| File name: | Mes_Drivers_3.0.4.exe |
| Full analysis: | https://app.any.run/tasks/0e3a8ca6-02f7-47da-9558-bee850600e56 |
| Verdict: | Suspicious activity |
| Analysis date: | June 26, 2020, 04:42:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 50A5E891DA27E63D54E68511E48AA026 |
| SHA1: | 87073D85A7BA420B15C8BB9A9E4ADC64DB2BCFEF |
| SHA256: | 0788AAEA249D92A84F70047EFCACAA54C26320B439C490BA3CE00457955031D6 |
| SSDEEP: | 24576:AfHFw5b9DOnFYrv+kjqipUompMEoNMDYSkbDknoI6JK+ZYtEi8ETtAM5B:sjFYrv+kjV45oeYSRnyJhOtEVcf5B |
MALICIOUS
Application was dropped or rewritten from another process
- curl_x86.exe (PID: 1720)
- detection.exe (PID: 2904)
SUSPICIOUS
Executable content was dropped or overwritten
- detection.exe (PID: 2904)
- Mes_Drivers_3.0.4.exe (PID: 3196)
Application launched itself
- cmd.exe (PID: 2692)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3040)
- Mes_Drivers_3.0.4.exe (PID: 3196)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (63.7) |
|---|---|---|
| .scr | | | Windows screen saver (20) |
| .exe | | | Win32 Executable (generic) (6.9) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:09 23:39:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 350720 |
| InitializedDataSize: | 1260544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5678c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.4.0 |
| ProductVersionNumber: | 3.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
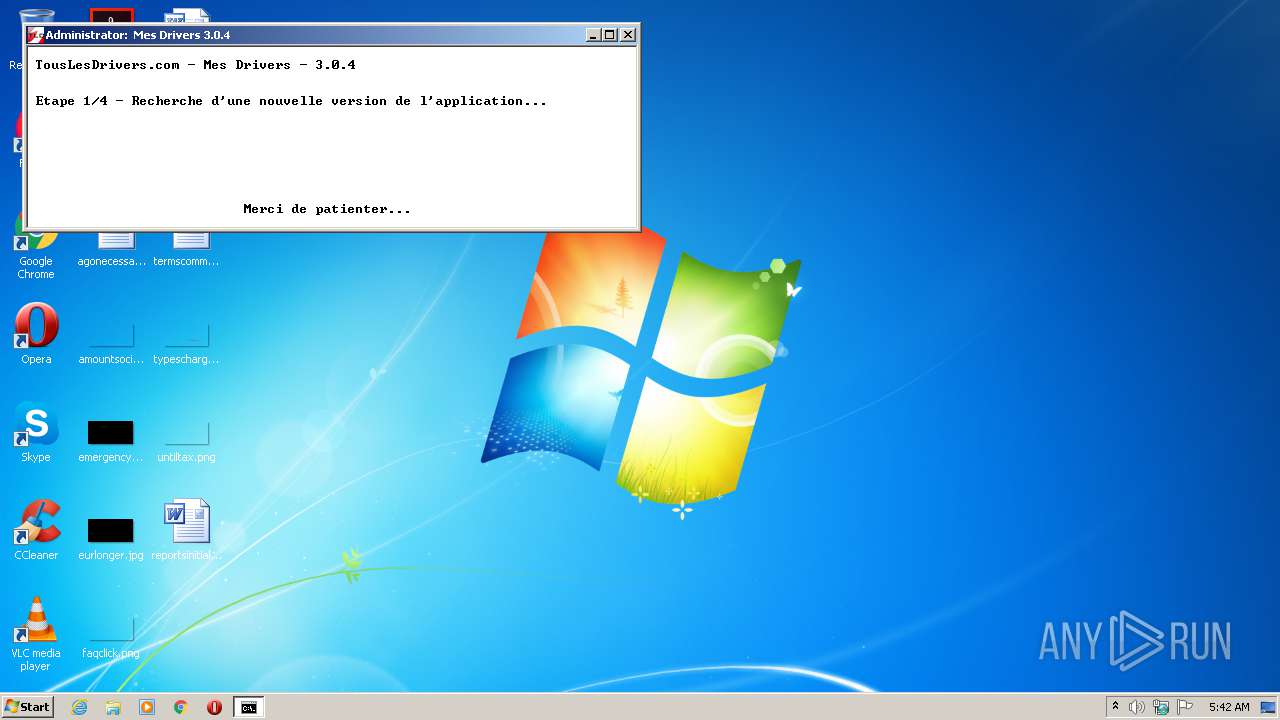
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2016 21:39:00 |
| Detected languages: |
|
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 09-Sep-2016 21:39:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00054BAC | 0x00054C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34359 |
.itext | 0x00056000 | 0x00000CD0 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.76395 |
.data | 0x00057000 | 0x00001C90 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.91883 |
.bss | 0x00059000 | 0x00006098 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00060000 | 0x00001486 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.84799 |
.didata | 0x00062000 | 0x00000154 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.41945 |
.tls | 0x00063000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00064000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.20692 |
.reloc | 0x00065000 | 0x000080A8 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x0006E000 | 0x0013029C | 0x00130400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.981 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07702 | 517 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4086 | 1.56933 | 56 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.32676 | 1784 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.47416 | 812 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.29282 | 904 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.27923 | 932 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.30087 | 328 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.34889 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.38228 | 516 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.30205 | 924 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
URLMON.DLL |
advapi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
48
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | MODE CON: COLS=76 LINES=15 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
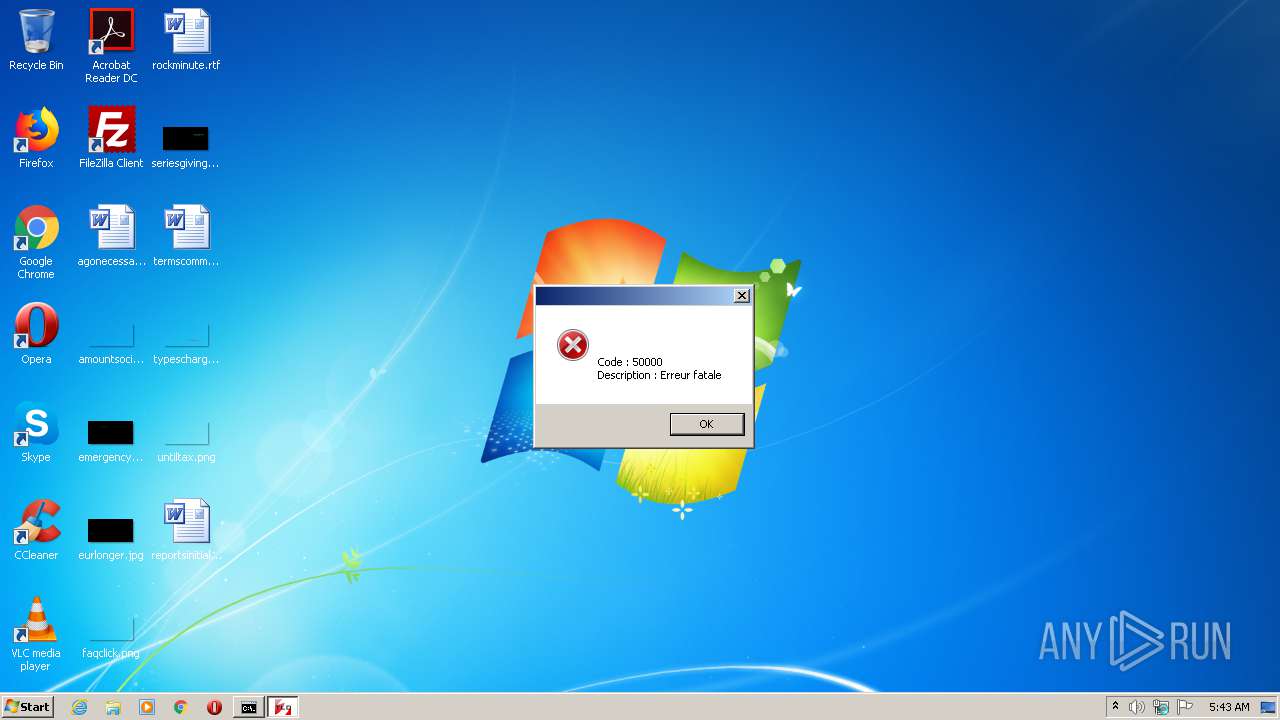
| 1720 | "C:\Users\admin\AppData\Local\Temp\curl_x86.exe" --connect-timeout 5 --max-time 20 --fail --silent --request GET "https://www.touslesdrivers.com/php/mes_drivers/version.php?v_version=3.0.4" | C:\Users\admin\AppData\Local\Temp\curl_x86.exe | detection.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 28 Version: 7.51.0 Modules
| |||||||||||||||
| 1940 | WAITFOR unlock | C:\Windows\system32\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\Mes_Drivers_3.0.4.exe" | C:\Users\admin\AppData\Local\Temp\Mes_Drivers_3.0.4.exe | — | explorer.exe | |||||||||||
User: admin Company: Tous Les Drivers Integrity Level: MEDIUM Description: Mes Drivers Exit code: 3221226540 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
| 2556 | C:\Windows\system32\cmd.exe /S /D /c" VER " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2692 | "C:\Windows\system32\cmd.exe" /C START "" "C:\Users\admin\AppData\Local\Temp\interface.lnk" | C:\Windows\system32\cmd.exe | — | Mes_Drivers_3.0.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2772 | FINDSTR /I /R /C:"version 5\.[0-1]\." | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\Temp\detection.exe" | C:\Users\admin\AppData\Local\Temp\detection.exe | Mes_Drivers_3.0.4.exe | ||||||||||||
User: admin Company: Tous Les Drivers Integrity Level: HIGH Description: Mes Drivers Exit code: 0 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
| 3040 | cmd /c ""C:\Users\admin\AppData\Local\Temp\interface.cmd" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\Mes_Drivers_3.0.4.exe" | C:\Users\admin\AppData\Local\Temp\Mes_Drivers_3.0.4.exe | explorer.exe | ||||||||||||
User: admin Company: Tous Les Drivers Integrity Level: HIGH Description: Mes Drivers Exit code: 0 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
Total events
725
Read events
717
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3196) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3196) Mes_Drivers_3.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2692) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2692) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
10
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\detection.exe | executable | |
MD5:02BA1C44B6392F013A7AA0B91314F45A | SHA256:7FBE59195F5F6F45C8B38B12488A169FDCB3A272004DBAF44C9D92A60A3690CB | |||
| 3196 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\interface.lnk | lnk | |
MD5:418EA7780101EC47CFC78D8CFD2E19D8 | SHA256:52460EA4EF85088356C724F277D2A4AF1BCD314CD68AEE21791FE62F734B3B4A | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\curl_x64.exe | executable | |
MD5:E80C8CB9887A7C9426D4E843DDDB8A44 | SHA256:3DF4725778C0351E8472A0F8E18CAF4FA9B95C98E4F2D160A26C3749F9869568 | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\curl_x86.exe | executable | |
MD5:213A2CE0C3E3BCC71DF42A9EDAD0BA35 | SHA256:FBC0D3A56DCC0B9C6FFE556D1FD58C57502325780F137B64788FBBBDFC13BB82 | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\detect_x64.exe | executable | |
MD5:6A7EC375AF8BA2E87FF7F23497E9944E | SHA256:65C68FD55281A0A4598807EA83531A0CB0E4E79A8C5BF38E9637E776F72C3514 | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | executable | |
MD5:42344B0A6F2941A402BF7AAC3893A6BA | SHA256:F6971D84A1600EA51FD7508C4DA636BE8BF9EA406D472FC2D9E42B4AC58B77D8 | |||
| 3196 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\interface.cmd | text | |
MD5:E0EB53551ACA2ACFF814DDD7ACA212E2 | SHA256:11993A03F68A33500A3CE8FBEB3E3C2042A28299D04F39EED40147709E76CA79 | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\aes_x64.exe | executable | |
MD5:E5125D4651C008EBA61D9FD3ABD5AB31 | SHA256:874CB7A8513B781B25E176828FE8FE5AC73FA2FE29EA2AAC5FE0EAAD50E63F39 | |||
| 2904 | detection.exe | C:\Users\admin\AppData\Local\Temp\waitfor_x86_2.exe | executable | |
MD5:DD8C73BDCF2077B82DBB6DDD8ECB6A6D | SHA256:C3370E8EC5CA54E8FD7EAC19C278689CF122EDAC91FAA4376DC24B1D807FE510 | |||
| 3196 | Mes_Drivers_3.0.4.exe | C:\Users\admin\AppData\Local\Temp\waitfor_x86.exe | executable | |
MD5:DD8C73BDCF2077B82DBB6DDD8ECB6A6D | SHA256:C3370E8EC5CA54E8FD7EAC19C278689CF122EDAC91FAA4376DC24B1D807FE510 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1720 | curl_x86.exe | 85.31.204.81:443 | www.touslesdrivers.com | Jaguar Network SAS | FR | unknown |
— | — | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.touslesdrivers.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |