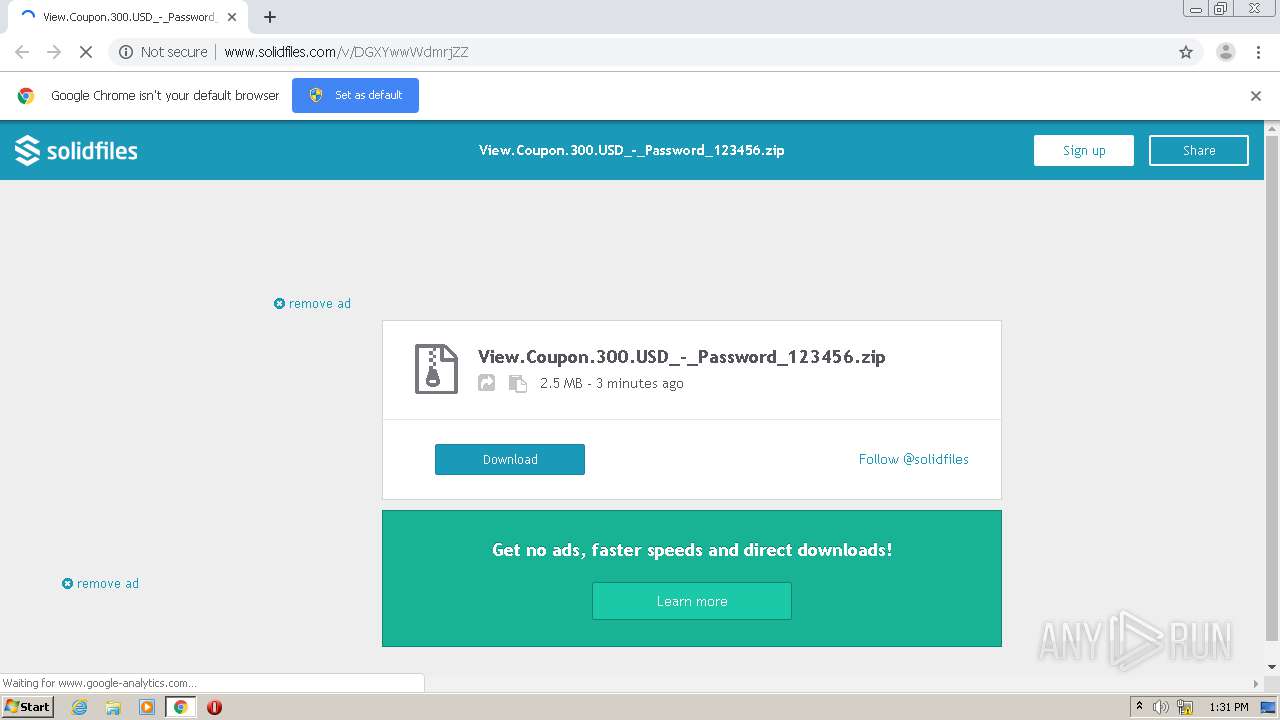
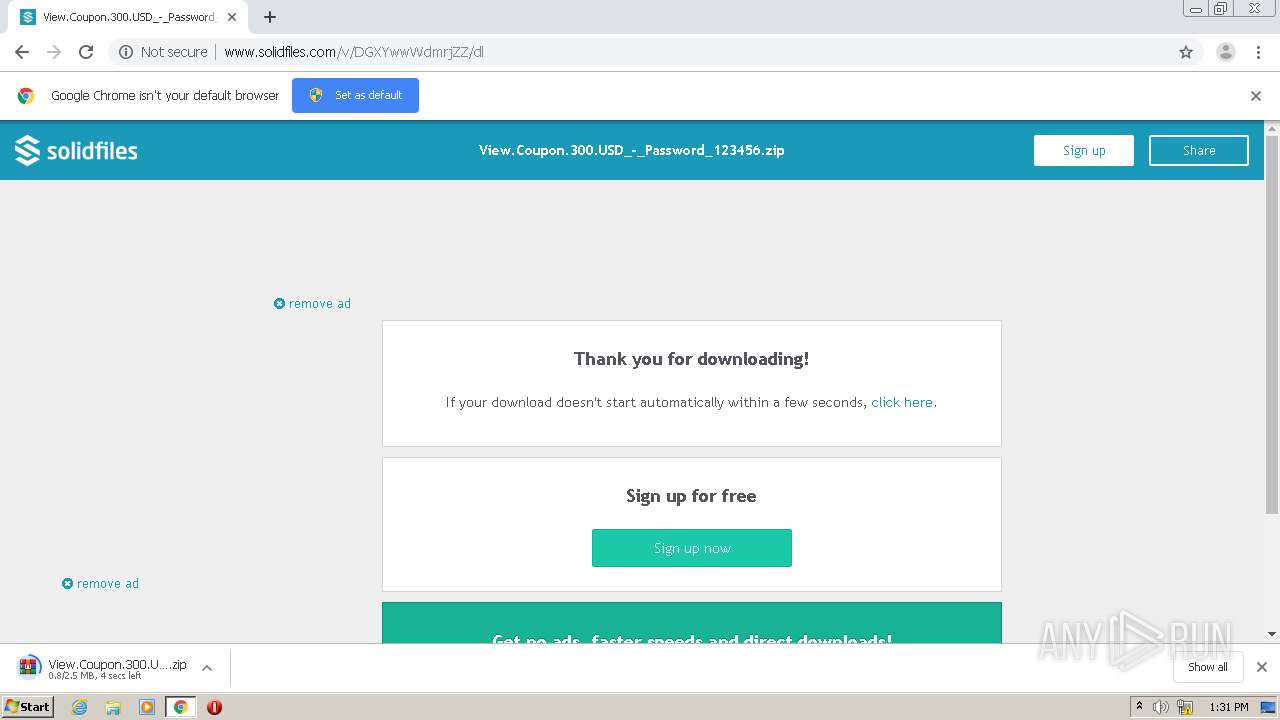
| URL: | http://www.solidfiles.com/v/DGXYwwWdmrjZZ |
| Full analysis: | https://app.any.run/tasks/04b81525-cc2e-4eb9-bda0-2bde1b12c475 |
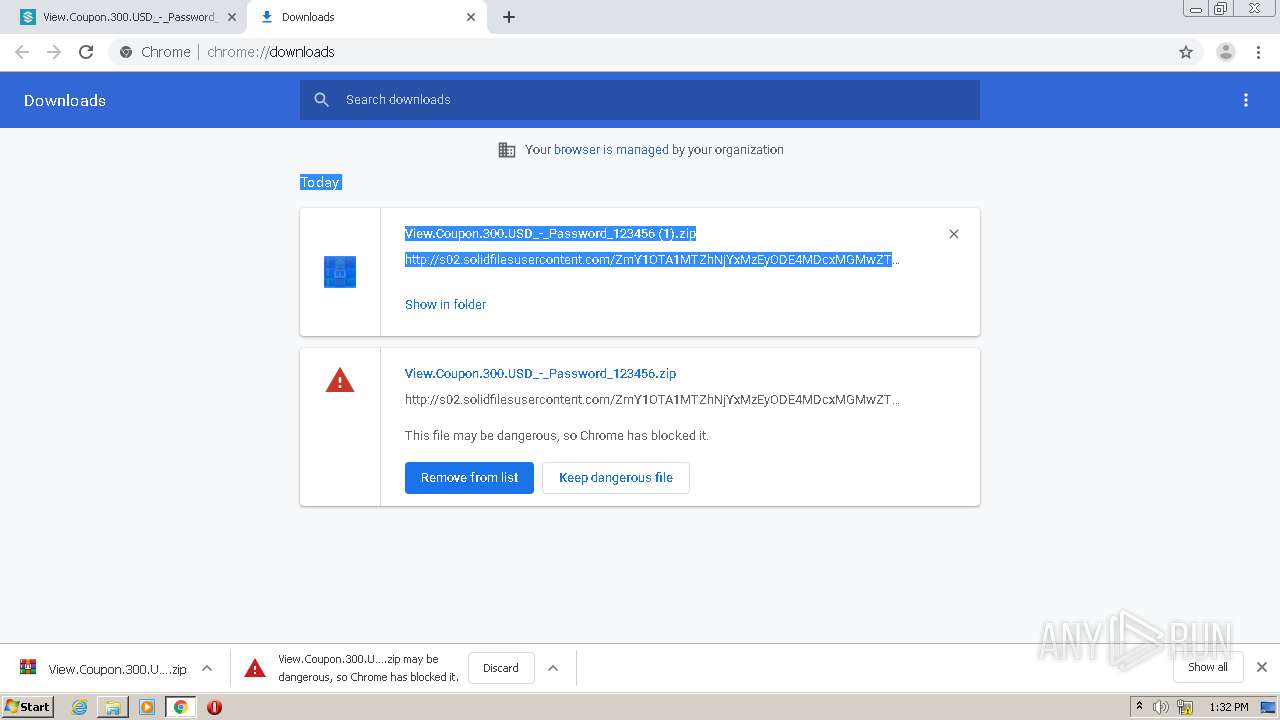
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2021, 13:31:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E3E661A9C4CFEB6D95E0029B1BFF86A4 |
| SHA1: | 99F1969494DBC93DA53FF15E475F73454D13F572 |
| SHA256: | 077258A4BEB54BFEA04F1131BFFAB64A6F1FA22E021E0D8B21FC8F25DE13D2A3 |
| SSDEEP: | 3:N1KJS4kIKfj/:Cc4k3r |
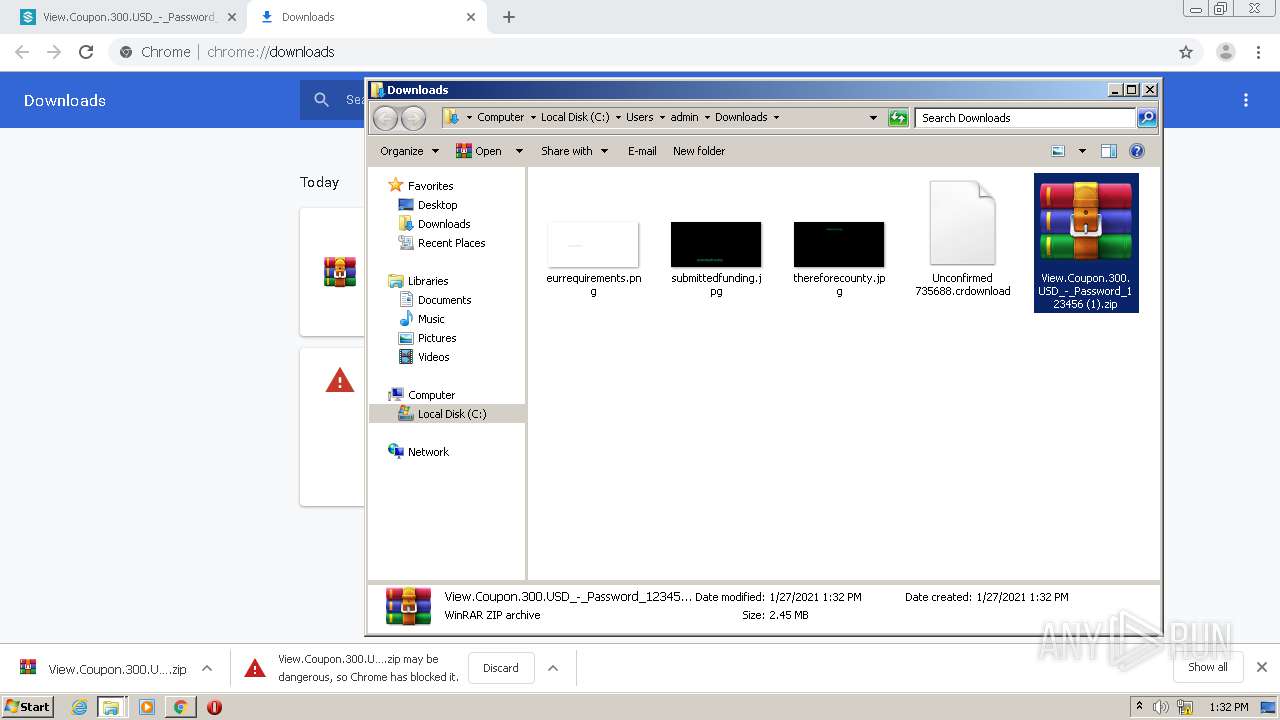
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 3140)
Application was dropped or rewritten from another process
- View Coupon $300.exe (PID: 3668)
- View Coupon $300.exe (PID: 2616)
SUSPICIOUS
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3140)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3140)
Drops a file with too old compile date
- WinRAR.exe (PID: 3140)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3140)
INFO
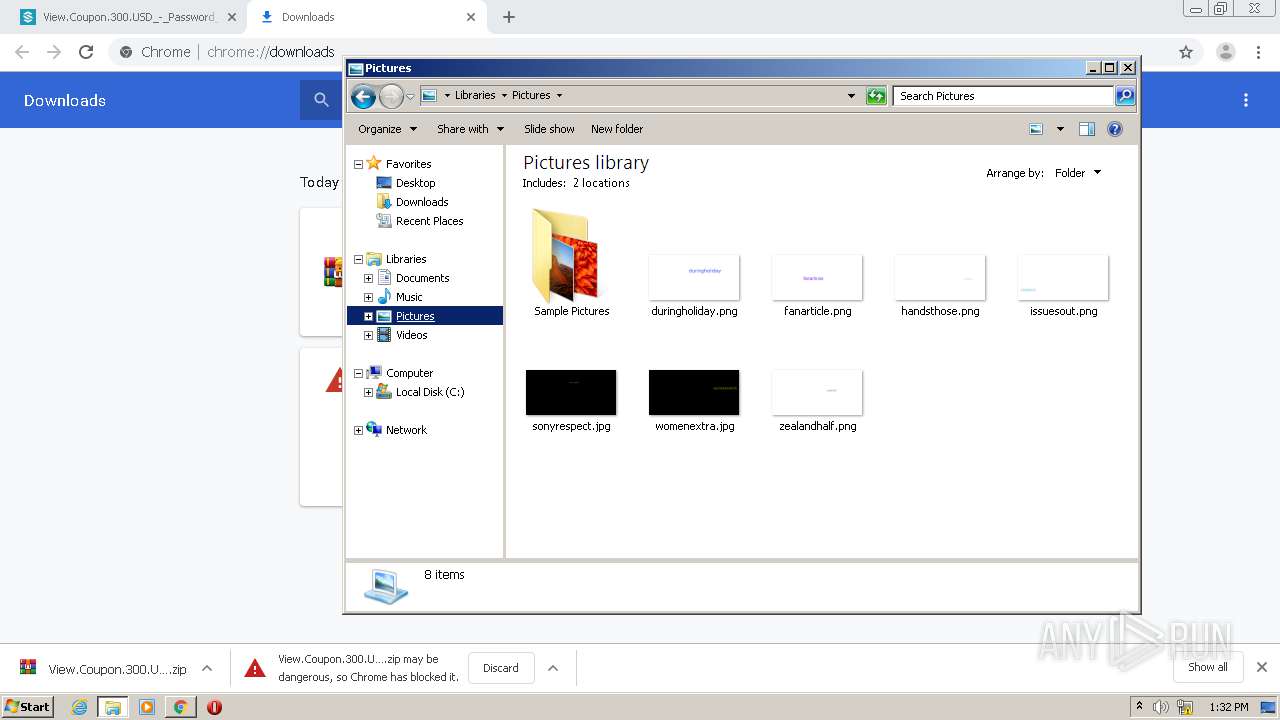
Manual execution by user
- WinRAR.exe (PID: 3140)
- View Coupon $300.exe (PID: 2616)
- View Coupon $300.exe (PID: 3668)
Reads the hosts file
- chrome.exe (PID: 3304)
- chrome.exe (PID: 3388)
Reads settings of System Certificates
- chrome.exe (PID: 3304)
Application launched itself
- chrome.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15147248292944537874 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6eaaa9d0,0x6eaaa9e0,0x6eaaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7588364326112311817 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
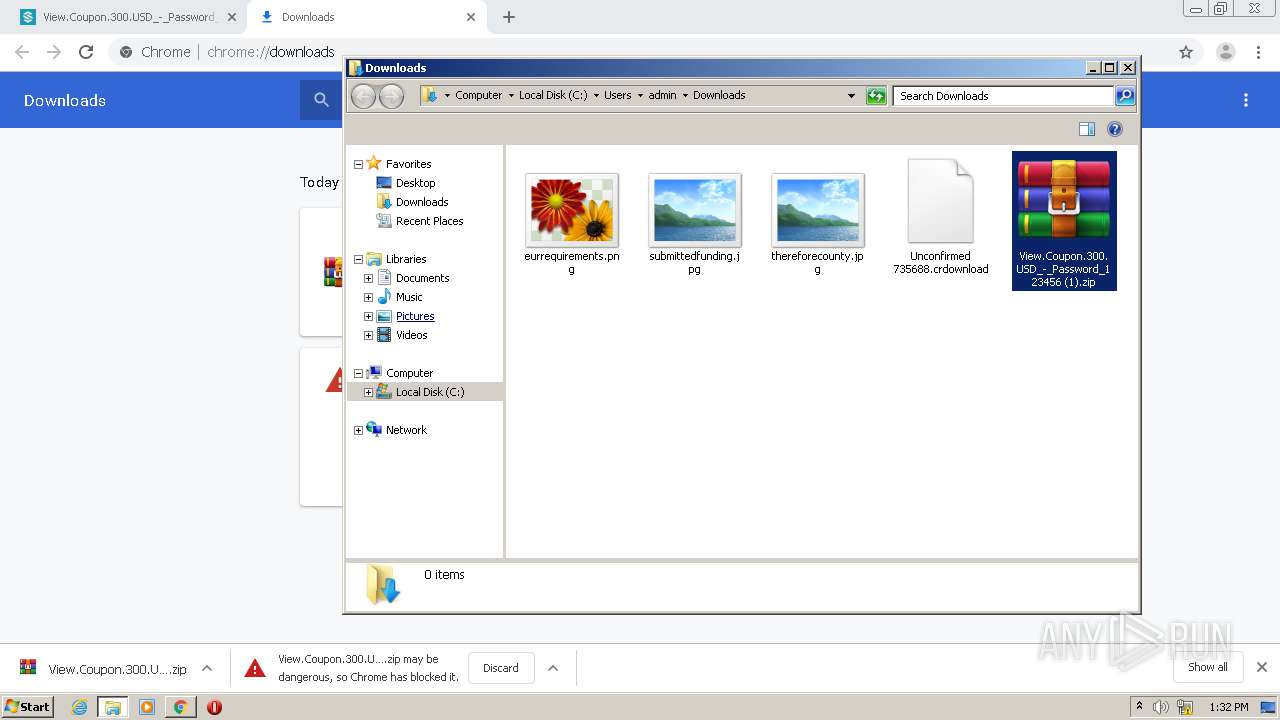
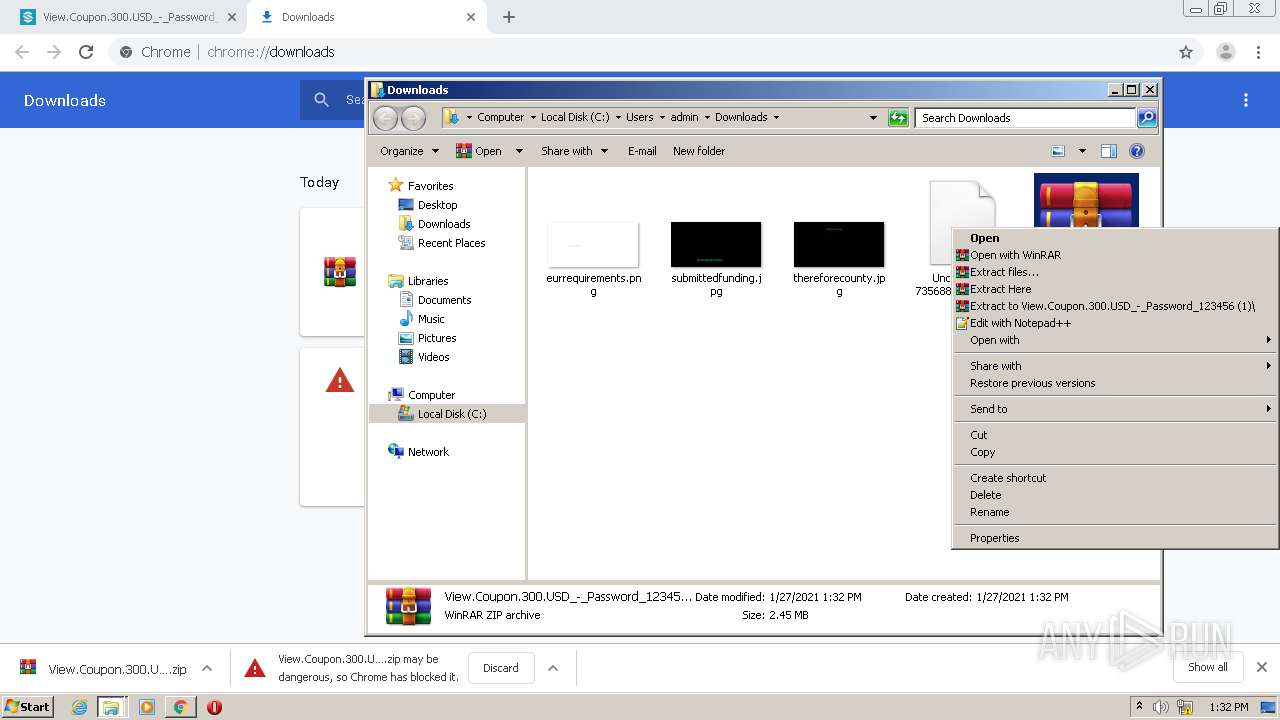
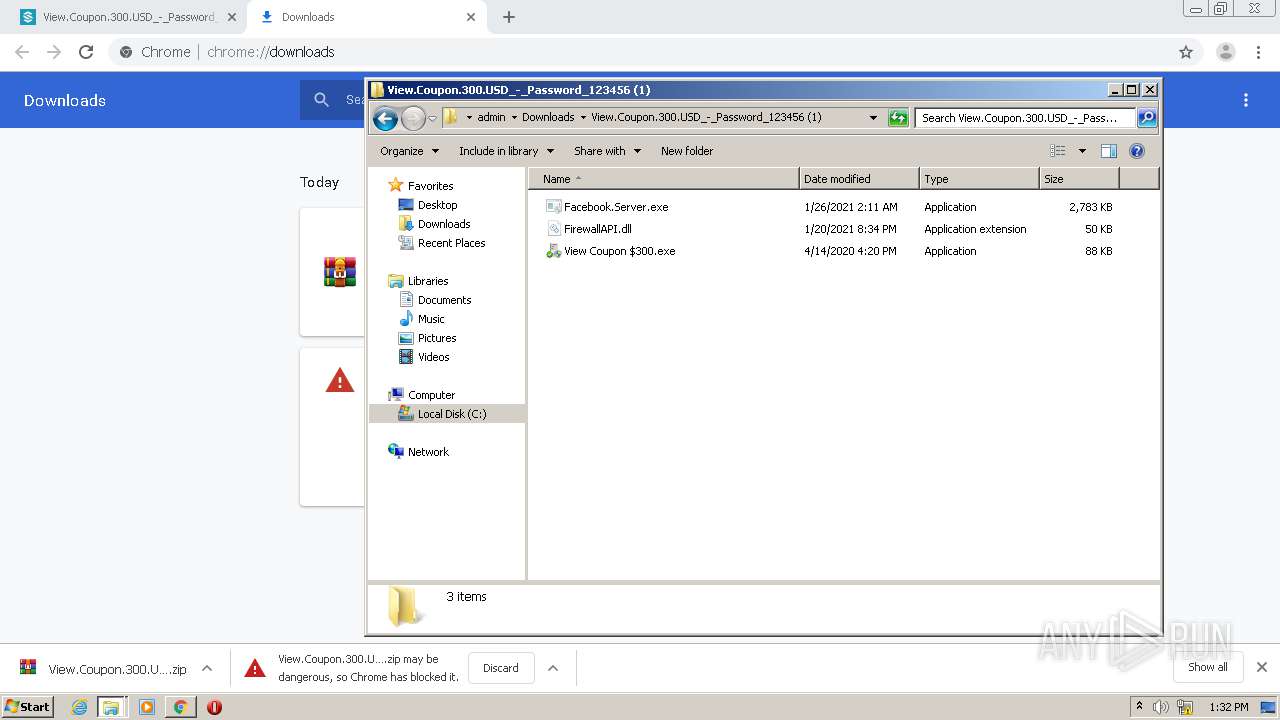
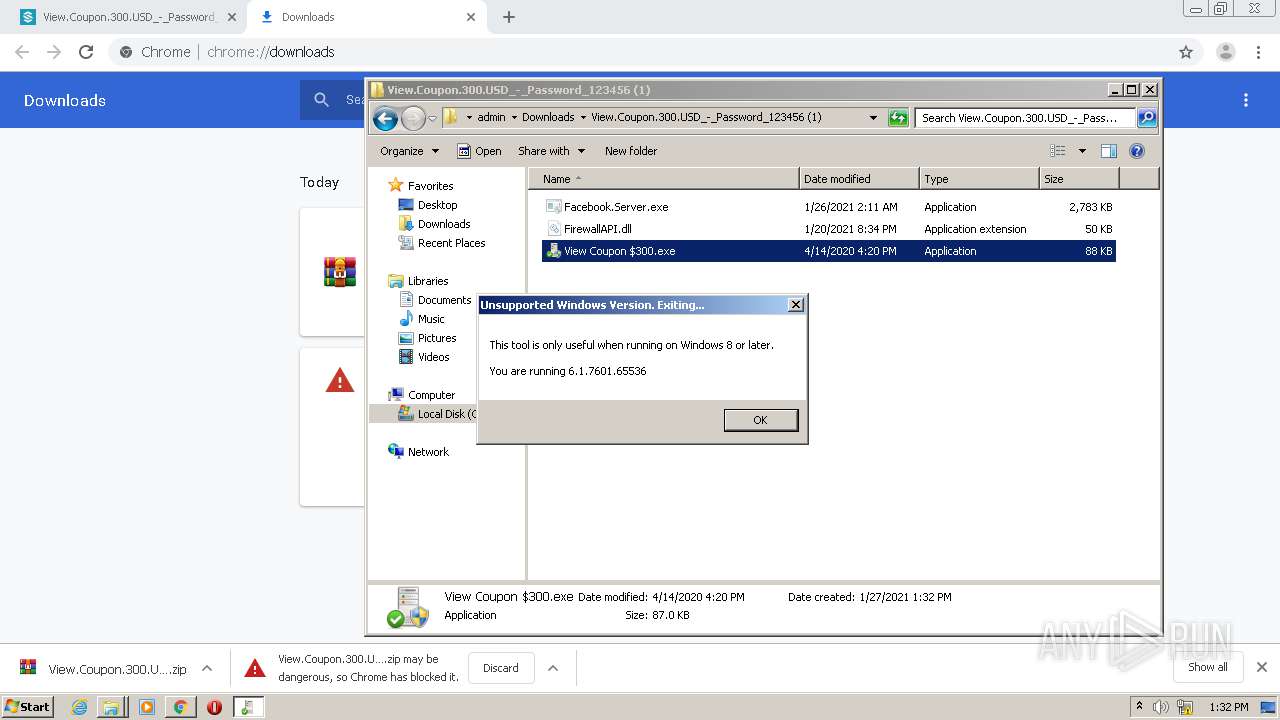
| 2616 | "C:\Users\admin\Downloads\View.Coupon.300.USD_-_Password_123456 (1)\View Coupon $300.exe" | C:\Users\admin\Downloads\View.Coupon.300.USD_-_Password_123456 (1)\View Coupon $300.exe | explorer.exe | ||||||||||||
User: admin Company: Progress Software Corporation Integrity Level: HIGH Description: EnableLoopback Exit code: 4294967295 Version: 1.4.3.0 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6432624982541374813 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11346634235435317285 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12419428562055836861 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8997271650901384442 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
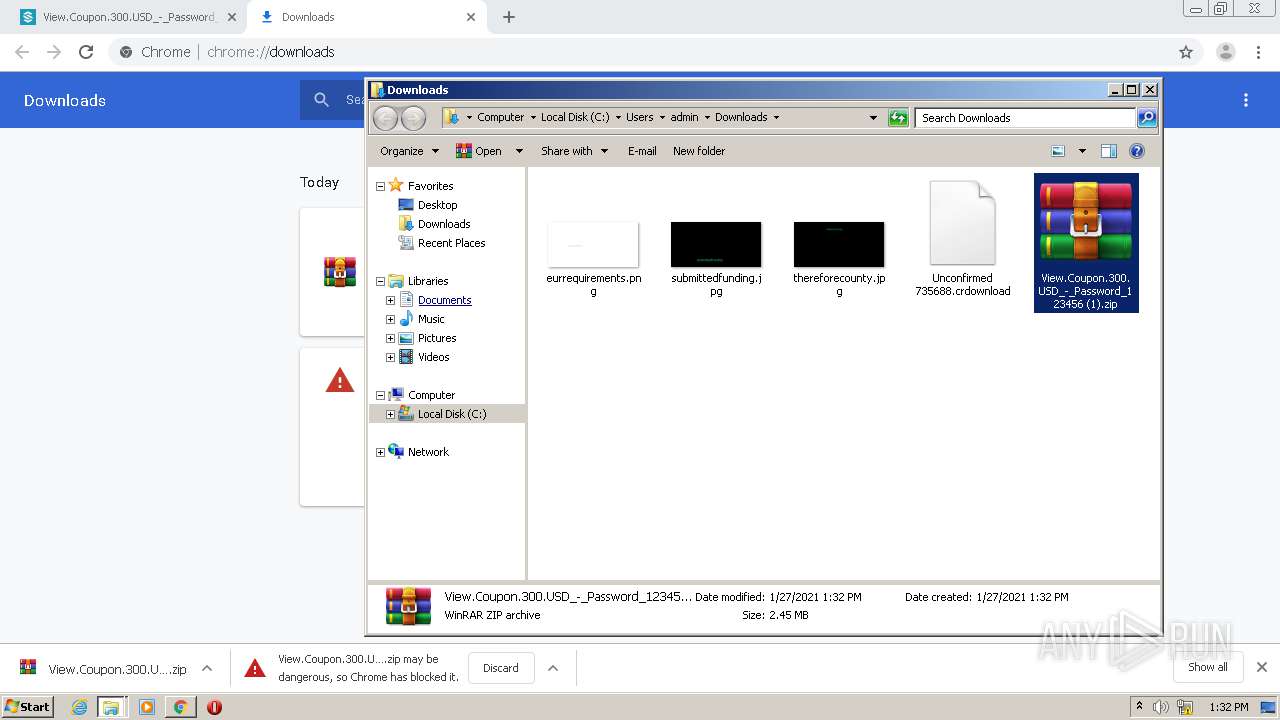
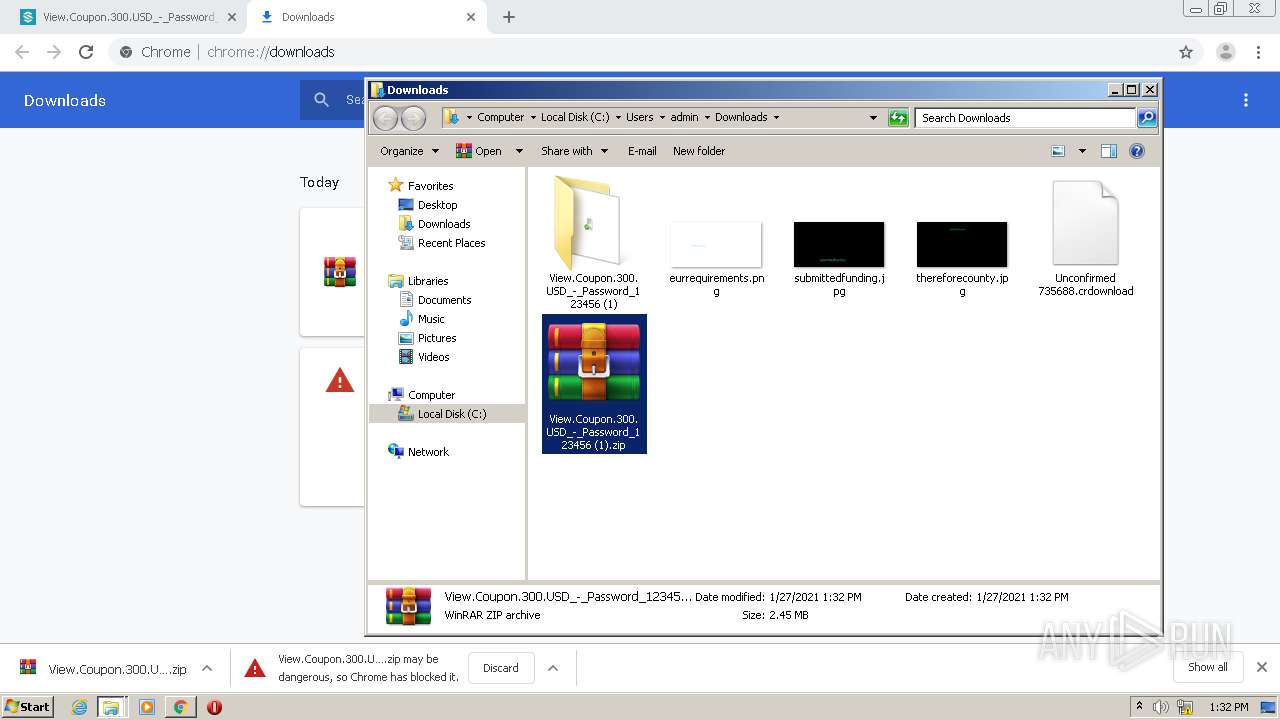
| 3140 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\View.Coupon.300.USD_-_Password_123456 (1).zip" "C:\Users\admin\Downloads\View.Coupon.300.USD_-_Password_123456 (1)\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8841971114048847778,13162638244140014819,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9721069940608594578 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 017
Read events
944
Write events
70
Delete events
3
Modification events
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3388-13256227893209000 |
Value: 259 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
34
Text files
75
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60116B36-D3C.pma | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3b751909-5104-48a9-8076-378b58e48864.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe2de.TMP | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe30d.TMP | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe4f1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
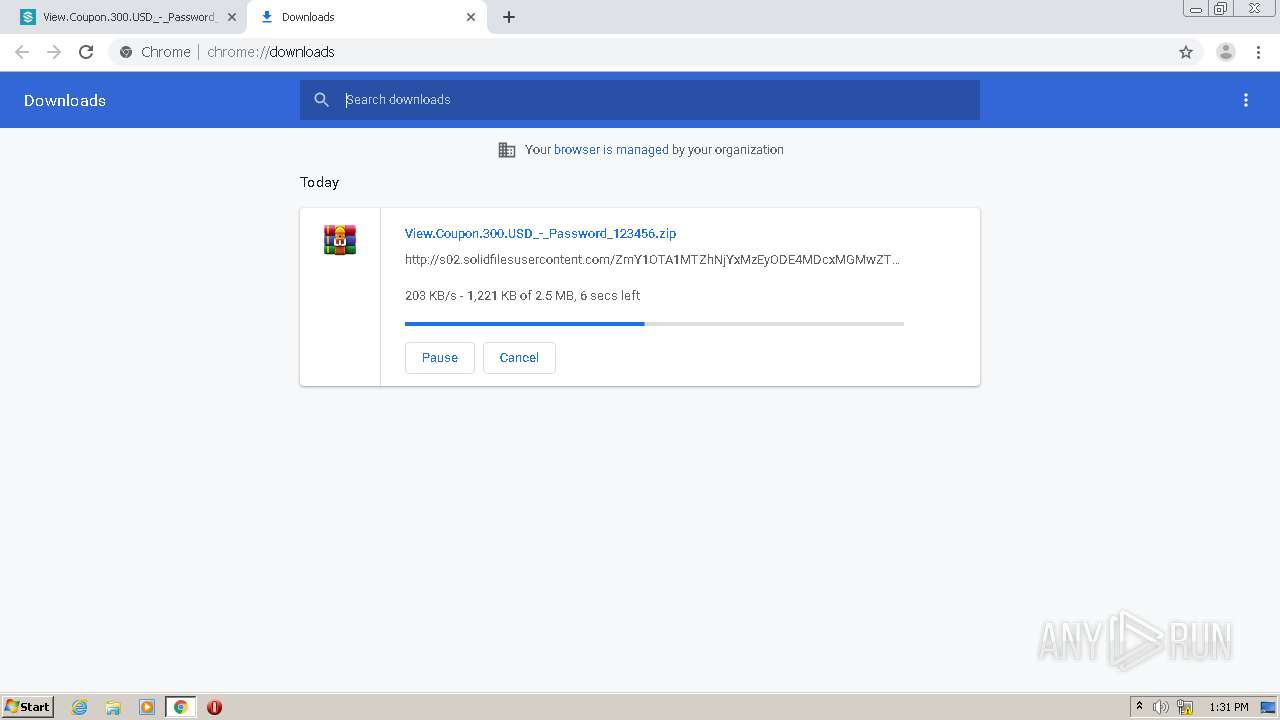
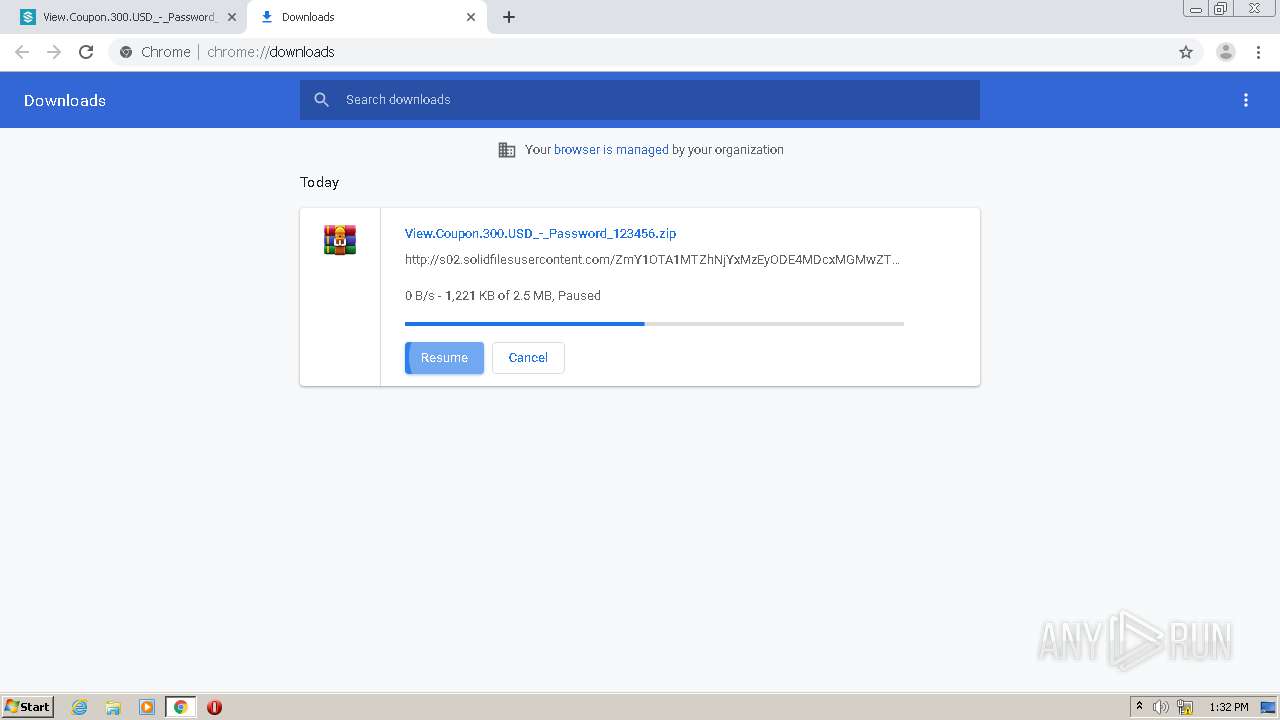
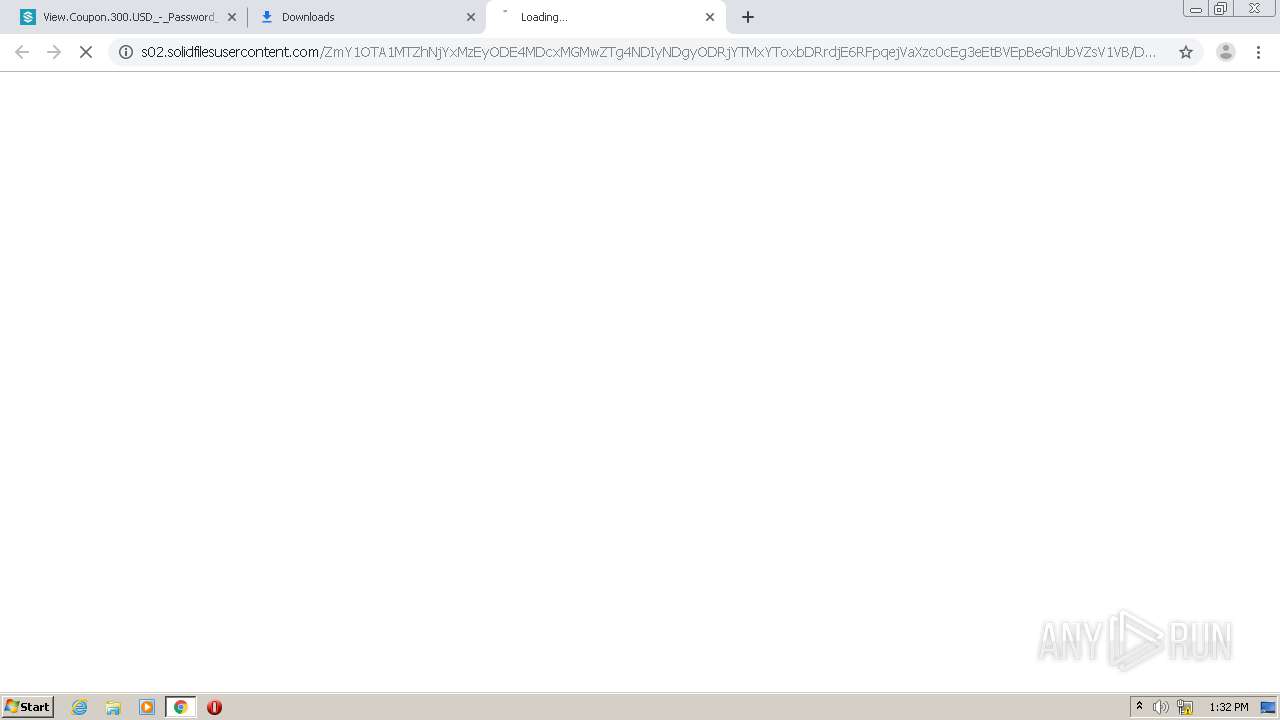
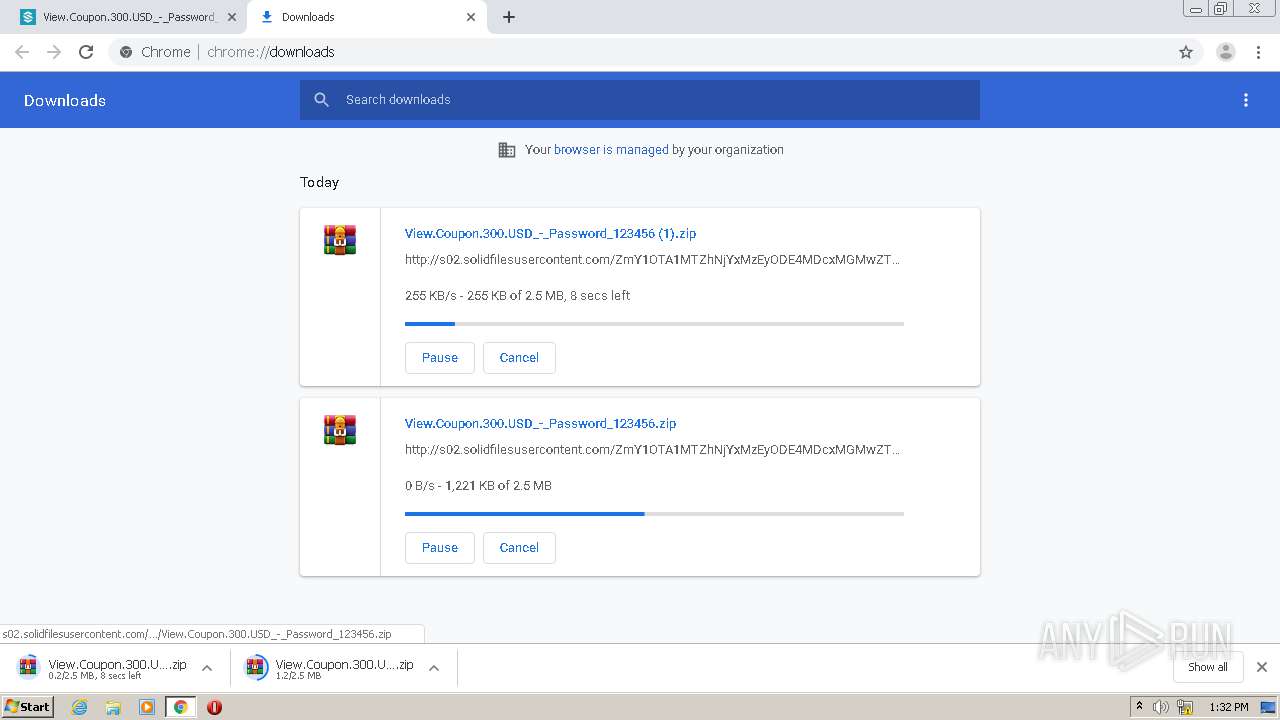
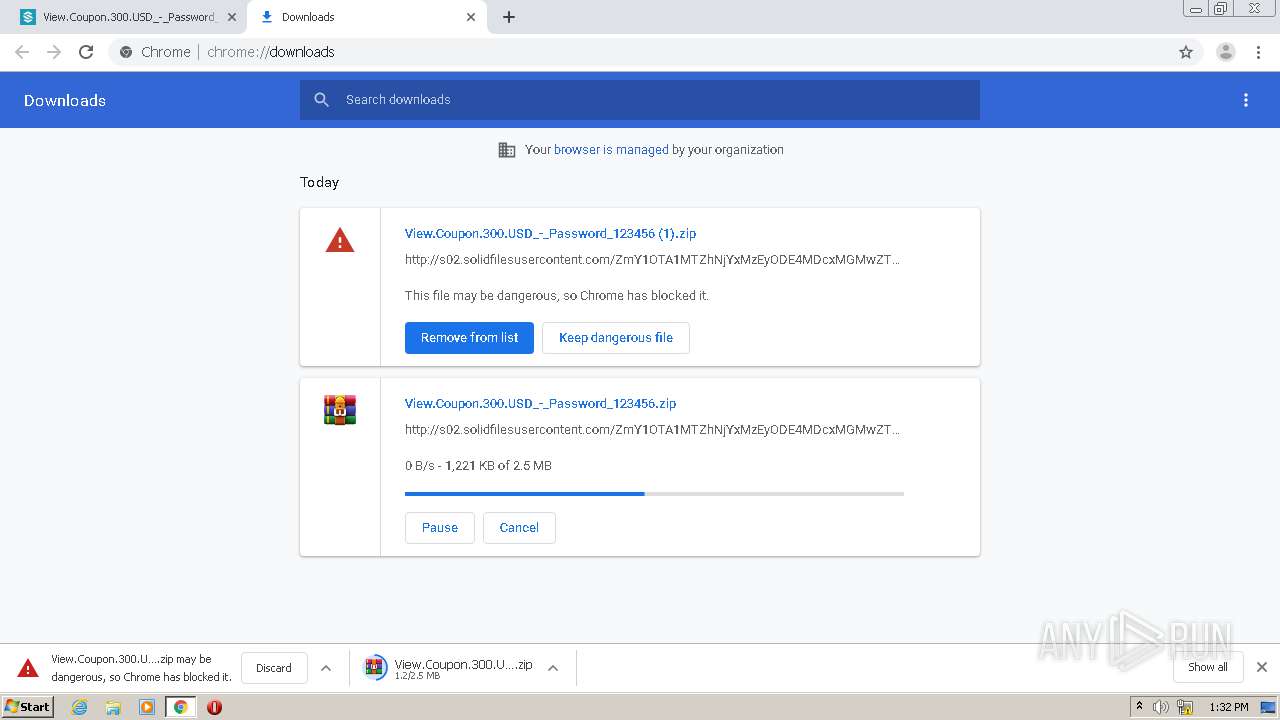
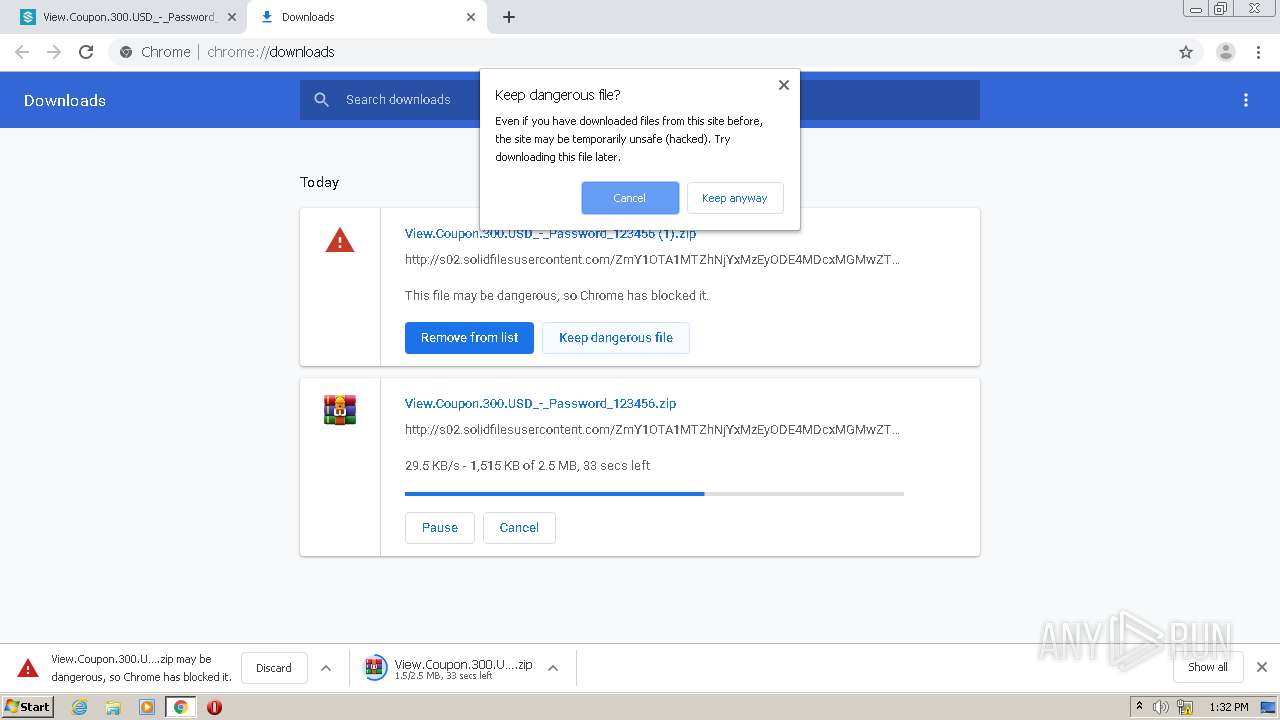
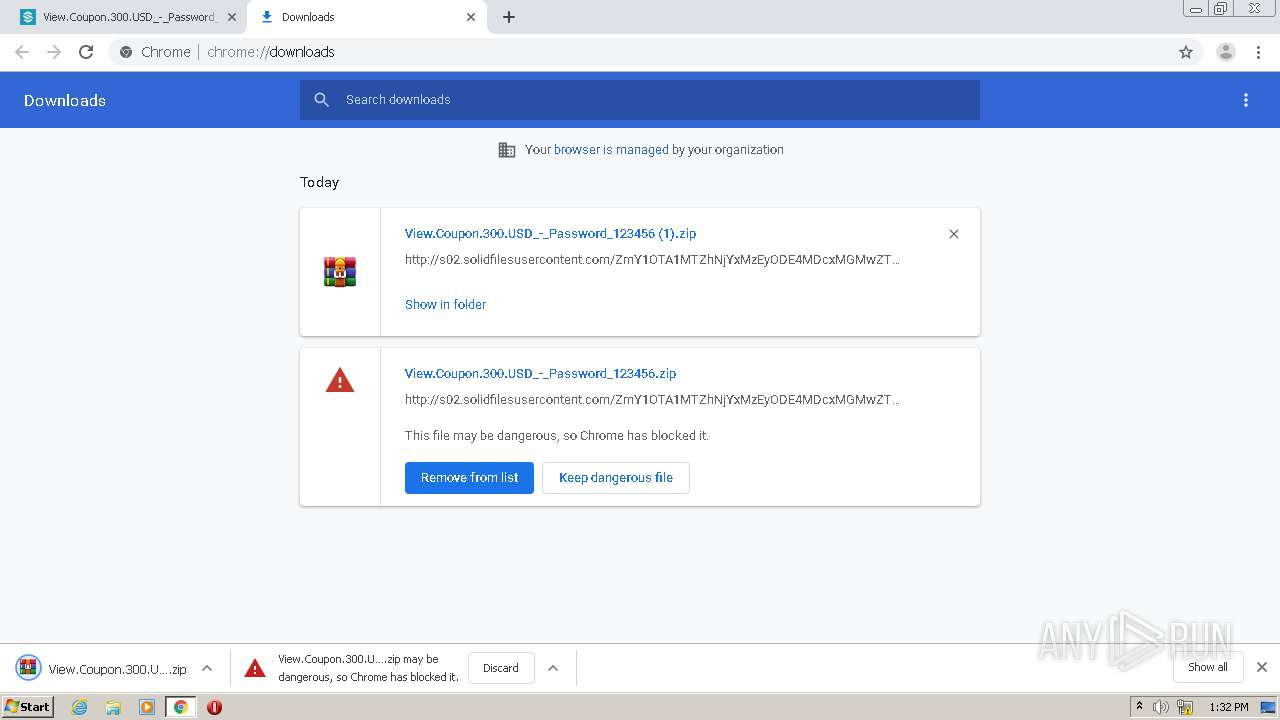
3304 | chrome.exe | GET | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/DGXYwwWdmrjZZ | RO | html | 15.0 Kb | suspicious |
3304 | chrome.exe | POST | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/DGXYwwWdmrjZZ/dl | RO | html | 14.0 Kb | suspicious |
3304 | chrome.exe | GET | 200 | 93.115.87.59:80 | http://s02.solidfilesusercontent.com/ZmY1OTA1MTZhNjYxMzEyODE4MDcxMGMwZTg4NDIyNDgyODRjYTMxYToxbDRrdjE6RFpqejVaXzc0cEg3eEtBVEpBeGhUbVZsV1VB/DGXYwwWdmrjZZ/View.Coupon.300.USD_-_Password_123456.zip | RO | compressed | 2.45 Mb | suspicious |
3304 | chrome.exe | GET | 200 | 93.115.87.59:80 | http://s02.solidfilesusercontent.com/ZmY1OTA1MTZhNjYxMzEyODE4MDcxMGMwZTg4NDIyNDgyODRjYTMxYToxbDRrdjE6RFpqejVaXzc0cEg3eEtBVEpBeGhUbVZsV1VB/DGXYwwWdmrjZZ/View.Coupon.300.USD_-_Password_123456.zip | RO | compressed | 2.45 Mb | suspicious |
3304 | chrome.exe | POST | 200 | 37.221.163.214:80 | http://www.solidfiles.com/api/nodes/1872502242767268085/downloads | RO | text | 15 b | suspicious |
3304 | chrome.exe | GET | 200 | 192.229.233.25:80 | http://platform.twitter.com/widgets.js | US | text | 28.0 Kb | whitelisted |
3304 | chrome.exe | GET | 200 | 31.13.92.14:80 | http://connect.facebook.net/en_US/all.js | IE | text | 1.74 Kb | whitelisted |
3304 | chrome.exe | GET | 200 | 108.177.121.95:80 | http://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js | US | text | 28.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | chrome.exe | 37.221.163.214:80 | www.solidfiles.com | Voxility S.R.L. | RO | suspicious |
3304 | chrome.exe | 108.177.121.95:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3304 | chrome.exe | 74.125.126.139:443 | www.google-analytics.com | Google Inc. | US | unknown |
— | — | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3304 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3304 | chrome.exe | 74.125.133.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3304 | chrome.exe | 192.229.233.25:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3304 | chrome.exe | 104.244.42.136:443 | syndication.twitter.com | Twitter Inc. | US | unknown |
3304 | chrome.exe | 93.115.87.59:80 | s02.solidfilesusercontent.com | Voxility S.R.L. | RO | suspicious |
3304 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solidfiles.com |
| suspicious |
accounts.google.com |
| shared |
solidfilescdn.com |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
outdatedbrowser.com |
| suspicious |
twitter.com |
| whitelisted |
www.google.com |
| malicious |
plus.google.com |
| whitelisted |