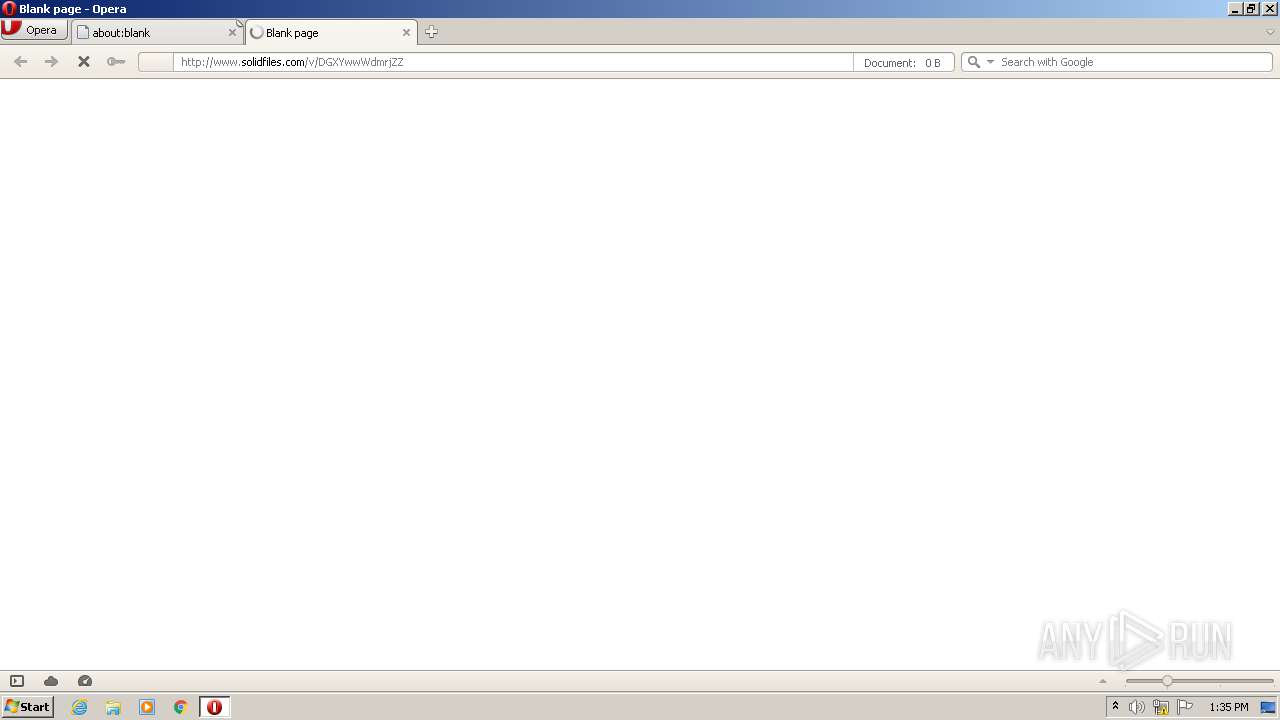
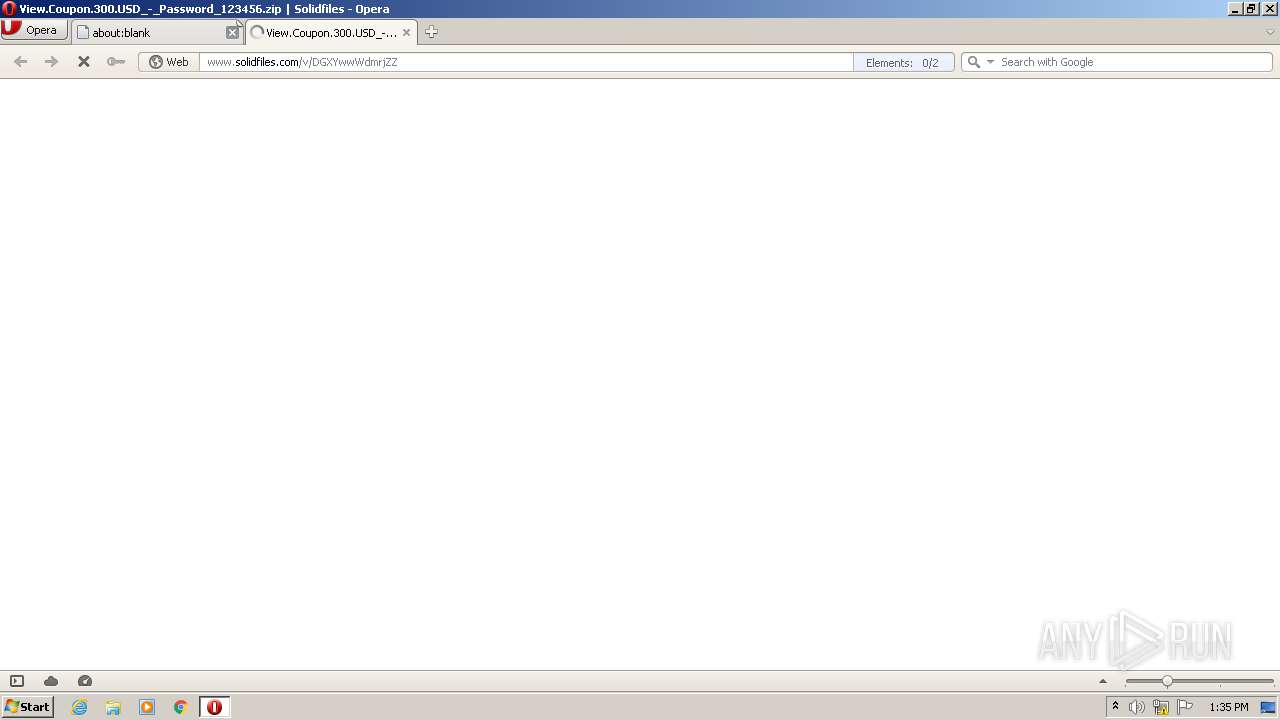
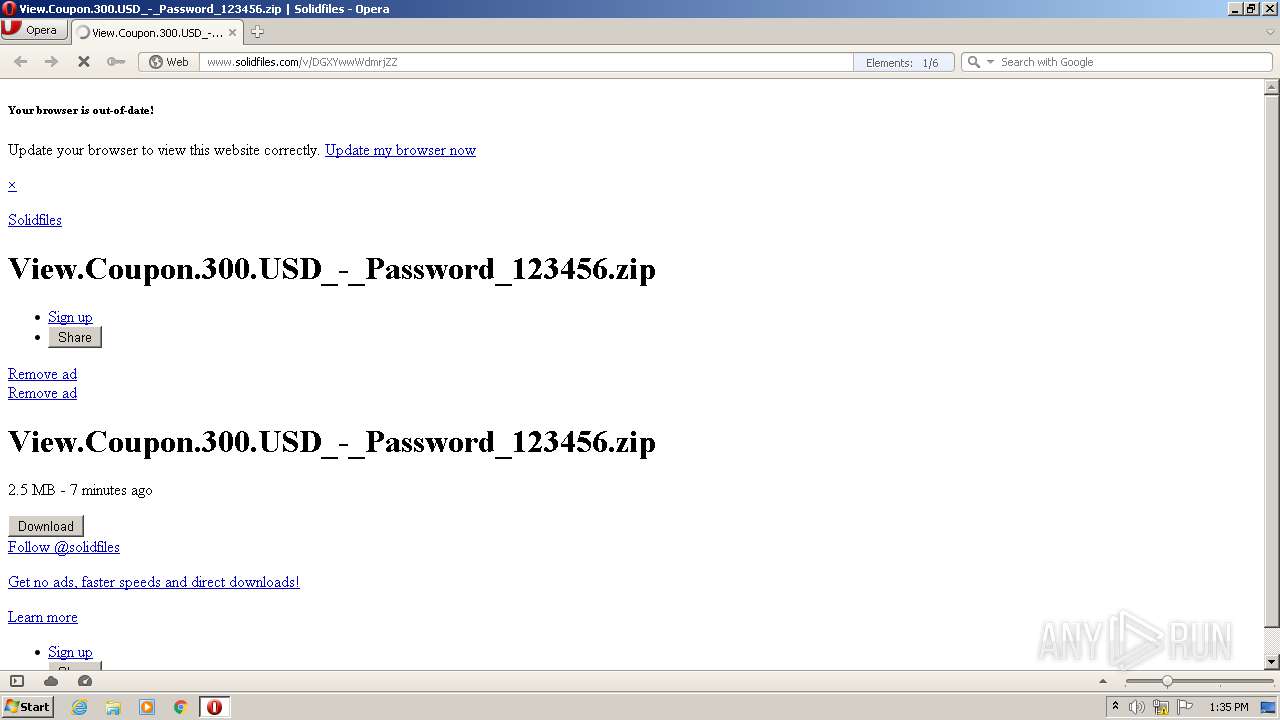
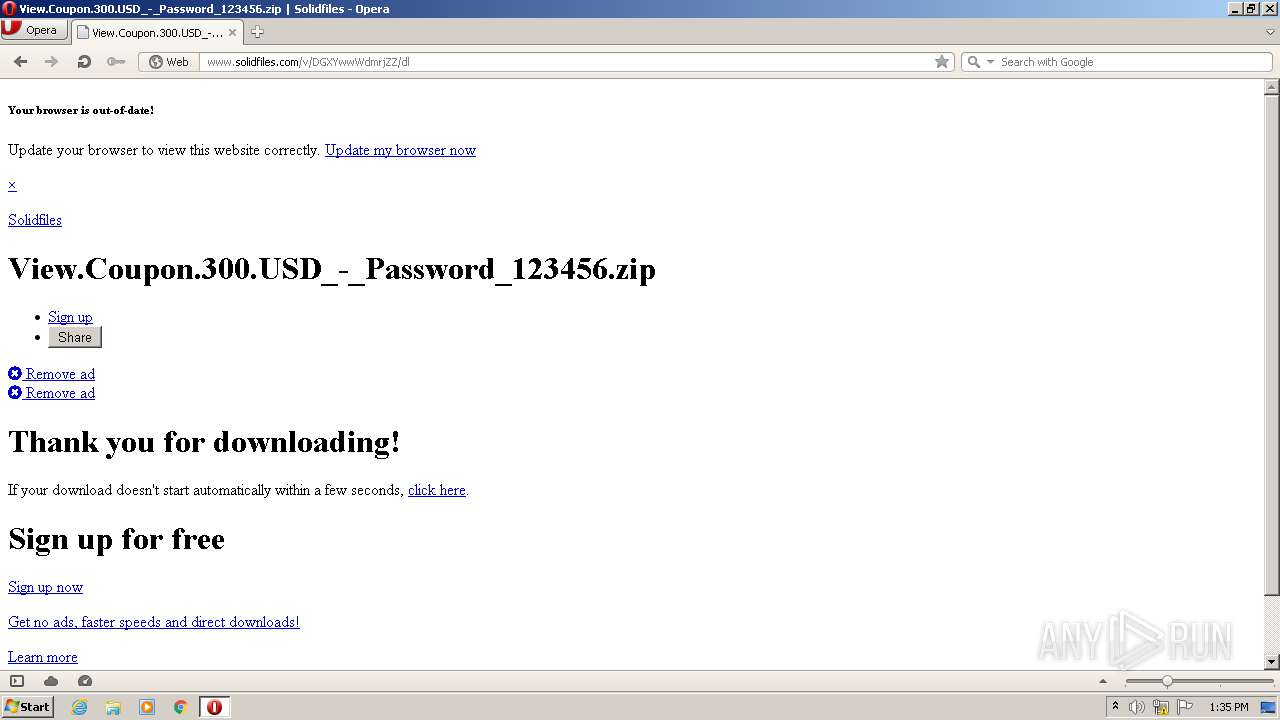
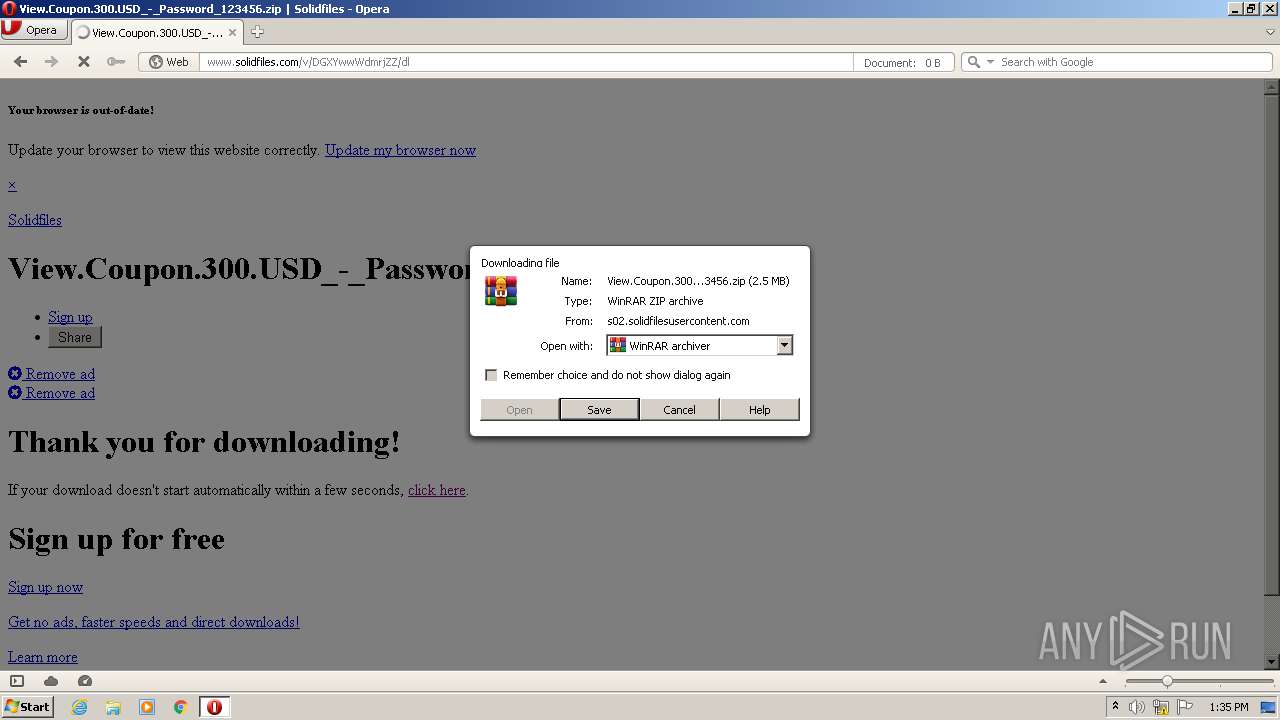
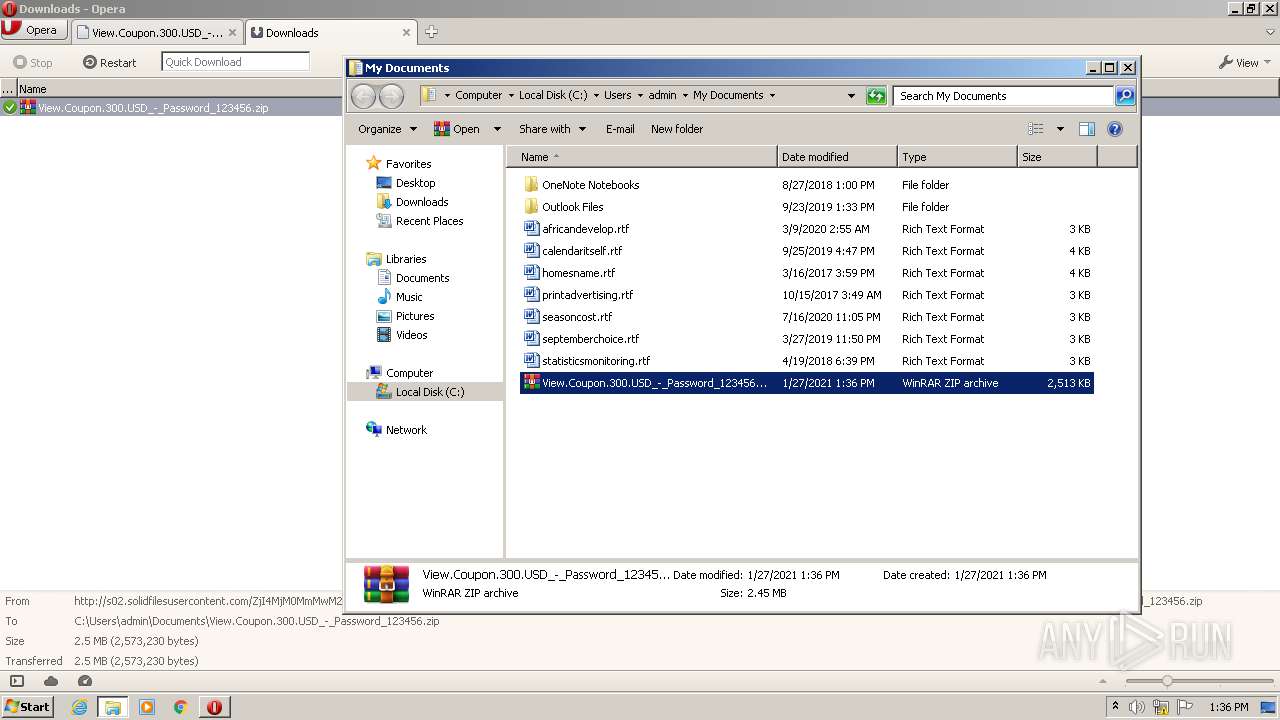
| URL: | http://www.solidfiles.com/v/DGXYwwWdmrjZZ |
| Full analysis: | https://app.any.run/tasks/d7e07fb0-3be3-4e20-a52b-164dd680e137 |
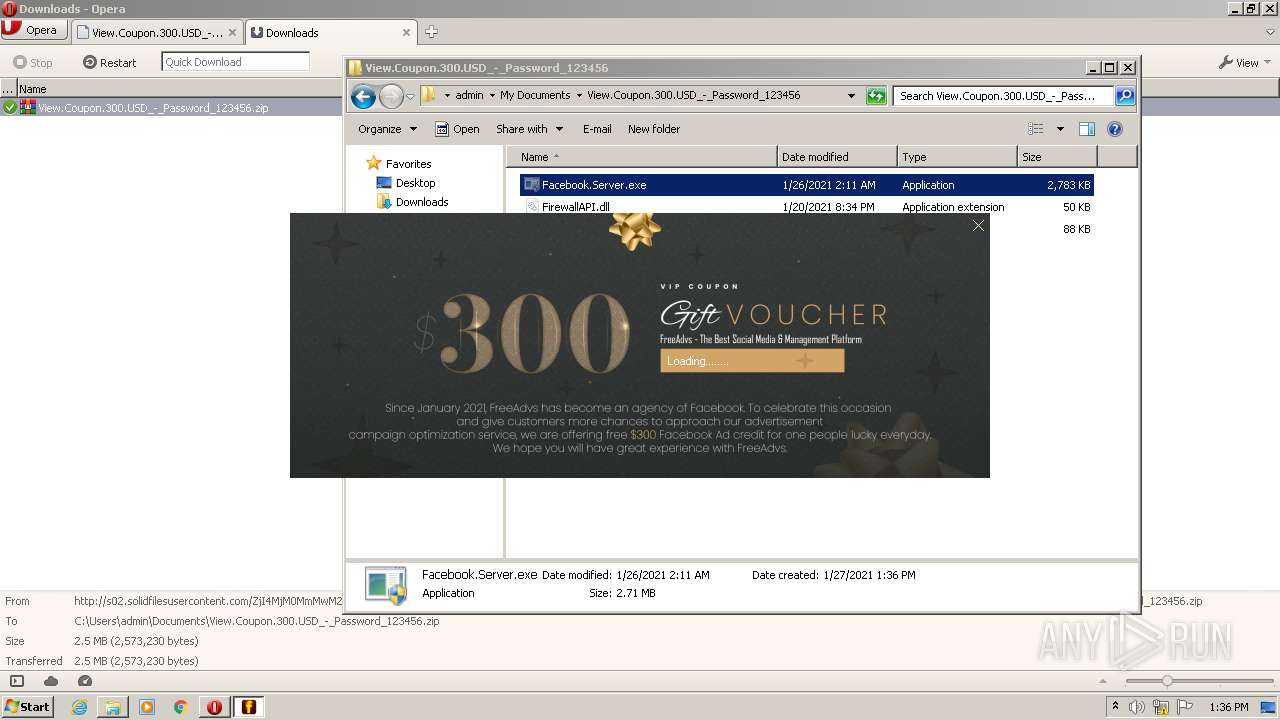
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2021, 13:35:17 |
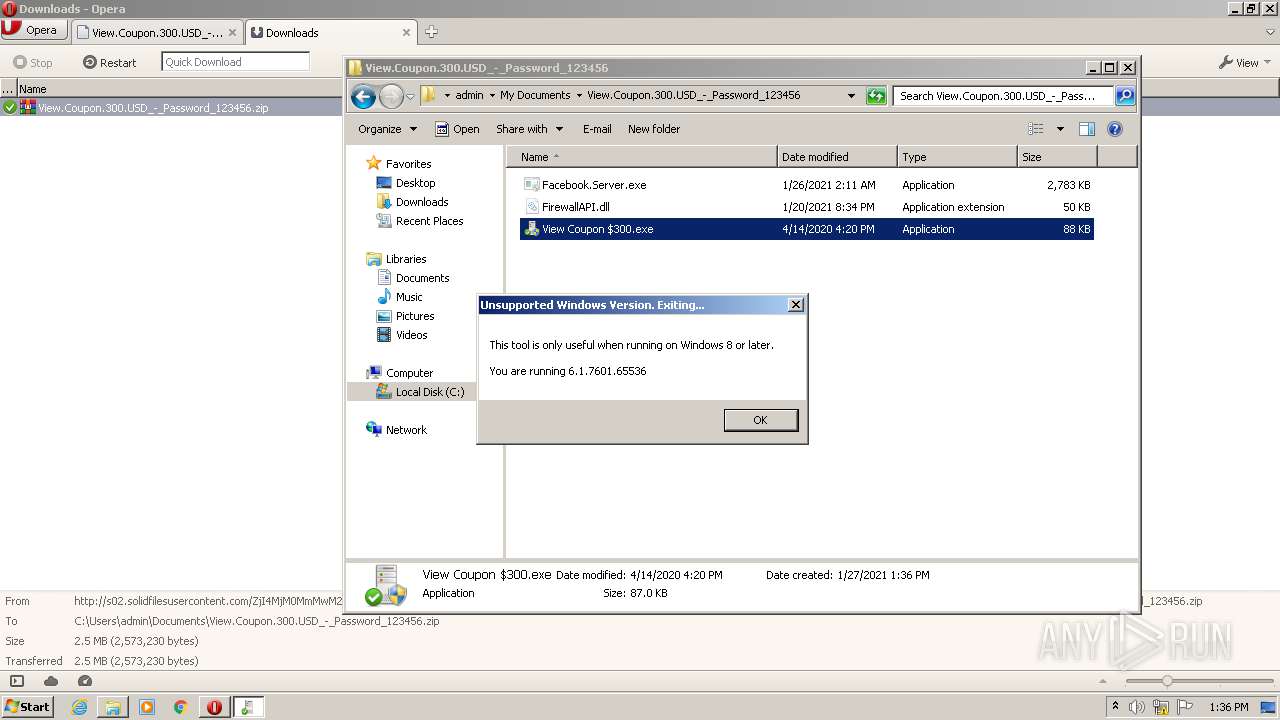
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E3E661A9C4CFEB6D95E0029B1BFF86A4 |
| SHA1: | 99F1969494DBC93DA53FF15E475F73454D13F572 |
| SHA256: | 077258A4BEB54BFEA04F1131BFFAB64A6F1FA22E021E0D8B21FC8F25DE13D2A3 |
| SSDEEP: | 3:N1KJS4kIKfj/:Cc4k3r |
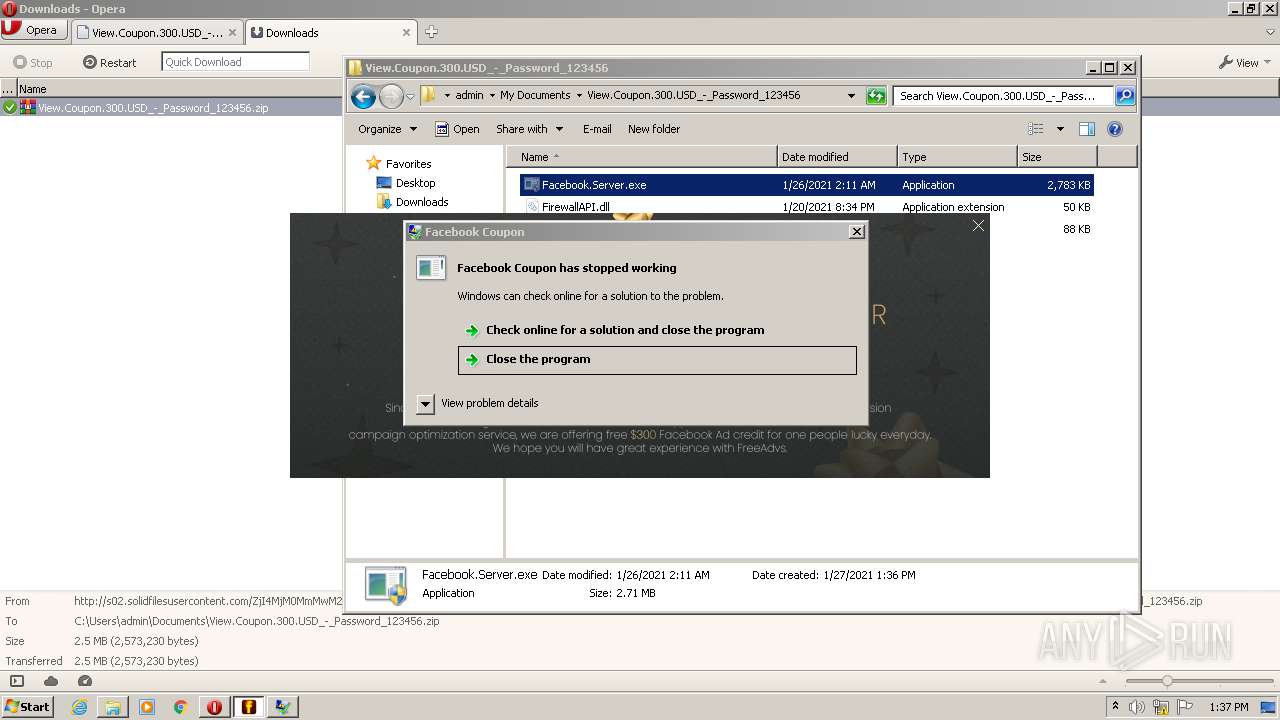
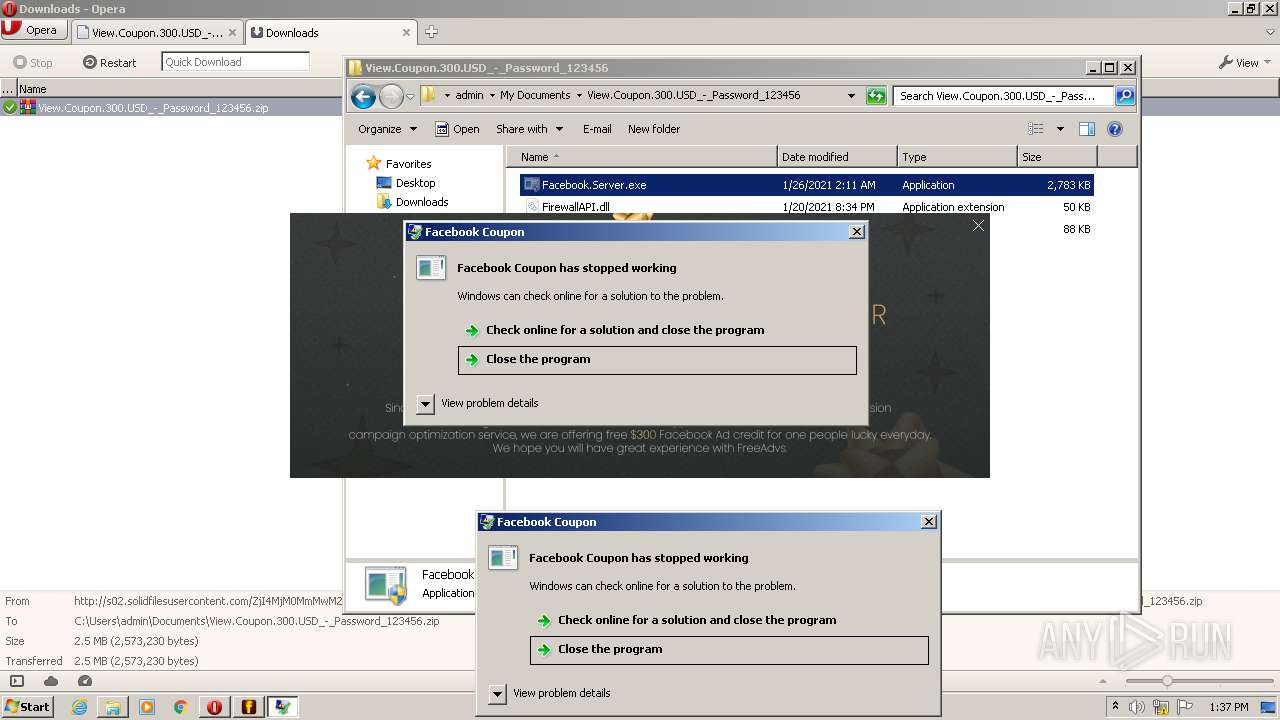
MALICIOUS
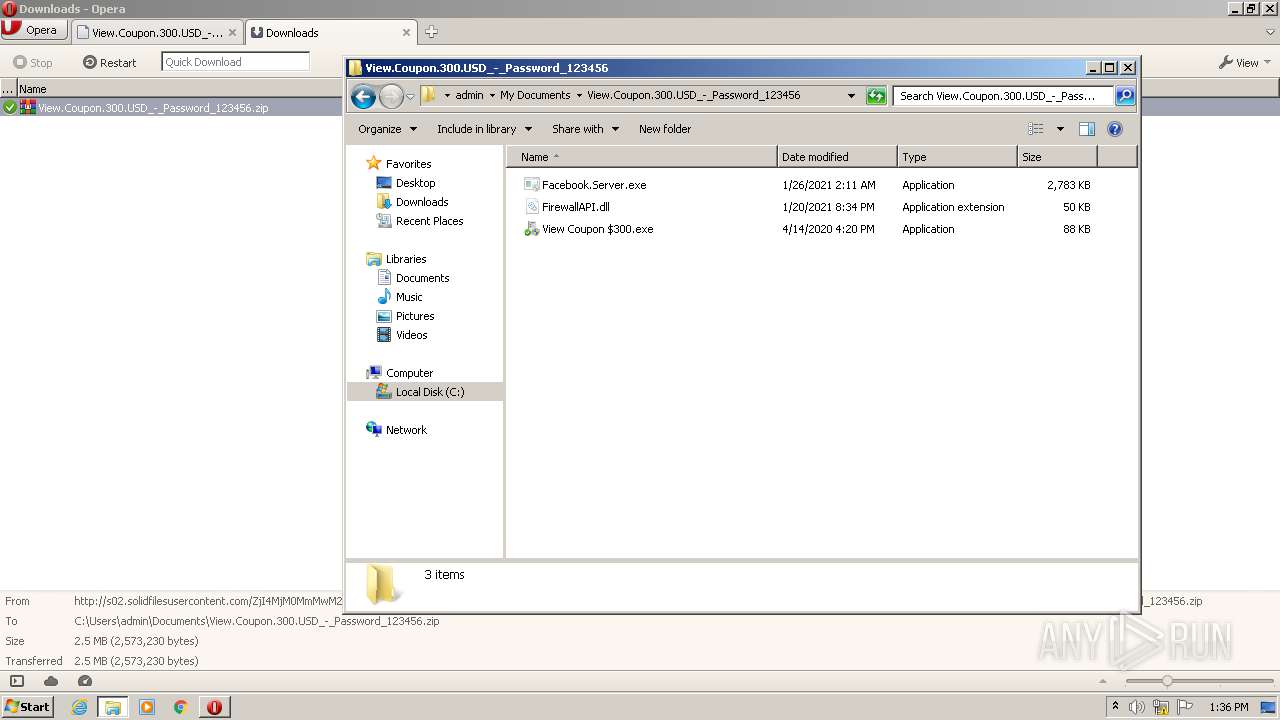
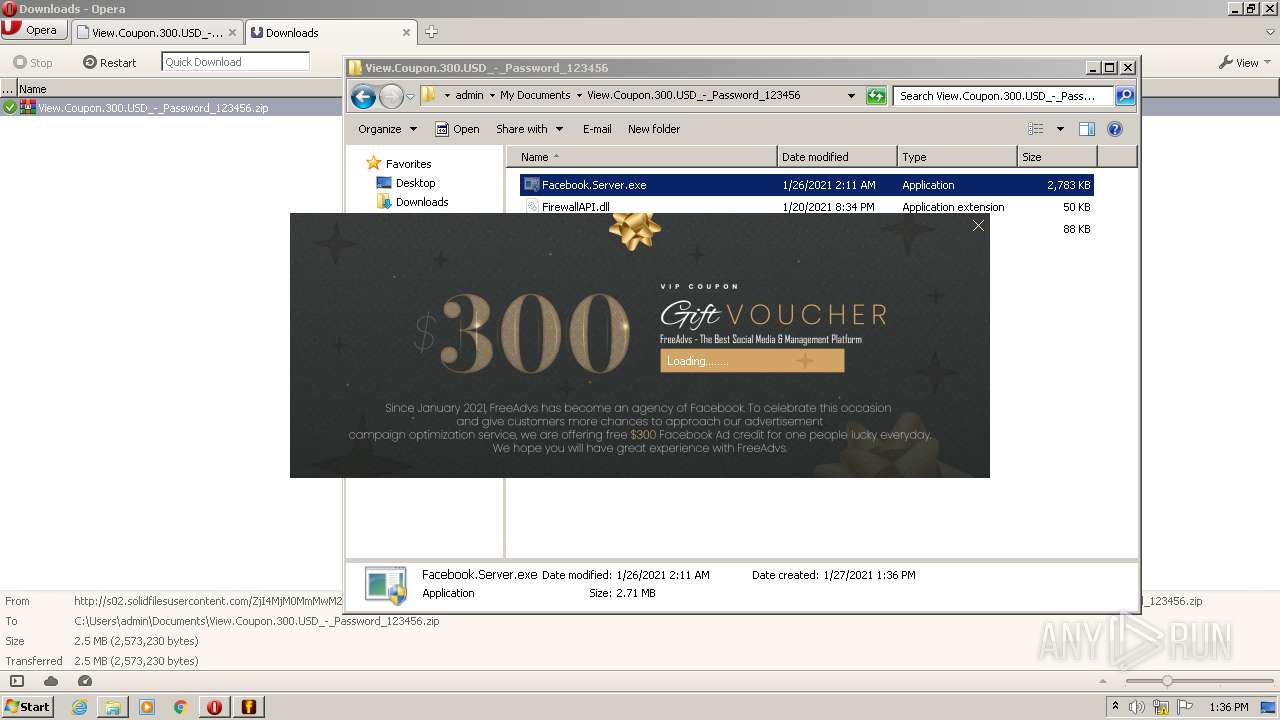
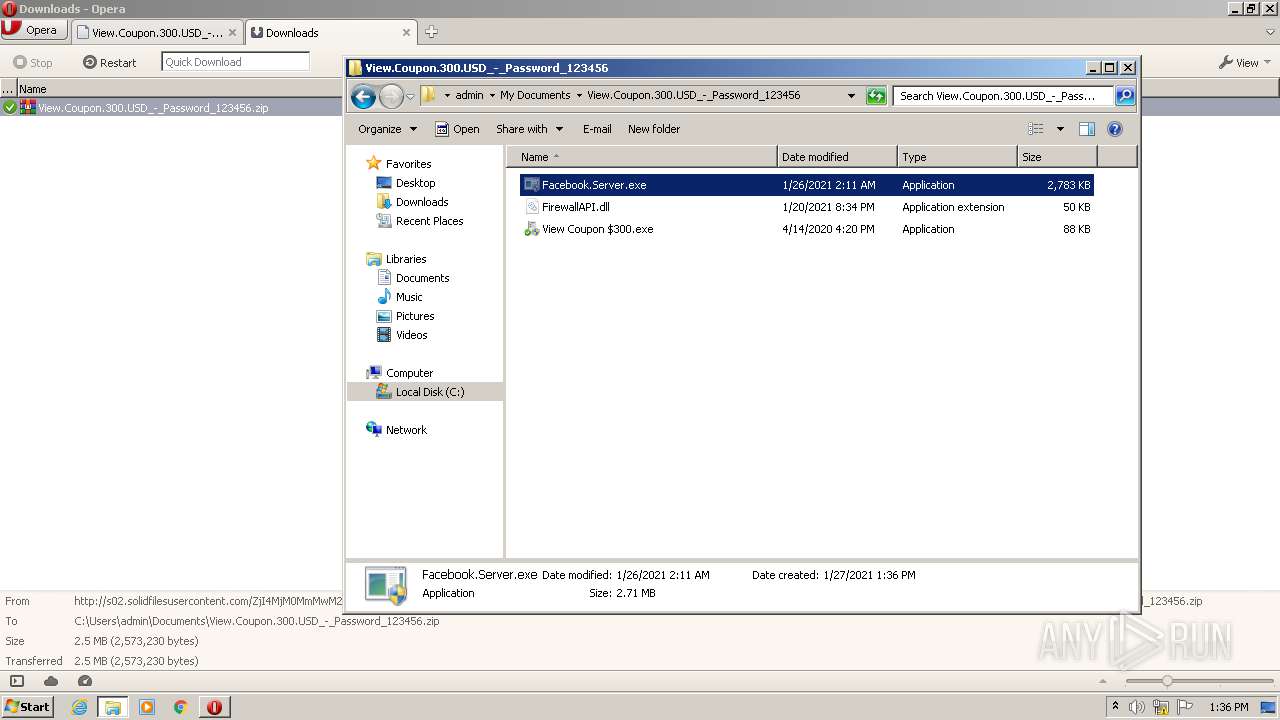
Application was dropped or rewritten from another process
- Facebook.Server.exe (PID: 3096)
- Facebook.Server.exe (PID: 3708)
- View Coupon $300.exe (PID: 2084)
- View Coupon $300.exe (PID: 2700)
- Facebook.Server.exe (PID: 2184)
- Facebook.Server.exe (PID: 3516)
Drops executable file immediately after starts
- WinRAR.exe (PID: 1052)
SUSPICIOUS
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1052)
Drops a file with too old compile date
- WinRAR.exe (PID: 1052)
Executed via COM
- explorer.exe (PID: 3192)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1052)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1052)
Creates files in the user directory
- Facebook.Server.exe (PID: 3708)
INFO
Creates files in the user directory
- opera.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
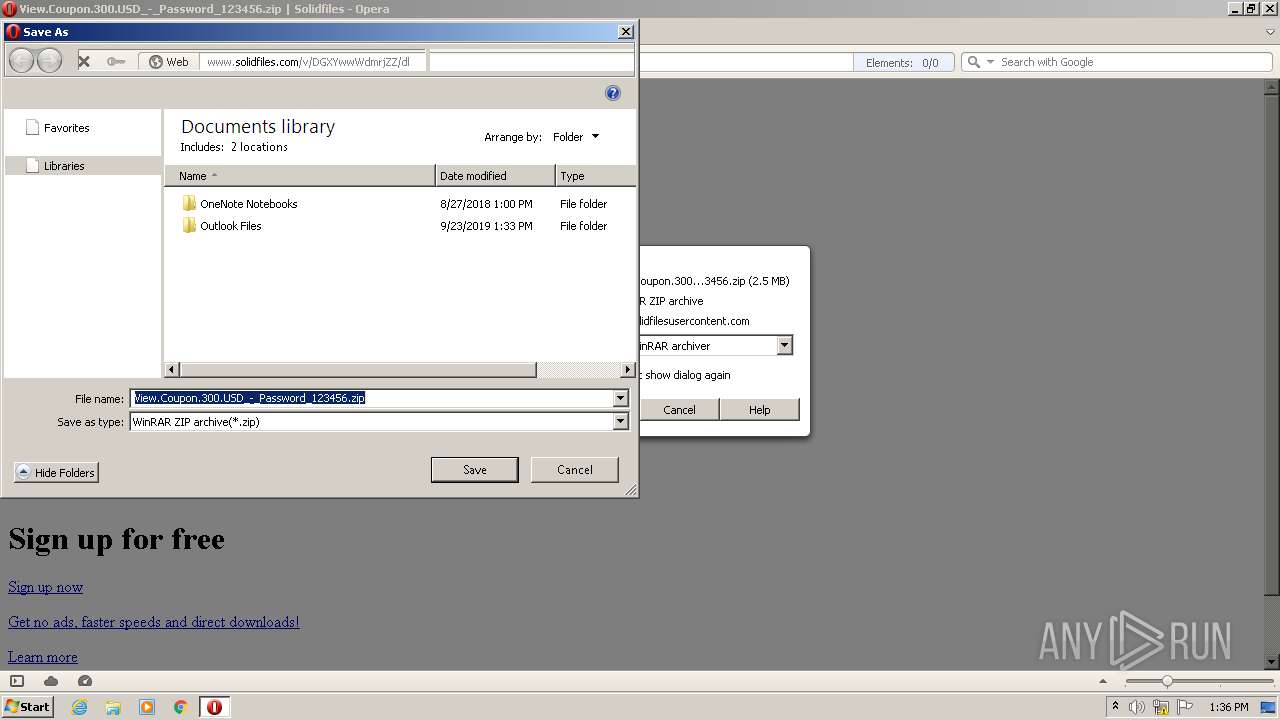
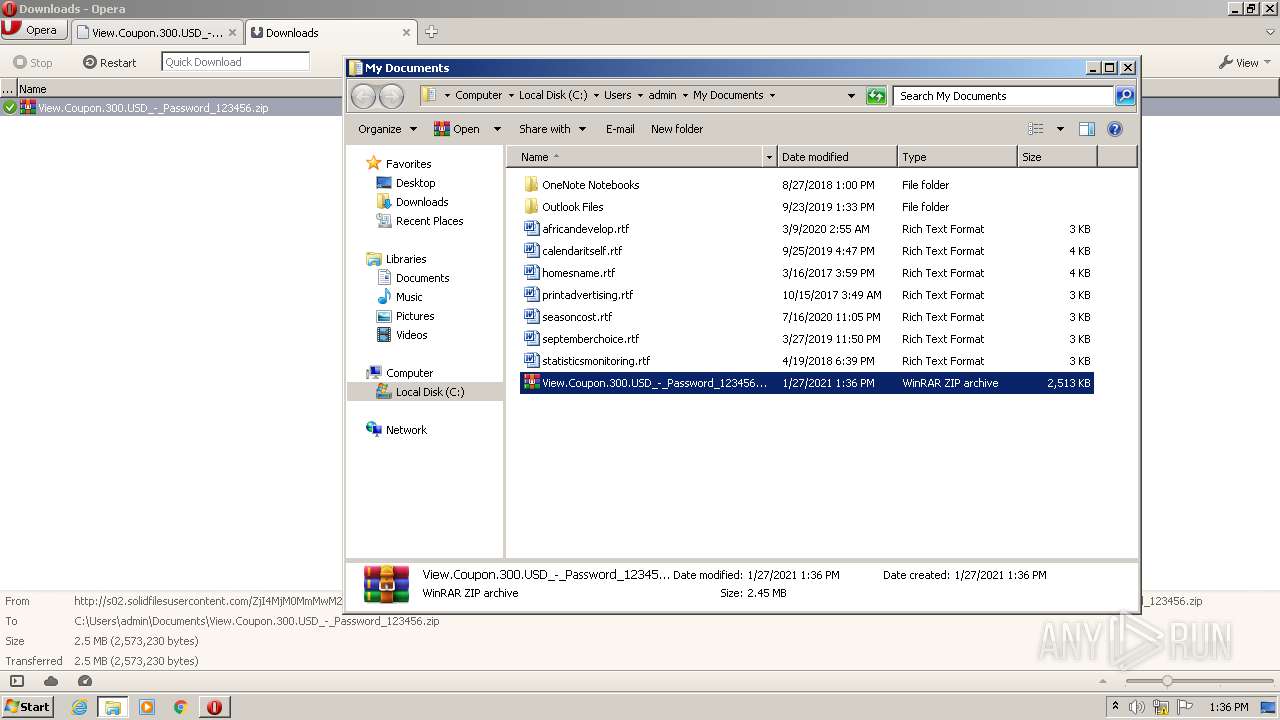
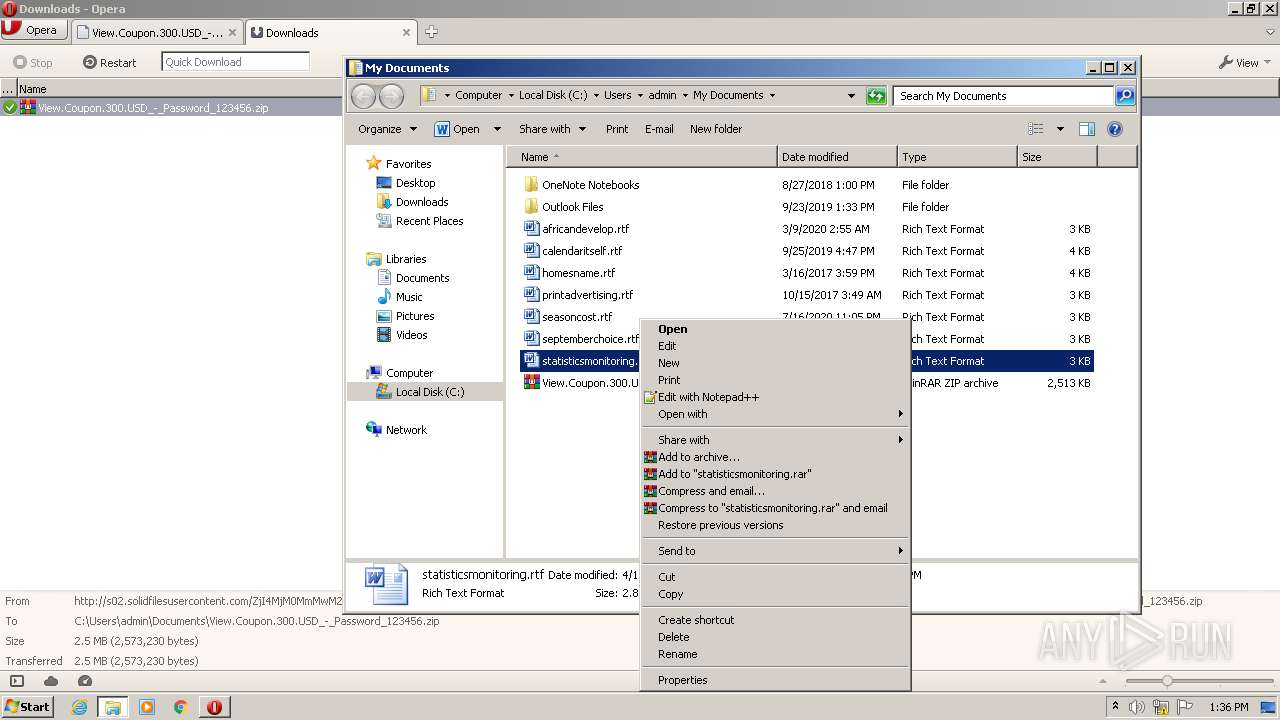
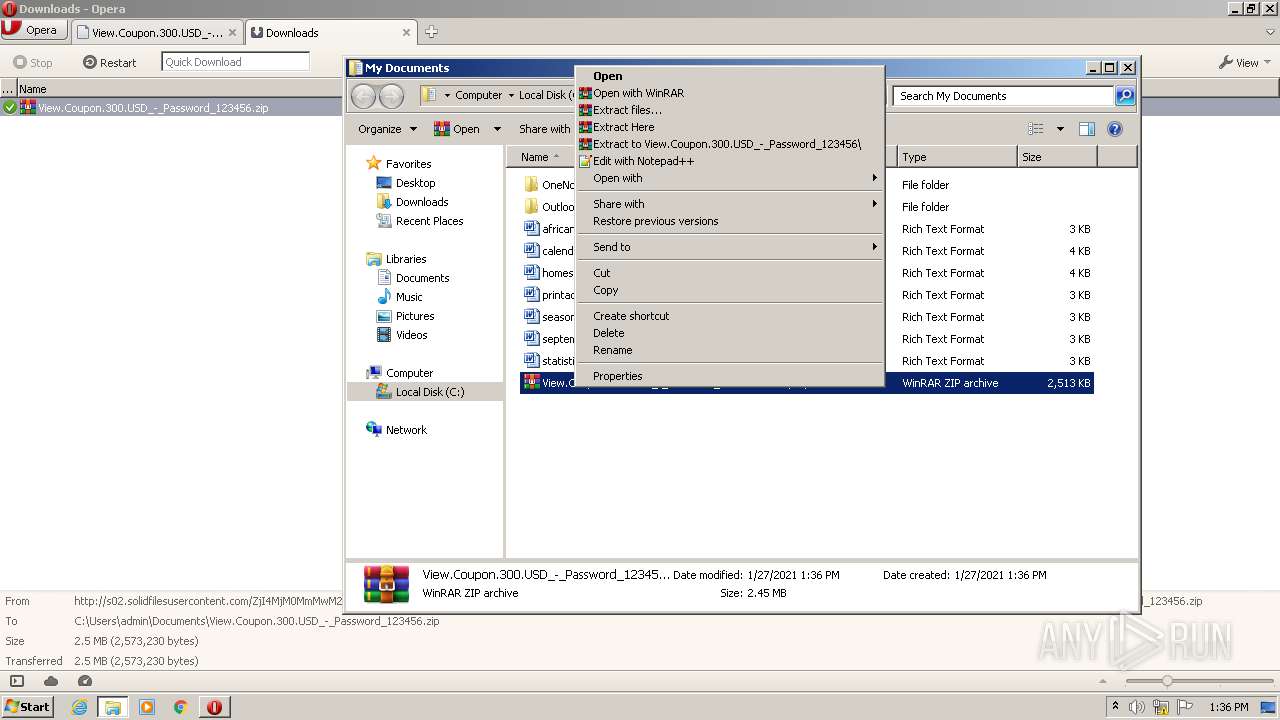
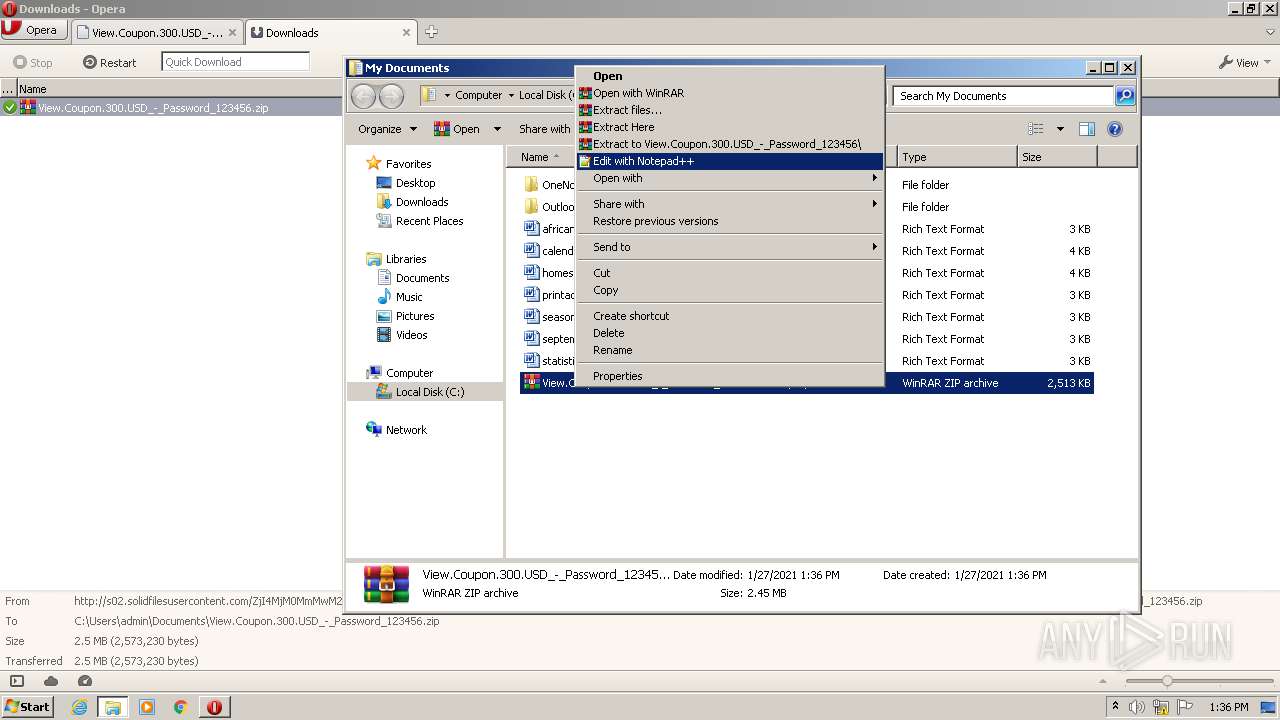
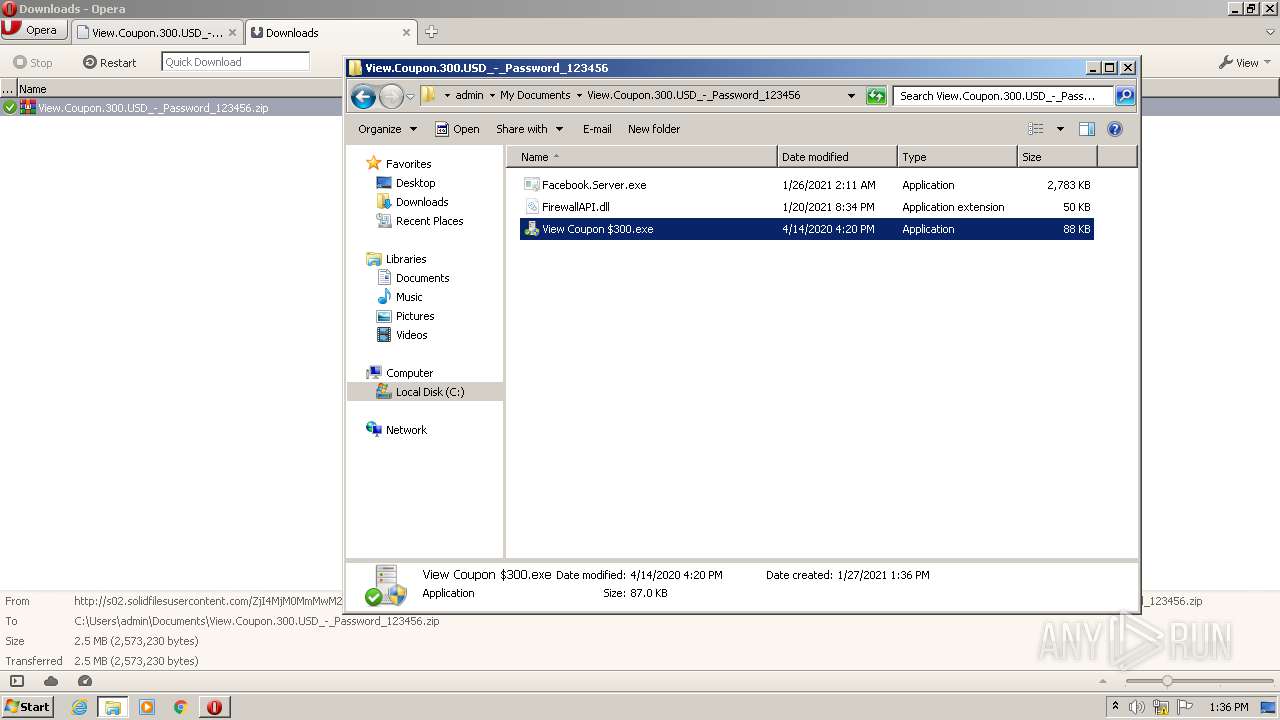
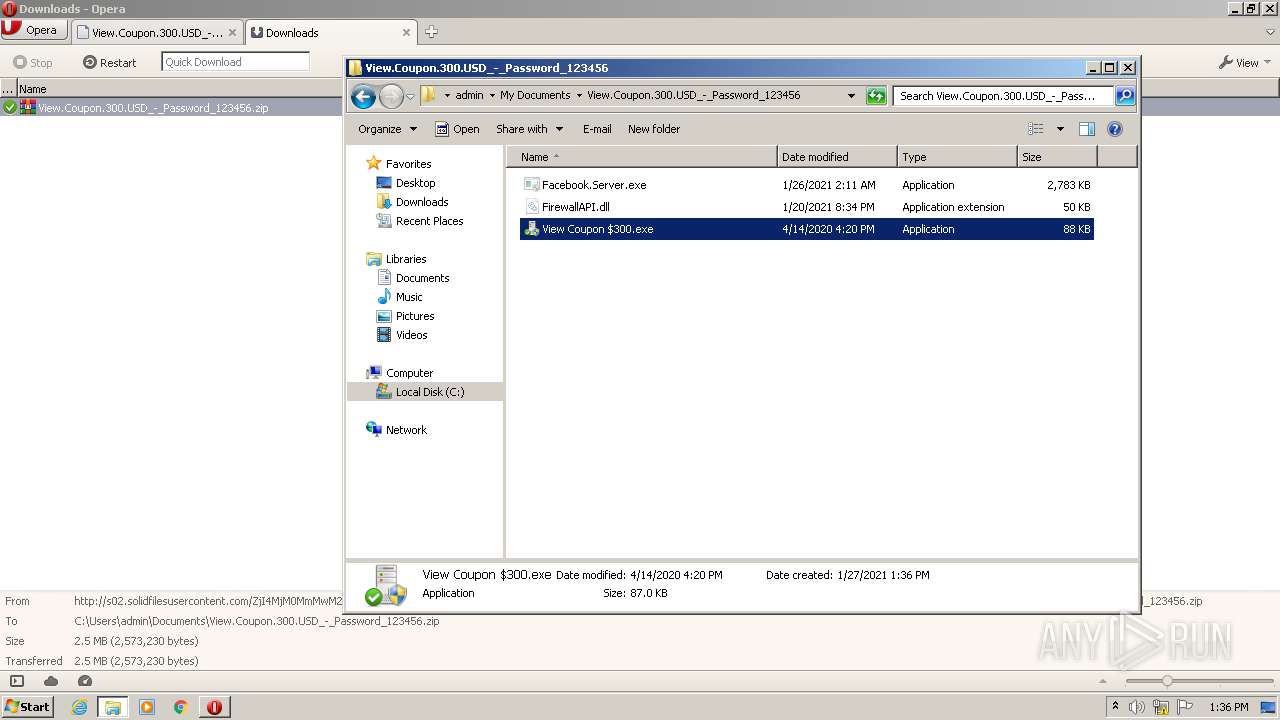
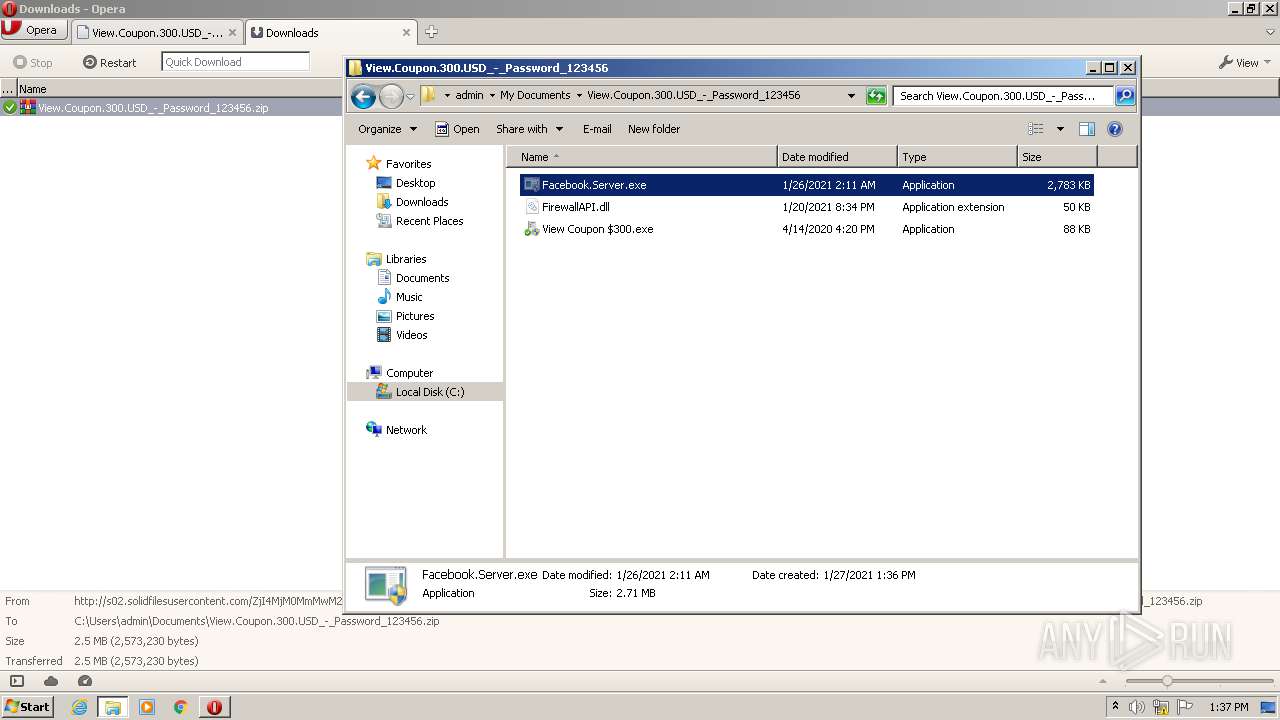
| 1052 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456.zip" C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
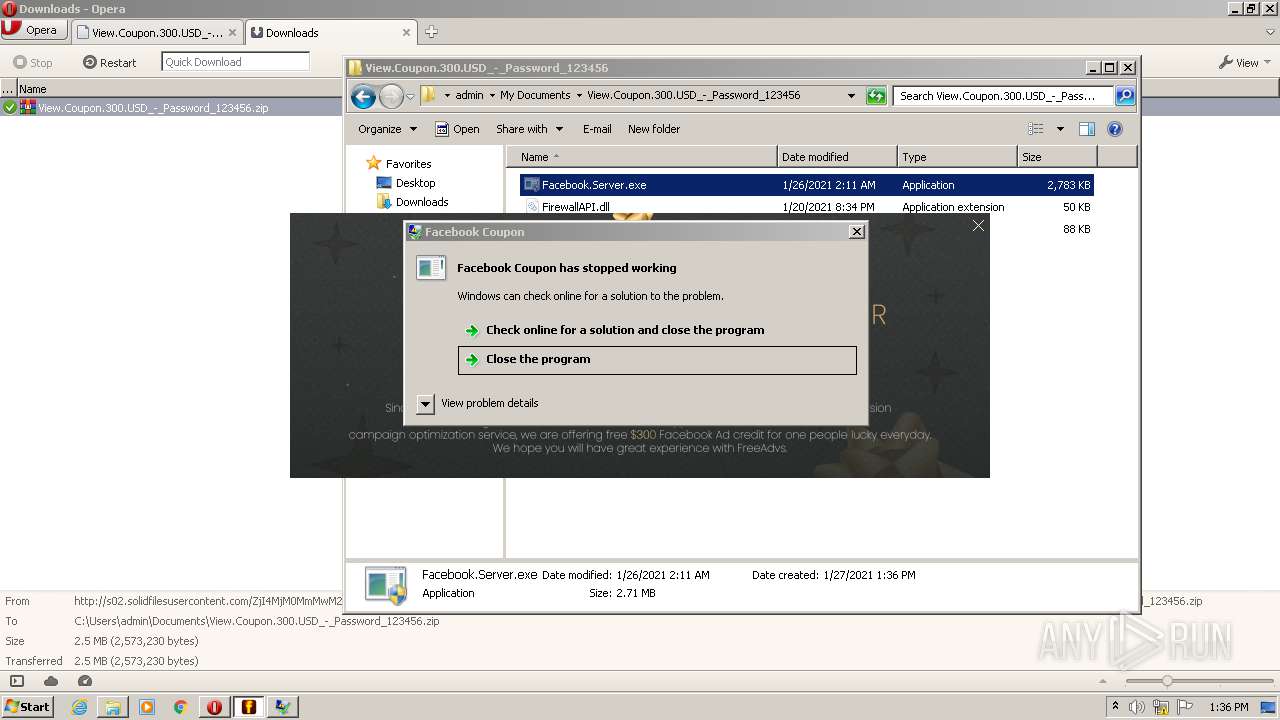
| 2084 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\View Coupon $300.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\View Coupon $300.exe | — | explorer.exe | |||||||||||
User: admin Company: Progress Software Corporation Integrity Level: MEDIUM Description: EnableLoopback Exit code: 3221226540 Version: 1.4.3.0 Modules
| |||||||||||||||
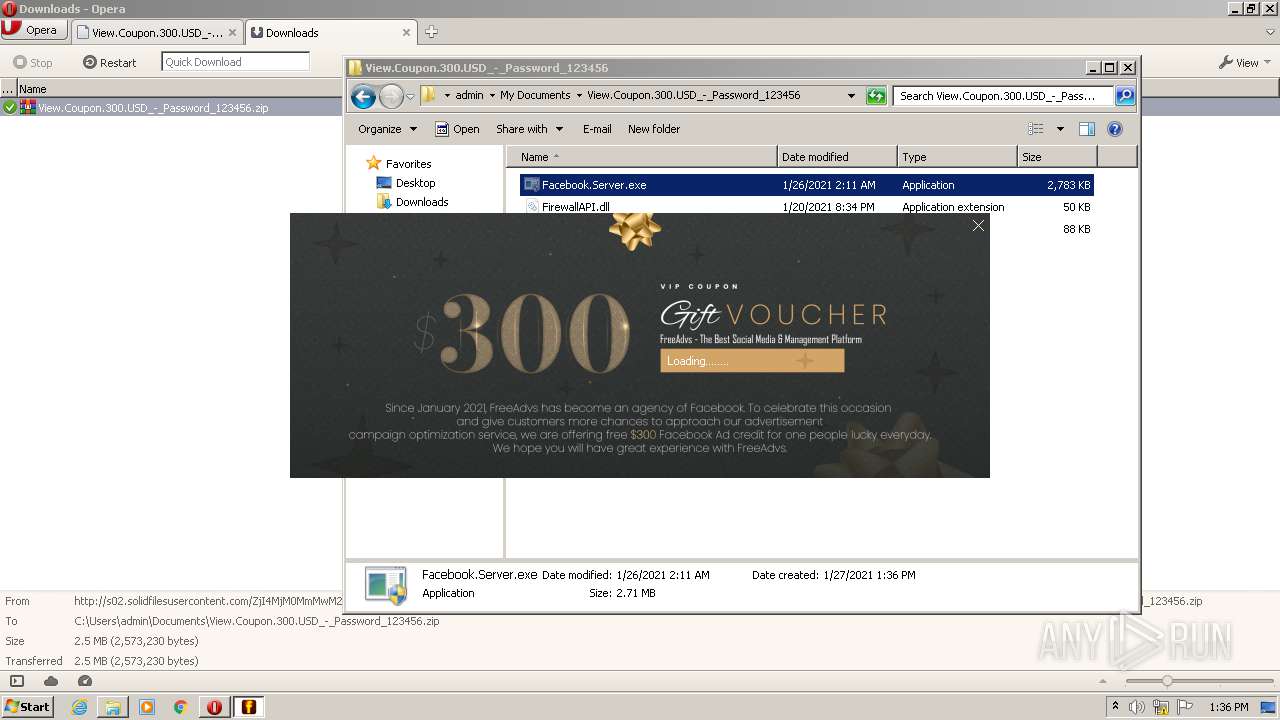
| 2184 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Facebook Coupon Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2656 | "C:\Windows\explorer.exe" /select,"C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456.zip" | C:\Windows\explorer.exe | — | opera.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Opera\opera.exe" "http://www.solidfiles.com/v/DGXYwwWdmrjZZ" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\View Coupon $300.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\View Coupon $300.exe | explorer.exe | ||||||||||||
User: admin Company: Progress Software Corporation Integrity Level: HIGH Description: EnableLoopback Exit code: 4294967295 Version: 1.4.3.0 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Facebook Coupon Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3192 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Facebook Coupon Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe" | C:\Users\admin\Documents\View.Coupon.300.USD_-_Password_123456\Facebook.Server.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Facebook Coupon Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 529
Read events
2 217
Write events
310
Delete events
2
Modification events
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://www.solidfiles.com/v/DGXYwwWdmrjZZ" | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000B00000000000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 2 |
Value: 6F0070006500720061002E00650078006500000014001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20000000 | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (2692) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\zip |
| Operation: | write | Name: | 0 |
Value: 14001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20009D0400009704811914106D0420000000486000000000000000000000000000000000000000000000000000000000A70000003153505330F125B7EF471A10A5F102608C9EEBAC650000000A000000001F0000002A00000056006900650077002E0043006F00750070006F006E002E003300300030002E005500530044005F002D005F00500061007300730077006F00720064005F003100320033003400350036002E007A00690070000000150000000C00000000150000000000000000000000110000000D00000000130000008000000000000000E802000031535053A66A63283D95D211B5D600C04FD918D01100000019000000001300000077014868390200002000000000111000002702000014001F50E04FD020EA3A6910A2D808002B30309D19002F433A5C000000000000000000000000000000000000007400310000000000454B314E1100557365727300600008000400EFBEEE3AA314454B314E2A0000005A01000000000100000000000000000036000000000055007300650072007300000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003300000014004C003100000000001C4D9960100061646D696E00380008000400EFBE454B804A1C4D99602A0000002D000000000004000000000000000000000000000000610064006D0069006E000000140080003100000000003B526E6C1100444F43554D457E310000680008000400EFBE454B814A3B526E6C2A0000007A0100000000020000000000000000003E000000000044006F00630075006D0065006E0074007300000040007300680065006C006C00330032002E0064006C006C002C002D003200310037003700300000001800B800320000000000000000008000566965772E436F75706F6E2E3330302E5553445F2D5F50617373776F72645F3132333435362E7A697000800008000400EFBE00000000000000002A0000000000000000000000000000000000000000000000000056006900650077002E0043006F00750070006F006E002E003300300030002E005500530044005F002D005F00500061007300730077006F00720064005F003100320033003400350036002E007A0069007000000038000000006500000018000000001F0000002A00000056006900650077002E0043006F00750070006F006E002E003300300030002E005500530044005F002D005F00500061007300730077006F00720064005F003100320033003400350036002E007A006900700000001D0000000B000000001F000000050000002E007A00690070000000000000000000DA0000003153505340E83E1E2BBC6C4782372ACD1A839B229900000008000000001F0000004300000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F00630075006D0065006E00740073005C0056006900650077002E0043006F00750070006F006E002E003300300030002E005500530044005F002D005F00500061007300730077006F00720064005F003100320033003400350036002E007A0069007000000000002500000003000000001F100000010000000700000066006F006C0064006500720000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
19
Text files
14
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr32F0.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr32F1.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3341.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K1EGSV7HQN2S6IU3U3CK.temp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr3FE4.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr4BAD.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\global_history.dat | text | |
MD5:— | SHA256:— | |||
| 2692 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF153e99.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
15
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | opera.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEA3pSlKCmaSrBQAAAACFj84%3D | US | der | 471 b | whitelisted |
2692 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
2692 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
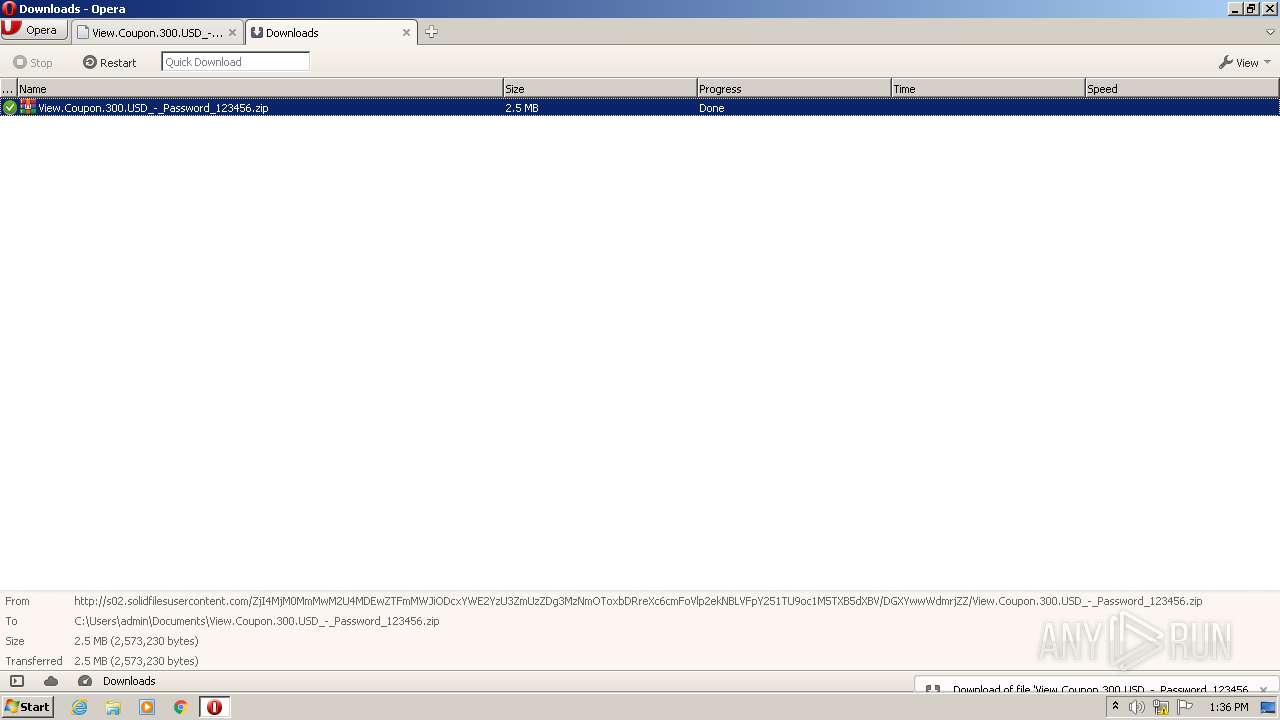
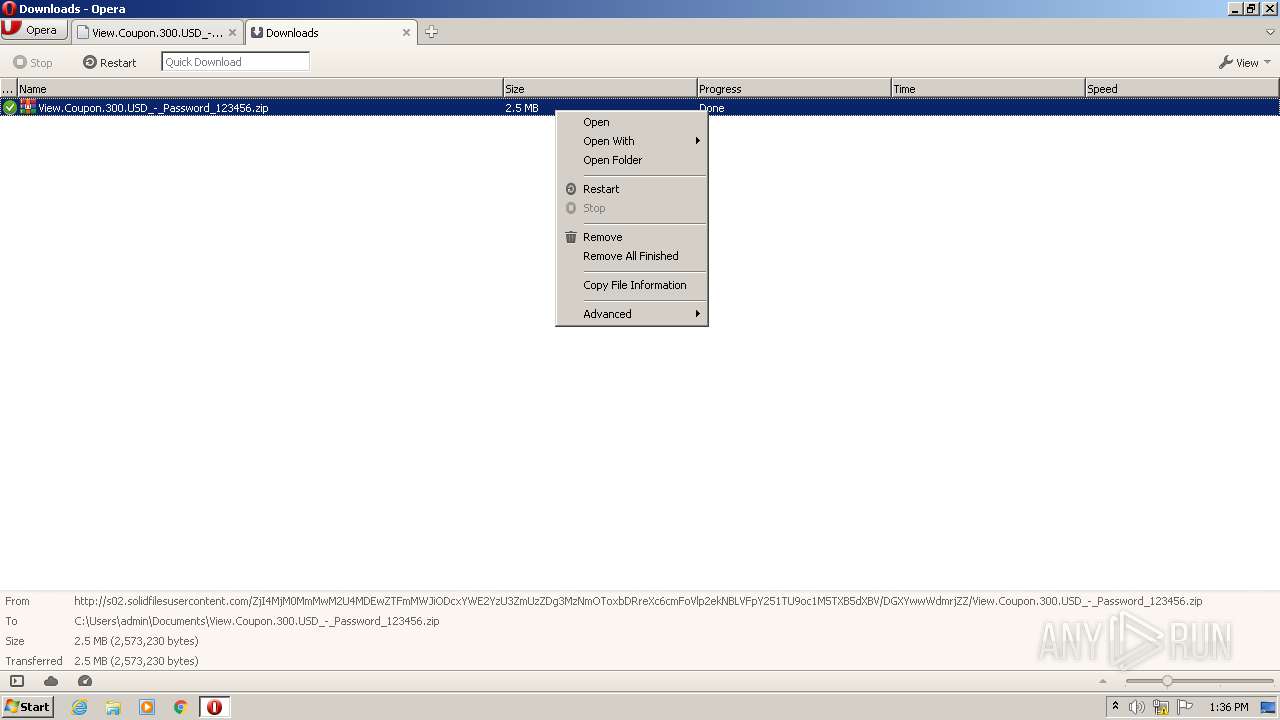
2692 | opera.exe | GET | 200 | 93.115.87.59:80 | http://s02.solidfilesusercontent.com/ZjI4MjM0MmMwM2U4MDEwZTFmMWJiODcxYWE2YzU3ZmUzZDg3MzNmOToxbDRreXc6cmFoVlp2ekNBLVFpY251TU9oc1M5TXB5dXBV/DGXYwwWdmrjZZ/View.Coupon.300.USD_-_Password_123456.zip | RO | compressed | 2.45 Mb | suspicious |
2692 | opera.exe | GET | 200 | 199.232.136.157:80 | http://platform.twitter.com/widgets.js | US | text | 28.0 Kb | whitelisted |
2692 | opera.exe | GET | 200 | 172.217.23.234:80 | http://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js | US | text | 28.9 Kb | whitelisted |
2692 | opera.exe | POST | 200 | 37.221.163.212:80 | http://www.solidfiles.com/v/DGXYwwWdmrjZZ/dl | RO | html | 14.0 Kb | suspicious |
2692 | opera.exe | POST | 200 | 37.221.163.212:80 | http://www.solidfiles.com/api/nodes/1872502242767268085/downloads | RO | text | 15 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | opera.exe | 172.217.23.195:80 | crl.pki.goog | Google Inc. | US | whitelisted |
2692 | opera.exe | 142.250.185.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2692 | opera.exe | 151.139.128.14:80 | crl.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2692 | opera.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2692 | opera.exe | 199.232.136.157:80 | platform.twitter.com | — | US | suspicious |
2692 | opera.exe | 93.115.87.59:80 | s02.solidfilesusercontent.com | Voxility S.R.L. | RO | suspicious |
2692 | opera.exe | 37.221.163.212:80 | www.solidfiles.com | Voxility S.R.L. | RO | suspicious |
2692 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2692 | opera.exe | 82.145.216.16:80 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
2692 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solidfiles.com |
| suspicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
solidfilescdn.com |
| malicious |
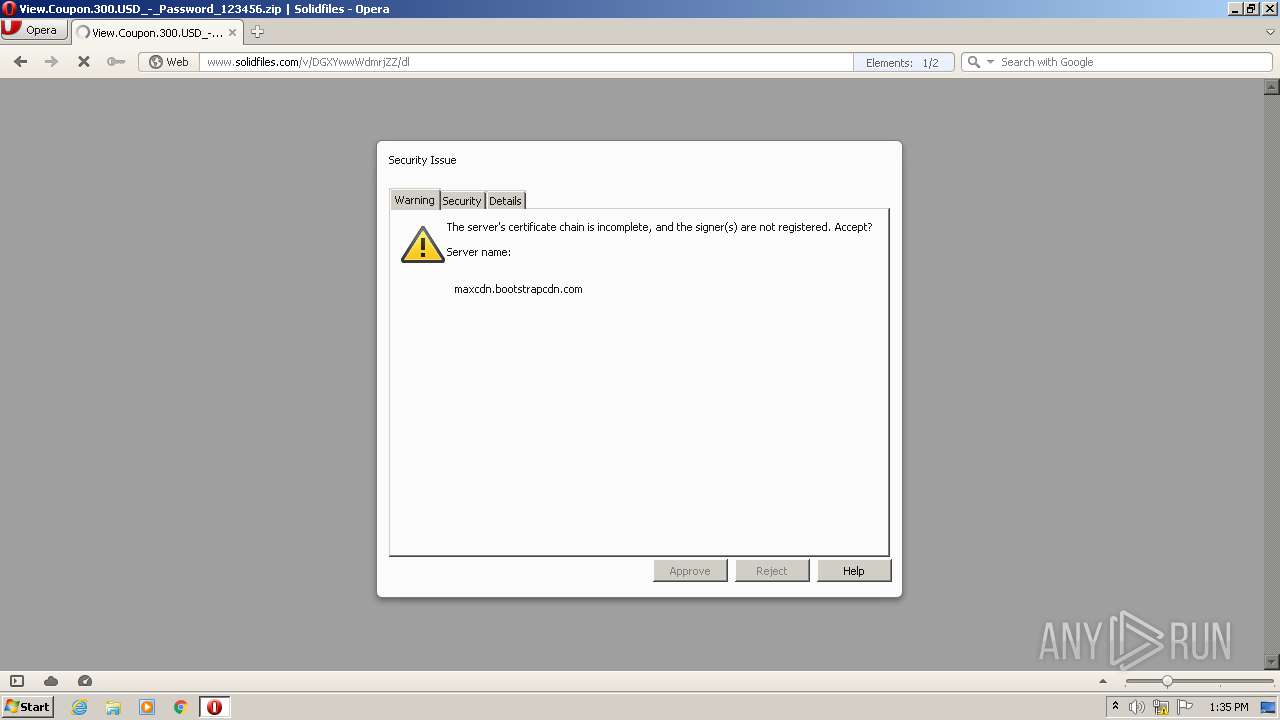
maxcdn.bootstrapcdn.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
twitter.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2692 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |