| File name: | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe |
| Full analysis: | https://app.any.run/tasks/16c6f3d6-a121-4175-8f19-d0e271072018 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2024, 14:20:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 50A5E891DA27E63D54E68511E48AA026 |
| SHA1: | 87073D85A7BA420B15C8BB9A9E4ADC64DB2BCFEF |
| SHA256: | 0788AAEA249D92A84F70047EFCACAA54C26320B439C490BA3CE00457955031D6 |
| SSDEEP: | 24576:AfHFw5b9DOnFYrv+kjqipUompMEoNMDYSkbDknoI6JK+ZYtEi8ETtAM5B:sjFYrv+kjV45oeYSRnyJhOtEVcf5B |
MALICIOUS
Drops the executable file immediately after the start
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Accesses environment variables (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Reads the value of a key from the registry (SCRIPT)
- detection.exe (PID: 2412)
Uses sleep, probably for evasion detection (SCRIPT)
- detection.exe (PID: 2412)
Deletes a file (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Process drops legitimate windows executable
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Executable content was dropped or overwritten
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Gets name of the script (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Gets full path of the running script (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Checks whether a specific file exists (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Reads the date of Windows installation
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Reads security settings of Internet Explorer
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Runs shell command (SCRIPT)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Starts CMD.EXE for commands execution
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 4696)
Application launched itself
- cmd.exe (PID: 4696)
- cmd.exe (PID: 3944)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3944)
Reads data from a binary Stream object (SCRIPT)
- detection.exe (PID: 2412)
Executing commands from ".cmd" file
- cmd.exe (PID: 4696)
INFO
Reads Environment values
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Reads the computer name
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
- curl_x64.exe (PID: 4796)
Checks supported languages
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
- mode.com (PID: 4392)
- curl_x64.exe (PID: 4796)
Create files in a temporary directory
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
- detection.exe (PID: 2412)
Process checks computer location settings
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Checks operating system version
- cmd.exe (PID: 3944)
Self-termination (SCRIPT)
- detection.exe (PID: 2412)
- 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe (PID: 1496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (63.7) |
|---|---|---|
| .scr | | | Windows screen saver (20) |
| .exe | | | Win32 Executable (generic) (6.9) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:09 21:39:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 350720 |
| InitializedDataSize: | 1260544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5678c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.4.0 |
| ProductVersionNumber: | 3.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
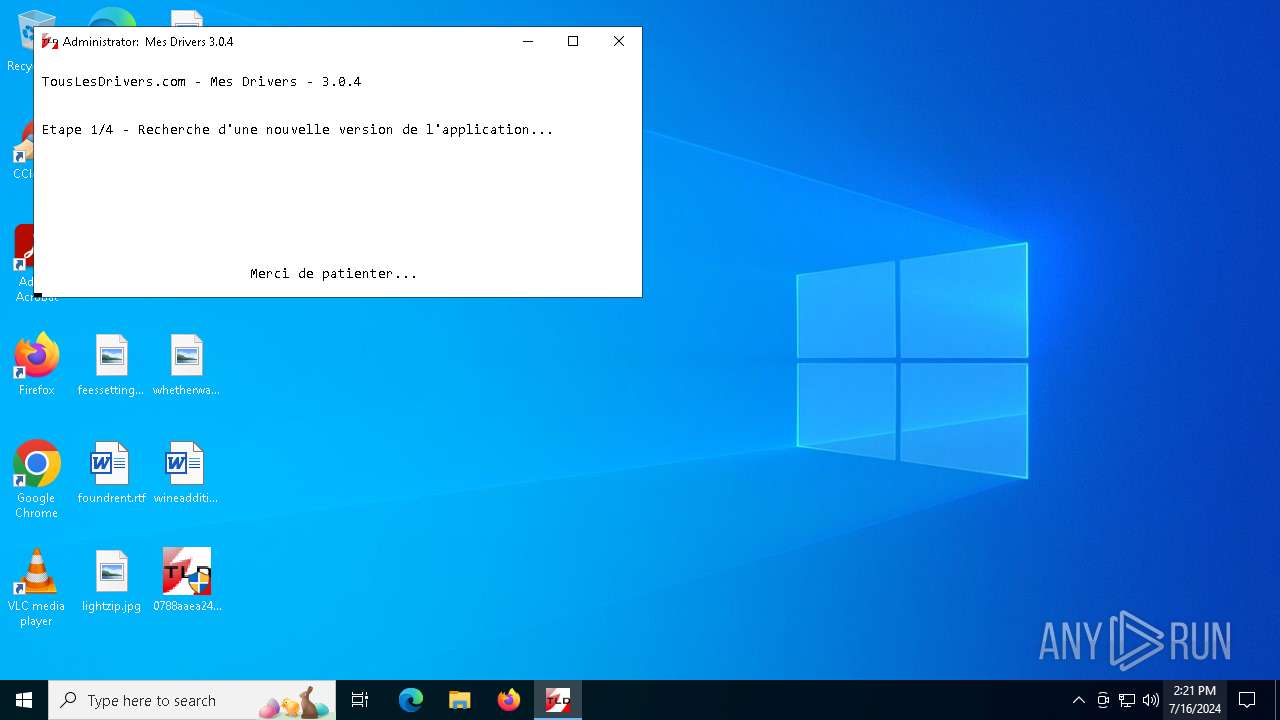
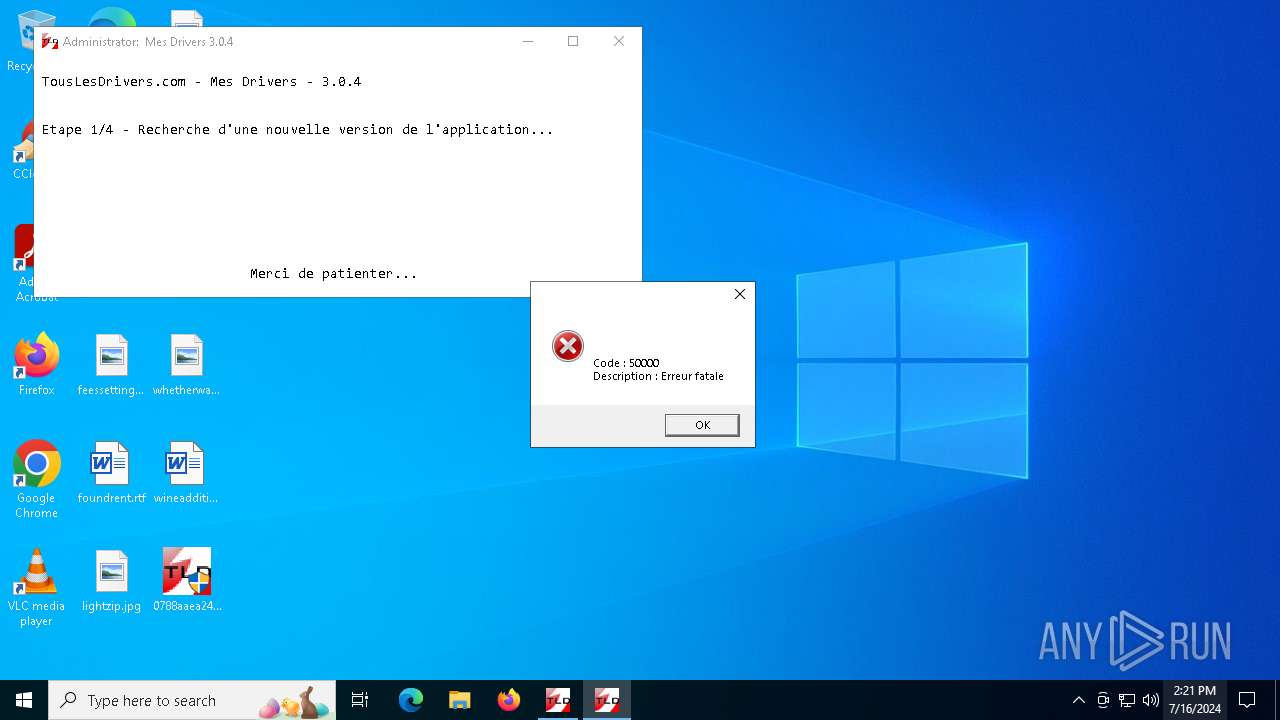
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
Total processes
134
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | WAITFOR unlock | C:\Windows\SysWOW64\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Desktop\0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe" | C:\Users\admin\Desktop\0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | — | explorer.exe | |||||||||||
User: admin Company: Tous Les Drivers Integrity Level: MEDIUM Description: Mes Drivers Exit code: 3221226540 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\Desktop\0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe" | C:\Users\admin\Desktop\0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | explorer.exe | ||||||||||||
User: admin Company: Tous Les Drivers Integrity Level: HIGH Description: Mes Drivers Exit code: 0 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
| 1768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | detection.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\detection.exe" | C:\Users\admin\AppData\Local\Temp\detection.exe | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | ||||||||||||
User: admin Company: Tous Les Drivers Integrity Level: HIGH Description: Mes Drivers Exit code: 0 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
| 2808 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3168 | C:\WINDOWS\system32\cmd.exe /S /D /c" VER " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3944 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\interface.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3976 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4392 | MODE CON: COLS=76 LINES=15 | C:\Windows\SysWOW64\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 596
Read events
11 577
Write events
19
Delete events
0
Modification events
| (PID) Process: | (1496) 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (1496) 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1496) 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1496) 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1496) 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C000000000000046FA0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
10
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1496 | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | C:\Users\admin\AppData\Local\Temp\detection.exe | executable | |
MD5:02BA1C44B6392F013A7AA0B91314F45A | SHA256:7FBE59195F5F6F45C8B38B12488A169FDCB3A272004DBAF44C9D92A60A3690CB | |||
| 1496 | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | C:\Users\admin\AppData\Local\Temp\interface.cmd | text | |
MD5:E0EB53551ACA2ACFF814DDD7ACA212E2 | SHA256:11993A03F68A33500A3CE8FBEB3E3C2042A28299D04F39EED40147709E76CA79 | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\curl_x86.exe | executable | |
MD5:213A2CE0C3E3BCC71DF42A9EDAD0BA35 | SHA256:FBC0D3A56DCC0B9C6FFE556D1FD58C57502325780F137B64788FBBBDFC13BB82 | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\aes_x86.exe | executable | |
MD5:82FF688AA9253B356E5D890FF311B59E | SHA256:B68FC901D758BA9EA3A5A616ABD34D1662197AA31B502F27CBF2579A947E53E9 | |||
| 1496 | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | C:\Users\admin\AppData\Local\Temp\waitfor_x86.exe | executable | |
MD5:DD8C73BDCF2077B82DBB6DDD8ECB6A6D | SHA256:C3370E8EC5CA54E8FD7EAC19C278689CF122EDAC91FAA4376DC24B1D807FE510 | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\detect_x64.exe | executable | |
MD5:6A7EC375AF8BA2E87FF7F23497E9944E | SHA256:65C68FD55281A0A4598807EA83531A0CB0E4E79A8C5BF38E9637E776F72C3514 | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\aes_x64.exe | executable | |
MD5:E5125D4651C008EBA61D9FD3ABD5AB31 | SHA256:874CB7A8513B781B25E176828FE8FE5AC73FA2FE29EA2AAC5FE0EAAD50E63F39 | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\curl_x64.exe | executable | |
MD5:E80C8CB9887A7C9426D4E843DDDB8A44 | SHA256:3DF4725778C0351E8472A0F8E18CAF4FA9B95C98E4F2D160A26C3749F9869568 | |||
| 1496 | 0788aaea249d92a84f70047efcacaa54c26320b439c490ba3ce00457955031d6.exe | C:\Users\admin\AppData\Local\Temp\interface.lnk | lnk | |
MD5:736503F980075D4D9C7162620C3D191F | SHA256:F633C3984BC67CFE0D70AFA37D73F0CEDB8D2F5DC772E3108C22DE80643F2DAC | |||
| 2412 | detection.exe | C:\Users\admin\AppData\Local\Temp\detect_x64_2.exe | executable | |
MD5:635E57FD7AEFFAF87F6242AF79F419AA | SHA256:4A097314779F4D9CC594F40DB5509487AA4C2C8BDC58BC7230FCB183334BFD97 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1220 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1792 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.189.173.24:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
1220 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1928 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1792 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1792 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1220 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1928 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1928 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1220 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1792 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1928 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4796 | curl_x64.exe | 51.255.80.171:443 | www.touslesdrivers.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.touslesdrivers.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |