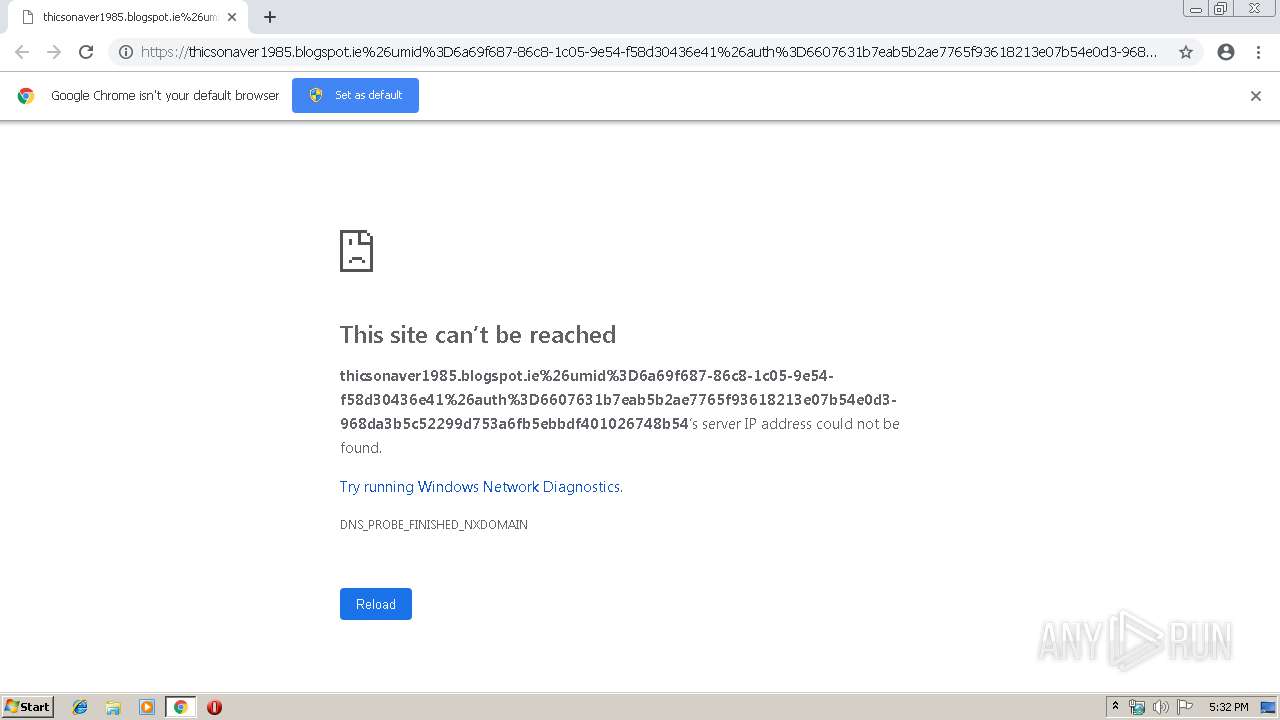
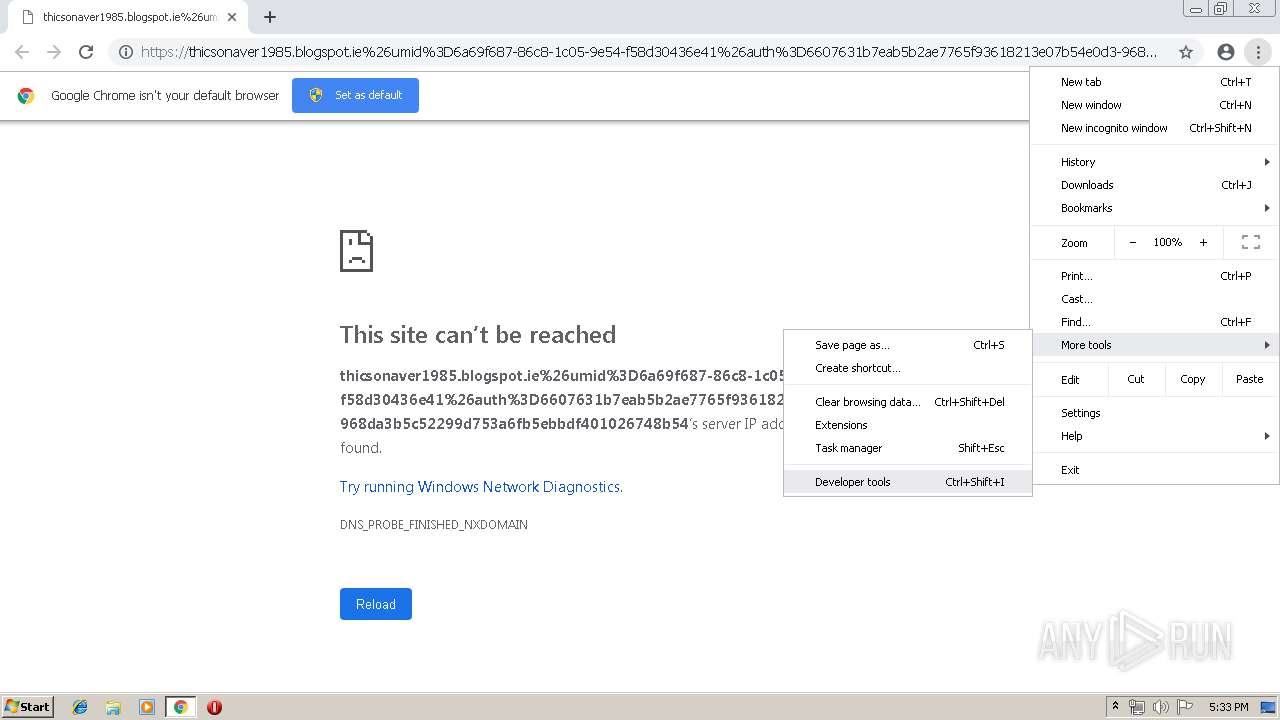
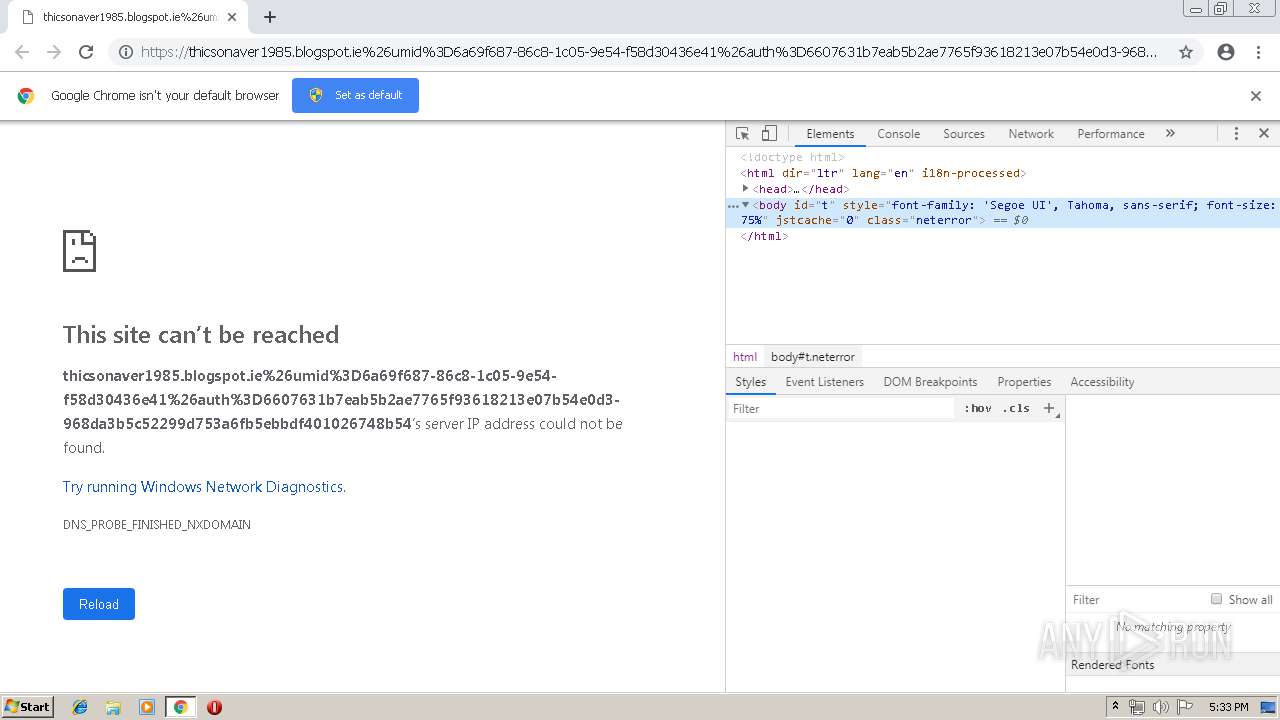
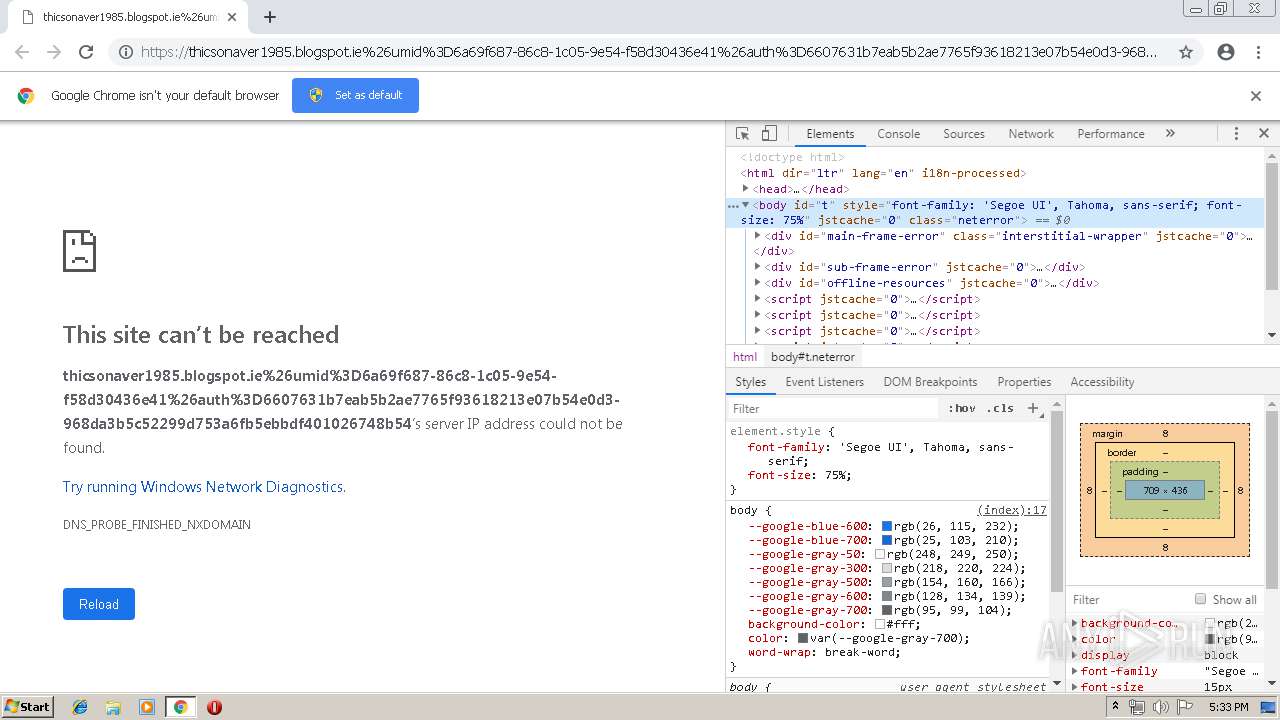
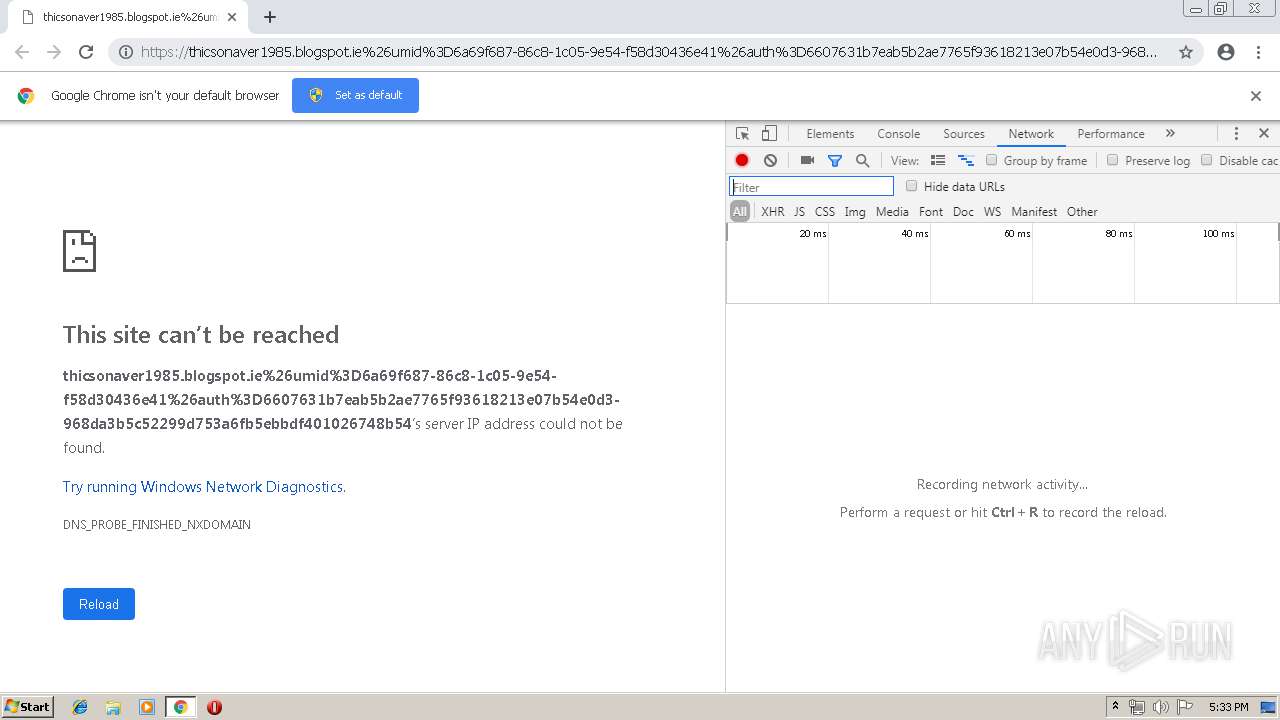
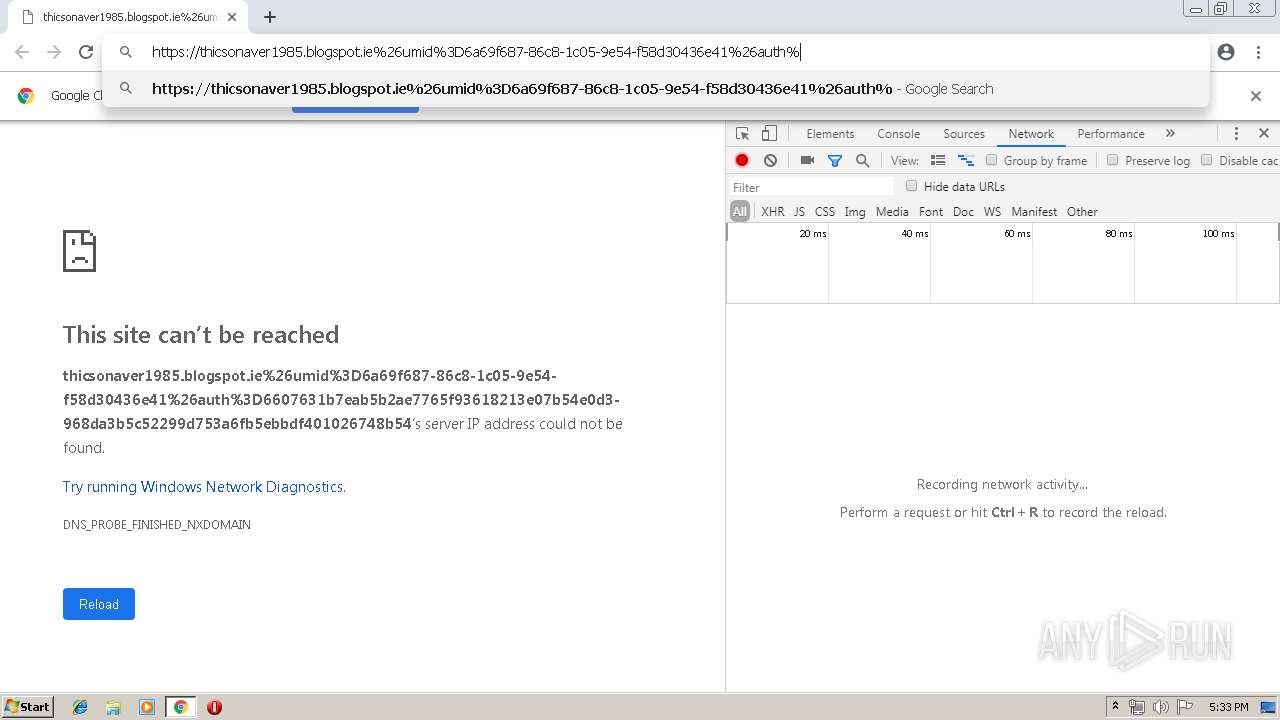
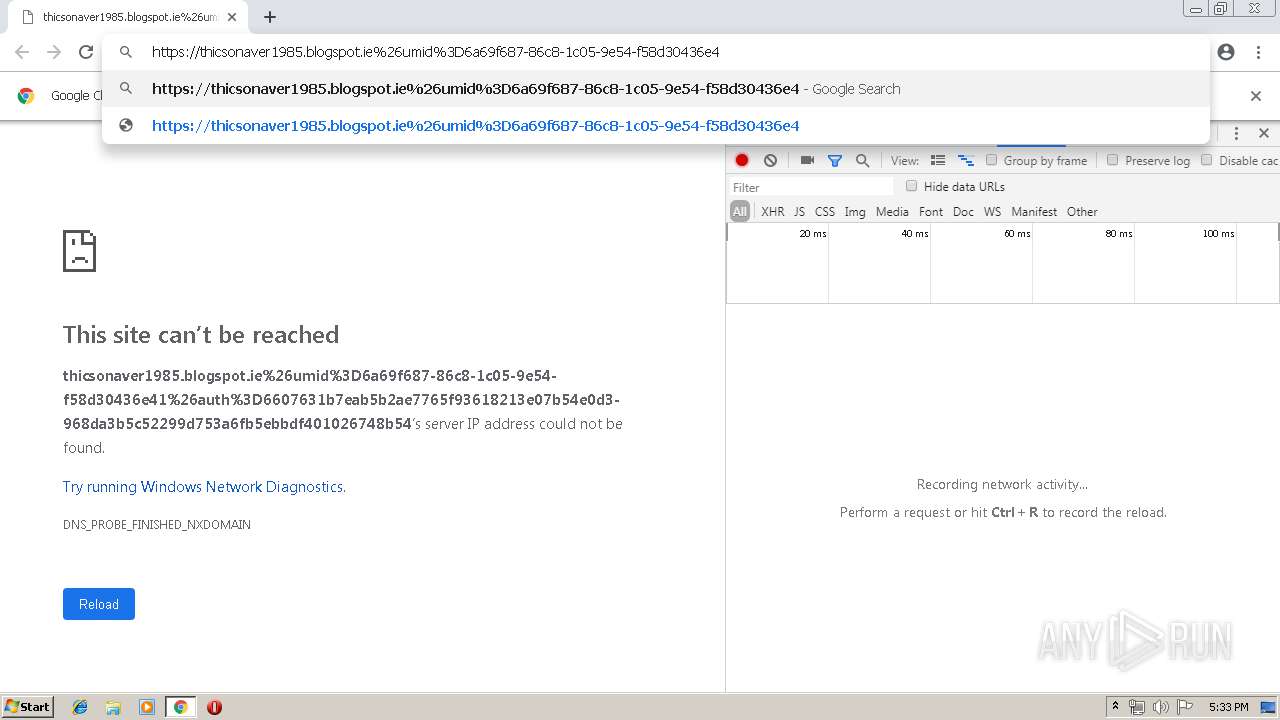
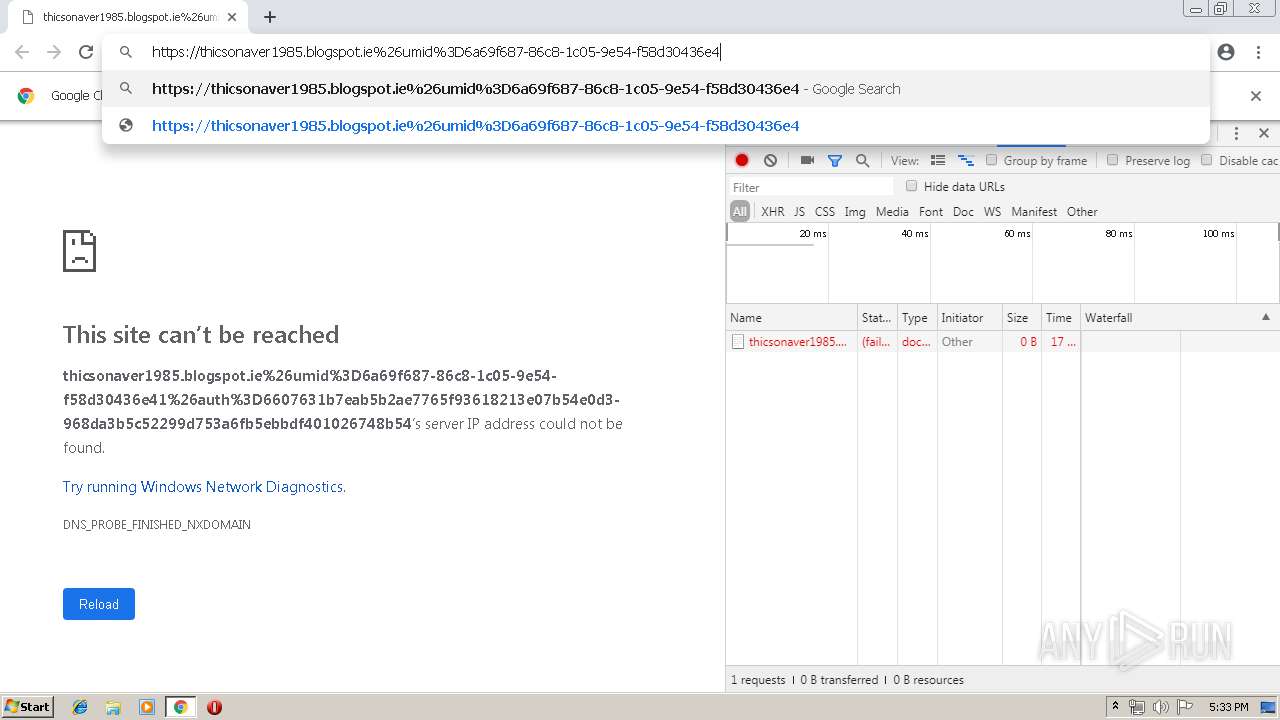
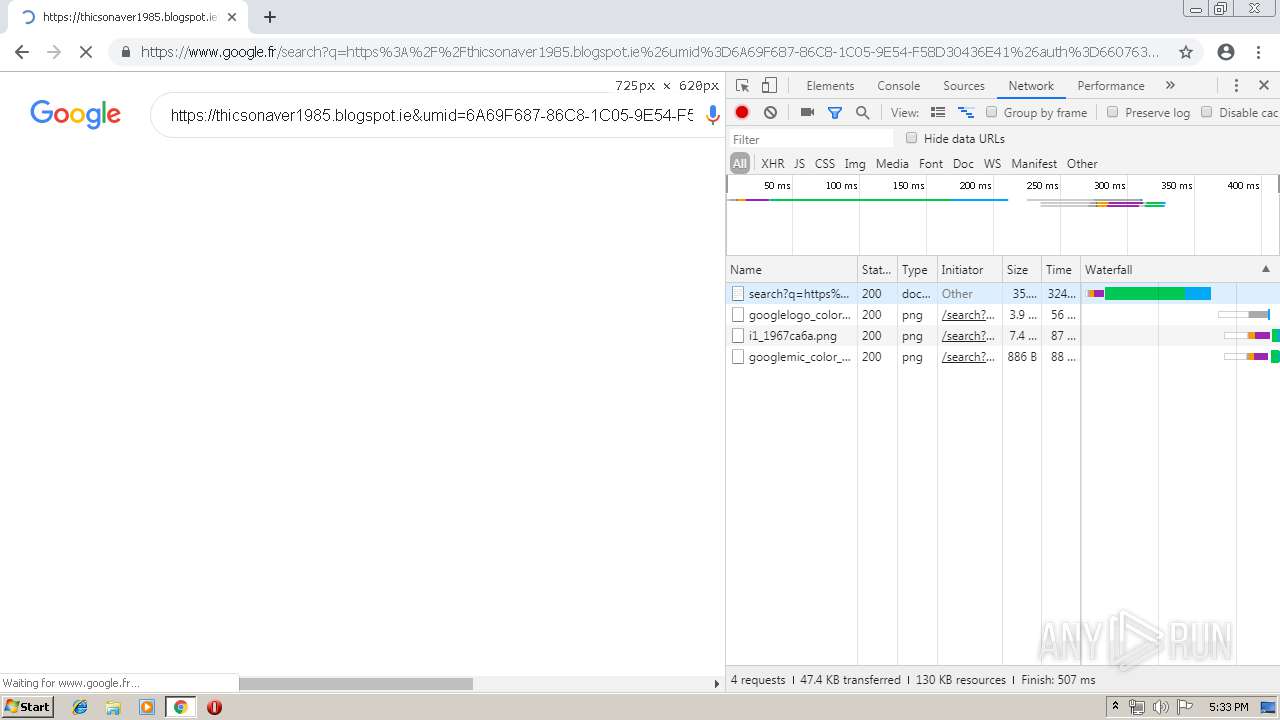
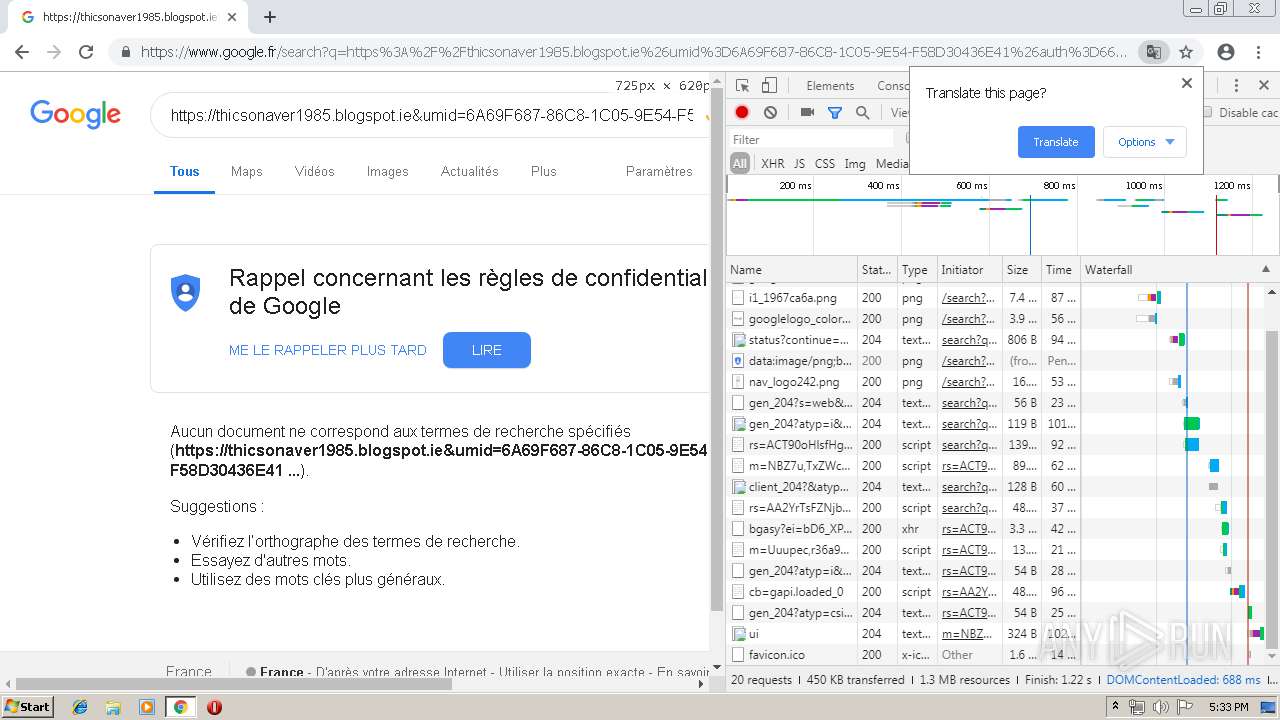
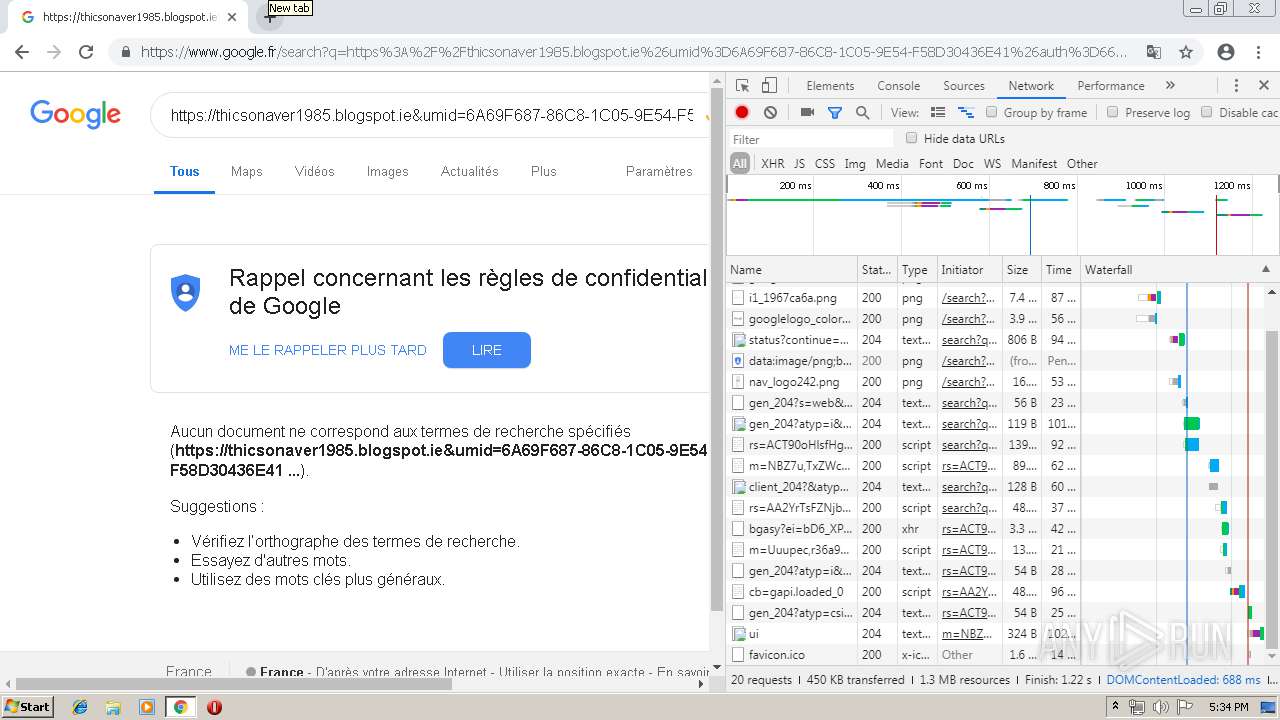
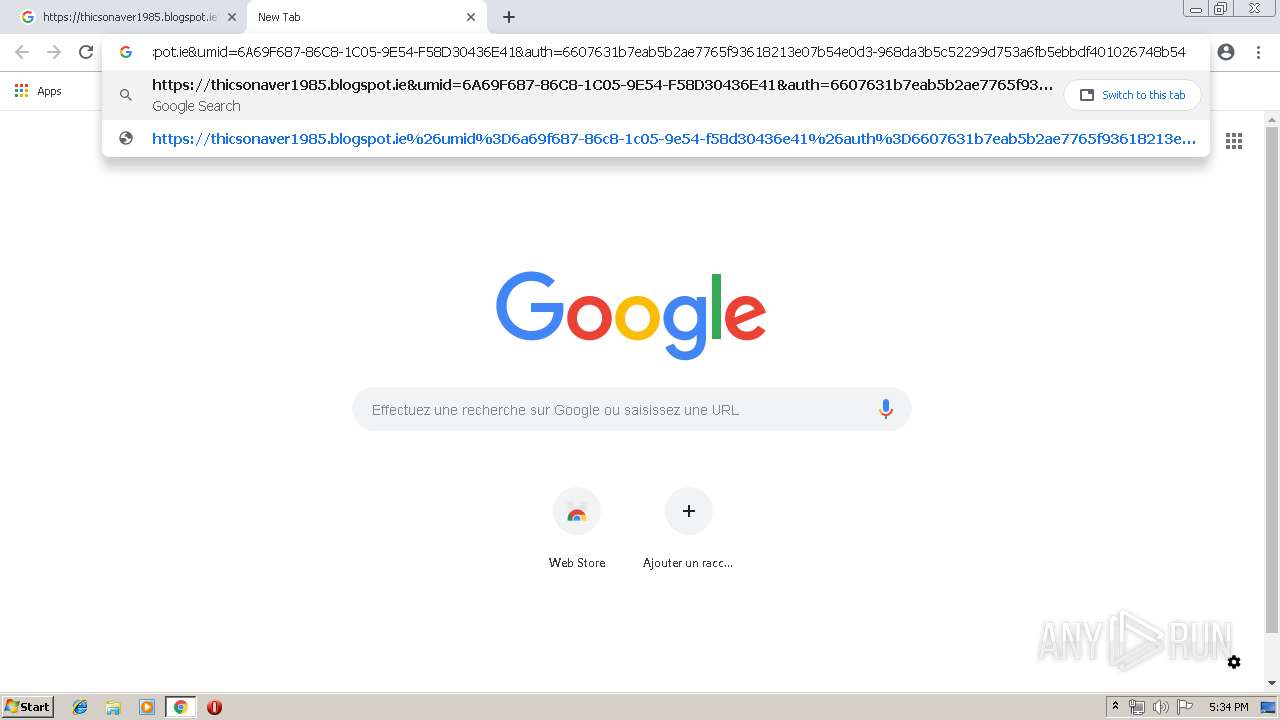
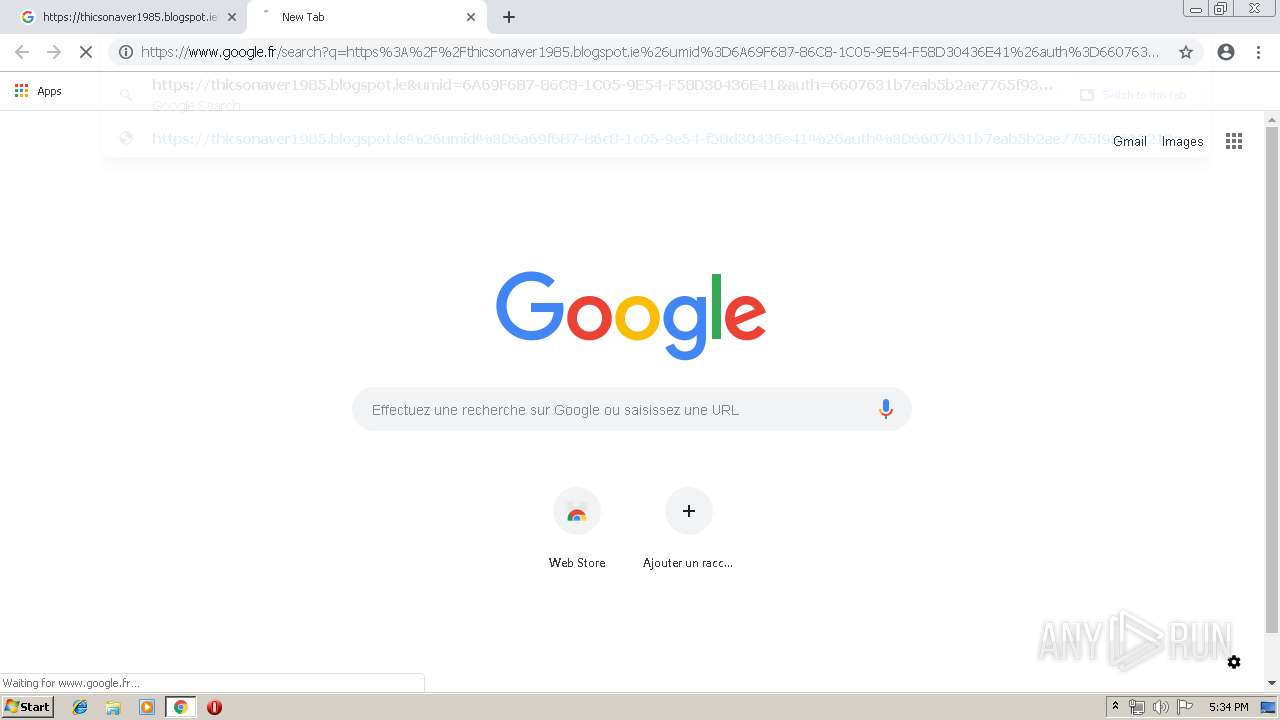
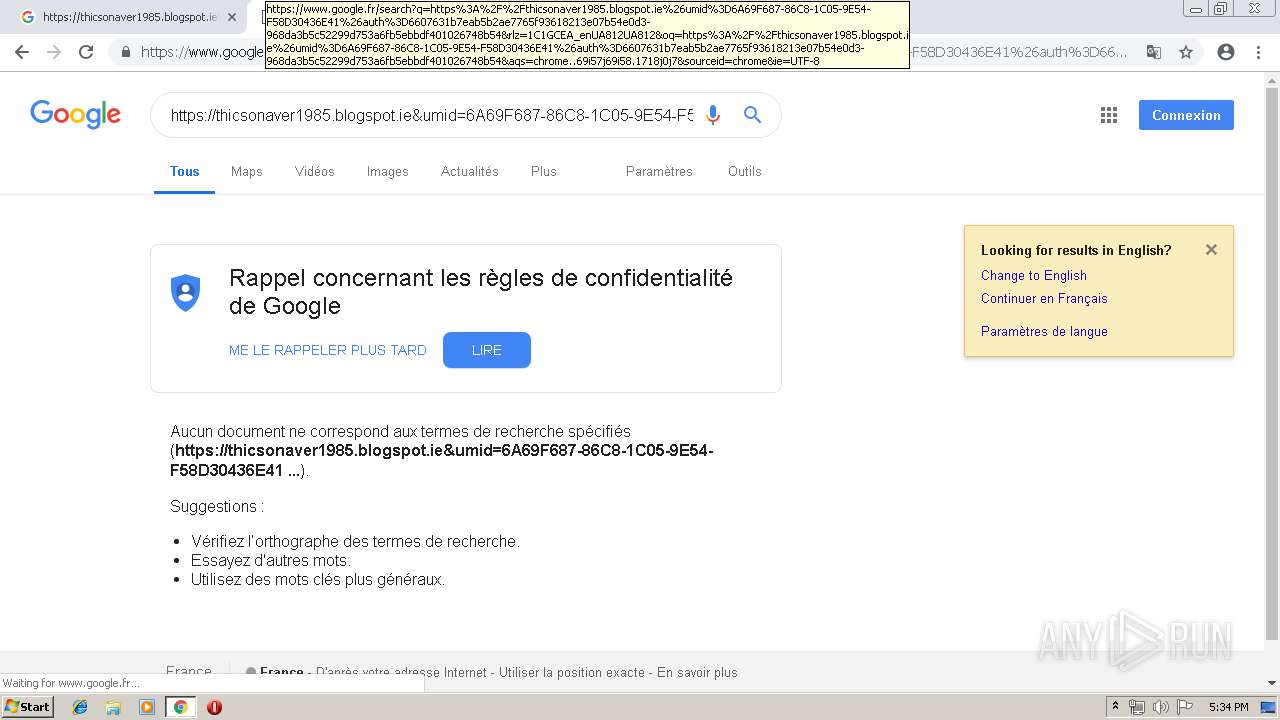
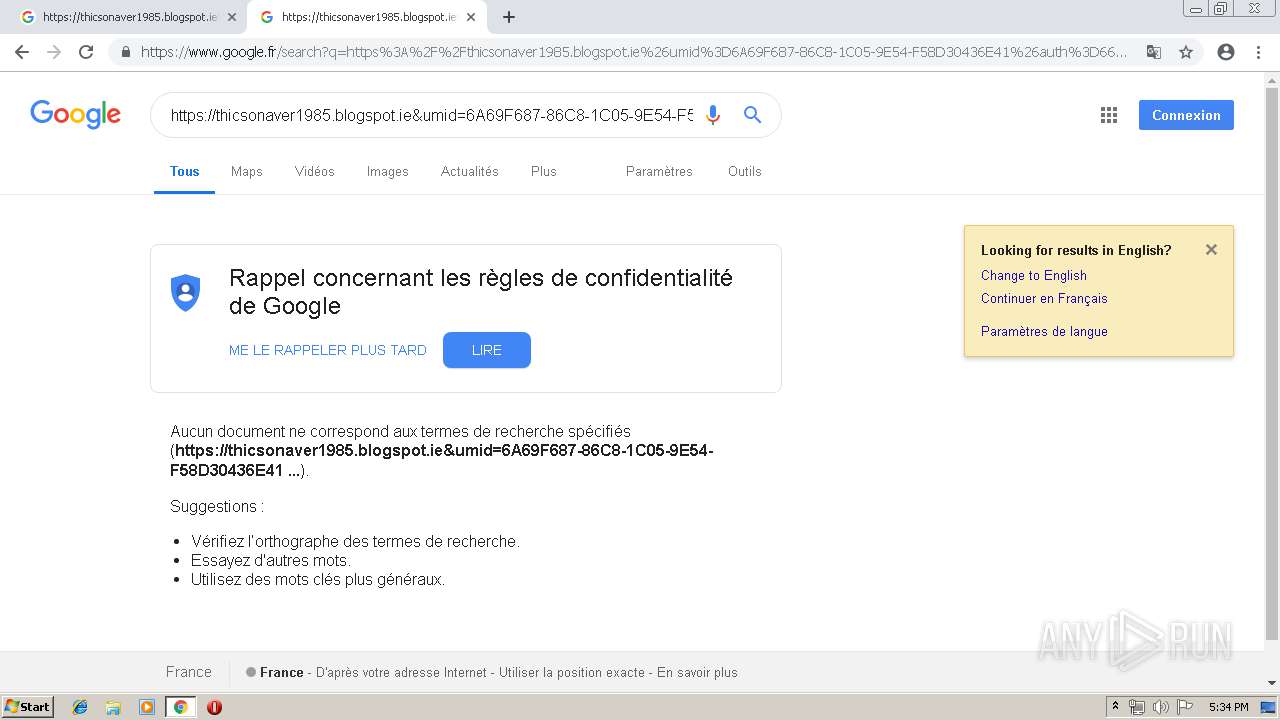
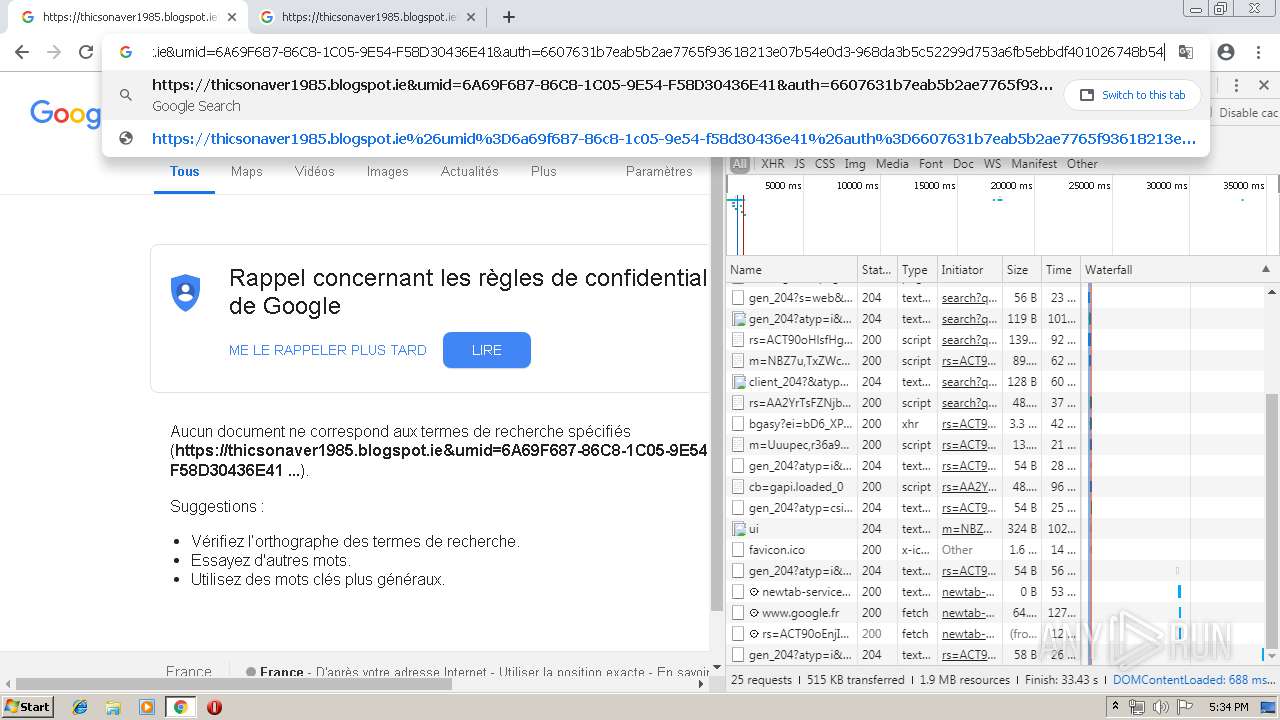
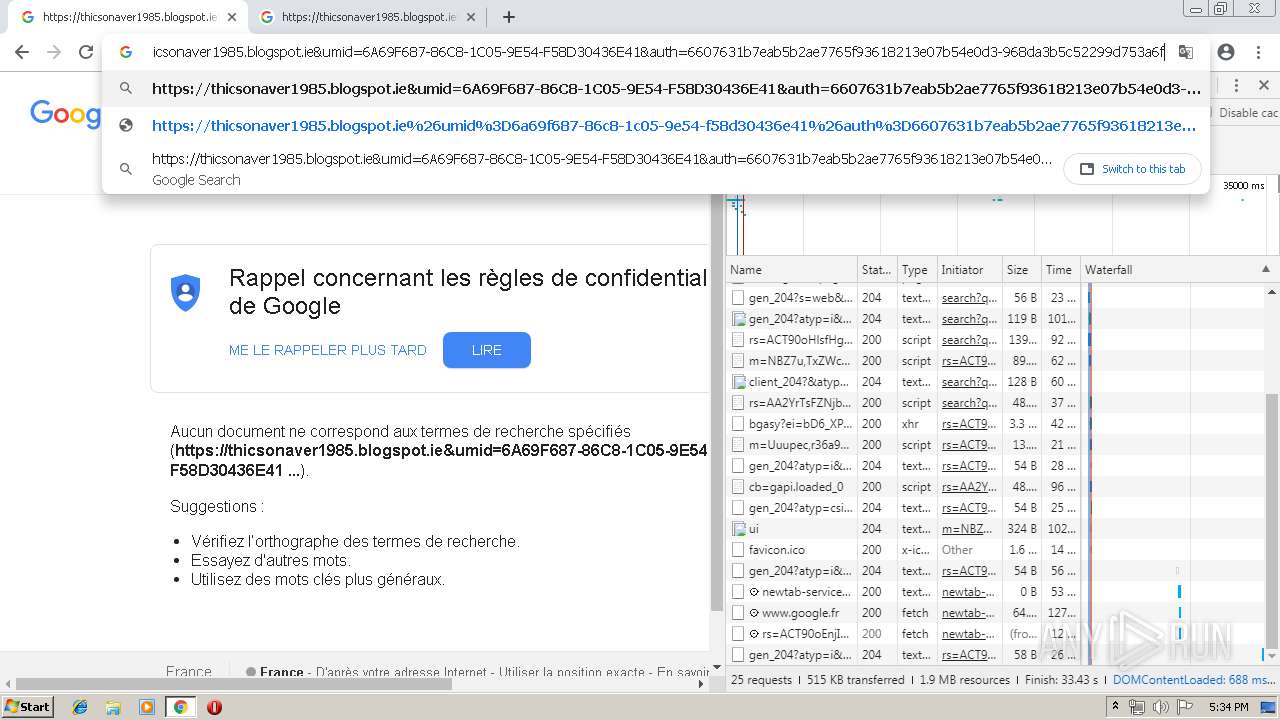
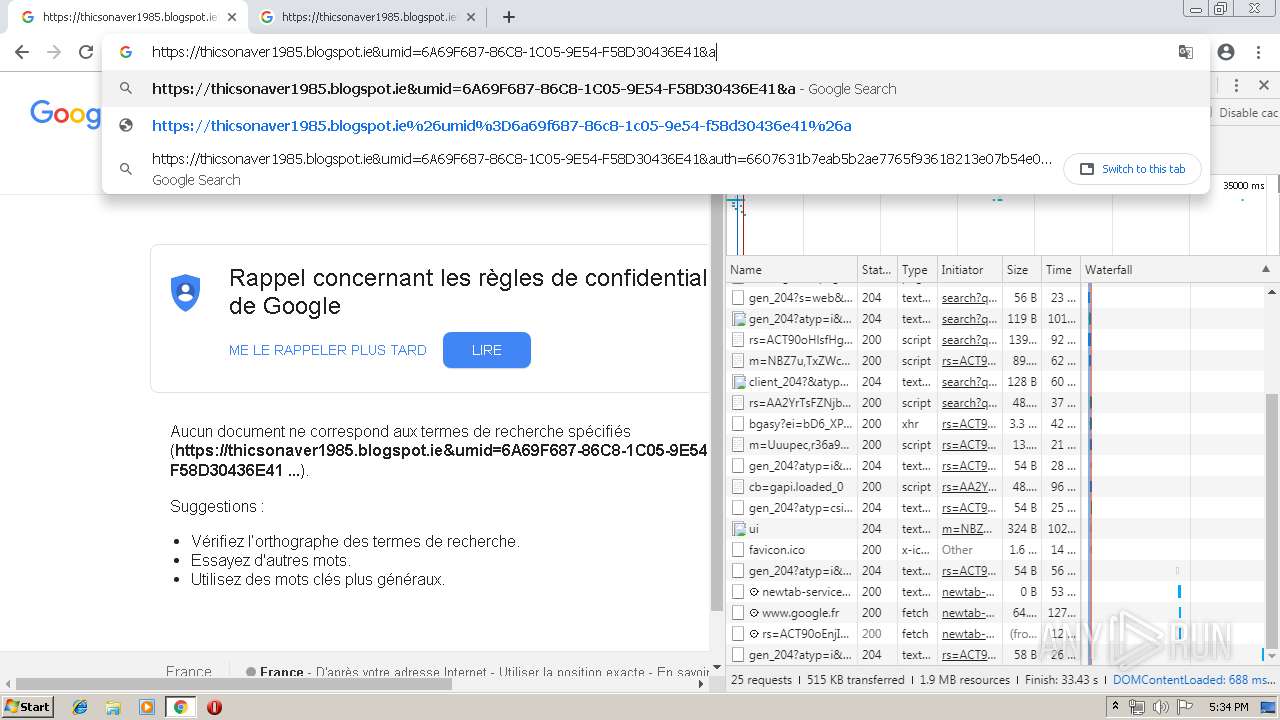
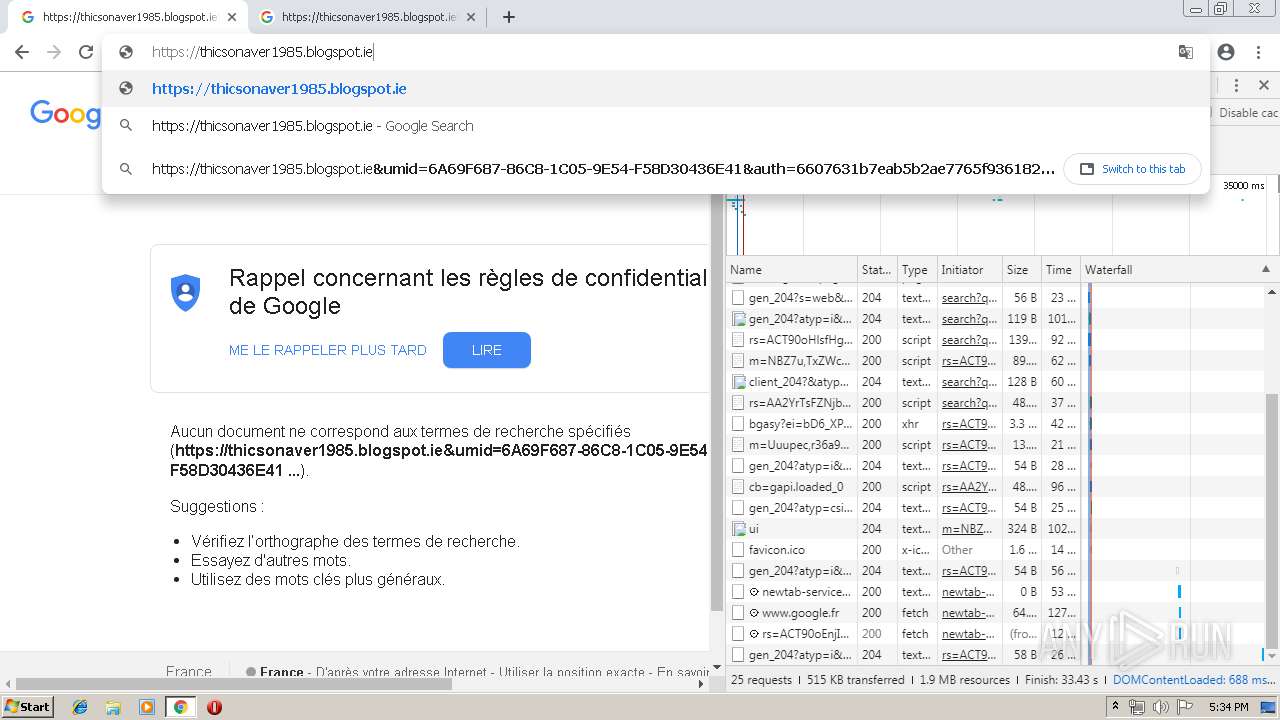
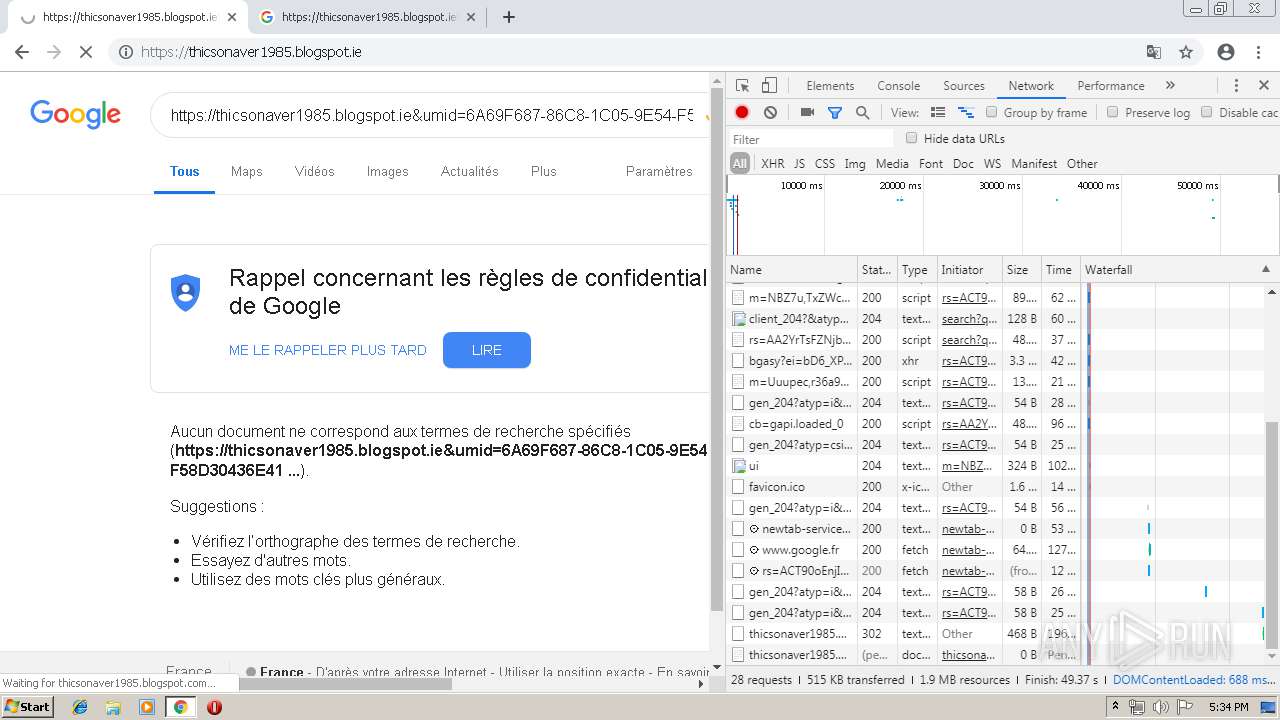
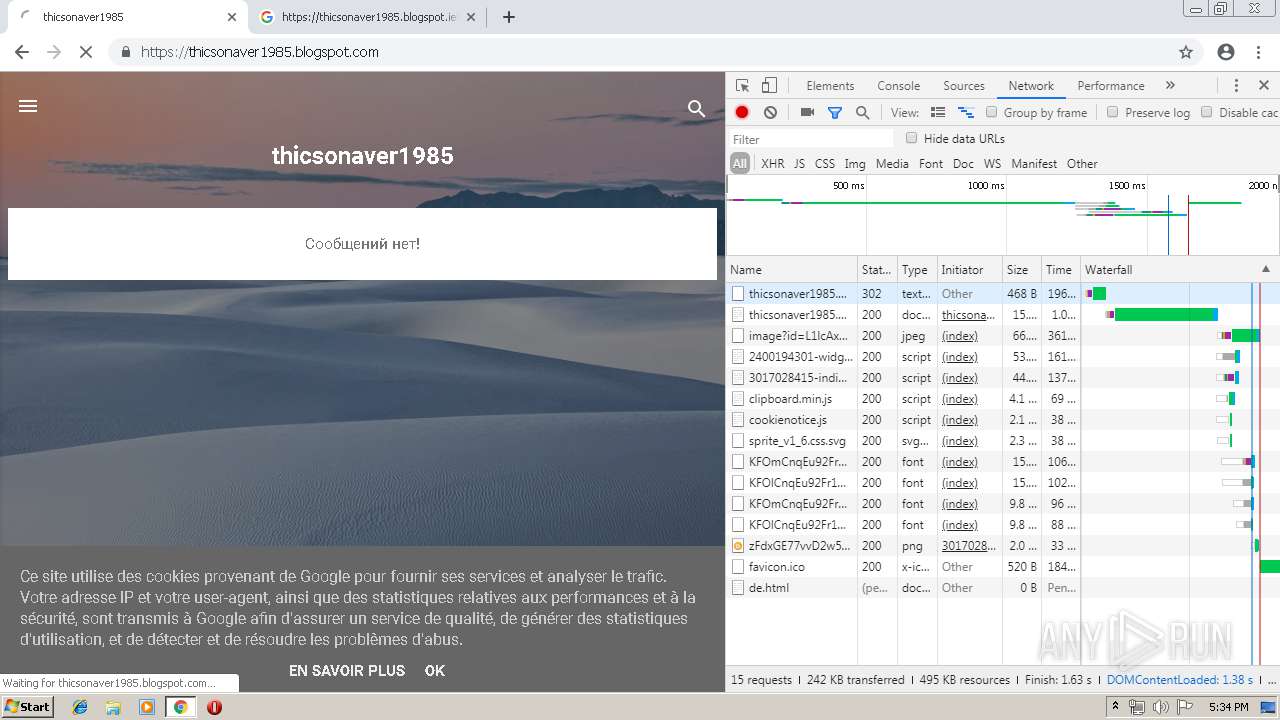
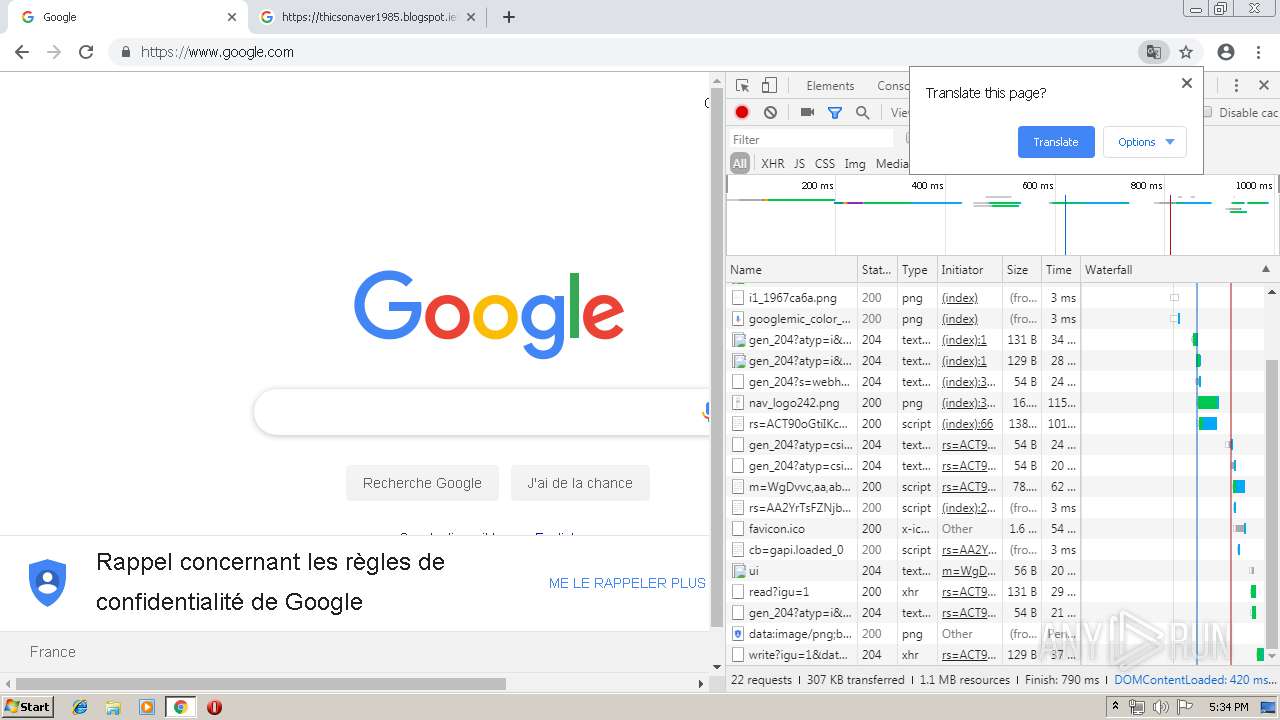
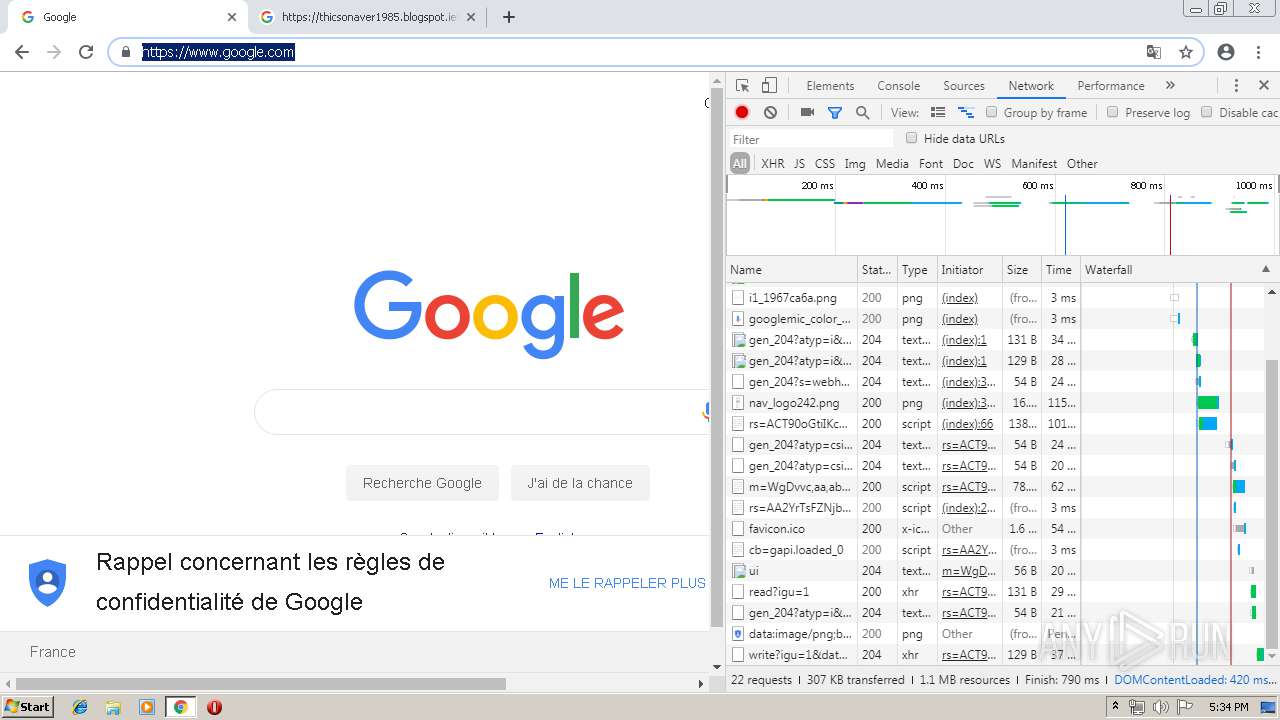
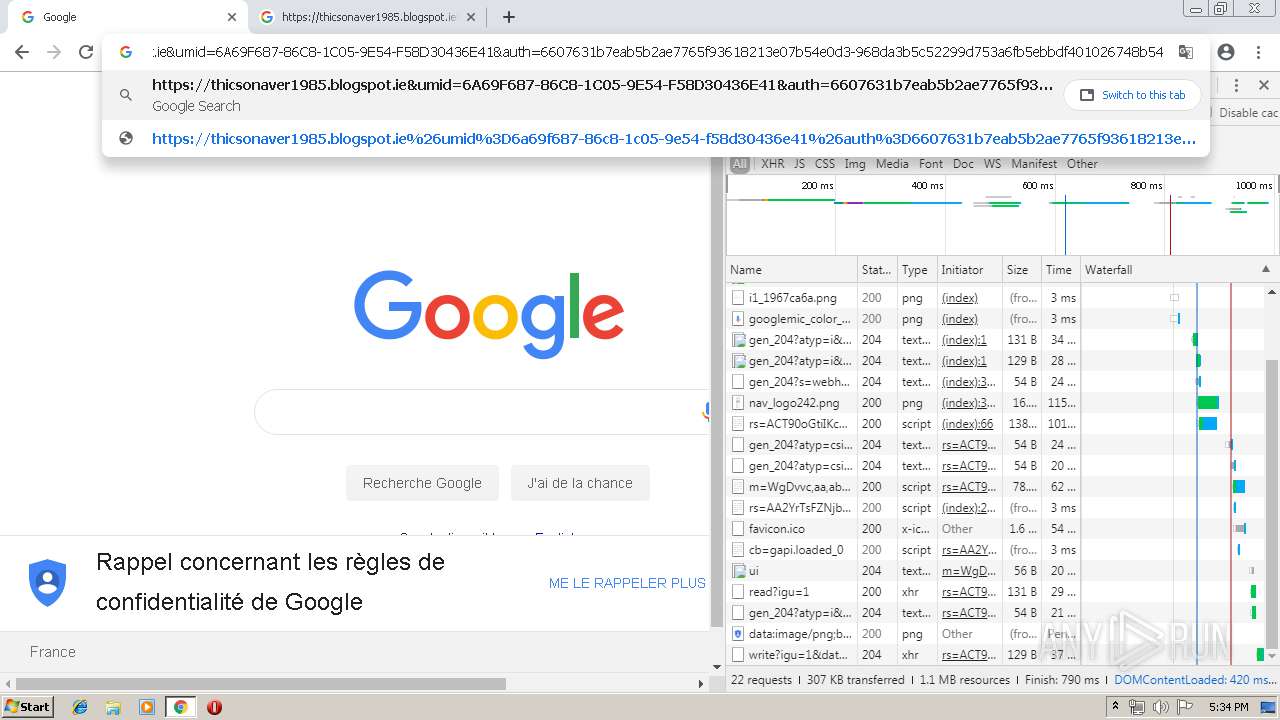
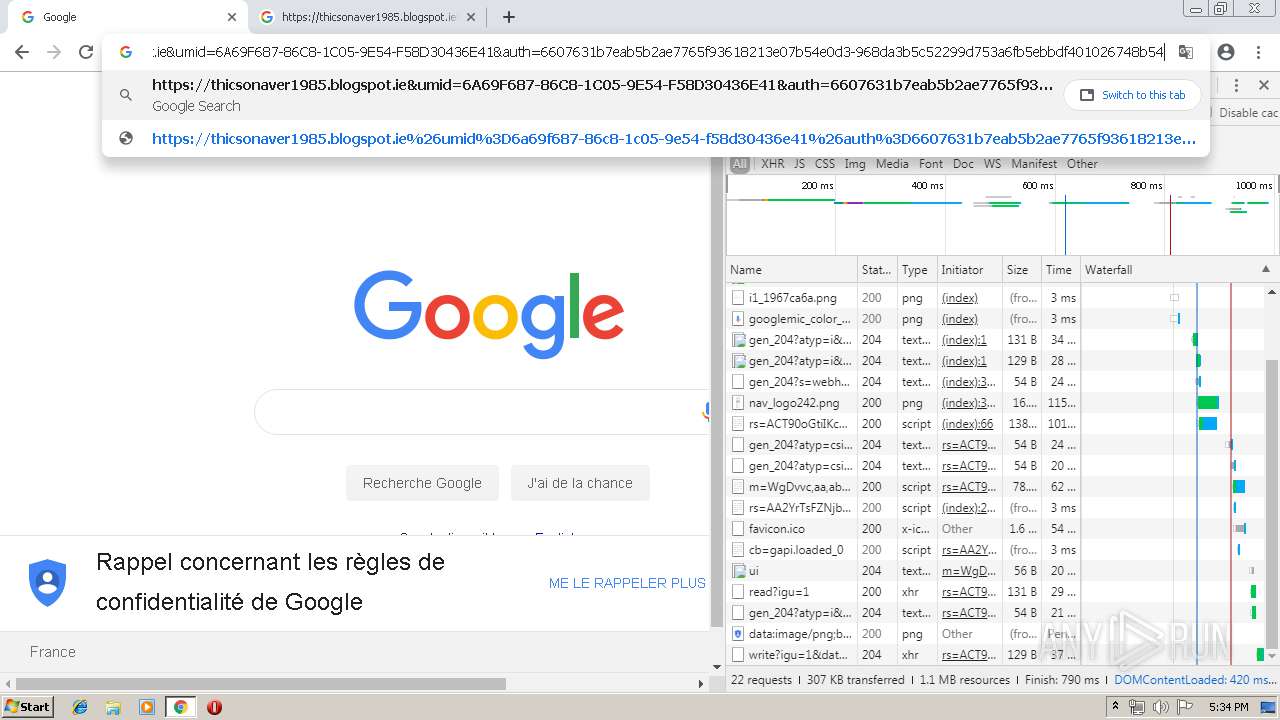
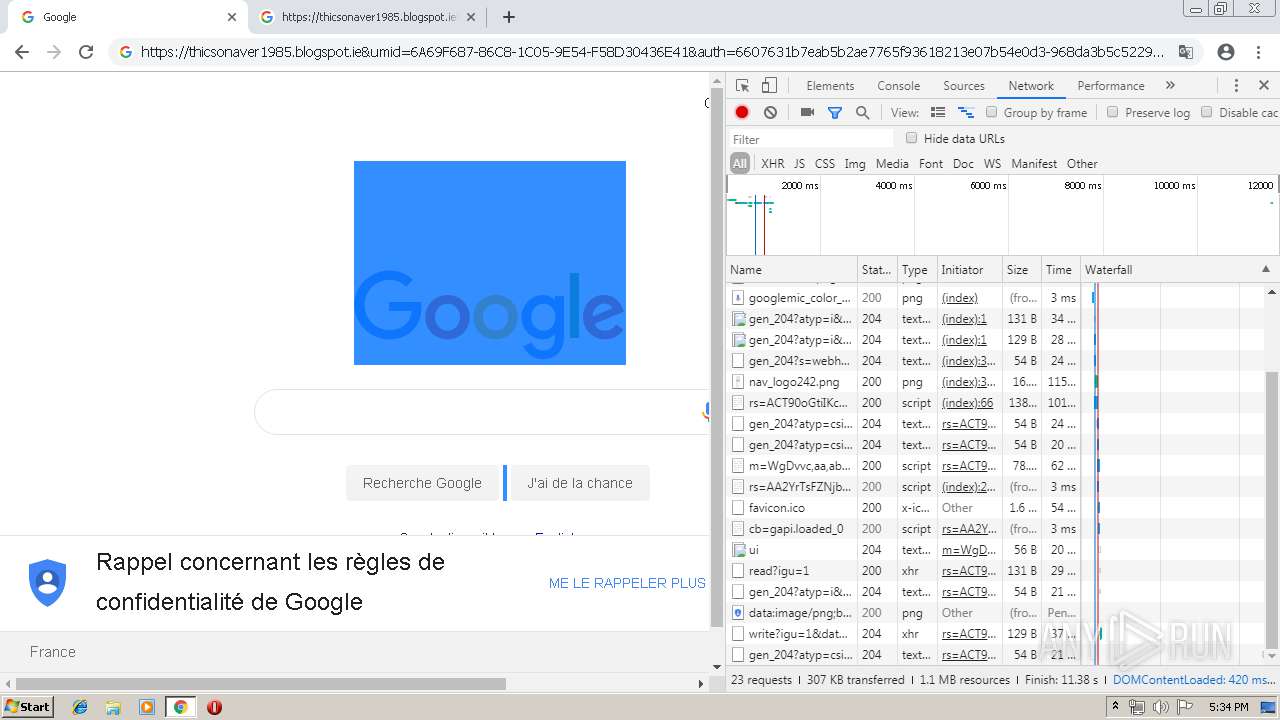
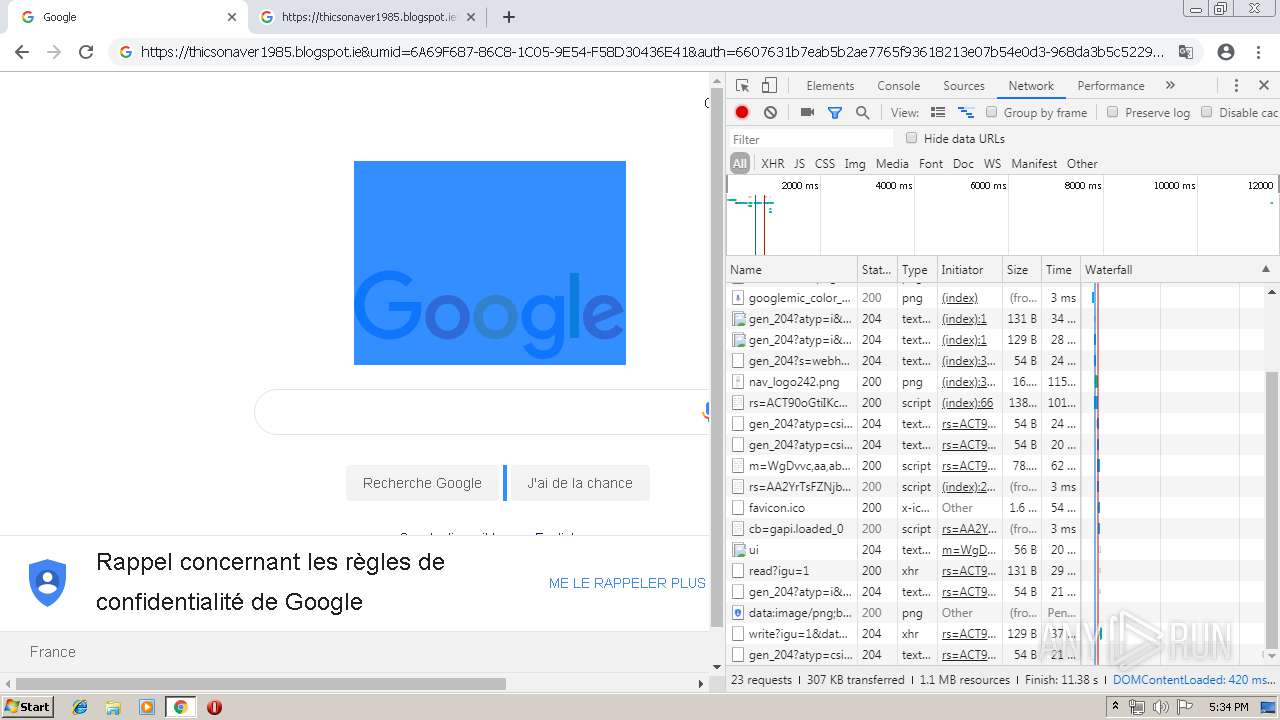
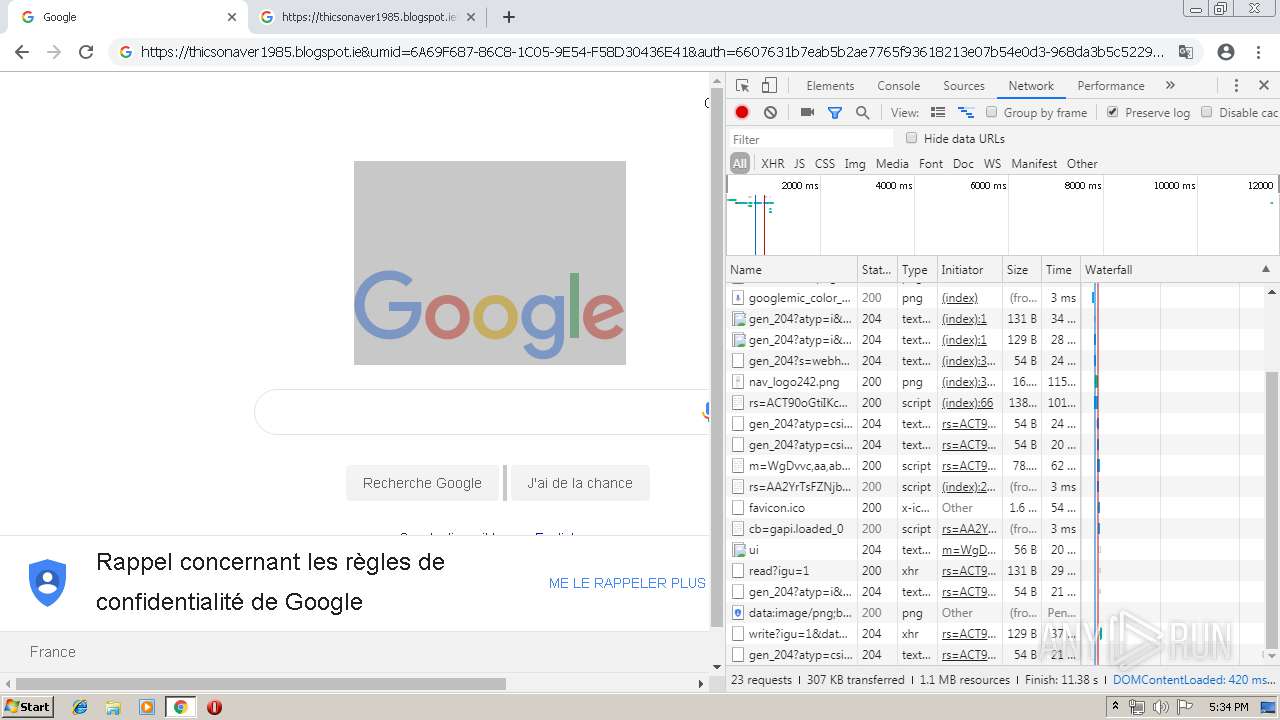
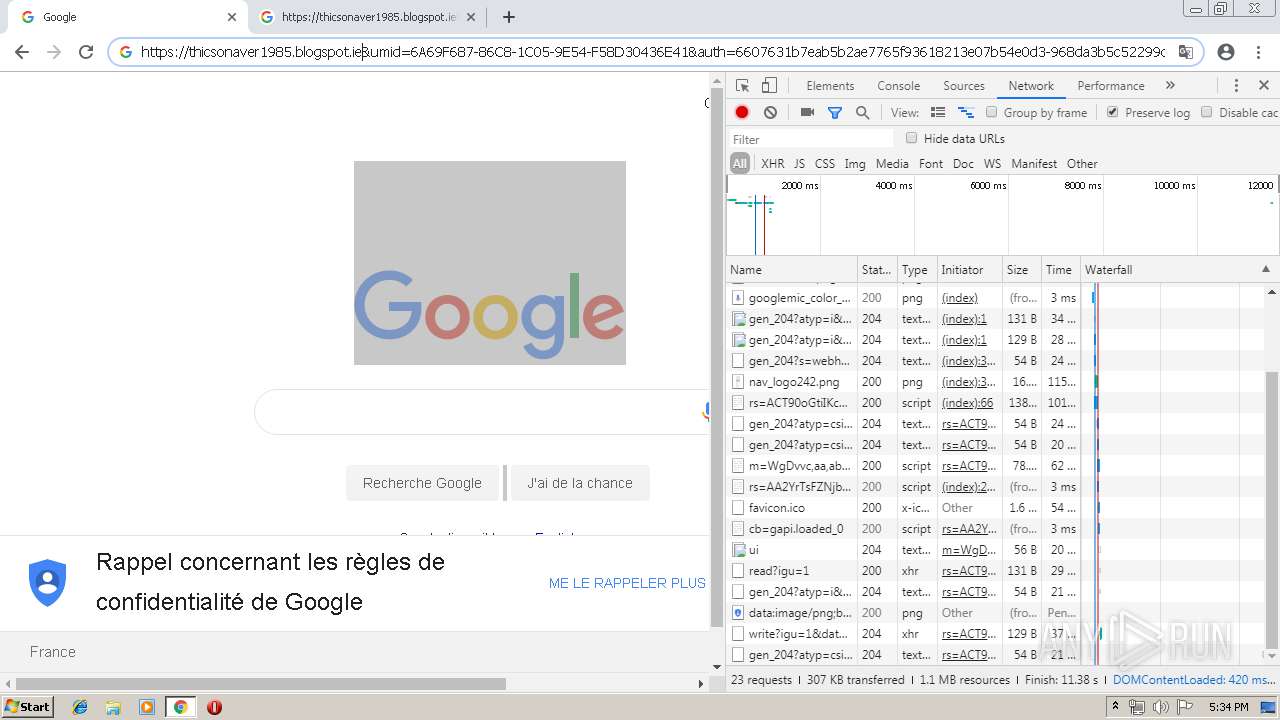
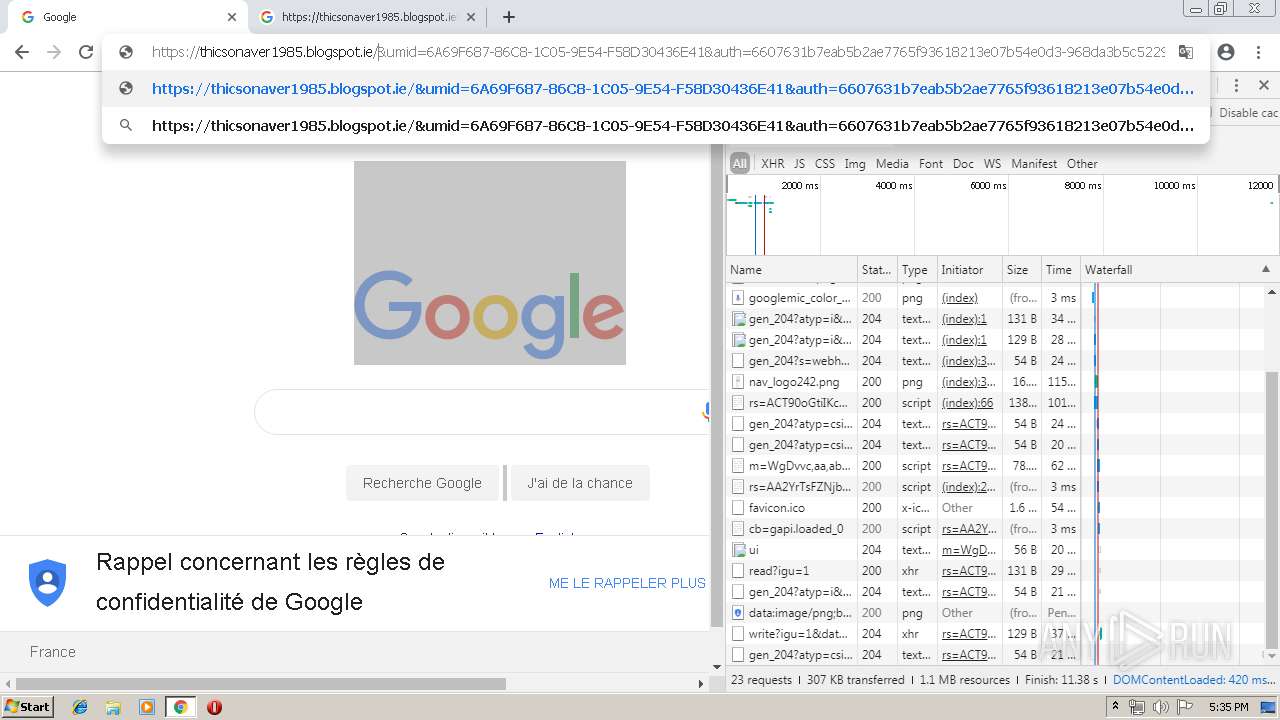
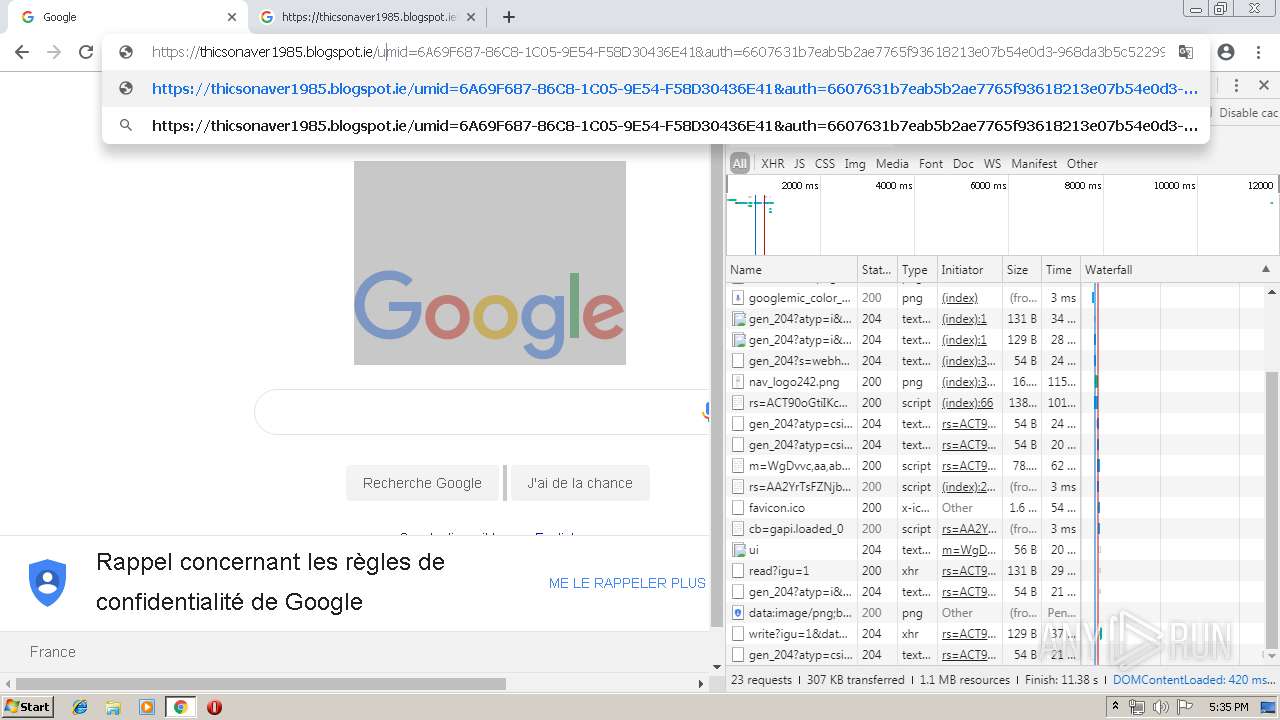
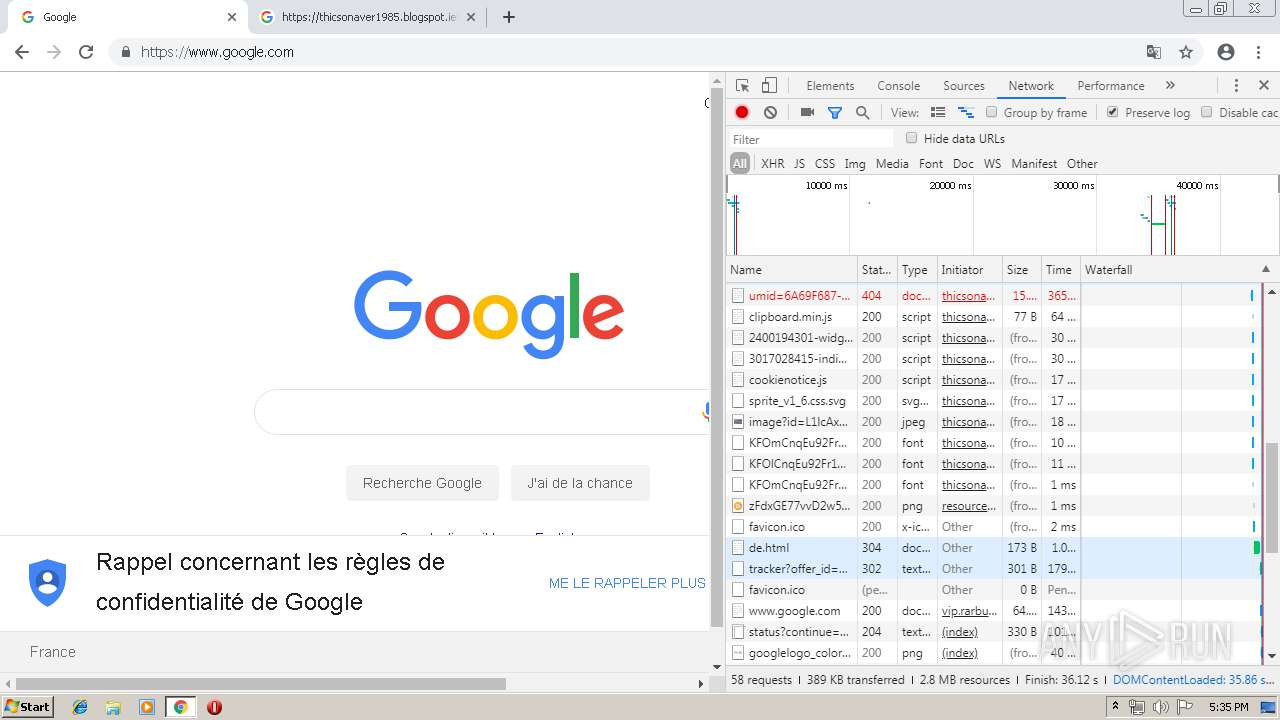
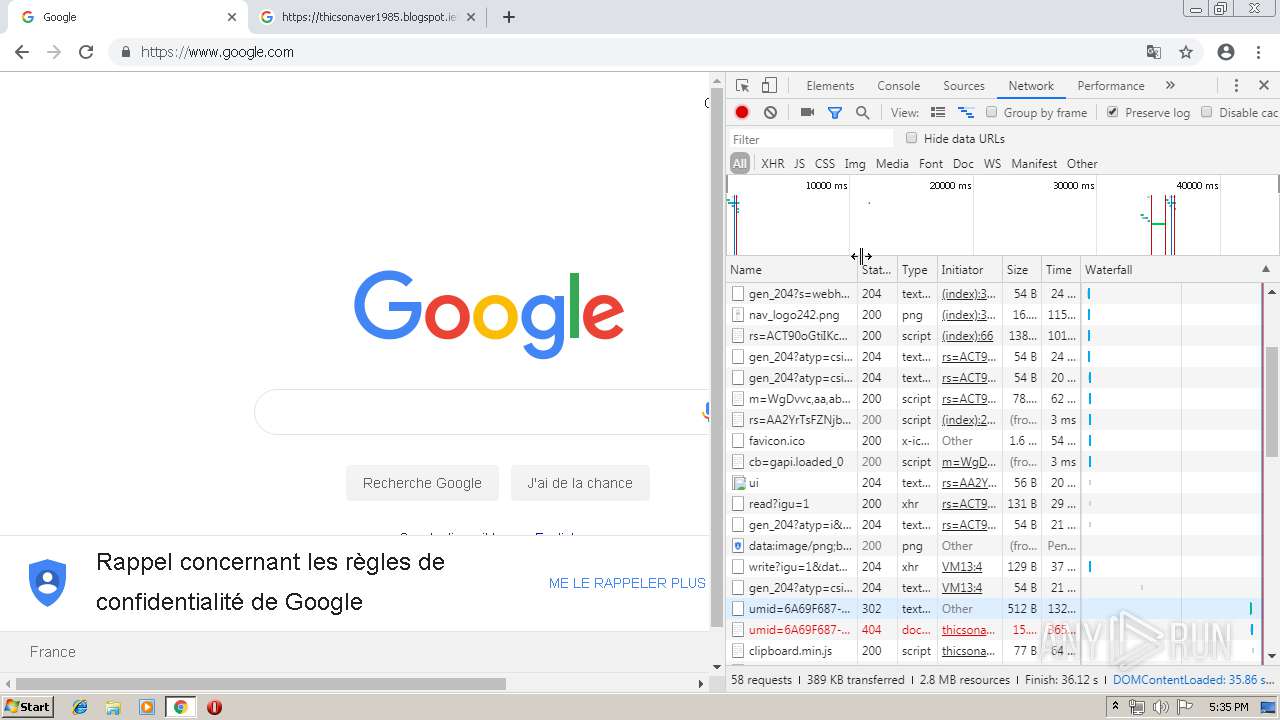
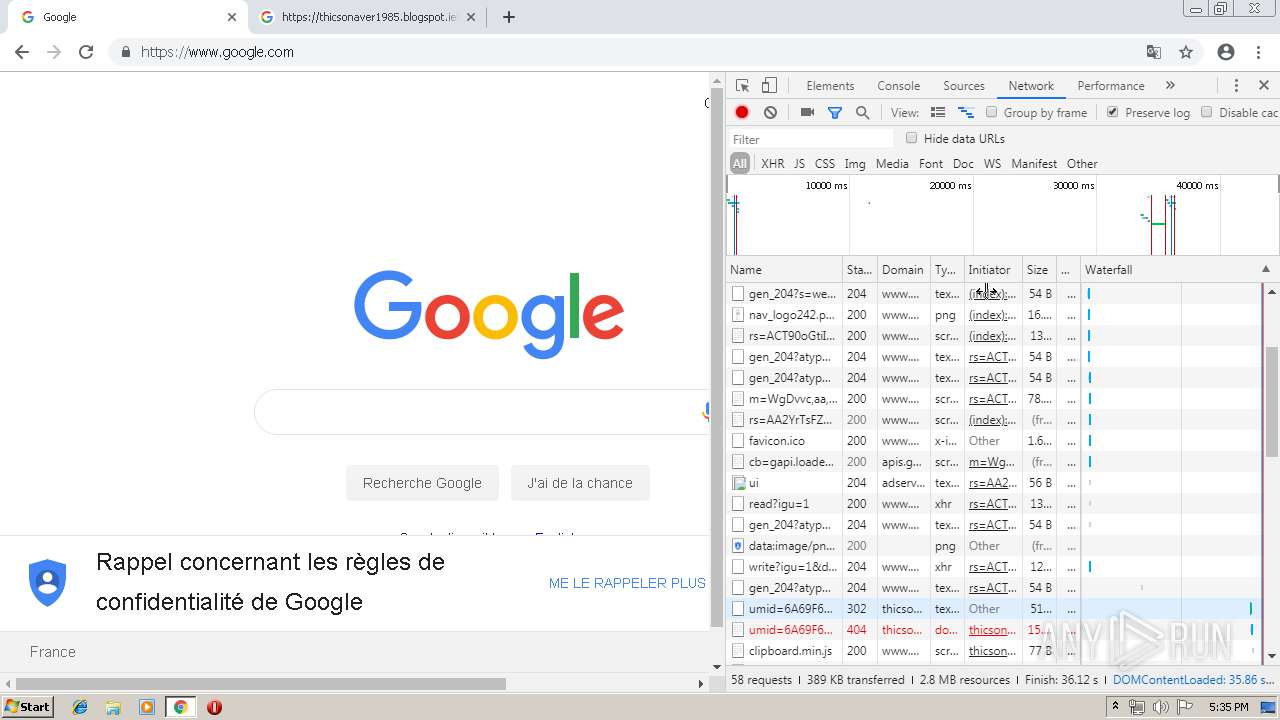
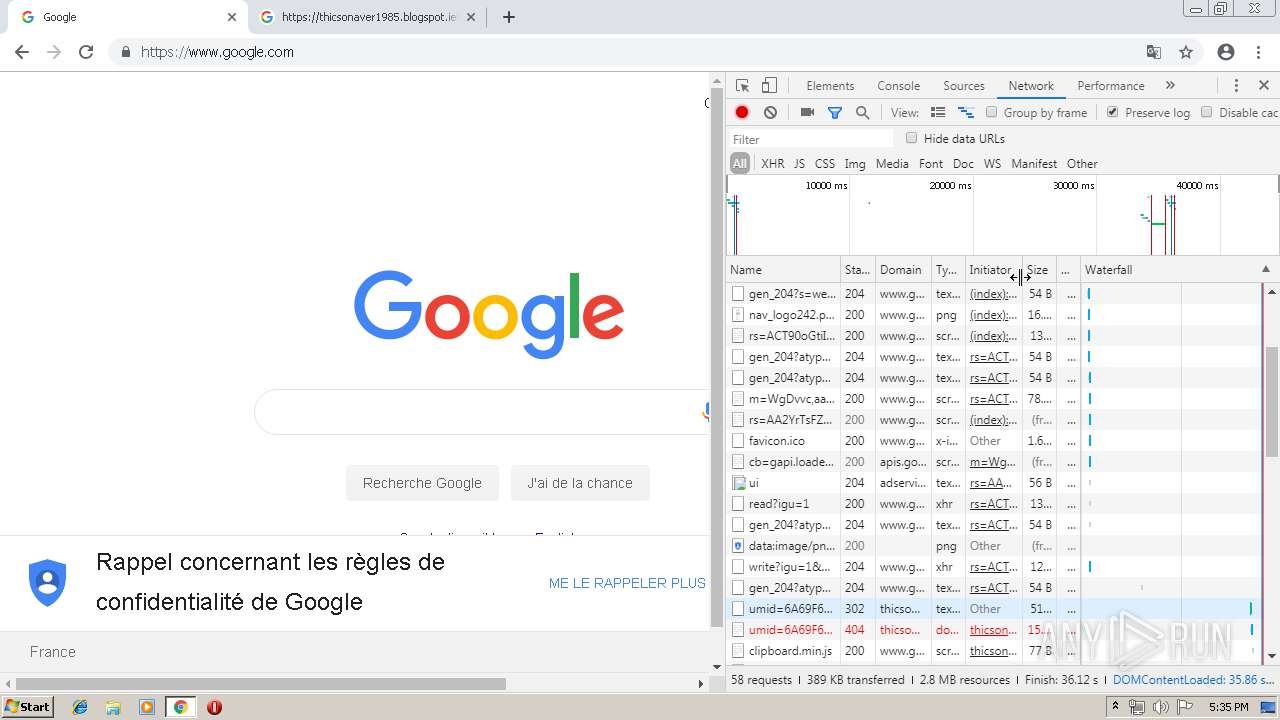
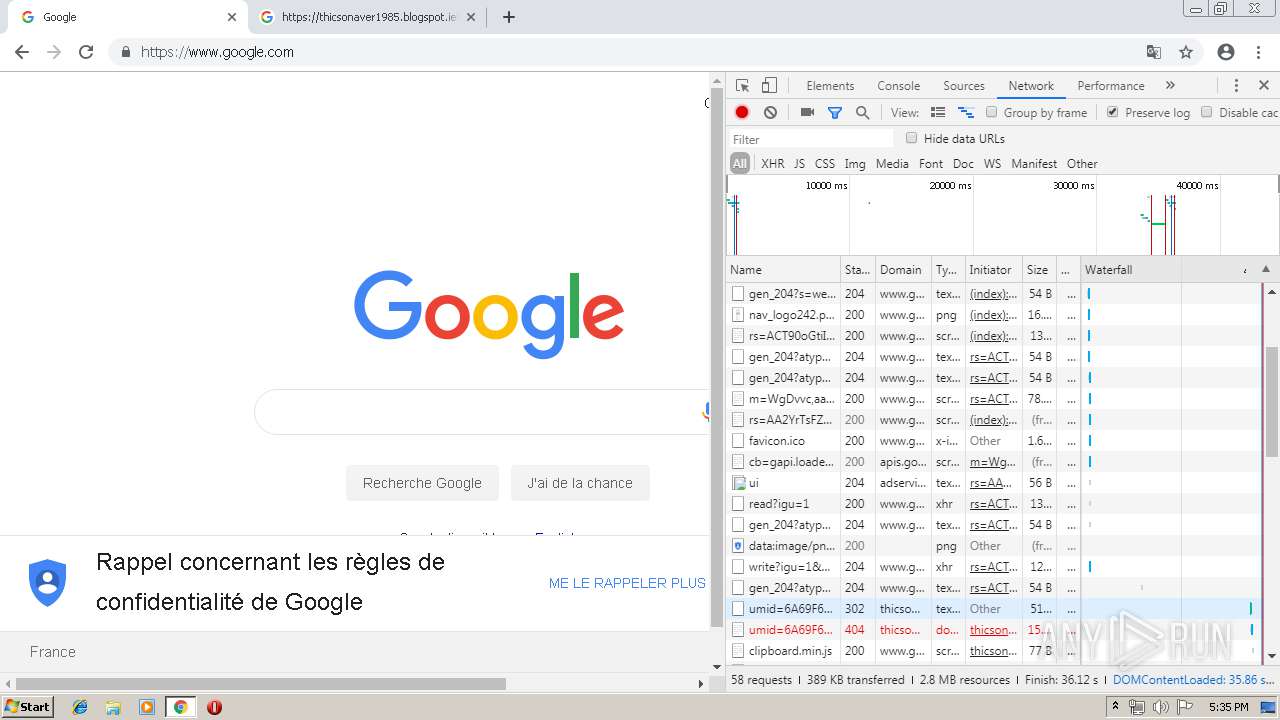
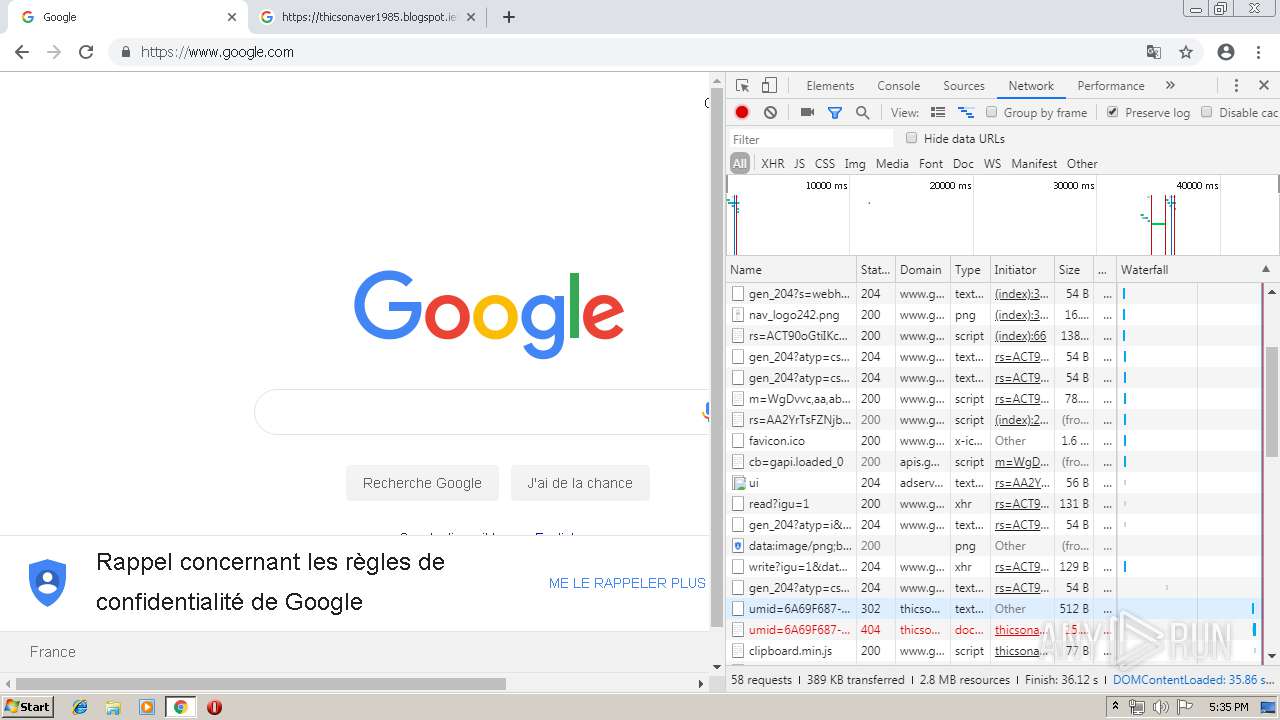
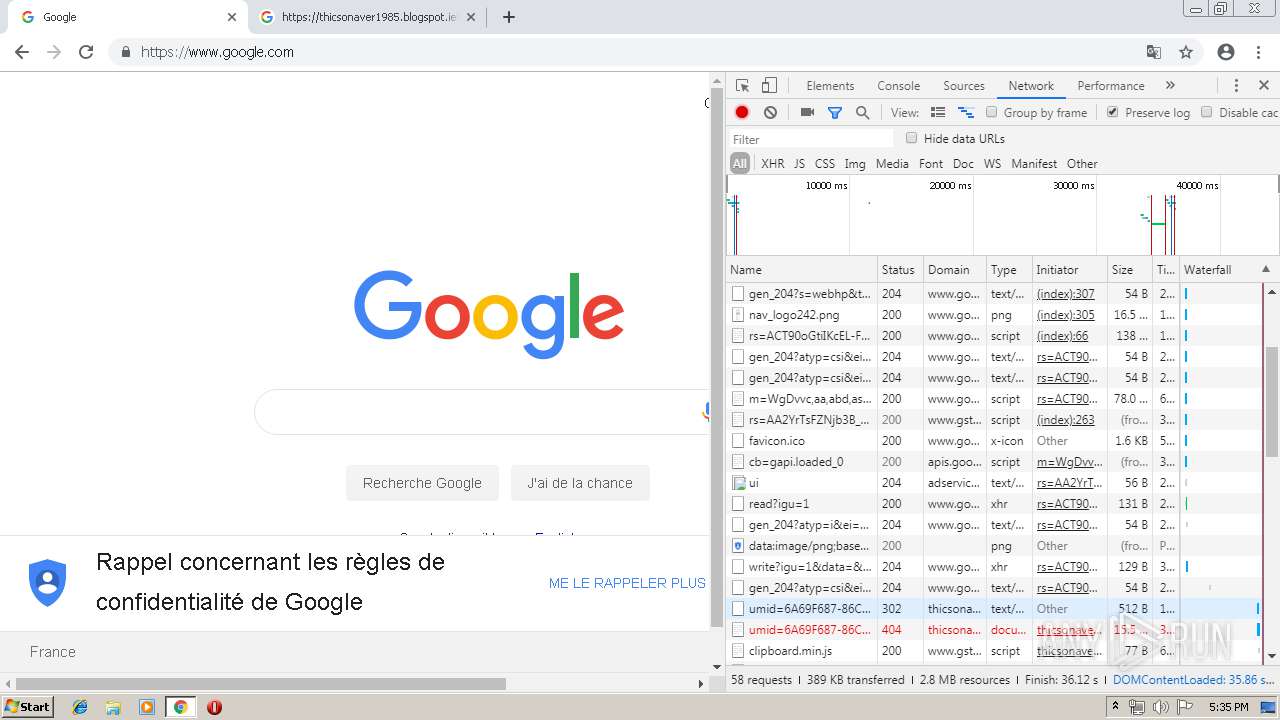
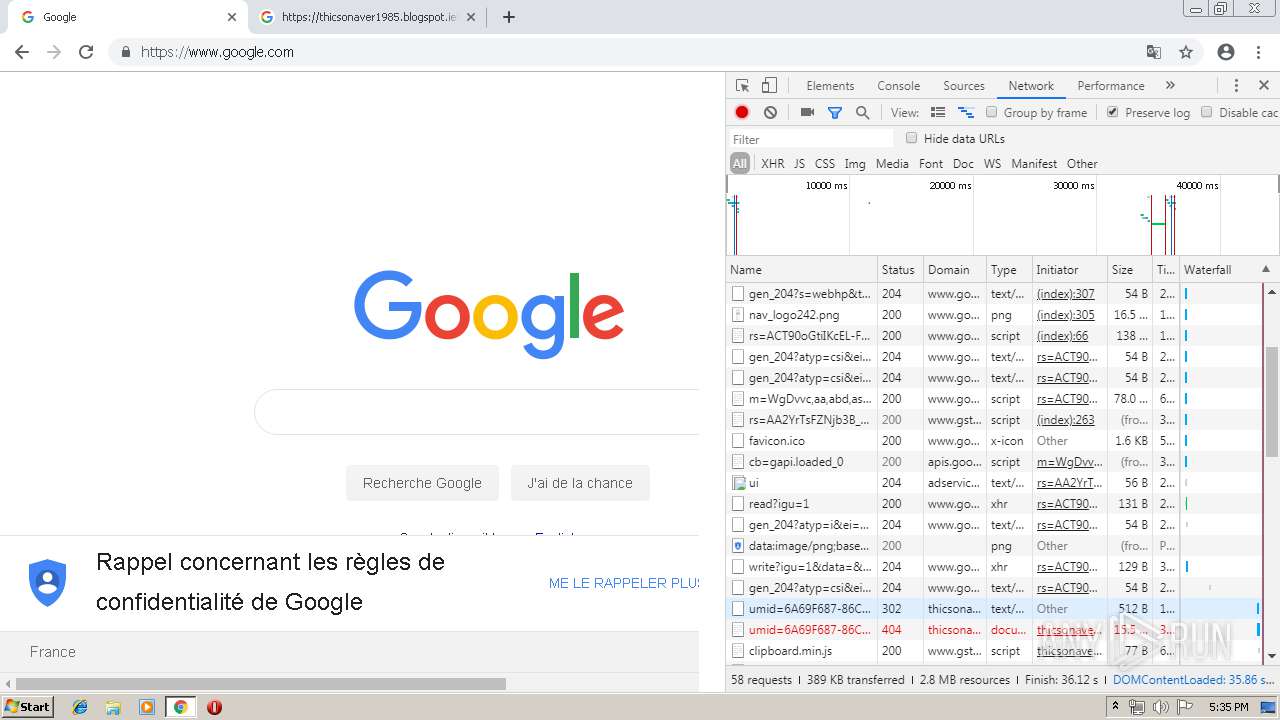
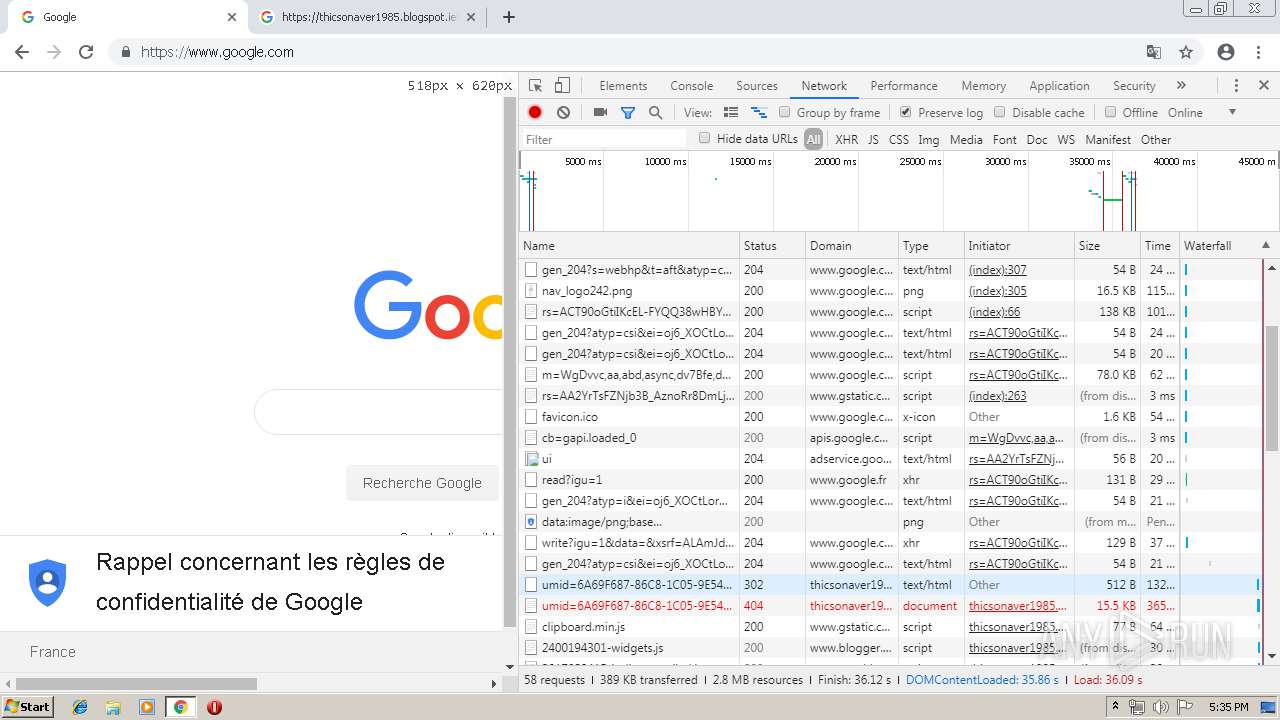
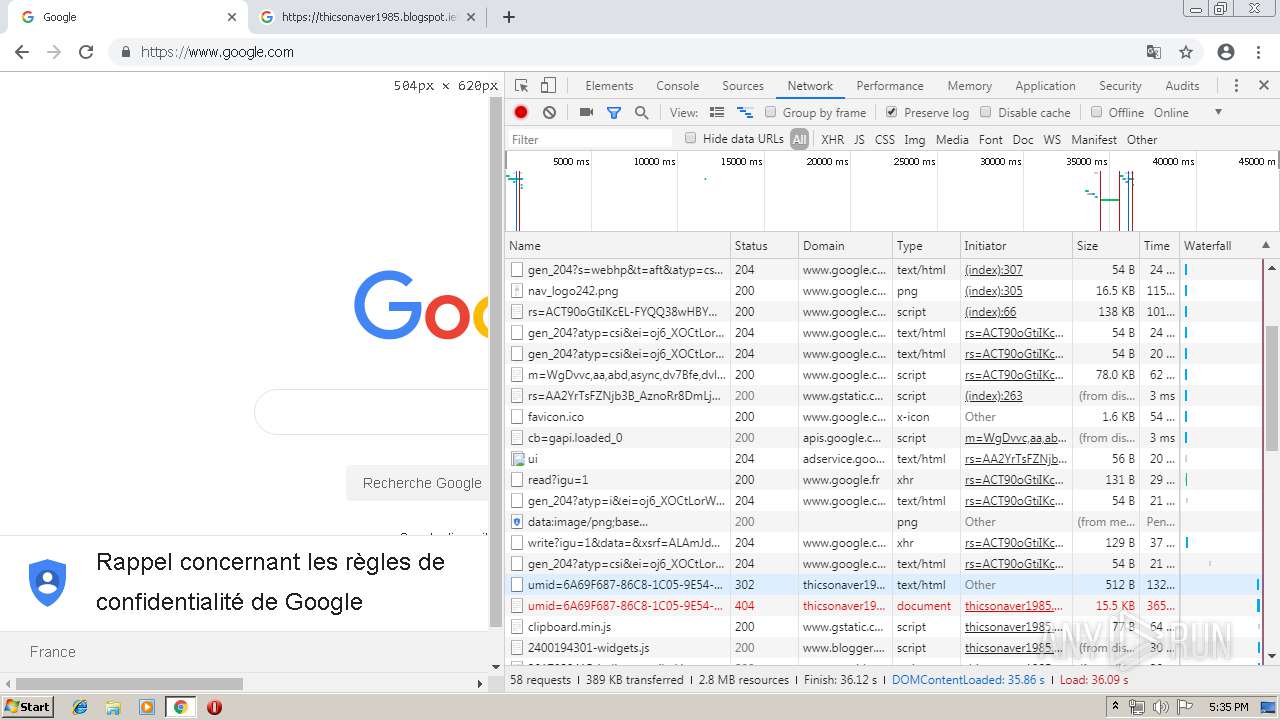
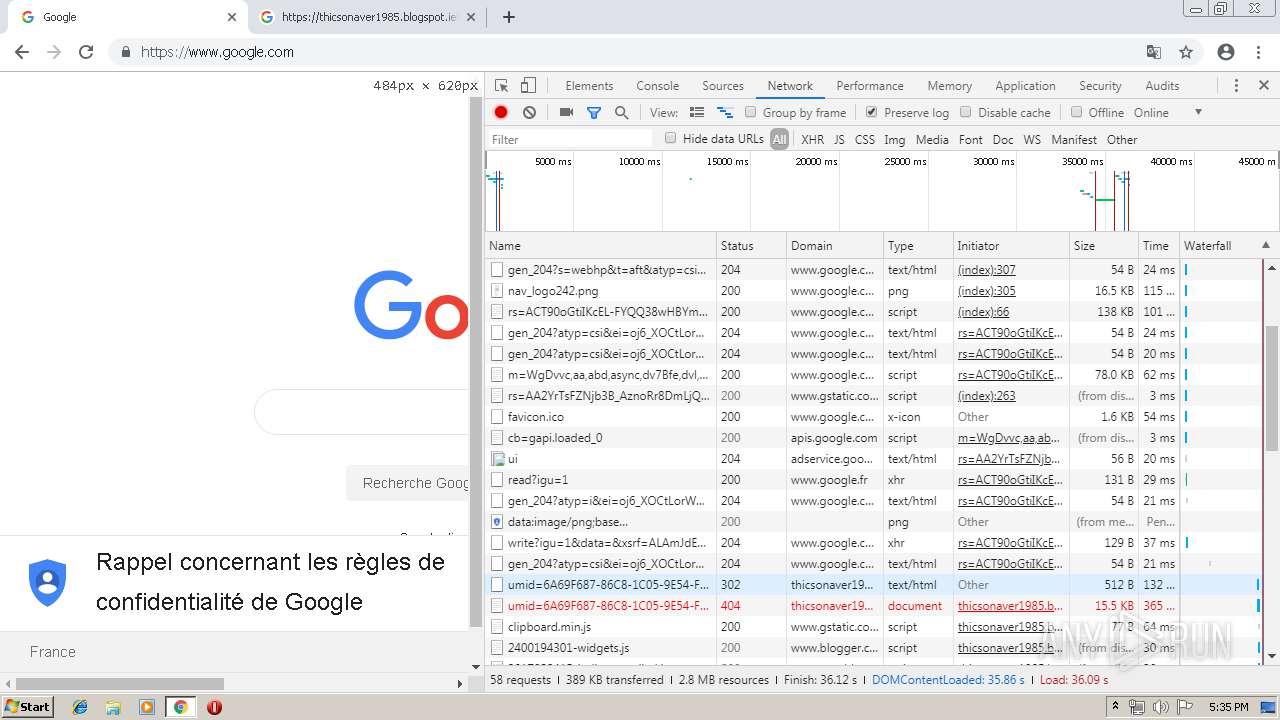
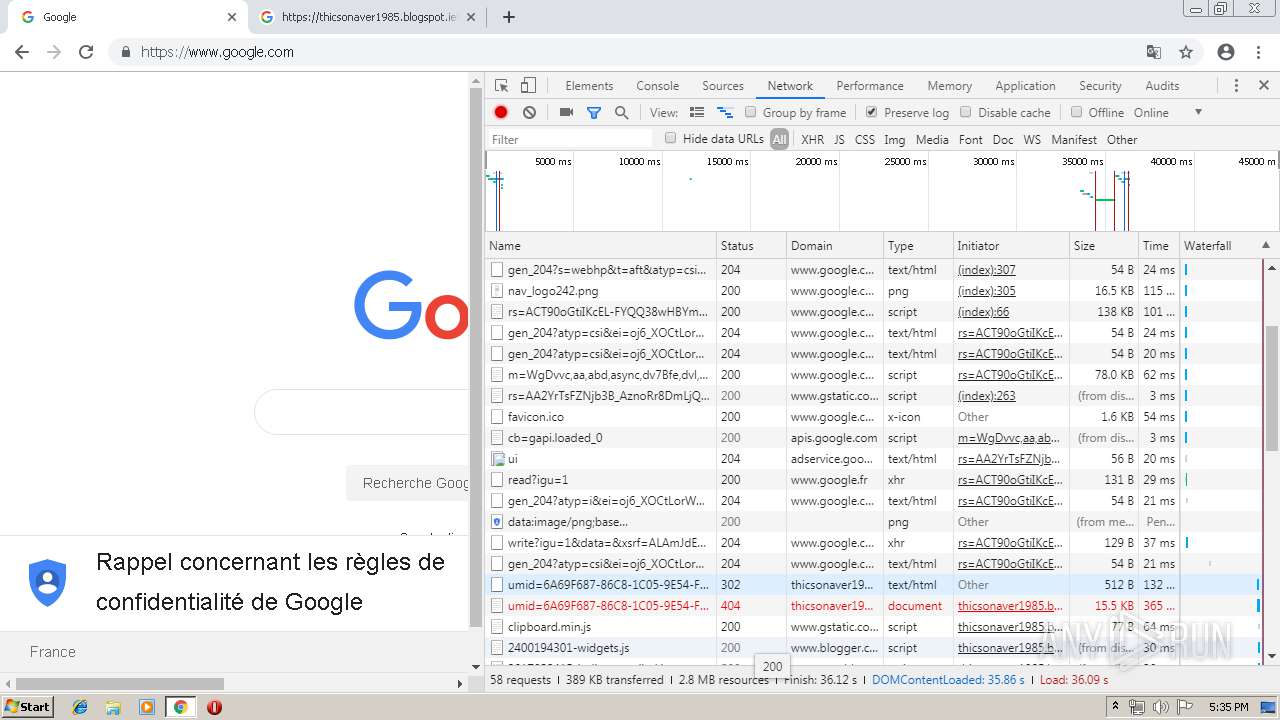
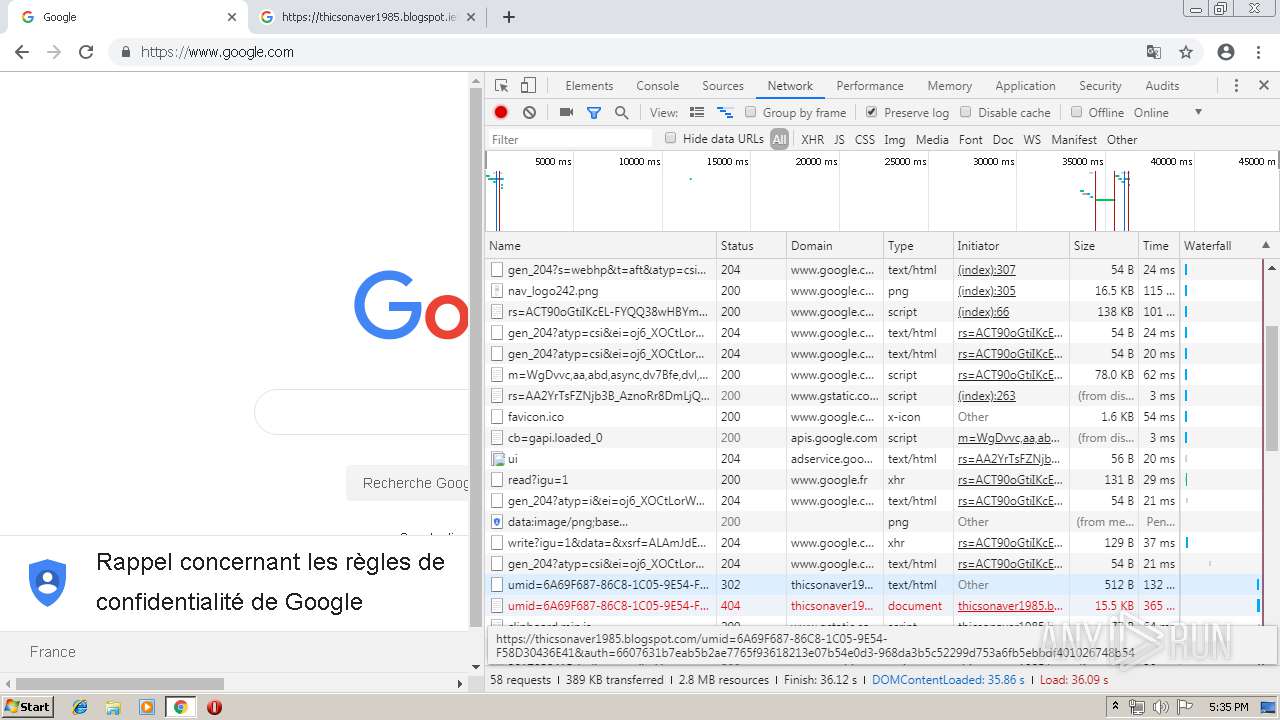
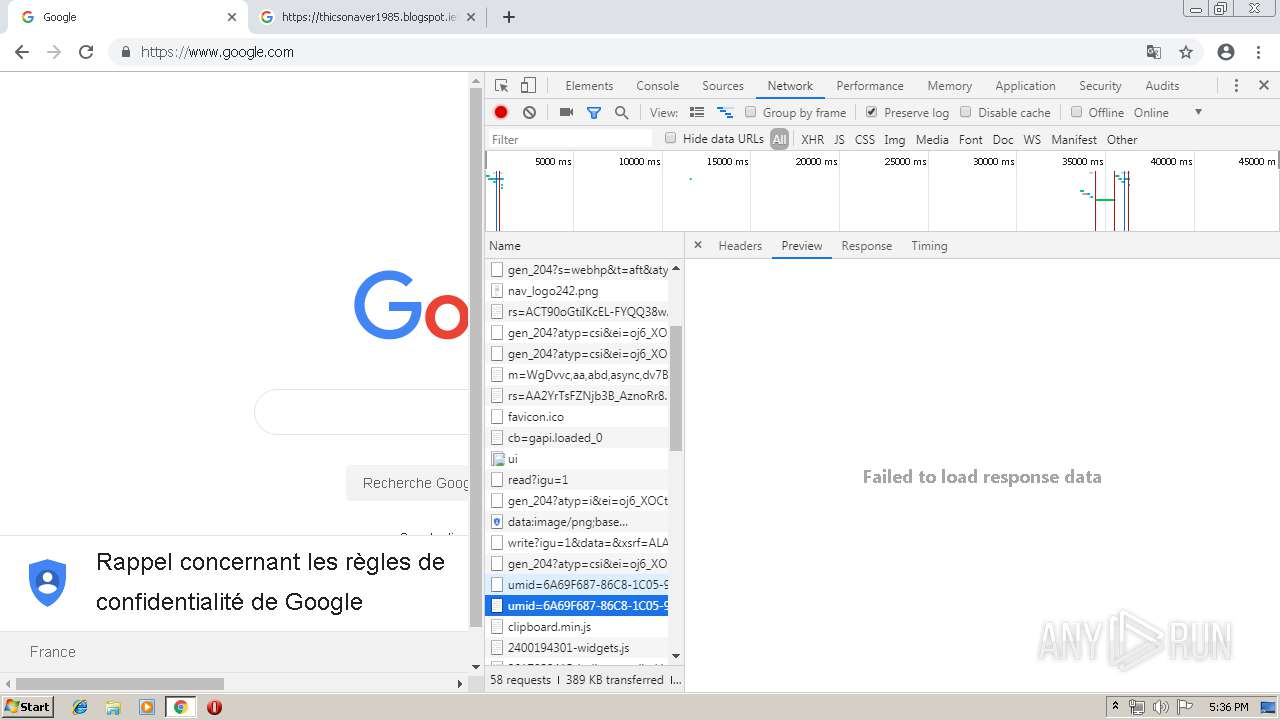
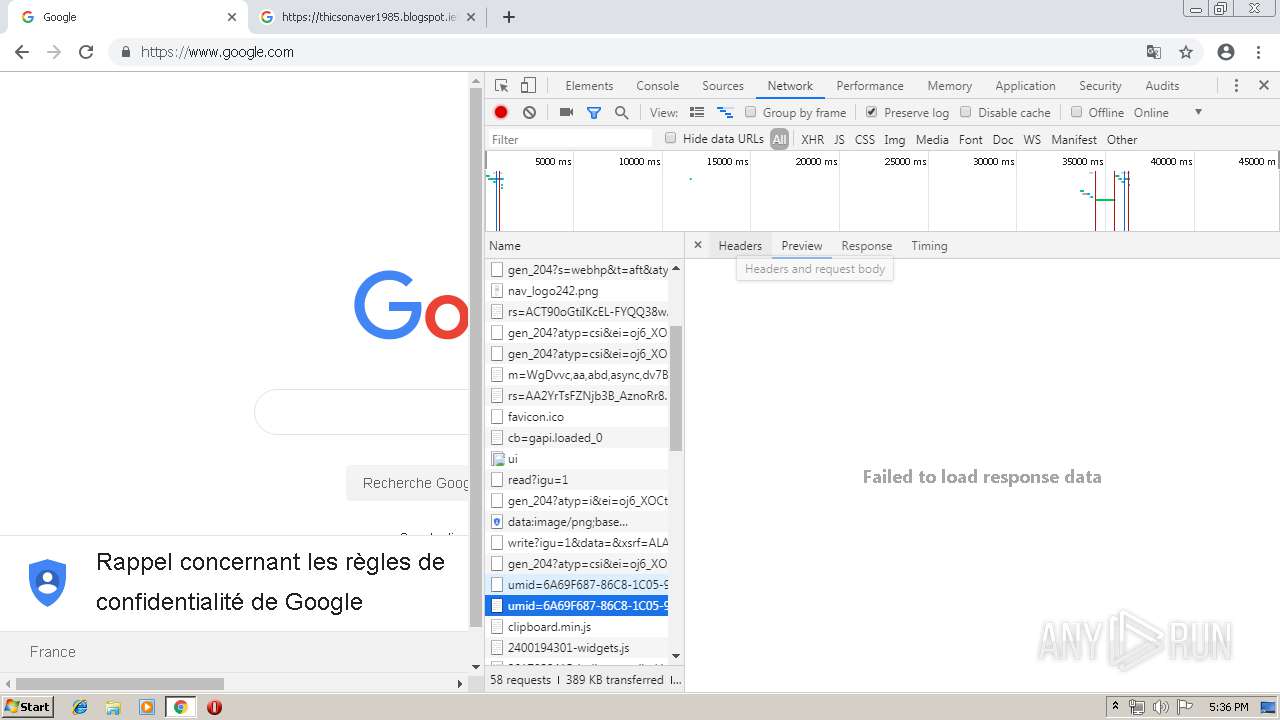
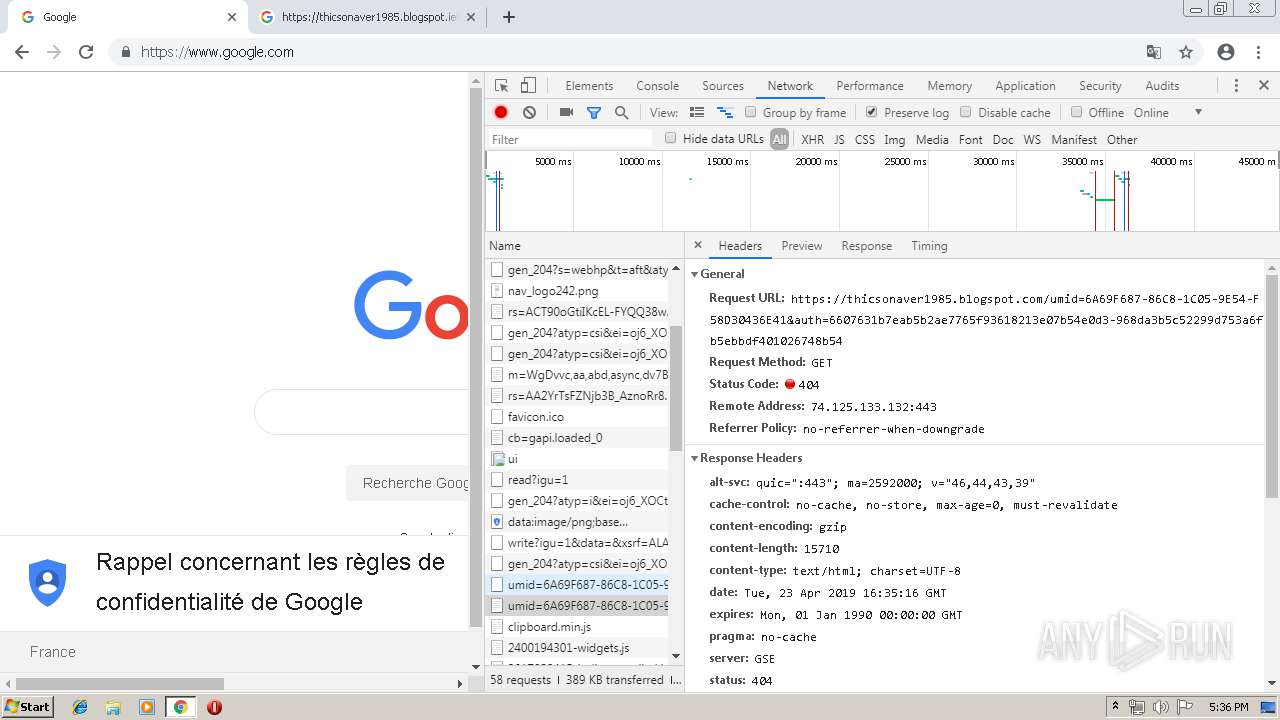
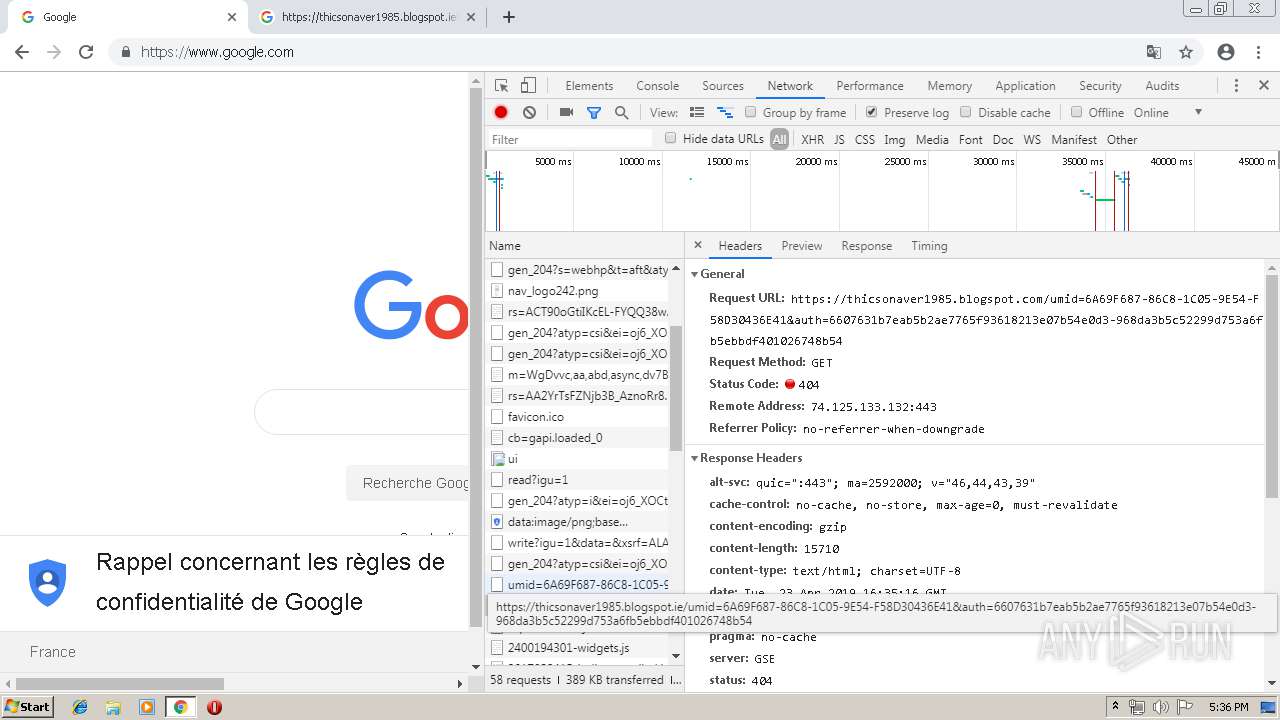
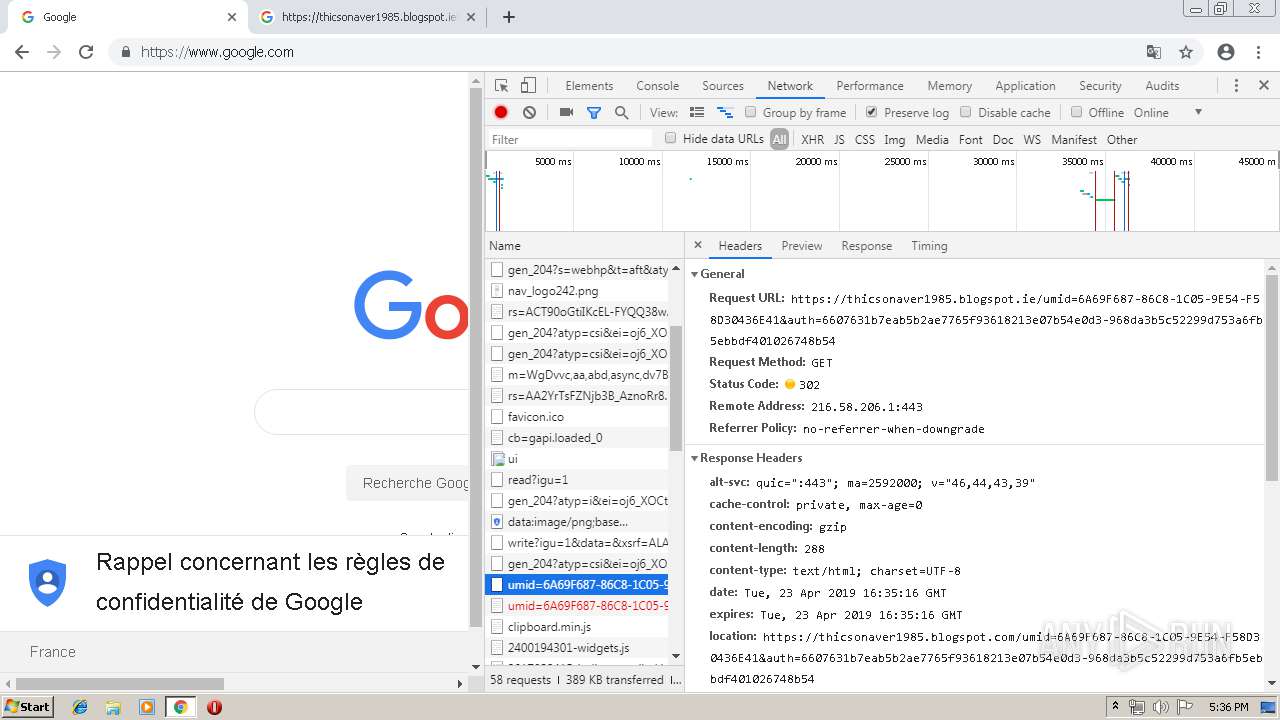
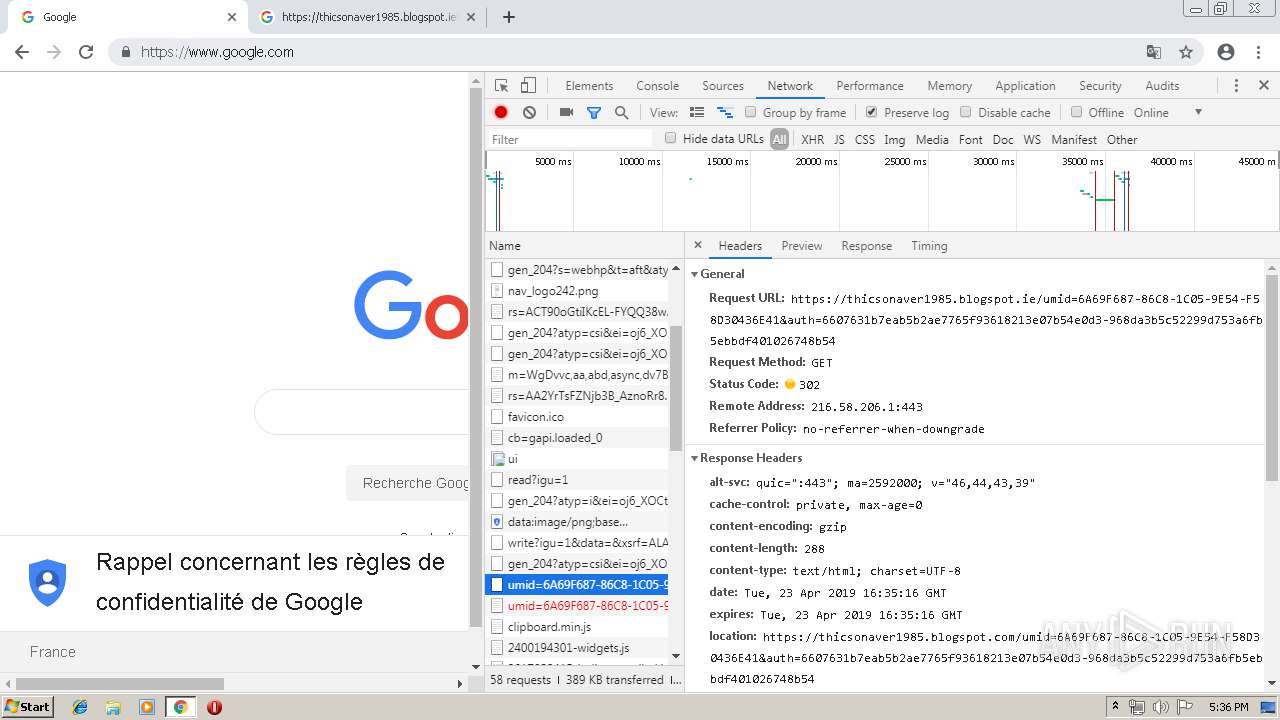
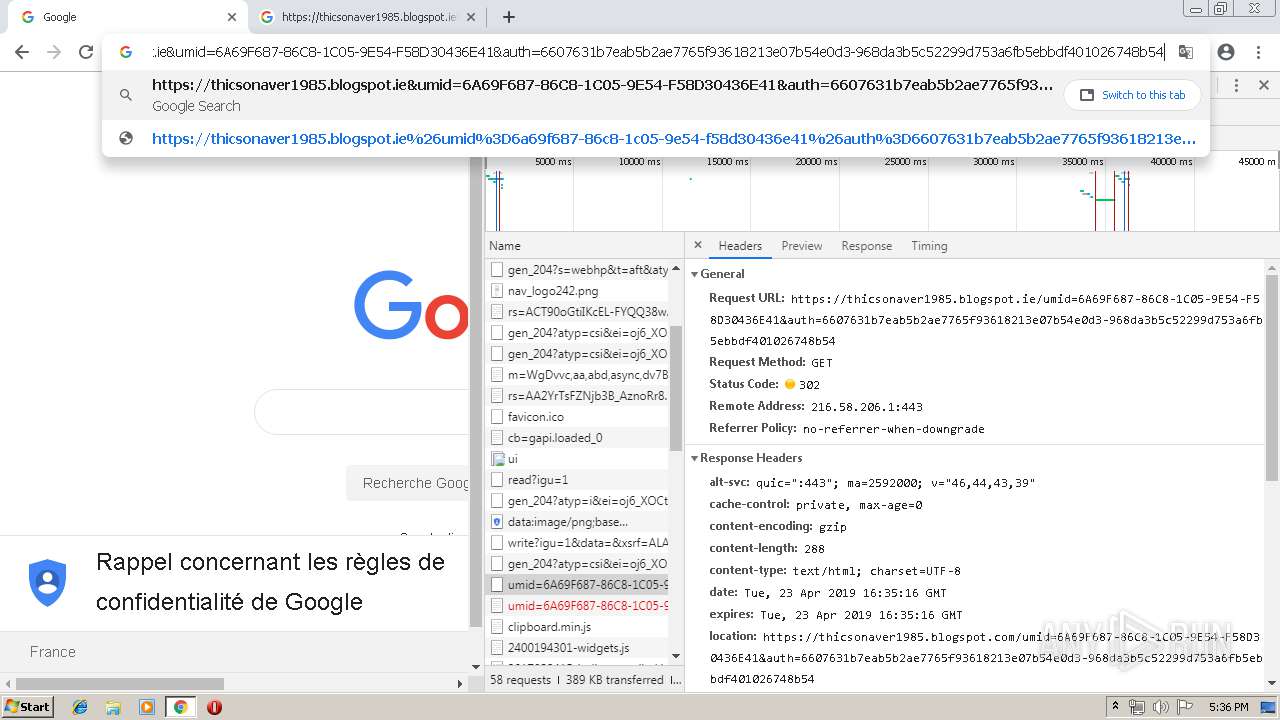
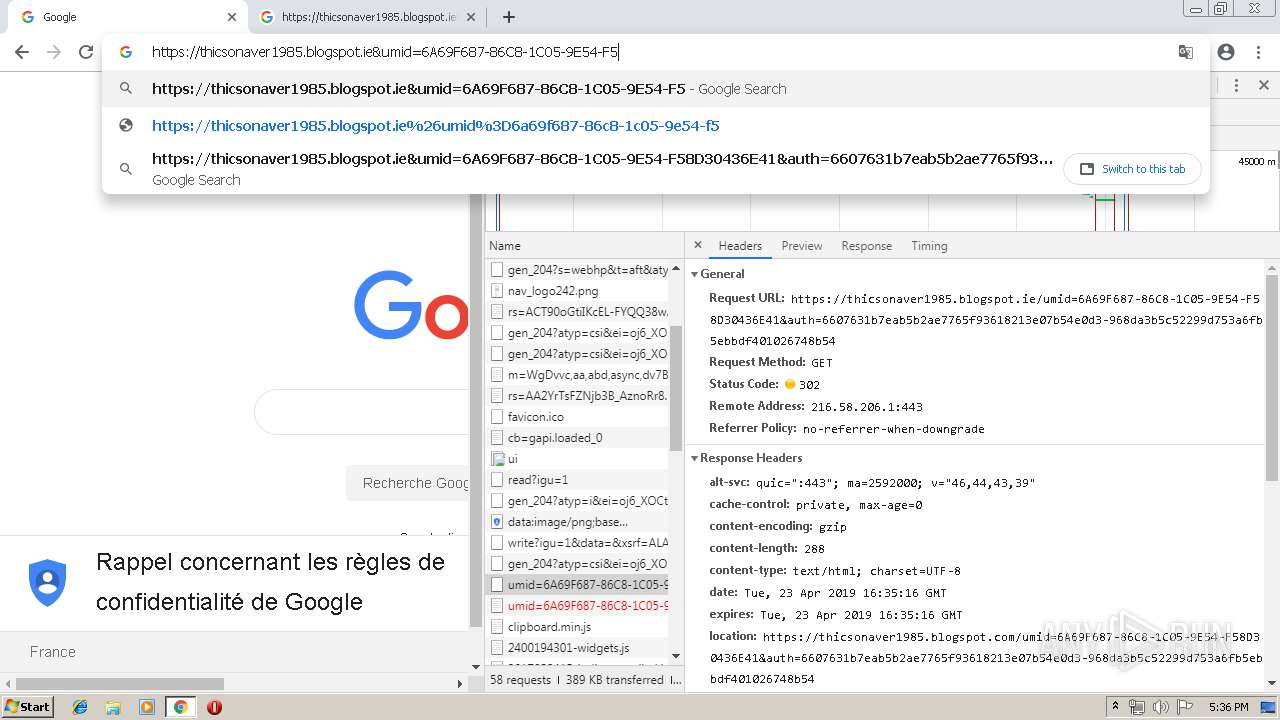
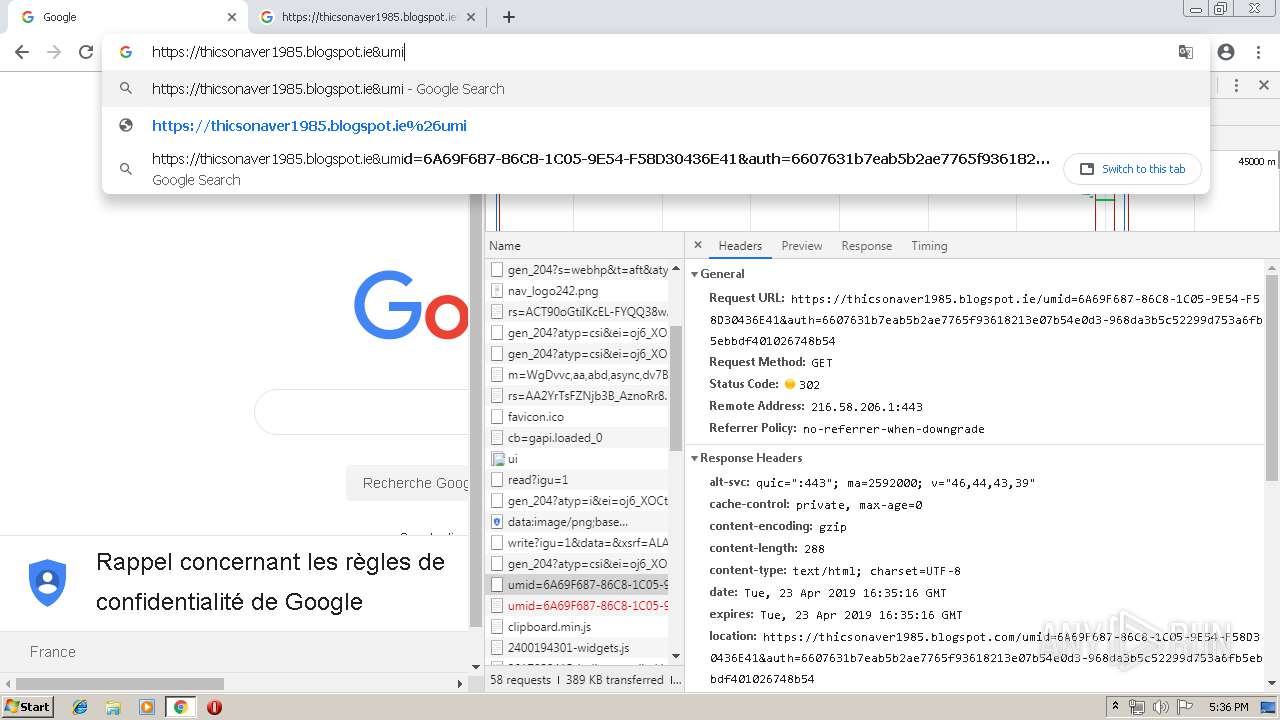
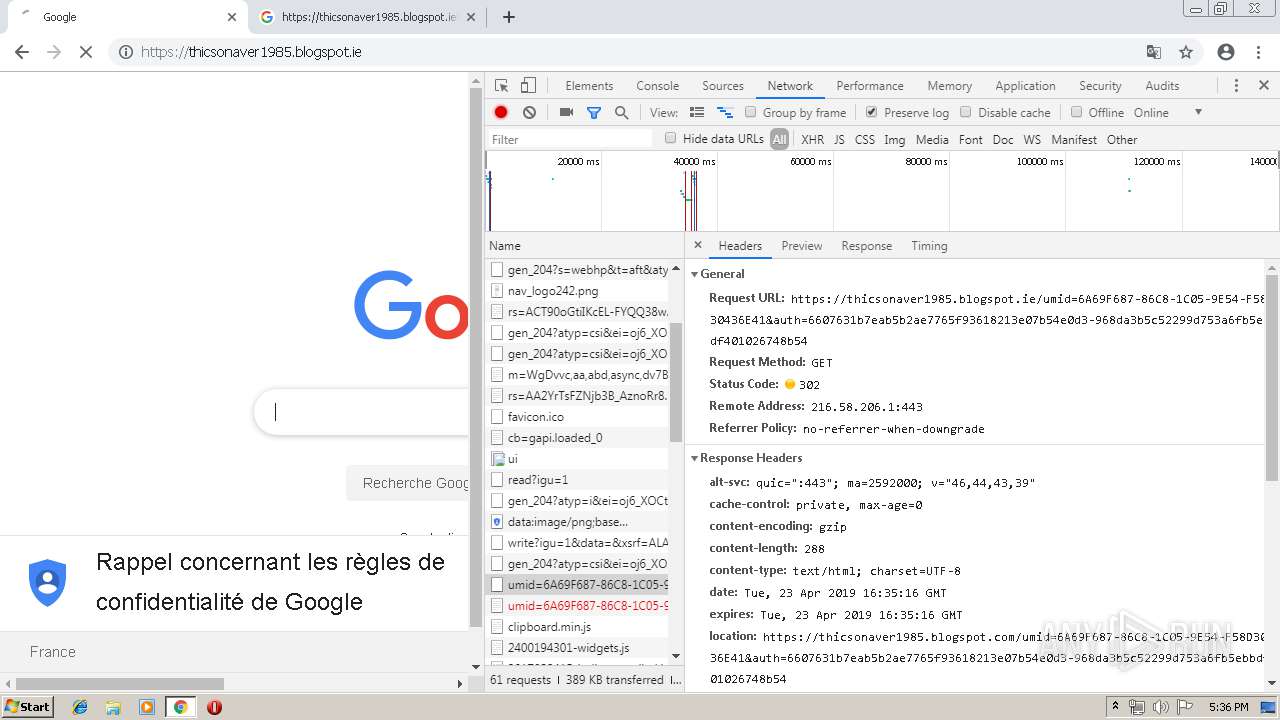
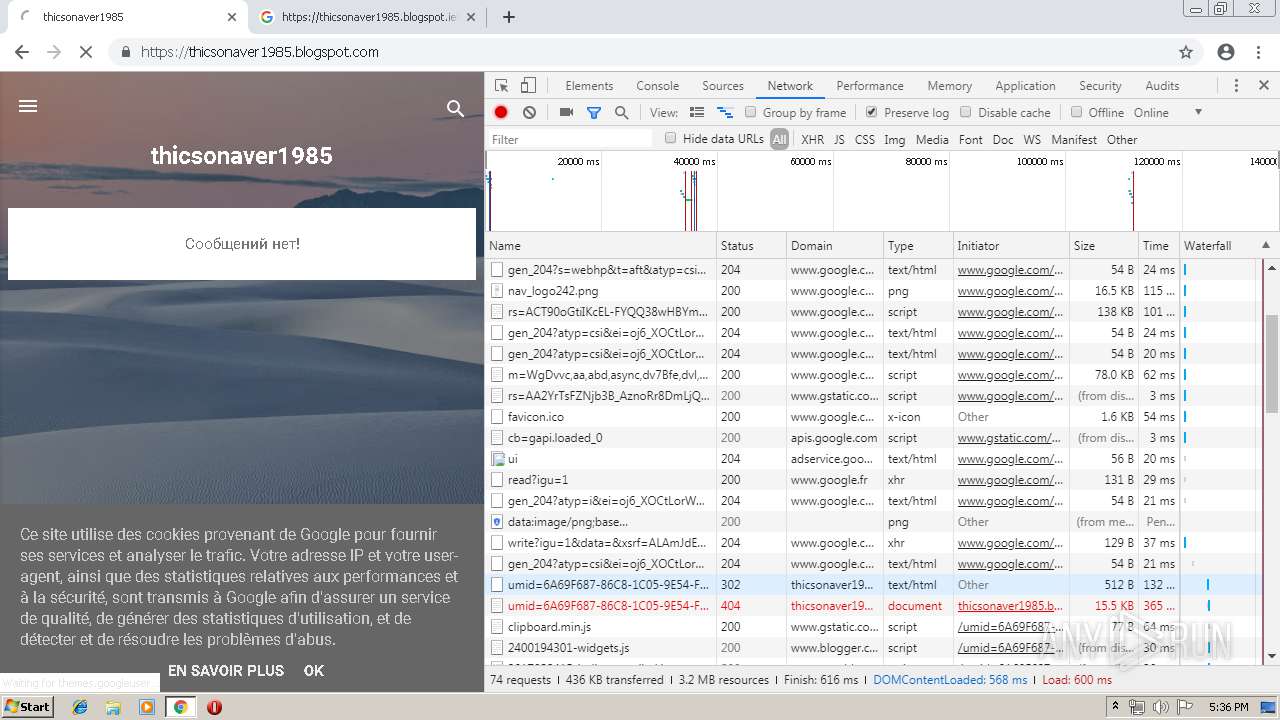
| URL: | https://thicsonaver1985.blogspot.ie&umid=6A69F687-86C8-1C05-9E54-F58D30436E41&auth=6607631b7eab5b2ae7765f93618213e07b54e0d3-968da3b5c52299d753a6fb5ebbdf401026748b54 |
| Full analysis: | https://app.any.run/tasks/fb34e9e3-9a42-4be4-a3e4-bc839f501e5e |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 16:32:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2746564D45DCDA73E8B2D6A8FD1EFDE1 |
| SHA1: | 2C8664EE5A7D3177844921E1C63CE663DE8135D1 |
| SHA256: | 0771AFBC135546A520D5FEFFDD77C5C770D85AA3CD5DF16A02B8F864EE7709AA |
| SSDEEP: | 3:N8FMGNwMzCzBDQHbQF7AeVQ8VRsD5Ru4vSgspUdIVSHEan+Do1HH7FEn:2hNw6CzUsV7dVRsDPu4vSgspUuKEOOk+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2952)
INFO
Application launched itself
- chrome.exe (PID: 2952)
Reads settings of System Certificates
- chrome.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
41
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --service-pipe-token=17249544413669539301 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17249544413669539301 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16954900819087346910 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16954900819087346910 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14770382354132348773 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14770382354132348773 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2687875739981966953 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2687875739981966953 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5018549448371904025 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5018549448371904025 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12068943839979364462 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12068943839979364462 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6130996546065017242 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6130996546065017242 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4710790985950123831 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4710790985950123831 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4668826713805366664 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4668826713805366664 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15586940584659214496 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
595
Read events
480
Write events
110
Delete events
5
Modification events
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2952-13200510764552375 |
Value: 259 | |||
Executable files
0
Suspicious files
119
Text files
157
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2ecec5eb-d372-4c6f-a821-a5077eb4c180.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
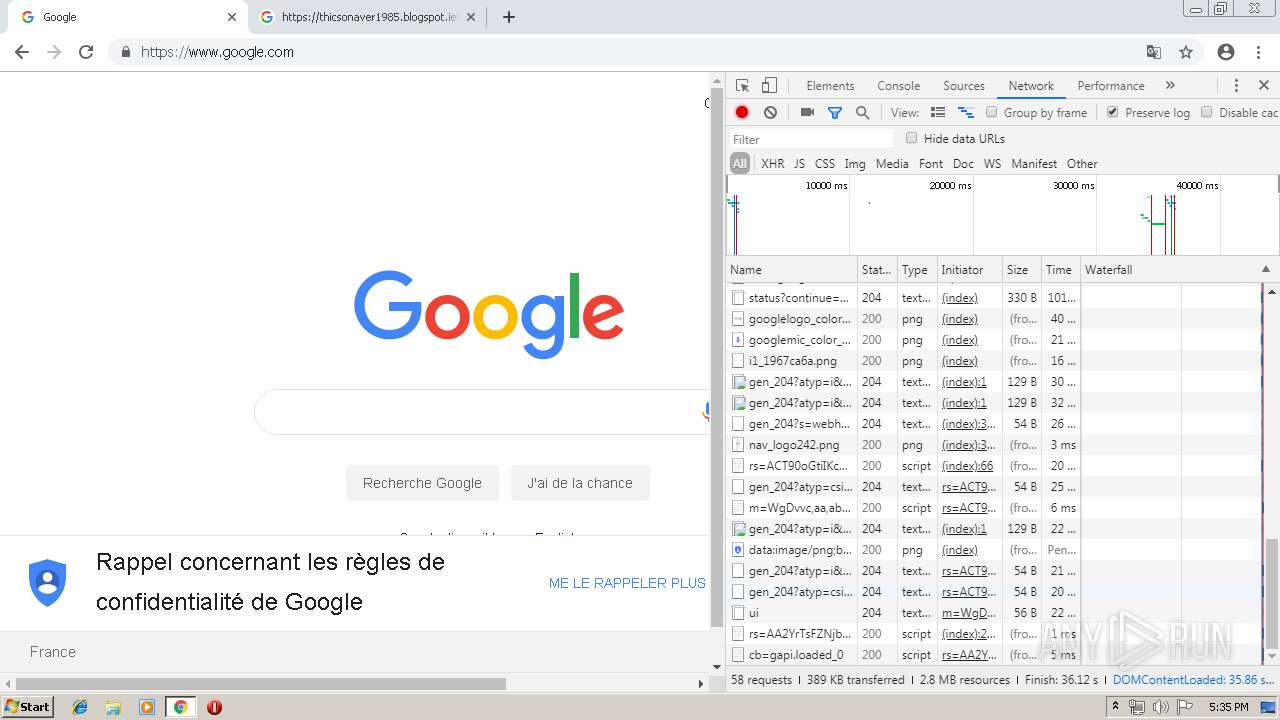
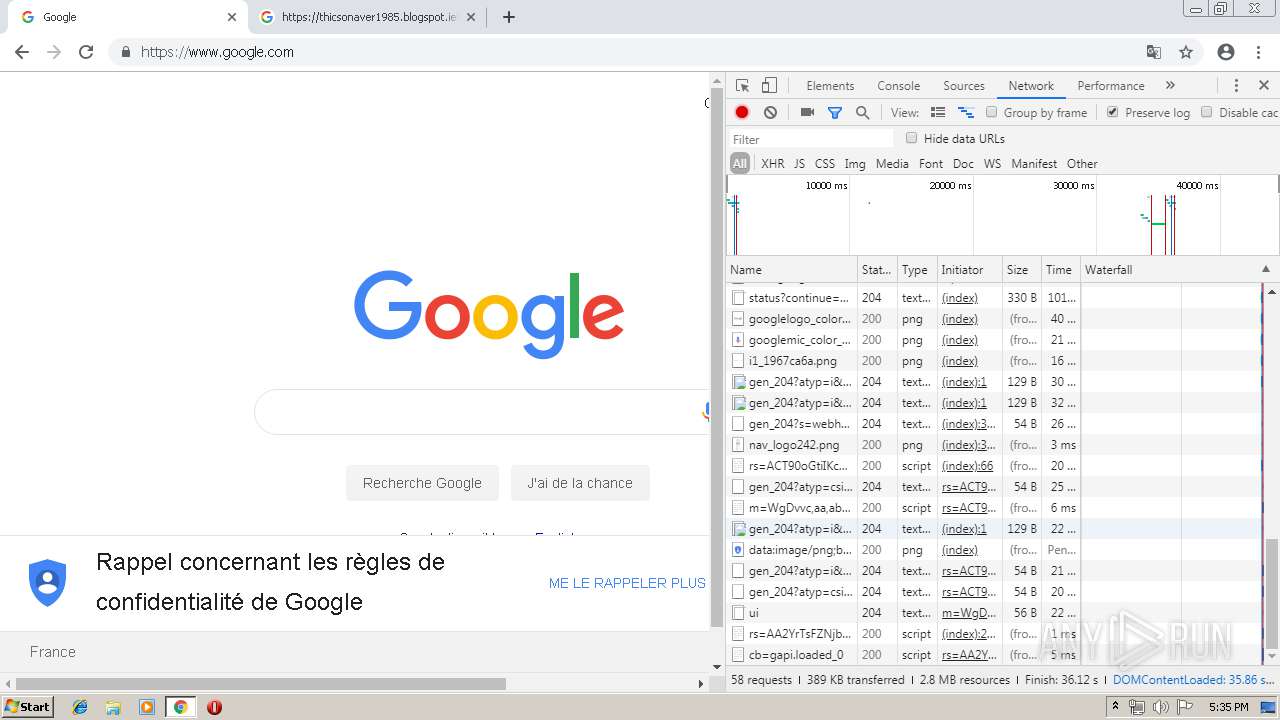
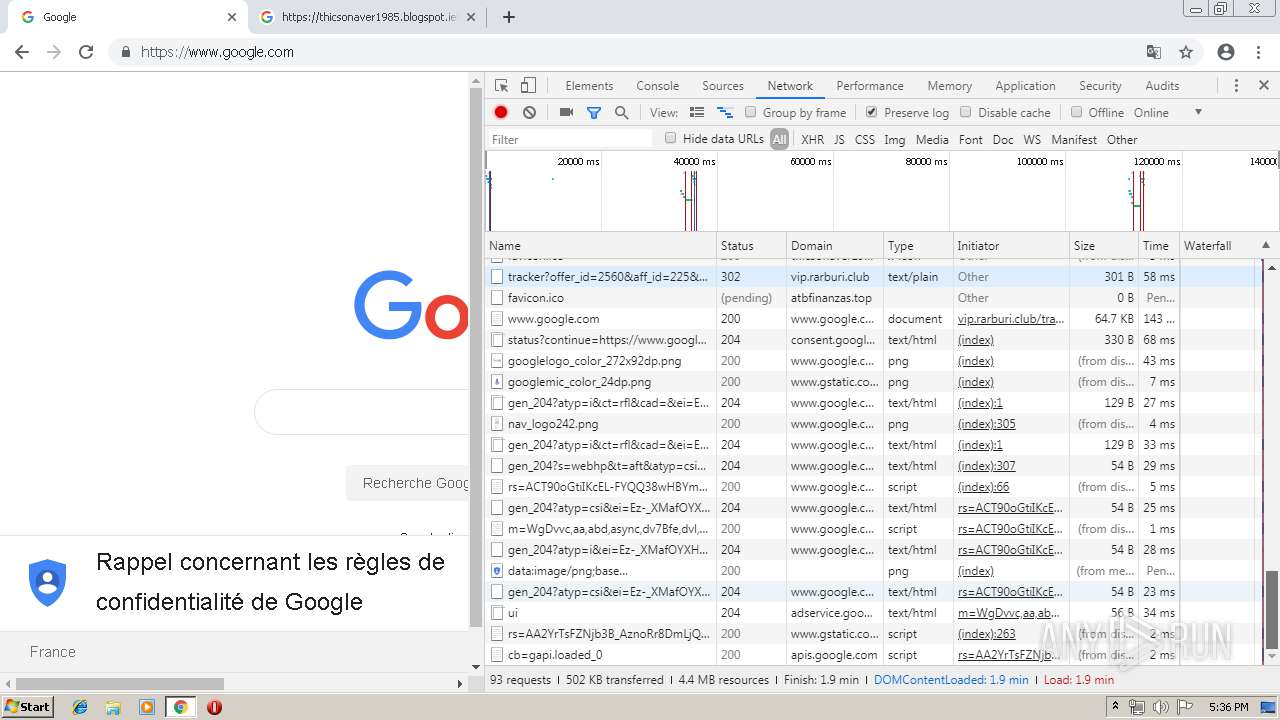
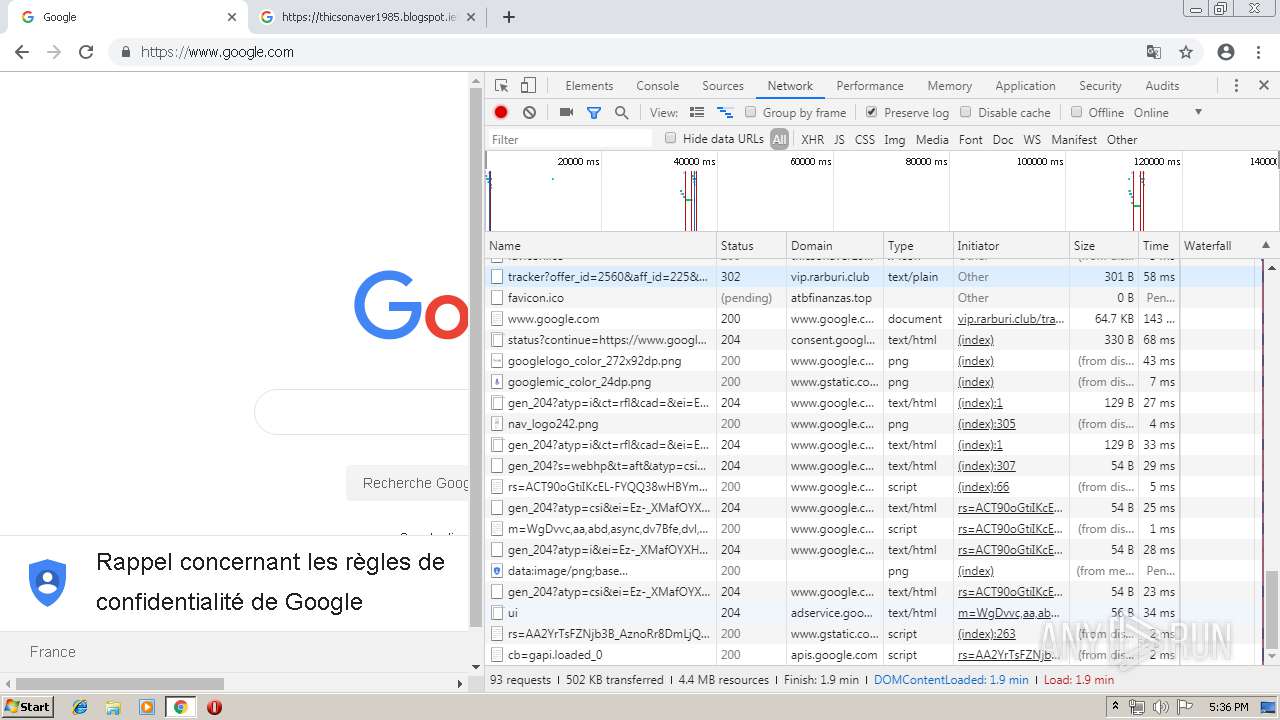
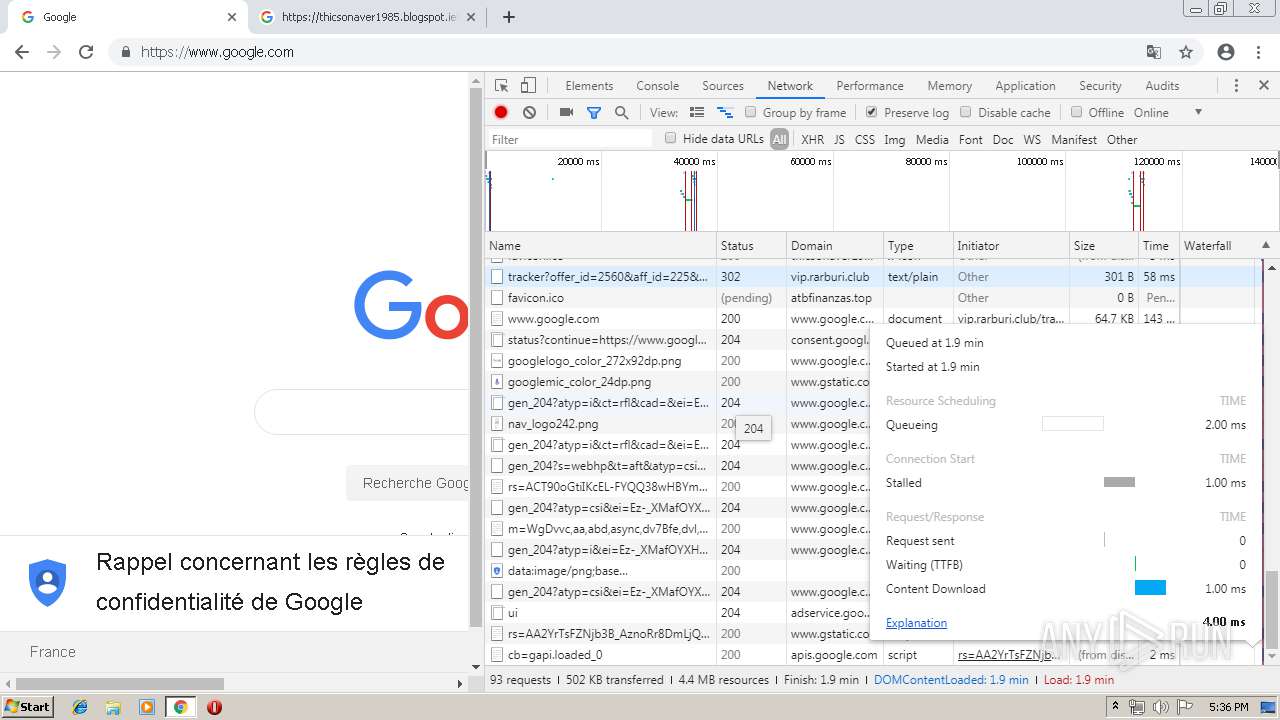
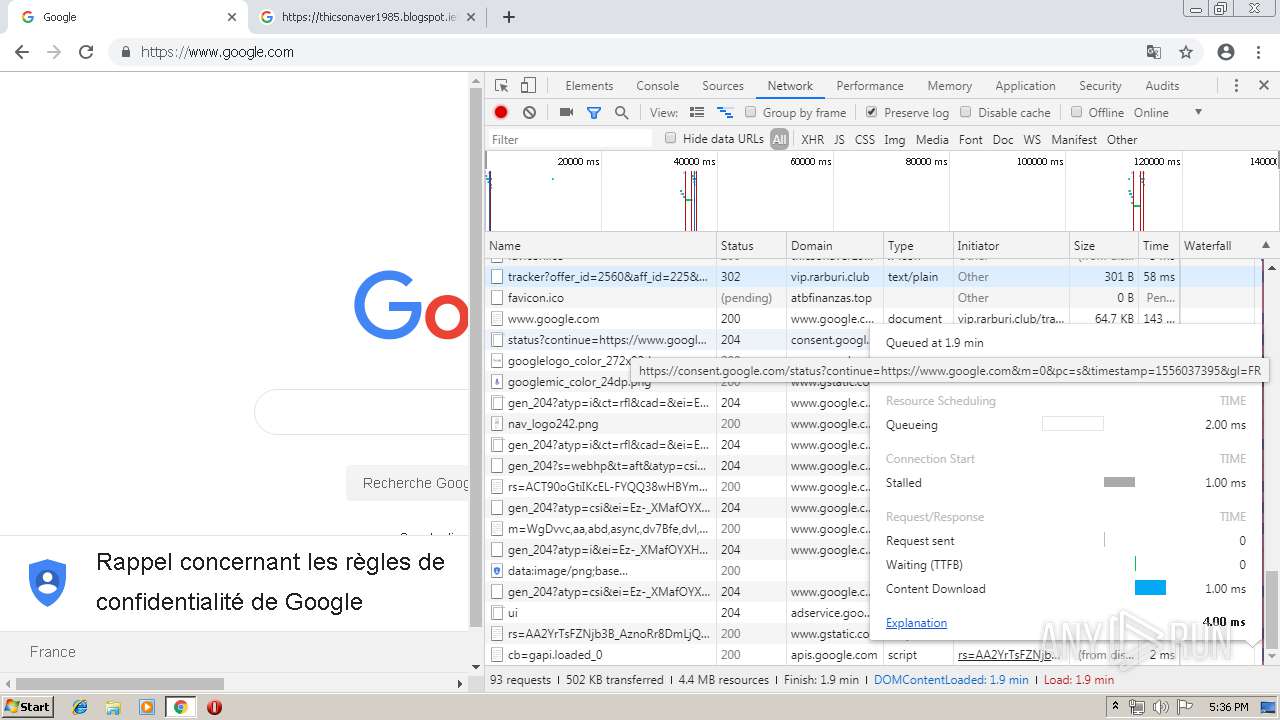
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
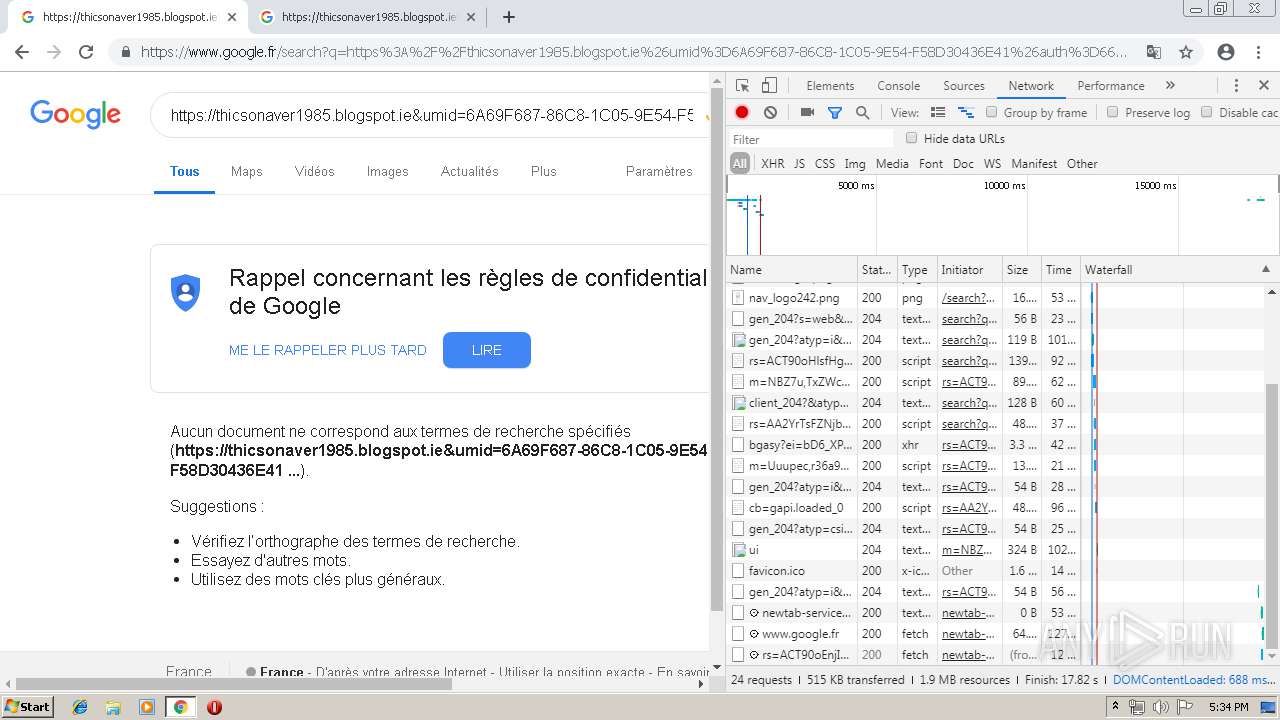
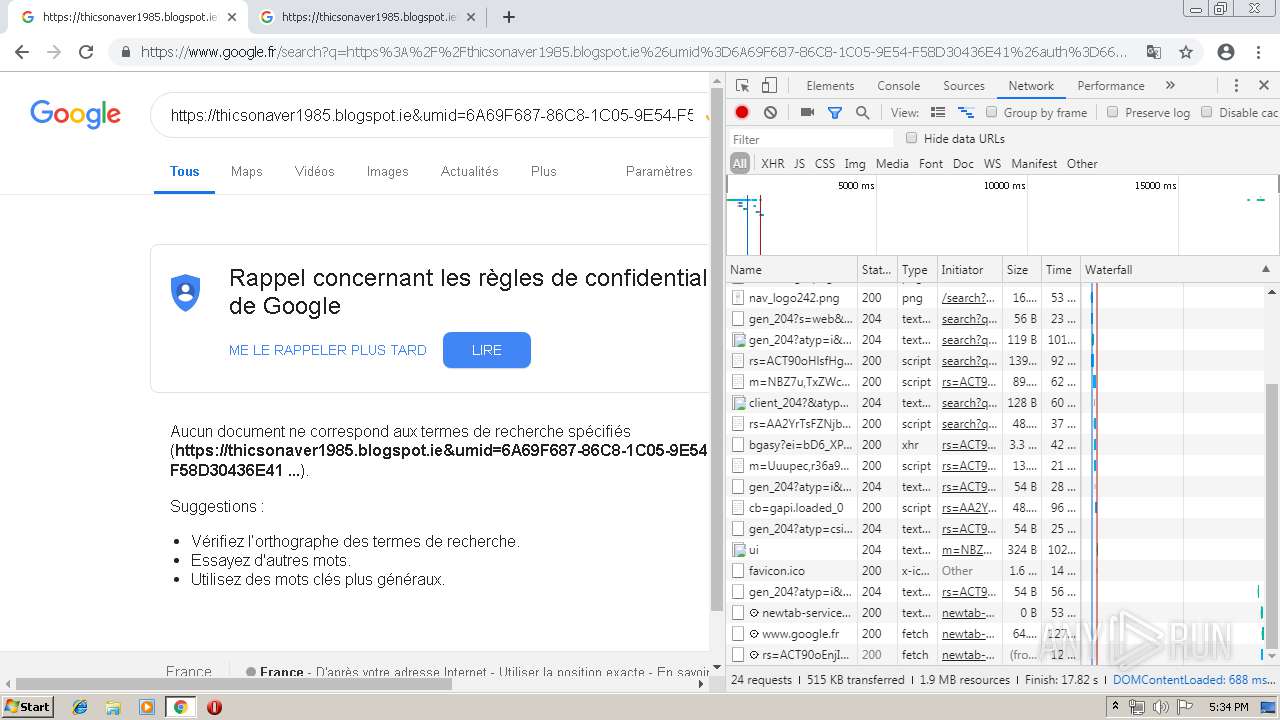
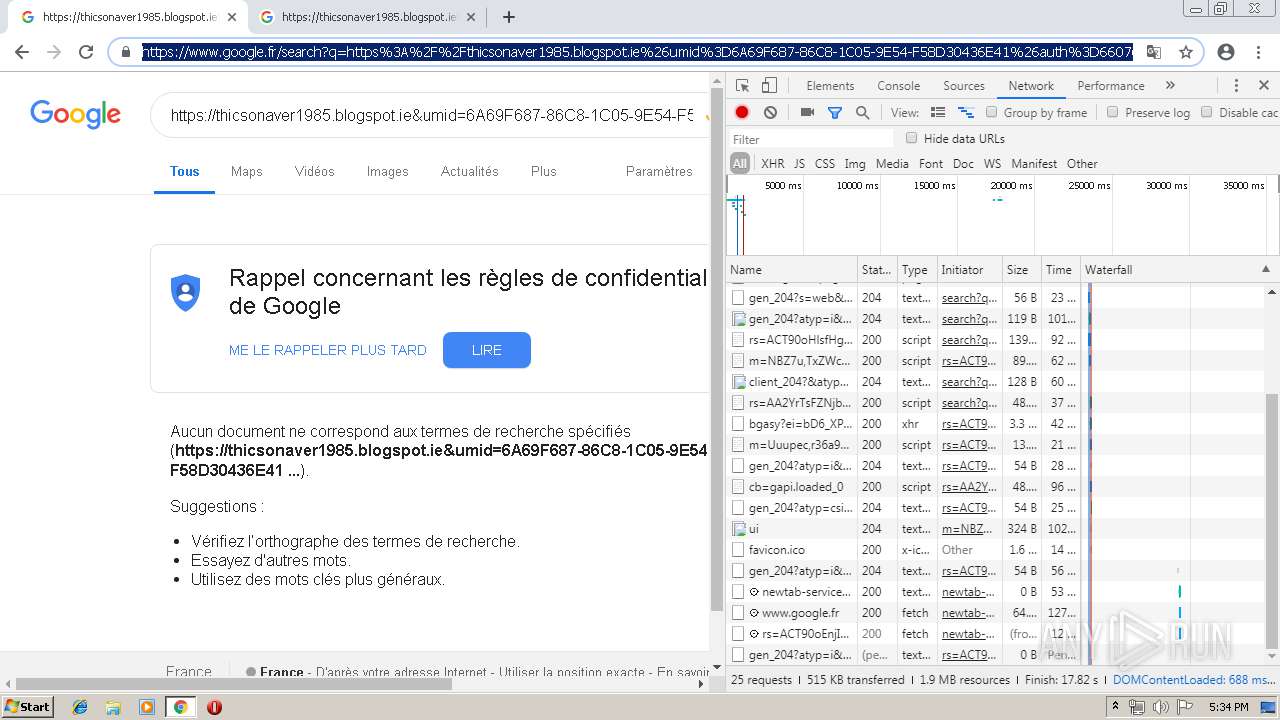
HTTP(S) requests
11
TCP/UDP connections
44
DNS requests
35
Threats
7
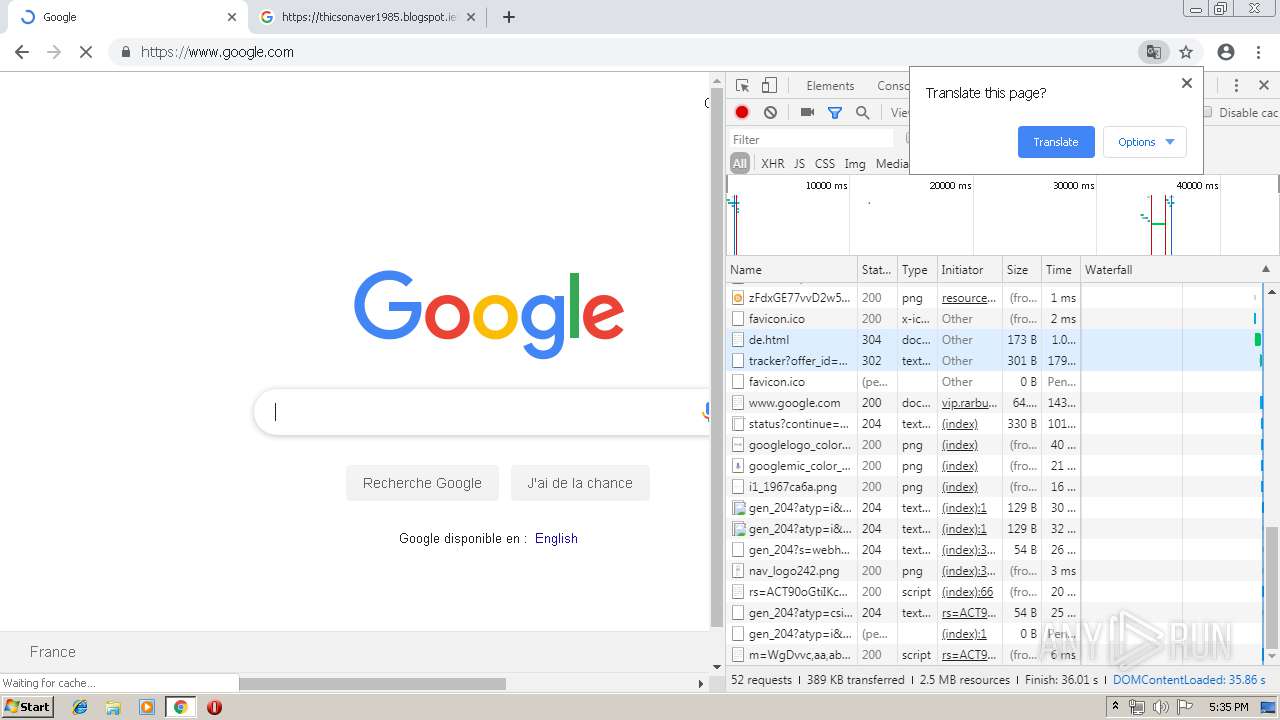
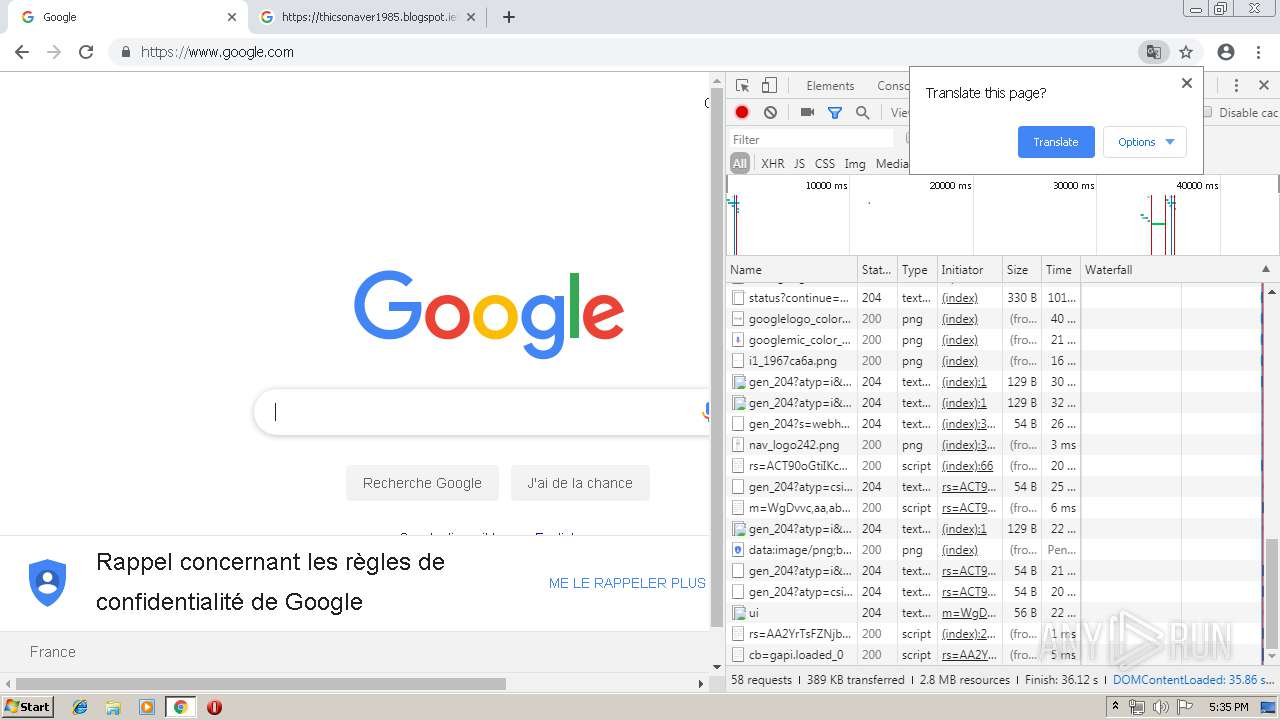
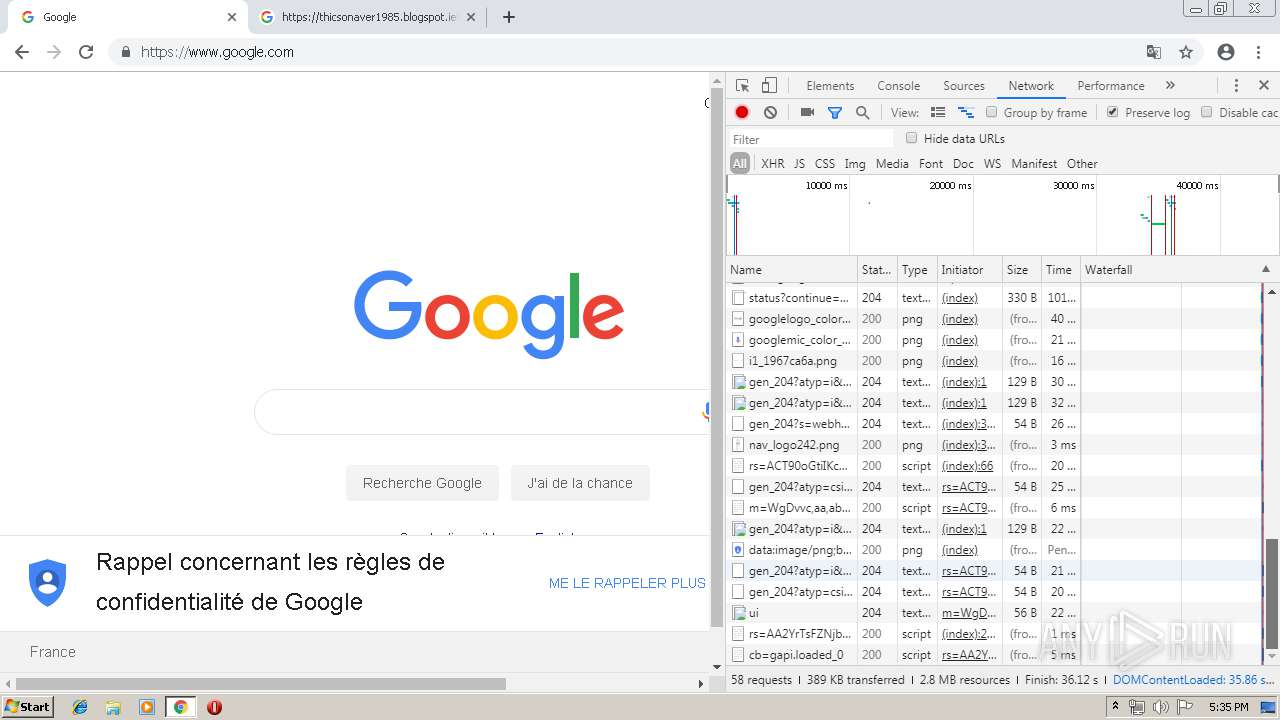
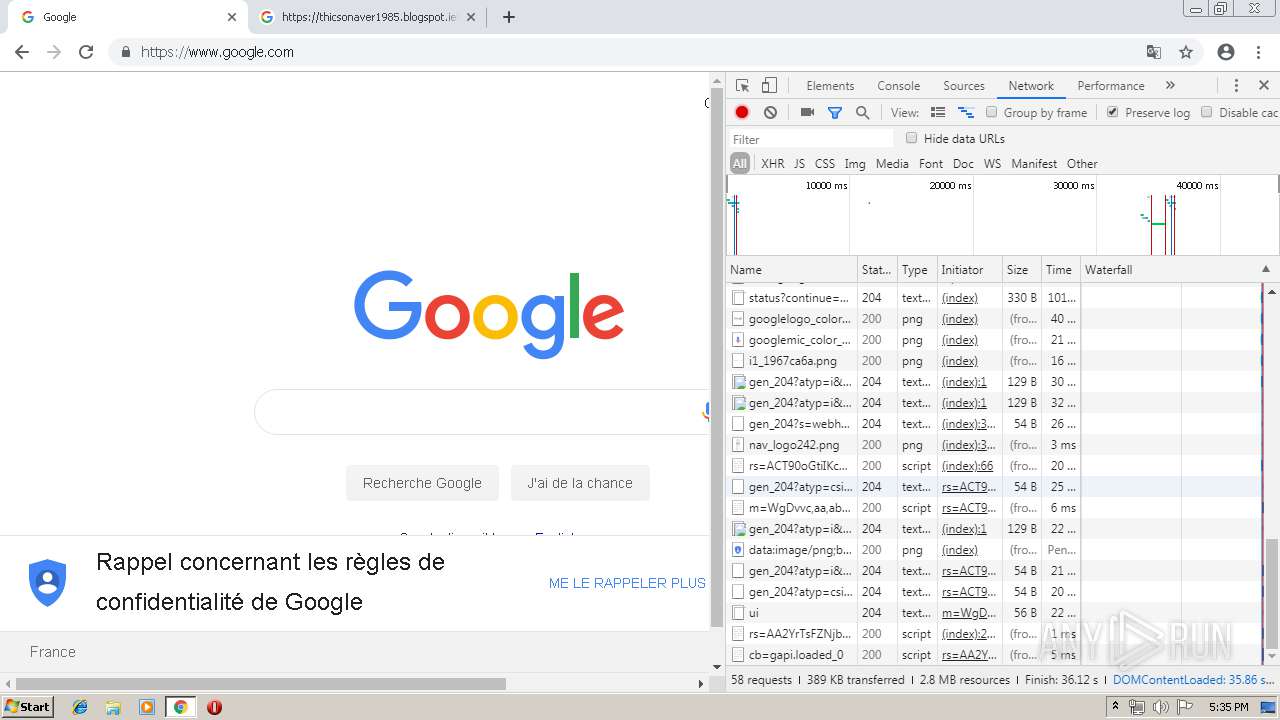
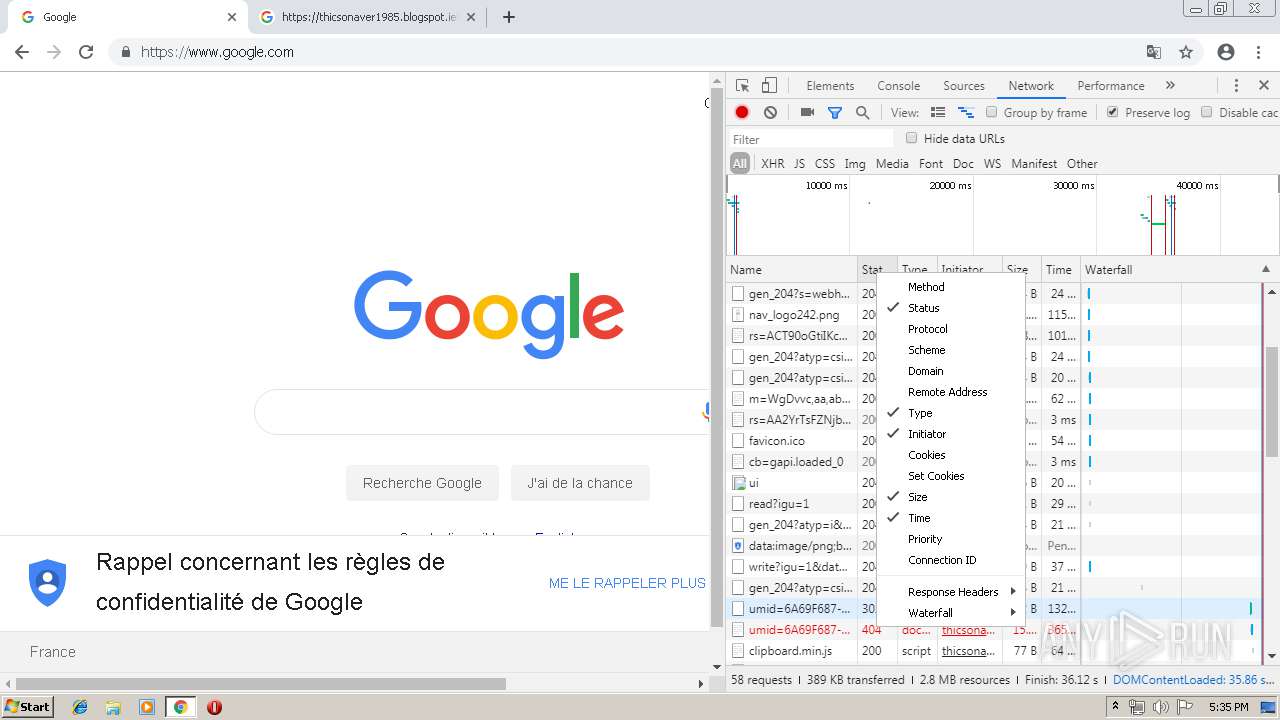
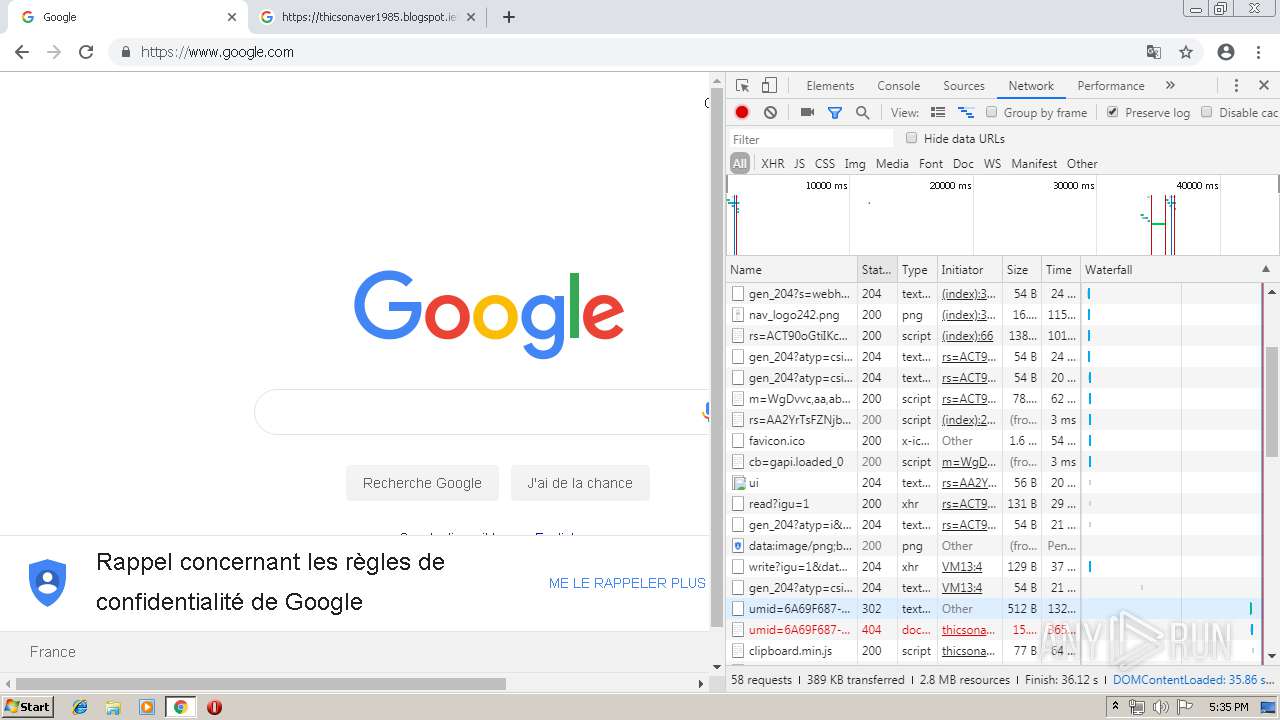
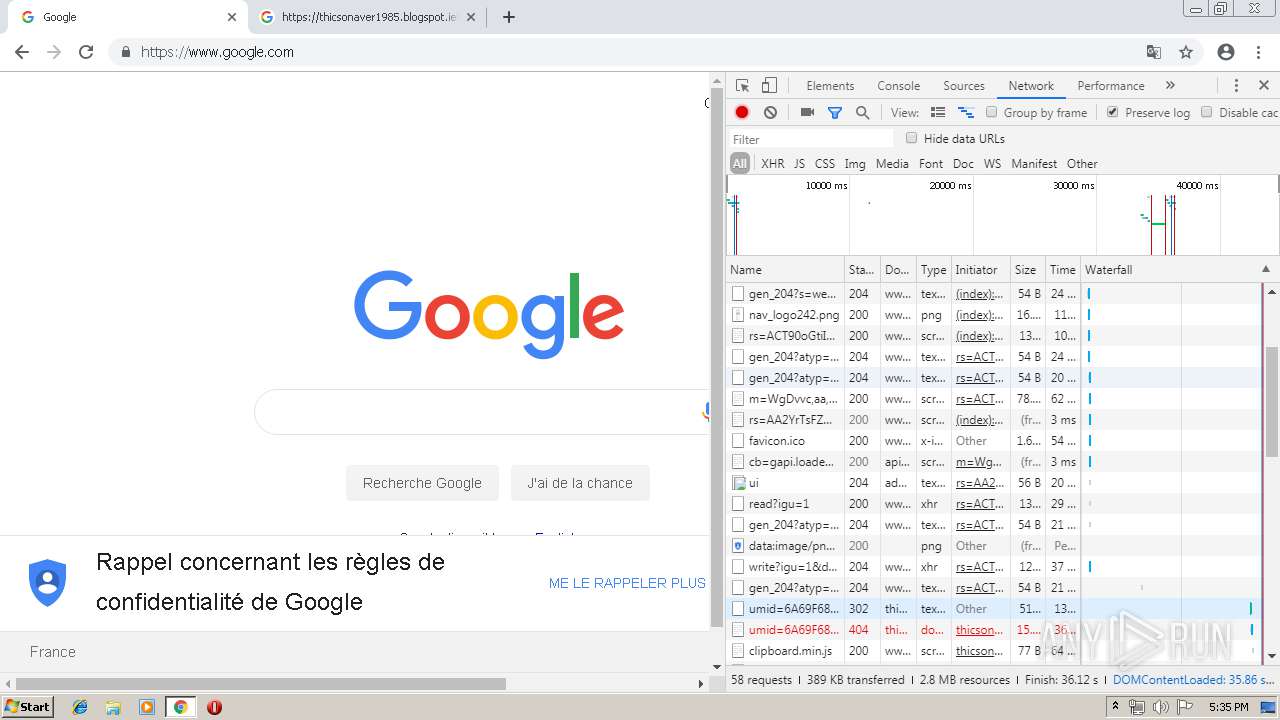
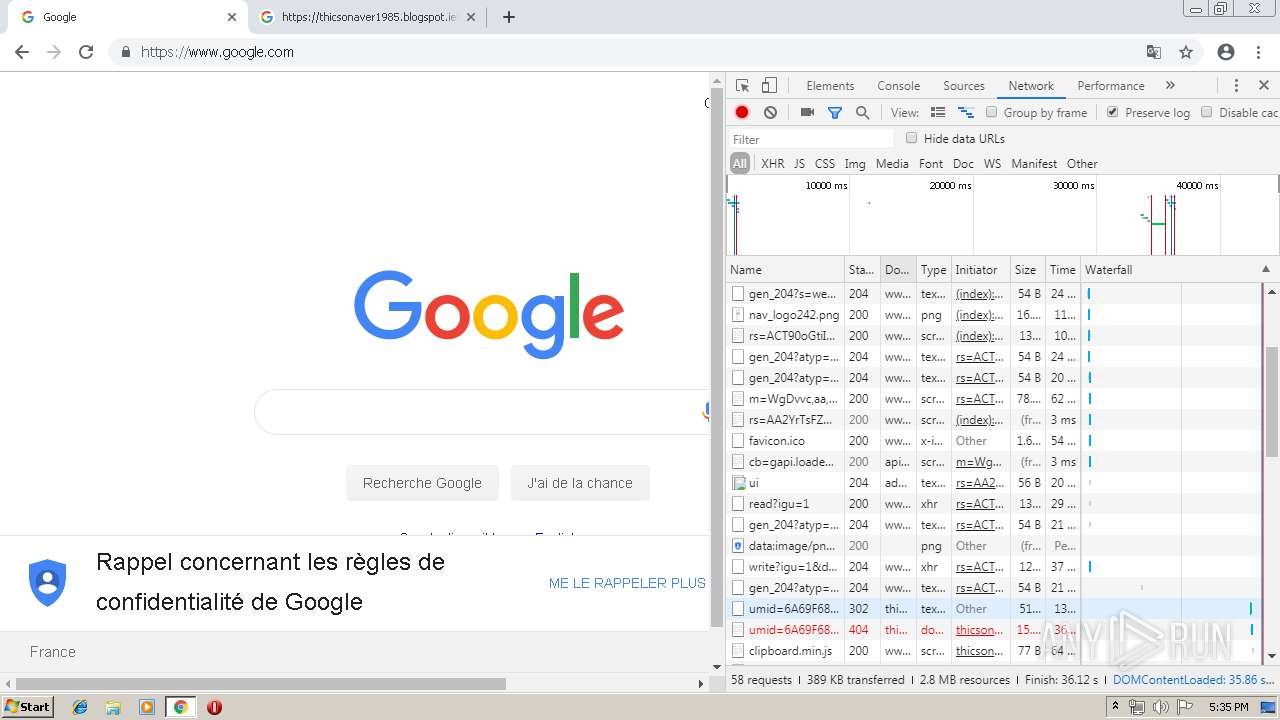
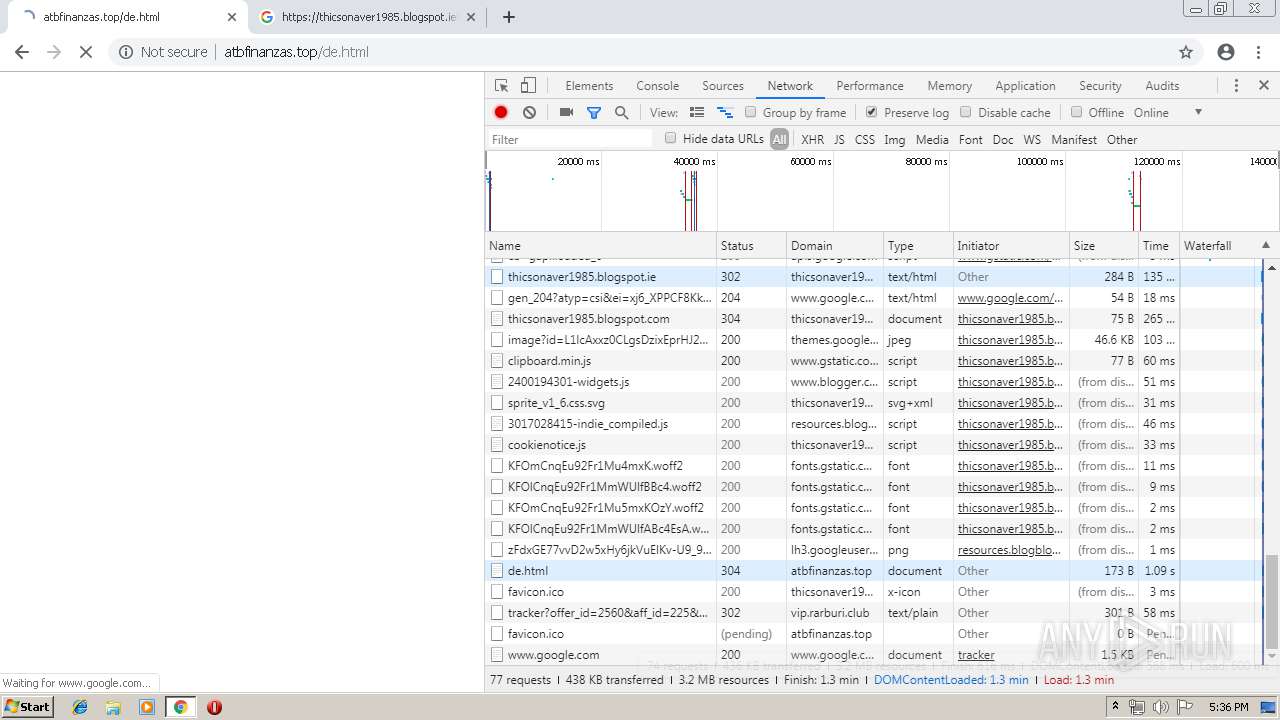
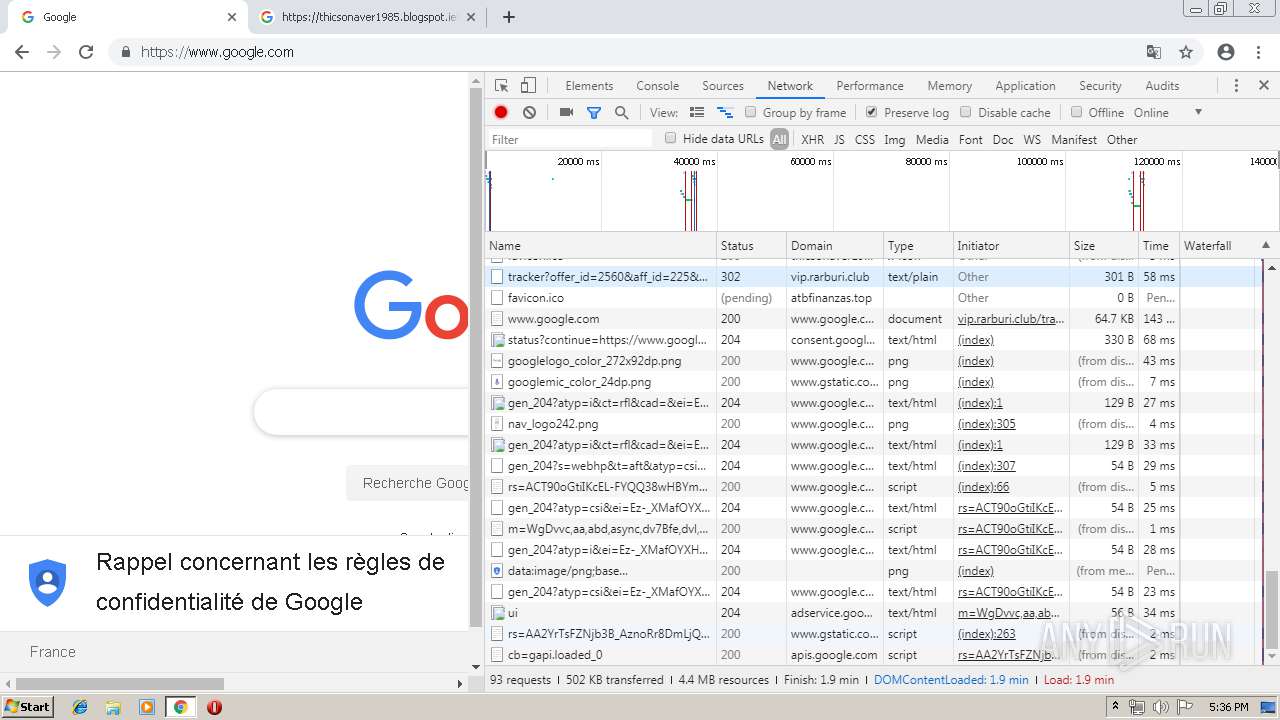
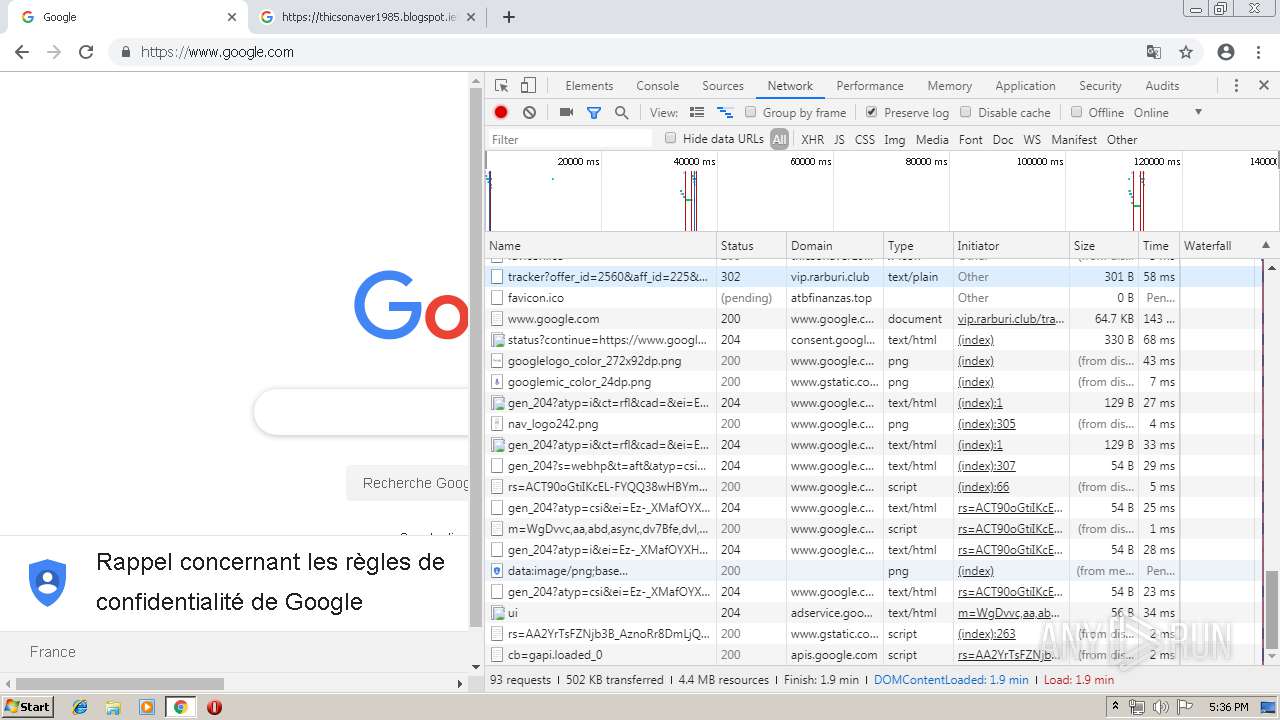
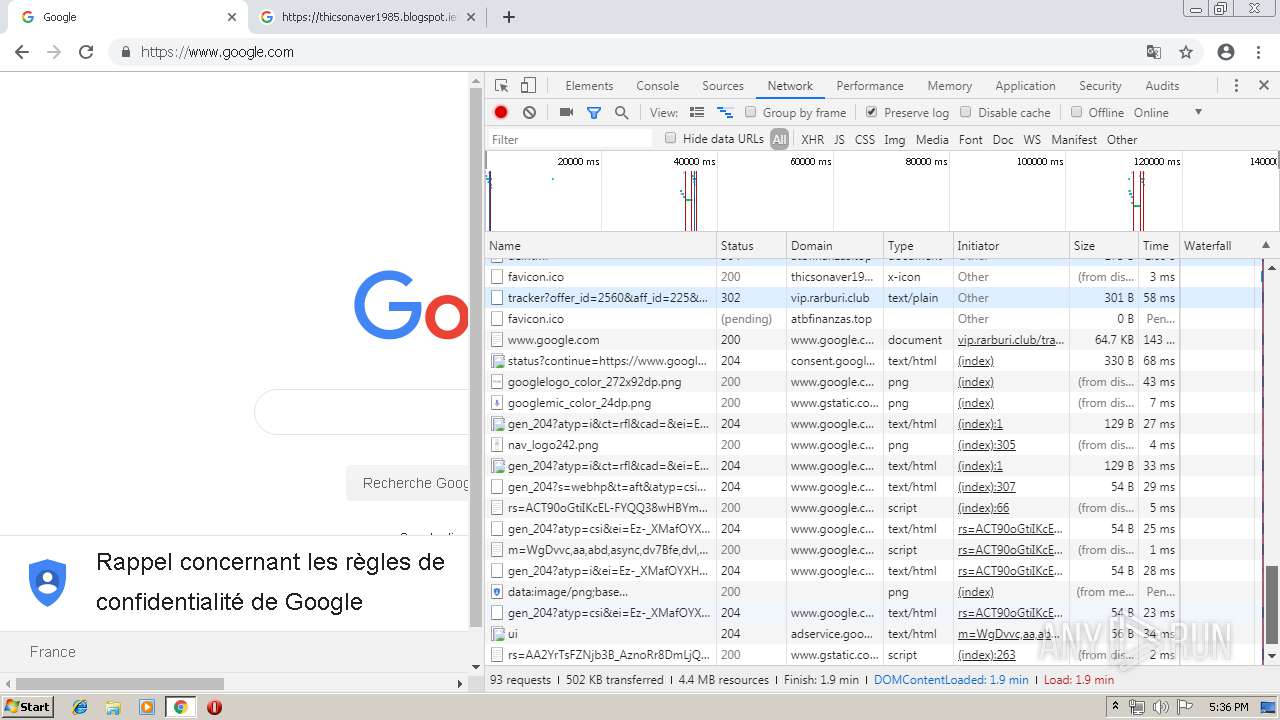
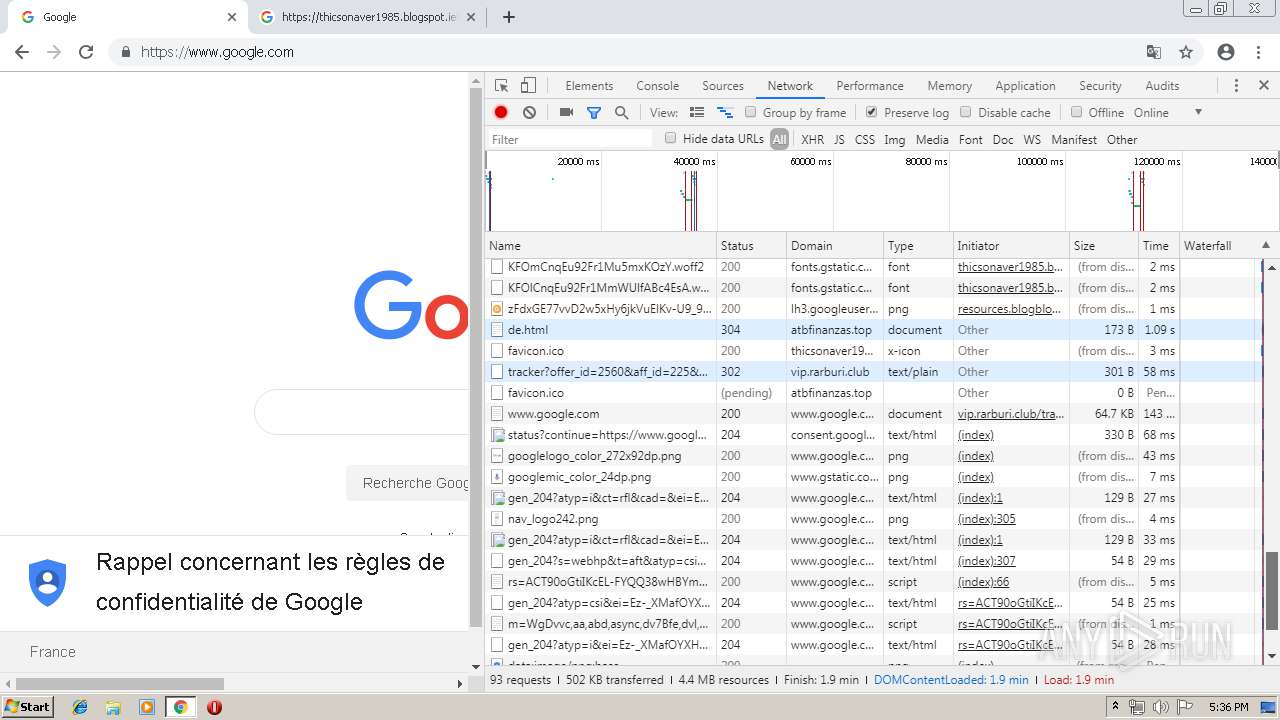
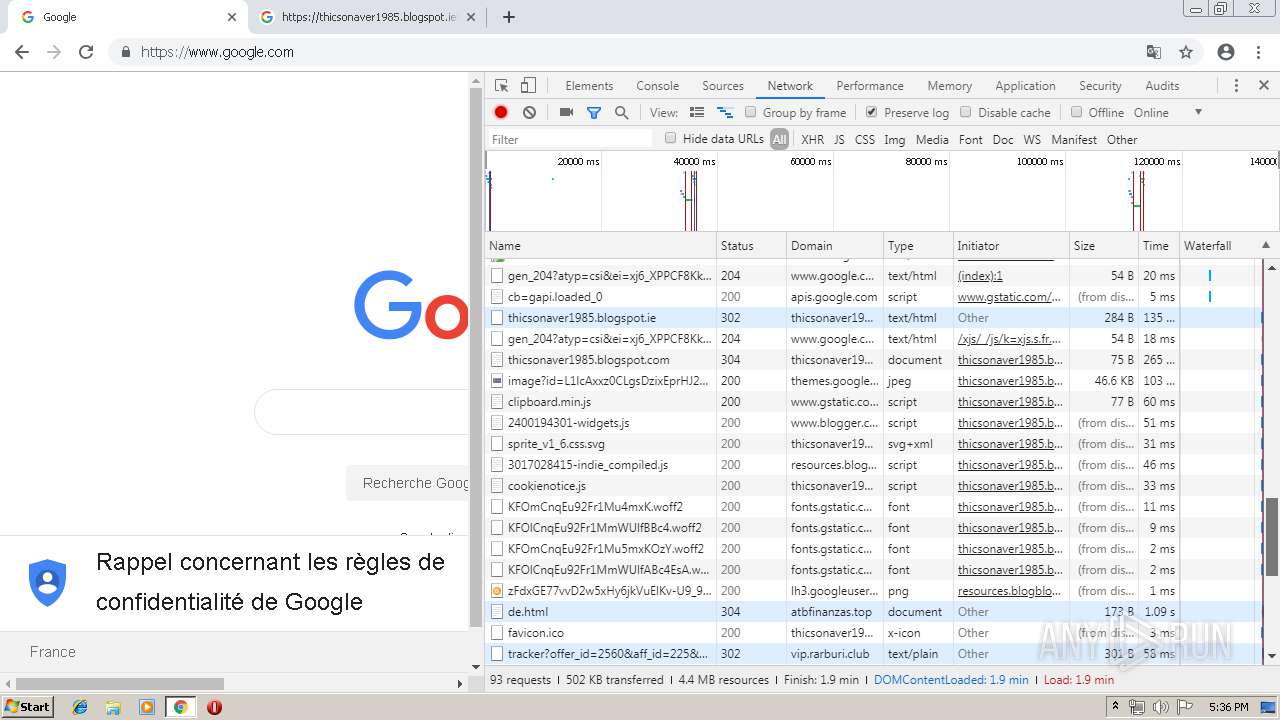
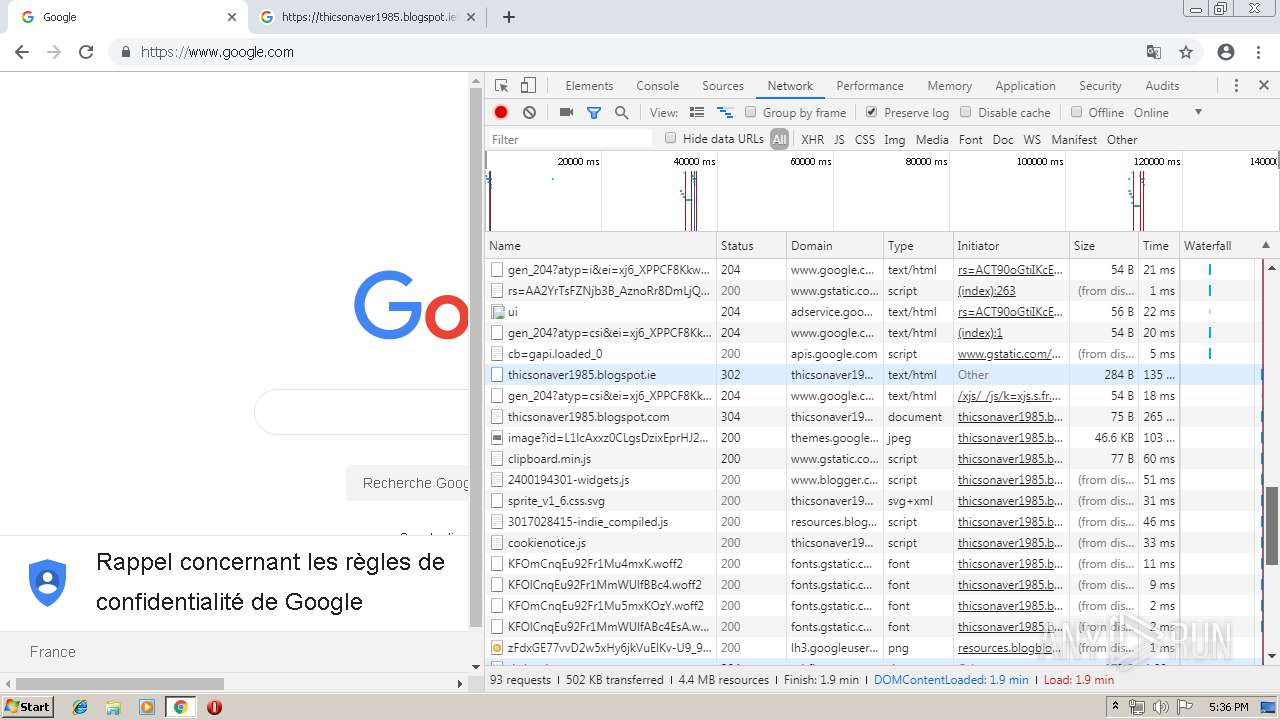
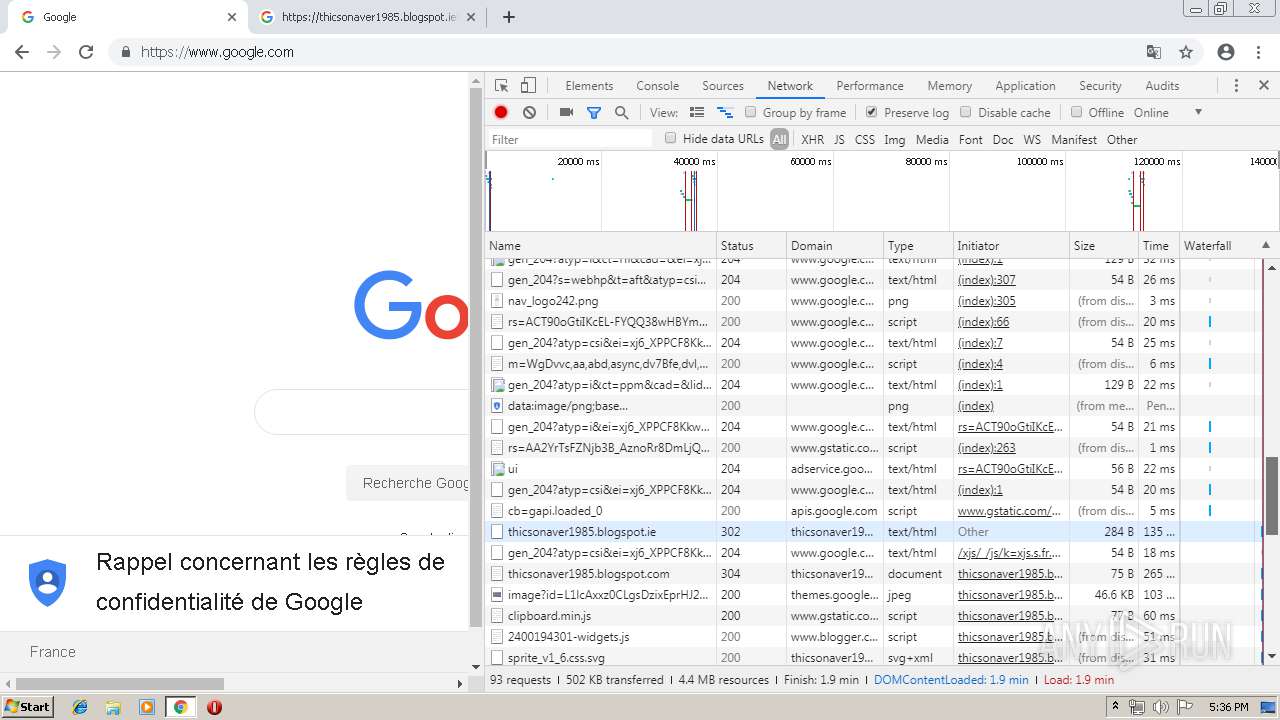
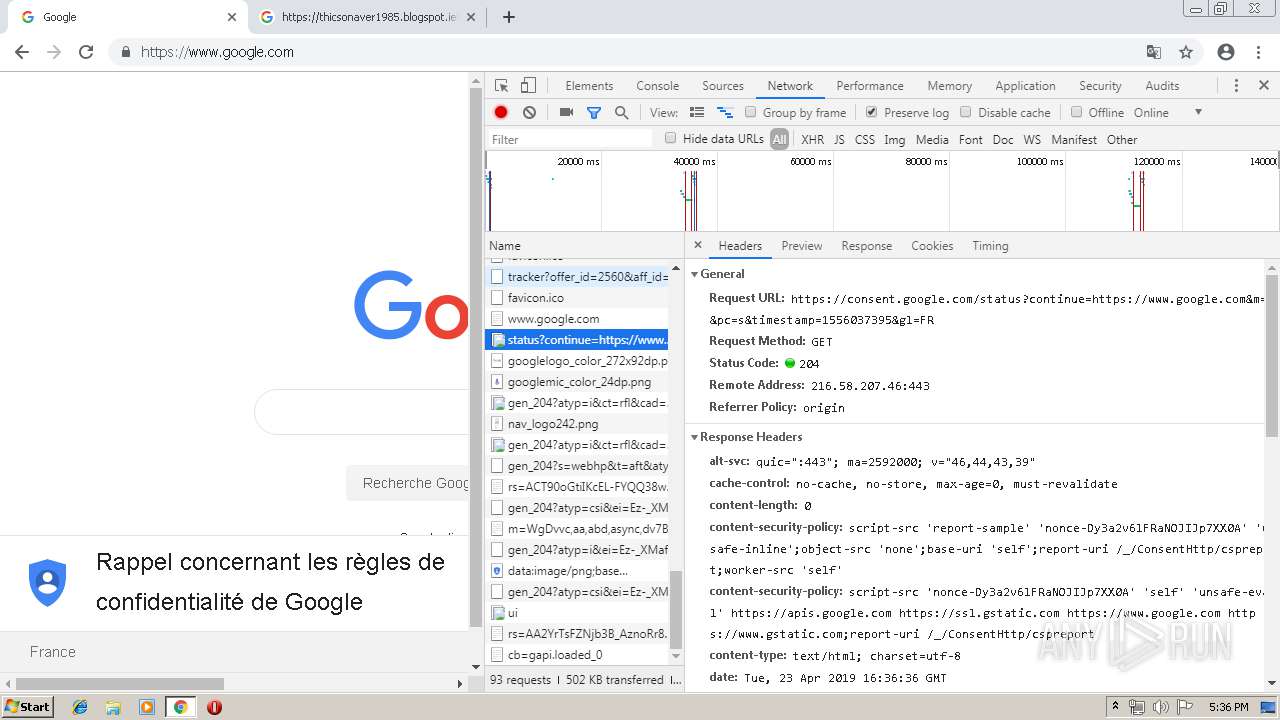
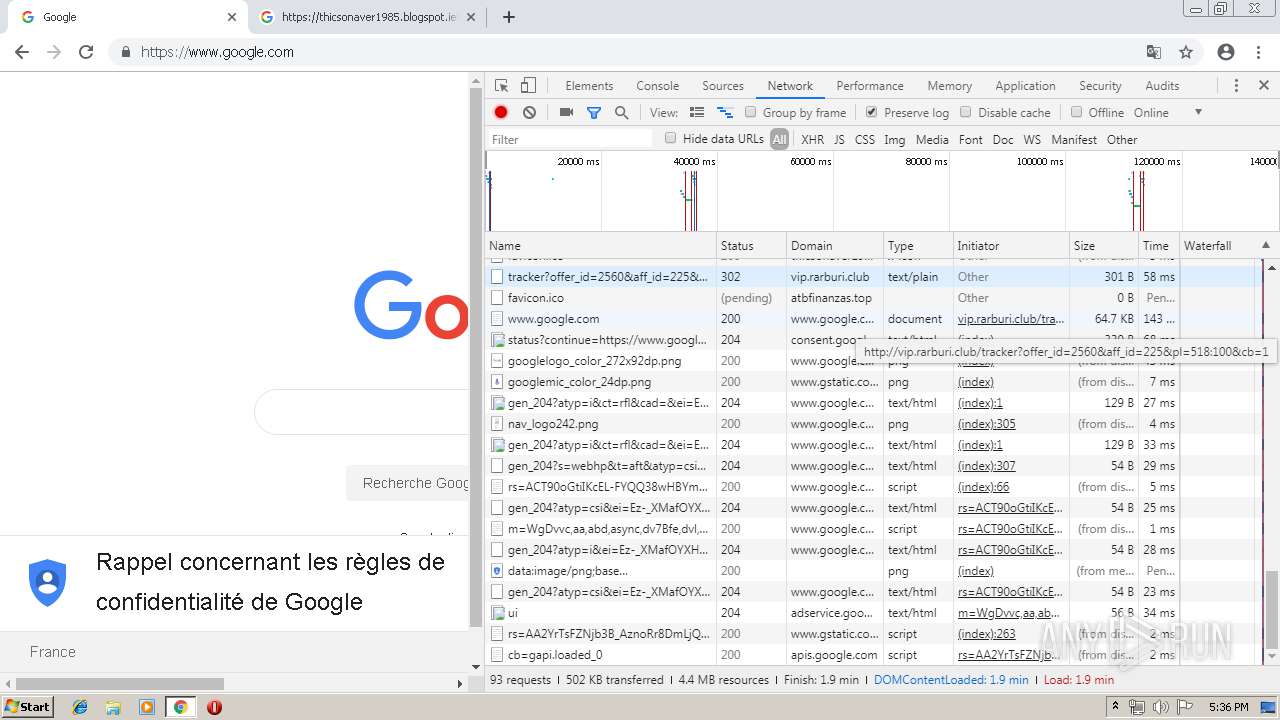
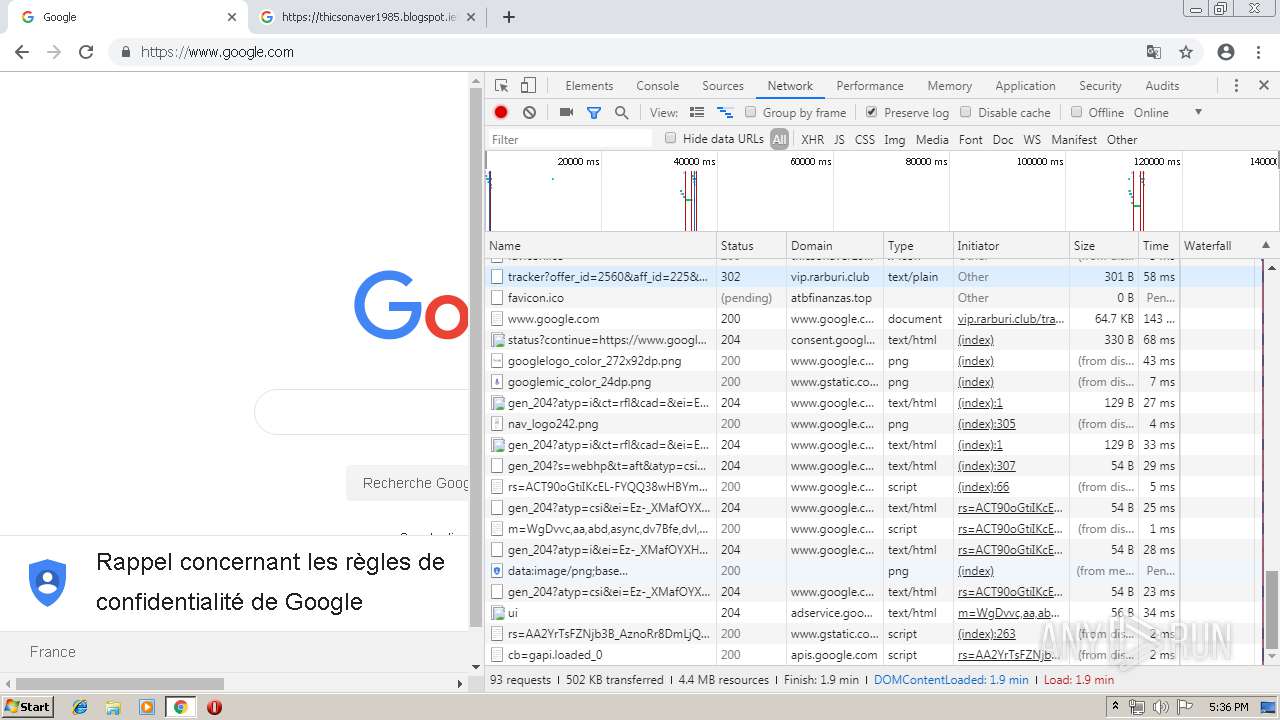
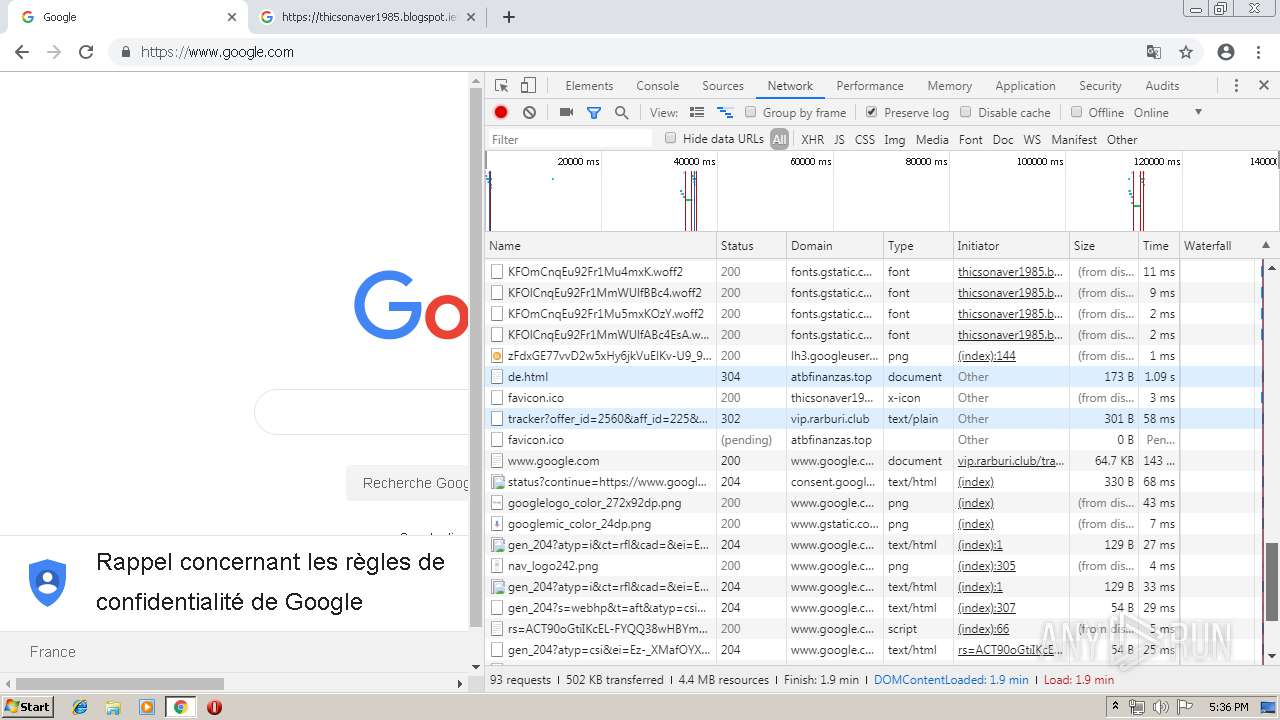
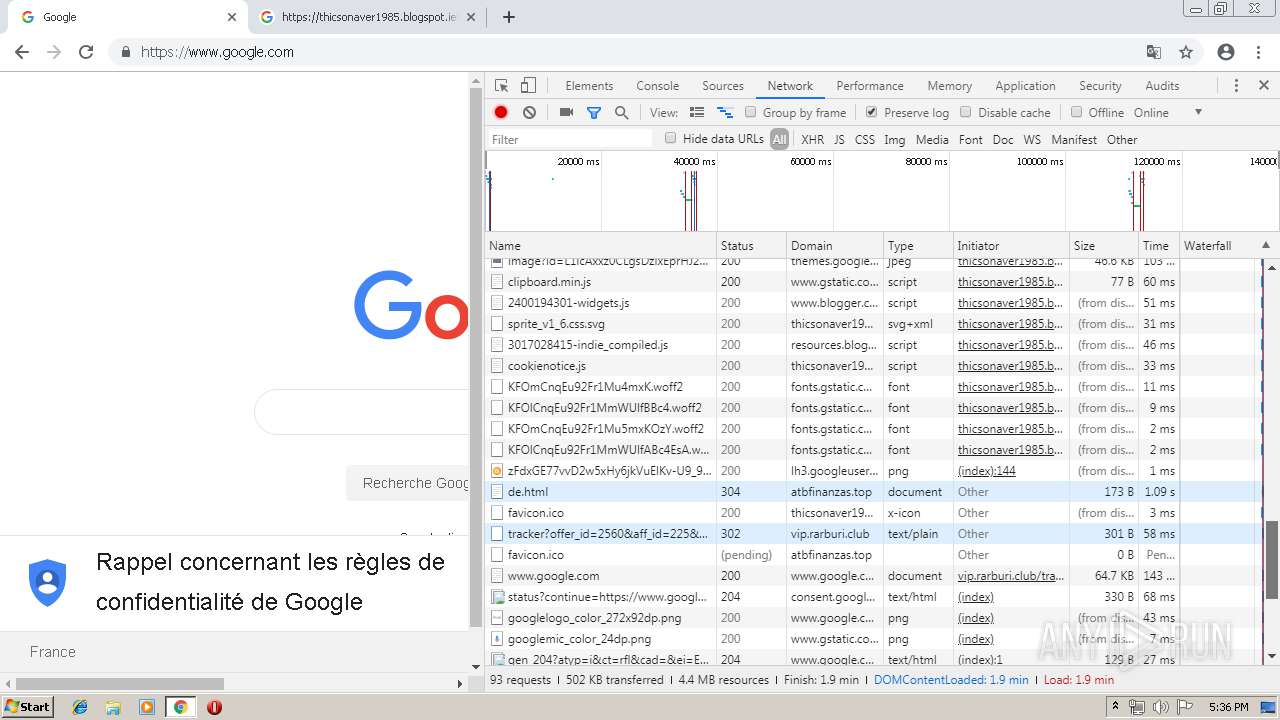
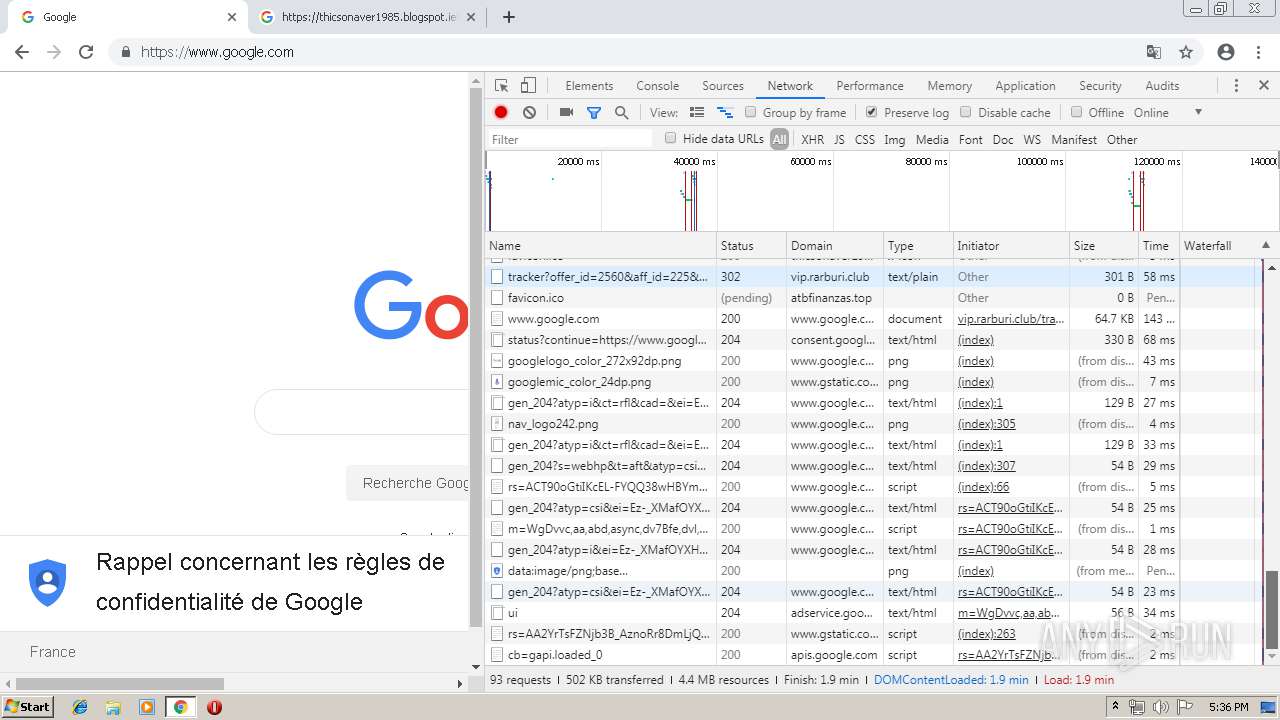
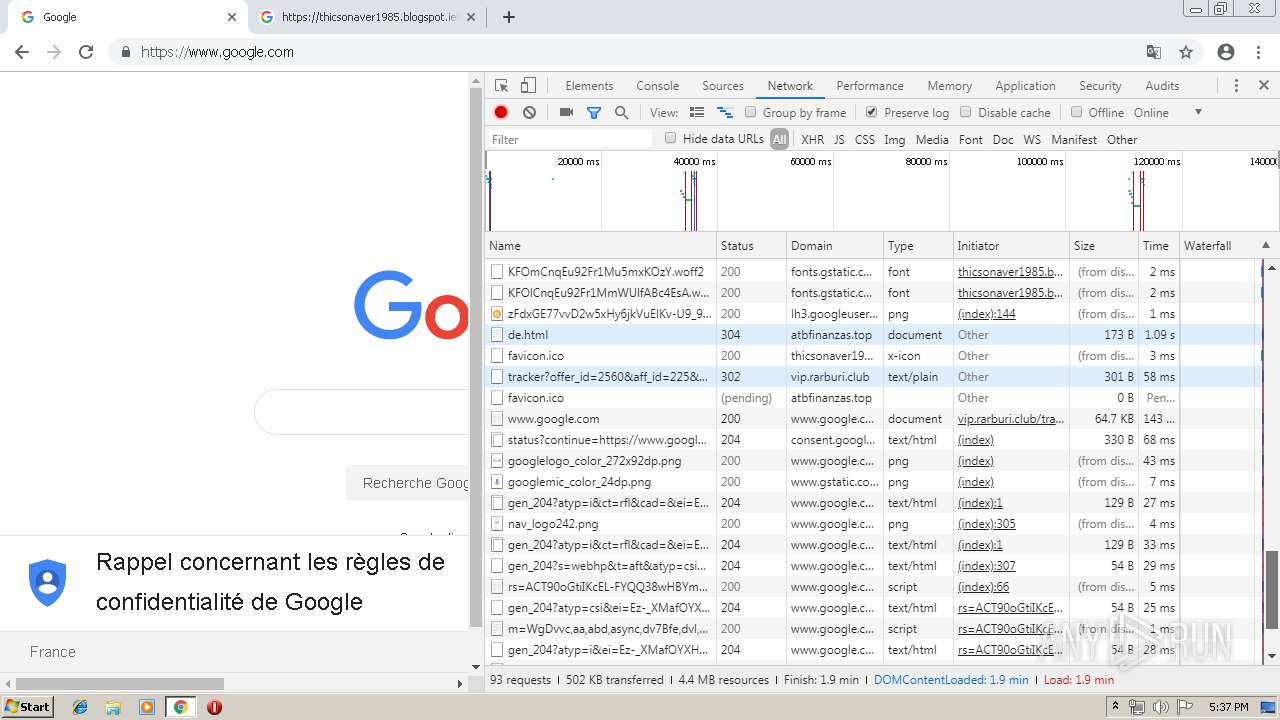
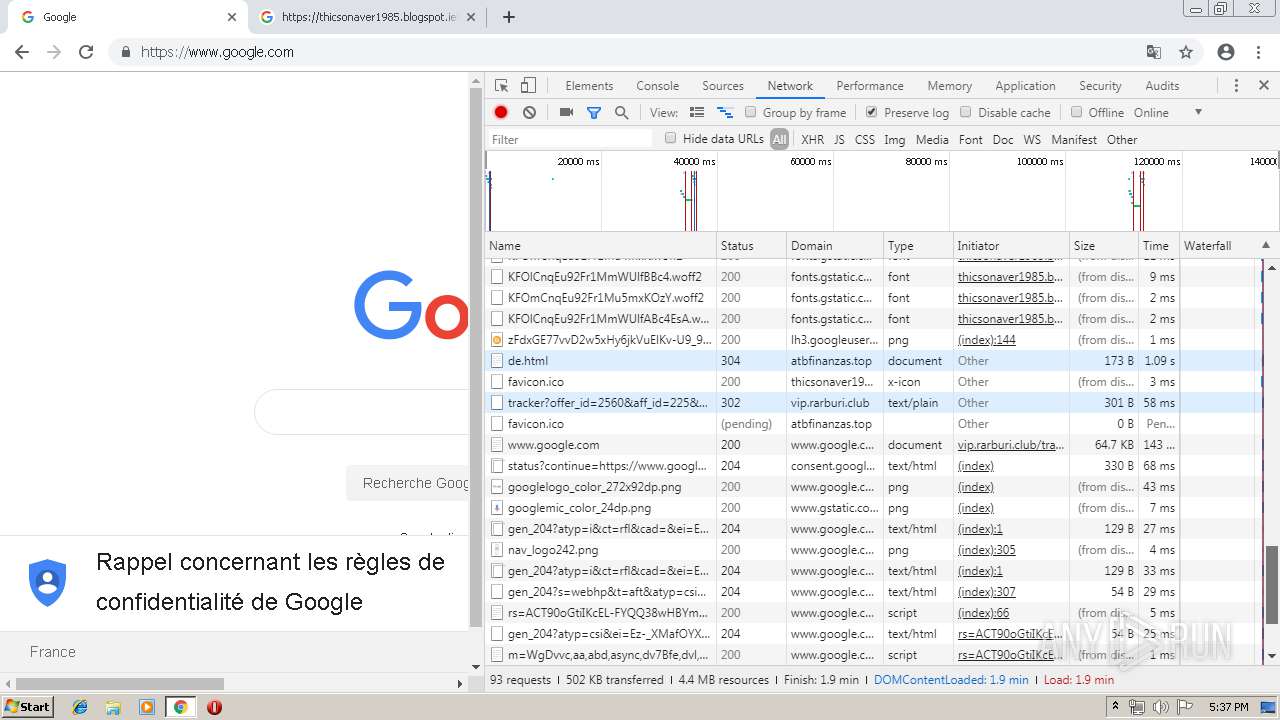
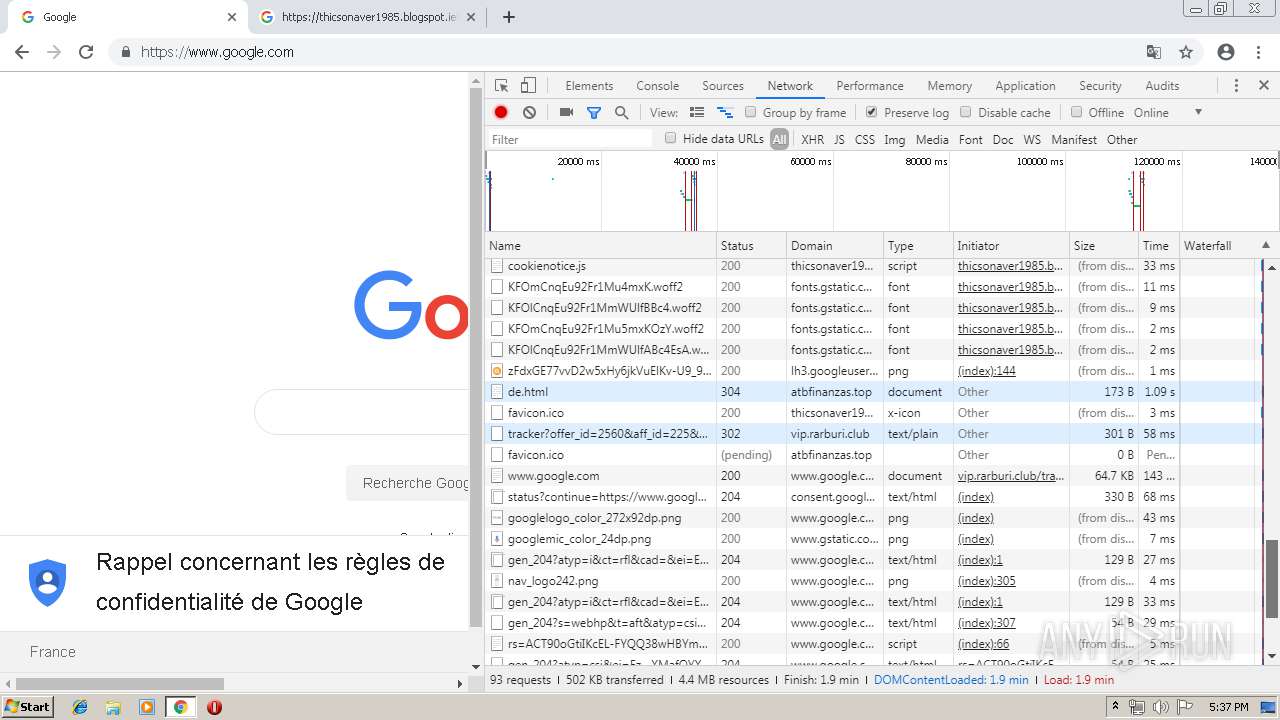
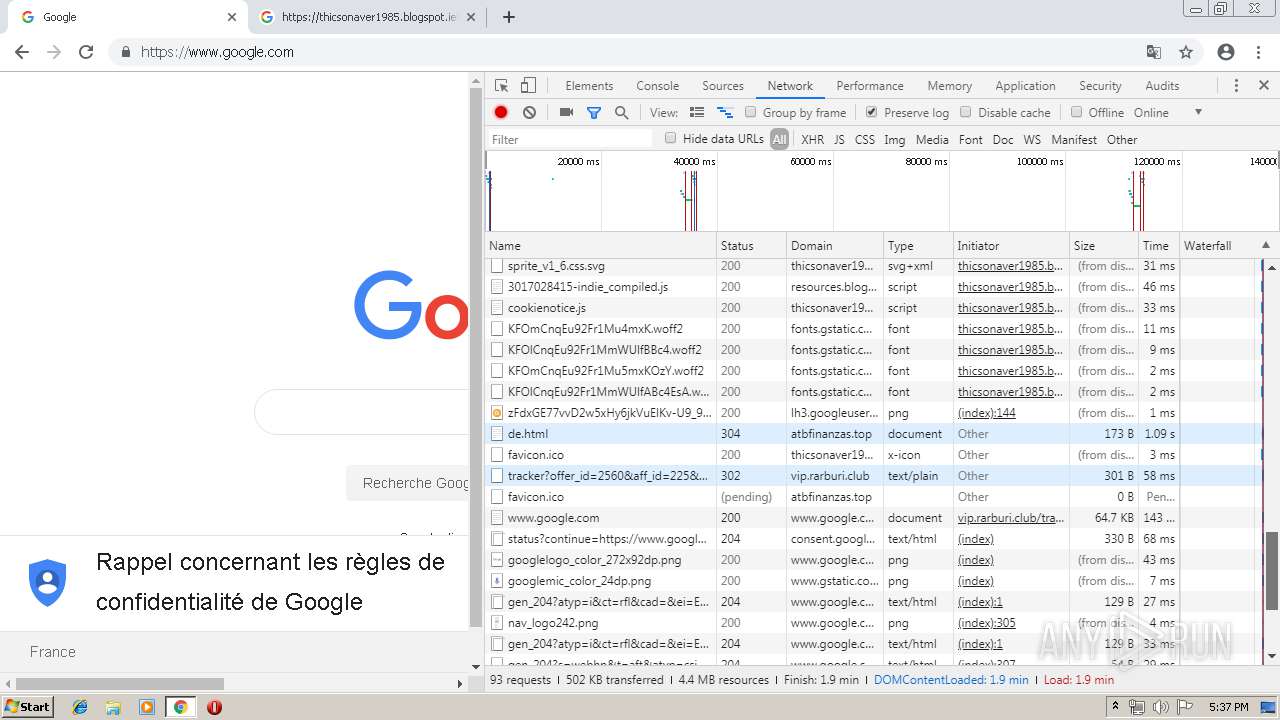
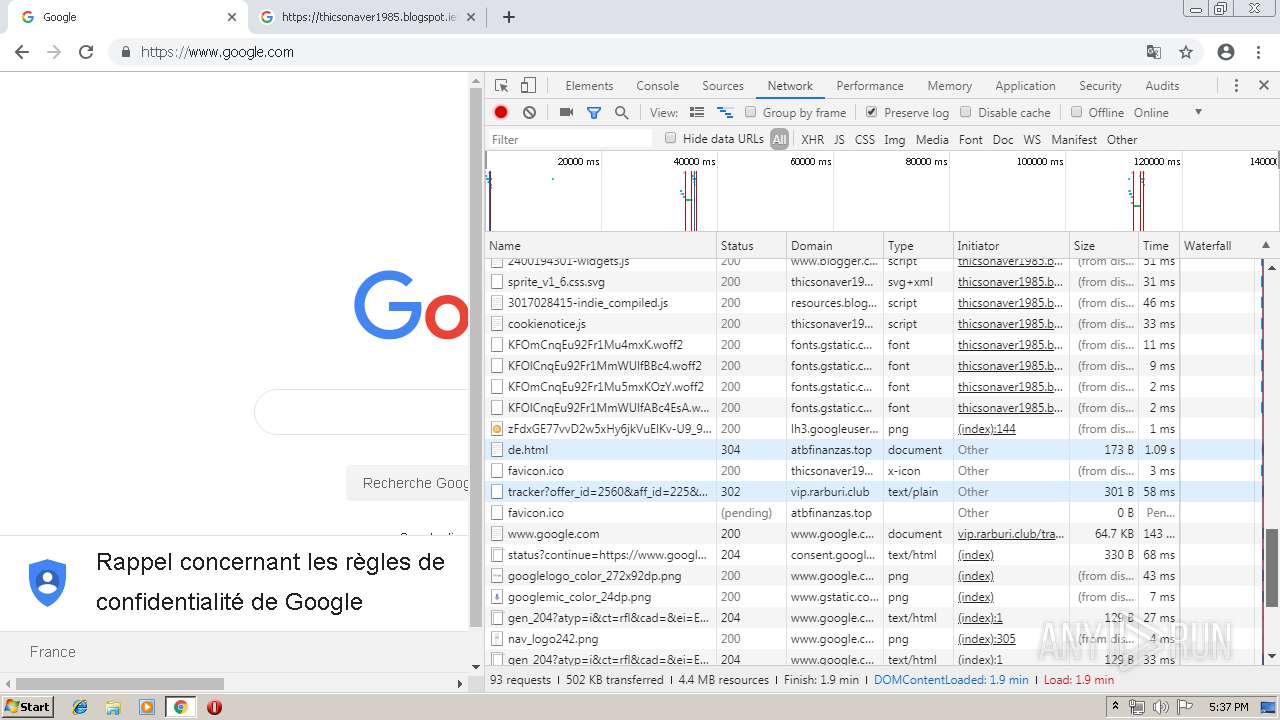
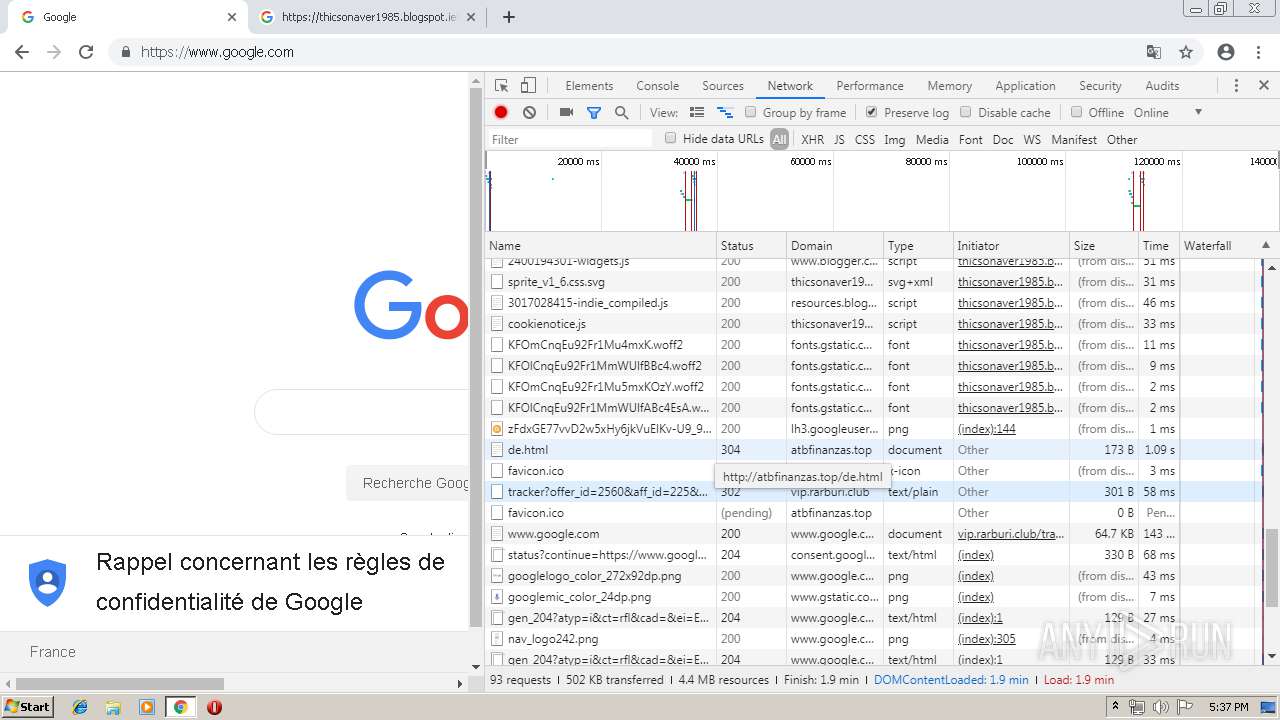
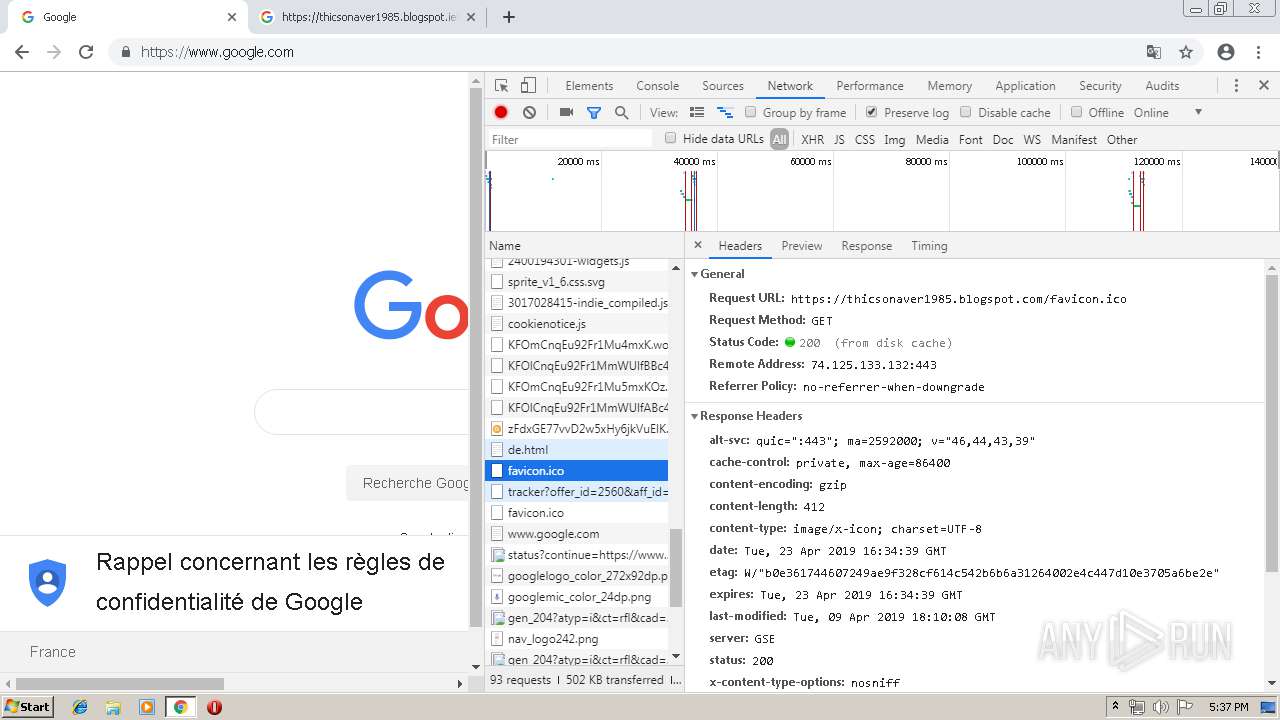
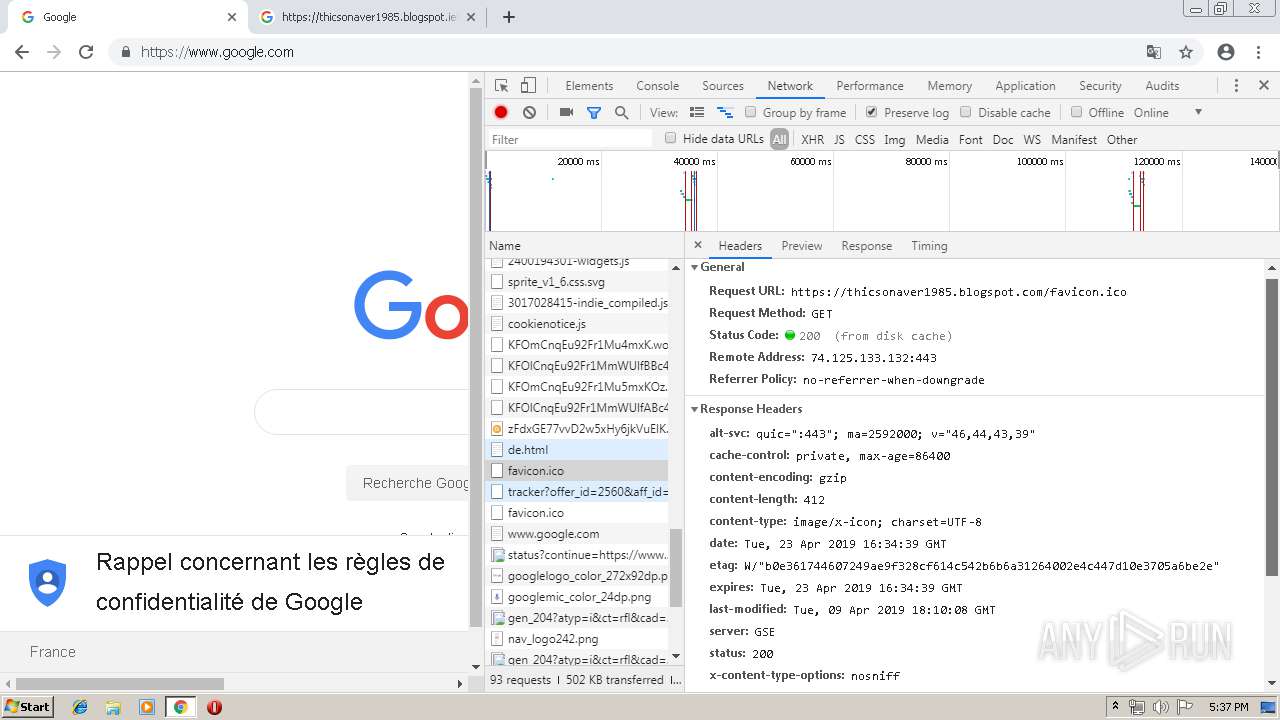
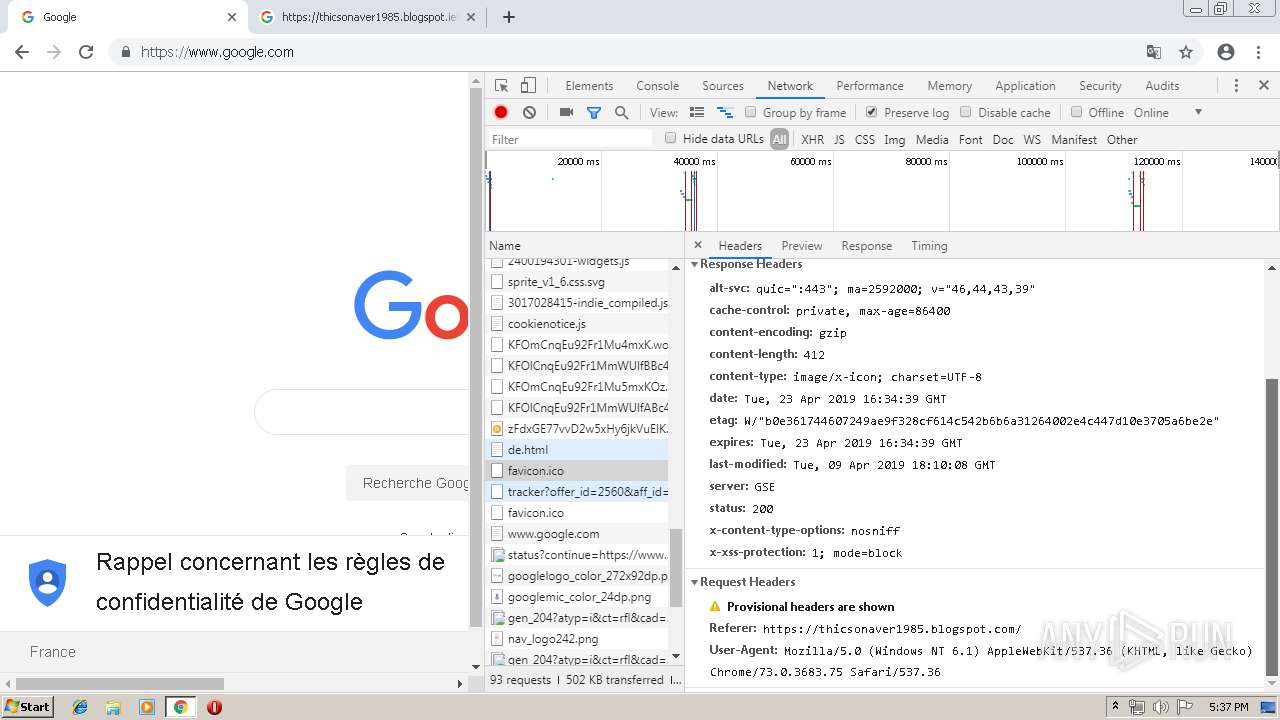
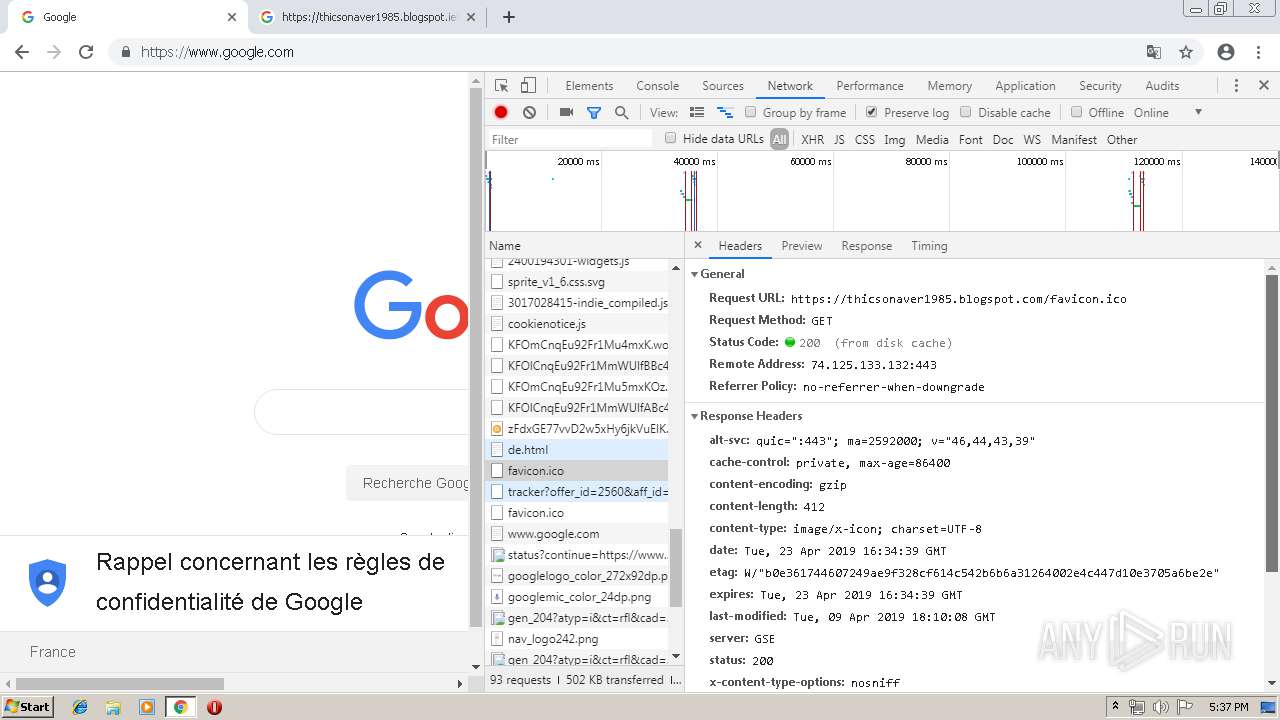
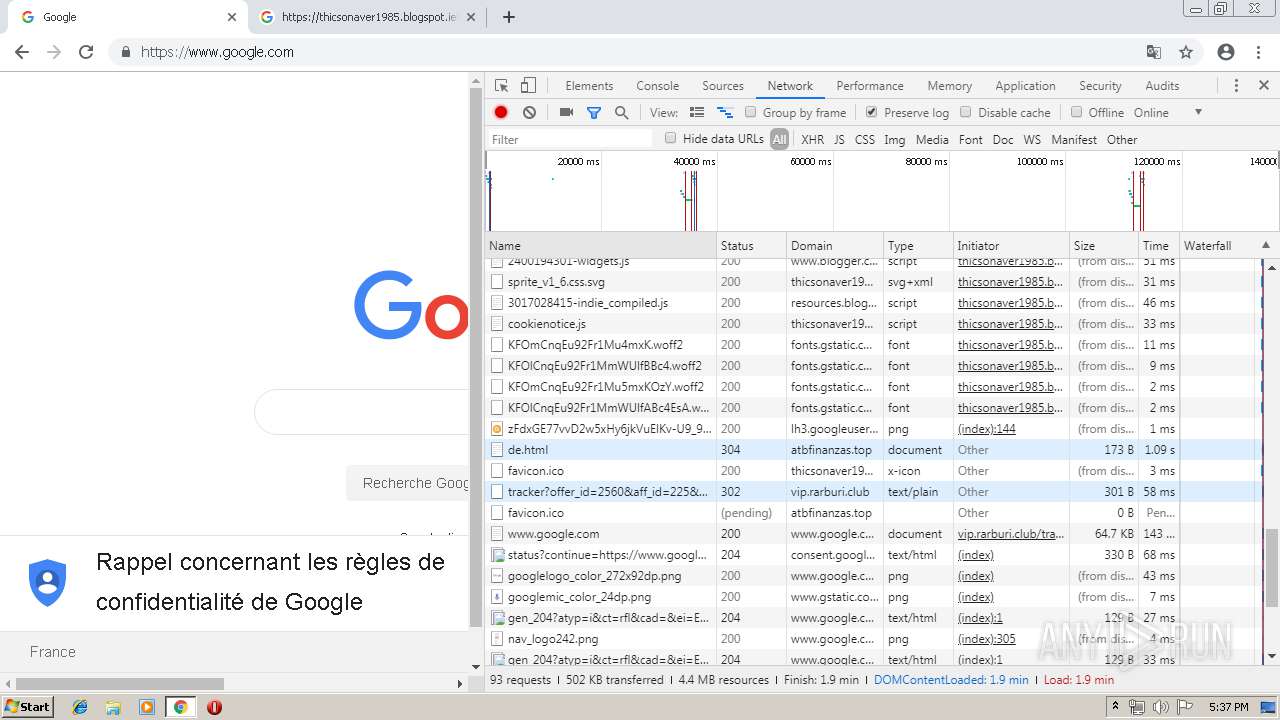
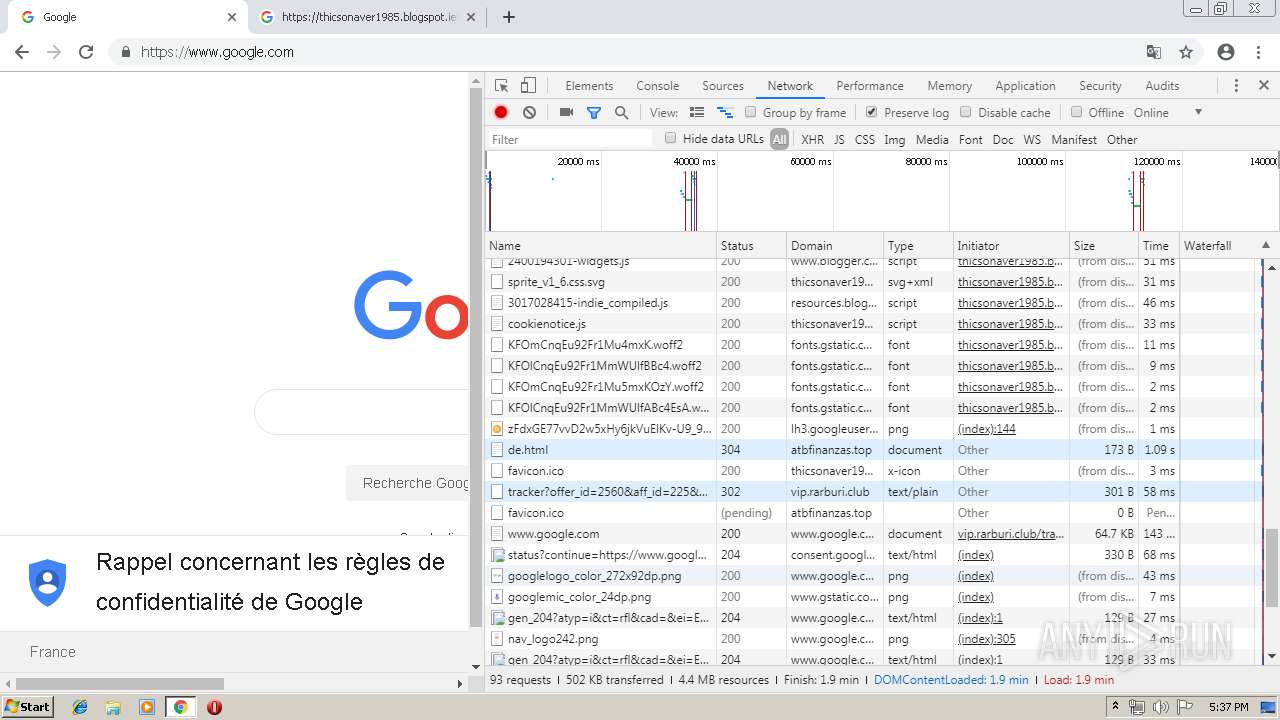
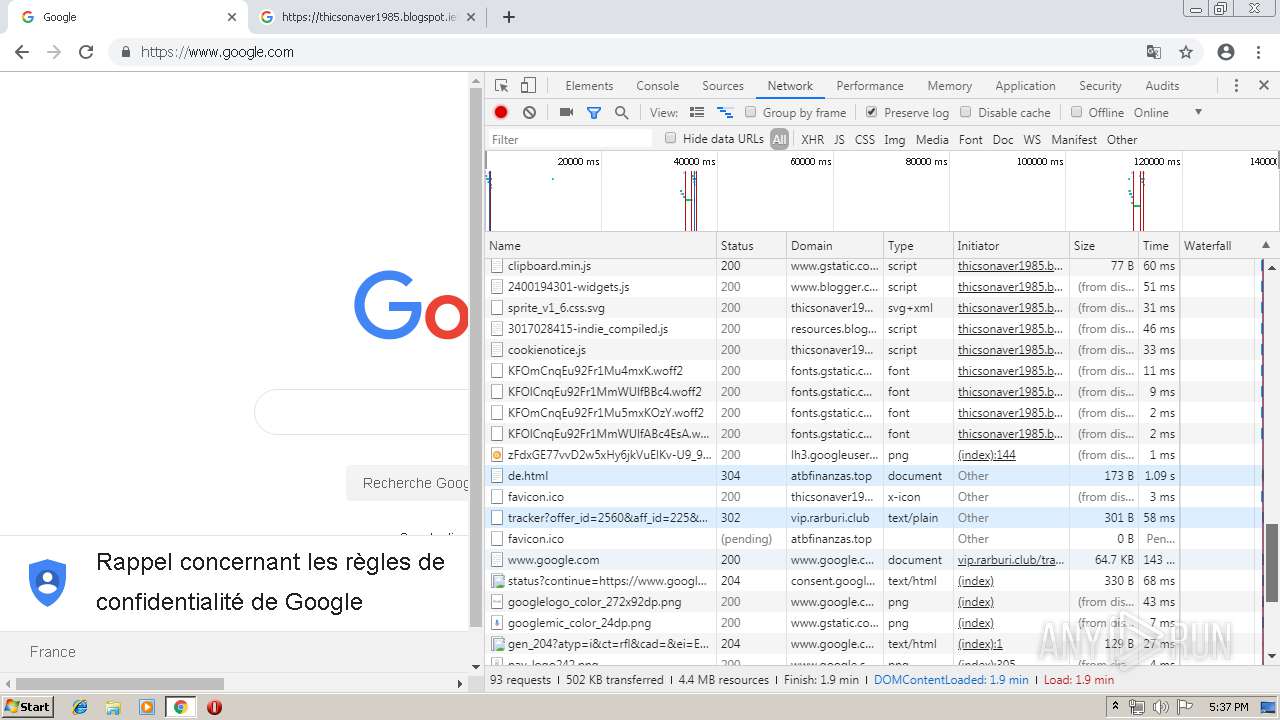
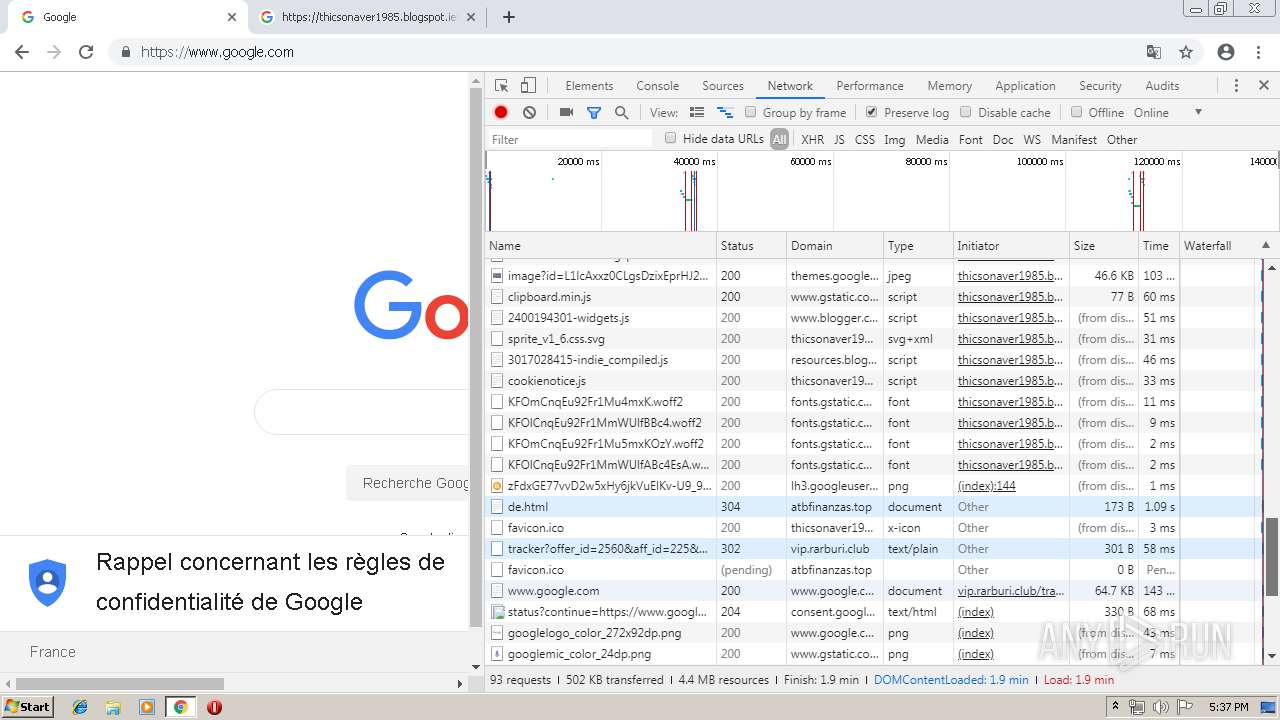
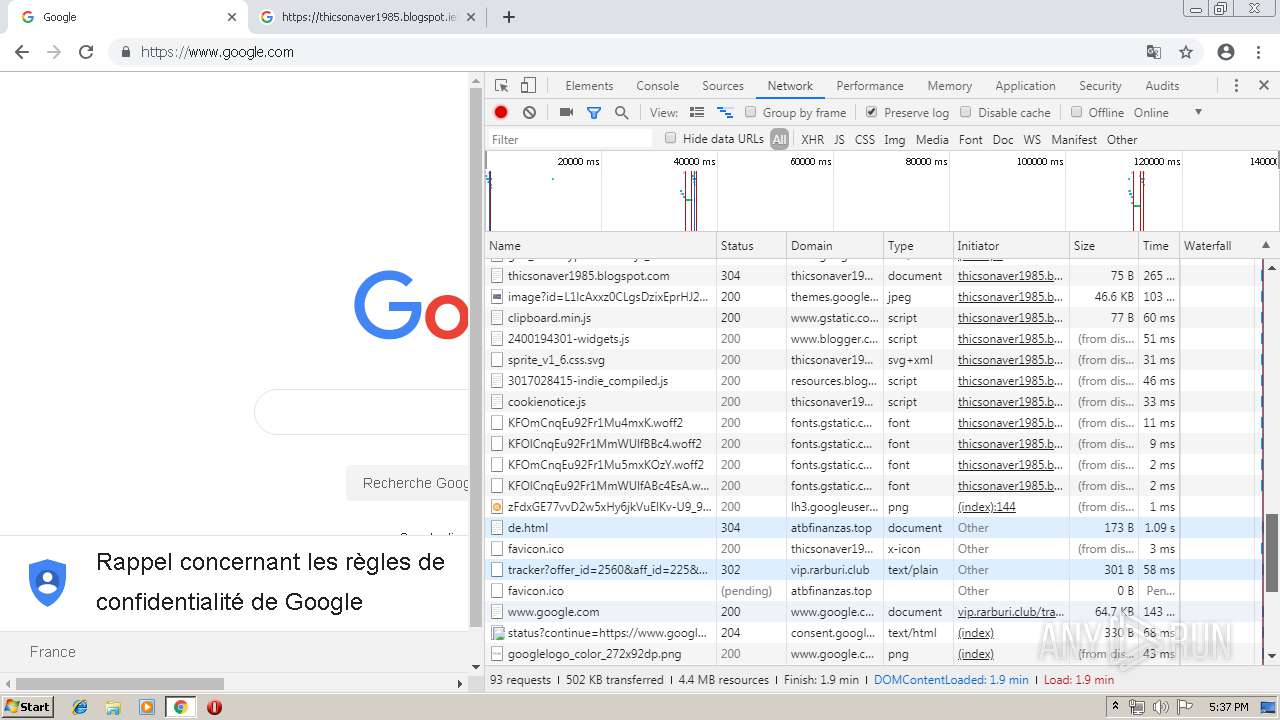
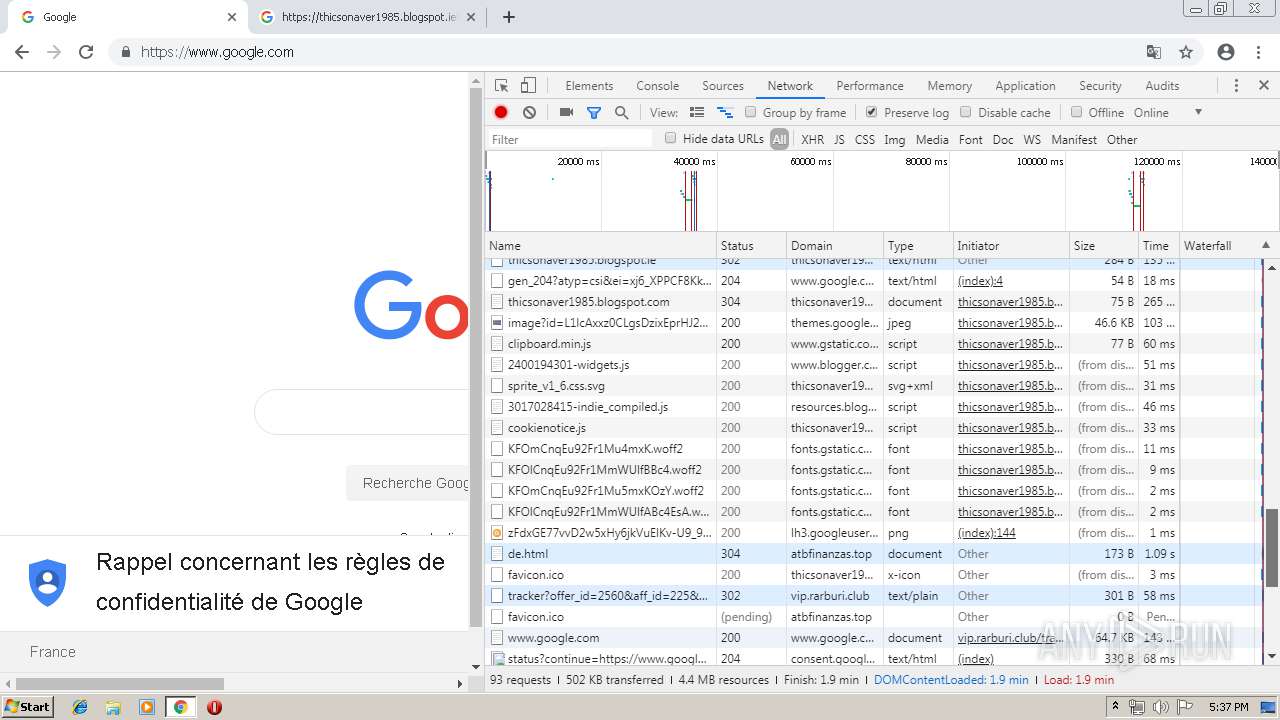
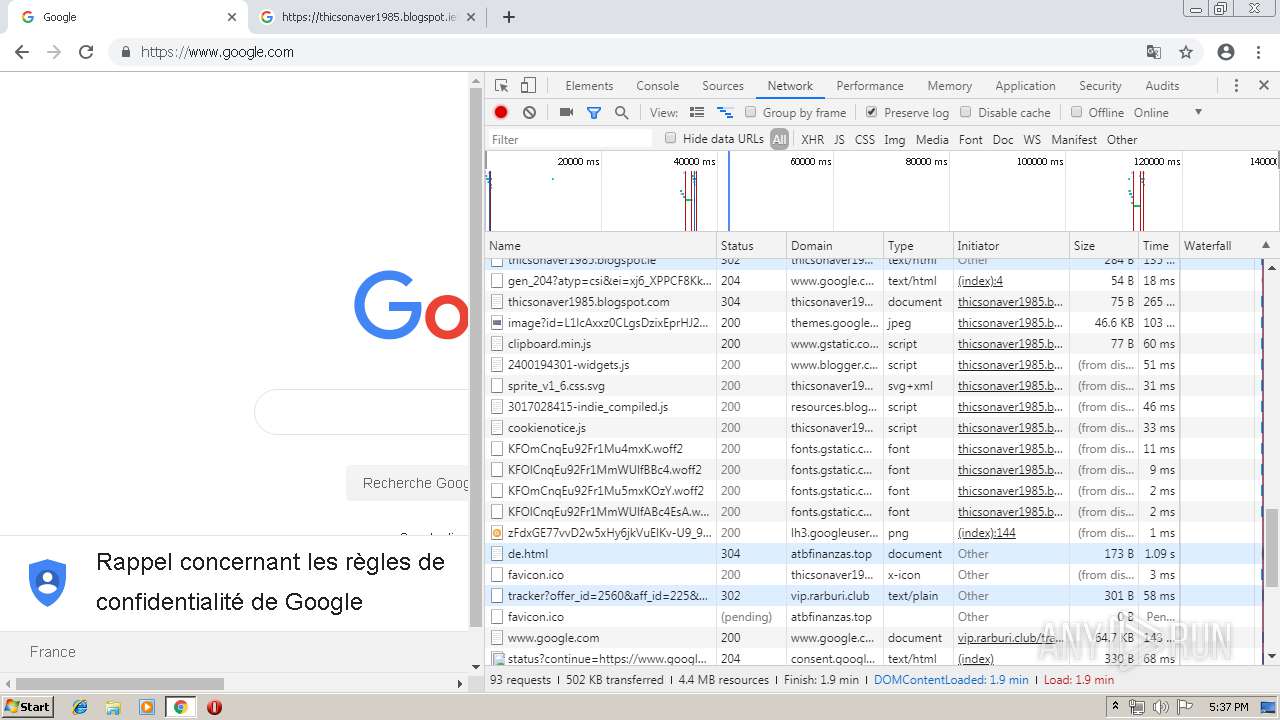
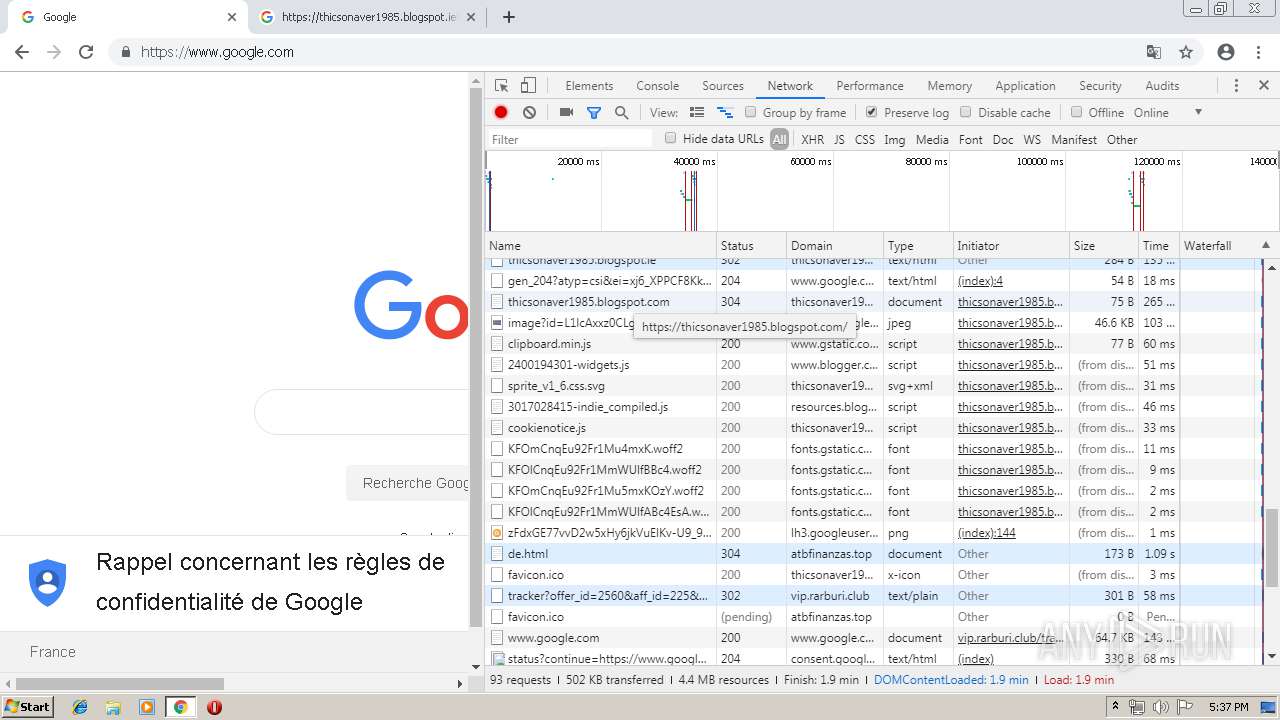
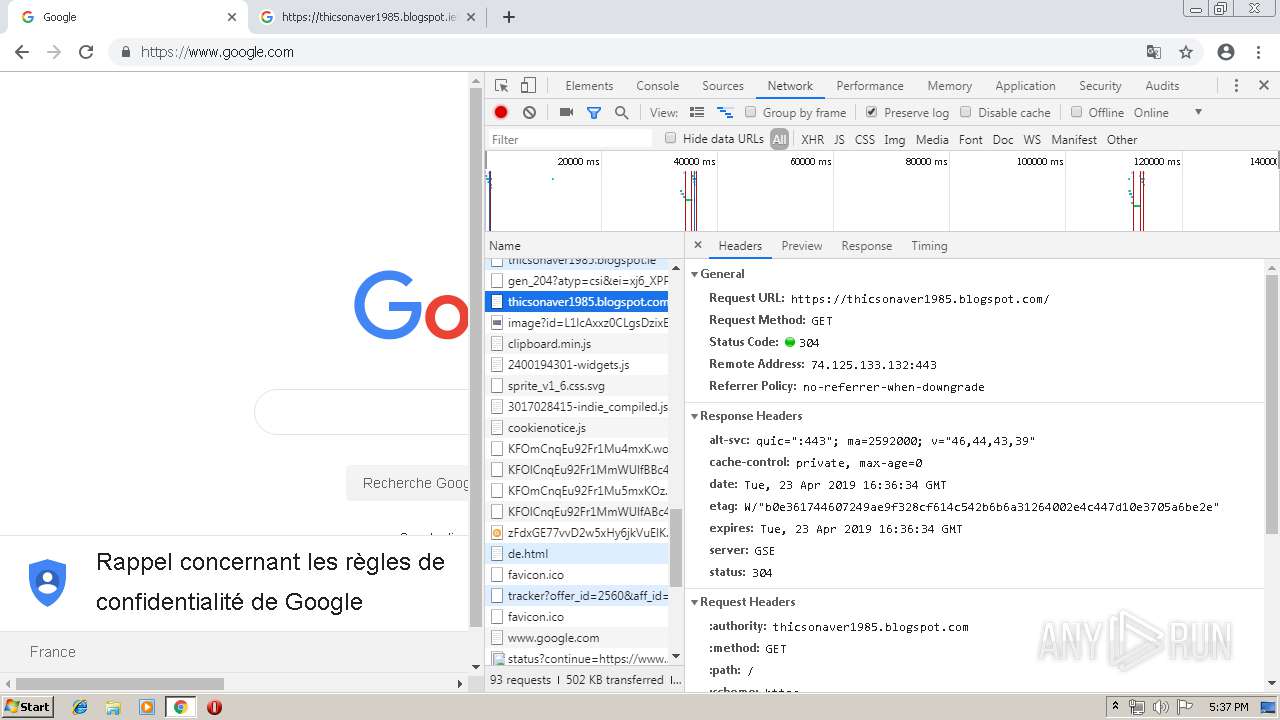
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
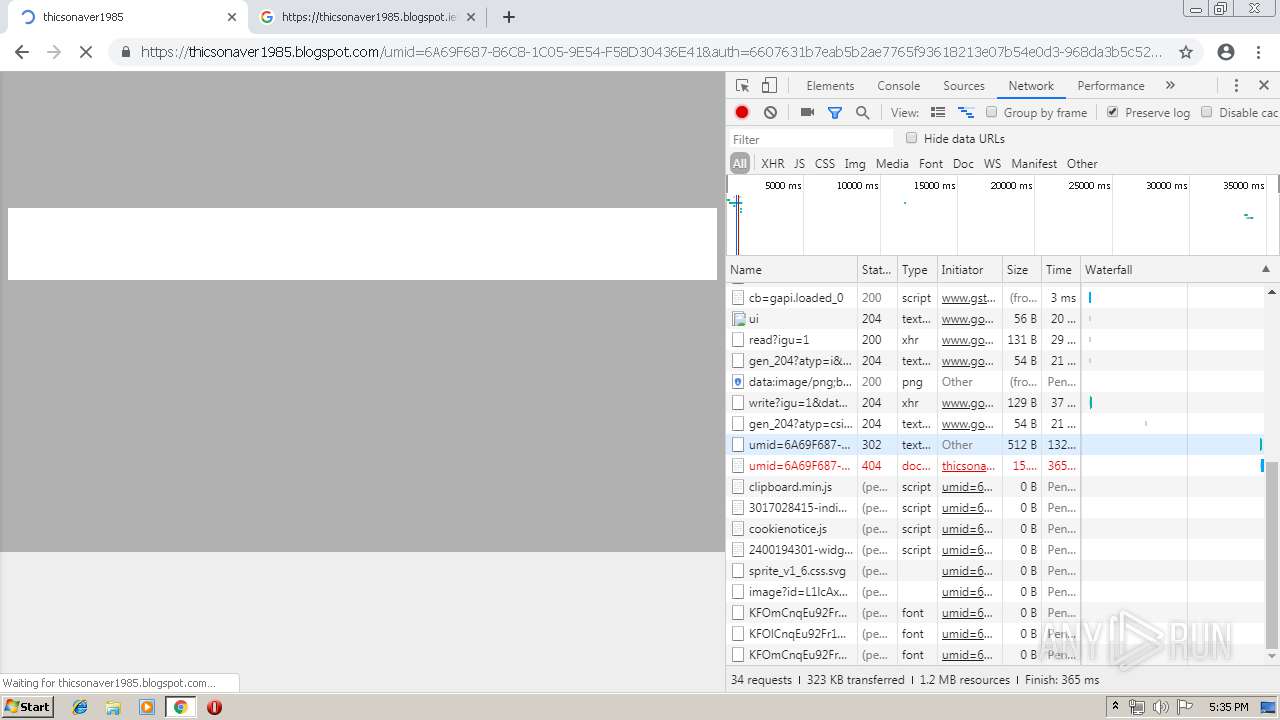
2952 | chrome.exe | GET | — | 47.74.1.120:80 | http://atbfinanzas.top/favicon.ico | JP | — | — | suspicious |
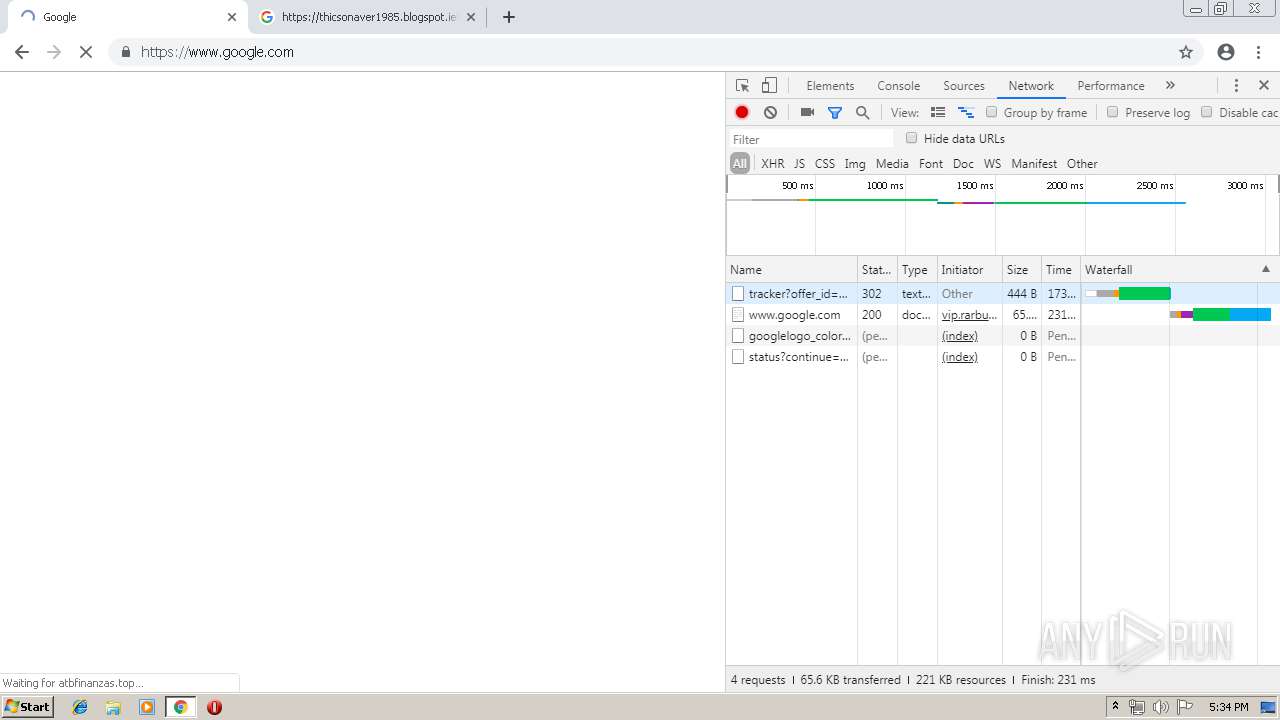
2952 | chrome.exe | GET | 302 | 104.28.7.235:80 | http://vip.rarburi.club/tracker?offer_id=2560&aff_id=225&pl=518:100&cb=1 | US | — | — | malicious |
2952 | chrome.exe | GET | 302 | 104.28.7.235:80 | http://vip.rarburi.club/tracker?offer_id=2560&aff_id=225&pl=518:100&cb=1 | US | — | — | malicious |
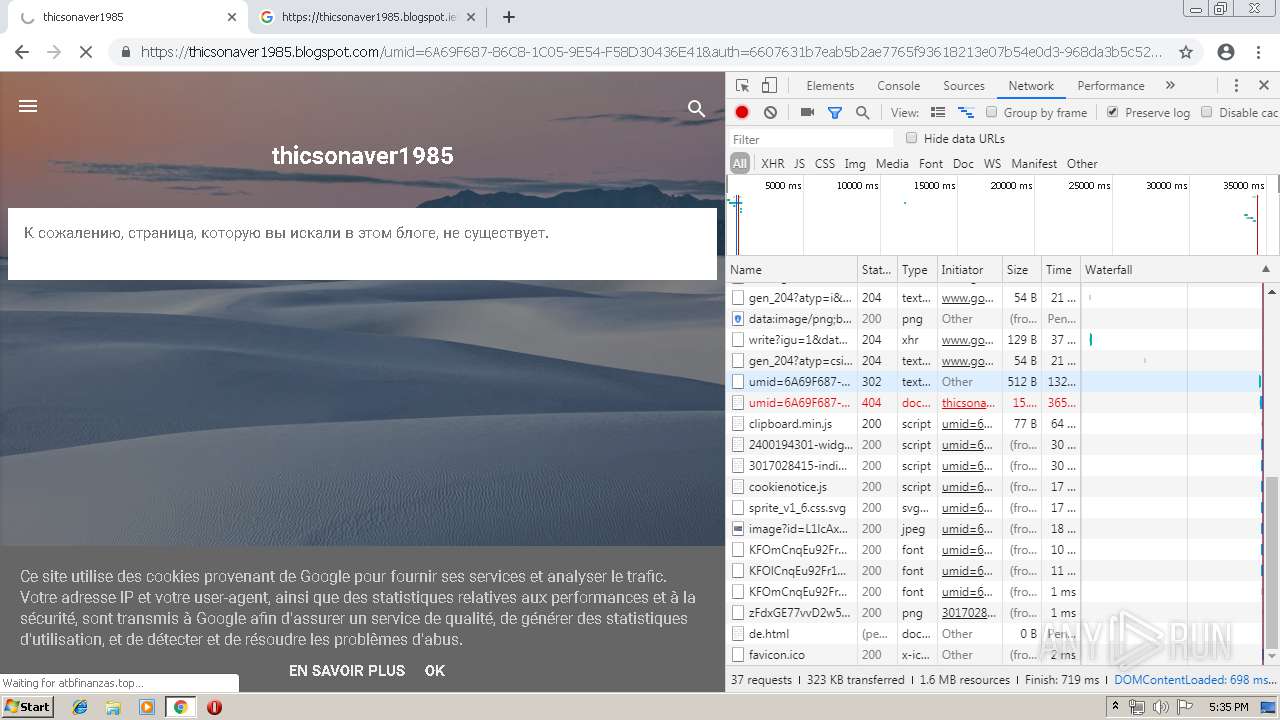
2952 | chrome.exe | GET | 304 | 47.74.1.120:80 | http://atbfinanzas.top/de.html | JP | — | — | suspicious |
2952 | chrome.exe | GET | — | 47.74.1.120:80 | http://atbfinanzas.top/favicon.ico | JP | — | — | suspicious |
2952 | chrome.exe | GET | 304 | 47.74.1.120:80 | http://atbfinanzas.top/de.html | JP | — | — | suspicious |
2952 | chrome.exe | GET | — | 47.74.1.120:80 | http://atbfinanzas.top/favicon.ico | JP | — | — | suspicious |
2952 | chrome.exe | GET | 302 | 104.28.7.235:80 | http://vip.rarburi.club/tracker?offer_id=2560&aff_id=225&pl=518:100&cb=1 | US | — | — | malicious |
2952 | chrome.exe | GET | 200 | 173.194.151.88:80 | http://r2---sn-4g5e6nez.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.13&mm=28&mn=sn-4g5e6nez&ms=nvh&mt=1556036555&mv=u&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2952 | chrome.exe | GET | 200 | 47.74.1.120:80 | http://atbfinanzas.top/de.html | JP | html | 149 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
2952 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 216.58.205.238:443 | google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 173.194.151.88:80 | r2---sn-4g5e6nez.gvt1.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.18.20:443 | chrome-devtools-frontend.appspot.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
google.com |
| malicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-4g5e6nez.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.fr |
| whitelisted |
chrome-devtools-frontend.appspot.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2952 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2952 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2952 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2952 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2952 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |