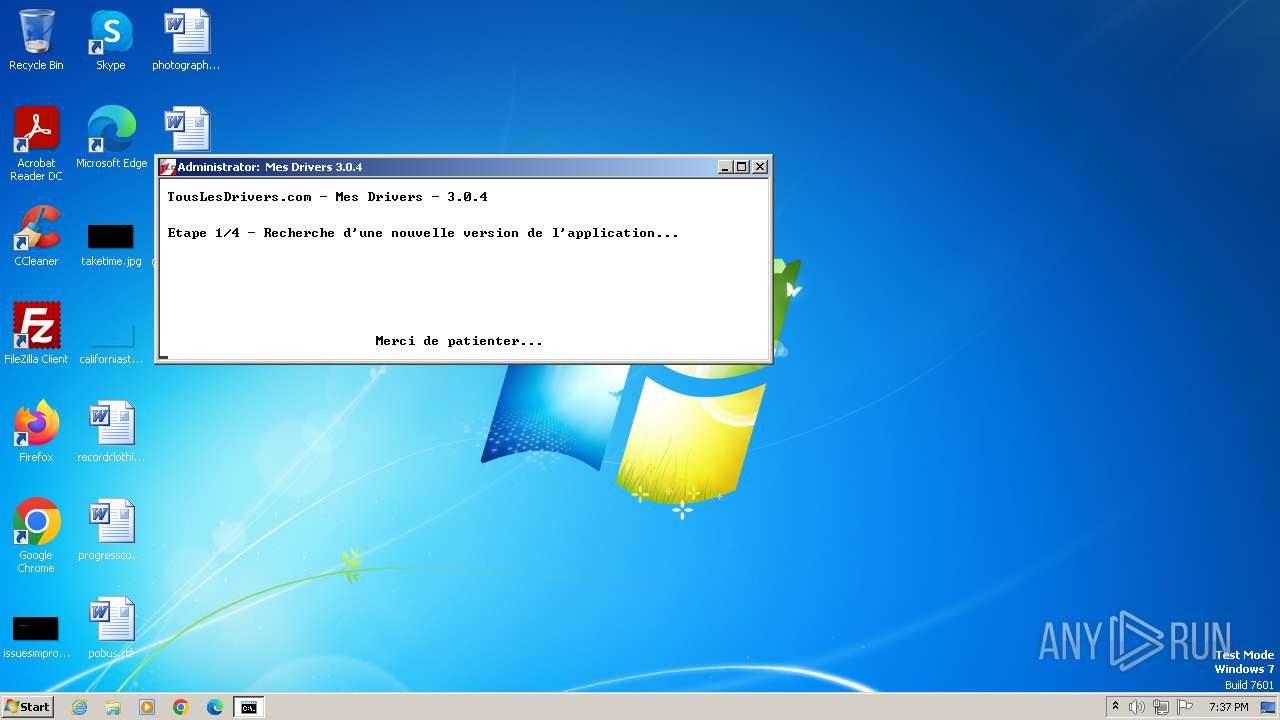
| File name: | Mes_Drivers_3.0.4.exe |
| Full analysis: | https://app.any.run/tasks/c46d4fac-020e-44c0-b30d-c65f29c9f17a |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2023, 19:37:31 |
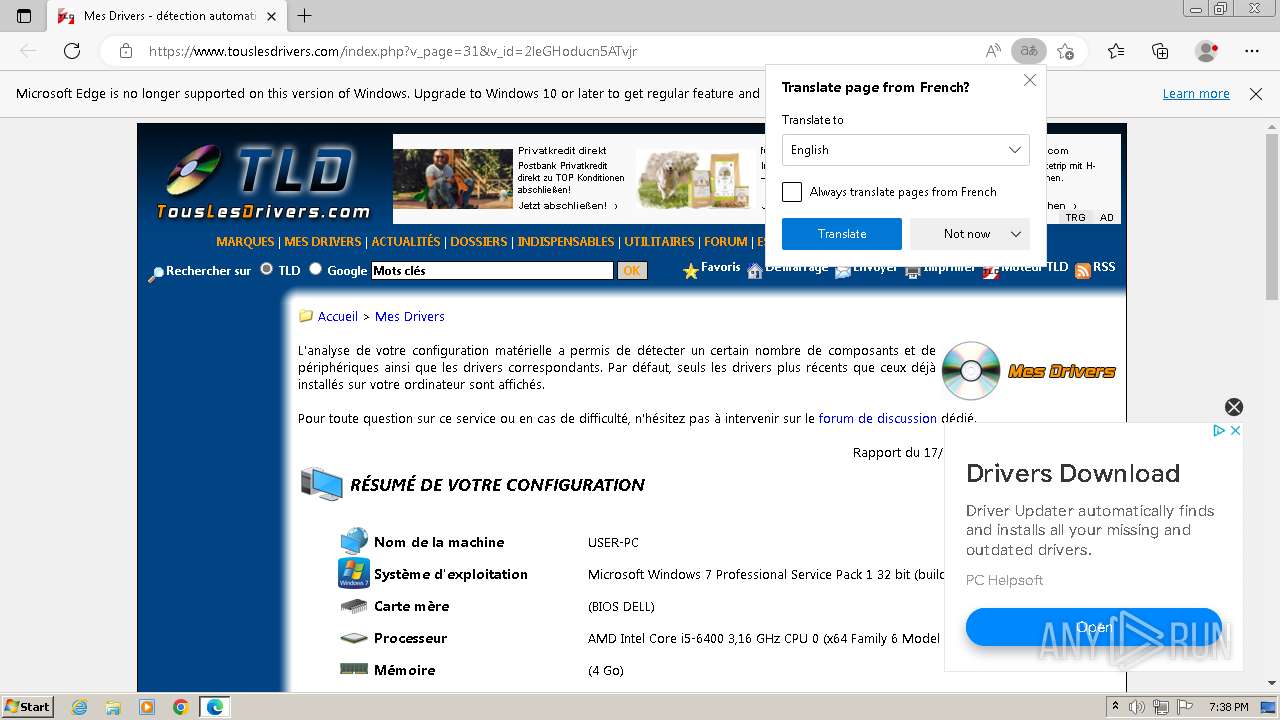
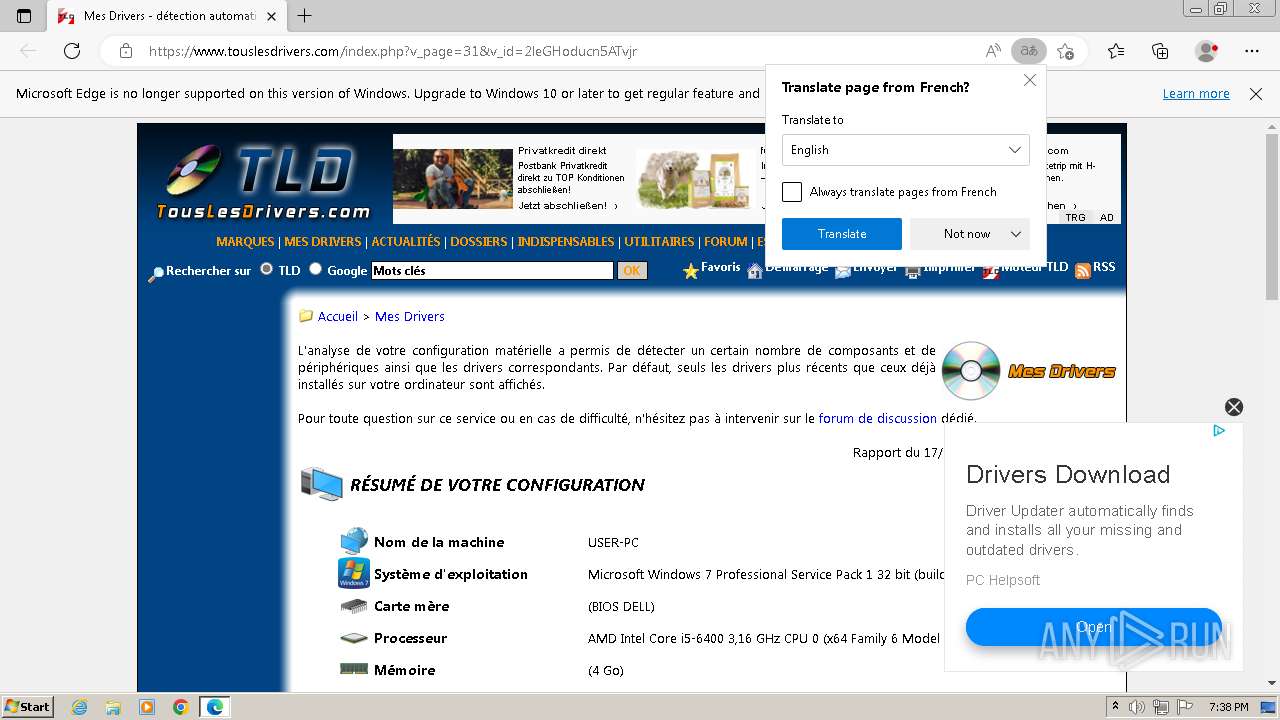
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 50A5E891DA27E63D54E68511E48AA026 |
| SHA1: | 87073D85A7BA420B15C8BB9A9E4ADC64DB2BCFEF |
| SHA256: | 0788AAEA249D92A84F70047EFCACAA54C26320B439C490BA3CE00457955031D6 |
| SSDEEP: | 24576:AfHFw5b9DOnFYrv+kjqipUompMEoNMDYSkbDknoI6JK+ZYtEi8ETtAM5B:sjFYrv+kjV45oeYSRnyJhOtEVcf5B |
MALICIOUS
Drops the executable file immediately after the start
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Accesses environment variables (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Reads the value of a key from the registry (SCRIPT)
- detection.exe (PID: 3596)
Uses sleep, probably for evasion detection (SCRIPT)
- detection.exe (PID: 3596)
Accesses physical disk drive(Win32_DiskDrive) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses Motherboard(Win32_BaseBoard, may evade sandboxes) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses the network adapter (Win32_NetworkAdapter) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses network adapter’s MAC address via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses Physical Memory (Win32_PhysicalMemory, may evade sandboxes) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses Processor(Win32_Processor, may evade sandboxes) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses Video Controller(Win32_VideoController, may evade sandboxes) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Creates a new folder (SCRIPT)
- detection.exe (PID: 3596)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- detection.exe (PID: 3596)
Checks whether a specified folder exists (SCRIPT)
- detection.exe (PID: 3596)
Deletes a file (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
SUSPICIOUS
Process drops legitimate windows executable
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Creates FileSystem object to access computer's file system (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Gets full path of the running script (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
Gets name of the script (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Reads the Internet Settings
- Mes_Drivers_3.0.4.exe (PID: 3524)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 2196)
Checks whether a specific file exists (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Executing commands from ".cmd" file
- cmd.exe (PID: 3516)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3516)
- cmd.exe (PID: 3644)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Application launched itself
- cmd.exe (PID: 3644)
- cmd.exe (PID: 3516)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3644)
Runs shell command (SCRIPT)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Starts SC.EXE for service management
- detection.exe (PID: 3596)
Reads data from a binary Stream object (SCRIPT)
- detection.exe (PID: 3596)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- detection.exe (PID: 3596)
Executes WMI query (SCRIPT)
- detection.exe (PID: 3596)
Reads settings of System Certificates
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4044)
Reads security settings of Internet Explorer
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4044)
Checks Windows Trust Settings
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4044)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- detection.exe (PID: 3596)
Accesses computer name via WMI (SCRIPT)
- detection.exe (PID: 3596)
Writes binary data to a Stream object (SCRIPT)
- detection.exe (PID: 3596)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3480)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
- curl_x86.exe (PID: 3936)
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4048)
- detect_x86.exe (PID: 4044)
- detect_x86.exe (PID: 4084)
- detect_x86.exe (PID: 3536)
- curl_x86.exe (PID: 3600)
Checks supported languages
- wmpnscfg.exe (PID: 3480)
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
- mode.com (PID: 3864)
- curl_x86.exe (PID: 3936)
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4044)
- detect_x86.exe (PID: 3536)
- detect_x86.exe (PID: 4084)
- detect_x86.exe (PID: 4048)
- aes_x86.exe (PID: 3236)
- curl_x86.exe (PID: 3600)
Manual execution by a user
- wmpnscfg.exe (PID: 3480)
- msedge.exe (PID: 684)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3480)
- detection.exe (PID: 3596)
- detect_x86.exe (PID: 2064)
- detect_x86.exe (PID: 4044)
- aes_x86.exe (PID: 3236)
- curl_x86.exe (PID: 3600)
Create files in a temporary directory
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
- aes_x86.exe (PID: 3236)
Reads Environment values
- Mes_Drivers_3.0.4.exe (PID: 3524)
- detection.exe (PID: 3596)
Checks operating system version
- cmd.exe (PID: 3644)
Reads the time zone
- detection.exe (PID: 3596)
Application launched itself
- msedge.exe (PID: 2368)
- msedge.exe (PID: 684)
Self-termination (SCRIPT)
- detection.exe (PID: 3596)
- Mes_Drivers_3.0.4.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (63.7) |
|---|---|---|
| .scr | | | Windows screen saver (20) |
| .exe | | | Win32 Executable (generic) (6.9) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:09 23:39:00+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 350720 |
| InitializedDataSize: | 1260544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5678c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.4.0 |
| ProductVersionNumber: | 3.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
Total processes
132
Monitored processes
91
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=5904 --field-trial-handle=1424,i,1247314584953910939,1900286422093150832,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1420 --field-trial-handle=1336,i,6599545812777074040,15115533600745578046,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6dbaf598,0x6dbaf5a8,0x6dbaf5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
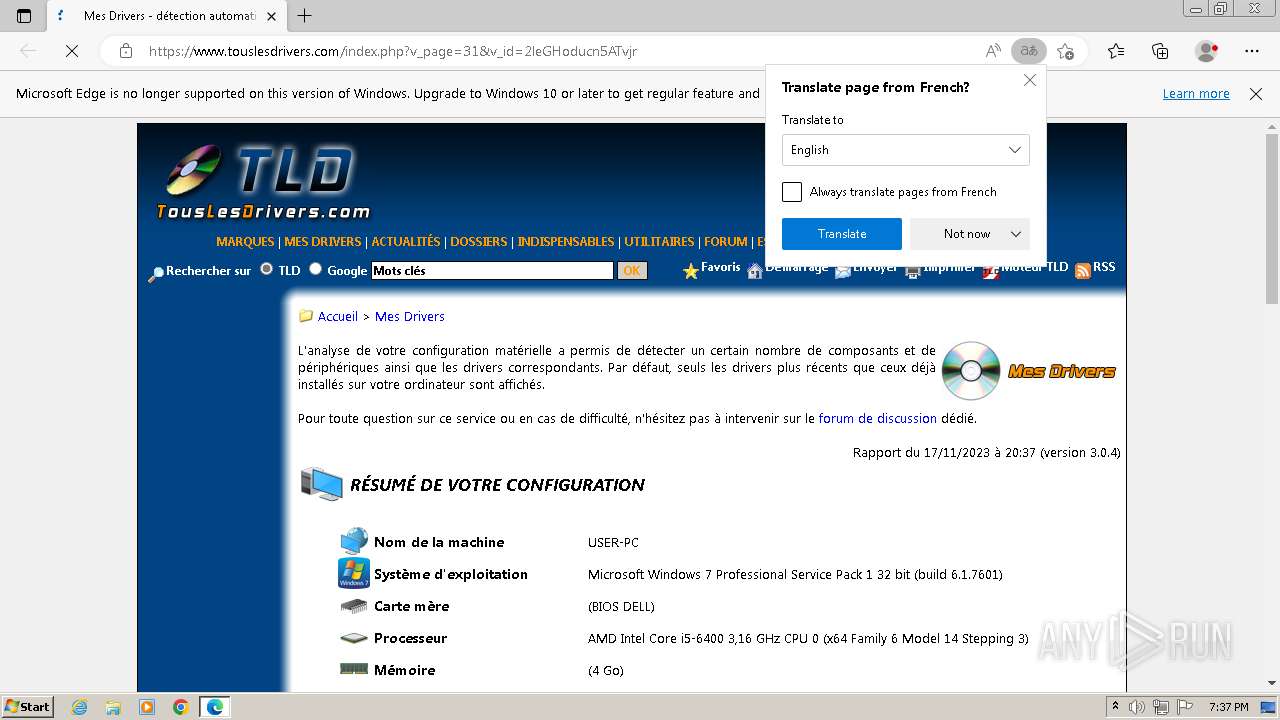
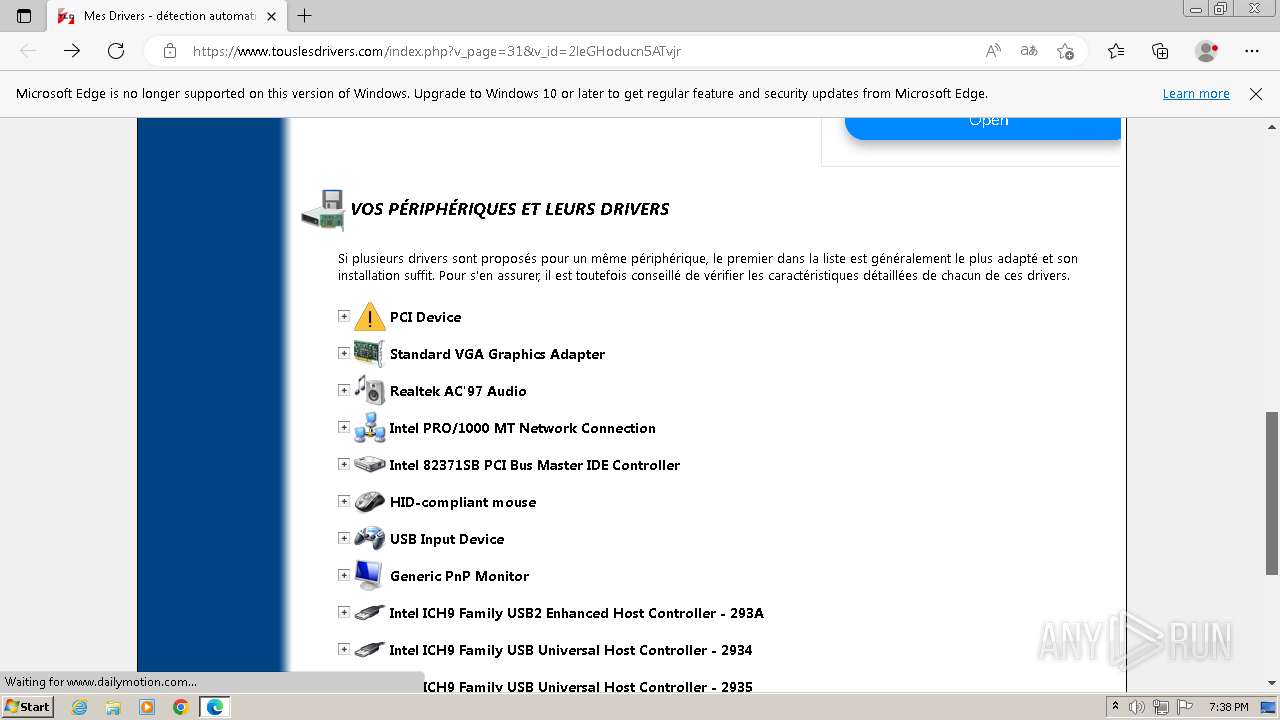
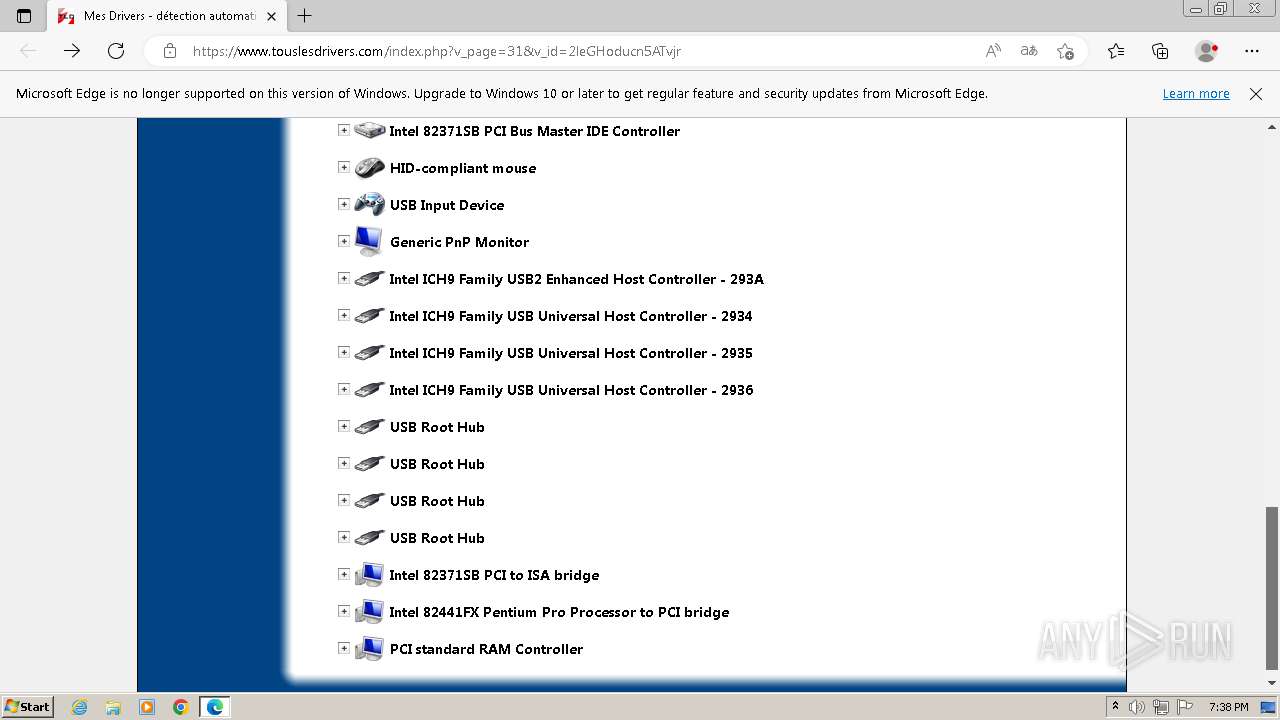
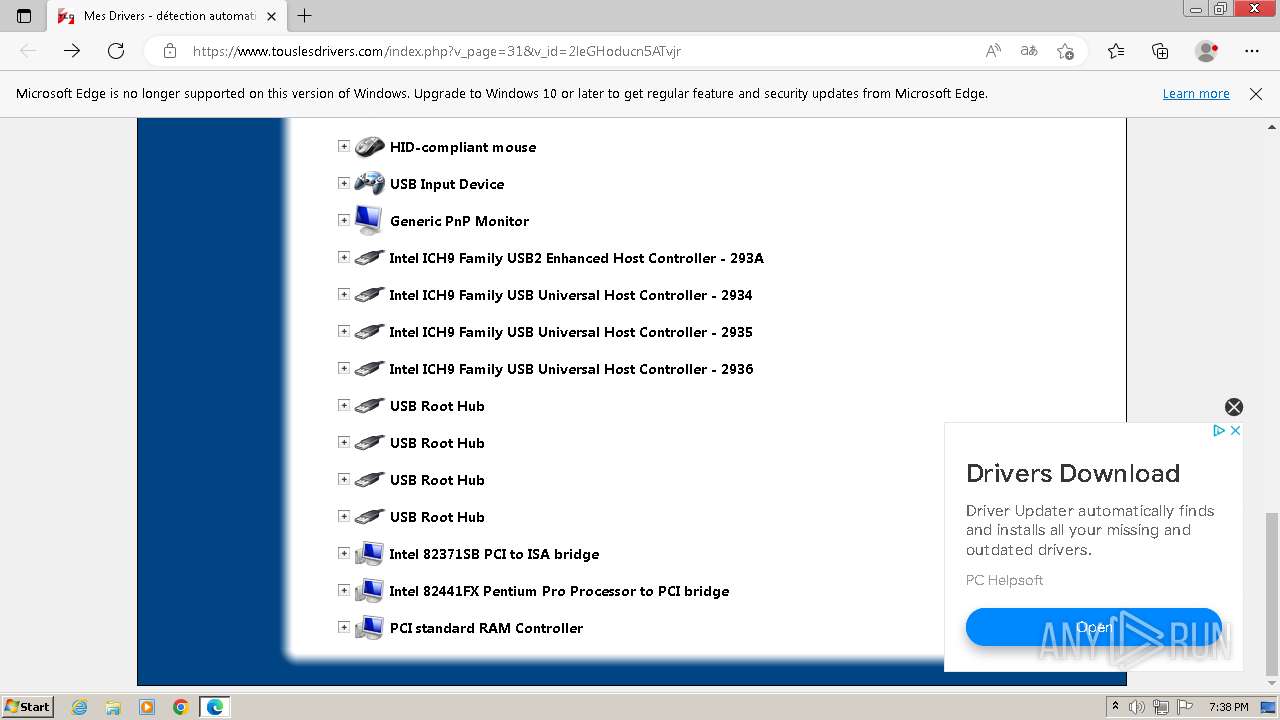
| 684 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate http://www.touslesdrivers.com/index.php?v_page=31&v_id=2leGHoducn5ATvjr | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=5824 --field-trial-handle=1424,i,1247314584953910939,1900286422093150832,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2312 --field-trial-handle=1424,i,1247314584953910939,1900286422093150832,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1436 | WAITFOR /S USER-PC /SI unlock | C:\Windows\System32\waitfor.exe | — | detection.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=4560 --field-trial-handle=1424,i,1247314584953910939,1900286422093150832,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1576 | WAITFOR unlock | C:\Windows\System32\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=2348 --field-trial-handle=1424,i,1247314584953910939,1900286422093150832,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
13 740
Read events
13 628
Write events
108
Delete events
4
Modification events
| (PID) Process: | (3480) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{81C320F4-547A-41DD-AD60-8DB17B702C31}\{03BA301B-6FEE-43BE-AFC9-0BA08DE591CE} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3480) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{81C320F4-547A-41DD-AD60-8DB17B702C31} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3480) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{4C66A10C-7ED5-455B-8A1E-8865147F1F98} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3524) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3524) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3524) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3524) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3516) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3516) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3516) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
13
Suspicious files
248
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | waitfor.exe | \Device\Mup:\USER-PC\mailslot\WAITFOR.EXE\unlock | — | |
MD5:— | SHA256:— | |||
| 4076 | waitfor.exe | \Device\Mup:\USER-PC\mailslot\WAITFOR.EXE\unlock | — | |
MD5:— | SHA256:— | |||
| 3700 | waitfor.exe | \Device\Mup:\USER-PC\mailslot\WAITFOR.EXE\unlock | — | |
MD5:— | SHA256:— | |||
| 1436 | waitfor.exe | \Device\Mup:\USER-PC\mailslot\WAITFOR.EXE\unlock | — | |
MD5:— | SHA256:— | |||
| 3596 | detection.exe | C:\Users\admin\AppData\Local\Temp\detect_x64_2.exe | executable | |
MD5:635E57FD7AEFFAF87F6242AF79F419AA | SHA256:4A097314779F4D9CC594F40DB5509487AA4C2C8BDC58BC7230FCB183334BFD97 | |||
| 2368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\f65e7e9c-1018-46d2-9848-5c695e344d37.tmp | binary | |
MD5:207F755355F4D636D65A985F8A8F07FF | SHA256:FB035A988125EFBE618CABAF60E70A81AC1B75AC44D7F5B5BA814C0752DA6765 | |||
| 1832 | msedge.exe | — | ||
MD5:— | SHA256:— | |||
| 3524 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\detection.exe | executable | |
MD5:02BA1C44B6392F013A7AA0B91314F45A | SHA256:7FBE59195F5F6F45C8B38B12488A169FDCB3A272004DBAF44C9D92A60A3690CB | |||
| 3524 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\interface.cmd | text | |
MD5:E0EB53551ACA2ACFF814DDD7ACA212E2 | SHA256:11993A03F68A33500A3CE8FBEB3E3C2042A28299D04F39EED40147709E76CA79 | |||
| 3524 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\waitfor_x86.exe | executable | |
MD5:DD8C73BDCF2077B82DBB6DDD8ECB6A6D | SHA256:C3370E8EC5CA54E8FD7EAC19C278689CF122EDAC91FAA4376DC24B1D807FE510 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
321
DNS requests
281
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
484 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCX%2BefD9f1Iq1caTv8hQqls | unknown | binary | 2.18 Kb | unknown |
484 | lsass.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?440741f4bd306e5a | GB | compressed | 4.66 Kb | unknown |
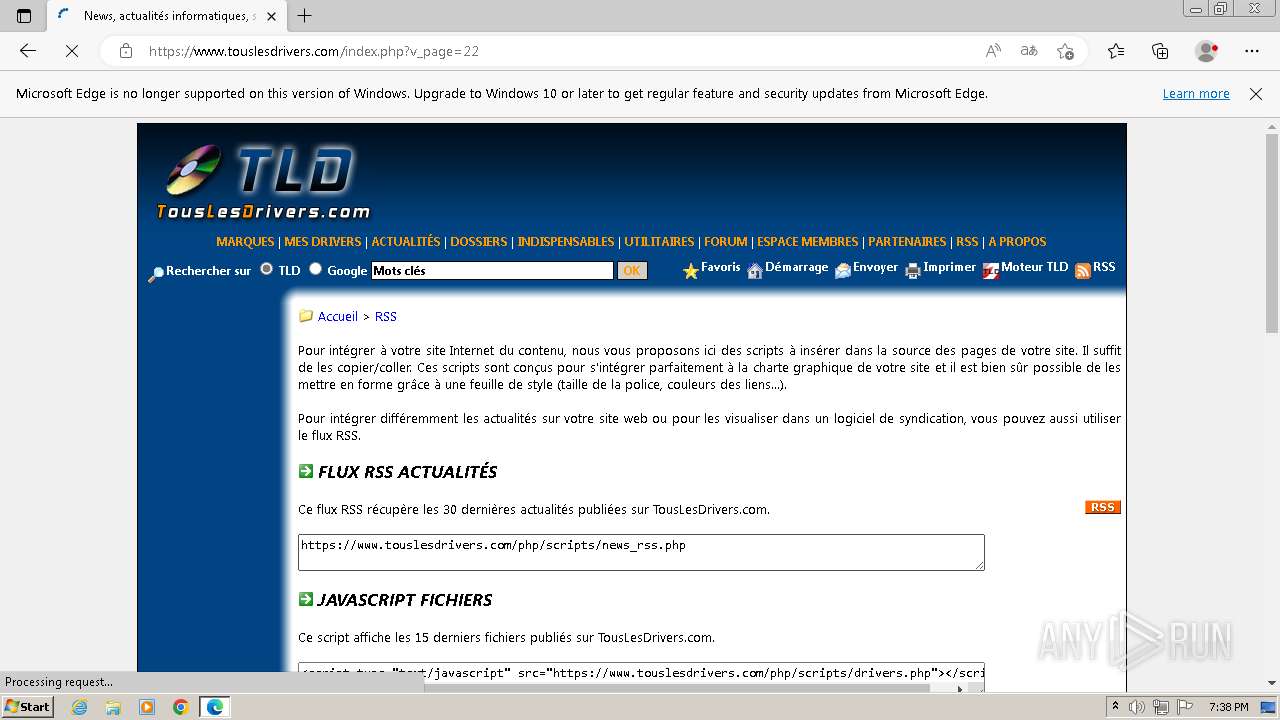
2628 | msedge.exe | GET | 301 | 51.255.80.171:80 | http://www.touslesdrivers.com/index.php?v_page=31&v_id=2leGHoducn5ATvjr | FR | html | 211 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3936 | curl_x86.exe | 51.255.80.171:443 | www.touslesdrivers.com | OVH SAS | FR | unknown |
484 | lsass.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
484 | lsass.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | shared |
3600 | curl_x86.exe | 51.255.80.171:443 | www.touslesdrivers.com | OVH SAS | FR | unknown |
2628 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
684 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2628 | msedge.exe | 51.104.176.40:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2628 | msedge.exe | 51.255.80.171:80 | www.touslesdrivers.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.touslesdrivers.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
ads.sportslocalmedia.com |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
cdn.appconsent.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2628 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |