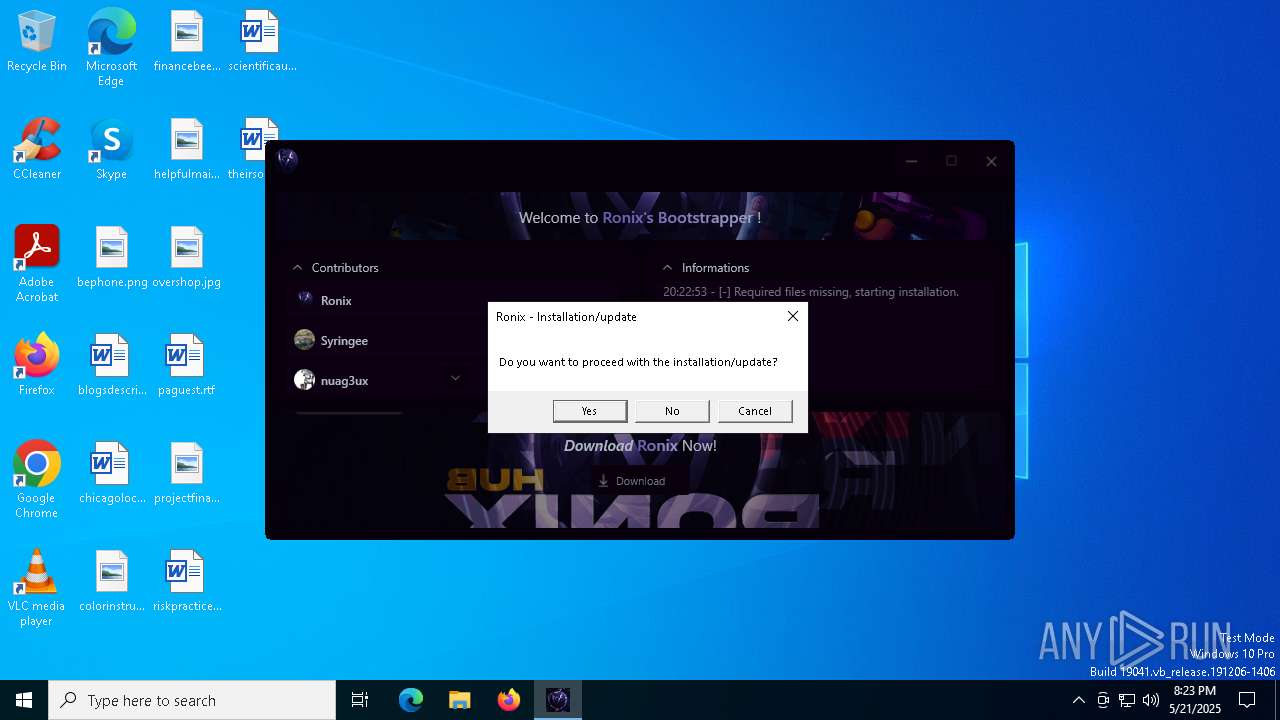
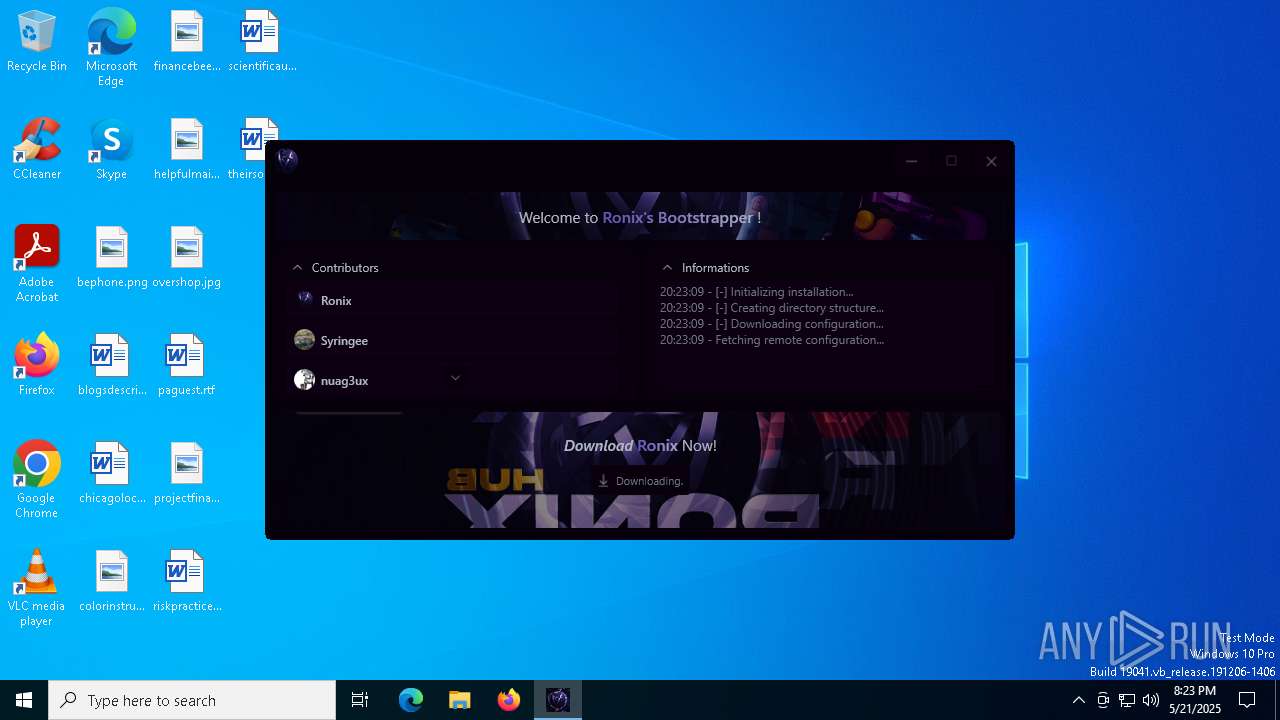
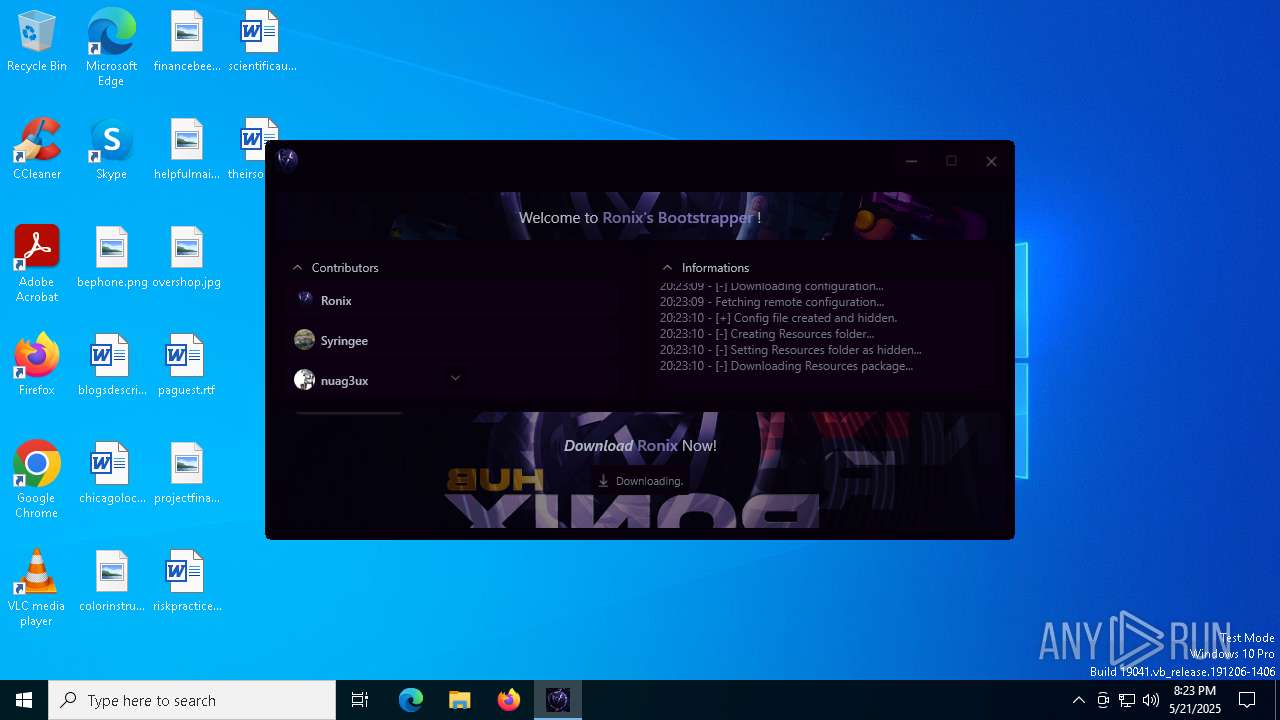
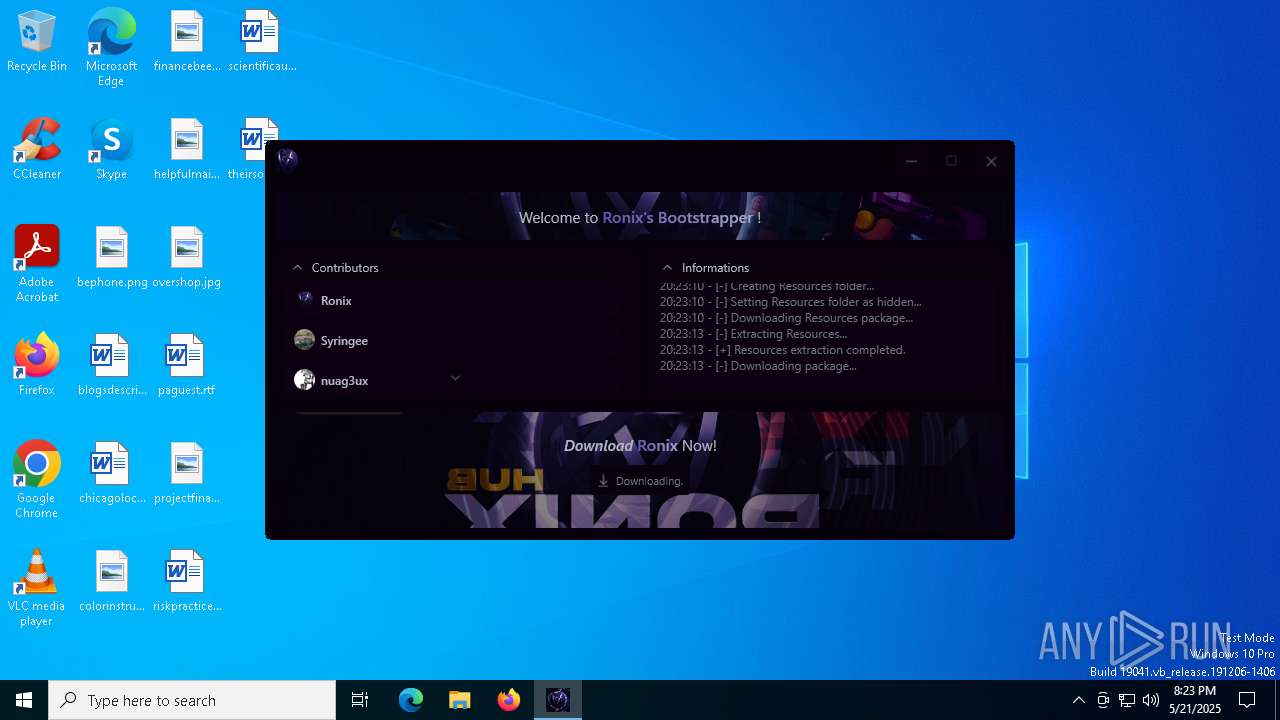
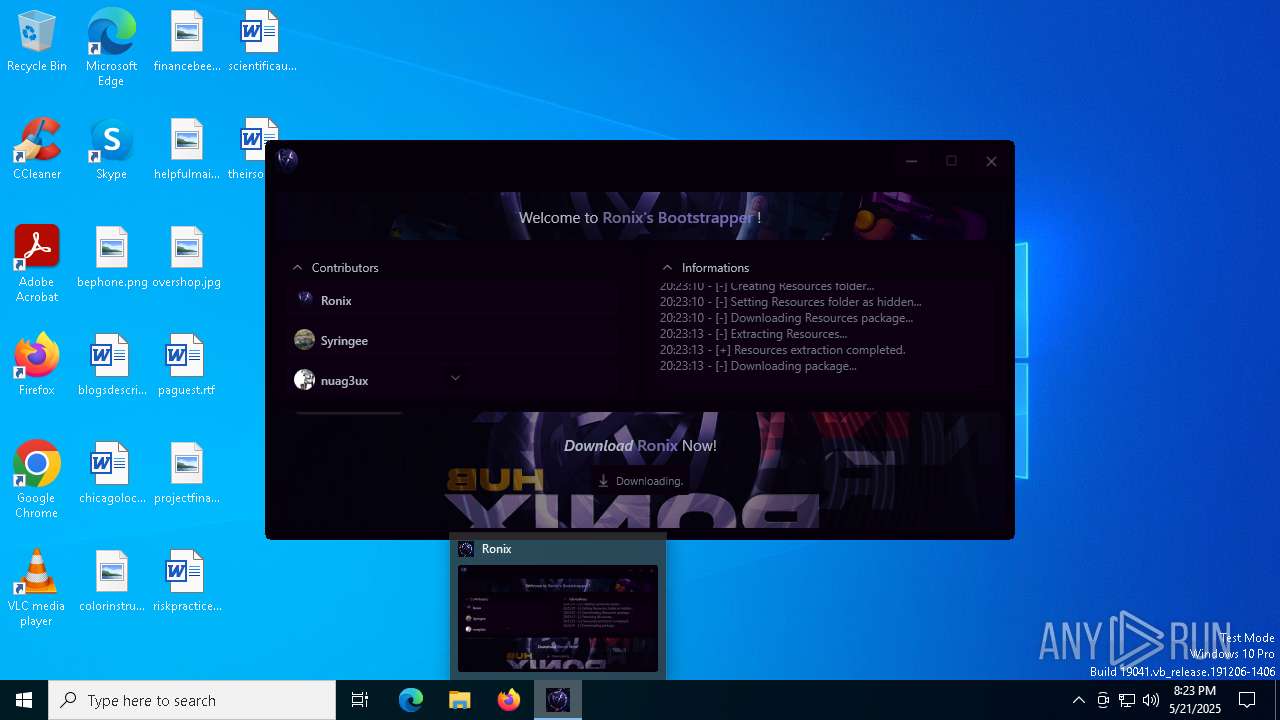
| File name: | Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/145abd71-3057-4a01-a699-6d8b20257269 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2025, 20:22:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A0C8FEF1A5260D19C146ABD2831CF31C |
| SHA1: | 8AC1DC596D85FD36D0BC8C78AD8911CB3438B52C |
| SHA256: | 079DFDF79EBE04E14BBDCBD3F4E0A410C156EB09802DFB457B4E07274D29147B |
| SSDEEP: | 98304:Q3W8iAp04jvqpkTdm/9u8dWc+ZClzyQq7p03/MSgsT6fwm/6Hrs3Hy57OffCG4q2:t3AJAc4/23 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Ronix.exe (PID: 5984)
- Bootstrapper.exe (PID: 6944)
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 6944)
Process drops legitimate windows executable
- Bootstrapper.exe (PID: 6944)
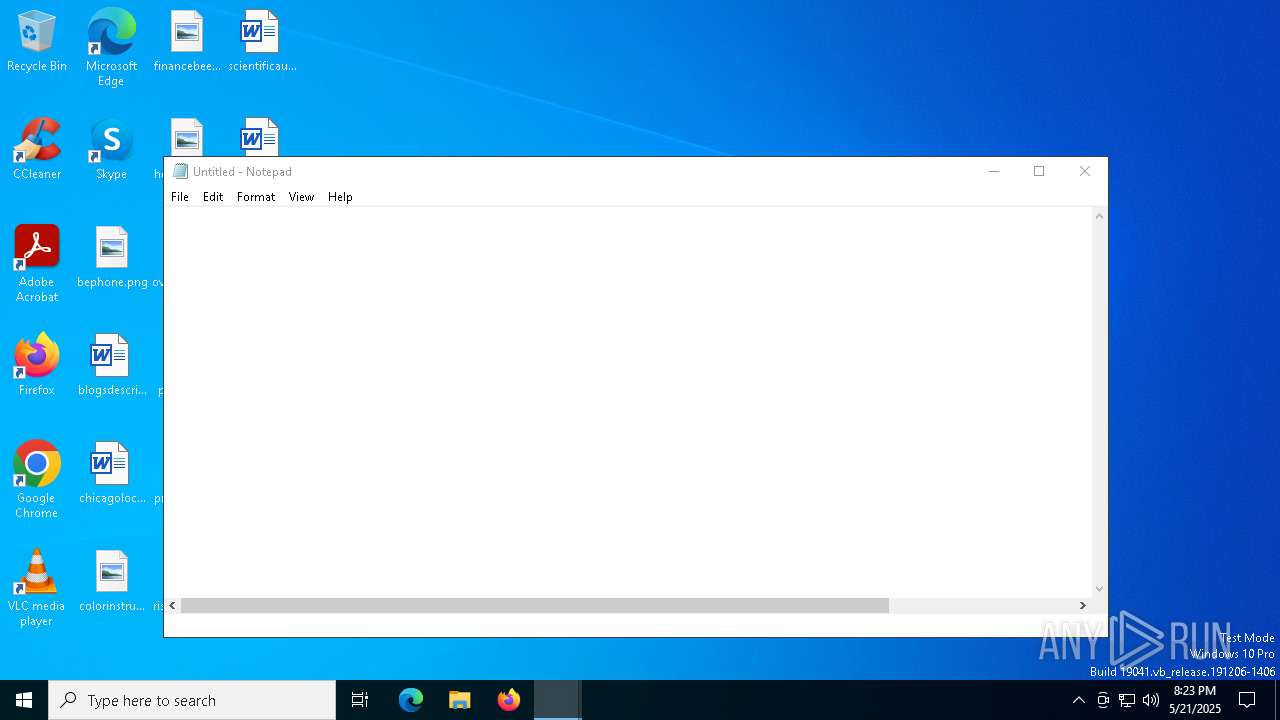
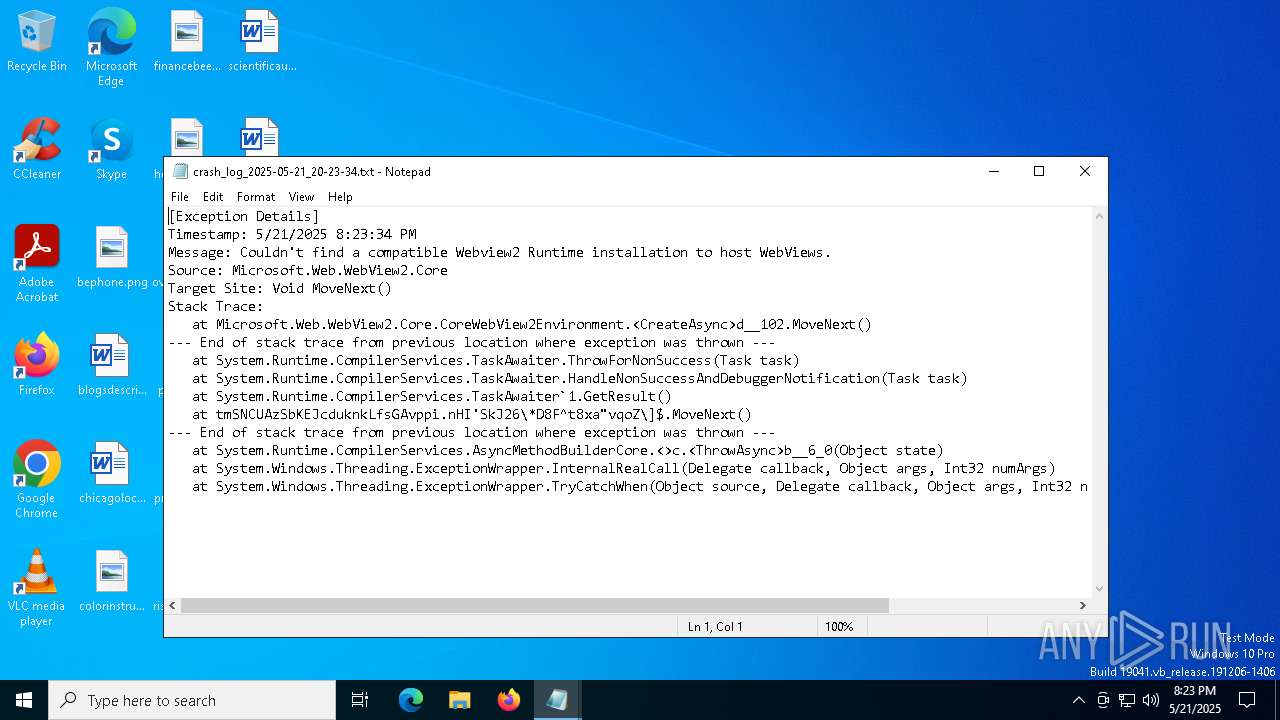
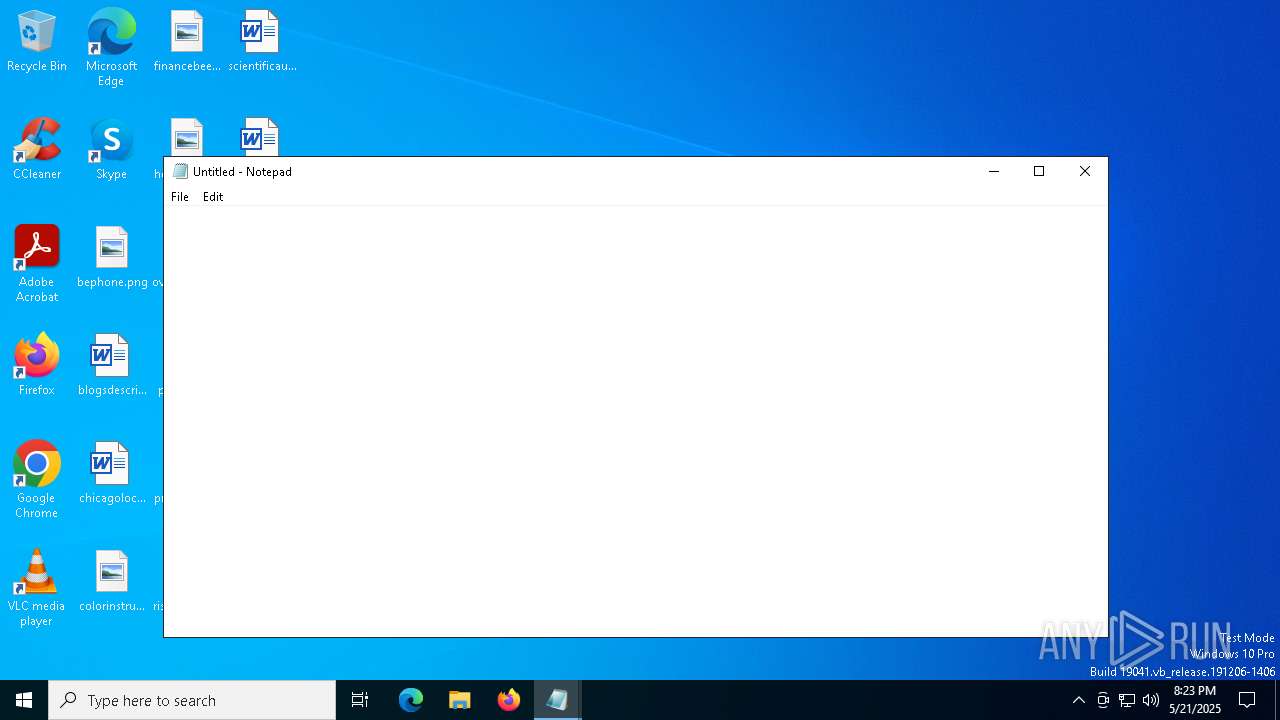
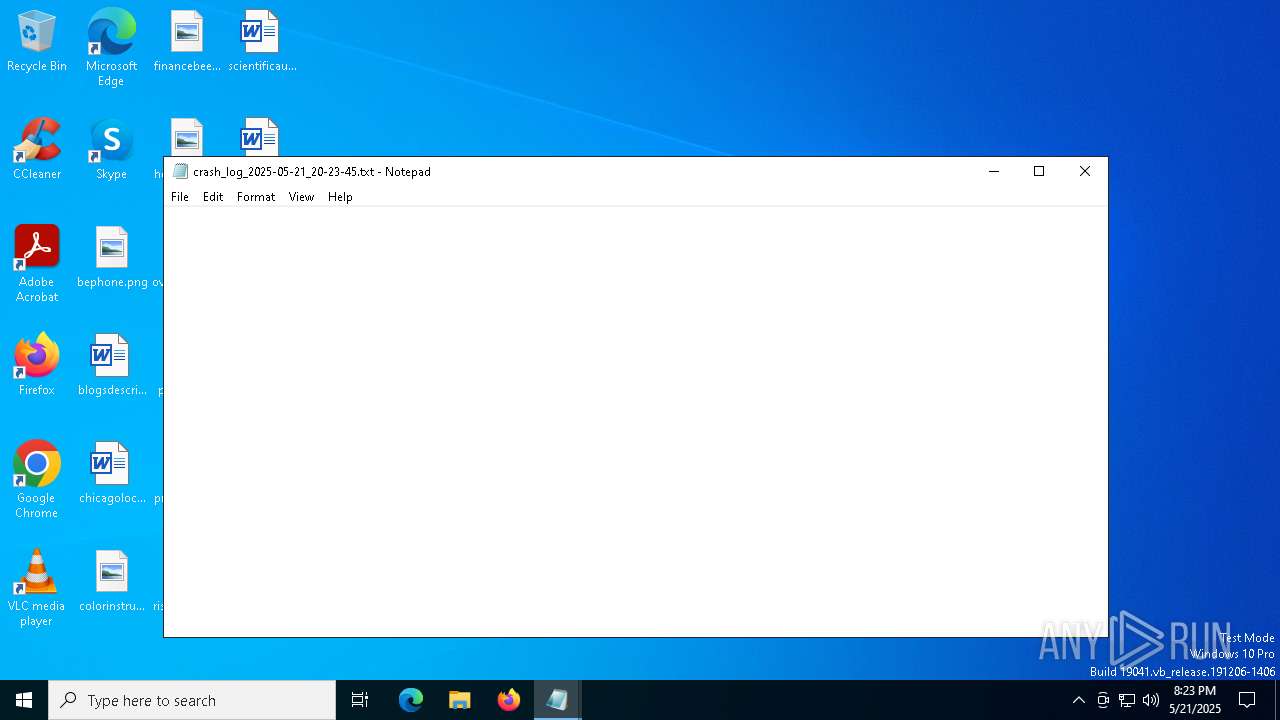
Start notepad (likely ransomware note)
- Ronix.exe (PID: 5984)
INFO
Reads the computer name
- Bootstrapper.exe (PID: 6944)
- Ronix.exe (PID: 5984)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 6944)
- Ronix.exe (PID: 5984)
Process checks computer location settings
- Ronix.exe (PID: 5984)
- Bootstrapper.exe (PID: 6944)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4696)
- notepad.exe (PID: 1628)
- notepad.exe (PID: 6228)
- notepad.exe (PID: 5588)
- notepad.exe (PID: 5304)
- notepad.exe (PID: 5228)
- notepad.exe (PID: 680)
- notepad.exe (PID: 3176)
- notepad.exe (PID: 960)
- notepad.exe (PID: 6108)
- notepad.exe (PID: 2268)
- notepad.exe (PID: 7156)
- notepad.exe (PID: 1324)
- notepad.exe (PID: 6816)
- notepad.exe (PID: 2392)
- notepad.exe (PID: 7020)
- notepad.exe (PID: 4428)
- notepad.exe (PID: 6660)
- notepad.exe (PID: 4488)
- notepad.exe (PID: 6988)
- notepad.exe (PID: 2656)
- notepad.exe (PID: 5960)
- notepad.exe (PID: 5892)
- notepad.exe (PID: 732)
- notepad.exe (PID: 7244)
- notepad.exe (PID: 6656)
- notepad.exe (PID: 7208)
- notepad.exe (PID: 7372)
- notepad.exe (PID: 6080)
- notepad.exe (PID: 7332)
- notepad.exe (PID: 6808)
- notepad.exe (PID: 872)
- notepad.exe (PID: 7676)
- notepad.exe (PID: 5332)
- notepad.exe (PID: 7580)
- notepad.exe (PID: 7528)
- notepad.exe (PID: 7568)
- notepad.exe (PID: 7544)
- notepad.exe (PID: 7648)
- notepad.exe (PID: 7748)
- notepad.exe (PID: 7868)
- notepad.exe (PID: 7884)
- notepad.exe (PID: 7740)
- notepad.exe (PID: 7392)
- notepad.exe (PID: 7964)
- notepad.exe (PID: 7732)
- notepad.exe (PID: 7948)
- notepad.exe (PID: 7704)
- notepad.exe (PID: 7832)
- notepad.exe (PID: 7840)
- notepad.exe (PID: 8196)
- notepad.exe (PID: 8004)
- notepad.exe (PID: 7804)
- notepad.exe (PID: 8112)
- notepad.exe (PID: 8100)
- notepad.exe (PID: 8320)
- notepad.exe (PID: 8128)
- notepad.exe (PID: 8208)
- notepad.exe (PID: 8300)
- notepad.exe (PID: 4736)
- notepad.exe (PID: 8160)
- notepad.exe (PID: 8548)
- notepad.exe (PID: 8452)
- notepad.exe (PID: 8440)
- notepad.exe (PID: 8488)
- notepad.exe (PID: 8536)
- notepad.exe (PID: 8388)
- notepad.exe (PID: 8648)
- notepad.exe (PID: 8660)
Disables trace logs
- Bootstrapper.exe (PID: 6944)
Checks supported languages
- Bootstrapper.exe (PID: 6944)
- Ronix.exe (PID: 5984)
Reads the software policy settings
- Bootstrapper.exe (PID: 6944)
Checks proxy server information
- Bootstrapper.exe (PID: 6944)
Create files in a temporary directory
- Bootstrapper.exe (PID: 6944)
- Ronix.exe (PID: 5984)
The sample compiled with english language support
- Bootstrapper.exe (PID: 6944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2086:06:06 07:48:43+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 6598656 |
| InitializedDataSize: | 264192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x64cede |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Bootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | Bootstrapper.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | Bootstrapper.exe |
| ProductName: | Bootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
302
Monitored processes
177
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-29.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-30.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-31.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-29.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-29.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-29.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-30.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-30.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2656 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Ronix\logs\crash_log_2025-05-21_20-23-30.txt | C:\Windows\SysWOW64\notepad.exe | — | Ronix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 324
Read events
70 135
Write events
189
Delete events
0
Modification events
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6944) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
10
Suspicious files
4
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\bin\Resources\song.mp3 | — | |
MD5:— | SHA256:— | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\bin\CONFIG | text | |
MD5:14607822426D690390607BB48A124F66 | SHA256:9FD28642D3ACA191E5C7FC2383CFD6FABB2AAC8743F029DABB8989AC584E31BC | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\temp.zip | compressed | |
MD5:CCC4A022526B1B9212146BA65B7296C8 | SHA256:08B415B243C205AD83886E789768D5EB6D0F8922622A813A5A825624C2D766B6 | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\Microsoft.Web.WebView2.Wpf.xml | xml | |
MD5:1F752A8BF8C538C6823159B4D159BDE1 | SHA256:D2A287558B133325DC5BD890B994EF954A78486AD488FED422B88386EB47EDA8 | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\bin\Resources\intro.mp3 | binary | |
MD5:7DE6A7A6C1946DCB6AAB9D90C32181C9 | SHA256:8B39AE62C33AFB9D1869EF7E66BF182753E28EED16854E64B9D4149E7BBE9467 | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\bin\Resources\Resources.zip | compressed | |
MD5:44D6B3F3B9153FEEC5E36AD41BE55626 | SHA256:7EAB510B54F8C9D5FD002D4879210207E9AAF30E67F296DAB51E9F1FEA6B5285 | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\Microsoft.Web.WebView2.WinForms.xml | xml | |
MD5:C09409AAC254F17C1C648E6F0464B035 | SHA256:4B40E49AEC5DBDA597224F997D57A16645DDC2EB00F31A6329204D1853A2245A | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\Ronix.exe | executable | |
MD5:A5768C57EF1A20A247601141917970C8 | SHA256:A38353BDF1C267CECC390C0767B63A6E20335C4CE8991F762F0CADE548154BAA | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\Hyperion.dll | executable | |
MD5:E4A6B13F6047F7794B256DFDCB4CC48D | SHA256:0AB58838CE6039CB159977A6D6C2BA23A498E61AE6975C6C2506564DD45B9875 | |||
| 6944 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Ronix\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.148:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.148:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4608 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4608 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.148:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.148:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |